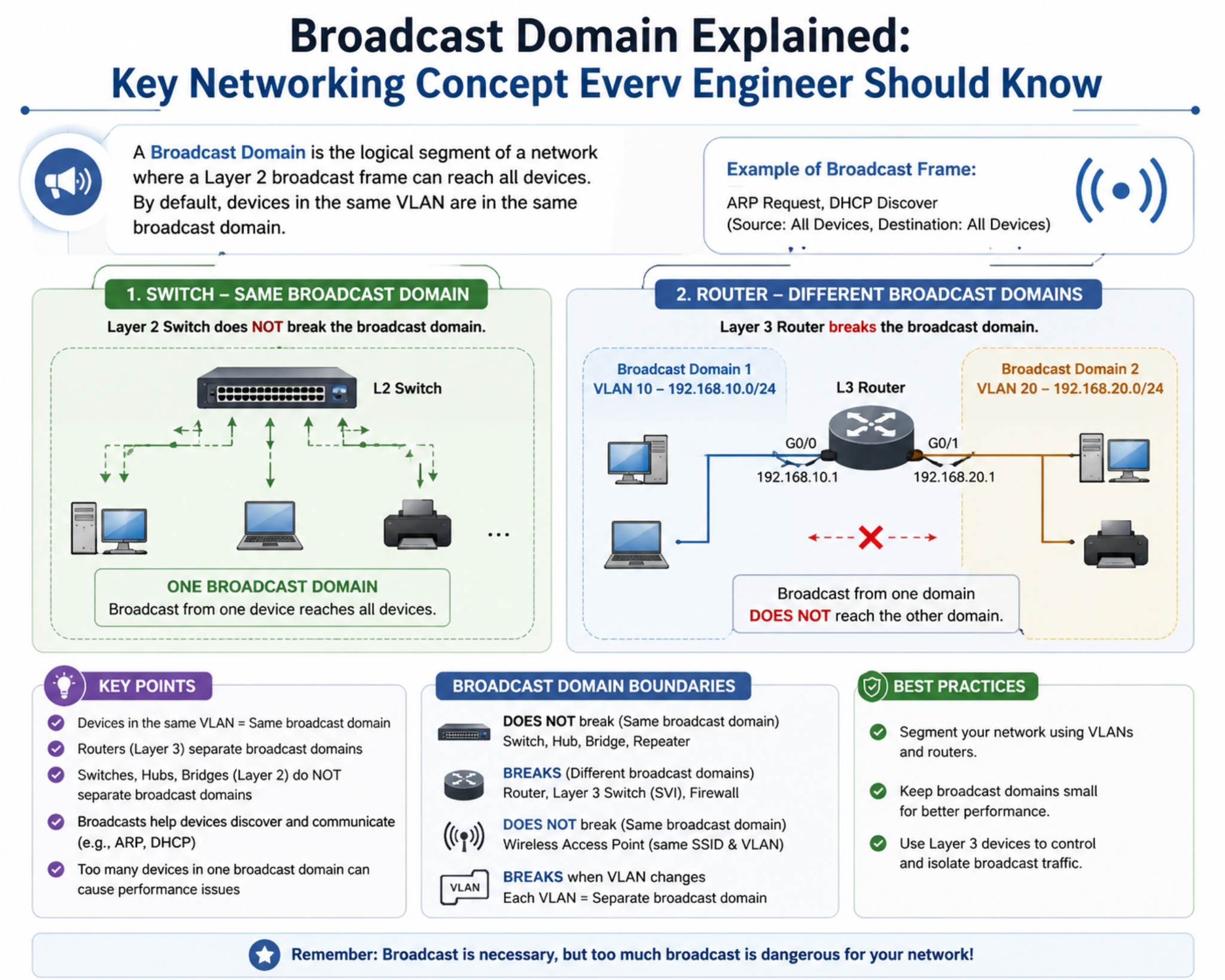
A broadcast domain is a logical division within a computer network where any broadcast frame transmitted by a device is received by all other devices within the same boundary. This concept exists at the data link layer of the OSI model and is essential for understanding how local network communication behaves. In practical terms, a broadcast domain defines the reach of broadcast traffic, meaning it determines which devices will process a broadcast message and which will ignore it due to being outside the defined boundary.
In networking environments, devices rarely communicate in isolation. Instead, they exist within interconnected systems where data must be exchanged efficiently. Broadcast domains help organize this communication by limiting how far broadcast traffic can travel. Without such boundaries, broadcast messages would propagate across entire networks, leading to unnecessary processing overhead and degraded performance. By restricting broadcast scope, networks maintain structure, efficiency, and control over data flow.
A broadcast domain is not defined by physical distance but rather by logical configuration. Devices connected to the same switching infrastructure or virtual network segment typically belong to the same broadcast domain unless segmentation techniques are applied. This logical grouping ensures that broadcast traffic remains confined to relevant devices while preventing unnecessary distribution across unrelated systems.
Layer 2 Switching and Its Role in Broadcast Domains
Layer 2 switching is a core mechanism that governs how broadcast domains function in modern networks. Operating at the data link layer, Layer 2 switches are responsible for forwarding frames based on MAC addresses rather than IP addresses. Each device connected to a switch has a unique MAC address assigned to its network interface, and the switch uses these addresses to determine where traffic should be delivered.
Unlike older networking devices such as hubs, which blindly broadcast all incoming traffic to every connected port, Layer 2 switches intelligently manage data flow. They examine the MAC address of incoming frames and consult an internal MAC address table to determine the appropriate forwarding path. This allows switches to send data only to the intended recipient device, significantly reducing unnecessary traffic within the network.
However, broadcast frames are treated differently. When a switch receives a broadcast frame, it forwards the frame to all ports within the same broadcast domain. This ensures that every device in that domain receives the message. The switch does not attempt to restrict broadcast traffic at this stage because broadcast communication is designed to reach all devices within a logical network segment.
Layer 2 switches therefore play a dual role in broadcast domains. They intelligently control unicast traffic while allowing controlled distribution of broadcast traffic within defined boundaries. This balance is essential for maintaining efficient communication in local networks.
MAC Address Structure and Network Identification
The MAC address is a fundamental component of Layer 2 networking and plays a critical role in broadcast domain behavior. Every network interface card is assigned a unique MAC address, typically represented in hexadecimal format such as ac:de:48:00:11:22. This address acts as a hardware-level identifier that distinguishes each device on a local network.
Unlike IP addresses, which can change depending on network configuration, MAC addresses are generally permanent and embedded into hardware by the manufacturer. This permanence allows switches to reliably identify devices within a broadcast domain and maintain consistent forwarding behavior.
When a device sends a frame, it includes both source and destination MAC addresses. The switch uses this information to determine how the frame should be handled. If the destination MAC address is known and present in the switch’s MAC address table, the frame is forwarded directly to the appropriate port. If the destination is unknown, the switch must flood the frame to all ports within the same broadcast domain until the destination responds.
This process ensures that communication can still occur even when devices are newly connected or their MAC addresses are not yet learned by the switch. Over time, as communication continues, the switch builds a complete map of MAC addresses and associated ports, improving forwarding efficiency.
MAC Address Learning and Forwarding Logic in Broadcast Domains
MAC address learning is a dynamic process that allows switches to adapt to changing network conditions. When a switch receives a frame, it first examines the source MAC address and records it in its MAC address table along with the port on which it was received. This information allows the switch to identify where devices are located within the network topology.
As more frames are received, the switch continuously updates its MAC address table. This learning process enables the switch to make increasingly accurate forwarding decisions. When a destination MAC address is known, the switch forwards the frame only to the specific port associated with that address. This reduces unnecessary traffic and ensures efficient communication within the broadcast domain.
If a destination MAC address is not found in the table, the switch assumes that the device may be unknown or recently connected. In such cases, it floods the frame across all ports within the same broadcast domain. This flooding mechanism ensures that the frame reaches its destination even in the absence of prior knowledge.
Over time, this process becomes highly efficient as the switch learns the location of all active devices. The MAC address table is continuously updated, and outdated entries are removed after a period of inactivity. This ensures that the switch maintains an accurate representation of the network at all times.
Broadcast Frame Structure and Communication Behavior
Broadcast frames are a special category of network communication designed to reach all devices within a broadcast domain. These frames use a specific destination MAC address known as ff:ff:ff:ff:ff:ff, which signals that the frame should be delivered to every device in the local segment.
When a switch receives a broadcast frame, it does not consult its MAC address table for forwarding decisions. Instead, it immediately replicates the frame and sends it out through all active ports within the same broadcast domain. Each device that receives the frame processes it independently, regardless of whether the message is relevant to its operation.
This behavior is essential for several foundational network functions. Many protocols rely on broadcast communication to discover devices, request configuration information, or announce services. Without broadcast capability, these processes would require more complex and less efficient communication methods.
However, broadcast traffic must be carefully managed because every device in the broadcast domain is required to process it. As the number of devices increases, the cumulative processing load also increases, which can impact performance.
Broadcast Domains and Network Traffic Containment
One of the primary purposes of broadcast domains is to contain broadcast traffic within a defined boundary. Without such containment, broadcast frames could propagate across entire networks, consuming bandwidth and reducing efficiency.
By limiting broadcast scope, networks ensure that only relevant devices process broadcast traffic. This reduces unnecessary workload on devices that do not need to receive the information. Containment also improves overall network stability by preventing excessive traffic from spreading uncontrollably.
Broadcast containment is achieved through switching logic, network design, and segmentation techniques. Layer 2 switches enforce broadcast boundaries by forwarding broadcast frames only within the same local segment. Routers further enforce separation by not forwarding broadcast traffic between different network interfaces.
This layered containment model ensures that broadcast traffic remains localized while still supporting essential communication functions within each segment.
Importance of Broadcast Domains in Network Efficiency
Broadcast domains have a direct impact on network efficiency. In smaller broadcast domains, fewer devices are required to process broadcast traffic, which reduces CPU usage and improves overall performance. In larger broadcast domains, however, every device must process a higher volume of broadcast frames, which can lead to inefficiencies.
As network size increases, uncontrolled broadcast traffic can become a significant performance bottleneck. This is why broadcast domain design is a critical aspect of network architecture. By dividing large networks into smaller broadcast domains, administrators can ensure that traffic remains manageable and efficient.
Efficient broadcast domain design also improves bandwidth utilization. Instead of being consumed by unnecessary broadcast traffic, bandwidth can be allocated to meaningful data transmission. This leads to better application performance and reduced latency across the network.
Additionally, smaller broadcast domains simplify troubleshooting and network management. When issues arise, administrators can isolate problems to specific segments rather than analyzing the entire network.
Broadcast Domains as a Foundation for Scalable Networking
Broadcast domains form a foundational concept in scalable network design. As networks grow in size and complexity, proper segmentation becomes essential for maintaining performance and reliability.
Scalable networks rely on dividing broadcast domains into logical segments that can operate independently. This allows networks to expand without increasing broadcast-related overhead. Each segment can be optimized individually based on its specific requirements.
Modern networking architectures often combine multiple technologies to manage broadcast domains effectively. These include switching, routing, virtualization, and software-defined networking. Together, these technologies ensure that broadcast traffic remains controlled even in highly complex environments.
Broadcast domain design is therefore not just a technical detail but a fundamental principle of network engineering. It ensures that communication remains efficient, structured, and scalable across all types of network environments.
VLAN Architecture and Logical Broadcast Domain Segmentation
Virtual Local Area Networks, commonly known as VLANs, represent one of the most important mechanisms for controlling and segmenting broadcast domains in modern computer networks. A VLAN is a logical construct that allows a single physical switching infrastructure to be divided into multiple isolated broadcast domains. Each VLAN behaves as an independent network segment, meaning that devices within the same VLAN can communicate with each other at Layer 2, while communication between different VLANs requires Layer 3 routing.
In traditional flat network designs, all devices connected to a switch belong to a single broadcast domain, which means broadcast traffic is delivered to every device regardless of relevance. This design becomes inefficient as the number of devices increases. VLANs solve this problem by introducing logical separation without requiring physical separation. This allows network administrators to group devices based on function, department, security level, or application type while still using the same physical switching infrastructure.
When a VLAN is created, it is assigned a unique identifier, and switch ports are configured to belong to that VLAN. Any device connected to those ports automatically becomes part of that broadcast domain. Broadcast traffic generated within a VLAN remains confined to that VLAN and is not forwarded to other VLANs. This isolation significantly reduces unnecessary traffic and improves overall network performance.
VLANs also enable greater flexibility in network design. Instead of deploying separate switches for each department or function, administrators can logically segment networks using VLAN configuration. This reduces hardware costs and simplifies management while maintaining strict separation between different network groups.
VLAN Tagging and Frame Identification in Broadcast Domains
To maintain VLAN separation across interconnected switches, VLAN tagging is used. VLAN tagging is a method of adding additional information to Ethernet frames to identify which VLAN they belong to. This is typically implemented using standardized protocols that insert VLAN identifiers into frame headers.
When a frame is sent from one switch to another over a trunk link, the VLAN tag ensures that the receiving switch knows which broadcast domain the frame belongs to. This allows multiple VLANs to share the same physical connection while maintaining logical separation. Without VLAN tagging, frames from different VLANs would become indistinguishable when transmitted between switches.
On receiving a tagged frame, the switch reads the VLAN identifier and forwards the frame only within the corresponding broadcast domain. This ensures that broadcast traffic remains isolated even in complex multi-switch environments. VLAN tagging is essential for maintaining consistency and integrity of broadcast domains across large network infrastructures.
In access ports, VLAN tagging is typically not visible to end devices. The switch handles tagging and untagging automatically, ensuring that devices operate as if they are part of a standard network segment. This abstraction simplifies network configuration while preserving logical segmentation.
Inter-Switch Communication and Broadcast Domain Extension
In larger networks, multiple switches are often interconnected to extend VLANs across different physical locations. These interconnections are typically implemented using trunk links, which carry traffic from multiple VLANs simultaneously.
Trunk links preserve VLAN information as frames travel between switches, ensuring that broadcast domains remain intact across the entire network. This allows devices in the same VLAN to communicate even if they are connected to different switches located in different parts of the network.
When a broadcast frame is sent within a VLAN, it is forwarded across trunk links but only within the same VLAN context. The receiving switch processes the frame and forwards it only to ports belonging to that VLAN. This ensures that broadcast domains remain logically consistent across multiple switching devices.
This capability is essential for enterprise and campus networks where devices are distributed across large physical areas. Without VLAN extension through trunking, broadcast domains would be limited to individual switches, significantly reducing scalability and flexibility.
Layer 2 Isolation and Broadcast Control Mechanisms
One of the primary advantages of VLAN-based segmentation is Layer 2 isolation. Each VLAN acts as an independent broadcast domain, meaning that devices in one VLAN cannot directly receive broadcast traffic from another VLAN. This isolation is enforced at the switching level and is fundamental to maintaining network separation.
Layer 2 isolation not only improves performance but also enhances security. By separating devices into different broadcast domains, sensitive traffic can be isolated from general user traffic. This reduces the risk of unauthorized access or unintended data exposure within the network.
Switches enforce isolation by maintaining separate MAC address tables for each VLAN. This ensures that forwarding decisions are made independently for each broadcast domain. As a result, even if two devices share the same physical switch, they cannot communicate at Layer 2 unless they belong to the same VLAN.
Broadcast control mechanisms also include features such as storm control, which limits the amount of broadcast traffic allowed on a port. This prevents excessive broadcast activity from disrupting network operations and ensures that broadcast domains remain stable even under heavy traffic conditions.
Broadcast Domain Design in Enterprise Network Topologies
Enterprise networks are typically designed using hierarchical models that incorporate access, distribution, and core layers. Each of these layers plays a specific role in managing broadcast domains and controlling traffic flow.
At the access layer, end devices such as computers, printers, and IoT systems are connected to switches. These switches assign devices to specific VLANs, thereby defining their broadcast domains. The access layer is responsible for enforcing initial segmentation and ensuring that devices are placed into the correct logical network segments.
The distribution layer aggregates traffic from multiple access layer switches and enforces policies related to VLAN routing and segmentation. This layer often handles inter-VLAN routing, allowing communication between different broadcast domains when necessary. It also ensures that broadcast traffic remains contained within its designated VLAN unless explicitly routed.
The core layer is designed for high-speed forwarding and minimal processing. It typically does not handle broadcast traffic directly but focuses on transporting large volumes of data between distribution points. This separation of responsibilities ensures that broadcast domains do not negatively impact backbone performance.
This hierarchical design allows enterprise networks to scale efficiently while maintaining strict control over broadcast traffic.
Inter-VLAN Communication and Broadcast Domain Boundaries
While VLANs effectively isolate broadcast domains, there are situations where communication between different VLANs is required. This is achieved through Layer 3 routing, which allows controlled communication between separate broadcast domains.
When a device in one VLAN needs to communicate with a device in another VLAN, the traffic is forwarded to a router or Layer 3 switch. The router processes the packet at the network layer and forwards it to the appropriate VLAN based on routing rules. This ensures that broadcast domains remain isolated while still allowing necessary communication between them.
Importantly, broadcast traffic does not cross VLAN boundaries. Instead, only unicast traffic is routed between VLANs. This ensures that broadcast domains remain strictly separated and that broadcast traffic does not propagate beyond its intended scope.
Inter-VLAN routing provides flexibility in network design while preserving the benefits of broadcast domain segmentation. It allows organizations to maintain logical separation without sacrificing communication capabilities between different network segments.
Broadcast Efficiency and Traffic Optimization Strategies
Efficient management of broadcast domains is essential for optimizing network performance. As the number of devices within a broadcast domain increases, the volume of broadcast traffic also increases. This can lead to congestion if not properly controlled.
To optimize performance, networks are designed to keep broadcast domains as small as practical. This ensures that broadcast traffic remains limited to relevant devices and does not overload the network. VLAN segmentation is the primary tool used to achieve this optimization.
In addition to VLANs, network devices may implement additional optimization techniques such as broadcast suppression and traffic filtering. These techniques help reduce unnecessary broadcast propagation and ensure that network resources are used efficiently.
Another important optimization strategy involves monitoring broadcast traffic levels. Network administrators often analyze traffic patterns to identify unusually high broadcast activity, which may indicate misconfigurations or network issues. By addressing these issues promptly, network performance can be maintained at optimal levels.
Broadcast Domains in Scalable and Distributed Network Systems
Modern networks are increasingly distributed across multiple locations and cloud environments. In such systems, broadcast domain management becomes more complex due to the need for consistency across geographically separated infrastructure.
Virtualization and software-defined networking technologies play a key role in extending broadcast domains across distributed environments. These technologies allow logical network segments to be defined independently of physical infrastructure, enabling consistent broadcast behavior across multiple locations.
Despite physical separation, devices within the same virtual broadcast domain can communicate as if they were on the same local network. This is achieved through encapsulation and tunneling techniques that preserve broadcast domain identity across network boundaries.
Scalability in such environments depends heavily on proper broadcast domain design. Poorly designed broadcast structures can lead to excessive traffic and performance degradation, while well-structured designs enable seamless expansion without impacting efficiency.
Operational Considerations in Broadcast Domain Management
Managing broadcast domains effectively requires careful planning and ongoing monitoring. Network administrators must consider factors such as device density, traffic patterns, application requirements, and security policies when designing broadcast segmentation.
Changes in network structure, such as adding new devices or expanding services, must be evaluated in terms of their impact on existing broadcast domains. Improper configuration can lead to increased broadcast traffic or unintended domain overlap.
Continuous monitoring tools are often used to observe broadcast activity and identify potential issues before they affect performance. This proactive approach ensures that broadcast domains remain stable and efficient over time.
Broadcast domain management is therefore an ongoing process that involves design, implementation, monitoring, and optimization. It is a critical aspect of maintaining reliable and high-performing network infrastructures.
Broadcast Domains in Large-Scale Network Architecture and Enterprise Environments
In modern large-scale networks, broadcast domains represent one of the most critical architectural concepts influencing performance, scalability, and stability. As network infrastructures expand to support thousands or even millions of connected devices, the way broadcast traffic is controlled becomes a defining factor in overall efficiency. A broadcast domain determines how far Layer 2 broadcast traffic can propagate, and in complex enterprise systems, these domains must be carefully designed to prevent congestion, reduce unnecessary processing overhead, and maintain predictable communication behavior.
In small networks, broadcast domains are relatively simple, often consisting of a single switch or a small group of interconnected devices. However, in enterprise-scale environments, broadcast domains must be logically segmented across multiple switches, routers, virtual networks, and even cloud-based systems. Without proper segmentation, broadcast traffic can overwhelm network devices, consume bandwidth, and degrade application performance. For this reason, broadcast domain control becomes a foundational principle in network architecture design.
Enterprise networks typically implement structured hierarchical models that divide responsibilities across different layers. Each layer plays a specific role in managing broadcast traffic and ensuring efficient communication. This layered approach ensures that broadcast domains remain localized, predictable, and optimized for performance even under heavy traffic conditions.
Hierarchical Network Design and Broadcast Domain Segmentation
In large enterprise environments, networks are commonly designed using a hierarchical model consisting of access, distribution, and core layers. Each of these layers contributes to the management and containment of broadcast domains in different ways.
The access layer is the point where end devices such as computers, printers, IoT devices, and workstations connect to the network. At this layer, devices are assigned to specific broadcast domains, often through VLAN configuration. The access layer is responsible for ensuring that devices are correctly segmented from the moment they connect to the network. This prevents unnecessary broadcast traffic from spreading across unrelated devices.
The distribution layer acts as an intermediary between access and core layers. It enforces policies related to VLAN segmentation, routing, and broadcast control. When communication needs to occur between different broadcast domains, the distribution layer handles inter-VLAN routing. This ensures that broadcast traffic remains confined while still allowing controlled communication between different network segments.
The core layer is designed for high-speed data forwarding and minimal processing. It serves as the backbone of the network, transporting large volumes of traffic between distribution points. Importantly, the core layer does not process broadcast traffic directly. This design ensures that broadcast domains do not impact backbone performance and that high-speed communication remains uninterrupted.
This hierarchical structure ensures that broadcast domains are not only segmented logically but also distributed efficiently across different layers of the network. It prevents broadcast traffic from propagating unnecessarily and ensures that each layer of the network performs a specific function in controlling traffic flow.
Broadcast Domain Boundaries in Multi-Switch Environments
In large networks, multiple switches are interconnected to extend connectivity across different physical locations. In such environments, maintaining broadcast domain boundaries becomes significantly more complex. Without proper configuration, broadcast traffic could easily spread across multiple switches, leading to inefficiency and congestion.
To prevent this, VLANs are extended across switches using trunk links. These links carry traffic for multiple broadcast domains simultaneously while preserving VLAN identification. Each frame transmitted over a trunk link contains VLAN tagging information that allows receiving switches to determine which broadcast domain the frame belongs to.
When a broadcast frame is generated within a VLAN, it is forwarded across trunk links but remains confined to that VLAN. Each switch that receives the frame processes it only within the context of the corresponding broadcast domain. This ensures that broadcast traffic remains isolated even when distributed across multiple physical devices.
This mechanism is essential for maintaining consistency in large-scale environments such as corporate campuses, data centers, and distributed networks. Without VLAN-aware trunking, broadcast domains would be limited to individual switches, significantly reducing scalability and flexibility.
Broadcast Traffic Behavior in High-Density Network Environments
In high-density networks where large numbers of devices are connected, broadcast traffic becomes a significant consideration. Every device within a broadcast domain must process broadcast frames, regardless of whether the content is relevant to it. As the number of devices increases, this processing overhead also increases.
Broadcast traffic is essential for many fundamental network operations, including device discovery, address resolution, and service advertisement. However, excessive broadcast traffic can lead to performance degradation. In densely populated broadcast domains, even small inefficiencies can accumulate into noticeable network slowdowns.
To manage this, network designers carefully limit the size of broadcast domains. Instead of allowing hundreds or thousands of devices to exist within a single domain, networks are segmented into smaller, more manageable groups. This ensures that broadcast traffic remains localized and does not overwhelm network resources.
Additionally, modern switching devices incorporate mechanisms to control broadcast traffic levels. These include rate-limiting features that restrict the amount of broadcast traffic a port can handle. If traffic exceeds predefined thresholds, excess frames are dropped or throttled to maintain network stability. This prevents broadcast storms and ensures consistent performance even under heavy load.
Broadcast Storms and Network Stability Challenges
One of the most critical risks associated with poorly designed broadcast domains is the occurrence of broadcast storms. A broadcast storm occurs when excessive broadcast traffic circulates within a network, consuming bandwidth and processing resources to the point where normal communication becomes severely degraded or completely disrupted.
Broadcast storms can be caused by network loops, misconfigured devices, or malfunctioning hardware. When a loop exists in a Layer 2 network, broadcast frames can circulate indefinitely, multiplying with each pass through a switch. This results in exponential traffic growth that can quickly overwhelm the network.
To prevent this, networks implement loop prevention mechanisms such as spanning tree protocols. These protocols ensure that redundant paths in the network are logically blocked, preventing the formation of loops that could generate broadcast storms. By maintaining a loop-free topology, the network ensures that broadcast domains remain stable and controlled.
In addition to loop prevention, storm control mechanisms are also used to limit the impact of excessive broadcast traffic. These mechanisms monitor traffic levels and automatically suppress broadcast frames when thresholds are exceeded. This ensures that even if a fault occurs, the impact on the network is contained.
Broadcast Domains in Virtualized Network Infrastructure
Modern network environments increasingly rely on virtualization to enhance flexibility and scalability. In virtualized infrastructures, broadcast domains are no longer tied strictly to physical hardware but are instead implemented through software-defined constructs.
Virtual switches within hypervisors create isolated broadcast domains for virtual machines. Each virtual network segment behaves like a traditional VLAN, ensuring that broadcast traffic remains confined within the appropriate group of virtual systems. This allows multiple isolated environments to coexist on the same physical hardware without interference.
In cloud environments, broadcast domains are extended across distributed data centers using overlay networking technologies. These technologies encapsulate Layer 2 frames within Layer 3 tunnels, allowing broadcast domains to span multiple physical locations. Despite this physical separation, devices within the same virtual broadcast domain behave as if they are on the same local network.
This abstraction enables dynamic scaling of broadcast domains based on application requirements. Virtual machines and containers can be moved between physical hosts without changing their network identity, ensuring seamless connectivity and consistent broadcast behavior.
Performance Optimization Through Broadcast Domain Design
Proper broadcast domain design is one of the most effective methods for optimizing network performance. By limiting the number of devices within each broadcast domain, networks reduce the volume of broadcast traffic and improve overall efficiency.
Smaller broadcast domains result in lower processing overhead for both network devices and end systems. This allows devices to allocate more resources to actual data processing rather than handling unnecessary broadcast frames. As a result, application performance improves, and latency is reduced.
Bandwidth utilization is also significantly improved when broadcast domains are properly segmented. Instead of consuming bandwidth with unnecessary broadcast traffic, network links can be used more efficiently for unicast and multicast communication. This leads to better throughput and more stable performance across the network.
In addition, smaller broadcast domains simplify network troubleshooting. When issues arise, administrators can isolate problems to specific segments rather than analyzing the entire network. This reduces diagnostic complexity and speeds up resolution times.
Broadcast Domains in Security and Access Control Architectures
Broadcast domain segmentation also plays an important role in network security. By isolating devices into separate broadcast domains, networks can limit the spread of traffic and reduce the risk of unauthorized access.
Devices within one broadcast domain cannot directly receive broadcast traffic from another domain. This isolation helps prevent lateral movement within the network, where an attacker might attempt to move between systems after gaining initial access. By separating sensitive systems into dedicated broadcast domains, organizations can reduce exposure to potential threats.
Broadcast domain separation also supports access control policies. Different departments or user groups can be assigned to separate VLANs, ensuring that their traffic remains isolated. This not only improves security but also enhances organizational structure and compliance with data handling policies.
Even in cases where inter-domain communication is required, it is handled through controlled routing mechanisms rather than direct broadcast propagation. This ensures that all cross-domain communication is explicitly managed and monitored.
Scalability Considerations in Broadcast Domain Design
Scalability is one of the most important considerations in modern network design, and broadcast domains play a central role in achieving it. As networks grow, broadcast traffic must remain manageable to avoid performance degradation.
Scalable network design involves carefully balancing the size of broadcast domains. Domains that are too large can become inefficient due to excessive broadcast traffic, while domains that are too small can increase management complexity. Finding the right balance is essential for maintaining long-term network performance.
In large-scale environments, automation tools are often used to manage broadcast domain configuration dynamically. These tools can adjust segmentation based on traffic patterns, device distribution, and application requirements. This ensures that broadcast domains remain optimized even as network conditions change.
Additionally, modern software-defined networking solutions allow broadcast domains to be created, modified, and removed programmatically. This enables highly flexible and adaptive network architectures that can respond quickly to changing demands.
Operational Management and Monitoring of Broadcast Domains
Effective management of broadcast domains requires continuous monitoring and analysis. Network administrators must observe traffic patterns to identify anomalies such as excessive broadcast activity or unexpected domain expansion.
Monitoring tools provide visibility into broadcast traffic levels, allowing administrators to detect potential issues before they impact performance. These tools can also identify misconfigurations that may lead to inefficient broadcast distribution.
Regular auditing of broadcast domains is essential to ensure that segmentation remains aligned with organizational requirements. As networks evolve, changes in device distribution or application usage may require adjustments to broadcast domain boundaries.
By maintaining active oversight, organizations can ensure that broadcast domains continue to support efficient, secure, and scalable network operations over time.
Conclusion
Broadcast domains remain one of the most fundamental concepts in computer networking, shaping how data moves, how devices interact, and how efficiently a network operates. At their core, broadcast domains define the reach of broadcast traffic within a Layer 2 network environment, ensuring that such traffic is contained within a logical boundary rather than spreading across an entire infrastructure. This simple idea has far-reaching implications for performance, scalability, security, and overall network design.
In any functioning network, communication is not limited to direct device-to-device exchanges. Many essential operations rely on broadcast messages to function correctly. These include device discovery, address resolution, configuration services, and various initialization processes that allow systems to join and operate within a network. Without broadcast communication, these foundational processes would require significantly more complex mechanisms. However, while broadcast traffic is necessary, it must be carefully controlled to prevent inefficiency. This is where the concept of a broadcast domain becomes critical.
By limiting the scope of broadcast traffic, broadcast domains ensure that only relevant devices receive and process broadcast frames. This prevents unnecessary workload on devices that do not require the information and reduces overall network congestion. In environments where hundreds or thousands of devices are connected, this containment becomes essential for maintaining stable performance. Without proper segmentation, broadcast traffic would quickly escalate, consuming bandwidth and processing power across the entire network.
One of the most important outcomes of properly designed broadcast domains is improved network efficiency. When broadcast traffic is restricted to smaller, well-defined segments, devices within those segments experience significantly lower overhead. They are not required to process irrelevant broadcast frames from unrelated parts of the network. This allows computing resources such as CPU and memory to be used more effectively for application-level tasks rather than network-level processing. The result is smoother performance, reduced latency, and a more predictable network experience.
Another key advantage lies in scalability. Modern networks are expected to support rapid growth, both in terms of device count and application complexity. Broadcast domains provide a structured way to manage this growth. By dividing large networks into smaller logical segments, administrators can ensure that expansion does not lead to performance degradation. Each broadcast domain operates independently, meaning that growth in one segment does not negatively impact others. This modular approach is essential in enterprise environments, data centers, and cloud-based infrastructures where scalability is a primary requirement.
Security is another area where broadcast domain design plays a crucial role. By isolating devices into separate broadcast domains, networks naturally limit the spread of traffic between different segments. This reduces the risk of unauthorized access and lateral movement within the network. Sensitive systems can be placed in isolated broadcast domains, ensuring that their traffic is not exposed to unrelated devices. Even if a security issue arises in one segment, its impact remains contained within that boundary, preventing widespread disruption.
Broadcast domains also contribute significantly to network manageability. When networks are logically segmented, it becomes easier to monitor, troubleshoot, and optimize performance. Network administrators can isolate issues to specific broadcast domains rather than analyzing the entire infrastructure. This targeted approach reduces diagnostic complexity and allows for faster resolution of problems. It also enables more precise performance tuning, as each segment can be optimized based on its specific traffic patterns and requirements.
From an architectural perspective, broadcast domains are closely tied to switching and routing behavior. Layer 2 switches define the boundaries within which broadcast traffic is distributed, while Layer 3 devices such as routers enforce separation between different broadcast domains. This interaction between switching and routing creates a layered communication model that supports both efficiency and control. Switches handle local traffic distribution, while routers manage communication between different network segments without forwarding broadcast traffic.
In modern networking environments, virtualization and software-defined technologies have further expanded the role of broadcast domains. No longer limited to physical hardware boundaries, broadcast domains can now exist as virtual constructs that span multiple physical locations. This abstraction allows networks to be highly flexible, enabling dynamic resource allocation and seamless workload mobility. Virtual machines and containers can move across physical hosts while maintaining consistent network identity within their broadcast domain.
Despite these technological advancements, the core principle remains unchanged: broadcast traffic must be controlled and contained to maintain network efficiency. Whether implemented through physical switches, virtual networks, or cloud-based systems, the concept of limiting broadcast scope continues to be essential for stable and scalable network design.
Another important consideration is the balance between broadcast domain size and network efficiency. If a broadcast domain is too large, it can lead to excessive broadcast traffic and reduced performance. On the other hand, if it is too small, it may introduce unnecessary complexity and management overhead. Effective network design requires finding an optimal balance where broadcast domains are large enough to support necessary communication but small enough to prevent inefficiency.
Broadcast domains also indirectly influence application performance. Many applications rely on underlying network services that depend on broadcast communication. If broadcast traffic is poorly managed, these services can become delayed or unreliable, affecting application responsiveness. By ensuring that broadcast domains are properly structured, networks provide a stable foundation for application-level performance.
In addition, broadcast domain design plays a role in preventing network instability caused by excessive traffic conditions. Poorly configured networks can experience broadcast storms, where large volumes of broadcast traffic overwhelm devices and disrupt normal communication. Proper segmentation, combined with traffic control mechanisms, helps prevent such conditions and ensures network resilience even under heavy load.
Ultimately, broadcast domains are not just a theoretical networking concept but a practical necessity in real-world infrastructure design. They provide the framework that allows networks to scale, perform efficiently, and remain secure under increasing demands. Every modern network, whether small or large, relies on carefully structured broadcast domains to function effectively.
As networking technology continues to evolve, the importance of broadcast domain management will remain central. Even as new paradigms such as cloud computing, virtualization, and software-defined networking redefine how infrastructure is built and operated, the underlying principle of controlling broadcast traffic will continue to guide network design decisions. Broadcast domains represent a balance between communication freedom and controlled efficiency, ensuring that networks remain both functional and optimized in increasingly complex environments.