Root guard is a critical network protection feature designed to maintain stability within Layer 2 switching environments. It ensures that the designated root bridge in a spanning tree topology remains unchanged unless explicitly intended by the network administrator. In complex enterprise infrastructures, where multiple switches are interconnected, the risk of unintended topology changes is always present. Root guard addresses this challenge by preventing unauthorized devices from influencing the root bridge election process.
In a stable network design, consistency is essential for predictable data flow. When the root bridge changes unexpectedly, the entire topology recalculates, which can result in temporary disruptions, suboptimal routing paths, and even network downtime. Root guard acts as a safeguard against such instability by controlling which switches are allowed to participate in root bridge selection.
This feature is especially important in environments where uptime and reliability are critical, such as enterprise campuses, data centers, and service provider networks. It provides administrators with greater control over spanning tree behavior and helps maintain the intended network architecture.
Understanding the Role of Root Bridge in Network Topology
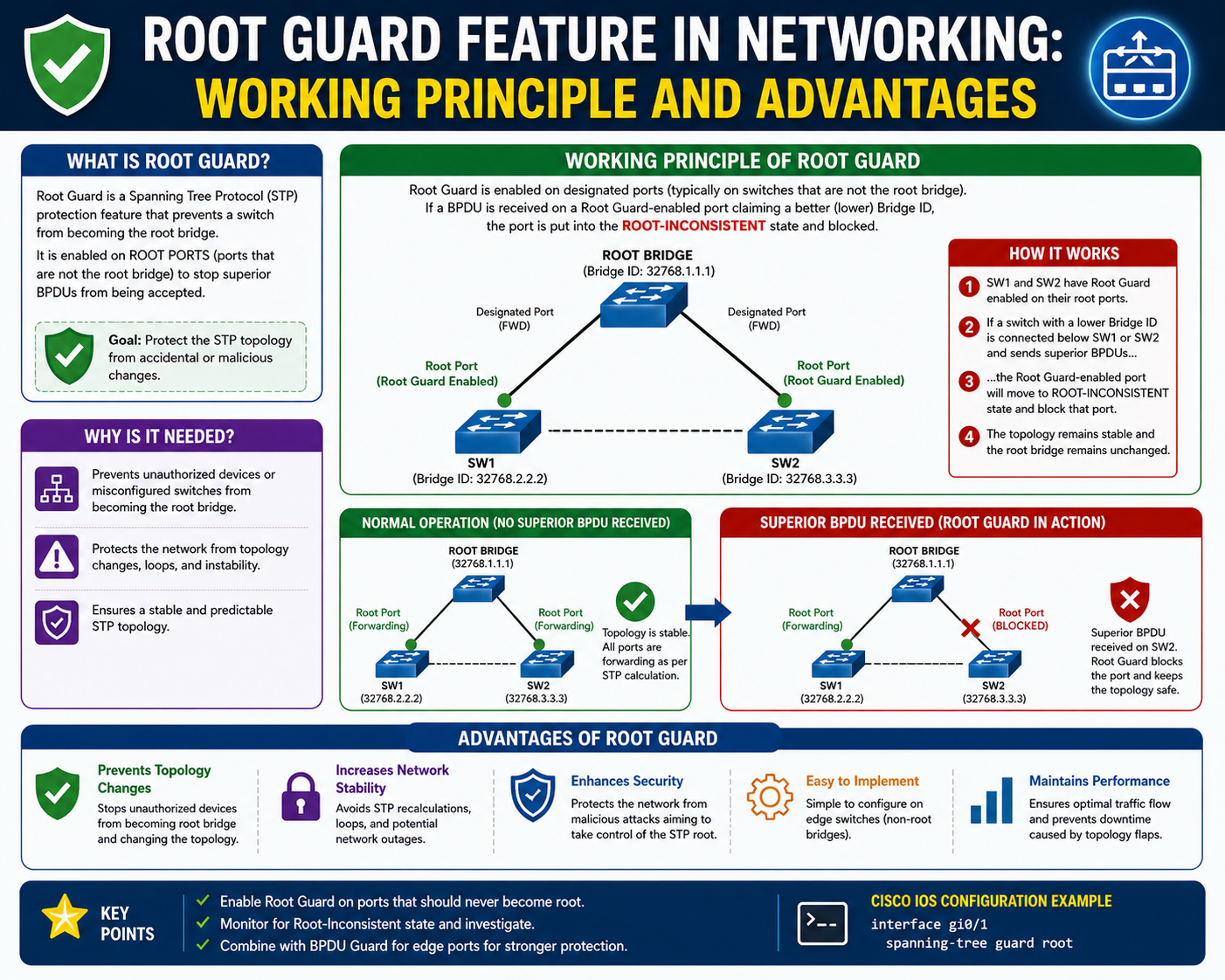
To fully understand root guard, it is essential to understand the concept of the root bridge. In a spanning tree topology, the root bridge is the central reference point that determines how all other switches calculate their shortest path to forward traffic. Every switch in the network selects the root bridge based on bridge priority and MAC address values exchanged through Bridge Protocol Data Units.
Once the root bridge is elected, all other switches build their forwarding paths around it. This structure prevents loops and ensures that there is only one active path between any two devices in the network. However, if a switch with a lower bridge ID is introduced or misconfigured, it may attempt to become the new root bridge. This can disrupt the entire topology and lead to unpredictable network behavior.
Root guard ensures that such changes do not occur unless explicitly intended. It locks the root bridge position and prevents external switches from overriding it.
Why Root Guard Is Necessary in Enterprise Networks
Enterprise networks are dynamic environments where devices are frequently added, removed, or reconfigured. In such scenarios, maintaining a consistent spanning tree topology becomes challenging. Without proper safeguards, a newly connected switch with a lower priority setting could unintentionally become the root bridge.
This can lead to several issues, including inefficient routing paths, increased latency, and potential traffic loops. In severe cases, broadcast storms may occur, consuming bandwidth and degrading overall network performance.
Root guard eliminates these risks by ensuring that only trusted switches within the network hierarchy can influence root bridge selection. It is particularly useful in environments where multiple teams manage different sections of the network, reducing the risk of configuration conflicts.
How Root Guard Operates Within Spanning Tree Protocol
Root guard works by monitoring incoming Bridge Protocol Data Units on configured interfaces. These BPDUs contain information about the sending switch, including its bridge priority and identifier. When a switch receives a BPDU that indicates a superior root bridge, root guard evaluates whether this change should be allowed.
If root guard is enabled on the interface and a superior BPDU is detected, the port is immediately placed into a restricted state known as root-inconsistent mode. In this state, the port stops participating in the spanning tree process and blocks traffic forwarding. However, it continues to listen for BPDU updates to determine when normal conditions are restored.
Once the superior BPDU condition is removed, the port automatically returns to its normal forwarding state without manual intervention. This self-healing behavior makes root guard highly efficient in maintaining network stability.
Difference Between Root Guard and Spanning Tree Protection Mechanisms
Root guard is often confused with other spanning tree protection features, but it serves a specific purpose. Its primary role is to protect the root bridge election process, not to block all BPDU activity.
For example, BPDU guard is designed to disable ports when unexpected BPDU messages are received on edge interfaces. This is typically used to protect against misconfigured end devices. In contrast, root guard is applied on ports where maintaining control over root bridge selection is essential.
This distinction allows network administrators to apply multiple layers of protection depending on the role of each interface within the network hierarchy. Root guard is generally used on distribution and access uplinks, while BPDU guard is used on edge ports.
Behavior of Root Guard During Network Changes
When a network is stable, root guard remains in a monitoring state, continuously evaluating incoming BPDU information. If no superior BPDU is detected, the interface continues to operate normally without any interruption.
However, when a switch connected to a root guard-enabled port attempts to become the root bridge, the system reacts immediately. The interface is placed into a blocking state, preventing any influence on spanning tree calculations. This ensures that the existing root bridge remains unchanged.
This behavior is temporary and dynamic. If the unauthorized switch is removed or reconfigured, the interface automatically recovers and resumes normal forwarding operations. This ensures that network administrators do not need to manually intervene in most cases.
Impact of Root Guard on Network Stability and Performance
Network stability is heavily dependent on consistent topology behavior. Root guard contributes directly to this stability by preventing unexpected changes in root bridge selection. Without such a mechanism, even minor configuration changes could lead to widespread recalculations of spanning tree paths.
These recalculations can cause temporary disruptions as switches converge on a new topology. During this process, certain links may be temporarily blocked, leading to packet loss or increased latency. In high-performance environments, even short disruptions can have a significant operational impact.
By enforcing root bridge consistency, root guard minimizes these risks and ensures that traffic flows remain predictable and optimized.
Strategic Importance of Root Guard in Network Design
In modern network design, hierarchical architectures are commonly used to improve scalability and manageability. These architectures typically include core, distribution, and access layers. The root bridge is usually placed at a controlled location within this hierarchy to ensure optimal traffic flow.
Root guard plays a key role in preserving this design. It prevents lower-level switches from interfering with root bridge selection, ensuring that the intended topology remains intact. This allows network engineers to design predictable and efficient routing structures without worrying about accidental disruptions.
In large-scale environments, where hundreds or even thousands of switches may be deployed, this level of control becomes essential.
Operational Importance of Controlled Root Bridge Selection
Controlled root bridge selection is a fundamental aspect of spanning tree optimization. By carefully selecting the root bridge, administrators can influence traffic flow and reduce latency across the network. Root guard ensures that this selection remains consistent over time.
Without root guard, a newly added switch with a lower bridge priority could unintentionally become the root bridge, altering traffic paths and potentially creating congestion in unintended areas of the network. This lack of control can lead to inefficiencies and unpredictable performance.
Root guard ensures that only authorized changes can affect root bridge election, maintaining operational consistency.
Role of Root Guard in Preventing Topology Instability
Topology instability occurs when frequent changes in network structure force continuous recalculations of spanning tree paths. This instability can negatively impact performance and reliability.
Root guard prevents such instability by locking down root bridge selection. It ensures that topology changes only occur when explicitly configured by the administrator. This controlled behavior allows networks to remain stable even in environments with frequent device changes.
By reducing unnecessary recalculations, root guard improves convergence times and enhances overall network efficiency.
Foundation for Advanced Network Security Practices
Root guard is often considered a foundational element in advanced network security strategies. While it does not directly block malicious traffic, it protects the structural integrity of the network. This structural protection is essential for maintaining the overall security posture.
When combined with other spanning tree security features, root guard contributes to a layered defense strategy that protects both network performance and topology integrity. It ensures that the underlying switching infrastructure remains stable, which is critical for higher-level security mechanisms to function effectively.
How Root Guard Is Configured on Network Devices
Root guard is typically configured at the interface level on switches that are part of the distribution or access layer uplinks. The configuration process is straightforward but must be applied carefully to avoid unintended blocking of legitimate network traffic.
The administrator first identifies interfaces where root bridge changes must be prevented. These are usually ports connecting downstream switches or segments where external devices should not influence spanning tree decisions. Once identified, root guard is enabled on those interfaces through the spanning tree configuration mode.
After activation, the interface begins monitoring all incoming Bridge Protocol Data Units. If any BPDU advertises a superior root bridge compared to the current network root, the port reacts immediately by entering a restricted state. This ensures that only the intended root bridge remains active.
Proper configuration requires careful planning of network topology to ensure that root guard is applied only where needed. Incorrect placement can lead to unnecessary blocking of legitimate switches, which may affect connectivity.
Interface-Level Behavior After Root Guard Activation
Once root guard is enabled on a port, the interface behaves differently compared to a standard spanning tree-enabled port. In normal operation, the interface participates in forwarding decisions and allows BPDU exchange without restrictions.
However, when a superior BPDU is detected, the interface transitions into a special state known as root-inconsistent mode. In this state, the port stops forwarding traffic but continues to listen for BPDU updates. This behavior ensures that the network remains aware of topology changes without allowing them to take effect.
This mechanism is dynamic and self-recovering. If the condition causing the inconsistency is removed, such as disconnecting the unauthorized switch or correcting its configuration, the port automatically returns to its normal forwarding state. This eliminates the need for manual intervention in most cases.
Root Guard in Spanning Tree Convergence Process
Spanning tree convergence is the process through which switches in a network agree on a stable topology after a change occurs. Without protection mechanisms, convergence can be triggered frequently by minor configuration changes or device additions.
Root guard plays a significant role in reducing unnecessary convergence events. By preventing changes to the root bridge, it ensures that the spanning tree remains stable even when new switches are introduced into the network.
When root guard is active, only allowed topology changes are processed. Any attempt to alter the root bridge election is blocked at the interface level. This reduces the frequency of recalculations and improves overall network stability.
Practical Deployment Scenarios for Root Guard
Root guard is most commonly deployed in hierarchical network architectures. In such designs, switches are organized into core, distribution, and access layers. The root bridge is typically placed in the core or distribution layer to optimize traffic flow.
In this structure, root guard is applied on ports connecting to lower-layer switches. This ensures that access layer devices cannot influence the root bridge election process. As a result, the network maintains a consistent and predictable topology.
Another common scenario involves environments with mixed administrative control. In large organizations, different teams may manage different segments of the network. Root guard ensures that changes in one segment do not unintentionally affect the overall spanning tree structure.
Interaction Between Root Guard and BPDU Messages
Bridge Protocol Data Units are essential for spanning tree operation. They carry information about bridge priority, root bridge identity, and path cost. Root guard specifically monitors these BPDU messages to determine whether a topology change should be allowed.
When a BPDU with a better root bridge value is received, root guard evaluates it as a potential threat to topology stability. Instead of accepting the new root bridge, the interface is placed into a blocking state. This prevents the BPDU from influencing the spanning tree calculation.
It is important to understand that root guard does not block all BPDU traffic. It only reacts to superior BPDU advertisements. Normal BPDU exchanges continue to occur, ensuring that the network remains aware of its environment.
Root Guard State Transitions in Network Operations
The behavior of the root guard can be understood through its state transitions. Under normal conditions, the interface remains in a forwarding state and participates fully in spanning tree operations.
When a superior BPDU is detected, the interface transitions into a root-inconsistent state. In this state, traffic forwarding is disabled, but BPDU monitoring continues. This ensures that the system can detect when conditions return to normal.
Once the superior BPDU is no longer present, the interface automatically returns to forwarding mode. This automatic recovery ensures minimal disruption and reduces administrative workload.
These state transitions are essential for maintaining both stability and responsiveness in dynamic network environments.
Common Misconfigurations in Root Guard Deployment
Although root guard is relatively simple to configure, incorrect deployment can lead to network issues. One common mistake is enabling root guard on trunk links between core switches. This can result in legitimate root bridge changes being blocked, causing network instability.
Another common issue is applying root guard on interfaces connected to devices that should participate in spanning tree calculations. This can lead to unintended blocking and connectivity loss.
Proper network design and planning are essential to avoid these issues. Root guard should only be applied on interfaces where external influence on root bridge selection is undesirable.
Monitoring Root Guard Activity in Live Networks
Monitoring is an important aspect of root guard management. Network administrators must regularly check interface status to ensure that root guard is functioning as expected.
When root guard is triggered, logs are generated indicating that a superior BPDU was received and the interface has been placed into a restricted state. These logs provide valuable information about potential misconfigurations or unauthorized devices in the network.
Monitoring tools can also help visualize root guard events across the network, making it easier to identify patterns and take corrective actions.
Root Guard in High-Availability Network Designs
In high-availability environments, network uptime is critical. Root guard contributes to high availability by preventing unnecessary topology changes that could disrupt service.
By locking down root bridge selection, it ensures that failover scenarios are predictable and controlled. This is particularly important in environments where redundancy is implemented across multiple network paths.
Without root guard, failover events could trigger unintended root bridge changes, leading to instability. With root guard in place, failover behavior remains consistent and reliable.
Combining Root Guard with Other Layer 2 Security Features
Root guard is often used in combination with other Layer 2 security features to provide comprehensive protection. While root guard protects the root bridge election process, other features handle different aspects of network security.
For example, BPDU guard protects edge ports from unauthorized BPDU reception, while loop guard helps prevent unidirectional link failures from causing loops. When used together, these features create a robust Layer 2 security framework.
This layered approach ensures that the network is protected from both accidental misconfigurations and intentional disruptions.
Impact of Root Guard on Network Performance Optimization
While root guard is primarily a security feature, it also has a positive impact on performance. By preventing unnecessary topology changes, it reduces convergence time and minimizes temporary disruptions in traffic flow.
Stable spanning tree topology ensures that data paths remain consistent, which improves latency and reduces packet loss. In large networks, even small improvements in convergence efficiency can have a significant impact on overall performance.
Root guard, therefore, contributes not only to security but also to operational efficiency.
Design Considerations for Root Guard Implementation
When designing a network that uses root guard, several factors must be considered. The placement of the root bridge must be carefully selected to ensure optimal traffic distribution. Once the root bridge is defined, root guard must be applied strategically to protect it.
Network segmentation also plays an important role. In segmented environments, different areas of the network may require different spanning tree configurations. Root guard helps enforce these boundaries by preventing cross-segment influence.
Proper documentation and planning are essential to ensure consistent deployment across the entire infrastructure.
Operational Reliability Achieved Through Root Guard
The primary benefit of root guard is operational reliability. By preventing unexpected changes in root bridge selection, it ensures that network behavior remains consistent over time.
This reliability is especially important in mission-critical environments where downtime is not acceptable. Root guard provides a simple yet effective mechanism to maintain control over network topology without requiring constant manual intervention.
Its ability to automatically recover from inconsistent states further enhances reliability and reduces administrative overhead.
Introduction to Advanced Root Guard Usage in Enterprise Networks
Root guard becomes most powerful when it is applied beyond basic configuration and used as part of a larger network design strategy. In real-world enterprise environments, networks are not static. Devices are added, moved, replaced, and sometimes misconfigured. These changes can introduce instability in the spanning tree topology if proper safeguards are not in place. Root guard plays a key role in ensuring that such changes do not disrupt the root bridge election process.
At an advanced level, root guard is not just a protection tool but a design control mechanism. It helps engineers enforce hierarchy, maintain predictable traffic flow, and ensure that spanning tree behavior remains aligned with the intended architecture. Understanding its deeper operational impact is essential for building stable, scalable networks.
Deep Behavior of Root Guard in Complex Topologies
In simple networks, the root guard operates in a straightforward manner by blocking superior BPDU advertisements. However, in complex multi-layered topologies, its behavior becomes more significant because multiple switching domains interact simultaneously.
When a superior BPDU is received on a root-guard-enabled interface, the switch does not immediately change global spanning tree decisions. Instead, it isolates the impact locally by placing only the affected interface into a root-inconsistent state. This ensures that instability does not propagate across the entire network.
Even in large-scale environments with redundant links and multiple VLANs, root guard maintains localized control. This isolation behavior is critical in preventing cascading topology changes that could otherwise lead to widespread convergence delays.
Root Guard and Network Convergence Stability
Network convergence refers to the process by which switches recalculate their spanning tree topology after a change occurs. In unstable networks, convergence can happen frequently, leading to delays and temporary traffic disruption.
Root guard improves convergence stability by eliminating one of the primary triggers of topology recalculation: root bridge changes. Since the root bridge is the foundation of spanning tree calculations, preventing its alteration ensures that the rest of the topology remains stable.
In environments where uptime is critical, reducing convergence events directly improves performance consistency. Applications that rely on continuous connectivity benefit significantly from this stability.
Troubleshooting Root Guard in Real Network Environments
Troubleshooting root guard requires understanding both its expected behavior and the conditions that trigger its activation. One of the most common indicators of root guard activity is a port entering a root-inconsistent state.
When this occurs, the first step is to identify the source of the superior BPDU. This usually involves checking connected switches for incorrect bridge priority settings or unexpected device insertion. Misconfigured switches are a common cause of root guard activation in enterprise environments.
Another important troubleshooting step is verifying network design assumptions. If root guard is blocking a legitimate switch, it may indicate that the intended root bridge hierarchy has not been properly configured. In such cases, reviewing spanning tree priorities across the network is necessary.
Logs and interface status outputs provide valuable insight into root guard events. These logs typically indicate when a superior BPDU was detected and which interface was affected. This information is essential for identifying the root cause of topology interference.
Common Root Guard Failure Scenarios and Their Causes
Although root guard itself is reliable, improper network design can lead to perceived failures. One common scenario occurs when root guard is enabled on a trunk link between core switches. In such cases, legitimate root bridge changes may be blocked, resulting in unexpected network behavior.
Another scenario involves the incorrect placement of the root guard on interfaces that connect to distribution switches. If these switches are expected to participate in the root bridge election, root guard may interfere with normal operations.
A third scenario involves inconsistent spanning tree configurations across VLANs. Since root bridge selection can vary per VLAN, misalignment in configuration can cause root guard to trigger unexpectedly.
Understanding these scenarios helps administrators distinguish between actual issues and expected root guard behavior.
Root Guard Optimization in Large-Scale Networks
Optimizing root guard deployment requires careful planning and segmentation. In large networks, not every interface requires root guard. It should be strategically applied where control over root bridge selection is necessary.
One optimization strategy involves defining a clear root bridge hierarchy before enabling root guard. This ensures that all switches agree on the intended topology structure. Once this hierarchy is established, root guard can be applied to enforce it.
Another optimization technique is combining root guard with consistent spanning tree mode across all switches. This ensures predictable behavior and reduces the likelihood of unexpected BPDU variations.
Proper VLAN segmentation also improves root guard efficiency. By isolating network segments, administrators can reduce the scope of spanning tree calculations and minimize unnecessary interactions between unrelated parts of the network.
Interaction Between Root Guard and Redundant Network Paths
Modern networks often include redundant links to improve reliability. While redundancy enhances availability, it also increases complexity in spanning tree operation.
Root guard plays a stabilizing role in such environments by ensuring that redundancy does not lead to root bridge conflicts. Even when multiple paths exist, root guard ensures that the root bridge remains unchanged unless explicitly modified.
This is particularly important in environments using link aggregation or multiple uplinks between switches. Without a root guard, redundant links could introduce unintended topology changes if bridge priorities are not carefully managed.
Root Guard in Multi-VLAN Environments
In networks that support multiple VLANs, the spanning tree operates independently for each VLAN. This means that root bridge selection can differ across VLANs depending on the configuration.
Root guard must be carefully applied in such environments to ensure that it aligns with VLAN-specific topology design. If applied incorrectly, it may block legitimate VLAN-specific root bridge changes.
Proper planning ensures that each VLAN maintains its intended root bridge while still benefiting from root guard protection. This allows for optimized traffic distribution across different network segments.
Design Strategy for Enterprise-Grade Root Guard Implementation
Enterprise network design requires a structured approach to root guard deployment. The first step is identifying the primary root bridge location, typically in the core layer of the network.
Once the root bridge is defined, root guard is applied to downstream interfaces to prevent external influence. This ensures that the root bridge remains stable regardless of changes in access layer devices.
Designers must also consider future scalability. As networks grow, additional switches may be introduced. Root guard configurations should be flexible enough to accommodate growth without requiring major redesign.
Documentation plays a key role in ensuring consistency. Clearly defined network diagrams and configuration standards help maintain alignment across different teams and locations.
Root Guard and Network Security Posture
Although root guard is not a traditional security feature like firewall filtering or access control lists, it plays an important role in maintaining network integrity. By preventing unauthorized topology changes, it indirectly strengthens overall network security.
In environments where physical access to network devices is not fully controlled, root guard helps protect against accidental or intentional misconfigurations. A rogue switch introduced into the network cannot easily disrupt the spanning tree hierarchy if root guard is properly deployed.
This contributes to a more resilient infrastructure that can withstand both operational errors and potential internal threats.
Performance Impact of Root Guard in High-Traffic Networks
Root guard has minimal direct impact on traffic performance under normal conditions. Since it only activates when a superior BPDU is detected, most of the time it operates silently in the background.
However, its indirect impact on performance is significant. By preventing unnecessary topology changes, it reduces network convergence events. This leads to more stable forwarding paths and consistent latency levels.
In high-traffic environments such as data centers, this stability is critical for maintaining application performance and user experience.
Best Practices for Long-Term Root Guard Maintenance
Maintaining root guard effectiveness requires ongoing monitoring and periodic review. As network topologies evolve, initial configuration decisions may need adjustment.
Regular audits help ensure that root guard is still applied correctly and that no unintended blocking is occurring. These audits should include verification of spanning tree roles, interface states, and BPDU activity logs.
Another best practice is aligning root guard configuration with overall network change management processes. Any addition or modification of switches should be evaluated for its impact on spanning tree behavior.
Root Guard in Evolving Network Architectures
Modern networks are increasingly moving toward hybrid and virtualized environments. Even in these advanced architectures, Layer 2 switching and spanning tree concepts remain relevant.
Root guard continues to play a role in these environments by ensuring that virtual switches and physical switches interact in a controlled manner. As networks become more dynamic, the importance of maintaining topology stability increases.
Its simplicity and effectiveness make Root Guard a long-lasting feature in network design, even as technologies evolve.
Conclusion
Root guard plays a foundational role in maintaining stability, predictability, and control within modern switched network environments. As networks continue to expand in size and complexity, the importance of safeguarding critical elements like the root bridge in spanning tree topologies becomes even more significant. Without mechanisms such as root guard, even a small misconfiguration or an unintended device connection can trigger widespread changes in network behavior, leading to instability, performance degradation, or temporary outages.
At its core, Root Guard is designed to preserve the intended structure of a Layer 2 network. The spanning tree protocol relies on a carefully selected root bridge to calculate optimal paths and prevent loops. When this root bridge is changed unexpectedly, the entire topology must recalculate its forwarding decisions. This process is not instantaneous and can result in noticeable disruption. Root guard eliminates this risk by ensuring that only authorized switches are capable of influencing root bridge selection. Any attempt by another switch to assume a superior role is immediately blocked at the interface level, keeping the network aligned with the original design.
One of the most valuable aspects of root guard is its simplicity in operation, combined with its powerful impact on stability. Once configured, it requires minimal ongoing intervention. The feature continuously monitors incoming bridge protocol messages and reacts only when necessary. This event-driven behavior ensures that the network remains efficient during normal operations while still being protected against unexpected topology changes. The automatic recovery mechanism further enhances its practicality, as interfaces return to normal operation once the inconsistent condition is resolved without requiring manual resets.
In real-world enterprise environments, this behavior translates into significant operational benefits. Network administrators are often responsible for managing large infrastructures with hundreds or thousands of interconnected devices. In such environments, the risk of human error or unauthorized device introduction is always present. Root guard acts as a safeguard layer that enforces design intent even when unexpected changes occur. This allows teams to focus on higher-level network optimization tasks rather than constantly troubleshooting spanning tree instability issues.
Another important benefit of root guard is its contribution to predictable network performance. Stability in spanning tree topology directly influences how efficiently data flows across the network. When the root bridge remains consistent, switches do not need to continuously recalculate paths. This reduces convergence events and helps maintain consistent latency across all connected devices. Applications that rely on real-time communication, such as voice, video, and financial systems, benefit greatly from this stability.
Root guard also plays an indirect but important role in network security. While it does not inspect data packets or block traffic based on content, it protects the structural integrity of the network. A compromised or misconfigured switch attempting to influence the spanning tree topology can cause significant disruption if left unchecked. By preventing such switches from becoming root bridges, root guard reduces the potential impact of internal misconfigurations or unauthorized devices. This makes it a valuable component of a broader network hardening strategy.
In hierarchical network designs, root guard helps enforce clear separation of responsibilities between different layers. Core switches are typically designated as the root bridge location, while distribution and access layer switches are configured to follow this hierarchy. By applying root guard on specific interfaces, administrators ensure that this structure cannot be unintentionally altered. This separation is essential for maintaining scalable and manageable network architectures, especially in large enterprise deployments.
Despite its advantages, effective use of root guard requires careful planning. Incorrect placement can lead to unintended consequences, such as blocking legitimate topology changes or disrupting expected redundancy behavior. For this reason, it is typically applied only on interfaces where root bridge influence must be strictly controlled. Understanding the network design and traffic flow is essential before enabling root guard in production environments. Proper documentation and topology mapping play a key role in ensuring correct deployment.
Another key aspect of root guard is its interaction with other spanning tree features. It is often used alongside mechanisms like BPDU guard and loop guard to create a multi-layered protection strategy. Each feature addresses a different aspect of spanning tree behavior, and when combined, they provide comprehensive control over Layer 2 network stability. Root guard specifically focuses on preventing root bridge changes, while other features handle edge protection and loop prevention. This layered approach ensures that the network is resilient against a wide range of potential issues.
From an operational perspective, monitoring root guard activity is an important part of network management. When root guard is triggered, it provides valuable insight into potential misconfigurations or unexpected device behavior. These events often serve as early warning signs that something in the network topology is not aligned with design expectations. By analyzing these events, administrators can proactively address underlying issues before they escalate into larger problems.
As networks continue to evolve toward more dynamic and hybrid architectures, the role of foundational Layer 2 protection mechanisms remains important. Even with advancements in virtualization and software-defined networking, spanning tree protocols are still widely used in many environments. Root guard continues to provide value by ensuring that these traditional switching environments remain stable and controlled. Its relevance persists because the fundamental challenge it addresses, maintaining consistent topology control, does not disappear with modernization.
In high-availability systems, root guard contributes to overall reliability by reducing unnecessary changes in network structure. Stability at the Layer 2 level supports higher-level redundancy mechanisms and failover systems. When the underlying switching topology remains predictable, failover events at higher layers can operate more efficiently. This improves overall system resilience and reduces the likelihood of cascading failures.
Ultimately, root guard is not just a technical feature but a design principle applied at the network edge. It represents the idea that control over critical infrastructure decisions should be intentional, not accidental. By enforcing this principle, root guard helps ensure that networks behave in a predictable, stable, and secure manner over time. Its simplicity, combined with its effectiveness, makes it an essential component in the toolkit of any network professional working with spanning tree-based environments.