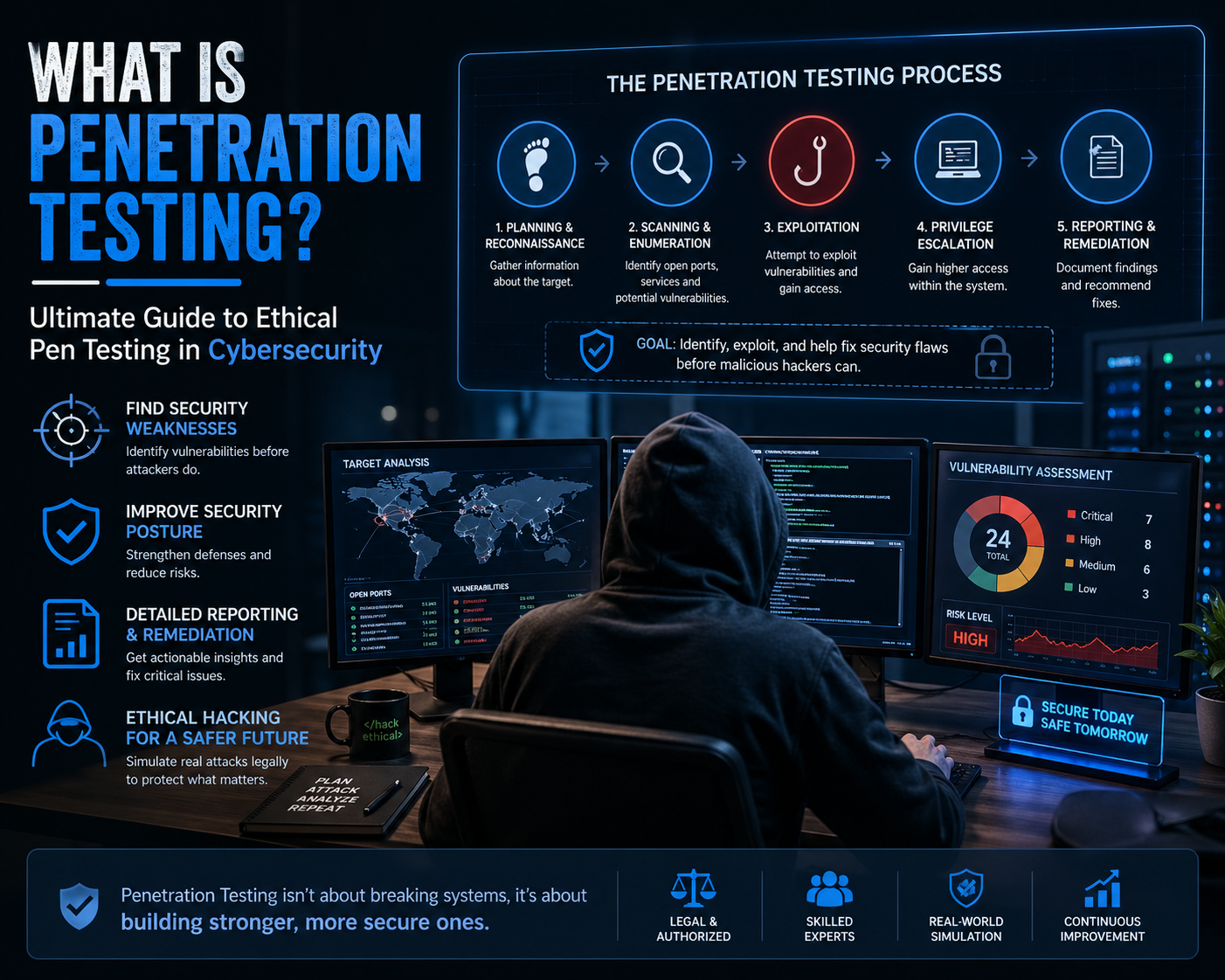
Penetration testing is a controlled and authorized simulation of a cyberattack performed on a computer system, network, application, or digital infrastructure. Its purpose is to evaluate how secure a system truly is when exposed to realistic attack techniques used by malicious actors. Unlike actual cyberattacks, penetration testing is conducted ethically, with permission, and within clearly defined boundaries. It is one of the most practical methods used in cybersecurity to uncover weaknesses before they can be exploited in the real world.
Modern digital environments are highly interconnected, and even a small vulnerability can lead to major security breaches. Penetration testing helps organizations understand how an attacker could potentially move through their systems, access sensitive information, or disrupt operations. Simulating real attack behavior, it provides insights that traditional security audits or automated vulnerability scanners may not fully reveal.
In simple terms, penetration testing answers a critical question: if someone tried to break into this system today, how far could they go?
Purpose of Penetration Testing in Security Environments
The main purpose of penetration testing is to identify security weaknesses before they are discovered by attackers. Every system, regardless of how secure it appears, contains some level of vulnerability. These weaknesses may exist in software design, configuration settings, authentication systems, or even human behavior.
Penetration testing helps organizations measure the real-world impact of these weaknesses. Instead of only identifying theoretical issues, it demonstrates how those issues can actually be exploited. For example, a weak password policy may seem like a minor concern on paper, but in practice, it can allow unauthorized access to critical systems.
Another major objective is risk prioritization. Not all vulnerabilities carry the same level of threat. Some may allow limited access, while others may expose entire databases or administrative control. Penetration testing helps security teams understand which vulnerabilities require immediate attention and which ones are of lower priority.
It also plays a key role in strengthening incident response strategies. By observing how systems react during simulated attacks, organizations can evaluate whether their monitoring tools, alerts, and response procedures are effective.
How Penetration Testing Simulates Real Cyberattacks
Penetration testing is designed to closely replicate the techniques used by real attackers. This includes methods such as scanning for open ports, analyzing system behavior, exploiting software vulnerabilities, and attempting unauthorized access to sensitive resources.
Testers often begin by mapping the target environment to understand its structure. This includes identifying servers, applications, network devices, and exposed services. Once the environment is understood, testers search for potential weaknesses that could be exploited.
These weaknesses may include outdated software versions, misconfigured security settings, unpatched systems, or insecure authentication mechanisms. In some cases, vulnerabilities may also be introduced through human error, such as weak password practices or a lack of awareness regarding phishing attacks.
Once a vulnerability is identified, testers attempt to exploit it in a controlled manner. This step is critical because it demonstrates whether a theoretical weakness can actually be used in a real attack scenario. Successful exploitation may lead to unauthorized access, privilege escalation, or exposure of sensitive data.
The final stage involves analyzing how far an attacker could progress after gaining initial access. This helps organizations understand the potential damage of a real-world breach.
Security Thinking Behind Penetration Testing
A key element of penetration testing is adopting the mindset of a cyber attacker. Instead of focusing only on defense mechanisms, testers think creatively about how those defenses could be bypassed. This includes analyzing system architecture, user behavior, software logic, and network design from an adversarial perspective.
This mindset is essential because attackers rarely follow predictable paths. They often combine multiple small weaknesses to achieve a larger objective. For example, a minor configuration flaw combined with weak authentication controls may lead to full system compromise.
Penetration testers are trained to identify these chains of vulnerabilities. This allows them to simulate realistic attack scenarios rather than isolated technical failures.
This approach also helps uncover hidden risks that traditional security tools might overlook. Automated systems are effective at detecting known vulnerabilities, but they may not fully understand complex attack strategies or logic-based weaknesses.
Real-World Value of Simulated Attacks
Simulated cyberattacks provide organizations with a realistic understanding of their security posture. Unlike theoretical assessments, penetration testing demonstrates how systems behave under actual attack conditions.
One of the most valuable outcomes is visibility. Many organizations assume their systems are secure because they use firewalls, antivirus software, or encryption tools. However, penetration testing often reveals gaps between security design and real-world implementation.
For example, a firewall may be properly configured, but internal systems may still be exposed due to misconfigured permissions. Similarly, encryption may be enabled, but weak authentication may still allow unauthorized access.
Another important outcome is validation. Security controls are often implemented in layers, but penetration testing verifies whether those layers actually work together effectively. It confirms whether defenses are strong enough to withstand coordinated attack attempts.
Types of Security Weaknesses Identified During Testing
Penetration testing uncovers a wide range of vulnerabilities across different layers of a system. Technical vulnerabilities are among the most common and include software bugs, outdated components, and insecure configurations.
Software vulnerabilities often arise from coding errors that allow unexpected behavior. These may include input validation issues, memory handling errors, or insecure API implementations. Such flaws can sometimes be exploited to execute unauthorized commands or access restricted data.
Configuration vulnerabilities occur when systems are not properly secured during setup. Examples include open network ports, default credentials, excessive user permissions, or disabled security features. These issues are often overlooked during deployment but can significantly weaken security.
Network vulnerabilities involve weaknesses in communication channels. These may include unencrypted data transmission, weak firewall rules, or poorly segmented networks. Attackers can exploit these weaknesses to intercept or manipulate data traffic.
Human-related vulnerabilities are also a major concern. Many attacks succeed not because of technical flaws, but because users are tricked into revealing sensitive information. Social engineering techniques such as phishing or impersonation are commonly simulated during penetration testing to assess human awareness.
Role of Information Gathering in Pen Testing
Before any simulated attack begins, penetration testers perform extensive information gathering. This phase is crucial because the success of an attack often depends on how much information is available about the target system.
Information gathering includes identifying publicly available data, system architecture details, exposed services, and potential entry points. It may also involve analyzing how systems respond to external queries or network requests.
This stage helps testers build a detailed understanding of the attack surface. The attack surface refers to all possible points where an attacker could attempt to gain access to a system.
The more complex and interconnected a system is, the larger its attack surface becomes. Penetration testing helps map this surface and identify areas that require stronger protection.
Controlled Nature of Ethical Cybersecurity Testing
Penetration testing is strictly controlled and authorized. It operates under predefined rules that determine what systems can be tested, what methods can be used, and what boundaries must not be crossed.
This controlled environment ensures that testing does not disrupt normal business operations. It also ensures that sensitive data is handled responsibly and not exposed beyond authorized personnel.
Ethical testing is a key distinction between penetration testing and malicious hacking. While both may use similar techniques, the intent, authorization, and outcome are completely different.
Penetration testing exists to improve security, not compromise it. Every action taken during testing is aimed at strengthening defenses and reducing risk exposure.
Foundation of Modern Cybersecurity Strategy
Penetration testing has become a core component of modern cybersecurity strategies. As cyber threats continue to evolve, organizations must constantly evaluate and improve their defenses.
Static security measures are no longer sufficient in dynamic digital environments. Attackers continuously develop new techniques, and systems must be tested regularly to ensure they remain secure.
Penetration testing provides a proactive approach to security. Instead of reacting to incidents after they occur, organizations can identify weaknesses in advance and take corrective action.
It also supports continuous improvement. Each test provides new insights into system behavior, security gaps, and defensive effectiveness. Over time, this leads to stronger and more resilient infrastructure.
What is Black Box Testing in Penetration Testing
Black box testing in penetration testing refers to a security assessment approach where the tester has no prior knowledge of the internal structure, architecture, or configuration of the target system. The tester begins the engagement from an external perspective, just like a real-world attacker who has no insider information. This method is designed to replicate how cybercriminals typically operate when targeting organizations from the outside.
In a black box scenario, the tester does not receive login credentials, system diagrams, source code, or internal documentation. The only information available is what can be gathered through external observation and reconnaissance techniques. This includes publicly accessible data such as domain information, exposed services, network footprints, and application behavior.
The strength of black box testing lies in its realism. Since attackers rarely have internal knowledge of a system, this approach closely mirrors real-world cyberattacks. It evaluates how well external defenses such as firewalls, intrusion detection systems, and access controls can withstand unknown threats.
Black box testing begins with reconnaissance, where testers collect as much publicly available information as possible. This may include identifying IP ranges, domain records, web applications, and server technologies. Once sufficient data is gathered, testers begin scanning for potential vulnerabilities.
These vulnerabilities may include open ports, misconfigured services, outdated software versions, or weak authentication mechanisms. The tester then attempts to exploit these weaknesses to determine whether unauthorized access can be achieved.
A key advantage of this approach is that it reveals how an external attacker perceives the system. It highlights weaknesses that may not be visible to internal teams because it removes any assumptions based on insider knowledge.
However, black box testing also has limitations. Since testers operate without internal knowledge, some deeper vulnerabilities may take longer to discover. Complex logic flaws within applications or systems may remain hidden unless external indicators are present.
Despite these limitations, black box testing remains one of the most widely used penetration testing approaches because of its strong alignment with real-world attack scenarios.
What is White Box Testing in Penetration Testing
White box testing is a penetration testing approach where the tester has full access to internal system information. This includes source code, architecture diagrams, configuration details, network topology, and sometimes administrative credentials. Unlike black box testing, which simulates an external attacker, white box testing simulates an insider or an attacker with privileged access.
This approach allows testers to conduct a much deeper and more thorough security evaluation. Because internal details are available, testers can analyze system logic, identify coding flaws, and examine security mechanisms at a granular level.
White box testing often begins with a detailed review of the system design. Testers examine how different components interact, how data flows between services, and how security controls are implemented. This helps identify structural weaknesses that may not be visible from the outside.
After understanding the system architecture, testers analyze the source code for vulnerabilities. This may include insecure input handling, improper authentication logic, weak encryption methods, or insecure API usage. These issues are often difficult to detect through external testing alone.
White box testing also allows for precise vulnerability validation. Since testers understand the internal workings of the system, they can quickly determine whether a vulnerability is exploitable and how it can be mitigated.
One of the major strengths of white box testing is its depth of coverage. It provides a comprehensive view of system security and allows organizations to identify hidden risks that may not be exposed through external testing methods.
However, white box testing also has challenges. It requires significant access to internal systems, which may not always be feasible in all environments. It can also be time-intensive due to the detailed analysis involved.
Despite these challenges, white box testing is highly valuable for secure software development, internal system audits, and code-level security validation.
What is Gray Box Testing in Penetration Testing
Gray box testing is a hybrid penetration testing approach that combines elements of both black box and white box testing. In this method, the tester has partial knowledge of the system. This may include limited credentials, partial documentation, or a basic understanding of the system architecture.
The goal of gray box testing is to simulate an attacker who has already gained some level of access to the system. This could represent a compromised user account, a disgruntled employee with limited privileges, or an attacker who has successfully breached the outer perimeter.
Gray box testing is widely used because it provides a balanced perspective between external attack simulation and internal system analysis. It allows testers to focus on both entry point vulnerabilities and post-access behavior.
The testing process typically begins with the available information provided to the tester. This may include user-level credentials, application workflows, or network access points. Using this information, testers attempt to escalate privileges, move laterally across systems, and access restricted resources.
Gray box testing is particularly effective in identifying privilege escalation vulnerabilities. These occur when a low-level user gains access to higher-level functions or sensitive data due to misconfigured permissions or logic flaws.
It also helps identify business logic vulnerabilities, where system functionality behaves in unintended ways under certain conditions. These types of vulnerabilities are often difficult to detect through purely external or internal testing alone.
One of the strengths of gray box testing is its efficiency. Since testers already have partial knowledge of the system, they can focus more quickly on high-risk areas without spending excessive time on initial reconnaissance.
However, gray box testing may not fully replicate either a pure external attacker or a fully internal audit perspective. It sits in the middle, providing a realistic but partially informed attack simulation.
Comparing Black Box, White Box, and Gray Box Approaches
Each penetration testing approach serves a different purpose and provides unique insights into system security. Black box testing focuses on external attack simulation, white box testing focuses on internal system analysis, and gray box testing focuses on partial-access attack scenarios.
Black box testing is most effective for evaluating external defenses. It shows how a system appears to outsiders and how well perimeter security controls perform against unknown threats. This approach is commonly used for testing public-facing applications, websites, and network services.
White box testing is most effective for identifying deep structural vulnerabilities. It provides full visibility into system design and code, allowing testers to uncover hidden flaws that may not be exposed externally. This approach is often used in secure software development and internal security audits.
Gray box testing combines both perspectives and is useful for simulating realistic compromise scenarios. It helps organizations understand what happens after an attacker gains initial access and how far they can move within the system.
The choice between these approaches depends on security objectives. Organizations may choose one method or combine all three to achieve a comprehensive security assessment.
Attack Simulation Techniques in Different Testing Models
In black box testing, attack simulation is based on external reconnaissance and probing. Testers rely heavily on scanning tools, publicly available information, and behavioral analysis of exposed systems. The goal is to discover entry points without prior knowledge of internal structures.
In white box testing, attack simulation is more analytical. Testers examine code logic, configuration settings, and system design to identify vulnerabilities. Exploitation is often simulated at the code level, allowing precise identification of root causes.
In gray box testing, the attack simulation begins with partial access. Testers may log in using provided credentials and explore the system from an authenticated user perspective. This allows them to simulate real-world scenarios such as account compromise or insider threats.
Each model uses different techniques, but all aim to replicate attacker behavior as realistically as possible.
Role of Access Levels in Security Testing
Access levels play a crucial role in determining how penetration testing is conducted. In black box testing, access is completely external. In white box testing, access is fully internal. In gray box testing, access is partially restricted.
These access levels influence how vulnerabilities are discovered and exploited. For example, an external attacker may only see login portals or public APIs, while an internal tester may see database structures and application logic.
Understanding access levels helps organizations evaluate security from multiple perspectives. It ensures that both external and internal threats are considered during security assessments.
Importance of Realistic Threat Modeling
Penetration testing is closely linked to threat modeling, which involves analyzing potential attack scenarios and identifying how threats could materialize in real environments. Each testing approach contributes differently to threat modeling.
Black box testing supports external threat modeling by simulating unknown attackers. White box testing supports internal threat modeling by analyzing system design flaws. Gray box testing supports hybrid threat modeling by simulating compromised user scenarios.
Together, these approaches provide a comprehensive understanding of how threats can emerge and evolve within a system.
Security Insights Derived from Testing Variations
Different penetration testing approaches generate different types of security insights. Black box testing highlights external exposure risks, white box testing reveals internal structural weaknesses, and gray box testing identifies privilege and access control issues.
These insights help organizations strengthen their overall security posture. By combining results from multiple testing methods, security teams can build layered defenses that address both external and internal threats.
Strategic Value of Multi-Approach Testing
Organizations often benefit from using multiple penetration testing approaches rather than relying on a single method. This is because each approach uncovers different categories of vulnerabilities.
A combined strategy ensures that systems are evaluated from multiple angles, reducing the likelihood of overlooked risks. It also provides a more accurate representation of how attackers with varying levels of access might behave.
This layered testing strategy is especially important in complex environments such as cloud infrastructures, enterprise networks, and large-scale applications where attack surfaces are extensive.
Advanced Penetration Testing Techniques in Modern Cybersecurity
Penetration testing has evolved far beyond basic vulnerability scanning and simple exploitation attempts. Modern cyber environments are highly dynamic, distributed, and layered with multiple security controls, which means penetration testers must adopt more advanced and adaptive techniques. These techniques are designed to mimic sophisticated threat actors who use multi-stage attacks, stealth methods, and long-term persistence strategies.
One of the key developments in advanced penetration testing is the focus on attack chaining. Instead of treating vulnerabilities as isolated issues, testers now combine multiple small weaknesses to achieve a larger compromise. For example, an exposed service may not be critical on its own, but when combined with weak credentials and misconfigured permissions, it can lead to full administrative control of a system. This chaining approach reflects how real attackers operate in modern cyberattacks.
Another advanced technique is privilege escalation analysis. Once initial access is achieved, testers explore ways to increase their level of control within the system. This may involve exploiting misconfigured user roles, insecure system services, or outdated operating system components. Privilege escalation is a critical phase because it determines how much damage an attacker can ultimately cause after breaching the system.
Lateral movement is also a major focus. After gaining access to one system, testers attempt to move across the network to other connected systems. This helps evaluate segmentation controls and internal security boundaries. In well-secured environments, lateral movement should be limited or completely blocked through proper network segmentation and access controls.
Persistence techniques are also simulated during advanced penetration testing. Persistence refers to the ability of an attacker to maintain access even after initial detection or partial remediation. Testers may simulate backdoor creation, credential harvesting, or scheduled task manipulation to assess whether an attacker could remain undetected within the environment.
Exploitation Methodologies and Attack Execution
Exploitation is the stage where identified vulnerabilities are actively tested to determine whether they can be used to compromise systems. In advanced penetration testing, exploitation is not just about proving a vulnerability exists but also understanding its full impact in a controlled environment.
Testers use different exploitation methodologies depending on the target environment. In web applications, this may involve injection-based attacks, session manipulation, or authentication bypass techniques. In network environments, exploitation may involve protocol weaknesses, service misconfigurations, or unpatched software vulnerabilities.
One important aspect of exploitation is safe execution. Since penetration testing is performed in live environments, testers must ensure that exploitation does not cause unintended damage. This requires careful planning, controlled payloads, and strict adherence to defined testing boundaries.
Another key aspect is verification of impact. After successful exploitation, testers analyze what level of access was achieved and what sensitive resources became available. This helps organizations understand the real-world consequences of a vulnerability rather than just its theoretical severity.
Advanced exploitation also involves bypassing security controls. Modern systems use firewalls, intrusion detection systems, endpoint protection tools, and behavioral monitoring systems. Penetration testers often simulate techniques used by advanced attackers to bypass or evade these defenses, helping organizations evaluate the effectiveness of their security stack.
Social Engineering in Penetration Testing
Not all vulnerabilities exist in technology. Many security breaches occur due to human behavior. Social engineering is the practice of manipulating individuals into revealing confidential information or performing actions that compromise security.
In penetration testing, social engineering is used to evaluate how employees respond to deception-based attacks. These may include phishing simulations, impersonation attempts, or fraudulent communication scenarios.
Phishing remains one of the most common social engineering techniques. Testers may simulate fake login pages or deceptive emails to assess whether users can identify and avoid suspicious content. The goal is not to trick users maliciously but to measure awareness levels and identify training gaps.
Impersonation attacks involve pretending to be a trusted authority figure or internal employee. This may be used to test whether sensitive information can be obtained through social trust rather than technical exploitation.
Social engineering assessments provide valuable insights into the human side of cybersecurity. Even the strongest technical defenses can be undermined by human error, making this aspect of penetration testing essential in comprehensive security evaluations.
Post-Exploitation Analysis and Impact Assessment
Once a system has been successfully exploited, penetration testing moves into the post-exploitation phase. This phase focuses on understanding the full extent of potential damage that could result from a real attack.
Post-exploitation analysis involves examining what data can be accessed, what systems can be controlled, and how deeply an attacker could penetrate the environment. This may include access to sensitive files, databases, administrative interfaces, or internal communication systems.
One key objective is data exposure assessment. Testers evaluate whether sensitive information such as personal data, financial records, or authentication credentials can be accessed or extracted.
Another important aspect is system control evaluation. This determines whether attackers could modify system configurations, disable security controls, or deploy malicious software within the environment.
Post-exploitation also includes assessing detection capabilities. Testers analyze whether security monitoring systems detect unusual activity during the attack simulation. If no alerts are triggered, it may indicate gaps in monitoring or logging systems.
This phase provides organizations with a realistic understanding of breach impact, helping them prioritize security improvements based on actual risk exposure rather than theoretical assumptions.
Reporting and Documentation in Penetration Testing
The reporting phase is one of the most important components of penetration testing. It transforms technical findings into actionable security intelligence that organizations can use to improve their defenses.
A penetration testing report typically includes detailed descriptions of vulnerabilities, how they were discovered, how they were exploited, and what impact they could have in a real attack scenario. It also includes risk classification, which helps organizations prioritize remediation efforts.
Effective reporting focuses not only on technical details but also on business impact. Instead of simply listing vulnerabilities, it explains how those vulnerabilities could affect operations, data integrity, customer trust, and regulatory compliance.
Another key aspect of reporting is clarity. Security teams, management, and technical staff all need to understand the findings, even if they do not have deep technical expertise. This requires translating complex technical issues into clear and structured insights.
Reports also include remediation guidance. This involves recommending specific actions to fix vulnerabilities, such as configuration changes, software updates, code modifications, or security control enhancements.
In advanced penetration testing, reporting may also include attack chain visualization. This shows how multiple vulnerabilities were combined to achieve a full compromise, helping organizations understand how small weaknesses can escalate into major breaches.
Risk Analysis and Security Prioritization
Penetration testing is closely tied to risk analysis. Not all vulnerabilities present the same level of threat, and organizations must prioritize their response based on potential impact and exploitability.
Risk analysis involves evaluating three main factors: likelihood, impact, and detectability. Likelihood refers to how easy it is for a vulnerability to be exploited. Impact refers to the level of damage that exploitation could cause. Detectability refers to how likely it is that an attack would be noticed.
By analyzing these factors, penetration testers help organizations determine which vulnerabilities require immediate attention. For example, a high-impact vulnerability that is easily exploitable would be prioritized over a low-impact issue that is difficult to exploit.
Risk prioritization also helps organizations allocate security resources efficiently. Instead of attempting to fix every issue at once, security teams can focus on the most critical threats first.
Real-World Attack Simulation Scenarios
Advanced penetration testing often involves simulating full attack scenarios rather than isolated vulnerabilities. These scenarios replicate how real attackers behave over time.
A typical scenario may begin with external reconnaissance, followed by exploitation of a web application vulnerability. After gaining initial access, the attacker may escalate privileges, move laterally across systems, and attempt to access sensitive databases.
Another scenario may involve insider threats, where an attacker already has limited access within the system. The tester evaluates how much damage can be done using internal credentials and whether sensitive resources are properly protected.
Long-term persistence scenarios are also simulated. These tests evaluate whether attackers could maintain access over extended periods without being detected.
By simulating these complete attack chains, organizations gain a realistic understanding of how breaches occur and how they can be prevented or contained.
Integration of Penetration Testing into Security Programs
Penetration testing is most effective when integrated into a broader cybersecurity strategy. It should not be treated as a one-time activity but rather as an ongoing process that evolves with the system.
Regular testing helps organizations stay ahead of emerging threats and adapt to changes in their infrastructure. As systems grow and evolve, new vulnerabilities may be introduced, making continuous assessment essential.
Integration also involves combining penetration testing with other security practices such as vulnerability management, threat intelligence, and security monitoring. Together, these elements create a layered defense strategy that improves overall resilience.
Penetration testing also supports secure development practices. By identifying vulnerabilities early in the development lifecycle, organizations can reduce the cost and complexity of fixing security issues.
Evolution of Penetration Testing in Modern Threat Landscapes
As cyber threats become more sophisticated, penetration testing continues to evolve. Modern attackers use advanced techniques such as automation, artificial intelligence, and multi-stage attack frameworks.
In response, penetration testing now incorporates more dynamic and adaptive methodologies. Testers must continuously update their techniques to reflect the latest attack strategies and defensive technologies.
Cloud environments, mobile applications, and distributed systems have also expanded the scope of penetration testing. Security assessments now cover a wider range of platforms and architectures than ever before.
This evolution ensures that penetration testing remains a critical component of cybersecurity defense, helping organizations stay resilient in an increasingly complex digital landscape.
Conclusion
Penetration testing represents one of the most practical and reality-driven approaches in modern cybersecurity because it shifts security evaluation from theory into real-world simulation. Instead of assuming that systems are secure based on design, policies, or automated scans, penetration testing actively challenges those assumptions by replicating how actual attackers think and operate. This makes it an essential discipline for any organization that relies on digital infrastructure, especially in environments where data protection, uptime, and trust are critical business priorities.
At its core, penetration testing demonstrates a fundamental truth in cybersecurity: no system is ever completely secure. Every application, network, or device has potential weaknesses, whether they come from software flaws, configuration errors, or human behavior. The value of penetration testing lies not in proving that systems are vulnerable, but in identifying how those vulnerabilities can be discovered and exploited before malicious actors do so in the real world. By uncovering these weaknesses in a controlled environment, organizations gain the opportunity to fix issues proactively rather than reacting to security incidents after damage has already occurred.
One of the most important contributions of penetration testing is its ability to bridge the gap between technical security controls and real attacker behavior. Traditional security tools such as firewalls, antivirus systems, and intrusion detection platforms are essential, but they operate based on known patterns and predefined rules. Attackers, however, do not always follow predictable paths. They combine techniques, exploit human psychology, and adapt their strategies dynamically. Penetration testing mirrors this behavior, allowing organizations to understand how their defenses perform under realistic pressure rather than ideal conditions.
Another key benefit is the clarity it brings to risk understanding. Security vulnerabilities are often abstract when viewed individually, but penetration testing translates them into real impact scenarios. For example, a misconfigured access control setting is not just a technical flaw; in a penetration test, it becomes a demonstration of how an attacker could access sensitive data, escalate privileges, or move laterally within a network. This transformation from technical issue to business impact helps decision-makers prioritize security investments more effectively and focus on risks that matter most to operational continuity and data protection.
Penetration testing also plays a critical role in strengthening organizational resilience. Cybersecurity is not just about preventing attacks, but also about ensuring that systems can withstand and recover from them. By simulating attacks in advance, organizations can evaluate how their monitoring systems respond, how quickly incidents are detected, and how effectively response procedures are executed. This allows security teams to refine their incident response strategies and reduce the time between detection and containment, which is often the difference between a minor security event and a major breach.
Human factors are another major area where penetration testing delivers significant value. Many successful cyberattacks are not purely technical in nature but rely on social engineering techniques that target human behavior. Users may unknowingly reveal sensitive credentials, click on malicious links, or bypass security procedures under deceptive circumstances. Penetration testing helps expose these weaknesses by simulating realistic manipulation scenarios. The results often highlight the need for improved awareness training and a stronger internal security culture, which are just as important as technical defenses in maintaining overall security.
In addition, penetration testing supports continuous improvement in secure system design. Modern systems are highly complex, often consisting of interconnected applications, cloud services, APIs, and third-party integrations. This complexity increases the likelihood of overlooked vulnerabilities. Regular testing ensures that as systems evolve, new risks are identified and addressed early. It also encourages development teams to adopt secure coding practices, better configuration standards, and stronger validation mechanisms throughout the software lifecycle.
From a strategic perspective, penetration testing contributes to long-term cybersecurity maturity. Organizations that regularly conduct testing tend to develop stronger security awareness, more structured risk management processes, and more resilient infrastructure over time. The insights gained from repeated testing cycles help security teams track improvements, identify recurring issues, and measure the effectiveness of implemented security controls. This creates a feedback loop where each test strengthens the overall security posture.
Another important aspect is compliance and regulatory alignment. Many industries operate under strict security standards that require regular assessment of systems and data protection mechanisms. Penetration testing provides documented evidence that systems are being actively evaluated and improved. This not only helps meet regulatory requirements but also builds trust with clients, partners, and stakeholders who rely on the organization to protect sensitive information.
As cyber threats continue to evolve, penetration testing has also adapted to new environments such as cloud infrastructure, hybrid networks, mobile platforms, and distributed systems. Attack surfaces are no longer limited to traditional on-premise networks. They now extend across virtual environments, remote access systems, and interconnected services. Penetration testing has expanded accordingly, ensuring that security assessments remain relevant in increasingly complex digital ecosystems.
Ultimately, penetration testing serves as both a diagnostic tool and a strategic defense mechanism. It identifies weaknesses, validates security controls, simulates attacker behavior, and strengthens overall resilience. More importantly, it transforms cybersecurity from a reactive discipline into a proactive one. Instead of waiting for breaches to occur, organizations can anticipate threats, understand their potential impact, and take informed action to reduce risk.
In a digital landscape where threats are constantly evolving and becoming more sophisticated, penetration testing is no longer optional. It is a necessary component of responsible security management. By continuously challenging systems under controlled conditions, organizations build stronger defenses, improve awareness, and develop the ability to respond effectively when real threats emerge.