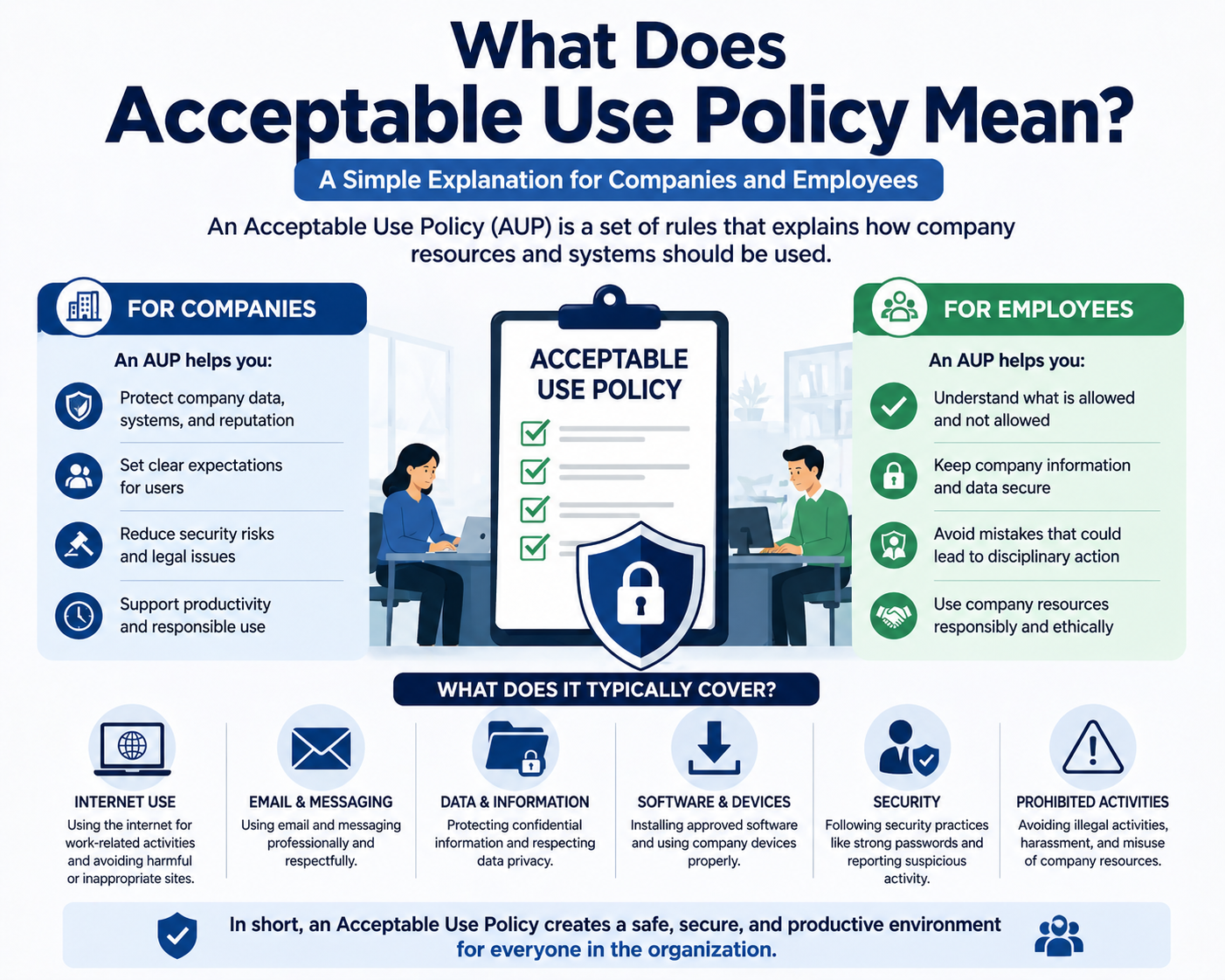
An Acceptable Use Policy is a structured governance document that defines how individuals are permitted to interact with an organization’s digital ecosystem. It establishes behavioral boundaries for the use of computing systems, networks, applications, data assets, and communication platforms. The purpose is to ensure that every interaction with IT infrastructure follows predefined security, operational, and compliance standards.
In enterprise environments, this policy is not treated as an isolated guideline but as a foundational control layer within the cybersecurity framework. It translates organizational expectations into enforceable rules that apply to employees, contractors, partners, and sometimes customers. The strategic role of this policy is to reduce uncertainty in user behavior while aligning day-to-day system usage with security objectives and regulatory requirements. By doing so, it supports consistency in digital operations and strengthens the overall governance model of the organization.
Role of Acceptable Use Policies in Cyber Risk Management
Cyber risk is heavily influenced by human behavior, making user activity one of the most unpredictable elements in security management. Acceptable Use Policies function as preventive controls designed to reduce this uncertainty by clearly defining what is and is not permitted.
These guidelines help prevent risks such as unauthorized access, accidental data exposure, insecure file sharing, and misuse of organizational systems. Instead of relying solely on technical defenses, organizations use behavioral governance to reduce the likelihood of security incidents originating from user actions. This approach strengthens risk management by addressing the human layer of cybersecurity, which is often the most exploited attack surface.
By setting clear expectations, the policy reduces ambiguity in decision-making and ensures users understand the consequences of unsafe behavior before engaging with digital systems.
Governance Scope Across Digital Systems and Enterprise Assets
The scope of an Acceptable Use Policy extends across all digital and information assets within an organization’s environment. This includes physical endpoints such as desktops, laptops, mobile devices, and tablets, as well as virtual infrastructure hosted in cloud environments.
It also covers communication tools such as email platforms, messaging applications, video conferencing systems, and collaboration suites. In addition, enterprise applications, databases, file storage systems, and internal portals fall under its governance structure. Network infrastructure, including wired and wireless connections, is also regulated under usage rules.
Even removable storage devices, personal hardware connected through approved access methods, and externally integrated systems are included within the policy scope. This wide coverage ensures that no interaction point with organizational data remains outside governance control.
Establishing User Behavior Standards in Enterprise Environments
One of the primary objectives of an Acceptable Use Policy is to establish clear behavioral standards for system users. These standards define how individuals should interact with organizational resources in a secure, responsible, and compliant manner.
Users are expected to follow approved authentication procedures, safeguard access credentials, and use systems only for authorized business purposes. They are also required to handle sensitive information carefully, avoid unauthorized sharing, and comply with internal communication guidelines.
Behavioral standards also extend to software usage, where only approved applications and tools may be installed or used. These rules ensure that user behavior aligns with organizational expectations and reduces the risk of introducing vulnerabilities into the environment.
Distinction Between Acceptable and Unacceptable System Usage
A key component of usage governance is the clear separation between acceptable and unacceptable actions. Acceptable activities typically include authorized system access, use of approved software, secure data handling, and compliance with organizational communication protocols.
Unacceptable activities include actions that compromise system integrity or security. These may involve installing unauthorized software, sharing login credentials, bypassing security controls, accessing restricted content, or transferring data to unapproved external devices or platforms.
By clearly defining both categories, organizations eliminate ambiguity and provide users with a structured decision-making framework. This helps reduce accidental policy violations and reinforces responsible system usage across all user groups.
Integration with Authentication and Access Control Mechanisms
Acceptable Use Policies are closely integrated with authentication and access control systems within enterprise environments. While technical systems enforce identity verification and restrict access based on roles, the policy defines how those credentials and access privileges should be used responsibly.
Users are expected to protect login information, avoid credential sharing, and follow secure authentication practices. These behavioral expectations reinforce the effectiveness of technical controls by ensuring that access privileges are not misused.
This integration creates a layered security approach where both human behavior and system controls work together to protect organizational resources from unauthorized access and misuse.
Applicability Across Internal and External User Groups
Acceptable Use Policies apply not only to internal employees but also to external users who interact with organizational systems. Internal users are required to follow strict operational guidelines when accessing enterprise resources, while external users such as vendors, contractors, and clients must comply with access conditions defined by the organization.
This dual applicability ensures consistent security expectations across all user categories. Whether an individual is inside or outside the organization, any interaction with systems or data is governed by the same foundational principles of responsible usage.
This consistency is critical in modern interconnected environments where external collaboration is common and system boundaries are often extended beyond traditional organizational limits.
Role in Enhancing Operational Efficiency and Resource Management
Beyond security enforcement, Acceptable Use Policies contribute significantly to operational efficiency. By regulating non-essential activities and restricting inappropriate system usage, organizations ensure that computing resources are used primarily for business-related purposes.
This helps maintain stable network performance, reduces unnecessary bandwidth consumption, and improves application responsiveness. It also ensures that critical systems remain available for essential operations without being impacted by excessive or irrelevant user activity.
In structured environments, this controlled usage contributes to better resource allocation and improved overall system reliability.
Alignment with Enterprise Security and Governance Frameworks
Acceptable Use Policies do not operate independently but are integrated into broader security and governance frameworks. They support identity management systems, data protection strategies, risk management models, and compliance structures.
This alignment ensures that behavioral controls are consistent with technical safeguards and organizational policies. It creates a unified governance ecosystem where user actions, system controls, and security objectives are fully synchronized.
By functioning as part of a larger framework, the policy strengthens organizational resilience against both internal misuse and external threats while maintaining operational consistency across all systems.
Operational Expansion of Acceptable Use Policy in Enterprise Environments
An Acceptable Use Policy extends beyond a foundational governance document and becomes operational when it is actively embedded into daily organizational workflows. In enterprise environments, this expansion transforms the policy from a static set of rules into a functional control mechanism that shapes how users interact with systems in real time. The operational layer ensures that guidelines are not only defined but also consistently applied across endpoints, networks, applications, and cloud platforms.
At this stage, the policy begins influencing actual user behavior through system configurations, access restrictions, onboarding procedures, and continuous monitoring structures. It becomes part of the organization’s operational security fabric, directly affecting how digital resources are consumed and managed. This integration is essential for maintaining consistency between written policy and real-world execution.
System-Wide Enforcement Through Technical and Administrative Controls
Enforcement of acceptable use rules relies on a combination of technical controls and administrative governance. Technical controls include authentication systems, endpoint management tools, network filtering mechanisms, and application-level restrictions that limit what users can do within digital environments. These systems enforce boundaries automatically, reducing reliance on manual supervision.
Administrative controls complement these mechanisms by defining procedures, responsibilities, and escalation paths for handling violations. This includes managerial oversight, audit processes, and structured disciplinary frameworks. Together, these two enforcement layers ensure that policy compliance is maintained across all operational levels.
The effectiveness of enforcement depends on consistency. When users understand that rules are actively monitored and consistently applied, adherence increases significantly. This reduces the likelihood of intentional misuse and discourages negligent behavior.
Role of Acceptable Use Policy in Identity and Access Governance
Identity and access governance forms a critical component of acceptable use enforcement. Every user interacting with enterprise systems is assigned a unique identity, which determines their access privileges and operational boundaries. The policy defines how these identities should be used, protected, and managed.
Users are expected to maintain strict confidentiality of authentication credentials and avoid any form of credential sharing. Access privileges are granted based on role definitions, ensuring that individuals can only interact with systems necessary for their job functions. This principle of least privilege reduces unnecessary exposure to sensitive resources.
When integrated with identity systems, acceptable use rules help prevent unauthorized access, privilege escalation, and misuse of shared credentials. This strengthens overall identity security and ensures that access control systems function as intended.
Monitoring Mechanisms and Behavioral Visibility in Digital Systems
Monitoring plays a central role in enforcing acceptable use governance. Organizations implement visibility mechanisms that track system usage patterns, access events, and network activity. These mechanisms provide insights into how users interact with digital resources and help identify deviations from expected behavior.
Monitoring systems may record login activity, file access patterns, application usage, and network connections. This data is analyzed to detect anomalies such as unusual access times, unauthorized system navigation, or abnormal data transfers. These indicators help security teams identify potential policy violations or security incidents.
Behavioral visibility ensures that organizations maintain awareness of user activity without necessarily interfering with productivity. It creates a controlled environment where usage is transparent and accountable.
Integration of Acceptable Use Policy with Endpoint Security Systems
Endpoint devices represent one of the most critical enforcement points for acceptable use governance. These include laptops, desktops, mobile devices, and other computing equipment used to access organizational resources. Endpoint security systems enforce policy rules by controlling software installation, device configuration, and data access.
Organizations often restrict unauthorized applications, prevent unapproved device connections, and enforce encryption standards on endpoints. These controls ensure that devices interacting with enterprise systems comply with defined security requirements.
By integrating acceptable use rules with endpoint security tools, organizations reduce the risk of malware introduction, data leakage, and unauthorized system modification. This integration strengthens the overall security posture at the device level.
Network-Level Controls Supporting Usage Governance
Network infrastructure plays a key role in enforcing acceptable use rules by regulating traffic flow and access permissions. Network-level controls include firewalls, access control lists, segmentation policies, and traffic monitoring systems that define how data moves within and outside the organization.
These controls can restrict access to specific websites, block unauthorized services, and limit communication between network segments. They also help enforce acceptable use rules related to internet browsing, data transfer, and external communication.
By managing network behavior, organizations ensure that users operate within defined digital boundaries, reducing exposure to external threats and minimizing misuse of network resources.
Application Governance and Software Usage Restrictions
Application governance ensures that users interact only with approved software systems within the enterprise environment. Acceptable Use Policies define which applications are authorized, how they should be used, and what restrictions apply to their operation.
This includes controlling installation privileges, limiting administrative access, and preventing the use of unauthorized or unverified software. Application governance also extends to cloud-based tools and third-party integrations that interact with internal systems.
By controlling software usage, organizations reduce the risk of vulnerabilities introduced through unapproved applications, outdated software versions, or malicious tools.
Data Handling Rules and Information Lifecycle Control
Data handling is a critical component of acceptable use governance. Policies define how information should be created, accessed, stored, transmitted, and eventually disposed of within the organization.
Users are required to follow secure handling practices, ensuring that sensitive data is not exposed to unauthorized individuals or systems. This includes restrictions on copying data to external devices, sharing information through unsecured channels, or storing data in unapproved locations.
Information lifecycle control ensures that data remains protected throughout its existence, from creation to deletion. This reduces the risk of unauthorized disclosure and strengthens data integrity across systems.
Remote Access Governance and Distributed Work Environments
Modern enterprise environments often include remote access capabilities that allow users to connect to systems from external locations. Acceptable Use Policies define how remote access should be conducted, including authentication requirements, device security standards, and permitted usage scenarios.
Remote users are expected to follow stricter security protocols due to increased exposure to external risks. This includes secure connections, device compliance checks, and restricted access to sensitive systems.
By governing remote access, organizations ensure that distributed workforces maintain the same security standards as on-site users, reducing risk in decentralized environments.
Compliance Alignment with Regulatory and Industry Standards
Acceptable Use Policies must align with external regulatory frameworks and industry standards that govern data protection and system security. These may include privacy regulations, financial compliance requirements, and sector-specific security mandates.
Compliance alignment ensures that organizational practices meet legal obligations and reduce exposure to regulatory penalties. It also provides a structured approach to auditing and accountability, allowing organizations to demonstrate adherence to required standards.
By integrating compliance requirements into usage governance, organizations ensure that behavioral rules support broader legal and operational obligations.
Incident Prevention Through Behavioral Control Mechanisms
One of the primary objectives of acceptable use governance is to prevent security incidents before they occur. Behavioral control mechanisms reduce the likelihood of actions that could lead to system compromise, data breaches, or operational disruption.
These mechanisms guide users toward secure practices and discourage unsafe behavior through clearly defined rules and monitoring structures. When users are aware that their actions are governed and observable, they are less likely to engage in risky activities.
Preventive control is more efficient than reactive response, making behavioral governance a critical component of proactive cybersecurity strategy.
Organizational Communication and Policy Dissemination Structures
Effective policy implementation requires structured communication channels that ensure all users are aware of acceptable use expectations. Organizations use onboarding programs, internal documentation systems, and awareness campaigns to disseminate policy information.
Clear communication ensures that users understand their responsibilities and the consequences of non-compliance. It also reinforces consistency across departments and user groups, reducing misinterpretation of policy rules.
Ongoing communication ensures that policy awareness remains high even as systems, technologies, and operational environments evolve over time.
Behavioral Accountability and Enforcement Consistency Models
Accountability is a key principle in acceptable use governance. Users must be aware that their actions within digital environments are subject to oversight and enforcement. Consistent application of rules ensures fairness and reinforces trust in the governance system.
When violations occur, structured escalation processes are used to assess impact and determine appropriate responses. These responses may vary depending on severity and intent, but consistency in enforcement is essential for maintaining credibility.
Accountability structures ensure that policy enforcement is not arbitrary but follows predefined organizational standards.
Lifecycle Adaptation of Acceptable Use Governance Systems
Acceptable Use Policies are not static documents; they evolve alongside technological advancements and organizational changes. Lifecycle management ensures that policies remain relevant in dynamic environments where new threats, tools, and workflows continuously emerge.
Regular reviews allow organizations to update usage rules, refine enforcement mechanisms, and adjust behavioral expectations based on operational feedback. This adaptability ensures long-term effectiveness and alignment with current digital practices.
Lifecycle adaptation also ensures that governance frameworks remain scalable as organizations grow and adopt new technologies.
Strategic Evolution of Acceptable Use Policy in Modern Digital Ecosystems
Acceptable Use Policy continues to evolve as organizations expand their digital ecosystems across hybrid infrastructures, cloud-native platforms, distributed endpoints, and third-party integrations. In earlier implementations, such policies primarily focused on restricting internet misuse and controlling basic system access. In modern enterprise environments, however, the scope has significantly expanded to include behavioral governance across complex, interconnected systems that operate in real time and across geographic boundaries.
This evolution reflects the increasing dependency on digital infrastructure for business continuity. As organizations adopt advanced technologies such as virtualization, SaaS ecosystems, and remote-first operations, acceptable use frameworks must adapt to regulate interactions across diverse environments. The policy now acts as a dynamic governance layer that continuously aligns user behavior with evolving technological and operational requirements.
Behavioral Engineering and User Compliance Mechanisms in Enterprise Systems
A critical dimension of acceptable use governance is behavioral engineering, which focuses on influencing user decisions through structured rules, constraints, and awareness mechanisms. Instead of relying solely on enforcement after violations occur, organizations design policies that proactively guide user behavior toward secure and compliant actions.
This includes defining clear interaction patterns, simplifying secure choices, and reducing opportunities for unsafe behavior. For example, restricting unauthorized software installation or limiting access to sensitive systems reduces cognitive load on users and minimizes the likelihood of accidental violations.
Compliance mechanisms also include automated reminders, system prompts, and access restrictions that reinforce policy adherence in real time. These mechanisms ensure that users are continuously guided toward correct behavior without requiring constant manual oversight.
Role of Acceptable Use Policy in Cloud and Hybrid Infrastructure Environments
The transition to cloud computing and hybrid infrastructure models has significantly expanded the operational scope of acceptable use governance. Users now interact with resources that are distributed across on-premises systems, private cloud environments, and public cloud platforms.
In such environments, acceptable use policies define how cloud services should be accessed, how data should be stored, and how applications should be utilized across different platforms. This includes controlling access to cloud storage, enforcing secure authentication for remote services, and regulating data transfer between environments.
Hybrid infrastructures introduce additional complexity because users often move between multiple systems during a single workflow. The policy ensures consistency in behavior regardless of where the resources are hosted, maintaining uniform security expectations across all environments.
Advanced Monitoring Techniques and Behavioral Analytics Integration
Modern acceptable use enforcement increasingly relies on behavioral analytics and advanced monitoring systems. These systems analyze user activity patterns to identify deviations from normal behavior. Instead of relying only on predefined rule violations, behavioral analytics uses statistical models to detect anomalies in real time.
For example, unusual login times, excessive data downloads, or irregular system access patterns may indicate potential misuse or compromised credentials. These insights allow organizations to respond proactively to emerging risks rather than reacting after damage has occurred.
Monitoring systems also integrate across multiple layers, including endpoints, networks, applications, and cloud environments. This multi-layer visibility ensures that user behavior is tracked holistically, providing a complete view of system interaction.
Acceptable Use Policy in Identity-Centric Security Models
Identity-centric security models place user identity at the core of all access decisions. Within this framework, acceptable use policies define how identities should be used, protected, and managed across systems.
Each user identity represents a controlled access point to organizational resources. Policies enforce strict rules regarding authentication practices, session management, and credential protection. Users are required to maintain secure authentication behavior, avoid credential reuse, and comply with multi-factor authentication requirements where applicable.
By integrating acceptable use governance with identity-centric models, organizations ensure that every digital interaction is tied to a verifiable and accountable identity, significantly reducing the risk of unauthorized access or impersonation.
Enforcement Challenges in Large-Scale Distributed Environments
As organizations scale across multiple regions and adopt distributed operational models, enforcing acceptable use policies becomes increasingly complex. Users may access systems from different locations, devices, and network conditions, making uniform enforcement more challenging.
One of the primary challenges is maintaining consistency across diverse environments. Differences in infrastructure, regulatory requirements, and technical capabilities can lead to variations in policy enforcement. Additionally, remote and mobile users introduce variability in system access patterns, which complicates monitoring and control.
To address these challenges, organizations rely on centralized governance frameworks and automated enforcement mechanisms that ensure consistent application of rules regardless of location or device type.
Acceptable Use Policy and Third-Party Risk Management Integration
Modern enterprise ecosystems frequently involve third-party vendors, contractors, and external service providers. Acceptable use governance extends to these external entities to ensure that their interactions with organizational systems meet defined security standards.
Third-party users are typically granted limited access based on contractual agreements and operational requirements. The policy defines how these users may interact with systems, what data they can access, and what restrictions apply to their activities.
This integration is a critical component of third-party risk management, as external entities often represent indirect access points into organizational infrastructure. By enforcing consistent usage rules, organizations reduce exposure to risks originating from external partnerships.
Incident Response Alignment with Acceptable Use Governance Structures
Incident response frameworks rely on acceptable use policies to define baseline behavior expectations and identify deviations that may indicate security incidents. When violations occur, response teams use policy definitions to assess severity and determine appropriate actions.
For example, unauthorized data access or policy violations involving sensitive systems may trigger incident escalation procedures. The policy provides a reference point for distinguishing between acceptable anomalies and genuine security threats.
This alignment ensures that incident response activities are structured, consistent, and based on predefined organizational expectations rather than subjective interpretation.
Human Factors and Psychological Influence on Policy Adherence
Human behavior plays a central role in the effectiveness of acceptable use governance. Psychological factors such as awareness, perception of risk, and ease of compliance directly influence how users interact with systems and whether they follow established rules. Users are not purely technical actors; their decisions are shaped by habits, cognitive load, time pressure, and perceived consequences. When policies are designed without considering these human elements, even well-intentioned users may fail to comply consistently.
Policies that are overly complex or difficult to interpret can create confusion, leading to unintentional violations. If users must invest excessive effort to understand what is permitted, they may default to assumptions or shortcuts. On the other hand, policies that are excessively restrictive can push users toward unofficial workarounds, which often introduce greater security risks than the original behavior the policy intended to prevent. Effective governance strikes a balance by providing clear, concise, and actionable guidance that aligns with natural user workflows and minimizes friction in daily tasks.
Role of Automation in Strengthening Policy Enforcement
Automation has become a critical enabler in enforcing acceptable use governance at scale, particularly in large and distributed enterprise environments. Manual enforcement alone is insufficient to manage the volume and complexity of modern system interactions. Automated systems provide the capability to enforce rules consistently, immediately, and without reliance on human intervention.
These systems can apply access restrictions, detect anomalies, and enforce compliance in real time. For instance, endpoint management solutions can automatically block unauthorized software installations, enforce configuration standards, and ensure that devices remain compliant with security requirements. Similarly, network-level controls can restrict access to unauthorized services or external destinations based on predefined policy rules. Automation ensures that these controls are applied uniformly across all users and devices, eliminating inconsistencies that may arise from manual processes.
In addition to enforcement, automation enhances monitoring capabilities by processing large volumes of behavioral data efficiently. Advanced analytics systems can identify patterns, detect anomalies, and flag potential violations before they escalate into serious incidents. This proactive approach allows organizations to respond quickly to emerging risks while maintaining continuous oversight of system usage.
Continuous Improvement and Adaptive Governance Models
Acceptable use governance must evolve continuously to remain effective in rapidly changing technological landscapes. Static policies quickly become outdated as new tools, platforms, and threat vectors emerge. Adaptive governance models address this challenge by enabling organizations to refine policies based on real-time feedback, risk assessments, and operational insights.
Continuous improvement involves regular evaluation of policy effectiveness through audits, monitoring data, and user feedback. Organizations identify gaps where policies may be unclear, overly restrictive, or insufficiently enforced. These insights are then used to update guidelines, improve clarity, and enhance enforcement mechanisms. This iterative process ensures that policies remain aligned with both organizational objectives and current risk environments.
Adaptive governance also supports scalability. As organizations grow, adopt new technologies, or expand into new operational domains, acceptable use policies must adjust accordingly. This may involve extending governance to new systems, redefining access controls, or introducing additional behavioral guidelines. Flexibility is essential to ensure that policies can accommodate change without compromising security or usability.
Cultural Integration of Acceptable Use Principles in Organizations
For acceptable use governance to achieve long-term effectiveness, it must become embedded within organizational culture. This means that compliance is not driven solely by enforcement mechanisms but by a shared understanding of responsible digital behavior. When users view acceptable use principles as part of their everyday responsibilities, adherence becomes more natural and consistent.
Cultural integration begins with leadership. When organizational leaders demonstrate commitment to policy adherence, it reinforces the importance of acceptable use across all levels. Consistent communication further strengthens this integration by keeping users informed about expectations, updates, and the rationale behind policies. Messaging should be clear, practical, and aligned with real-world scenarios to ensure relevance.
Alignment with workflows is another critical factor. Policies must support productivity rather than hinder it. When users can follow guidelines without disrupting their tasks, compliance becomes easier to maintain. This requires collaboration between technical teams, management, and end users to ensure that policies reflect operational realities.
Long-Term Sustainability of Acceptable Use Governance Frameworks
The sustainability of acceptable use governance depends on its ability to remain relevant, adaptable, and consistently enforced over time. As organizations evolve, their digital environments become more complex, introducing new challenges for policy management. Sustainable frameworks are designed to accommodate these changes while maintaining core governance principles.
Regular review cycles are essential for ensuring that policies remain up to date. Changes in technology, regulatory requirements, and organizational structure may necessitate adjustments to acceptable use guidelines. Without periodic updates, policies risk becoming outdated and ineffective. Sustainability also requires balancing security requirements with operational flexibility. Overly rigid policies may hinder productivity, while overly lenient policies may expose the organization to risk.
Feedback mechanisms play a crucial role in maintaining sustainability. By collecting input from users, administrators, and security teams, organizations can identify areas for improvement and refine policies accordingly. This collaborative approach ensures that governance frameworks remain practical and aligned with user needs.
Conclusion
The Acceptable Use Policy functions as a core behavioral and governance mechanism within modern digital environments, shaping how individuals interact with organizational technology resources. Across all of this discussion, it becomes clear that the policy is not simply a static document but a continuously operating control layer embedded within cybersecurity architecture, operational workflows, and organizational culture. Its influence extends across systems, users, data, and infrastructure, forming a structured boundary between acceptable and unacceptable digital behavior.
At its foundation, the policy exists to reduce ambiguity in user decision-making. In complex enterprise environments where users interact with a wide range of systems, applications, and data sets, uncertainty can easily lead to mistakes or misuse. By defining clear behavioral expectations, the policy removes guesswork and ensures that users understand the limits of their authority and responsibility. This clarity plays a direct role in reducing operational risk, particularly in environments where human error remains one of the leading causes of security incidents.
Another critical dimension of the policy is its role in strengthening cybersecurity posture through behavioral control. While technical defenses such as firewalls, encryption systems, and authentication mechanisms form the backbone of security architecture, they are not sufficient on their own. Human behavior remains a variable that can either reinforce or weaken these protections. The Acceptable Use Policy addresses this gap by guiding how users should interact with systems in ways that support security objectives rather than compromise them. When users follow structured behavioral rules, the effectiveness of technical controls increases significantly.
The policy also contributes to organizational efficiency by regulating non-essential or potentially disruptive activities. In digital environments, unrestricted usage can lead to resource exhaustion, network congestion, and reduced system performance. By defining appropriate usage boundaries, organizations ensure that computing resources are allocated primarily toward productive business functions. This not only improves system reliability but also enhances overall operational stability, especially in large-scale environments where multiple users share critical infrastructure.
From a governance perspective, the Acceptable Use Policy reinforces accountability across all levels of the organization. Every user interaction with digital systems becomes traceable and governed by predefined rules. This accountability structure ensures that deviations from expected behavior can be identified, analyzed, and addressed in a consistent manner. It also establishes a fair framework where all users are subject to the same expectations, regardless of role or seniority, which strengthens trust in the governance system.
The policy’s integration with identity and access management systems further enhances its effectiveness. By aligning behavioral rules with technical access controls, organizations create a unified security model where identity determines both access privileges and usage responsibilities. This ensures that users not only have appropriate access to systems but also understand how to use that access responsibly. The principle of least privilege is reinforced through behavioral constraints, reducing unnecessary exposure to sensitive resources.
In modern distributed environments, the importance of acceptable use governance becomes even more pronounced. With the widespread adoption of remote work, cloud computing, and hybrid infrastructures, users are no longer confined to a single controlled network perimeter. Instead, they interact with organizational systems from multiple locations and devices. This decentralization increases complexity and expands the potential attack surface. The Acceptable Use Policy provides a consistent behavioral framework that remains applicable regardless of location, ensuring that security expectations do not change based on access context.
Monitoring and enforcement mechanisms play a critical role in maintaining the integrity of the policy. Without visibility into user activity, governance frameworks lose their effectiveness. Continuous monitoring allows organizations to detect deviations from expected behavior and respond appropriately. However, the goal of monitoring is not only enforcement but also awareness. When users understand that system activity is observable, they are more likely to adhere to defined rules, which reinforces compliance through behavioral awareness rather than purely punitive measures.
The policy also interacts closely with data protection principles. In modern organizations, data is one of the most valuable assets, and its protection depends heavily on user behavior. Improper handling of sensitive information can lead to breaches, regulatory violations, and reputational damage. The Acceptable Use Policy establishes rules for how data should be accessed, shared, and stored, ensuring that information remains protected throughout its lifecycle. This behavioral layer complements technical safeguards such as encryption and access control, creating a multi-layered defense structure.
Third-party interactions introduce additional complexity into acceptable use governance. Vendors, contractors, and external partners often require access to internal systems to perform their functions. Without clear usage boundaries, these external connections can become potential risk vectors. The policy ensures that third-party users adhere to the same behavioral standards as internal users, reducing inconsistency and minimizing exposure from external integrations. This is particularly important in ecosystems where supply chain relationships are deeply integrated into operational processes.
Another important aspect is the role of training and awareness in sustaining policy effectiveness. A policy that is not understood by users cannot be effectively enforced. Organizations must ensure that individuals are not only aware of the rules but also understand the reasoning behind them. This understanding improves compliance because users are more likely to follow guidelines when they recognize their purpose and relevance. Continuous reinforcement through communication and training ensures that acceptable use principles remain embedded in daily operations.
Despite its benefits, implementing and maintaining an effective Acceptable Use Policy presents challenges. Balancing security requirements with usability is one of the most significant difficulties. Overly restrictive policies can hinder productivity and lead to user frustration, while overly flexible policies can weaken security posture. Achieving the right balance requires ongoing evaluation and adjustment based on organizational needs, technological changes, and user feedback.
Ultimately, the Acceptable Use Policy serves as a foundational pillar in the broader cybersecurity and governance ecosystem. It connects human behavior with technical controls, ensuring that both work in alignment to protect organizational assets. Its effectiveness depends not only on how it is written but also on how it is implemented, enforced, and integrated into organizational culture. When properly designed and maintained, it becomes an essential mechanism for reducing risk, improving operational efficiency, and strengthening overall digital resilience.