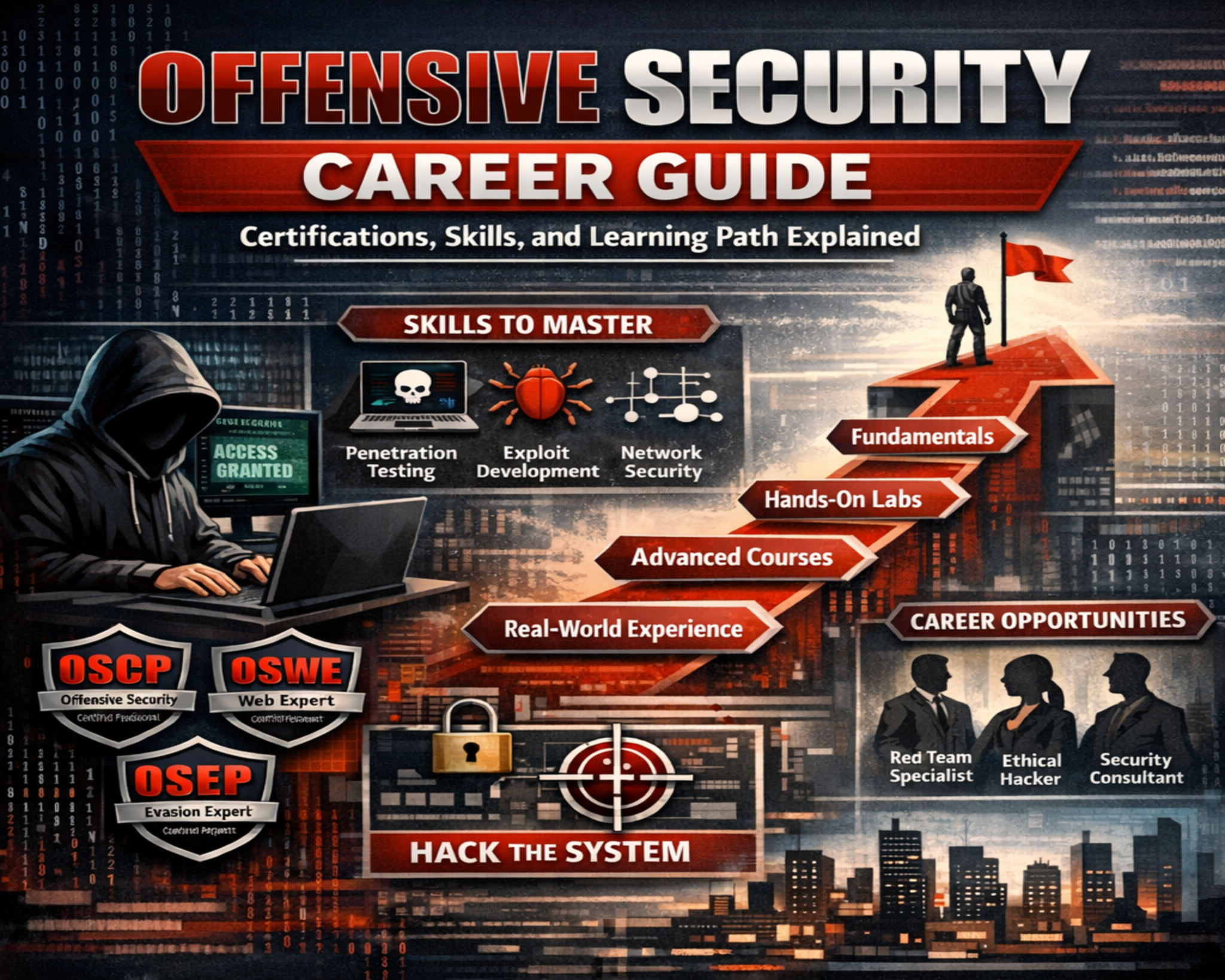
Offensive security certification programs are designed to evaluate real-world cybersecurity capability through controlled, hands-on environments. Instead of relying on theoretical recall or multiple-choice assessments, these certifications focus on practical execution of security tasks. Candidates are required to demonstrate how they approach system reconnaissance, vulnerability identification, exploitation, and post-exploitation analysis within realistic lab infrastructures. The emphasis is on applied skill rather than memorized knowledge, ensuring that certified professionals can operate effectively in environments that simulate real cyberattacks. This model reflects modern cybersecurity requirements where organizations value practitioners who can actively defend and assess systems under pressure.
Evolution of Practical Cybersecurity Training Methodologies
Cybersecurity education has shifted from theory-based instruction toward immersive, performance-driven learning. Earlier certification models focused heavily on conceptual understanding, which often failed to translate into real operational capability. As cyber threats became more advanced, training environments evolved to include interactive labs that simulate enterprise networks. These environments allow candidates to work directly with live systems, replicate attack behaviors, and analyze system responses in real time. This shift has significantly increased the relevance of certifications in professional cybersecurity roles by prioritizing execution over memorization.
Endurance Demands in Long-Duration Security Examinations
Offensive security certification exams are known for their extended duration, often ranging between 24 and 72 hours. This structure is intentionally designed to reflect real-world attack scenarios where adversaries may persist over long periods. Candidates must maintain focus, accuracy, and logical thinking while performing continuous technical tasks. As fatigue builds, decision-making becomes more difficult, making mental resilience a key factor in success. The endurance element ensures that certified professionals can sustain performance under pressure, similar to real cybersecurity incident conditions.
Ethical Hacking as a Foundational Security Discipline
Ethical hacking is the core principle behind offensive security certification programs. It involves simulating malicious attack techniques in controlled environments to identify vulnerabilities before they are exploited by real attackers. This approach helps professionals understand system weaknesses from an attacker’s perspective. By analyzing how systems behave under simulated attacks, candidates learn how to detect and prevent security flaws. Ethical hacking strengthens organizational security by shifting focus from reaction to prevention and proactive defense.
Core Technical Competencies Evaluated in Certification Exams
These certification exams assess a wide range of technical cybersecurity skills. Candidates must perform network enumeration to identify systems and services, followed by vulnerability analysis to detect weaknesses. Exploitation techniques are then applied to gain controlled access to systems. Additional areas include web application security testing, where injection flaws and authentication issues are evaluated. Some certifications also include wireless security assessment, focusing on encryption weaknesses and network access control bypass techniques. Scripting and automation skills are often required to improve efficiency during assessments.
Use of Controlled Lab Environments in Security Training
Offensive security training relies heavily on isolated virtual environments that replicate real enterprise infrastructures. These environments contain multiple interconnected systems, each configured with specific vulnerabilities. Candidates must navigate through these systems step by step to achieve assigned objectives. The environment reacts dynamically to user actions, requiring adaptive thinking and strategic planning. This simulation-based structure closely mirrors real penetration testing engagements, where each system requires a different approach based on discovered weaknesses.
Essential Foundational Knowledge for Certification Success
Success in offensive security certification programs depends on strong technical foundations. Networking knowledge, especially TCP/IP communication, is essential for understanding how systems interact. Linux operating systems are heavily used, making command-line proficiency critical. Basic programming knowledge helps candidates modify scripts and automate tasks during assessments. Understanding system architecture, including memory management and process execution, is important for advanced exploitation scenarios. These foundational skills enable candidates to approach complex environments with structured analysis.
Specialized Security Operating Environments and Toolsets
These certification programs use specialized operating systems designed for penetration testing. These environments include tools for network scanning, vulnerability detection, packet analysis, and exploit development. The integration of tools into a single system allows candidates to focus on methodology rather than setup. Additional tools support wireless security testing, password attacks, and web application analysis. Scripting support is also included to enhance automation capabilities. Familiarity with these environments is essential for effective performance during both training and exams.
Modular Structure of Advanced Security Certifications
Offensive security certifications are structured into specialized domains rather than a strict linear path. Each certification focuses on a specific area such as penetration testing, web application security, wireless assessment, or advanced exploitation. This modular approach allows professionals to develop expertise based on career goals. As candidates progress, technical complexity increases significantly, requiring deeper analytical skills and advanced exploitation methods. This flexible structure supports specialization within cybersecurity careers.
Examination Control Systems and Assessment Integrity
Certification exams are conducted in controlled, monitored environments to ensure fairness and integrity. Candidates work within isolated systems under continuous supervision. External assistance is strictly prohibited to ensure that performance reflects individual capability. Each candidate receives a unique environment with specific objectives that must be completed independently. This controlled structure guarantees that certification results accurately reflect technical skill and problem-solving ability.
Importance of Analytical Reasoning in Security Operations
Analytical thinking is essential in offensive security environments. Candidates must interpret system behavior and identify relationships between different components. This helps determine the most effective attack paths and exploitation strategies. Complex systems often require multi-step solutions that depend on accurate analysis. Strong reasoning skills allow candidates to prioritize tasks, adapt strategies, and respond effectively to changing system conditions.
Relevance to Professional Cybersecurity Development Pathways
Offensive security certification training plays a major role in cybersecurity career development. The skills gained are directly applicable to roles such as penetration testing, security analysis, and vulnerability assessment. Organizations value professionals who can simulate real attacks and identify weaknesses proactively. These certifications prepare individuals for operational environments where practical skills are more important than theoretical knowledge. As cyber threats continue to evolve, demand for professionals with hands-on expertise continues to grow across industries.
Kali Linux and Its Role in Offensive Security Training
Kali Linux plays a central role in offensive security certification pathways because it provides a preconfigured environment optimized for penetration testing and cybersecurity analysis. Built on a Linux foundation, it includes a wide range of tools designed for network reconnaissance, vulnerability assessment, exploit development, and digital forensics. The distribution is widely used in training environments because it eliminates the need for manual tool installation and configuration, allowing candidates to focus entirely on methodology and execution. In offensive security scenarios, familiarity with Kali Linux is essential since most tasks are performed through command-line interfaces and scripting environments. The system is structured to support real-world attack simulation, where professionals must analyze network behavior, identify weak points, and execute controlled exploitation techniques. Its integrated toolset enables efficient workflow management, particularly in complex environments involving multiple systems and layered security controls.
Core Philosophy Behind Penetration Testing Methodology
Penetration testing within offensive security frameworks is built on a structured methodology that mirrors real adversarial behavior. The process typically begins with reconnaissance, where information about target systems is collected through passive and active techniques. This is followed by scanning and enumeration, which help identify open services, network configurations, and potential vulnerabilities. Once weaknesses are identified, exploitation techniques are applied to gain access to systems under controlled conditions. After initial access, privilege escalation methods are used to expand control within the environment. The final stage involves maintaining access and documenting findings. This structured workflow ensures that candidates develop a systematic approach to security testing rather than relying on random or unorganized attempts. The methodology reflects real-world penetration testing engagements where precision, documentation, and repeatability are critical.
Network Reconnaissance and Information Gathering Techniques
Network reconnaissance is one of the most important stages in offensive security operations because it provides the foundation for all subsequent actions. During this phase, candidates gather detailed information about target systems, including IP ranges, active hosts, open ports, and running services. This information helps build a map of the network architecture, which is essential for identifying potential attack vectors. Information gathering can be passive, where data is collected without direct interaction with the target, or active, where systems are directly probed for responses. Each approach has advantages depending on the scenario. Effective reconnaissance requires analytical thinking and attention to detail, as even small pieces of information can reveal significant vulnerabilities when properly interpreted within the larger system context.
Vulnerability Identification and Exploitation Strategy
Once reconnaissance is complete, the next stage involves identifying vulnerabilities within the target environment. This process requires analyzing system configurations, software versions, and service behaviors to detect weaknesses that can be exploited. Vulnerabilities may include outdated software, misconfigured services, weak authentication mechanisms, or insecure network protocols. After identifying potential entry points, candidates must develop exploitation strategies that allow controlled access to systems. This may involve leveraging known vulnerabilities or adapting existing exploit techniques to fit specific environments. The goal is not only to gain access but also to understand how vulnerabilities interact within the system. This stage requires a combination of technical knowledge, logical reasoning, and creativity, as each environment presents unique challenges.
Privilege Escalation and System Control Techniques
Privilege escalation is a critical phase in offensive security operations where attackers attempt to increase their level of access within a compromised system. After gaining initial access, candidates analyze system configurations, running processes, and permission structures to identify opportunities for escalation. This may involve exploiting misconfigured services, leveraging kernel vulnerabilities, or abusing weak file permissions. Successful privilege escalation allows deeper control over the system, enabling further exploration and lateral movement within the network. This phase requires detailed understanding of operating system internals, user management systems, and security boundaries. It is often one of the most challenging aspects of penetration testing because it requires precise execution and deep technical insight.
Web Application Security and Common Attack Vectors
Web application security is a major focus area in offensive security certifications because web-based systems are among the most frequently targeted components in modern infrastructure. Candidates must analyze application behavior to identify vulnerabilities such as injection flaws, broken authentication mechanisms, and insecure data handling practices. SQL injection remains one of the most common vulnerabilities, allowing attackers to manipulate backend databases. Cross-site scripting enables malicious code execution within user browsers, while insecure direct object references allow unauthorized access to sensitive data. Understanding these attack vectors requires knowledge of how web applications process input, manage sessions, and interact with databases. Effective testing involves both manual analysis and automated techniques to identify weaknesses across multiple layers of the application.
Wireless Network Security Assessment Techniques
Wireless security assessment is another important domain within offensive security certification programs. This area focuses on evaluating the security of wireless communication protocols and identifying weaknesses in encryption and authentication mechanisms. Candidates analyze wireless traffic to detect vulnerabilities in protocols such as WEP, WPA, and WPA2. Attack techniques may include packet capture, handshake analysis, and brute-force attacks against weak encryption keys. Wireless environments are particularly challenging because they involve both physical and logical security considerations. Attackers must be within range of the network, but once access is obtained, they can potentially compromise connected systems. Understanding wireless security requires knowledge of radio communication principles, encryption algorithms, and network authentication processes.
Scripting and Automation in Security Operations
Scripting plays a crucial role in offensive security workflows because it enables automation of repetitive tasks and customization of attack strategies. Candidates often use scripting languages to automate scanning processes, modify exploit code, or analyze large sets of data. Automation improves efficiency by reducing manual workload and allowing faster identification of vulnerabilities. In complex environments, scripting is essential for managing multiple systems simultaneously and executing coordinated attacks. It also allows customization of tools to fit specific scenarios, which is often necessary when dealing with unique system configurations. Proficiency in scripting enhances overall effectiveness and is considered a key skill in advanced cybersecurity roles.
Memory Exploitation and Binary Analysis Concepts
Advanced offensive security certifications often include topics related to memory exploitation and binary analysis. These concepts involve understanding how programs execute at the memory level and how vulnerabilities can be exploited through buffer overflows, heap manipulation, and stack corruption. Candidates analyze binary files to identify insecure functions or flawed memory management practices. Exploitation at this level requires deep understanding of system architecture, processor behavior, and memory allocation patterns. Techniques such as return-oriented programming and shellcode injection may be used to achieve code execution. This area of study is highly technical and requires strong analytical skills, as small errors in memory handling can lead to system compromise.
Lateral Movement and Network Traversal Strategies
Lateral movement refers to the process of expanding access within a network after initial system compromise. Once a foothold is established, candidates analyze connected systems to identify additional targets. This involves mapping internal networks, identifying trust relationships, and exploiting weak authentication mechanisms between systems. Lateral movement allows attackers to escalate impact by accessing multiple systems rather than a single entry point. Effective traversal requires understanding network segmentation, domain structures, and access control policies. This phase demonstrates how vulnerabilities in one system can lead to broader compromise across an entire infrastructure if proper segmentation is not enforced.
Reporting and Documentation in Security Assessments
Documentation is a critical component of offensive security practice, as it ensures that findings are clearly communicated and actionable. During assessments, candidates are expected to record vulnerabilities, exploitation methods, and system behavior in a structured format. This includes detailing the steps taken to compromise systems, evidence of successful exploitation, and recommendations for remediation. Clear documentation is essential for translating technical findings into meaningful security improvements. In professional environments, these reports are used by organizations to strengthen defenses and prioritize risk mitigation efforts. Strong reporting skills are therefore as important as technical execution in cybersecurity roles.
Time Management and Strategic Planning in Exams
Time management is a crucial factor in offensive security certification exams due to their extended and complex nature. Candidates must allocate time effectively across reconnaissance, exploitation, and documentation phases. Poor time management can result in incomplete objectives, even if technical skills are strong. Strategic planning involves prioritizing targets based on difficulty, potential impact, and available information. Candidates often need to decide whether to focus on easier systems first to gain initial access or attempt more complex targets that may yield higher rewards. Effective planning ensures steady progress throughout the exam duration and reduces the risk of running out of time before completing objectives.
Real-World Application of Offensive Security Skills
The skills developed through offensive security certification training have direct applications in real-world cybersecurity environments. Professionals use these techniques to identify vulnerabilities in enterprise systems, simulate attack scenarios, and assess overall security posture. Organizations rely on these assessments to improve defenses and reduce risk exposure. Offensive security practices also support incident response efforts by helping teams understand how attackers operate. This knowledge is valuable for designing stronger security architectures and implementing effective defensive strategies. The practical nature of these skills ensures that certified professionals can contribute meaningfully to cybersecurity operations across various industries.
Career Impact of Advanced Security Certifications
Advanced offensive security certifications have a significant impact on cybersecurity career development. They demonstrate a high level of technical proficiency and practical experience, which is highly valued by employers. Professionals with these certifications are often considered for roles involving penetration testing, red teaming, and security consulting. These roles require the ability to simulate real attacks, identify vulnerabilities, and provide actionable security recommendations. The certification pathway also supports long-term career growth by building a strong foundation in both technical and analytical skills. As cybersecurity threats continue to evolve, professionals with validated hands-on expertise remain in high demand across global industries.
Advanced Exploitation Techniques in Offensive Security Environments
Advanced exploitation techniques form a critical part of offensive security certification training because they focus on the deeper mechanics of system compromise beyond basic vulnerability usage. At this level, candidates are expected to understand how software behaves at runtime, how memory is allocated, and how system processes interact under different conditions. Exploitation may involve manipulating memory structures, bypassing security protections, or chaining multiple vulnerabilities together to achieve system control. These techniques require a detailed understanding of both operating system behavior and application-level logic. In many cases, candidates must adapt existing exploit methods to suit unique environments, which demands strong analytical reasoning and technical creativity. The goal is not only to gain access but to demonstrate the ability to reliably reproduce controlled exploitation in complex and dynamic systems.
Windows and Linux Security Model Differences in Exploitation
Understanding the differences between Windows and Linux security models is essential for effective offensive security practice. Each operating system enforces permissions, memory management, and process isolation in distinct ways, which directly impacts exploitation strategies. Linux systems typically rely on user-based permission structures and command-line interaction, making them more transparent for reconnaissance and scripting. Windows environments, on the other hand, involve complex permission hierarchies, registry structures, and service-based execution models. Exploitation techniques must be adapted accordingly, as privilege escalation paths differ significantly between these systems. Candidates must understand how authentication, access control, and system services function in both environments to identify vulnerabilities effectively and execute successful attacks.
Binary Exploitation and Low-Level System Analysis
Binary exploitation is one of the most technically demanding areas within offensive security certification training. It involves analyzing compiled programs to identify vulnerabilities that exist at the machine level. These vulnerabilities often arise from improper memory handling, such as buffer overflows, use-after-free conditions, or stack corruption. Candidates must understand how instructions are executed at the processor level and how memory addresses are managed during program execution. Exploiting binaries requires precise control over memory layouts and execution flow, often involving techniques that manipulate return addresses or inject custom code into memory. This level of analysis demands strong knowledge of computer architecture and system internals, as well as the ability to interpret disassembled code effectively.
Buffer Overflow Exploitation and Memory Corruption Concepts
Buffer overflow exploitation is a foundational concept in advanced cybersecurity training. It occurs when a program writes more data to a memory buffer than it can safely hold, causing adjacent memory regions to be overwritten. Attackers can exploit this behavior to manipulate program execution and gain unauthorized control over system functions. Understanding buffer overflows requires knowledge of stack and heap memory structures, as well as how function calls are managed during execution. Candidates must also understand how modern operating systems implement protections such as stack canaries and address space layout randomization. Exploiting these vulnerabilities often requires bypassing multiple security mechanisms, making it a highly technical and precision-driven process.
Privilege Escalation in Modern Operating Systems
Privilege escalation remains one of the most important objectives in offensive security operations. After gaining initial access to a system, attackers attempt to increase their level of control to administrative or root privileges. This process involves identifying misconfigurations, insecure file permissions, or vulnerable services that allow elevation of privileges. In some cases, kernel-level vulnerabilities may be exploited to bypass system restrictions entirely. Candidates must carefully analyze system logs, running processes, and configuration files to identify potential escalation paths. Successful privilege escalation provides full control over the system, enabling further exploitation, data extraction, or lateral movement across connected networks.
Persistence Mechanisms in Compromised Systems
Persistence refers to techniques used to maintain access to a compromised system over time. In offensive security training, understanding persistence is important for simulating real-world attacker behavior. Attackers often implement mechanisms that allow them to retain access even after system reboots or credential changes. This may involve modifying startup scripts, creating hidden user accounts, or leveraging scheduled tasks. Persistence techniques require deep understanding of operating system behavior and service management. In controlled environments, candidates study these mechanisms to understand how attackers maintain long-term access and how defenders can detect and remove unauthorized persistence mechanisms effectively.
Lateral Movement Across Enterprise Networks
Lateral movement is the process of expanding access from one compromised system to others within a network. Once an initial system is compromised, attackers analyze network connections, shared resources, and trust relationships to identify additional targets. This process often involves credential harvesting, pass-the-hash techniques, or exploitation of weak internal services. Lateral movement is a key component of advanced penetration testing because it demonstrates how a single vulnerability can escalate into a full network compromise. Candidates must understand domain structures, authentication protocols, and internal network segmentation to execute lateral movement effectively and responsibly within controlled environments.
Active Directory Security and Domain Exploitation
Active Directory environments are common in enterprise networks and represent a significant focus area in offensive security training. These systems manage authentication, authorization, and policy enforcement across multiple machines. Exploiting Active Directory involves identifying misconfigurations, weak permissions, or vulnerable service accounts that can be leveraged for privilege escalation. Candidates must understand how domain controllers function, how group policies are applied, and how trust relationships are established between systems. Exploiting these environments often requires chaining multiple vulnerabilities together to gain domain-wide access. This area of study is highly relevant because Active Directory remains a central component of enterprise security infrastructure.
Web Application Exploitation at Advanced Levels
Advanced web application exploitation goes beyond basic injection attacks and focuses on complex logic flaws, insecure API implementations, and session management weaknesses. Candidates analyze application workflows to identify conditions where security controls can be bypassed. This may involve manipulating request parameters, exploiting race conditions, or bypassing authorization mechanisms. Unlike basic web vulnerabilities, advanced exploitation requires deep understanding of application architecture and business logic. Candidates must also be able to interpret server responses and identify hidden functionality that may not be visible through standard user interfaces. This level of analysis is essential for identifying high-impact vulnerabilities in modern web applications.
API Security and Modern Application Attack Surfaces
Modern applications rely heavily on APIs for communication between services, making API security an important area of focus in offensive security training. APIs often expose sensitive functionality that can be exploited if not properly secured. Candidates analyze API endpoints to identify weak authentication mechanisms, improper input validation, and excessive data exposure. Exploitation may involve manipulating API requests, bypassing authorization checks, or exploiting insecure data handling practices. Understanding API security requires knowledge of RESTful architecture, token-based authentication, and data serialization formats. As modern systems become increasingly API-driven, this area continues to grow in importance within cybersecurity assessments.
Wireless Network Exploitation and Advanced Attack Methods
Wireless network exploitation involves identifying weaknesses in wireless communication protocols and authentication systems. At an advanced level, candidates analyze handshake processes, encryption algorithms, and access control mechanisms to identify vulnerabilities. Attack methods may include capturing authentication handshakes and attempting offline key recovery or exploiting weak configuration settings in wireless access points. Wireless environments also introduce physical proximity considerations, as attackers must be within range of target networks. Understanding these systems requires knowledge of radio communication, encryption standards, and network authentication workflows. This area remains relevant in both enterprise and personal security contexts.
Post-Exploitation Activities and System Control
Post-exploitation refers to the activities performed after gaining access to a target system. These activities include gathering sensitive data, identifying additional attack paths, and maintaining control over compromised environments. Candidates analyze file systems, network configurations, and running processes to extract valuable information. Post-exploitation also involves understanding how to move through systems without detection in real-world scenarios. While certification environments are controlled, these concepts are important for understanding how attackers operate after initial compromise. This stage demonstrates the full lifecycle of an attack, from entry to sustained system control.
Security Evasion Techniques and Defensive Countermeasures
Security evasion techniques involve bypassing defensive mechanisms such as antivirus software, intrusion detection systems, and endpoint protection tools. Candidates study how security solutions detect malicious behavior and how attackers attempt to avoid detection. This may involve obfuscating payloads, modifying exploit code, or using legitimate system tools to carry out malicious actions. Understanding defensive countermeasures is equally important, as it helps candidates identify how systems detect anomalies. This dual perspective strengthens overall cybersecurity knowledge by combining offensive and defensive understanding into a unified analytical approach.
Forensic Awareness and Operational Stealth Concepts
Forensic awareness refers to understanding how digital evidence is created, stored, and analyzed within systems. In offensive security training, candidates learn how system logs, file timestamps, and network activity can reveal attacker behavior. While certification environments are controlled, this knowledge helps professionals understand how real-world attacks are investigated. Operational stealth involves minimizing detectable activity during system interaction. This includes reducing system noise, avoiding unnecessary changes, and maintaining low-profile access patterns. These concepts are important for understanding the full impact of security operations in real environments.
Automation of Complex Attack Chains
Automation plays an increasingly important role in advanced offensive security operations. Candidates often develop scripts to automate multi-step attack processes, such as scanning, exploitation, and data extraction. Automation reduces manual effort and increases efficiency, especially in large-scale environments with multiple targets. It also allows repeatability, ensuring that attack methods can be consistently applied across similar systems. Understanding how to build automated workflows requires programming knowledge and logical structuring of attack sequences. This skill is particularly valuable in professional penetration testing environments where time and accuracy are critical.
Real-World Cybersecurity Application of Advanced Skills
The advanced skills developed through offensive security certification training are directly applicable to real-world cybersecurity operations. Professionals use these techniques to simulate attacks, identify vulnerabilities, and assess organizational security posture. These activities help organizations strengthen defenses and reduce exposure to cyber threats. In addition, understanding attacker methodologies allows security teams to build more resilient systems and improve incident response strategies. The practical nature of these skills ensures that certified professionals can contribute effectively to security operations in enterprise environments.
Strategic Importance of Offensive Security Expertise in Modern IT
Offensive security expertise plays a strategic role in modern IT infrastructure protection. Organizations rely on professionals who can think like attackers to identify weaknesses before they are exploited. This proactive approach helps reduce the risk of data breaches, service disruptions, and financial losses. As cyber threats continue to evolve, the demand for skilled offensive security professionals continues to increase across industries. These certifications provide a structured pathway for developing the technical, analytical, and strategic skills required to operate effectively in high-risk digital environments.
Conclusion
Offensive security certification represents one of the most rigorous and practical validation frameworks in the cybersecurity field. Unlike traditional certification models that emphasize theoretical knowledge or structured exam-based recall, this approach focuses on real-world performance in controlled but highly realistic environments. The primary value of this certification lies in its ability to measure applied technical capability—how effectively a professional can analyze systems, identify vulnerabilities, and execute exploitation techniques under pressure. In modern cybersecurity landscapes where threats are dynamic and continuously evolving, this form of validation is increasingly aligned with industry expectations.
A key strength of this certification approach is its shift away from memorization-based learning toward hands-on execution. Cybersecurity as a discipline cannot be fully mastered through theory alone, because real systems behave unpredictably and attackers rarely follow structured patterns. By placing candidates in simulated environments that mirror enterprise infrastructure, the certification forces them to engage with systems directly. This includes reconnaissance, enumeration, vulnerability discovery, exploitation, and post-exploitation analysis. Each stage requires logical thinking and technical precision, ensuring that candidates develop operational competence rather than surface-level familiarity.
Another defining characteristic is the emphasis on endurance and sustained cognitive performance. Unlike standard examinations that last a few hours, offensive security assessments can extend over one to three days depending on the certification level. This extended duration is intentional, as it reflects the reality of real-world cyber operations where attackers and defenders often work over long periods without interruption. During these exams, candidates must maintain focus while dealing with fatigue, shifting problem complexity, and evolving system behavior. This combination of technical challenge and psychological pressure ensures that only individuals capable of consistent performance under stress are successful.
The certification also plays a significant role in developing an attacker-oriented mindset, which is essential for modern cybersecurity professionals. Instead of viewing systems purely from a defensive standpoint, candidates are trained to think in terms of exploitation paths, system weaknesses, and potential attack vectors. This perspective allows them to understand how malicious actors operate, which in turn strengthens defensive strategies. Organizations benefit from professionals who can anticipate threats rather than simply respond to them after incidents occur. This proactive mindset is one of the most valuable outcomes of offensive security training.
From a technical perspective, the certification covers a wide range of domains that reflect the complexity of real-world systems. Candidates are required to demonstrate proficiency in network analysis, service enumeration, vulnerability assessment, web application security, and system exploitation. These areas are interconnected, meaning that weaknesses in one layer can often be leveraged to compromise another. For example, a vulnerability in a web application might provide access to internal systems, which can then be escalated through misconfigurations or weak permissions. This interconnected nature of modern infrastructure makes holistic understanding essential.
Operating systems and infrastructure knowledge also play a critical role. Candidates must understand how Linux and Windows systems function at both user and kernel levels. This includes file systems, process management, memory allocation, and permission structures. Each operating system presents different security challenges and requires distinct exploitation approaches. Linux environments often emphasize command-line operations and scripting, while Windows systems introduce complexities such as registry manipulation, Active Directory structures, and service-based architecture. Mastery of both environments is essential for effective security analysis.
Another important dimension is web application and API security. Modern systems rely heavily on web-based interfaces and interconnected services, making them prime targets for attackers. Candidates must understand how applications process input, manage authentication, and handle data flow. Vulnerabilities such as injection flaws, broken access control, and insecure APIs are common areas of focus. As applications become more complex and distributed, attackers increasingly exploit logic flaws rather than simple technical errors, requiring deeper analytical thinking from security professionals.
Wireless security and network exploitation further expand the scope of assessment. Wireless networks introduce unique challenges due to their broadcast nature and reliance on encryption protocols. Candidates must understand how wireless authentication works, how handshake processes can be analyzed, and how encryption weaknesses can be exploited. These skills are particularly relevant in environments where wireless infrastructure is integrated into broader enterprise networks, creating additional attack surfaces.
A critical component of the certification process is the use of isolated, controlled lab environments. These environments simulate real enterprise systems with multiple interconnected machines, each configured with specific vulnerabilities. Candidates must navigate these systems strategically, identifying entry points and progressing through layered security structures. Unlike static testing environments, these labs respond dynamically to user actions, requiring adaptive thinking and continuous reassessment of strategy. This closely mirrors real penetration testing engagements where no two environments behave identically.
Foundational knowledge is another essential requirement for success. Strong understanding of networking principles, particularly TCP/IP communication, is necessary for analyzing data flow and identifying weak points. Linux proficiency is critical due to the extensive use of command-line tools and scripting. Basic programming knowledge enhances the ability to modify exploits or automate repetitive tasks. Additionally, understanding system architecture, including memory management and process execution, is vital for advanced exploitation scenarios. These foundational skills collectively support deeper technical analysis.
Advanced topics such as binary exploitation and system-level analysis further distinguish this certification from more general cybersecurity training. Candidates are expected to understand how software executes at the memory level and how vulnerabilities arise from improper handling of system resources. Exploitation at this level requires precision and deep technical understanding, often involving manipulation of memory structures or execution flow. These concepts are highly technical but essential for professionals working in advanced security roles.
Beyond technical execution, analytical reasoning plays a central role throughout the certification process. Candidates must interpret system behavior, identify patterns, and determine the most efficient paths for exploitation. This involves breaking down complex systems into smaller components and understanding how each part interacts with others. Strong analytical skills allow professionals to prioritize tasks effectively and adapt strategies based on changing conditions within the environment. This ability to think critically under pressure is one of the most valuable outcomes of the certification process.
In professional contexts, the skills developed through offensive security certification have direct and measurable impact. Organizations rely on professionals trained in these methodologies to identify vulnerabilities, simulate attack scenarios, and strengthen overall security posture. These individuals are often involved in penetration testing, red team operations, and security assessments that inform strategic defense decisions. Their ability to think like attackers provides a significant advantage in identifying risks that might otherwise go unnoticed.
Overall, offensive security certification represents a comprehensive approach to cybersecurity education and validation. It integrates technical knowledge, practical execution, analytical reasoning, and psychological resilience into a single framework. The result is a certification path that not only measures capability but actively develops it through immersive experience. As cybersecurity threats continue to evolve in complexity and scale, the demand for professionals with validated hands-on expertise continues to grow, making this certification increasingly relevant in modern digital environments.