Next-generation firewalls represent a significant shift in how network security is designed and enforced in modern enterprise environments. Traditional firewalls were primarily built around static rule sets that filtered traffic based on IP addresses, ports, and protocols. While effective in early network architectures, this approach became increasingly insufficient as applications moved to dynamic ports, cloud infrastructures expanded, and encrypted traffic became the dominant form of communication.
NGFW systems emerged to address these limitations by introducing deeper inspection capabilities that extend beyond basic packet filtering. Instead of treating traffic as simple network flows, NGFW platforms analyze the actual application behavior, user identity context, and content characteristics embedded within the traffic. This shift allows organizations to enforce security policies that are more aligned with how modern applications actually function.
Enterprise networks today are highly distributed, with users accessing resources from multiple environments including on-premises infrastructure, cloud platforms, remote locations, and mobile devices. This complexity introduces a larger attack surface, making visibility and control more challenging. NGFW systems help reduce this complexity by consolidating multiple security functions into a unified enforcement layer.
In addition to traditional firewall capabilities, NGFW platforms integrate intrusion prevention systems, application identification engines, malware detection mechanisms, and content filtering systems. This consolidation reduces the need for multiple standalone appliances and allows security teams to respond more efficiently to threats across the entire network ecosystem.
Modern Threat Landscape and the Need for Deep Traffic Inspection
The modern cybersecurity landscape is defined by increasingly sophisticated attack methods that bypass conventional perimeter defenses. Attackers frequently use encrypted channels, legitimate cloud services, and application-layer vulnerabilities to evade detection. As a result, visibility into network traffic has become one of the most critical requirements for enterprise security architectures.
A significant portion of modern network traffic is encrypted using protocols such as TLS. While encryption improves privacy and data integrity, it also creates blind spots for traditional inspection systems. Attackers often exploit these blind spots to embed malicious payloads within encrypted sessions. NGFW systems address this challenge by implementing SSL/TLS inspection capabilities that decrypt and analyze traffic in real time.
Another major challenge is the increasing use of application-layer evasion techniques. Malicious software may disguise itself as legitimate application traffic or use non-standard communication patterns to avoid detection. NGFW platforms counter this by identifying applications based on behavior rather than relying solely on port numbers or protocol signatures.
Additionally, enterprises face challenges related to insider threats and compromised user accounts. Traditional firewall models lack identity awareness, making it difficult to distinguish between legitimate and unauthorized user activity. NGFW systems incorporate identity-based controls to address this gap, enabling more precise policy enforcement.
Core Inspection Architecture in Next-Generation Firewalls
At the core of NGFW functionality is the inspection pipeline, which processes network traffic through multiple security engines. Unlike traditional firewalls that evaluate packets independently, NGFW systems apply a layered inspection approach that evaluates traffic across several dimensions simultaneously.
The inspection process typically includes application identification, user mapping, content analysis, threat detection, and policy enforcement. Each of these stages contributes to a more comprehensive understanding of network activity.
Application identification determines what type of application is generating traffic, regardless of port or encryption. User mapping associates traffic with authenticated identities. Content analysis inspects payloads for malicious patterns or sensitive data. Threat detection identifies known and unknown attack signatures. Policy enforcement determines whether traffic should be allowed or blocked based on organizational rules.
This multi-layered approach improves detection accuracy while reducing false positives. It also enables more granular control over network behavior, allowing organizations to define policies based on business context rather than static network parameters.
Palo Alto Networks NGFW Architectural Design and Processing Model
Palo Alto Networks NGFW systems are built around a unique processing architecture designed to optimize both security depth and performance efficiency. The platform uses a single-pass parallel processing model that allows traffic to be inspected once while simultaneously applying multiple security functions.
This approach reduces redundancy in packet handling and minimizes processing delays. Instead of passing traffic through separate inspection engines sequentially, all relevant security functions are applied in parallel during a single inspection cycle. This results in more consistent throughput and improved latency performance under high traffic loads.
The architecture is tightly integrated with a centralized policy engine that governs how traffic is handled across the network. Policies are not based on static network attributes but are instead driven by application behavior, user identity, and device context.
By shifting policy definition away from infrastructure-based parameters, the system enables more flexible and adaptive security enforcement. This is particularly important in dynamic environments where IP addresses and network locations frequently change.
Application-Centric Security Model and Traffic Classification
One of the defining characteristics of Palo Alto Networks NGFW systems is the application-centric security model. Instead of relying on ports and protocols, the system identifies applications through deep packet inspection and behavioral analysis.
This identification process allows the firewall to recognize applications even when they use non-standard ports or attempt to disguise their traffic patterns. Once an application is identified, it is classified into categories based on risk level, function, and behavior.
Policies can then be applied directly to application categories rather than network-level attributes. This enables more precise control over traffic, such as allowing collaboration tools while blocking high-risk file-sharing applications or restricting unknown application traffic entirely.
The application identification engine continuously updates its classification database using behavioral analysis and threat intelligence feeds. This ensures that emerging applications and evolving traffic patterns are quickly incorporated into the security model.
Identity-Based Policy Enforcement and User Context Integration
User identity plays a central role in modern NGFW policy enforcement. Palo Alto Networks integrates identity services that map network traffic to authenticated users, enabling policies to follow users across different devices and locations.
This identity mapping is typically achieved through integration with directory services and authentication systems. Once a user is identified, their network activity can be monitored and controlled based on organizational roles and access privileges.
Identity-based policies allow security teams to define access rules that are independent of IP addresses. This is particularly important in environments where users frequently switch between devices or connect from remote locations.
For example, access to sensitive applications can be restricted to specific user groups regardless of where they connect from. This reduces the risk of unauthorized access and helps enforce consistent security policies across distributed environments.
Device Awareness and Context-Driven Security Policies
In addition to user identity, device context is also an important factor in NGFW policy enforcement. Palo Alto Networks systems can classify devices based on their characteristics, including operating system type, device category, and compliance status.
Device awareness enables security policies to differentiate between trusted corporate devices and unmanaged or potentially risky endpoints. This allows organizations to apply stricter security controls to devices that do not meet compliance requirements.
Context-driven policies can also adapt dynamically based on device behavior. For example, if a device exhibits unusual activity patterns or connects from an unexpected location, additional security measures can be applied automatically.
This adaptive approach helps reduce the risk of lateral movement within the network and strengthens overall security posture in complex enterprise environments.
Threat Prevention and Content Inspection Mechanisms
Content inspection is a critical function of NGFW systems, enabling detection of malicious payloads and suspicious behavior within network traffic. Palo Alto Networks integrates multiple threat prevention engines that analyze traffic for different types of security risks.
These engines operate simultaneously to identify malware, exploit attempts, command-and-control communication, and data exfiltration behavior. By combining multiple detection methods, the system improves accuracy and reduces the likelihood of undetected threats.
Advanced inspection techniques include real-time analysis of file transfers, behavioral monitoring of network sessions, and signature-based detection of known attack patterns. This multi-layered approach provides comprehensive coverage against both known and emerging threats.
SSL/TLS decryption capabilities further enhance visibility by allowing encrypted traffic to be inspected without compromising performance efficiency. This is essential in modern environments where encrypted traffic constitutes a significant portion of overall network activity.
Traffic Intelligence and Policy Adaptation Mechanisms
NGFW systems rely heavily on continuous traffic intelligence to maintain effective security enforcement. Palo Alto Networks integrates dynamic threat intelligence feeds that update application classifications, threat signatures, and risk profiles in real time.
This continuous update process ensures that the firewall remains effective against evolving attack techniques. It also allows policies to adapt automatically based on new threat information and changing network behavior.
Machine learning techniques are increasingly used to enhance traffic analysis and anomaly detection. These systems can identify deviations from normal traffic patterns and flag potentially malicious activity even when no known signature exists.
Policy adaptation mechanisms ensure that security rules remain aligned with current network conditions. This reduces administrative overhead while maintaining a high level of security responsiveness.
Performance Optimization and Traffic Processing Efficiency
Performance is a critical consideration in NGFW deployment, particularly in high-throughput enterprise environments. Palo Alto Networks achieves performance optimization through its single-pass architecture, which minimizes redundant processing and reduces inspection latency.
Traffic is processed in a streamlined pipeline where multiple security functions are applied simultaneously. This ensures that inspection depth does not significantly impact throughput performance.
Hardware acceleration and optimized processing engines further enhance performance under heavy network loads. These optimizations allow the system to maintain consistent inspection capabilities even in high-density traffic environments.
The combination of architectural efficiency and intelligent processing design ensures that security enforcement does not become a bottleneck in network performance.
Fortinet NGFW Architecture and Security-Driven Design Philosophy
Fortinet’s next-generation firewall platform is built around a fundamentally different architectural philosophy compared to many software-centric firewall designs. At its core, Fortinet integrates hardware acceleration with deeply embedded security processing logic, allowing it to deliver high-throughput inspection while maintaining broad security functionality. This approach is centered on purpose-built security processors designed to handle specific types of network workloads efficiently, particularly in environments where traffic volume and latency sensitivity are both high.
The architecture is designed to distribute processing tasks across multiple specialized components rather than relying solely on general-purpose CPU processing. This includes dedicated acceleration for encryption and decryption tasks, intrusion detection workflows, and high-speed packet forwarding. By offloading these intensive operations, the system maintains consistent performance even when advanced security services are enabled simultaneously.
Fortinet’s design is also closely aligned with scalability requirements in enterprise and service provider environments. The platform supports deployment across a wide range of hardware models, from compact branch-level appliances to large-scale data center systems. This scalability is achieved through a consistent operating framework that ensures policy and configuration uniformity across different device classes.
A defining characteristic of this architecture is its emphasis on integrated security services. Instead of treating firewalling, intrusion prevention, and application control as separate modules, Fortinet embeds these functions into a unified processing pipeline. This reduces latency introduced by context switching between security engines and enhances visibility across all traffic flows.
Security Fabric Integration and Unified Threat Intelligence Model
A key differentiator in Fortinet’s NGFW ecosystem is the Security Fabric concept, which represents a unified security intelligence framework that connects multiple security components across an enterprise network. This model is designed to extend visibility beyond a single firewall instance and into a broader ecosystem of endpoints, cloud environments, and distributed network segments.
The Security Fabric operates as an interconnected intelligence-sharing system where security events detected in one part of the network can influence enforcement decisions elsewhere. This allows for coordinated response mechanisms that adapt dynamically to emerging threats. For example, if malicious behavior is detected at a remote endpoint, related firewall policies can automatically adjust to restrict associated traffic patterns across the network.
This interconnected model enhances situational awareness by correlating data from multiple security layers. It enables administrators to gain a more comprehensive understanding of attack paths, lateral movement attempts, and persistent threat behaviors. The result is a more proactive security posture that reduces response time and improves containment efficiency.
The Security Fabric also extends into third-party integrations, allowing interoperability with external security tools and cloud platforms. This creates a broader security ecosystem where intelligence is continuously shared and updated across different environments. Such integration is particularly important in hybrid infrastructures where workloads are distributed across multiple platforms and service providers.
Hyperscale Security and High-Throughput Network Processing
Fortinet’s NGFW systems are engineered to support hyperscale environments where traffic volume can reach extremely high levels without compromising security inspection depth. This is achieved through a combination of hardware acceleration, optimized packet processing pipelines, and parallel execution of security functions.
Hyperscale security design focuses on maintaining consistent throughput regardless of the number of active security features. This is particularly important in enterprise environments where multiple services such as intrusion prevention, web filtering, and application control must operate simultaneously.
The architecture distributes workloads across multiple processing units, allowing traffic to be handled in parallel rather than sequentially. This reduces bottlenecks and ensures that latency remains stable even under heavy network load conditions. The system is also designed to handle burst traffic scenarios where sudden spikes in network activity occur.
Another key aspect of hyperscale design is efficient encryption handling. As encrypted traffic becomes more prevalent, NGFW systems must inspect SSL/TLS sessions without introducing significant performance degradation. Fortinet addresses this through hardware-assisted cryptographic processing, which significantly reduces the overhead associated with encryption and decryption tasks.
Intrusion Prevention System and Advanced Threat Detection Capabilities
The intrusion prevention system integrated within Fortinet NGFW platforms plays a central role in detecting and mitigating network-based attacks. This system analyzes traffic patterns in real time to identify exploit attempts, malicious payloads, and abnormal protocol behavior.
Unlike traditional signature-based detection systems that rely solely on known attack patterns, Fortinet’s IPS incorporates behavioral analysis techniques that allow it to identify previously unseen attack vectors. This is particularly important in defending against zero-day exploits and polymorphic malware that constantly change their signatures.
The IPS engine operates directly within the traffic processing pipeline, allowing threats to be identified and mitigated before they reach their target systems. This inline deployment model ensures immediate response capabilities without requiring additional traffic rerouting or external analysis systems.
Advanced detection capabilities include anomaly-based monitoring, protocol validation, and contextual analysis of network sessions. These mechanisms work together to provide a multi-layered defense system that reduces false positives while maintaining high detection accuracy.
Application Control and Traffic Classification Mechanisms
Application control is a core function of Fortinet NGFW systems, enabling granular visibility and enforcement over application-layer traffic. The system identifies applications based on behavioral signatures, protocol analysis, and contextual metadata rather than relying solely on port numbers.
This allows the firewall to accurately classify applications even when they use encrypted channels or non-standard communication methods. Once identified, applications are categorized based on risk level, business relevance, and security posture.
Policies can then be applied to allow, restrict, or monitor application usage based on organizational requirements. This enables security teams to enforce acceptable use policies while maintaining operational flexibility for business-critical applications.
Application control is continuously updated through threat intelligence feeds and behavioral learning systems. This ensures that new applications and evolving usage patterns are quickly incorporated into the classification framework.
Integrated Proxy Architecture and Secure Traffic Mediation
Fortinet NGFW systems incorporate a native proxy architecture that enables secure mediation of network traffic between clients and external resources. This architecture provides an additional layer of inspection by fully terminating and re-establishing sessions at the firewall level.
The proxy model allows deeper inspection of application-layer content, including HTTP, HTTPS, and other protocol-based communications. It also enables advanced filtering capabilities that can identify malicious payloads embedded within legitimate application traffic.
This approach enhances security by isolating internal network resources from direct exposure to external threats. It also allows for more granular control over session behavior, including authentication enforcement, content filtering, and traffic shaping.
The proxy architecture is tightly integrated with other security services, ensuring that inspection results are correlated across multiple detection engines. This unified approach improves threat detection accuracy and reduces gaps in visibility.
Zero Trust Network Access and Identity-Centric Security Enforcement
Fortinet NGFW platforms increasingly incorporate Zero Trust principles into their security model, emphasizing strict identity verification and continuous access validation. This approach assumes that no user or device should be trusted by default, regardless of network location.
Identity-centric enforcement ensures that access decisions are based on verified user credentials, device posture, and contextual risk factors. This allows organizations to enforce adaptive access controls that adjust dynamically based on security conditions.
Zero Trust Network Access capabilities extend security enforcement beyond traditional perimeter boundaries. Users accessing resources from remote locations are subject to the same policy enforcement mechanisms as those within the internal network.
This model significantly reduces the risk of unauthorized access and lateral movement within enterprise environments. It also enhances visibility into user activity across distributed infrastructure components.
Automation-Driven Network Management and Operational Efficiency
Operational efficiency is a critical requirement in large-scale NGFW deployments, particularly in environments where network complexity continues to increase. Fortinet addresses this challenge through automation-driven management capabilities that streamline configuration, monitoring, and response workflows.
Centralized management systems allow administrators to define policies that are automatically propagated across multiple devices and network segments. This reduces manual configuration overhead and ensures consistency across the security infrastructure.
Automation capabilities also extend to threat response mechanisms. When suspicious activity is detected, predefined automated actions can be triggered to contain or mitigate the threat without requiring manual intervention.
This approach improves response time and reduces the risk of human error in critical security situations. It also allows security teams to focus on higher-level strategic tasks rather than routine operational management.
FortiGuard Intelligence and Real-Time Security Updates
Fortinet NGFW systems rely heavily on continuous intelligence updates delivered through a global threat intelligence framework. This system aggregates data from multiple sources to provide real-time updates on emerging threats, vulnerabilities, and attack techniques.
The intelligence framework supports multiple security functions including intrusion prevention, web filtering, malware detection, and application control. Updates are distributed continuously to ensure that security policies remain aligned with current threat landscapes.
Machine learning and behavioral analytics are also used to enhance detection capabilities. These systems analyze large volumes of network data to identify patterns associated with malicious activity, enabling proactive threat mitigation.
The integration of real-time intelligence ensures that the firewall remains adaptive in dynamic environments where attack methods evolve rapidly.
Performance Optimization Through Hardware Acceleration and Parallel Processing
Performance optimization in Fortinet NGFW systems is achieved through a combination of hardware acceleration and parallel processing techniques. Dedicated security processors handle specific workloads such as encryption, deep packet inspection, and traffic forwarding.
This division of processing responsibilities allows the system to maintain high throughput even when multiple security services are active simultaneously. It also reduces CPU utilization on general-purpose processing units, improving overall system efficiency.
Parallel processing ensures that multiple traffic streams can be analyzed simultaneously without introducing significant latency. This is particularly important in high-density environments such as data centers and service provider networks.
The combination of hardware and software optimization provides a balanced approach to performance and security depth, enabling consistent operation under demanding network conditions.
Performance Engineering and Real-World Throughput Behavior in NGFW Environments
In large-scale enterprise security deployments, performance is not just a benchmark figure but a continuous operational requirement that determines whether security controls can be enforced without degrading application experience. Next-generation firewalls must handle simultaneous workloads such as intrusion inspection, SSL/TLS decryption, application classification, and user identity mapping while sustaining predictable throughput under varying traffic conditions.
Performance engineering in NGFW platforms is therefore deeply tied to architectural decisions. Systems that rely heavily on sequential processing pipelines often face bottlenecks when multiple security features are enabled simultaneously. In contrast, architectures that support parallel processing or hardware offloading can maintain more stable performance curves under load.
In enterprise environments, traffic is rarely uniform. Bursts of activity occur during peak business hours, cloud synchronization events, or distributed application updates. NGFW systems must absorb these fluctuations without introducing latency spikes or packet drops. This requirement places emphasis on internal buffering mechanisms, efficient session tracking, and optimized packet scheduling algorithms.
A critical aspect of performance behavior is encrypted traffic handling. As the majority of modern traffic is encrypted, NGFW systems must perform SSL/TLS decryption and inspection without significantly increasing processing overhead. Efficient cryptographic acceleration becomes essential in maintaining throughput stability, especially in environments where deep inspection policies are enabled across most traffic flows.
Another performance consideration is session persistence. NGFW systems must track large numbers of concurrent sessions while maintaining state information for each connection. This includes application context, user identity mapping, and threat inspection results. Efficient session table management is crucial to prevent memory exhaustion and ensure consistent response times.
Security Intelligence Correlation and Multi-Layer Threat Analysis
Modern NGFW platforms do not rely on a single detection mechanism to identify threats. Instead, they use multi-layered intelligence correlation, where data from different inspection engines is combined to form a unified threat assessment. This approach significantly improves detection accuracy and reduces false positives.
At the core of this model is the correlation between application behavior, network traffic patterns, and content inspection results. When these data points are analyzed together, the system can distinguish between legitimate application anomalies and malicious activity more effectively.
Threat intelligence correlation also extends across time. NGFW systems often maintain historical traffic data to identify slow-moving attacks that may not be immediately detectable through real-time inspection alone. This includes reconnaissance activities, low-and-slow data exfiltration attempts, and multi-stage intrusion campaigns.
Machine learning models further enhance this capability by identifying deviations from established baseline behavior. These models are trained on large datasets of network traffic patterns and continuously updated with new threat intelligence. As a result, they can detect previously unknown attack techniques without relying solely on signature databases.
Behavioral correlation is particularly important in identifying advanced persistent threats, where attackers attempt to blend into normal network activity. By analyzing long-term patterns and cross-referencing multiple security signals, NGFW systems can identify subtle indicators of compromise.
Advanced Encryption Handling and SSL/TLS Inspection Strategies
Encryption has become both a security necessity and a visibility challenge. While SSL/TLS protocols protect data integrity and confidentiality, they also obscure payload content from traditional inspection systems. NGFW platforms must therefore implement advanced decryption strategies to maintain visibility without degrading performance.
SSL/TLS inspection typically involves intercepting encrypted sessions, decrypting them for analysis, and then re-encrypting traffic before forwarding it to its destination. This process requires significant computational resources and must be carefully optimized to avoid introducing latency.
Hardware acceleration plays a key role in enabling scalable decryption. Dedicated cryptographic processors handle encryption and decryption tasks more efficiently than general-purpose CPUs, allowing NGFW systems to inspect large volumes of encrypted traffic simultaneously.
Policy-based decryption controls are also essential. Not all traffic should be decrypted due to privacy, compliance, or performance considerations. NGFW systems allow administrators to define granular rules that determine which traffic categories are subject to inspection and which are exempt.
Advanced inspection techniques may also include certificate validation, session re-establishment, and selective decryption based on risk scoring. These methods help balance security visibility with operational efficiency.
Application Layer Security and Behavioral Traffic Classification
Application-layer security has become one of the most critical components of modern NGFW design. Unlike traditional firewall models that rely on static port definitions, application-layer classification analyzes actual traffic behavior to determine the true nature of network communication.
Behavioral classification examines how applications interact with network resources, including request patterns, payload structures, and session characteristics. This allows NGFW systems to identify applications even when they attempt to disguise their traffic or use non-standard communication methods.
Once an application is identified, it is evaluated based on its risk profile. High-risk applications may include file-sharing platforms, anonymization services, or unknown protocols that do not match established behavioral signatures.
Policy enforcement at the application layer enables organizations to control how specific applications are used within the network. This includes allowing partial functionality, restricting certain features, or blocking applications entirely based on security requirements.
Behavioral classification also plays a role in detecting malicious applications that mimic legitimate software. By analyzing deviations in expected behavior, NGFW systems can identify compromised or rogue applications attempting to bypass security controls.
Identity-Aware Security Models and Contextual Access Enforcement
Identity-aware security represents a fundamental shift from infrastructure-based control to user-centric enforcement. In NGFW environments, identity is used as a primary factor in determining access permissions and policy application.
User identity is typically established through authentication systems and directory services. Once authenticated, user activity is tracked across all network sessions, regardless of device or location.
This identity mapping allows security policies to follow users dynamically. For example, a user accessing the network from a corporate device will have the same security policy applied when connecting remotely from a personal device, provided authentication is verified.
Contextual enforcement further enhances this model by incorporating additional factors such as device posture, geographic location, and behavioral risk scoring. This allows policies to adapt dynamically based on current risk conditions.
Identity-aware security significantly reduces the risk of unauthorized access and improves visibility into user behavior across distributed environments. It also simplifies policy management by reducing reliance on static IP-based rules.
Enterprise Deployment Models and Network Segmentation Strategies
NGFW systems are deployed across a variety of enterprise environments, each with unique segmentation and security requirements. Common deployment models include perimeter protection, internal segmentation, and cloud-native security enforcement.
Perimeter deployment focuses on protecting the boundary between internal networks and external internet traffic. This remains a foundational use case, although modern architectures extend far beyond traditional perimeter models.
Internal segmentation involves dividing enterprise networks into smaller security zones. This reduces lateral movement opportunities for attackers and limits the impact of compromised systems. NGFW systems enforce segmentation policies by controlling traffic flow between these zones.
Cloud-native deployments extend NGFW capabilities into virtualized and containerized environments. This allows consistent security policies to be applied across hybrid infrastructures that span on-premises and cloud platforms.
Each deployment model requires careful consideration of traffic flow, policy consistency, and integration with existing network architecture. NGFW systems must maintain uniform enforcement while adapting to different operational contexts.
Scalability Challenges and Distributed Security Enforcement
Scalability is a key requirement for NGFW systems operating in large enterprise or service provider environments. As network traffic increases, security systems must scale without introducing bottlenecks or compromising inspection depth.
Distributed enforcement models allow security workloads to be spread across multiple devices or nodes. This ensures that no single system becomes a performance bottleneck. It also improves redundancy and fault tolerance within the security infrastructure.
Load balancing mechanisms are often used to distribute traffic across multiple NGFW instances. These mechanisms ensure that traffic is processed efficiently while maintaining session consistency.
Scalability also involves efficient management of policy synchronization across distributed systems. Security rules must remain consistent across all enforcement points to avoid policy gaps or misconfigurations.
Cloud-based management platforms are increasingly used to centralize control over distributed NGFW deployments. This enables unified policy management and real-time visibility across geographically dispersed networks.
Operational Visibility and Security Analytics Integration
Operational visibility is essential for understanding network behavior and identifying security incidents. NGFW systems provide detailed analytics that cover application usage, user activity, threat detection, and traffic patterns.
Security analytics platforms aggregate this data to provide actionable insights into network behavior. This includes identifying abnormal traffic spikes, detecting unauthorized access attempts, and tracking long-term security trends.
Visualization of security data allows administrators to quickly interpret complex network activity. This improves incident response time and enhances situational awareness across the organization.
Integration with external analytics systems further extends visibility by correlating firewall data with endpoint telemetry, cloud logs, and external threat intelligence sources.
This holistic approach enables more accurate threat detection and improves overall security decision-making processes.
Comparative Engineering Perspectives Between NGFW Platforms
When analyzing NGFW platforms from an engineering perspective, differences in design philosophy become evident in how performance, scalability, and security depth are balanced.
Some architectures prioritize streamlined packet processing with minimal redundancy, focusing on consistent throughput and reduced latency. Others emphasize hardware acceleration and distributed processing to maximize performance under large-scale deployments.
Security depth also varies depending on how inspection engines are integrated. Some systems use tightly coupled inspection pipelines, while others rely on modular architectures where security functions operate semi-independently.
These design decisions influence how each platform behaves under real-world conditions, particularly in environments with heavy encryption, high application diversity, and dynamic user populations.
Ultimately, NGFW effectiveness is determined not by a single feature set but by how well architecture, intelligence, and performance engineering align with enterprise operational requirements.
Conclusion
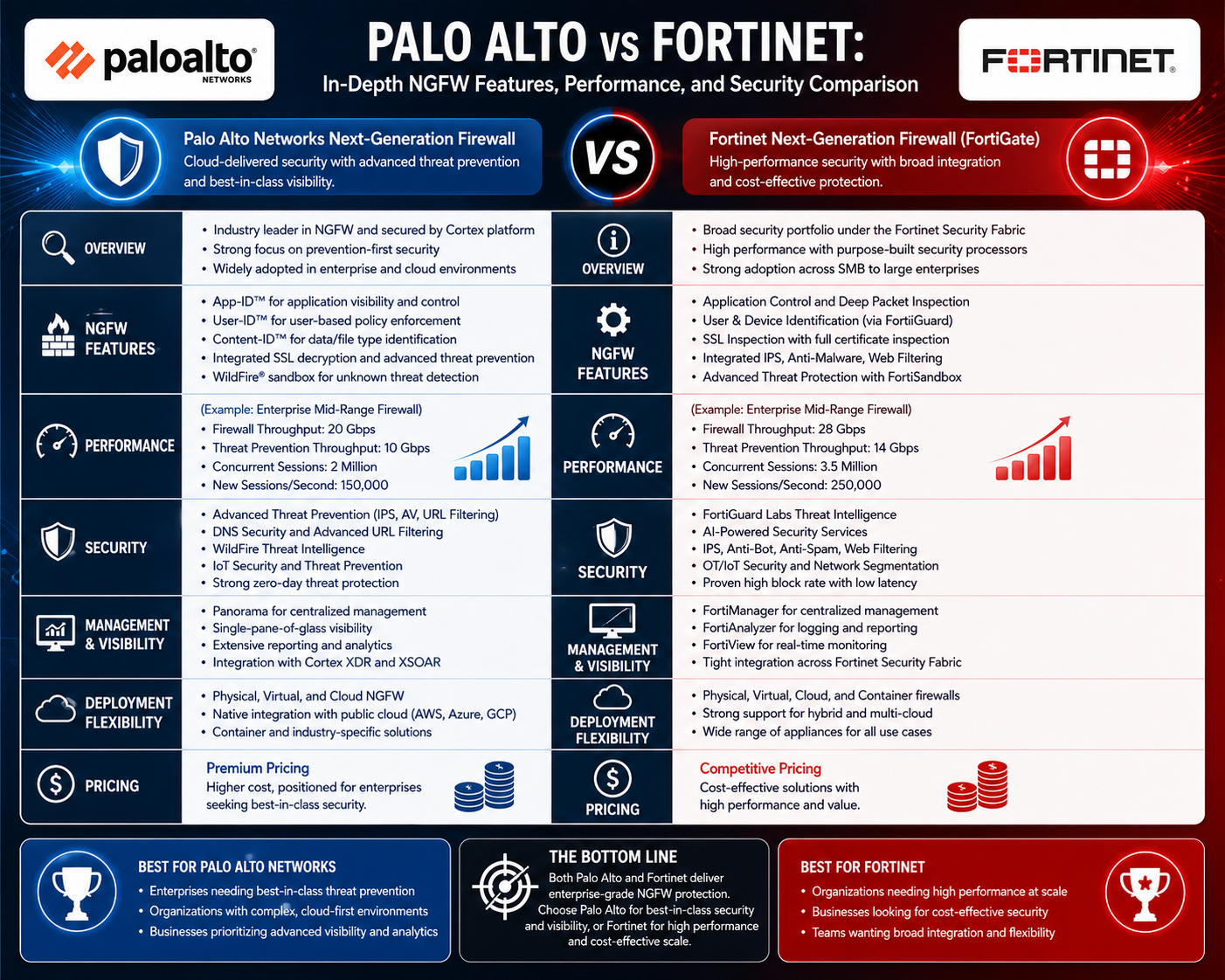
The comparison between Palo Alto Networks and Fortinet in the next-generation firewall landscape ultimately reflects two mature but distinctly engineered approaches to enterprise network security. Both platforms have reached a level of sophistication where they are capable of handling modern threats such as encrypted malware delivery, lateral movement inside enterprise networks, application-layer exploitation, and cloud-based attack surfaces. However, the way each system achieves these outcomes is shaped by different architectural priorities, operational philosophies, and optimization strategies.
At a broad level, NGFW technology has moved far beyond simple packet filtering and port-based control. Modern deployments require deep inspection of application behavior, user identity awareness, device-level context, and continuous threat intelligence integration. This shift has made firewall selection less about basic security capability and more about how efficiently a system can process complex security functions at scale while maintaining predictable performance. Both Palo Alto and Fortinet address these demands, but they differ in how they balance security depth with throughput efficiency.
Palo Alto Networks is often associated with a software-driven, intelligence-centric model where security decisions are tightly integrated with application identification, user mapping, and content inspection. The emphasis is on unified visibility and consistent policy enforcement through a streamlined processing approach. Its single-pass inspection concept is designed to reduce redundancy by analyzing traffic once and applying multiple security functions simultaneously. This model is particularly effective in environments where granular application control and identity-based policies are prioritized over raw hardware acceleration.
Fortinet, on the other hand, builds its NGFW ecosystem around a performance-optimized architecture that leverages specialized hardware acceleration alongside a tightly integrated security framework. The focus is on scalability and throughput efficiency, especially in distributed environments where traffic volumes can fluctuate significantly. Its design philosophy is more hardware-centric, enabling high-speed processing of encrypted traffic, intrusion detection, and application control without requiring extensive trade-offs in performance.
From a security functionality perspective, both platforms provide comparable core capabilities, including intrusion prevention systems, SSL/TLS inspection, application awareness, malware protection, and web filtering. However, the way these capabilities are implemented and integrated into the broader architecture differs. Palo Alto tends to emphasize contextual intelligence, where user identity, application behavior, and content analysis are tightly correlated to form policy decisions. Fortinet emphasizes coordinated security enforcement through its integrated ecosystem approach, where multiple security components share intelligence and respond collectively to threats.
Performance behavior is another key differentiator. In real-world enterprise environments, firewalls must handle sustained traffic loads as well as sudden spikes in demand. Palo Alto’s processing model aims for consistent latency control by minimizing redundant inspection stages, which can be advantageous in environments requiring stable application performance and predictable user experience. Fortinet’s approach focuses on maximizing throughput through parallel processing and hardware acceleration, which often results in strong performance under high-volume traffic conditions, particularly in large-scale deployments.
Security effectiveness is not solely determined by throughput or feature count but by how well the system can detect and prevent modern attack techniques. Both platforms incorporate advanced threat intelligence, machine learning-based detection, and behavioral analysis techniques to identify unknown threats. Palo Alto’s strength lies in its application-level visibility and identity-driven enforcement, which can provide precise control in complex enterprise environments. Fortinet’s strength lies in its ability to rapidly process large volumes of traffic while maintaining integrated threat detection across its Security Fabric ecosystem.
Another important consideration is operational complexity and management overhead. NGFW systems are not only security enforcement points but also operational platforms that require continuous monitoring, policy tuning, and incident response integration. Palo Alto environments are often recognized for their detailed visibility and structured policy framework, which can support highly granular control but may require more careful policy design. Fortinet environments, through centralized management and automation capabilities, aim to simplify large-scale operations by reducing manual intervention and enabling coordinated policy distribution across multiple security layers.
Scalability also plays a major role in enterprise decision-making. Organizations with distributed networks, multiple branch offices, and hybrid cloud deployments require firewall systems that can scale horizontally and maintain consistent policy enforcement across different environments. Fortinet’s architecture is often aligned with these requirements due to its emphasis on distributed security processing and integrated ecosystem connectivity. Palo Alto also supports large-scale deployments but typically focuses more on centralized intelligence and consistent policy enforcement across unified environments.
In terms of long-term strategic adoption, enterprises often evaluate how well each platform aligns with future infrastructure trends. As cloud adoption increases and network boundaries become less defined, security models are shifting toward identity-centric and application-aware frameworks. Both platforms are evolving in this direction, incorporating zero trust principles, cloud-native integrations, and advanced analytics capabilities. However, their implementation strategies differ based on their foundational architectures.
Cost considerations also influence deployment decisions, particularly in large-scale environments. NGFW solutions vary widely in pricing depending on throughput requirements, feature sets, and hardware configurations. Organizations often evaluate not just initial acquisition cost but total cost of ownership, including maintenance, scaling, licensing, and operational overhead. In general, environments prioritizing high performance at lower entry cost may lean toward one approach, while those prioritizing deep inspection and advanced analytics may justify higher investment in more feature-rich systems.
Ultimately, the selection between these platforms is not a matter of superiority but of alignment with specific enterprise requirements. Organizations with complex application ecosystems, strict identity-based access control requirements, and a need for deep visibility into user and application behavior may find one approach more suitable. Conversely, environments requiring high throughput, broad scalability, and integrated security across distributed infrastructure may favor the alternative.
What becomes clear in modern cybersecurity architecture is that NGFW platforms are no longer isolated security tools. They are foundational components of enterprise digital infrastructure, influencing how traffic is inspected, how policies are enforced, and how threats are detected and mitigated across hybrid environments. The evolution of both Palo Alto Networks and Fortinet demonstrates how firewall technology has shifted toward intelligent, adaptive, and deeply integrated security systems capable of operating at the scale and complexity of modern networks.
As threats continue to evolve in sophistication, the role of NGFW systems will increasingly depend on their ability to combine real-time intelligence, behavioral analysis, and scalable performance. Both platforms represent mature responses to this challenge, each optimized for different operational priorities but ultimately contributing to the same objective: maintaining secure, visible, and controllable enterprise networks in an environment where traditional boundaries no longer exist.