Malware, short for malicious software, represents one of the most persistent and evolving threats in modern computing environments. It is specifically engineered to infiltrate, damage, disrupt, or gain unauthorized access to systems, networks, and data. As digital infrastructure continues to expand across personal, corporate, and governmental domains, malware has grown from simple experimental code into a sophisticated tool used by organized cybercriminal groups and advanced threat actors.
At its core, malware operates by exploiting trust and vulnerability. Whether through user interaction, unpatched software flaws, or deceptive tactics, it leverages weaknesses in both human behavior and technical systems. The widespread adoption of connected devices has significantly increased the attack surface, making malware a constant concern across all levels of technology usage.
The concept of malicious code dates back decades, long before the modern internet. Early experiments demonstrated that self-replicating programs could move across systems, highlighting the inherent risks of interconnected computing. Over time, these concepts were refined and weaponized, leading to the diverse and complex malware ecosystem that exists today. What began as curiosity-driven development has transformed into a global cybersecurity challenge with financial, operational, and reputational consequences.
Malware distribution methods have also evolved. Initially spread through physical media, modern malware primarily propagates through digital channels such as email attachments, compromised websites, software downloads, and network vulnerabilities. Attackers often combine multiple techniques to increase infection success rates, including phishing, exploit kits, and social engineering strategies designed to manipulate user behavior.
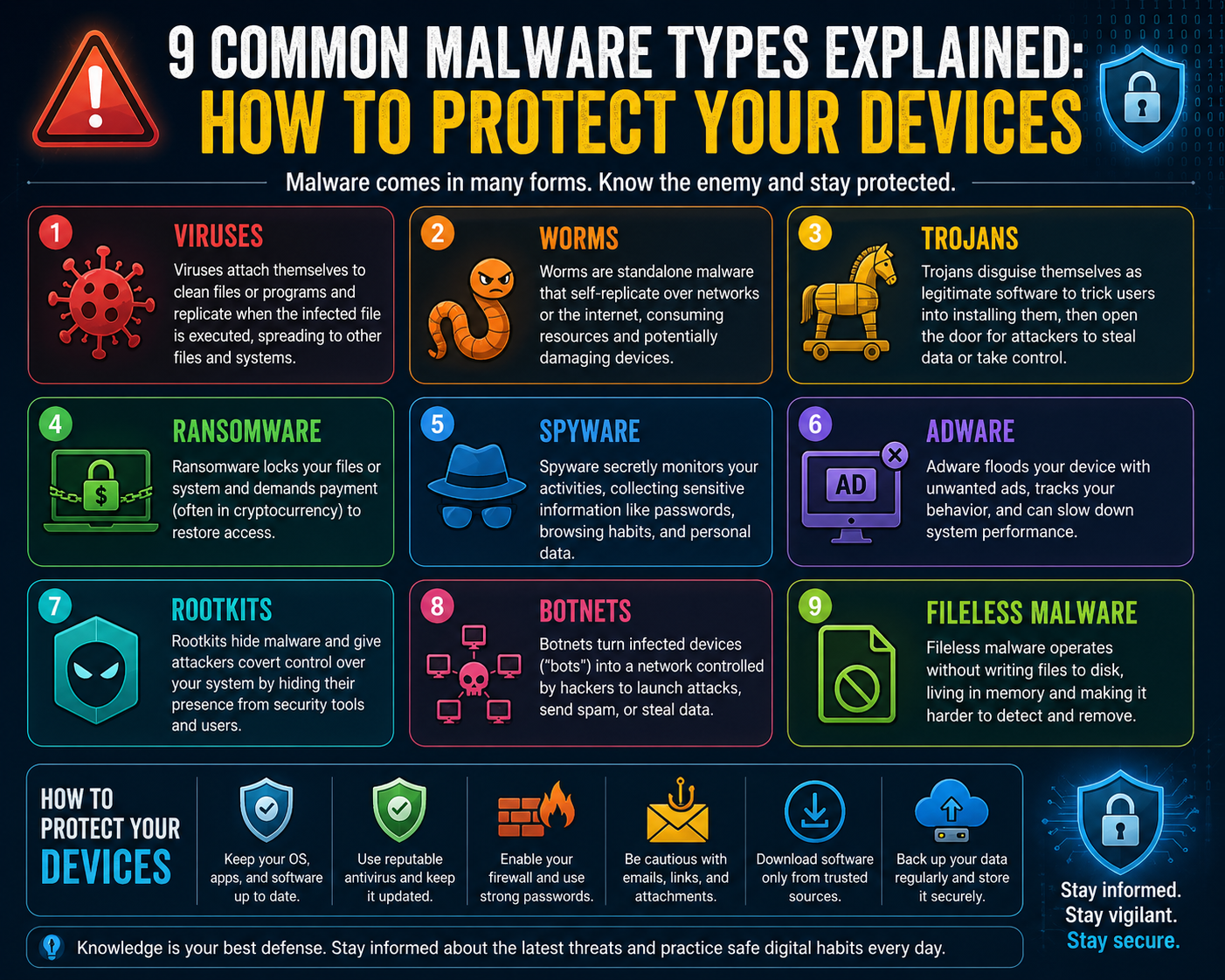
Understanding how malware functions is essential for anyone responsible for maintaining system integrity. Each type of malware has distinct characteristics, infection vectors, and impacts. Recognizing these differences allows for more effective detection, prevention, and response strategies.
How Malware Spreads Across Systems
Malware propagation relies on various mechanisms, each tailored to exploit specific weaknesses. One of the most common methods is through infected files. Users may unknowingly download malicious software disguised as legitimate applications, documents, or media files. Once executed, the malware activates and begins its intended operation.
Network-based spreading is another critical vector. Some malware types are designed to scan for vulnerable systems within a network and replicate themselves without user intervention. This capability allows rapid expansion across interconnected devices, especially in environments lacking proper segmentation or patch management.
Phishing remains a dominant delivery method. Attackers craft deceptive messages that appear legitimate, encouraging users to click links or download attachments. These interactions often trigger malware installation, granting attackers initial access to the system.
Web-based exploitation also plays a significant role. Visiting a compromised or malicious website can result in automatic malware downloads through browser vulnerabilities or outdated plugins. These drive-by attacks require minimal user interaction, making them particularly dangerous.
Removable media, although less common today, still presents risks. External storage devices can carry hidden malware that activates when connected to a system. This method is especially relevant in environments where strict access controls are not enforced.
Each propagation method underscores the importance of layered security. No single defense mechanism is sufficient, as attackers continuously adapt their techniques to bypass traditional protections.
Viruses: The Traditional Malware Archetype
Viruses are among the earliest and most recognizable forms of malware. They operate by attaching themselves to legitimate files or programs, activating when the host file is executed. Once active, a virus can replicate and spread to other files, often causing damage to data or system functionality.
The defining characteristic of a virus is its dependency on user action. Unlike some modern threats, viruses typically require execution by the user to initiate infection. This reliance makes user awareness a critical factor in prevention.
Historically, viruses spread through physical media such as floppy disks. In contemporary environments, they are more commonly distributed through email attachments, downloads, and shared files. Despite advances in security technologies, viruses remain relevant due to their adaptability and integration into broader attack strategies.
The impact of a virus can vary widely. Some are designed to corrupt files or disrupt system operations, while others may serve as entry points for more advanced malware. Their ability to replicate and spread makes them particularly disruptive in unprotected environments.
Worms: Autonomous Network Exploiters
Worms represent a more advanced form of malware, distinguished by their ability to spread independently without requiring user interaction. They exploit vulnerabilities in operating systems or network services to propagate across systems.
Once a worm infects a device, it begins scanning for other vulnerable targets. This process allows rapid expansion, often leading to widespread network disruption. Unlike viruses, worms do not need to attach themselves to existing files, enabling more efficient and aggressive propagation.
The consequences of worm infections can be severe. Network bandwidth may become saturated, system performance can degrade, and critical services may become unavailable. In large-scale outbreaks, worms have been known to impact entire organizations and infrastructure systems.
Effective defense against worms relies heavily on timely patching and vulnerability management. Ensuring that systems are updated reduces the attack surface and limits the ability of worms to exploit known weaknesses.
Trojans: Deceptive Entry Points
Trojans are a form of malware that relies on deception rather than technical exploitation. They disguise themselves as legitimate software, tricking users into installing them. Once executed, the malicious payload is activated, often without the user’s knowledge.
The success of trojans depends on social engineering. Attackers design convincing applications or files that appear useful or harmless. These may include software utilities, media files, or documents that entice users to interact with them.
Unlike viruses and worms, trojans do not replicate themselves. Instead, they serve as gateways for other malicious activities. Once installed, they may create backdoors, allowing attackers to access the system remotely. This access can be used to deploy additional malware, steal data, or monitor user activity.
Trojans highlight the importance of user vigilance. Even the most advanced security systems can be bypassed if users unknowingly install malicious software. Education and awareness play a crucial role in mitigating this threat.
Ransomware: High-Impact Data Extortion
Ransomware has emerged as one of the most damaging forms of malware in recent years. It operates by encrypting files on an infected system, rendering them inaccessible. The attacker then demands payment in exchange for a decryption key.
The impact of ransomware extends beyond individual devices. In networked environments, it can spread to shared resources, encrypting large volumes of data. This capability can disrupt entire organizations, halting operations and causing significant financial losses.
Ransomware attacks often exploit weak access controls and outdated systems. Once inside a network, the malware seeks to maximize its impact by targeting critical data and backups. In some cases, attackers also threaten to release sensitive information, increasing pressure on victims to comply.
Preventing ransomware requires a combination of technical and procedural measures. Regular backups, restricted access permissions, and timely updates are essential components of an effective defense strategy.
Spyware: Covert Data Collection
Spyware is designed to operate silently, monitoring user activity and collecting sensitive information. This data may include login credentials, financial details, browsing habits, and personal communications.
The stealthy nature of spyware makes it particularly dangerous. Users are often unaware of its presence, allowing it to gather information over extended periods. This data can then be used for identity theft, financial fraud, or targeted attacks.
Spyware is frequently bundled with other malware types, such as trojans. This combination increases its effectiveness by providing multiple layers of functionality. Once installed, it may operate in the background, avoiding detection by standard security tools.
Protecting against spyware involves maintaining updated security software and exercising caution when downloading or installing applications. Monitoring system behavior for unusual activity can also help identify potential infections.
Advanced Malware Types and Their Expanding Role in Cyber Threat Ecosystems
The evolution of malware has moved far beyond simple file corruption or visible system disruption. Modern malicious software operates within layered ecosystems designed to persist, evade detection, and achieve long-term objectives such as data theft, surveillance, and large-scale infrastructure disruption. As digital environments become more interconnected, malware has adapted into more specialized and stealth-oriented categories that operate silently within systems for extended periods.
Understanding advanced malware types is essential for recognizing how modern cyber threats function beyond traditional infection models. These threats often combine multiple techniques, blending deception, persistence, and automation to maximize impact while minimizing detection probability.
Adware: Commercial Exploitation Through Persistent Advertising Manipulation
Adware is a form of malware that focuses primarily on generating unwanted advertisements on infected systems. While it is often considered less destructive than other malware categories, its presence can significantly degrade user experience and system performance. Adware typically infiltrates systems through bundled software installations or deceptive download prompts.
Once installed, adware modifies browser behavior or system settings to display excessive advertising content. This may include pop-ups, banner injections, or automatic redirects to promotional pages. In some cases, adware tracks user activity to generate targeted advertisements based on browsing habits.
Although adware is often associated with nuisance-level disruption, it can also serve as a gateway to more serious threats. Some variants collect user data without consent, effectively blurring the line between adware and spyware. Additionally, excessive system resource usage caused by adware can lead to slow performance and instability.
The persistence of adware stems from its commercial value. Even when not overtly destructive, it generates revenue for attackers through advertising fraud schemes and data monetization.
Rootkits: Deep System Compromise and Stealth Persistence Mechanisms
Rootkits represent one of the most sophisticated categories of malware due to their ability to operate at a deep system level while remaining hidden from standard detection tools. Unlike conventional malware, rootkits are designed specifically to conceal their presence and maintain persistent access to compromised systems.
These threats often integrate directly into operating system components, including kernel-level processes. By doing so, they gain elevated privileges that allow them to manipulate system functions, hide files, and disable security mechanisms. This level of control makes rootkits extremely difficult to detect and remove.
Rootkits are commonly deployed as part of multi-stage attacks. Initial access may be gained through phishing or Trojan-based malware, after which the rootkit is installed to maintain long-term control. Once active, it can facilitate additional malicious activities such as data theft, surveillance, or further malware deployment.
The most dangerous aspect of rootkits is their invisibility. Traditional antivirus tools may fail to detect them because they operate below the level at which these tools function. Specialized detection methods and system integrity verification techniques are often required to identify rootkit infections.
Keyloggers: Behavioral Surveillance Through Input Capture
Keyloggers are designed to record user input, primarily keystrokes, and transmit this data to attackers. This allows cybercriminals to capture sensitive information such as passwords, banking credentials, personal messages, and confidential business data.
Keyloggers can exist in both software and hardware forms. Software-based keyloggers are typically installed through malicious downloads or bundled applications, while hardware keyloggers are physical devices inserted between keyboards and computers.
Once active, keyloggers operate silently in the background, recording all keyboard activity. Some advanced variants also capture clipboard data, screenshots, and application usage patterns. This expands the scope of data collection beyond simple keystrokes.
The data gathered by keyloggers is often used for identity theft, financial fraud, or unauthorized access to secure systems. In corporate environments, keyloggers can expose sensitive internal communications and credentials, leading to broader security breaches.
Protection against keyloggers involves maintaining strong endpoint security, monitoring system processes for anomalies, and implementing multi-factor authentication to reduce reliance on password-only security.
Botnets: Distributed Networks of Compromised Devices
Botnets represent a coordinated network of infected devices controlled remotely by an attacker. Each compromised device, often referred to as a “bot,” becomes part of a larger infrastructure used to execute large-scale malicious operations.
Once a device is infected and added to a botnet, it typically connects to a command-and-control server that issues instructions. These instructions can include sending spam emails, launching distributed denial-of-service attacks, or spreading additional malware.
The scale of botnets can vary significantly, ranging from a few hundred devices to millions of compromised systems. The larger the botnet, the more powerful and disruptive it becomes.
Botnets are particularly dangerous because they distribute malicious activity across many systems, making detection and mitigation more difficult. Each device may contribute only a small portion of activity, masking the overall attack pattern.
Modern botnets frequently target internet-connected devices such as routers, cameras, and smart home systems. These devices often lack robust security controls, making them easy targets for mass exploitation.
Advanced Persistence Techniques in Modern Malware
Beyond specific malware categories, modern threats increasingly rely on persistence techniques that ensure long-term system access. Persistence mechanisms allow malware to survive system reboots, updates, and partial removal attempts.
Common persistence strategies include modifying startup processes, altering system registry configurations, and embedding malicious code within legitimate applications. Some advanced malware also uses fileless techniques, operating directly in system memory without leaving traditional file traces.
These techniques make detection significantly more challenging. Traditional signature-based detection methods may fail because no persistent file exists on disk. Instead, behavioral analysis and anomaly detection become critical for identifying suspicious activity.
Persistence is often a key objective in advanced attacks, especially those targeting high-value systems or organizations. Maintaining long-term access allows attackers to conduct surveillance, exfiltrate data over time, or prepare for larger coordinated attacks.
Exploit-Based Malware and Vulnerability Abuse
A significant category of malware relies on exploiting software vulnerabilities. These exploits target weaknesses in operating systems, applications, or network services to execute malicious code without user interaction.
Exploit-based malware is particularly dangerous because it can operate silently and automatically. In many cases, simply visiting a compromised website or connecting to an unpatched system is enough to trigger an infection.
These attacks are often highly targeted, focusing on known vulnerabilities that have not yet been patched. Attackers may also use zero-day exploits, which take advantage of previously unknown security flaws.
The effectiveness of exploit-based malware highlights the importance of timely software updates. Delayed patching leaves systems exposed to known attack vectors that are actively exploited in the wild.
Fileless Malware: Memory-Resident Threat Execution
Fileless malware represents a modern evolution in attack techniques where malicious code does not rely on traditional files stored on disk. Instead, it operates directly in system memory, making it significantly harder to detect using conventional security tools.
This type of malware often leverages legitimate system tools and processes to execute its payload. By using trusted system components, it blends into normal activity and avoids raising suspicion.
Fileless attacks commonly begin through phishing or malicious scripts that execute code in memory. Once active, the malware can perform a range of actions, including data theft, system manipulation, or lateral movement across networks.
Because fileless malware leaves minimal forensic evidence, detection requires advanced monitoring of system behavior, process activity, and network traffic patterns.
Hybrid Malware and Multi-Stage Attack Structures
Modern cyber threats frequently combine multiple malware types into hybrid attack structures. These multi-stage attacks begin with one form of malware and progressively deploy additional components to achieve broader objectives.
For example, aTrojann may be used to gain initial access, followed by a rootkit for persistence, and then spyware or ransomware for data exploitation. This layered approach increases attack effectiveness and reduces the likelihood of detection.
Hybrid malware strategies reflect the professionalization of cybercrime. Attackers now operate with structured methodologies similar to software development lifecycles, optimizing each stage of infection for maximum impact.
These complex attack chains require equally sophisticated defense strategies that combine prevention, detection, and response capabilities across multiple system layers.
Network-Level Malware Propagation and Lateral Movement
Once inside a system, many malware types focus on lateral movement across networks. This involves spreading from one device to another within the same environment, often using shared credentials or unpatched vulnerabilities.
Network propagation is especially common in enterprise environments where systems are interconnected. Poor segmentation allows malware to move freely between departments, increasing the scope of infection.
Some malware is specifically designed to map internal networks, identify valuable targets, and escalate privileges. This behavior is often a precursor to large-scale data breaches or system-wide disruptions.
Controlling lateral movement requires strict network segmentation, access control policies, and continuous monitoring of internal traffic patterns.
Ransomware Evolution and Modern Extortion Ecosystems
Ransomware has evolved from relatively simple file-locking programs into highly organized and financially motivated cyber extortion ecosystems. Modern ransomware operations are no longer isolated attacks; they are structured campaigns often supported by affiliates, negotiation teams, and even data leak platforms designed to maximize pressure on victims.
At its core, ransomware functions by encrypting critical files or systems and demanding payment for decryption. However, the modern landscape has expanded this model into more complex strategies that include data theft prior to encryption. This dual-pressure approach ensures that even if victims restore systems from backups, sensitive data may still be exposed.
Early ransomware variants focused primarily on locking individual machines. In contrast, contemporary ransomware targets entire networks, including servers, shared storage, and backup systems. This expansion is made possible through lateral movement techniques that allow malware to spread after initial compromise.
One of the most significant developments in ransomware behavior is the adoption of “double extortion.” In this model, attackers not only encrypt data but also exfiltrate it. Victims are then threatened with public disclosure if payment is not made. This increases the likelihood of compliance, particularly for organizations handling sensitive or regulated data.
Some ransomware groups have further refined their operations into service-based models. Under this structure, ransomware tools are developed by one group and distributed to affiliates who carry out attacks. Profits are shared between developers and operators, creating a scalable criminal business model.
The impact of ransomware extends beyond financial loss. It can disrupt essential services, halt production systems, and compromise critical infrastructure. Recovery often requires extensive system restoration, forensic analysis, and long-term security improvements.
Advanced Evasion Techniques in Modern Malware
Modern malware is designed not only to infect systems but also to avoid detection. Evasion techniques have become increasingly sophisticated, allowing malicious software to remain hidden within environments for extended periods.
One common evasion strategy involves obfuscation. Malware code is intentionally scrambled or encoded to prevent analysis by security tools. This makes it difficult for signature-based detection systems to identify known patterns.
Another technique is polymorphism, where malware changes its structure each time it replicates. Although the core functionality remains the same, the code appears different, allowing it to bypass traditional detection methods.
Some malware also uses anti-analysis techniques to detect when it is being run in a virtual environment or sandbox. If such conditions are detected, the malware may remain inactive or behave normally to avoid revealing its malicious intent.
Time-based activation is another method used to evade detection. In these cases, malware delays its execution until a specific time or condition is met. This reduces the likelihood of immediate discovery during security scans or initial system analysis.
Fileless execution methods further enhance evasion. By operating directly in system memory, malware avoids writing detectable files to disk. This reduces forensic traces and complicates detection efforts.
These advanced techniques highlight the ongoing arms race between attackers and defenders. As security tools improve, malware developers continuously adapt their methods to remain undetected.
Internet of Things Malware and Expanding Attack Surfaces
The rapid growth of connected devices has introduced new opportunities for malware propagation. Internet of Things environments include devices such as smart cameras, routers, industrial sensors, and home automation systems. Many of these devices are designed with limited security capabilities, making them attractive targets.
IoT malware typically focuses on exploiting weak authentication mechanisms, outdated firmware, or exposed network services. Once compromised, these devices can be integrated into larger botnets or used as entry points into internal networks.
One of the key challenges in IoT security is the lack of standardized update mechanisms. Many devices are rarely patched, leaving known vulnerabilities unaddressed for extended periods. This creates long-term exposure that attackers can repeatedly exploit.
IoT botnets have demonstrated the potential scale of this threat. By compromising thousands of low-security devices, attackers can generate massive distributed attacks capable of overwhelming major internet services.
In addition to denial-of-service attacks, IoT malware can also be used for surveillance, data interception, and network infiltration. As more devices become interconnected, the potential attack surface continues to expand.
Securing IoT environments requires strong authentication practices, network segmentation, and continuous monitoring of device behavior.
Fileless and Memory-Based Malware Execution Models
Fileless malware represents a shift away from traditional file-based infection models. Instead of relying on stored executable files, these threats operate directly within system memory. This approach significantly reduces their visibility to conventional security tools.
Fileless malware often leverages legitimate system utilities to execute malicious code. By using trusted processes, it blends into normal system activity, making detection more challenging.
Initial infection typically occurs through phishing or malicious scripts. Once executed, the malware loads into memory and begins performing its intended actions without writing permanent files to disk.
The absence of disk artifacts makes forensic investigation more complex. Security teams must rely on behavioral analysis, process monitoring, and network traffic inspection to identify anomalies.
Memory-based malware is particularly effective in environments where endpoint protection is focused on file scanning rather than runtime behavior analysis. This has led to increased adoption of behavior-based detection systems.
Lateral Movement and Internal Network Exploitation
Once malware gains access to a system, one of its primary objectives is often lateral movement. This involves spreading to other devices within the same network environment to increase impact and access additional resources.
Lateral movement techniques include credential theft, exploitation of shared services, and abuse of administrative tools. Attackers may harvest login credentials from compromised systems and reuse them to access other devices.
Weak network segmentation significantly increases the effectiveness of lateral movement. In flat network architectures, malware can freely traverse systems without restriction, leading to widespread infection.
Some advanced malware includes automated discovery mechanisms that map internal networks. These tools identify high-value targets such as file servers, domain controllers, and backup systems.
Restricting lateral movement requires strict access control policies, network segmentation, and continuous monitoring of internal traffic flows.
Command and Control Infrastructure in Malware Operations
Many modern malware types rely on external communication channels known as command and control infrastructure. These systems allow attackers to remotely issue instructions, update malware behavior, and collect stolen data.
Command and control channels can take many forms, including encrypted communication over standard protocols, domain-based communication, or peer-to-peer architectures. The goal is to maintain reliable communication while avoiding detection.
Some malware uses domain generation algorithms to dynamically create communication endpoints. This makes it difficult for defenders to block malicious traffic, as the communication targets constantly change.
Disrupting command and control infrastructure is a key defensive strategy. Without communication, many malware types lose their ability to receive instructions or exfiltrate data.
Privilege Escalation and System Control Abuse
Privilege escalation is a critical phase in many malware attacks. After initial compromise, malware attempts to gain higher-level permissions within the system. This allows it to access restricted resources, modify system configurations, and disable security controls.
Privilege escalation can occur through software vulnerabilities, misconfigurations, or credential theft. Once elevated access is achieved, malware can operate with significantly fewer restrictions.
With administrative or system-level privileges, malware can disable antivirus tools, alter security policies, and install persistent components. This greatly increases the difficulty of removal.
Preventing privilege escalation requires strict user access management, regular patching, and monitoring for unusual permission changes.
Data Exfiltration Techniques and Stealth Communication
Data exfiltration refers to the unauthorized transfer of information from a compromised system to an external location. Modern malware uses a variety of techniques to accomplish this while avoiding detection.
Common methods include encrypted communication channels, disguised network traffic, and staged data transfer. Some malware compresses and fragments data to avoid triggering security alerts.
Exfiltration may occur gradually over time to avoid detection thresholds. Instead of transferring large volumes of data at once, malware may send small amounts periodically.
Monitoring outbound network traffic is essential for detecting potential exfiltration attempts. Unusual patterns or unexpected destinations can indicate malicious activity.
Defense Architecture and Layered Security Models
Effective malware defense requires a layered security approach that addresses multiple stages of the attack lifecycle. No single security control is sufficient to prevent all forms of malware.
Endpoint protection systems provide the first layer of defense by detecting known malicious behavior and blocking suspicious activity. However, these systems must be complemented by network monitoring and behavioral analysis tools.
Network segmentation limits the spread of malware by restricting communication between systems. This reduces the impact of lateral movement and containment failures.
Regular patch management ensures that known vulnerabilities are addressed before they can be exploited. Many malware infections rely on outdated software to gain initial access.
User awareness plays a critical role in preventing socially engineered attacks. Many malware infections originate from user interactions with malicious emails or downloads.
Incident Response and Recovery Frameworks
When malware infections occur, a rapid response is essential to minimize damage. Incident response frameworks typically involve detection, containment, eradication, and recovery phases.
Detection involves identifying abnormal behavior or confirmed infections. This may include system alerts, network anomalies, or user reports.
Containment focuses on isolating affected systems to prevent further spread. This may involve disconnecting devices from the network or restricting access permissions.
Eradication involves removing malware components from infected systems. This may require system reinstallation or restoration from clean backups.
Recovery focuses on restoring normal operations while ensuring that vulnerabilities have been addressed to prevent reinfection.
Continuous improvement is a key aspect of incident response. Post-incident analysis helps identify weaknesses and improve future defenses.
Long-Term Cybersecurity Adaptation Against Evolving Malware
Malware continues to evolve alongside technological advancements. As systems become more interconnected and complex, attackers develop new methods to exploit weaknesses.
Long-term defense strategies require continuous adaptation. Security systems must evolve to address emerging threats such as artificial intelligence-driven attacks, advanced persistent threats, and supply chain compromises.
Organizations must adopt proactive security models that focus not only on detection but also on prediction and prevention. This includes threat intelligence integration, behavioral analytics, and automated response mechanisms.
The future of malware defense depends on resilience, adaptability, and layered protection strategies that account for both known and unknown threats.
Conclusion
Malware remains one of the most persistent and adaptable threats in the digital landscape, continuously evolving alongside advancements in technology, connectivity, and user behavior. Its progression from simple experimental programs to highly structured, multi-layered attack systems reflects how deeply integrated it has become in modern cybercrime ecosystems. Understanding its behavior, categories, and operational methods is no longer optional for anyone relying on digital systems; it is a foundational requirement for maintaining security, stability, and operational continuity.
Across its many forms, malware demonstrates a consistent pattern: exploitation of weakness. These weaknesses may exist in software vulnerabilities, outdated systems, misconfigured networks, or even human behavior. Attackers often prioritize the easiest entry point rather than the most complex one, which is why social engineering remains one of the most effective infection methods. Even the most advanced technical defenses can be undermined if users are manipulated into granting access or executing malicious files. This interaction between human psychology and technical vulnerability is what makes malware especially difficult to eliminate.
The diversity of malware types highlights the breadth of modern cyber threats. Some variants focus on disruption, such as viruses and worms that spread rapidly and degrade system performance. Others, such as trojans and spyware, prioritize stealth and deception, operating quietly to steal data or establish hidden access points. More aggressive forms like ransomware introduce direct financial pressure by encrypting data and demanding payment, while botnets transform infected devices into components of larger coordinated attack infrastructures. Each type serves a different purpose, yet many are used together in layered attack chains that increase effectiveness and resilience against detection.
One of the most significant developments in recent years is the shift toward persistence and stealth. Malware is no longer designed to simply infect and execute; it is engineered to remain hidden for long durations while maintaining control over compromised systems. Techniques such as rootkits, fileless execution, and memory-based operations demonstrate how attackers prioritize invisibility over immediate impact. These methods make detection significantly more challenging, requiring advanced behavioral analysis rather than reliance on traditional signature-based tools. As a result, cybersecurity strategies must evolve continuously to keep pace with these increasingly subtle attack methods.
Another important trend is the professionalization and commercialization of malware operations. Cybercriminal activity is no longer limited to isolated individuals but often involves structured groups with specialized roles. Some focus on developing malware tools, others manage distribution networks, while additional teams handle negotiation and monetization. This division of labor has led to more efficient and scalable attack models, particularly in ransomware ecosystems where affiliate programs allow rapid expansion of attack campaigns across multiple targets and regions. The result is a cybercrime economy that mirrors legitimate business structures in its organization and efficiency.
The expansion of connected devices has further increased the complexity of malware threats. With the growth of internet-enabled systems across homes, industries, and infrastructure, the potential attack surface has expanded dramatically. Devices such as routers, cameras, sensors, and smart appliances often lack strong security mechanisms, making them easy targets for large-scale exploitation. Once compromised, these devices can be integrated into botnets or used as entry points into broader networks. This interconnected environment means that a single weak device can compromise the security of an entire system, highlighting the importance of holistic security design.
Despite the sophistication of modern malware, many infections still succeed due to fundamental security gaps. Unpatched software remains one of the most common entry points, as attackers frequently exploit known vulnerabilities that have not yet been addressed. Delayed updates, unsupported systems, and outdated applications create predictable weaknesses that malware can systematically target. This reinforces the importance of timely patch management as a critical defensive measure. Maintaining updated systems significantly reduces exposure to many common attack vectors and limits the effectiveness of automated exploitation tools.
Equally important is the role of network architecture in preventing malware spread. Flat and poorly segmented networks allow malware to move freely between systems once initial access is gained. In contrast, properly segmented environments restrict lateral movement and contain potential infections within limited zones. This containment strategy is essential in minimizing damage and preventing widespread compromise. Combined with access control mechanisms and continuous monitoring, network design becomes a key factor in reducing overall risk.
Data protection strategies also play a crucial role in mitigating malware impact. Regular backups, stored securely and tested for integrity, provide a critical recovery mechanism in cases of ransomware or destructive attacks. However, backups alone are not sufficient unless they are isolated from active systems, as modern malware often attempts to locate and encrypt backup data as well. A well-structured recovery plan ensures that organizations can restore operations without yielding to extortion demands or suffering prolonged downtime.
User awareness remains one of the most powerful defenses against malware infection. Many successful attacks originate from phishing messages, deceptive downloads, or social engineering tactics that exploit trust rather than technical flaws. Educating users to recognize suspicious activity, verify sources, and avoid unsafe interactions significantly reduces the likelihood of initial compromise. While technical defenses are essential, human vigilance often determines whether an attack succeeds or fails.
The ongoing challenge in malware defense lies in its constant evolution. Attackers continuously adapt their methods to bypass existing security measures, forcing defenders to develop equally dynamic strategies. This ongoing cycle creates a cybersecurity environment where static defenses quickly become outdated. As a result, modern security approaches increasingly rely on behavioral analysis, machine learning, and real-time threat intelligence to identify anomalies rather than relying solely on known threat signatures.
Incident response capability is another critical component of effective malware defense. Even with strong preventative measures, no system is completely immune to compromise. The ability to quickly detect, isolate, and recover from infections determines the overall impact of an attack. Structured response frameworks ensure that organizations can limit damage, restore functionality, and strengthen defenses based on lessons learned from each incident. This adaptive cycle of response and improvement is essential in maintaining long-term resilience.
Ultimately, malware represents a dynamic and evolving challenge that reflects the broader complexity of modern digital ecosystems. Its impact spans individual users, corporate environments, and critical infrastructure systems, making it a universal cybersecurity concern. While the threats continue to grow in sophistication, effective defense remains achievable through layered security strategies, continuous system maintenance, informed user behavior, and adaptive response mechanisms. The key lies not in eliminating risk entirely but in managing it intelligently, reducing exposure, and maintaining resilience in the face of ongoing and evolving threats.