The cybersecurity landscape has undergone a major transformation as organizations have shifted away from traditional on-premises infrastructure toward cloud-first and hybrid environments. This shift has fundamentally changed how security teams approach protection, monitoring, and response. Instead of securing a fixed perimeter, modern enterprises must now defend distributed ecosystems that include remote endpoints, cloud workloads, mobile devices, SaaS applications, and identity systems that operate across multiple environments.
In earlier security models, organizations relied heavily on firewalls and network-based defenses that assumed most resources existed inside a controlled internal network. However, the rise of remote work, cloud computing, and mobile access has dissolved this perimeter. Employees now connect from multiple locations using different devices, and applications are often hosted in dynamic cloud environments that scale up and down based on demand.
This distributed structure introduces new challenges, particularly in visibility and threat detection. Attackers no longer need to breach a centralized network boundary; instead, they exploit weaknesses in endpoints, stolen credentials, misconfigured cloud services, and identity systems. As a result, endpoint detection and response platforms have become central to modern cybersecurity strategies.
These platforms are designed to continuously monitor endpoints, analyze behavioral patterns, and detect suspicious activity in real time. They also integrate threat intelligence, automation, and machine learning to improve detection accuracy and reduce response time. Among the leading solutions in this space, CrowdStrike has established itself as a major cloud-native security platform designed to operate at scale across complex environments.
CrowdStrike Cloud-Native Security Model and Design Philosophy
CrowdStrike is built on a fundamentally cloud-native architecture that emphasizes scalability, speed, and centralized intelligence. Unlike legacy security tools that rely on on-premises servers and heavy infrastructure, CrowdStrike uses a lightweight agent deployed on endpoints that communicates continuously with a cloud-based platform.
This design eliminates the need for extensive local infrastructure and allows security updates, detection rules, and threat intelligence to be delivered instantly. The cloud-based model ensures that all endpoints are protected with the latest security insights without requiring manual updates or downtime.
The architecture is designed to process massive volumes of endpoint telemetry in real time. Every action performed on an endpoint, such as file execution, process creation, network connection, or registry modification, is collected and analyzed. This data is streamed to the cloud, where advanced analytics engines evaluate behavior patterns and identify anomalies that may indicate malicious activity.
One of the core strengths of this model is scalability. Whether an organization has hundreds or hundreds of thousands of endpoints, the system can handle the data flow without requiring significant changes in infrastructure. This makes it particularly suitable for large enterprises with globally distributed environments.
Endpoint Telemetry and Behavioral Analysis Engine
At the heart of CrowdStrike’s detection capability is its behavioral analysis engine. Instead of relying solely on signature-based detection, which identifies known malware patterns, the platform uses behavioral indicators to detect unknown and emerging threats.
This approach is essential in modern cybersecurity because attackers frequently use fileless malware, zero-day exploits, and living-off-the-land techniques that do not leave traditional signatures. By analyzing behavior rather than static indicators, the system can identify suspicious activity even when the specific malware has never been seen before.
The endpoint agent continuously collects telemetry data and sends it to the cloud for processing. Machine learning models then analyze this data to establish a baseline of normal behavior for each endpoint and user. Any deviation from this baseline is flagged for further investigation.
For example, if a user account that typically accesses files during business hours suddenly begins executing administrative commands at unusual times, the system can detect this anomaly. Similarly, if a process attempts to access sensitive system areas or communicate with unknown external servers, it may be flagged as potentially malicious.
This behavioral approach significantly improves detection accuracy and reduces false positives compared to traditional security tools.
Unified Agent Architecture and Endpoint Efficiency
CrowdStrike’s platform relies on a single-agent architecture that consolidates multiple security functions into one lightweight component. This agent is installed on endpoints and is responsible for collecting telemetry, enforcing policies, and communicating with the cloud platform.
By using a unified agent, the platform reduces system overhead and avoids conflicts that can arise when multiple security tools are installed on the same device. This simplifies deployment and maintenance while improving performance on endpoint devices.
The agent is designed to operate with minimal impact on system resources. It runs silently in the background, continuously monitoring system activity without interfering with user operations. Updates to detection logic and security policies are delivered automatically through the cloud, ensuring that endpoints remain protected against the latest threats.
This architecture also simplifies scaling across large environments. Organizations can deploy the agent across thousands of endpoints without needing to configure complex local infrastructure or manage multiple security tools.
Cloud Security Visibility and Workload Protection
As organizations move more workloads into cloud environments, visibility into cloud infrastructure becomes a critical requirement. CrowdStrike addresses this through its cloud security capabilities, which extend protection beyond traditional endpoints to include cloud workloads, containers, and virtual machines.
The system can operate in both agent-based and agentless modes, depending on the environment. In agent-based deployments, the same endpoint agent is used to secure cloud workloads. In agentless configurations, the platform integrates directly with cloud service APIs to collect security data without requiring installation on individual workloads.
This flexibility allows organizations to secure diverse environments without redesigning their infrastructure. It also enables continuous monitoring of cloud assets, ensuring that misconfigurations, exposed services, and unauthorized access attempts are detected early.
A key component of cloud security is asset discovery. In dynamic cloud environments, resources are frequently created and destroyed, making it difficult to maintain an accurate inventory. The platform continuously scans cloud accounts to identify active resources and assess their security posture.
Once assets are identified, they are evaluated for risks such as overly permissive access policies, exposed storage buckets, or unpatched software. These findings are prioritized based on severity, allowing security teams to focus on the most critical issues first.
Identity Protection and Credential Security Layer
Identity has become one of the most targeted attack surfaces in modern cybersecurity. Attackers often focus on compromising user credentials, service accounts, and directory services to gain access to systems without triggering traditional security alerts.
CrowdStrike addresses this challenge through its identity protection capabilities, which monitor authentication events and user behavior across the enterprise environment. The system analyzes login attempts, privilege changes, and access patterns to detect anomalies that may indicate compromised accounts.
For example, if a user account suddenly attempts to access systems outside its normal scope or from unusual geographic locations, the system can flag this behavior as suspicious. It also correlates identity activity with endpoint behavior to identify multi-stage attacks where credentials are used to move laterally across systems.
This integration between identity and endpoint telemetry provides a more comprehensive view of potential threats and helps security teams identify attack chains more effectively.
Threat Intelligence and Adversary Tracking System
CrowdStrike incorporates a global threat intelligence framework that continuously monitors cyber threat activity across industries and regions. This intelligence is gathered from multiple sources, including incident investigations, research teams, and real-time telemetry data.
The system analyzes attacker behavior, tools, and techniques to build profiles of known adversaries. These profiles help predict future attack patterns and improve detection capabilities across the platform.
When new threats are identified, intelligence updates are distributed through the cloud, enhancing the platform’s ability to detect similar activity across all protected environments. This proactive approach allows organizations to defend against emerging threats before they become widespread.
Threat intelligence also plays a role in incident response. When an attack is detected, the system can provide context about the likely attacker, their methods, and potential objectives. This helps security teams prioritize response actions and mitigate damage more effectively.
Next-Generation SIEM and Security Data Integration
The platform extends its capabilities into security information and event management by aggregating data from endpoints, cloud workloads, identity systems, and third-party tools. This centralized data model allows for comprehensive analysis of security events across the entire environment.
Advanced correlation engines analyze event data to identify relationships between seemingly unrelated activities. For example, a failed login attempt followed by unusual process execution on an endpoint may indicate a coordinated attack.
Once threats are identified, the system can automate investigation workflows. It maps affected assets, traces attack paths, and identifies compromised systems. This reduces the time required for manual analysis and accelerates incident response.
Automated response capabilities allow the system to take immediate action against threats. This may include isolating endpoints, terminating malicious processes, or disabling compromised accounts. These actions help contain threats before they spread further.
Operational Strengths and Deployment Efficiency
One of the primary advantages of CrowdStrike’s architecture is operational simplicity. The single-agent model reduces complexity at the endpoint level and simplifies deployment across large environments. Organizations benefit from centralized management, consistent policy enforcement, and reduced administrative overhead.
The cloud-native design also ensures rapid scalability. New endpoints can be added quickly without requiring extensive configuration or infrastructure changes. This is particularly valuable for organizations with rapidly changing environments or global operations.
Automation is another key strength. Many security processes, including detection, analysis, and response, are automated through machine learning and predefined workflows. This reduces the workload on security teams and improves response times.
Architectural Limitations and Considerations
Despite its advantages, the cloud-dependent nature of the platform introduces certain considerations. Organizations operating in highly restricted environments or those with limited internet connectivity may face challenges in deployment and performance.
Cost can also be a factor for large-scale implementations, particularly for enterprises with extensive endpoint coverage. Additionally, reliance on cloud infrastructure means that service disruptions, although rare, can temporarily impact visibility and response capabilities.
Organizations must also consider integration requirements when operating hybrid environments that include legacy systems or on-premises infrastructure. While the platform supports diverse environments, some configurations may require additional planning and customization.
The Shift Toward Autonomous Cybersecurity Platforms
As cyber threats become more automated, adaptive, and distributed, security platforms are also evolving toward greater autonomy. Modern attackers increasingly use machine-driven techniques such as polymorphic malware, credential stuffing, and automated reconnaissance to bypass traditional defenses. In response, cybersecurity platforms are shifting toward AI-driven systems capable of detecting and responding to threats in real time without heavy human intervention.
SentinelOne represents this evolution through its autonomous endpoint protection model. Instead of relying primarily on cloud-only processing or manual investigation workflows, SentinelOne emphasizes onboard intelligence at the endpoint level. This means that endpoints themselves play a more active role in detecting, analyzing, and responding to threats.
This architectural philosophy differs from many traditional cloud-first security platforms because it reduces dependency on constant cloud communication for core detection functions. While cloud intelligence is still important, the system is designed to continue functioning even in disconnected or degraded environments. This makes it particularly relevant for hybrid infrastructures, industrial systems, and organizations with strict operational continuity requirements.
SentinelOne Singularity Platform Architecture
The core of SentinelOne’s ecosystem is the Singularity platform, a unified security architecture that integrates endpoint protection, cloud security, identity protection, SIEM capabilities, and threat intelligence into a single framework.
Unlike fragmented security toolsets that require multiple agents and consoles, the Singularity platform is built around consolidation. It uses a single-agent model similar in concept to other modern platforms, but with a stronger emphasis on local decision-making and autonomous response.
The architecture is designed to operate across diverse environments, including Windows, Linux, macOS, cloud workloads, and containerized applications. This cross-platform compatibility allows organizations to maintain consistent security policies regardless of infrastructure type.
A key aspect of the Singularity architecture is its ability to function in both connected and disconnected states. Even if cloud connectivity is lost, endpoints can continue to detect threats, enforce policies, and respond to attacks using onboard intelligence.
AI-Driven Detection and Behavioral Intelligence Engine
At the core of SentinelOne’s detection capability is its behavioral AI engine. Instead of relying solely on signatures or cloud-based analytics, the system uses local machine learning models embedded within the endpoint agent.
These models continuously analyze system activity, including process behavior, file execution patterns, memory usage, registry modifications, and network communications. By establishing a behavioral baseline, the system can detect deviations that indicate malicious activity.
This approach is particularly effective against fileless malware and advanced persistent threats that avoid traditional detection methods. Because the analysis occurs directly on the endpoint, detection can happen in real time without waiting for cloud round-trips.
The behavioral engine also supports rollback capabilities in certain environments. If malicious activity is detected, the system can reverse unauthorized changes, restoring affected systems to a pre-attack state. This feature is especially valuable in ransomware scenarios where rapid containment and recovery are critical.
Autonomous Response and Real-Time Mitigation
One of the defining characteristics of SentinelOne’s architecture is its focus on autonomous response. Once a threat is detected, the system can take immediate action without requiring manual approval or external orchestration.
These actions may include killing malicious processes, isolating affected endpoints, blocking network communication, or removing persistence mechanisms. Because these responses occur at the endpoint level, they can be executed even when the device is offline or disconnected from the central platform.
This autonomy significantly reduces response time during active attacks. Instead of waiting for security analysts to investigate alerts, the system can automatically neutralize threats as they occur.
In high-risk environments, this capability can be critical for maintaining operational continuity. For example, in industries such as healthcare, manufacturing, or financial services, rapid containment of threats can prevent widespread disruption.
Cloud Security and Workload Protection Model
SentinelOne extends its protection beyond endpoints into cloud environments through its Singularity Cloud Security module. This component is designed to secure workloads running in public cloud platforms, virtual machines, and containerized environments.
Unlike traditional cloud security tools that rely heavily on external scanning or periodic assessments, SentinelOne integrates runtime protection directly into cloud workloads. This allows continuous monitoring of system behavior within cloud environments.
The platform can detect misconfigurations, unauthorized access attempts, and anomalous behavior in real time. It also provides visibility into cloud assets, helping organizations maintain accurate inventories of resources across multiple cloud providers.
A key strength of this model is its ability to unify cloud and endpoint security under a single operational framework. This reduces fragmentation and ensures consistent policy enforcement across environments.
Identity Security and Attack Surface Protection
Identity systems represent one of the most targeted components in modern cyberattacks. Attackers frequently exploit weak credentials, misconfigured access controls, and compromised authentication systems to gain unauthorized access.
SentinelOne addresses this risk through its identity protection capabilities integrated within the Singularity platform. The system monitors authentication events, user behavior, and privilege changes across enterprise environments.
By analyzing identity activity in real time, the platform can detect anomalies such as unusual login locations, abnormal access patterns, or attempts to escalate privileges. These indicators may suggest compromised credentials or insider threats.
The integration of identity security with endpoint and cloud telemetry allows the platform to correlate activities across multiple domains. This provides a more complete understanding of attack chains and helps security teams identify root causes more effectively.
AI SIEM and Data Lake Architecture
SentinelOne’s security information and event management capabilities are built on a modern data lake architecture known as Singularity Data Lake. This system aggregates security data from endpoints, cloud workloads, identity systems, and third-party sources.
Unlike traditional SIEM systems that rely on rigid schemas and manual configuration, this architecture is designed for flexibility and scalability. It allows organizations to ingest large volumes of structured and unstructured security data without performance degradation.
The AI SIEM layer applies machine learning and behavioral analytics to detect patterns across the data lake. It identifies correlations between events that may indicate coordinated attacks or multi-stage intrusion attempts.
For example, multiple failed login attempts combined with unusual process execution on a cloud workload may be linked into a single attack narrative. This helps security teams understand the broader context of incidents rather than analyzing isolated alerts.
Automation is also integrated into the SIEM layer. Once threats are identified, the system can trigger workflows for investigation, containment, or remediation. This reduces manual effort and improves incident response efficiency.
Threat Intelligence Integration and Adversary Insights
SentinelOne integrates advanced threat intelligence capabilities into its platform through partnerships and internal research. One of the key components of this intelligence layer is adversary tracking, which analyzes attacker behavior, tools, and techniques.
This intelligence is continuously updated based on global threat activity and incident data. It helps the platform recognize emerging attack patterns and adjust detection models accordingly.
By understanding how attackers operate, the system can anticipate future threats and improve its detection accuracy. This proactive approach reduces reliance on reactive signature updates and enhances resilience against zero-day attacks.
Threat intelligence also supports incident investigation by providing contextual information about detected threats. Security teams can understand the likely origin, intent, and methods of attackers, which helps prioritize response actions.
Singularity Marketplace and Ecosystem Extensibility
One of SentinelOne’s distinguishing features is its extensibility through the Singularity Marketplace. This ecosystem allows organizations to integrate third-party tools, applications, and security extensions into the platform.
This modular approach enables customization based on organizational needs. For example, enterprises can add specialized analytics tools, compliance modules, or additional threat intelligence feeds.
The marketplace model supports organizations with complex or highly specialized environments. Instead of relying solely on built-in capabilities, they can extend functionality to meet specific operational requirements.
This flexibility is particularly useful for organizations that operate in regulated industries or require tailored security workflows.
Hybrid Infrastructure and Legacy System Compatibility
SentinelOne is often favored in environments that include a mix of modern cloud infrastructure and legacy on-premises systems. Its architecture is designed to support hybrid deployments without requiring complete infrastructure modernization.
The endpoint agent can operate on older systems while still providing modern behavioral detection capabilities. This allows organizations to secure legacy environments without replacing existing infrastructure.
This compatibility is important for industries where legacy systems cannot be easily upgraded or replaced, such as manufacturing, government, or healthcare sectors.
By supporting both modern and legacy environments, SentinelOne enables organizations to transition gradually toward more advanced security models without disrupting operations.
Operational Strengths of SentinelOne Architecture
SentinelOne’s primary strength lies in its autonomous detection and response capabilities. By enabling endpoints to make real-time decisions, the platform reduces dependency on cloud connectivity and human intervention.
This autonomy improves resilience in disconnected or degraded environments. It also reduces response time during active attacks, which is critical in minimizing damage.
Another strength is its flexibility across hybrid environments. The platform supports a wide range of operating systems, deployment models, and infrastructure types.
Its rollback capabilities provide additional protection against ransomware and destructive attacks, offering recovery options that go beyond simple detection and containment.
Architectural Challenges and Operational Considerations
Despite its strengths, SentinelOne’s architecture introduces a level of complexity due to its advanced configuration and customization options. Organizations may require more expertise to fully leverage their capabilities.
The extensibility of the platform, while powerful, can also increase operational overhead if not properly managed. Custom integrations and marketplace components require careful configuration and maintenance.
In some cases, organizations may need to balance automation with manual oversight to ensure that autonomous responses align with operational requirements.
Additionally, while the platform supports hybrid environments, integrating it into highly diverse infrastructures may require additional planning and tuning to achieve optimal performance.
Understanding the Core Philosophical Difference Between Both Platforms
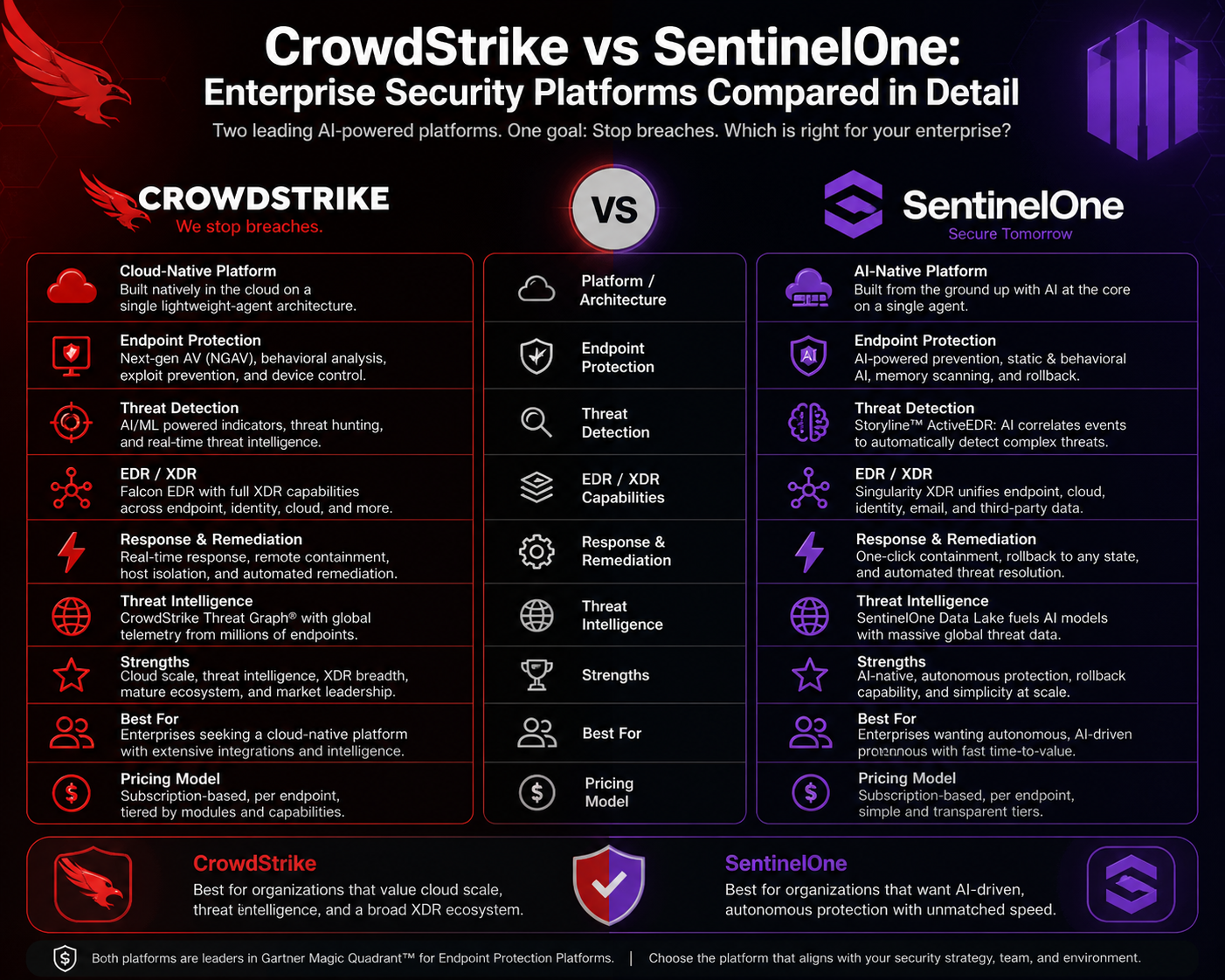
When comparing CrowdStrike and SentinelOne, the most important distinction is not just in features but in architectural philosophy. CrowdStrike is designed around a cloud-first intelligence model where most detection, correlation, and response logic is processed centrally in the cloud. SentinelOne, on the other hand, is built around endpoint autonomy, where significant detection and response capabilities are executed directly on the device itself.
This difference shapes how each platform behaves in real-world environments. CrowdStrike emphasizes centralized visibility, scalability, and cloud-native analytics. SentinelOne emphasizes resilience, offline capability, and autonomous decision-making at the endpoint.
Both approaches are valid and effective, but they serve different operational priorities. Organizations must evaluate which philosophy aligns better with their infrastructure, risk tolerance, and security maturity.
Threat Detection and Response Model Comparison
CrowdStrike’s detection model relies heavily on cloud-based analytics. Endpoint telemetry is continuously streamed to the cloud, where machine learning models analyze behavior, correlate events, and detect anomalies. This allows for large-scale pattern recognition across millions of endpoints globally.
The advantage of this model is its ability to leverage collective intelligence. If a threat is detected on one endpoint anywhere in the world, that intelligence can be rapidly distributed to all other protected systems. This creates a global threat awareness network that improves detection speed for emerging attacks.
SentinelOne, in contrast, performs a large portion of detection locally on the endpoint. Its behavioral AI engine analyzes processes, memory activity, and system behavior in real time without requiring constant cloud communication.
This local-first approach allows SentinelOne to detect and respond to threats even in offline or isolated environments. It also reduces latency in detection because decisions are made immediately on the device.
However, CrowdStrike’s centralized model provides broader visibility across environments, while SentinelOne’s model provides deeper autonomy at the endpoint level.
Endpoint Protection Capabilities and Effectiveness
Both platforms offer strong endpoint detection and response capabilities, but their implementation differs.
CrowdStrike focuses on lightweight endpoint agents that prioritize telemetry collection and cloud-based analysis. This ensures minimal performance impact on endpoints while maintaining continuous monitoring.
SentinelOne’s agent is slightly more autonomous and feature-rich at the endpoint level. It not only collects data but also performs local analysis, threat mitigation, and, in some cases, rollback operations.
In terms of malware detection, both platforms are highly effective against known and unknown threats. CrowdStrike excels in large-scale correlation and threat intelligence enrichment, while SentinelOne excels in immediate behavioral detection and autonomous mitigation.
Organizations that prioritize centralized visibility and global intelligence often prefer CrowdStrike, while those that prioritize endpoint independence and offline protection often lean toward SentinelOne.
Cloud Security Capabilities Comparison
CrowdStrike’s cloud security capabilities are deeply integrated into its ecosystem. It provides unified visibility across cloud workloads, containers, and infrastructure with a strong emphasis on asset discovery, risk prioritization, and misconfiguration detection.
Its strength lies in continuous cloud monitoring and integration with identity and endpoint data, allowing for a unified security view across environments.
SentinelOne also provides cloud security capabilities through runtime protection and workload monitoring. Its approach focuses more on securing workloads during execution rather than primarily relying on external scanning.
This makes SentinelOne particularly strong in environments where workloads are highly dynamic or distributed across multiple cloud providers.
CrowdStrike generally offers broader cloud visibility and centralized analytics, while SentinelOne offers more runtime-focused protection and flexibility in hybrid environments.
Identity Protection and Attack Surface Security
Identity security has become a critical battleground in cybersecurity. Both platforms recognize that compromised credentials are often the starting point of major breaches.
CrowdStrike integrates identity protection tightly with endpoint telemetry. This allows it to correlate identity behavior with device activity, providing a unified view of user behavior across systems.
It focuses heavily on detecting anomalies in authentication patterns, privilege escalation attempts, and lateral movement across endpoints.
SentinelOne also provides identity protection but emphasizes behavioral correlation across endpoints, cloud workloads, and identity systems through its unified Singularity platform.
Its strength lies in connecting identity events with broader system behavior in real time, enabling detection of multi-stage attacks that span across environments.
Both platforms are effective, but CrowdStrike tends to excel in large enterprise identity visibility, while SentinelOne emphasizes cross-domain correlation and autonomy.
Security Information and Event Management (SIEM) Approach
CrowdStrike’s SIEM capabilities are built around cloud-native ingestion and AI-driven correlation. It aggregates large volumes of security data and applies machine learning models to detect patterns and anomalies.
The focus is on scalability and centralized intelligence, allowing organizations to process massive datasets efficiently.
SentinelOne’s AI SIEM approach is built on its Singularity Data Lake architecture, which is designed for flexible ingestion and real-time analytics.
It emphasizes unifying security data from multiple sources and applying AI-driven correlation directly on the data lake. This allows for more flexible querying and deeper contextual analysis.
CrowdStrike’s SIEM model is often seen as more mature in large-scale enterprise environments, while SentinelOne’s model offers more flexibility and extensibility through its data lake structure.
Automation and Incident Response Capabilities
Automation is a key differentiator between the two platforms.
CrowdStrike focuses on automated detection, investigation, and response workflows that are orchestrated through its cloud platform. It reduces manual intervention by automating common response actions such as endpoint isolation, process termination, and alert triage.
SentinelOne takes automation further by embedding autonomous response directly into the endpoint. This means that certain actions can occur instantly without waiting for cloud confirmation or analyst approval.
For example, SentinelOne can automatically kill malicious processes or reverse system changes in real time during an attack.
This makes SentinelOne particularly strong in high-risk environments where immediate containment is critical.
CrowdStrike offers broader orchestration capabilities, while SentinelOne offers deeper endpoint-level autonomy.
Performance, Scalability, and Operational Efficiency
CrowdStrike is widely recognized for its scalability and lightweight agent design. It performs well in large enterprise environments with thousands or even millions of endpoints.
Its cloud-native architecture ensures that performance remains consistent regardless of deployment scale.
SentinelOne also scales effectively but places more processing responsibility on the endpoint itself. While this improves autonomy, it can introduce slightly higher resource usage depending on configuration.
In terms of operational efficiency, CrowdStrike is often easier to deploy and manage at scale due to its centralized model. SentinelOne may require more tuning and customization, but it offers greater flexibility in complex environments.
Reliability and Resilience Considerations
Reliability is a critical factor in cybersecurity platform selection.
CrowdStrike’s reliance on cloud infrastructure means that service disruptions can temporarily impact visibility or management capabilities. While such incidents are rare, they highlight dependency on centralized systems.
SentinelOne’s endpoint autonomy provides greater resilience in disconnected environments. Even if cloud connectivity is lost, endpoints can continue to detect and respond to threats independently.
This makes SentinelOne particularly suitable for environments where continuous connectivity cannot be guaranteed.
Cost Structure and Enterprise Considerations
CrowdStrike is generally positioned as a premium enterprise solution. Its pricing reflects its extensive cloud infrastructure, global intelligence network, and advanced analytics capabilities.
SentinelOne is often considered more flexible in pricing models, especially for organizations that require hybrid deployments or customized configurations.
However, the total cost of ownership depends not only on licensing but also on operational complexity, integration requirements, and staffing needs.
CrowdStrike may reduce operational overhead due to its simplicity, while SentinelOne may require more customization but offer greater long-term flexibility.
Ideal Use Cases for CrowdStrike
CrowdStrike is particularly well-suited for large enterprises with cloud-centric infrastructure, high scalability requirements, and strong reliance on centralized visibility.
It performs best in environments where endpoints are consistently connected and where organizations prioritize global threat intelligence and rapid cloud-based analytics.
Industries such as financial services, technology companies, and large multinational enterprises often benefit from its unified architecture and automation capabilities.
Ideal Use Cases for SentinelOne
SentinelOne is well-suited for organizations with hybrid infrastructure, legacy systems, or environments where endpoint autonomy is critical.
It is particularly effective in industries such as healthcare, manufacturing, and critical infrastructure where offline resilience and rapid endpoint response are essential.
Organizations that require high customization and flexible integration with third-party tools also benefit from SentinelOne’s extensible ecosystem.
Strategic Selection Considerations
Choosing between CrowdStrike and SentinelOne is not simply a matter of comparing features but aligning platform architecture with organizational priorities.
If centralized intelligence, global threat visibility, and cloud-native scalability are top priorities, CrowdStrike aligns more closely with those needs.
If endpoint autonomy, hybrid infrastructure support, and offline resilience are more important, SentinelOne may be the stronger fit.
Many organizations also consider long-term operational maturity, staffing capabilities, and integration complexity when making this decision.
Conclusion
The comparison between CrowdStrike and SentinelOne ultimately reflects a broader shift in cybersecurity itself. Security is no longer about a single layer of defense or a perimeter-based model; it is about continuous visibility, rapid detection, and adaptive response across endpoints, identities, cloud workloads, and hybrid infrastructures. Both platforms represent advanced responses to these modern challenges, but they approach the problem from different architectural and operational philosophies.
CrowdStrike is fundamentally built around a cloud-native intelligence ecosystem. Its strength lies in centralization, scalability, and global threat visibility. By aggregating endpoint telemetry from millions of devices and analyzing it in a unified cloud environment, CrowdStrike creates a powerful intelligence network that benefits from collective learning. When a new threat is detected anywhere in its ecosystem, insights can be rapidly propagated across all protected environments. This gives organizations access to a continuously improving security model that evolves with global threat activity.
This centralized model is particularly effective for large enterprises with distributed workforces and cloud-first infrastructure. Organizations operating across multiple regions, cloud providers, and high-volume endpoint environments benefit from CrowdStrike’s ability to unify visibility and simplify management. The single-agent design also reduces operational overhead, allowing security teams to deploy and manage protection at scale without introducing significant complexity at the endpoint level.
However, this model also introduces dependencies. Because CrowdStrike relies heavily on cloud connectivity for analysis and coordination, its effectiveness can be influenced by network availability and service continuity. While rare, any disruption in cloud services can temporarily impact visibility or response capabilities. Additionally, its enterprise-grade pricing structure can be a consideration for smaller organizations or those with limited budgets.
SentinelOne, on the other hand, takes a different path by emphasizing autonomy at the endpoint. Its architecture is designed to ensure that detection and response capabilities remain active even when cloud connectivity is limited or unavailable. This endpoint-first intelligence model allows systems to make real-time decisions locally, reducing latency and enabling immediate response during active threats.
This autonomous approach is especially valuable in environments where downtime is unacceptable or where systems may operate in isolated or hybrid conditions. Industries such as healthcare, manufacturing, critical infrastructure, and government environments often benefit from this resilience because operational continuity is essential and network disruptions can have serious consequences.
SentinelOne’s strength lies in its ability to combine behavioral AI with local execution. By embedding intelligence directly into the endpoint agent, it enables rapid threat detection and mitigation without relying on external communication. Features such as autonomous response and system rollback further enhance its ability to recover from attacks like ransomware, where rapid containment and restoration are critical.
At the same time, SentinelOne’s flexibility and extensibility through its ecosystem allow organizations to tailor security capabilities to their specific needs. The Singularity platform integrates endpoint protection, cloud security, identity defense, and data analytics into a unified system, but it also supports customization through integrations and marketplace extensions. This makes it appealing to organizations with complex or evolving infrastructure requirements.
However, this flexibility comes with trade-offs. The increased configurability and endpoint-level intelligence can introduce operational complexity. Organizations may require more specialized expertise to fully optimize deployments and manage advanced configurations. While powerful, the system may demand more hands-on tuning compared to more centralized platforms.
When evaluating both solutions, it becomes clear that neither platform is universally superior. Instead, each excels in different operational contexts. CrowdStrike is optimized for scale, centralized intelligence, and cloud-native environments where global visibility and streamlined management are priorities. SentinelOne is optimized for resilience, autonomy, and hybrid environments where endpoint independence and offline functionality are critical.
From a strategic cybersecurity perspective, the decision between the two should not be based solely on feature comparison but on organizational architecture, risk tolerance, and operational maturity. Enterprises with highly distributed cloud environments and strong reliance on centralized security operations may find CrowdStrike’s model more aligned with their needs. Organizations with complex hybrid systems, legacy infrastructure, or strict uptime requirements may find SentinelOne’s autonomous model more suitable.
It is also important to recognize that modern cybersecurity is increasingly moving toward convergence. Both platforms are expanding their capabilities across endpoint, identity, cloud, and SIEM domains. CrowdStrike continues to deepen its cloud-native intelligence and global threat correlation capabilities, while SentinelOne continues to enhance its autonomous decision-making and cross-domain integration. This convergence means that the gap between centralized and autonomous models is narrowing over time, with both approaches incorporating elements of each other.
Another key consideration is operational resilience. In today’s threat landscape, organizations must assume that attacks will occur and that no system is immune to compromise. The focus has therefore shifted from prevention alone to detection, response, and recovery. CrowdStrike supports this through rapid cloud-based detection and global intelligence sharing, while SentinelOne supports it through local autonomy and rapid endpoint-level remediation.
Ultimately, the most effective security strategy is not necessarily choosing one platform over the other in isolation but understanding how each aligns with broader security architecture goals. Some organizations may even adopt a layered or hybrid approach, leveraging different tools for different segments of their infrastructure based on specific risk profiles and operational needs.
As cyber threats continue to evolve in sophistication, speed, and scale, security platforms must also continue to evolve. The future of cybersecurity will likely involve greater integration of artificial intelligence, deeper automation of response workflows, and more seamless coordination between cloud and endpoint intelligence. Both CrowdStrike and SentinelOne are actively contributing to this evolution, each pushing the boundaries of how modern security platforms operate.
In conclusion, CrowdStrike and SentinelOne represent two highly advanced but philosophically distinct approaches to cybersecurity. One emphasizes centralized intelligence and global visibility, while the other emphasizes autonomous protection and endpoint resilience. Understanding these differences allows organizations to make more informed decisions based on their unique infrastructure, operational requirements, and long-term security strategy.