The digital ecosystem has evolved into a highly interconnected environment where applications, systems, and users continuously exchange sensitive information. Among the most critical elements in this ecosystem are secrets, which include passwords, API keys, encryption keys, tokens, and certificates. These secrets act as the backbone of authentication and authorization processes, ensuring that only trusted entities can access protected resources. However, managing these secrets securely has long been a challenge for organizations of all sizes.
Historically, many systems relied on manual methods of storing and sharing credentials. Developers often embedded passwords directly into application code, configuration files, or scripts. While this approach offered convenience, it introduced severe security risks. Over time, this practice led to what is widely known as password sprawl, a condition where credentials are scattered across multiple systems without proper control or visibility. This lack of centralized management made it nearly impossible to track who had access to sensitive data and when it was used.
The consequences of poor secret management are far-reaching. Unauthorized access, data breaches, compliance violations, and operational inefficiencies are just a few of the risks organizations face. As businesses increasingly adopt cloud computing, microservices architectures, and DevOps practices, the number of secrets in use has grown exponentially. This surge has made traditional security approaches obsolete and highlighted the need for more advanced solutions.
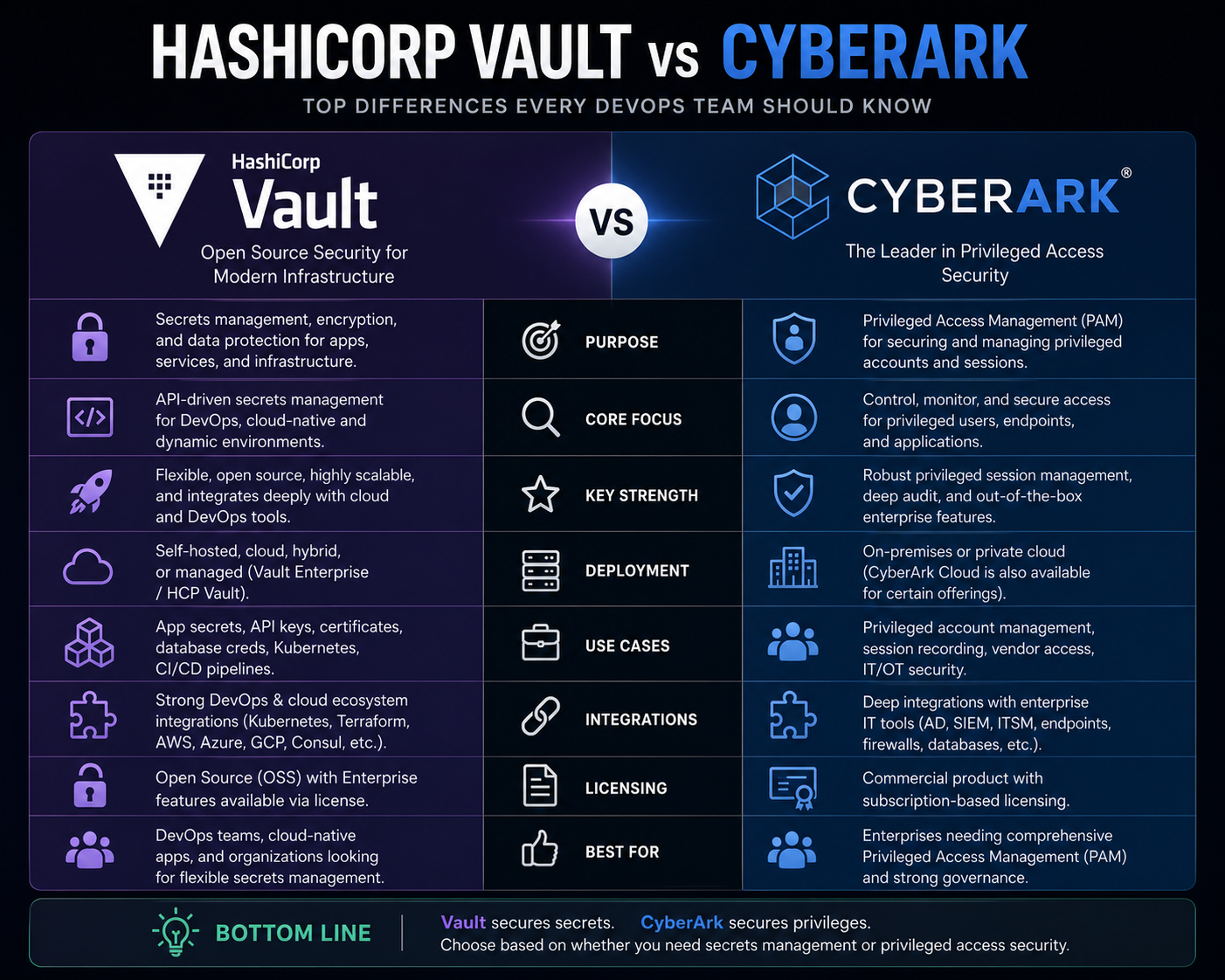
Modern secret management platforms address these challenges by providing centralized, automated, and secure methods for handling sensitive data. Among the most recognized solutions in this space are HashiCorp Vault and CyberArk. These platforms have redefined how organizations protect and manage secrets, offering robust features that align with contemporary security requirements.
The Core Problem of Password Sprawl and Security Gaps
Password sprawl is not merely a technical inconvenience; it represents a fundamental breakdown in security governance. When credentials are distributed across multiple environments without proper controls, organizations lose the ability to enforce consistent security policies. This often results in weak passwords, outdated credentials, and excessive access privileges.
In traditional setups, developers and system administrators frequently reused passwords across different systems. This practice increased the risk of lateral movement, where an attacker who gains access to one system can easily move to others. Additionally, credentials stored in plain text or weakly encrypted formats became easy targets for malicious actors.
Another critical issue associated with password sprawl is the lack of auditability. Without proper logging and monitoring, organizations cannot determine who accessed a particular secret or whether it was misused. This absence of visibility complicates incident response efforts and makes compliance with regulatory standards more challenging.
Credential rotation presents yet another challenge. Regularly updating passwords and keys is a fundamental security practice, but manual rotation is time-consuming and prone to errors. In many cases, organizations delay or neglect this process, leaving systems vulnerable to exploitation.
The shift toward cloud-native environments has further intensified these challenges. Applications are now distributed across multiple platforms and services, each requiring secure access to resources. Managing secrets in such dynamic environments demands a solution that can scale seamlessly while maintaining strict security controls.
Secret management platforms were developed to address these exact issues. By centralizing the storage and management of credentials, these solutions eliminate the risks associated with decentralized approaches. They also introduce automation, enabling organizations to enforce security policies consistently and efficiently.
Key Principles Behind Modern Secret Management
To understand how advanced platforms operate, it is essential to explore the foundational principles of secret management. These principles guide the design and implementation of secure systems and ensure that sensitive data remains protected throughout its lifecycle.
One of the most important principles is encryption. Secrets must be encrypted both at rest and in transit to prevent unauthorized access. This ensures that even if data is intercepted or compromised, it remains unreadable without the appropriate decryption keys.
Another critical principle is least privilege access. Users and applications should only have access to the secrets they absolutely need. By limiting permissions, organizations can reduce the risk of misuse and minimize the impact of potential breaches.
Dynamic secrets play a significant role in enhancing security. Instead of relying on static credentials, modern platforms generate temporary secrets that expire after a predefined period. This approach significantly reduces the window of opportunity for attackers.
Auditability and monitoring are also essential components. Comprehensive logging allows organizations to track every interaction with a secret, providing valuable insights for security analysis and compliance reporting.
Automation is a key enabler of efficient secret management. By automating tasks such as credential rotation, access provisioning, and policy enforcement, organizations can reduce human error and improve overall security posture.
These principles form the foundation of platforms like HashiCorp Vault and CyberArk, enabling them to deliver robust and scalable solutions for managing sensitive information.
Introduction to HashiCorp Vault and Its Architecture
HashiCorp Vault is a widely adopted secret management platform designed to secure, store, and control access to sensitive data. It provides a centralized system where secrets can be managed efficiently while maintaining high levels of security.
At its core, Vault operates on a simple yet powerful concept. Instead of storing credentials in multiple locations, all secrets are kept in a secure, centralized repository. Applications and users must authenticate with Vault before accessing any secret, ensuring that only authorized entities can retrieve sensitive information.
Vault uses a modular architecture that allows it to integrate with various authentication methods and storage backends. This flexibility makes it suitable for a wide range of use cases, from small development environments to large enterprise deployments.
One of the defining features of Vault is its ability to generate dynamic secrets. For example, instead of providing a static database password, Vault can create a temporary credential that is valid for a limited time. Once the credential expires, it is automatically revoked, eliminating the need for manual rotation.
Vault also includes a comprehensive audit logging system. Every request and response is recorded, providing a detailed history of all interactions with secrets. This level of visibility is crucial for maintaining security and meeting compliance requirements.
Another important aspect of Vault is its support for encryption as a service. Organizations can use Vault to encrypt and decrypt data without exposing encryption keys to applications. This approach enhances security by separating key management from data processing.
The platform supports both human and machine authentication, enabling seamless integration with modern DevOps workflows. Whether it is a developer accessing a secret through a command-line interface or an application retrieving credentials via an API, Vault ensures secure and controlled access.
How Vault Enables Secure Automation and DevOps Integration
In modern development environments, automation is essential for maintaining efficiency and scalability. Continuous integration and continuous deployment pipelines rely on seamless access to resources, which often requires the use of sensitive credentials. Managing these credentials securely is a critical challenge.
Vault addresses this challenge by providing programmatic access to secrets through APIs. Applications can request credentials dynamically during runtime, eliminating the need to store them in code or configuration files. This approach aligns with best practices in DevOps and reduces the risk of credential exposure.
Another advantage of Vault is its ability to integrate with orchestration platforms. In containerized environments, applications are frequently deployed and scaled dynamically. Vault can provide secrets to these applications on demand, ensuring that each instance has access to the necessary credentials without compromising security.
Vault also supports policy-based access control. Administrators can define granular policies that determine who can access specific secrets and under what conditions. This level of control ensures that access is restricted to authorized users and applications.
The platform’s leasing and revocation mechanisms further enhance security. When a secret is issued, it comes with a lease that defines its validity period. Once the lease expires, the secret is automatically revoked, preventing unauthorized reuse.
These capabilities make Vault an ideal solution for organizations adopting cloud-native and DevOps practices. By automating secret management, it enables teams to focus on development and innovation while maintaining strong security controls.
Introduction to CyberArk and Its Approach to Privileged Access
CyberArk is another leading solution in the field of secret management, with a strong focus on privileged access security. Unlike traditional approaches that rely on shared credentials, CyberArk emphasizes controlled access and comprehensive monitoring.
CyberArk’s platform is designed to protect privileged accounts, which are often targeted by attackers due to their elevated permissions. These accounts include administrators, service accounts, and other high-level users who have access to critical systems.
One of the key features of CyberArk is its ability to manage sessions without exposing credentials. Users can access systems through CyberArk without ever seeing the actual password. This eliminates the risk of credential leakage and ensures that sensitive information remains protected.
Session recording is another important capability. CyberArk records user interactions during privileged sessions, providing a detailed audit trail. This feature enhances accountability and allows organizations to investigate suspicious activities effectively.
CyberArk also supports dynamic credential management. Similar to Vault, it can generate temporary passwords that expire after use. This approach reduces the risk associated with static credentials and improves overall security.
The platform integrates with various systems and applications, enabling organizations to implement a unified approach to access management. By centralizing control, CyberArk helps enforce consistent security policies across the entire infrastructure.
Zero Trust and the Evolution of Access Control
The concept of Zero Trust has become a cornerstone of modern cybersecurity strategies. It is based on the principle that no user or system should be trusted by default, regardless of their location or role. Every access request must be verified and validated before granting permission.
Both Vault and CyberArk align with this philosophy by implementing strict authentication and authorization mechanisms. Instead of relying on perimeter-based security, these platforms focus on protecting individual resources and ensuring that access is granted only when necessary.
Zero Trust also emphasizes continuous monitoring and verification. Access is not a one-time event but an ongoing process that requires constant evaluation. This approach helps detect and prevent unauthorized activities in real time.
By adopting Zero Trust principles, organizations can significantly reduce their attack surface and improve their resilience against cyber threats. Secret management platforms play a crucial role in this strategy by securing the credentials that enable access to critical systems.
The Growing Importance of Secret Management in Modern Infrastructure
As organizations continue to embrace digital transformation, the importance of secure secret management cannot be overstated. The increasing complexity of IT environments, combined with the rise of sophisticated cyber threats, has made traditional security approaches insufficient.
Modern infrastructures rely on a vast number of interconnected components, each requiring secure access to resources. Without proper secret management, these systems become vulnerable to attacks and operational failures.
Platforms like HashiCorp Vault and CyberArk provide the tools needed to address these challenges. By centralizing control, automating processes, and enforcing strict security policies, they enable organizations to protect sensitive data effectively.
The adoption of these solutions is not just a technical decision but a strategic one. It reflects a commitment to security, compliance, and operational excellence. As the digital landscape continues to evolve, secret management will remain a critical component of any robust cybersecurity framework.
Deep Dive Into HashiCorp Vault Architecture and Security Model
In modern distributed systems, secret management is not just about storing credentials securely, but about designing an architecture that can operate reliably at scale across cloud, on-premises, and hybrid environments. HashiCorp Vault is built around a centralized security model that emphasizes encryption, policy enforcement, and controlled access through identity-based authentication mechanisms.
At the core of Vault’s architecture is a tightly controlled storage layer where all sensitive data is encrypted before it is persisted. Vault does not rely on trusting the underlying storage system. Instead, it assumes the storage backend is untrusted and ensures that all secrets remain encrypted even if the storage layer is compromised. This design significantly reduces risk in environments where infrastructure security cannot be guaranteed.
Vault operates using a concept known as a “sealing and unsealing” mechanism. When Vault starts, it remains in a sealed state, meaning it cannot access stored secrets. To become operational, it must be unsealed using a quorum of cryptographic keys or automated unsealing methods integrated with cloud key management services. This ensures that even if the system is restarted or compromised, secrets are not immediately exposed.
Another critical architectural component is Vault’s token-based authentication system. Every request to Vault requires a valid token that is issued after successful authentication. These tokens are associated with specific policies that define what actions are permitted. This approach enforces fine-grained access control and aligns closely with modern identity-centric security principles.
Vault also supports a plugin-based architecture. This allows integration with multiple authentication backends such as LDAP, cloud identity providers, and Kubernetes service accounts. The flexibility of this system makes it suitable for highly heterogeneous environments where multiple identity systems coexist.
A key strength of Vault is its ability to generate dynamic secrets. Instead of relying on static credentials, Vault can create temporary credentials for databases, cloud services, and APIs. These credentials are automatically revoked after their lease expires, reducing the risk of credential reuse or leakage.
The audit logging system in Vault is designed for full traceability. Every request, whether successful or denied, is recorded with contextual metadata. This ensures that organizations can reconstruct access patterns and detect anomalies in real time.
Vault’s architecture is optimized for high availability and scalability. It supports clustering, replication, and disaster recovery configurations. These capabilities allow organizations to deploy Vault in production environments that require continuous uptime and resilience against failures.
CyberArk Security Framework and Privileged Access Strategy
CyberArk takes a fundamentally different but complementary approach to secret management. While Vault focuses heavily on developer-centric and cloud-native secret distribution, CyberArk is designed around privileged access management and securing high-risk administrative credentials.
CyberArk’s architecture is built around a central vault system that stores privileged credentials in an encrypted and highly controlled environment. Access to these credentials is never directly exposed to end users. Instead, CyberArk mediates access through controlled session brokering.
One of the defining characteristics of CyberArk is its Privileged Access Security model. This model ensures that administrative credentials are isolated, rotated, and monitored continuously. Unlike traditional systems where administrators might know or reuse passwords, CyberArk eliminates direct password exposure entirely.
When a user needs to access a system, CyberArk initiates a secure session without revealing the actual password. The platform retrieves the credential internally, authenticates the session, and establishes a connection between the user and the target system. This process ensures that credentials remain hidden throughout the interaction.
CyberArk also introduces session isolation and monitoring. Every privileged session is recorded in detail, including keystrokes, commands, and system interactions. This creates a complete audit trail that can be reviewed for compliance or forensic analysis.
A significant advantage of CyberArk is its ability to enforce real-time session controls. If suspicious activity is detected during a session, it can be immediately terminated. This capability is critical in environments where privileged accounts represent a high-value target for attackers.
The platform also integrates strongly with identity lifecycle management systems. It can automatically provision and de-provision access based on organizational roles, reducing the risk of orphaned accounts or excessive privileges.
CyberArk’s architecture is designed to support large enterprise environments with complex compliance requirements. It includes multiple layers of security controls, including credential vaulting, session management, threat analytics, and behavioral monitoring.
Secret Lifecycle Management and Automation in Vault
A major advantage of modern secret management systems is their ability to automate the entire lifecycle of a secret, from creation to revocation. Vault is designed to treat secrets as ephemeral objects rather than static entities.
When an application requests access to a secret, Vault generates a new credential dynamically. This credential is assigned a lease duration, which defines how long it remains valid. Once the lease expires, the credential is automatically revoked without requiring manual intervention.
This lifecycle approach significantly reduces the attack surface. Even if a credential is compromised, its usefulness is limited to a short time window. This is particularly important in cloud-native environments where applications are frequently scaled up and down.
Vault also supports automatic rotation of static secrets. In cases where dynamic secrets are not possible, Vault can periodically rotate credentials to ensure they remain secure. This process is fully automated and does not require application downtime.
Another important capability is secret leasing revocation. Administrators can revoke all secrets associated with a particular token or policy instantly. This is useful in incident response scenarios where rapid containment is required.
Vault’s API-driven architecture enables seamless integration with CI/CD pipelines. Applications can retrieve secrets at runtime without embedding credentials in source code. This eliminates one of the most common sources of security vulnerabilities in software development.
The automation capabilities extend to policy enforcement as well. Access policies can be defined in code and applied consistently across environments. This ensures that security rules remain consistent regardless of infrastructure changes.
CyberArk Session Management and Real-Time Monitoring
CyberArk introduces a different perspective on secret lifecycle management by focusing on real-time session control rather than ephemeral credential generation. Instead of simply issuing temporary secrets, CyberArk manages how those secrets are used during active sessions.
When a user initiates a privileged session, CyberArk acts as an intermediary between the user and the target system. The user never directly interacts with the underlying credentials. Instead, CyberArk brokers the connection and enforces security policies in real time.
Session recording is a critical component of this model. Every action performed during a session is logged and stored securely. This includes commands executed, files accessed, and system changes made. These recordings provide full visibility into administrative activities.
CyberArk also uses behavioral analytics to detect anomalies. By analyzing user behavior patterns, the system can identify deviations from normal activity. If suspicious behavior is detected, the session can be paused or terminated automatically.
Another important feature is just-in-time access provisioning. Users are granted privileged access only when necessary and for a limited time period. Once the task is completed, access is revoked automatically.
CyberArk’s monitoring capabilities extend across multiple systems and platforms. This centralized visibility allows security teams to track privileged activity across the entire infrastructure from a single interface.
The platform also supports compliance reporting by generating detailed audit logs. These logs are essential for meeting regulatory requirements in industries such as finance, healthcare, and government sectors.
Identity-Centric Security and Access Control Models
Both Vault and CyberArk rely heavily on identity-based security models, but they implement them in different ways. Vault focuses on machine identity and application-level authentication, while CyberArk emphasizes human and privileged identity management.
In Vault, identity is often tied to workloads such as containers, virtual machines, or services. Each workload is assigned a unique identity that determines what secrets it can access. This approach is particularly effective in microservices architectures where applications frequently communicate with each other.
Policies in Vault are highly granular and define access at the path level. This means administrators can control exactly which secrets an application can read or write. This level of precision is essential for large-scale distributed systems.
CyberArk, on the other hand, focuses on human users and privileged accounts. Identity is managed through role-based access control combined with behavioral analysis. Users are assigned roles that define what systems they can access and under what conditions.
A key difference is that CyberArk emphasizes session control, while Vault emphasizes credential distribution. Vault provides secrets to applications, whereas CyberArk governs how users interact with systems using those secrets.
Despite these differences, both platforms align with Zero Trust principles. Neither assumes trust based on network location or previous access. Instead, every request is verified independently.
Integration Capabilities and Ecosystem Compatibility
Modern IT environments require seamless integration between multiple tools and platforms. Both Vault and CyberArk provide extensive integration capabilities, but their focus areas differ.
Vault integrates deeply with cloud platforms, container orchestration systems, and CI/CD pipelines. It is commonly used in environments that rely heavily on automation and infrastructure as code. Its API-first design allows developers to embed secret retrieval directly into application workflows.
CyberArk integrates more extensively with enterprise identity systems, security information and event management platforms, and compliance tools. It is often deployed in organizations with strict regulatory requirements and complex administrative structures.
Vault’s ecosystem is particularly strong in DevOps environments where speed and automation are critical. CyberArk’s ecosystem is stronger in traditional enterprise environments where governance and compliance are top priorities.
Both platforms support hybrid deployments, allowing organizations to manage secrets across on-premises and cloud environments simultaneously. This flexibility is essential in modern IT strategies where infrastructure is rarely confined to a single environment.
Operational Differences in Real-World Deployment
In practical deployment scenarios, Vault and CyberArk serve different operational needs. Vault is often used to manage secrets for applications, services, and cloud infrastructure. It is heavily integrated into development pipelines and automated systems.
CyberArk is typically used to secure administrative access, manage privileged accounts, and enforce strict session controls. It is more focused on human interaction with critical systems rather than application-to-application communication.
Vault deployments tend to be lightweight and developer-driven. CyberArk deployments are often more structured and governed by security teams.
Vault excels in environments that prioritize agility and automation. CyberArk excels in environments that prioritize control and compliance.
Despite these differences, many organizations use both platforms together to create a layered security architecture. Vault manages application secrets, while CyberArk secures administrative access and privileged operations.
Enterprise Use Case Landscape for HashiCorp Vault and CyberArk
In large-scale enterprise environments, secret management is no longer a standalone function but a foundational layer of cybersecurity architecture. Both HashiCorp Vault and CyberArk are widely deployed across global organizations, but their real-world applications differ significantly based on organizational structure, infrastructure maturity, and security governance requirements.
Vault is commonly adopted in cloud-native enterprises that rely heavily on automation, microservices, and DevOps practices. These environments typically involve thousands of dynamically changing workloads that require secure, programmatic access to secrets. Vault’s ability to generate dynamic credentials and integrate with orchestration systems makes it highly suitable for such environments.
For example, in large distributed systems where applications are deployed across multiple regions, Vault ensures that each service instance receives only the credentials it needs, and only for a limited duration. This reduces the risk of credential reuse and limits exposure in the event of compromise.
CyberArk, on the other hand, is widely used in traditional enterprise environments with strong regulatory requirements. Industries such as banking, healthcare, defense, and government sectors rely heavily on CyberArk to secure privileged accounts and enforce strict access governance policies.
In these environments, human access to critical infrastructure is tightly controlled. CyberArk ensures that administrators never directly see or handle passwords, instead routing access through secure session brokers. This model significantly reduces insider risk and strengthens audit compliance.
Both platforms are often deployed together in hybrid security architectures. Vault manages application-level secrets, while CyberArk governs privileged human access. This dual-layer approach ensures comprehensive coverage across both machine and human identity domains.
Cloud-Native Integration and Multi-Cloud Strategy Support
Modern enterprises rarely operate within a single infrastructure environment. Instead, they adopt multi-cloud strategies involving platforms such as AWS, Azure, and Google Cloud, along with private cloud and on-premises systems. Secret management in such environments requires flexibility, scalability, and seamless integration.
Vault is designed with cloud-native principles at its core. It integrates deeply with container orchestration platforms, serverless computing environments, and infrastructure-as-code tools. Its API-first design enables applications to retrieve secrets dynamically without hardcoding credentials.
In Kubernetes environments, Vault can inject secrets directly into pods at runtime. This ensures that applications remain stateless and do not store sensitive information locally. It also supports identity-based authentication using service accounts, allowing fine-grained access control at the workload level.
Vault’s cloud integration extends to dynamic infrastructure provisioning. When new virtual machines or services are created, Vault can automatically generate and assign credentials based on predefined policies. This makes it highly efficient for environments with rapid scaling requirements.
CyberArk also supports cloud integration, but its focus is more aligned with securing privileged access across cloud infrastructure rather than managing application secrets. It provides secure access gateways that allow administrators to connect to cloud resources without exposing credentials.
In multi-cloud environments, CyberArk ensures that privileged access remains consistent regardless of the underlying platform. It centralizes identity management and enforces uniform security policies across different cloud providers.
This makes CyberArk particularly valuable for enterprises that operate hybrid infrastructures where governance and compliance consistency are critical.
Security Architecture Comparison and Trust Models
At the core of both Vault and CyberArk lies a fundamentally different interpretation of trust and access control.
Vault is built around a distributed trust model where identity is verified at every request. It assumes that no system or application should be inherently trusted. Instead, each request must be authenticated and authorized based on identity, policy, and context.
Vault’s architecture emphasizes ephemeral trust. Credentials are short-lived, dynamically generated, and frequently rotated. This reduces the impact of compromise and aligns closely with modern Zero Trust principles.
CyberArk, in contrast, is built around privileged trust isolation. It assumes that privileged accounts are inherently high-risk and must be strictly controlled. Instead of distributing credentials, CyberArk isolates them completely and mediates access through controlled sessions.
This approach creates a strong separation between users and credentials. Even administrators never directly interact with passwords, reducing the risk of credential theft or misuse.
CyberArk’s trust model is heavily focused on session-level control. Every privileged action is monitored, recorded, and analyzed in real time. This ensures accountability and provides forensic visibility into administrative operations.
Vault’s trust model is more focused on workload identity and automation. It ensures that applications can securely retrieve secrets without human intervention, enabling seamless machine-to-machine communication.
Both models are effective but serve different security philosophies. Vault prioritizes automation and scalability, while CyberArk prioritizes governance and control.
Identity and Access Governance Across Modern Infrastructure
Identity management is a critical component of any secret management strategy. Both Vault and CyberArk implement identity-driven security, but their approaches differ in scope and application.
Vault focuses heavily on machine identity. In modern cloud environments, applications are constantly created, destroyed, and updated. Each of these workloads requires secure access to secrets without manual intervention.
Vault assigns identities to workloads using authentication methods such as cloud identity services, Kubernetes service accounts, or application tokens. These identities are then mapped to policies that define what secrets can be accessed.
This approach ensures that access is tightly scoped and dynamically managed. As workloads change, their access permissions automatically adjust based on identity and policy rules.
CyberArk focuses on human identity and privileged access governance. It manages users, administrators, and service accounts that require elevated permissions. These identities are governed through role-based access control and policy enforcement.
CyberArk also incorporates identity lifecycle management, ensuring that access is granted, modified, and revoked based on organizational changes. For example, when an employee changes roles or leaves an organization, their access is automatically updated or removed.
This reduces the risk of orphaned accounts and ensures compliance with internal and external security regulations.
In many enterprise environments, Vault and CyberArk complement each other by managing different aspects of identity. Vault handles application identity, while CyberArk manages human and administrative identity.
Automation, DevOps Integration, and CI/CD Security Models
Automation plays a central role in modern software development and infrastructure management. Continuous integration and continuous deployment pipelines require secure access to credentials at multiple stages of the development lifecycle.
Vault is specifically designed to integrate with DevOps workflows. Its API-driven architecture allows pipelines to retrieve secrets dynamically during build and deployment processes. This eliminates the need to store credentials in code repositories or configuration files.
Vault also supports secret injection into runtime environments. This means that applications can receive credentials only when needed, without persisting them locally. This significantly reduces the risk of credential exposure in CI/CD pipelines.
Additionally, Vault enables policy-driven automation. Security teams can define rules that control how secrets are accessed, rotated, and revoked. These policies are automatically enforced across all environments.
CyberArk integrates with DevOps environments in a different way. Instead of focusing on application-level secret injection, it focuses on securing privileged access within deployment pipelines.
For example, when deployment tools require administrative access to infrastructure, CyberArk ensures that credentials are retrieved securely and used within controlled sessions. These sessions are monitored and recorded for compliance purposes.
CyberArk also supports just-in-time access for deployment operations. This ensures that privileged access is granted only when necessary and revoked immediately after use.
Together, Vault and CyberArk provide a comprehensive DevOps security model where Vault handles application secrets and CyberArk secures administrative operations.
Compliance, Auditability, and Regulatory Alignment
In regulated industries, compliance is a major driver of secret management adoption. Organizations must adhere to strict standards related to data protection, access control, and audit logging.
Vault provides detailed audit logging capabilities that record every interaction with a secret. This includes authentication attempts, secret retrievals, and policy evaluations. These logs are critical for demonstrating compliance with security frameworks.
Vault’s ability to maintain immutable audit trails ensures that organizations can reconstruct access events during security investigations or compliance audits.
CyberArk places an even stronger emphasis on compliance through session recording and privileged activity monitoring. Every action performed during a privileged session is recorded in detail, providing full visibility into administrative behavior.
This level of auditability is particularly important in industries such as finance and healthcare, where regulatory requirements demand strict oversight of privileged access.
CyberArk also provides reporting tools that help organizations demonstrate compliance with frameworks such as GDPR, HIPAA, and SOX. These reports include access reviews, entitlement analysis, and behavioral monitoring insights.
Vault’s compliance strength lies in application-level auditing, while CyberArk’s strength lies in human and privileged session auditing.
Scalability, Performance, and Operational Efficiency
Scalability is a critical factor in secret management systems, especially in environments with rapidly changing workloads.
Vault is designed for horizontal scalability. It supports clustering, replication, and multi-region deployments. This allows organizations to distribute secret management workloads across global infrastructure.
Vault’s performance is optimized for high-frequency secret requests, making it suitable for large-scale microservices architectures.
CyberArk is optimized for enterprise-scale privileged access management. Its architecture is designed to handle large numbers of concurrent administrative sessions while maintaining strict security controls.
While Vault focuses on distributed scalability, CyberArk focuses on centralized control and session governance. This reflects their different design philosophies.
Operational efficiency in Vault is achieved through automation and self-service access for applications. In CyberArk, efficiency is achieved through controlled access workflows and automated policy enforcement.
Strategic Decision Factors in Choosing Between Vault and CyberArk
Selecting between Vault and CyberArk is not a matter of superiority but of alignment with organizational needs. Each platform excels in different domains of secret management.
Vault is best suited for environments that prioritize automation, cloud-native architecture, and developer-driven workflows. It is particularly effective in systems where applications require frequent and dynamic access to secrets.
CyberArk is best suited for environments that require strict governance, privileged access control, and compliance-driven security models. It is commonly used in enterprises with high regulatory oversight.
In many cases, organizations do not choose one over the other. Instead, they implement both systems to create a layered security model. Vault manages application secrets and machine identity, while CyberArk governs privileged human access.
This combined approach ensures comprehensive coverage across the entire identity spectrum, reducing risk and improving security resilience.
Evolving Trends in Secret Management and Future Direction
Secret management continues to evolve as organizations adopt more complex infrastructure models. The rise of serverless computing, edge computing, and AI-driven systems is increasing the demand for more adaptive and intelligent security solutions.
Vault is evolving toward deeper integration with cloud-native ecosystems and enhanced automation capabilities. Its focus remains on enabling secure, scalable secret distribution for dynamic environments.
CyberArk is expanding its capabilities in identity security, behavioral analytics, and real-time threat detection. Its focus is shifting toward proactive security measures that anticipate and prevent privileged access misuse.
Both platforms are also increasingly integrating artificial intelligence and machine learning to enhance anomaly detection and access governance.
As digital ecosystems continue to expand, the role of secret management will become even more critical in ensuring secure and reliable infrastructure operations.
Conclusion
In modern enterprise security architecture, secret management has evolved from a niche operational concern into a foundational requirement for maintaining trust, continuity, and resilience across digital systems. As organizations expand into distributed cloud environments, adopt microservices architectures, and automate infrastructure at scale, the handling of sensitive credentials becomes one of the most critical security challenges. Solutions such as HashiCorp Vault and CyberArk represent two mature but philosophically different approaches to solving this challenge, each shaped by distinct security priorities and operational assumptions.
A key takeaway from comparing these platforms is that secret management is not a single problem with a single solution. Instead, it is a layered discipline involving application security, identity governance, privileged access control, automation, and compliance enforcement. Vault primarily addresses the challenge of securing machine-to-machine communication in highly dynamic environments. It is designed to integrate deeply with modern application ecosystems where services are frequently created, destroyed, and redeployed. Its emphasis on dynamic secrets, API-driven access, and short-lived credentials reflects the needs of cloud-native and DevOps-driven organizations.
CyberArk, in contrast, addresses a different but equally important dimension of security: the protection of privileged human access. In most security breaches, privileged credentials are a primary target because they offer direct access to sensitive infrastructure and data. CyberArk’s model removes direct human interaction with these credentials entirely, replacing it with controlled session brokering, real-time monitoring, and strict governance policies. This approach is particularly valuable in industries where regulatory compliance and operational oversight are non-negotiable requirements.
When viewed together, these systems illustrate a broader shift in cybersecurity philosophy. Traditional perimeter-based security models, which relied on network boundaries and implicit trust, are no longer sufficient in modern environments. Instead, identity has become the new security perimeter. Every access request must be verified, authorized, and continuously monitored. Both Vault and CyberArk embody this shift, but they apply it in different domains: Vault focuses on workload identity and automation, while CyberArk focuses on human identity and privileged access control.
Another important insight is the role of automation in reducing security risk. Manual credential management has historically been one of the weakest points in enterprise security. Human error, inconsistent practices, and lack of visibility often lead to credential leakage or misuse. Vault addresses this by automating the lifecycle of secrets, ensuring that credentials are generated, distributed, and revoked without manual intervention. This reduces the operational burden on teams while significantly improving security posture.
CyberArk complements this by automating privileged access workflows. Instead of allowing static administrative accounts to persist indefinitely, it enforces just-in-time access provisioning and session-based authentication. This means that elevated access is granted only when necessary and revoked immediately after use. By reducing the duration and scope of privileged access, CyberArk minimizes the potential impact of compromised credentials.
From an architectural perspective, both systems highlight the importance of separation of concerns. Vault separates secret storage from application logic, ensuring that credentials are never hardcoded or statically embedded in software. CyberArk separates credential ownership from credential usage, ensuring that users never directly interact with sensitive passwords. These separations create multiple layers of defense, reducing the likelihood of systemic compromise.
Scalability is another critical factor in evaluating secret management solutions. Modern enterprises operate at a scale where thousands of services and users may require access to sensitive data simultaneously. Vault’s distributed architecture allows it to scale horizontally across regions and environments, making it suitable for large cloud-native deployments. CyberArk, while more centralized in design, scales effectively in enterprise environments where structured governance and controlled access flows are required.
Compliance and auditability also play a significant role in enterprise adoption. Regulatory frameworks across industries require organizations to maintain detailed records of who accessed what data, when, and under what conditions. Vault provides comprehensive audit logs for secret access and policy enforcement, enabling organizations to track machine-level interactions. CyberArk extends this visibility to human activity by recording full privileged sessions, including commands executed and actions performed. Together, these capabilities ensure end-to-end traceability across both human and machine identities.
In practice, many organizations find that the most effective security strategy involves using both platforms in a complementary manner. Vault secures the internal communication between applications, services, and infrastructure components. CyberArk secures the external and administrative layer where human users interact with systems. This layered approach aligns closely with modern Zero Trust principles, where no entity is inherently trusted and every access request is continuously validated.
The decision between Vault and CyberArk is therefore not a binary choice but a matter of architectural alignment. Organizations focused on cloud-native development, rapid deployment cycles, and infrastructure automation tend to gravitate toward Vault as their primary secret management solution. Enterprises with strict compliance requirements, legacy systems, and high-value administrative operations often rely heavily on CyberArk to enforce privileged access controls.
Another dimension worth considering is operational complexity. Vault typically requires integration into development pipelines, infrastructure orchestration systems, and application runtimes. It is deeply embedded in the software delivery lifecycle. CyberArk, on the other hand, is more aligned with security operations teams, identity governance frameworks, and compliance departments. It operates at a higher governance level, overseeing how privileged access is granted and monitored.
Despite their differences, both systems are converging toward a shared future shaped by identity-centric security. As environments become more distributed and dynamic, the distinction between human and machine identity is becoming increasingly important. Future developments in secret management are likely to focus on deeper automation, behavioral analytics, and context-aware access control. Systems will not only verify identity but also evaluate risk based on behavior, environment, and historical patterns.
Ultimately, secure secret management is about reducing uncertainty in complex systems. Whether through dynamic credential generation, real-time session monitoring, or strict access policies, the goal remains the same: ensure that only the right entity has access to the right resource at the right time. Vault and CyberArk represent two advanced implementations of this principle, each optimized for different operational realities but aligned in their overarching objective of securing modern digital infrastructure.