The global digital environment continues to expand at a rapid pace, increasing reliance on interconnected systems across industries such as finance, healthcare, government services, retail, and critical infrastructure. As organizations migrate more operations to cloud-based platforms and hybrid environments, the attack surface for malicious activity expands significantly. This has led to a persistent imbalance between the number of skilled cybersecurity professionals available and the growing demand for security expertise. While hundreds of thousands of professionals are currently employed in information security roles in major economies, the demand continues to outpace supply by a significant margin. The shortage is not static; it is accelerating as new technologies emerge faster than training pipelines can produce qualified defenders. This imbalance has created one of the most competitive and opportunity-rich career landscapes in information technology, particularly for individuals specializing in threat detection, incident response, and security monitoring functions.
Evolution of Modern Cyber Threats and Defensive Requirements
Cyber threats have evolved from simple, opportunistic attacks into highly coordinated and sophisticated operations. Early security models relied heavily on perimeter-based defenses such as firewalls and signature-based detection systems, which were effective against known threats. However, modern attackers now frequently use polymorphic malware, zero-day vulnerabilities, fileless attacks, and social engineering techniques that bypass traditional detection methods. These changes have forced organizations to adopt more adaptive security strategies that emphasize continuous monitoring, behavioral analysis, and proactive threat hunting. Security teams are no longer only responding to alerts but are expected to identify anomalies in real time, correlate events across systems, and predict potential intrusion paths before damage occurs. This shift in defensive strategy has significantly influenced the design of modern cybersecurity training and certification frameworks, particularly those focused on analytical and operational security skills.
Purpose of an Intermediate Cybersecurity Analyst Certification
Within the cybersecurity career progression, foundational knowledge is typically established through entry-level training that covers basic networking concepts, security principles, and system protection techniques. However, as professionals transition into more specialized roles, there is a clear need for intermediate-level validation that bridges the gap between theoretical understanding and real-world operational capability. An intermediate cybersecurity analyst certification is designed to address this gap by focusing on applied security skills rather than purely conceptual knowledge. It evaluates an individual’s ability to interpret security data, identify suspicious activity, and respond effectively to incidents across diverse environments. Unlike foundational credentials, this level of certification emphasizes decision-making under uncertainty, situational awareness, and the ability to work with security tools in practical scenarios that reflect enterprise environments.
Rise of Behavioral Analytics in Security Operations
One of the most significant shifts in modern cybersecurity practices is the adoption of behavioral analytics as a core defensive strategy. Instead of relying solely on known threat signatures, security systems now analyze patterns of behavior across users, devices, and networks to identify anomalies that may indicate malicious activity. This includes monitoring login patterns, data access behaviors, network traffic flows, and system interactions to establish a baseline of normal activity. When deviations occur, they can signal potential compromise or insider threats. Behavioral analytics allows security teams to detect previously unknown attack vectors and respond more effectively to stealthy intrusion attempts. This approach has become central to the role of cybersecurity analysts, who must interpret complex data signals and distinguish between legitimate anomalies and genuine threats.
Core Structure of Intermediate Security Certification Frameworks
Intermediate cybersecurity certifications are typically structured around multiple domains that collectively represent the responsibilities of a security analyst in a professional environment. These domains generally include security operations, incident response, threat detection, vulnerability management, system security, and compliance-related assessment. Each domain reflects a specific aspect of cybersecurity work, requiring both technical knowledge and practical application. Security operations focus on continuous monitoring and analysis of system activity, while incident response emphasizes containment, mitigation, and recovery procedures following a security event. Threat and vulnerability management involves identifying weaknesses within systems and prioritizing remediation efforts based on risk levels. System security examines the configuration and hardening of applications and infrastructure, and compliance-related assessment ensures alignment with organizational and regulatory standards. Together, these domains create a comprehensive framework for evaluating analytical and operational competency.
Importance of Continuous Security Monitoring in Modern Environments
Continuous monitoring has become a foundational principle in enterprise cybersecurity strategy. Organizations can no longer rely on periodic security assessments or reactive incident handling due to the speed and sophistication of modern attacks. Instead, real-time visibility into network activity, system behavior, and user interactions is essential for maintaining a security posture. Security analysts play a critical role in interpreting and monitoring data, identifying unusual patterns, and escalating potential incidents for further investigation. This requires familiarity with various monitoring tools, log analysis techniques, and correlation methodologies that help transform raw data into actionable intelligence. Continuous monitoring also supports compliance requirements by ensuring that security events are recorded, analyzed, and reported in accordance with organizational policies and regulatory frameworks.
Role of Security Analysts in Organizational Defense Strategy
Security analysts serve as a central component of an organization’s defensive strategy by acting as the primary interface between security tools and operational decision-making. Their responsibilities typically include monitoring alerts generated by security systems, investigating potential incidents, and coordinating response actions with other IT teams. They must also maintain awareness of emerging threats and adapt defensive strategies accordingly. In many environments, security analysts are expected to understand both offensive and defensive perspectives, enabling them to anticipate attacker behavior and strengthen system defenses. This dual perspective enhances their ability to identify vulnerabilities before they are exploited and to respond effectively when incidents occur. As organizations become more digitally dependent, the importance of skilled analysts continues to increase, reinforcing the value of structured certification pathways.
Integration of Automation and Security Intelligence
Automation has become an increasingly important component of modern cybersecurity operations. Security teams often deal with large volumes of alerts and log data, making manual analysis inefficient and prone to error. Automation tools help streamline repetitive tasks such as log parsing, alert correlation, and initial threat classification. This allows analysts to focus on higher-level investigative work and strategic decision-making. Security intelligence platforms further enhance this capability by aggregating data from multiple sources and applying analytical models to detect patterns of malicious activity. The integration of automation and intelligence does not replace human analysts but rather augments their capabilities, enabling faster and more accurate responses to potential threats.
Foundational Skill Requirements for Intermediate Security Roles
To operate effectively in an intermediate cybersecurity role, professionals must develop a strong understanding of network behavior, system architecture, and security principles. This includes knowledge of how data flows across networks, how systems authenticate and authorize users, and how applications interact with underlying infrastructure. Analysts must also be familiar with common attack techniques and defensive countermeasures, enabling them to recognize indicators of compromise during investigations. Practical experience with monitoring tools, packet analysis, and log interpretation is essential for translating theoretical knowledge into operational capability. Additionally, strong analytical thinking skills are required to correlate disparate data points and construct a coherent understanding of security events.
Impact of Certification Pathways on Career Progression
Structured certification pathways play an important role in guiding professional development within cybersecurity. Entry-level certifications establish foundational knowledge, while intermediate certifications validate applied skills and readiness for operational roles. Advanced certifications further extend expertise into specialized or leadership domains. This tiered approach ensures that professionals build competency progressively, reducing skill gaps and improving workforce readiness. Employers often use certification frameworks as benchmarks for hiring and promotion decisions, making them a significant factor in career progression. Intermediate-level certifications, in particular, serve as a critical milestone for individuals transitioning from general IT roles into dedicated cybersecurity positions, as they demonstrate both technical capability and practical understanding of security operations.
Advanced Operational Security Environment in Modern Enterprises
Modern enterprise environments operate within highly dynamic digital ecosystems where infrastructure is distributed across on-premises systems, cloud platforms, and hybrid architectures. This complexity has significantly changed the operational responsibilities of cybersecurity professionals. Security is no longer a static layer applied at the perimeter but an integrated function embedded within every component of the digital environment. Systems continuously generate telemetry data from applications, endpoints, network devices, and user activities. The challenge for security operations teams lies not in collecting data but in interpreting it accurately and efficiently to identify meaningful threats. This requires a deep understanding of how systems behave under normal conditions, as well as the ability to recognize subtle deviations that may indicate malicious activity or system compromise.
Security Operations Centers and Real-Time Monitoring Frameworks
Security operations centers serve as centralized hubs for monitoring, detecting, and responding to cybersecurity incidents. These environments rely on continuous data ingestion from multiple sources, including network traffic logs, authentication systems, endpoint detection tools, and application monitoring platforms. Analysts working in these environments must process large volumes of alerts, prioritize incidents based on severity, and coordinate response actions. Real-time monitoring frameworks are designed to provide visibility into ongoing activities across the entire infrastructure. This includes identifying unauthorized access attempts, unusual data transfers, and anomalous system behavior. Analysts must distinguish between benign irregularities and genuine security threats, a process that requires both technical expertise and contextual awareness of organizational operations.
Threat Detection Through Behavioral Correlation Techniques
Traditional threat detection methods relied heavily on known signatures of malicious software or predefined rules. However, modern cybersecurity environments require more advanced detection methods that focus on behavioral correlation. This approach involves analyzing sequences of events across multiple systems to identify patterns that may indicate coordinated attacks. For example, repeated failed login attempts followed by successful access from an unusual location may suggest credential compromise. Similarly, unexpected data transfers during non-business hours could indicate data exfiltration attempts. Behavioral correlation techniques allow analysts to detect previously unknown threats by identifying relationships between seemingly unrelated events. This requires the ability to synthesize information from multiple data sources and apply analytical reasoning to complex scenarios.
Incident Response Lifecycle and Analytical Decision-Making
Incident response is a structured process designed to manage and mitigate cybersecurity events in a controlled and efficient manner. The lifecycle typically begins with identification, where potential security incidents are detected through monitoring systems or user reports. Once an incident is identified, analysts perform initial triage to determine its severity and scope. Containment strategies are then implemented to prevent further damage, followed by eradication of the threat and recovery of affected systems. Post-incident analysis is conducted to understand the root cause and improve future defenses. Each stage of this lifecycle requires careful decision-making, often under time-sensitive conditions. Analysts must balance the need for rapid response with the importance of accurate assessment to avoid unnecessary disruption to business operations.
Threat Intelligence Integration in Security Operations
Threat intelligence plays a crucial role in enhancing the effectiveness of security operations by providing contextual information about emerging threats, attacker behaviors, and known vulnerabilities. This intelligence is gathered from multiple sources, including internal logs, external feeds, and collaborative security networks. Analysts use this information to enrich their understanding of observed security events and to prioritize response efforts. For example, if an observed IP address is associated with known malicious activity, alerts generated from that source may be escalated more quickly. Threat intelligence also helps organizations anticipate future attack patterns and adjust their defensive strategies accordingly. The integration of intelligence into operational workflows transforms raw data into actionable insights, improving overall security posture.
Vulnerability Management and Risk Prioritization Strategies
Vulnerability management is a continuous process that involves identifying, assessing, and addressing security weaknesses within systems and applications. Organizations typically conduct regular scans to detect known vulnerabilities, which are then evaluated based on their potential impact and likelihood of exploitation. Not all vulnerabilities carry equal risk, so prioritization is essential for effective resource allocation. High-risk vulnerabilities that are actively exploited in the wild are typically addressed first, while lower-risk issues may be scheduled for later remediation. Risk prioritization also considers the criticality of affected systems, ensuring that vulnerabilities in high-value assets receive immediate attention. Security analysts play a key role in interpreting vulnerability data and supporting remediation decisions through risk-based analysis.
Log Analysis and Data Interpretation Techniques
Log analysis is a fundamental skill in cybersecurity operations, as logs provide detailed records of system activity, user behavior, and network communication. Analysts must be able to interpret logs from various sources, including operating systems, firewalls, intrusion detection systems, and application servers. Effective log analysis involves filtering large datasets, identifying relevant events, and correlating information across multiple sources. This process helps uncover patterns that may indicate security incidents, such as unauthorized access attempts or unusual system behavior. Analysts must also be able to distinguish between normal operational noise and meaningful security signals. Advanced interpretation techniques often involve the use of correlation rules, time-based analysis, and anomaly detection methodologies.
Network Traffic Analysis and Packet Inspection Methods
Understanding network traffic behavior is essential for identifying potential security threats within an infrastructure. Packet inspection techniques allow analysts to examine the contents of network communications to detect malicious activity. This includes analyzing source and destination addresses, protocol usage, payload contents, and transmission patterns. Network traffic analysis can reveal hidden communication channels used by attackers, such as command-and-control infrastructure or data exfiltration pathways. Analysts must be able to interpret both high-level flow data and detailed packet-level information to gain a complete understanding of network behavior. This skill is particularly important in environments where encrypted traffic is prevalent, requiring analysts to rely on metadata and behavioral indicators rather than direct content inspection.
Endpoint Security Monitoring and Host-Based Analysis
Endpoints represent one of the most common entry points for cyberattacks, making endpoint security monitoring a critical component of defensive strategies. Host-based analysis involves examining system-level activity on individual devices, including process execution, file modifications, registry changes, and user interactions. Security analysts must be able to identify suspicious behavior at the endpoint level, such as unauthorized software installation, privilege escalation attempts, or abnormal process activity. Endpoint detection tools provide continuous monitoring capabilities that help detect threats that may not be visible at the network level. By combining endpoint data with network and log information, analysts can construct a comprehensive view of security incidents.
Security Automation and Workflow Optimization in Analysis Operations
As the volume of security data continues to increase, automation has become essential for maintaining operational efficiency. Automation tools assist analysts by performing repetitive tasks such as data aggregation, alert triage, and initial classification of security events. This reduces the workload on human analysts and allows them to focus on more complex investigative tasks. Workflow optimization involves designing efficient processes for handling security incidents, ensuring that alerts are properly escalated and resolved promptly. Automation also supports consistency in response actions, reducing the likelihood of human error. However, effective automation requires careful configuration to avoid false positives and ensure that critical threats are not overlooked.
Role-Based Responsibilities in Cybersecurity Operations Teams
Cybersecurity operations teams are typically structured around specialized roles that focus on different aspects of security management. Analysts are responsible for monitoring and investigating security events, while engineers focus on designing and maintaining security infrastructure. Threat intelligence specialists analyze external threat data to identify potential risks, and incident responders manage active security breaches. Each role contributes to the overall security posture of the organization, and effective collaboration between roles is essential for maintaining strong defenses. Analysts often serve as the first line of detection, making their ability to accurately interpret data and escalate incidents critical to the success of the entire security operation.
Skill Progression and Practical Competency Development
Developing practical cybersecurity competency requires continuous exposure to real-world scenarios and hands-on experience with security tools. Theoretical knowledge alone is insufficient for effective performance in operational environments, where analysts must make decisions based on incomplete or rapidly changing information. Skill progression typically involves moving from basic system understanding to advanced analytical reasoning and threat detection capabilities. This includes learning how to interpret complex datasets, recognize attack patterns, and respond effectively under pressure. Over time, professionals build intuition for identifying security anomalies, allowing them to operate more efficiently and accurately in high-pressure environments.
Cybersecurity Career Pathways in Analytical Security Roles
The cybersecurity field offers a wide range of specialized career pathways, particularly within analytical and defensive security domains. As organizations mature their security posture, roles become more defined and segmented based on operational focus. Analytical security roles typically revolve around interpreting security data, identifying threats, and supporting organizational defense strategies. These roles often serve as entry points into more advanced positions such as threat intelligence, security engineering, and security architecture. Career progression is rarely linear; instead, it is shaped by exposure to different security domains, hands-on experience, and the ability to adapt to evolving threat landscapes. Professionals who begin in monitoring and analysis roles gradually develop a deeper understanding of system behavior, attacker methodologies, and organizational risk structures. Over time, this enables them to transition into more strategic responsibilities that influence security design and policy decisions.
How Organizations Evaluate Security Analysts in Hiring
Organizations assess security analysts based on a combination of technical competence, analytical thinking ability, and situational judgment. Technical evaluation typically focuses on understanding network protocols, system behavior, and security monitoring principles. However, equal importance is placed on how candidates approach problem-solving scenarios. Employers often look for evidence of structured thinking when analyzing ambiguous security events, as real-world incidents rarely present clear or complete information. Analytical reasoning is assessed through the ability to correlate disparate data points and identify meaningful patterns. Additionally, behavioral evaluation plays a role, with emphasis on communication clarity, adaptability, and decision-making under pressure. Employers prefer candidates who demonstrate not only knowledge of security concepts but also the ability to apply them effectively in dynamic environments where threats evolve rapidly.
Operational Tools and Data Ecosystem in Security Analysis
Security analysis relies on a diverse ecosystem of tools designed to collect, process, and interpret security-related data. These tools span multiple categories, including network monitoring systems, endpoint detection platforms, log aggregation systems, and intrusion detection solutions. Each tool contributes a different layer of visibility into system activity. The challenge for analysts lies in synthesizing information from these sources into a coherent understanding of security posture. Data normalization and correlation are essential processes that enable analysts to connect events across different systems. Without this integration, individual alerts may appear isolated and lack context. A well-structured operational environment ensures that data flows efficiently between systems, allowing for timely detection and investigation of potential security incidents.
Frameworks That Shape Modern Security Operations
Security operations are guided by structured frameworks that provide standardized approaches to threat detection, response, and risk management. These frameworks help organizations maintain consistency in their security practices and ensure alignment with industry best practices. Structured models for understanding attacker behavior and system vulnerabilities allow analysts to categorize threats and prioritize responses effectively. Framework-based thinking also supports better communication within security teams, as it provides a shared language for describing incidents and vulnerabilities. By mapping observed behavior to established categories, analysts can more quickly identify attack patterns and determine appropriate response strategies. These frameworks evolve continuously to reflect changes in the threat landscape, ensuring that security practices remain relevant in the face of emerging attack techniques.
Cloud-Driven Security Monitoring and Shared Responsibility
The widespread adoption of cloud computing has significantly transformed security monitoring practices. In cloud environments, responsibility for security is distributed between service providers and customers, creating a shared responsibility model. This requires analysts to understand which aspects of security are managed externally and which remain under organizational control. Cloud platforms generate extensive telemetry data, including access logs, configuration changes, and resource utilization metrics. Analysts must interpret this data to detect unauthorized activity, misconfigurations, or potential exposure risks. The dynamic nature of cloud infrastructure, where resources can be created or destroyed rapidly, introduces additional complexity into monitoring processes. Security teams must adapt their strategies to account for this elasticity while maintaining consistent visibility across all environments.
Integration of DevSecOps in Security Analysis Workflows
Modern software development practices increasingly incorporate security considerations throughout the development lifecycle. This integration ensures that security is not treated as a final checkpoint but as an ongoing process embedded within development and deployment workflows. Security analysts play a role in supporting this integration by identifying vulnerabilities early in the development cycle and collaborating with development teams to address them. Automated security testing, continuous integration pipelines, and configuration validation processes all contribute to reducing the introduction of vulnerabilities into production environments. Analysts must understand how applications are built and deployed to effectively identify potential security weaknesses. This requires familiarity with both development practices and operational security principles, bridging the gap between traditionally separate disciplines.
Metrics and Performance Indicators in Security Operations
Measuring the effectiveness of security operations requires the use of defined metrics and performance indicators. These metrics provide insight into how efficiently security teams are detecting, responding to, and resolving incidents. Common indicators include detection speed, response time, false positive rates, and incident resolution duration. By analyzing these metrics, organizations can identify areas for improvement and optimize their security workflows. Performance measurement also supports resource allocation decisions, ensuring that security teams are appropriately staffed and equipped to handle workload demands. Analysts contribute to this process by accurately documenting incidents and ensuring that data used for measurement is reliable and consistent. Over time, these metrics help organizations refine their security strategies and improve overall operational maturity.
Communication and Reporting in Security Teams
Effective communication is a critical component of cybersecurity operations. Security analysts must be able to convey complex technical information in a clear and structured manner to both technical and non-technical stakeholders. Reporting involves documenting security incidents, summarizing findings, and providing actionable recommendations. These reports are often used by management teams to make decisions regarding risk mitigation and resource allocation. Clear communication is also essential during active incidents, where timely and accurate information sharing can significantly impact response effectiveness. Analysts must balance technical detail with clarity, ensuring that their communication is both precise and understandable. Strong communication skills enhance collaboration within security teams and improve overall organizational response capability.
Hands-On Skill Building Through Practical Environments
Practical experience plays a central role in developing cybersecurity expertise. Hands-on environments allow analysts to apply theoretical knowledge in controlled settings that simulate real-world scenarios. These environments typically include simulated networks, virtual systems, and controlled attack scenarios designed to replicate common threat patterns. Through repeated exposure to these environments, analysts develop familiarity with security tools, detection techniques, and investigative methodologies. Practical skill development also improves intuition for identifying anomalies and understanding attacker behavior. Over time, this experiential learning process builds confidence and competence, enabling analysts to operate effectively in live operational environments where the stakes are significantly higher.
Emerging Technologies Reshaping Security Analysis
The cybersecurity landscape is continuously evolving due to the introduction of emerging technologies such as artificial intelligence, machine learning, and advanced automation systems. These technologies are increasingly being integrated into security operations to enhance detection capabilities and reduce manual workload. Artificial intelligence systems can analyze large volumes of data to identify patterns that may not be immediately visible to human analysts. Machine learning models can adapt to changing threat patterns, improving detection accuracy over time. However, these technologies also introduce new challenges, including model interpretability, data quality concerns, and potential adversarial manipulation. Security analysts must understand how these technologies function in order to effectively interpret their outputs and validate their findings.
Long-Term Career Development in Security Analytics
Long-term career development in cybersecurity analytics involves continuous learning and adaptation to evolving technologies and threat landscapes. Professionals in this field often progress by expanding their expertise across multiple domains, including threat intelligence, incident response, and security architecture. Career advancement is influenced by both technical depth and strategic understanding of organizational security needs. As professionals gain experience, they may transition into leadership roles where they are responsible for guiding security strategy and managing operational teams. Continuous skill development is essential, as the cybersecurity field changes rapidly in response to new attack techniques and technological advancements. Over time, experienced analysts develop a holistic understanding of security ecosystems, enabling them to contribute to both tactical operations and long-term strategic planning.
Conclusion
The role of cybersecurity within modern digital ecosystems has shifted from being a specialized technical function to a foundational requirement for nearly every organization that relies on technology. As systems become more interconnected and data-driven, the importance of skilled professionals who can interpret security signals, respond to incidents, and anticipate threats continues to grow. This evolution has created a sustained demand for practitioners who not only understand theoretical security concepts but can also apply them in real operational environments where decisions must often be made quickly and with incomplete information. The growing complexity of digital infrastructure has made cybersecurity analysis one of the most critical components of organizational resilience.
One of the defining characteristics of this field is its constant state of change. Threat actors continuously refine their techniques, moving beyond traditional attack methods and adopting more sophisticated approaches that exploit both technical vulnerabilities and human behavior. As a result, defensive strategies must evolve at an equally rapid pace. Security professionals are now expected to work in environments where static defense mechanisms are no longer sufficient. Instead, they must rely on continuous monitoring, behavioral analysis, and adaptive response strategies to maintain effective protection. This shift has fundamentally changed how organizations approach cybersecurity training and skill validation, placing greater emphasis on applied knowledge rather than purely theoretical understanding.
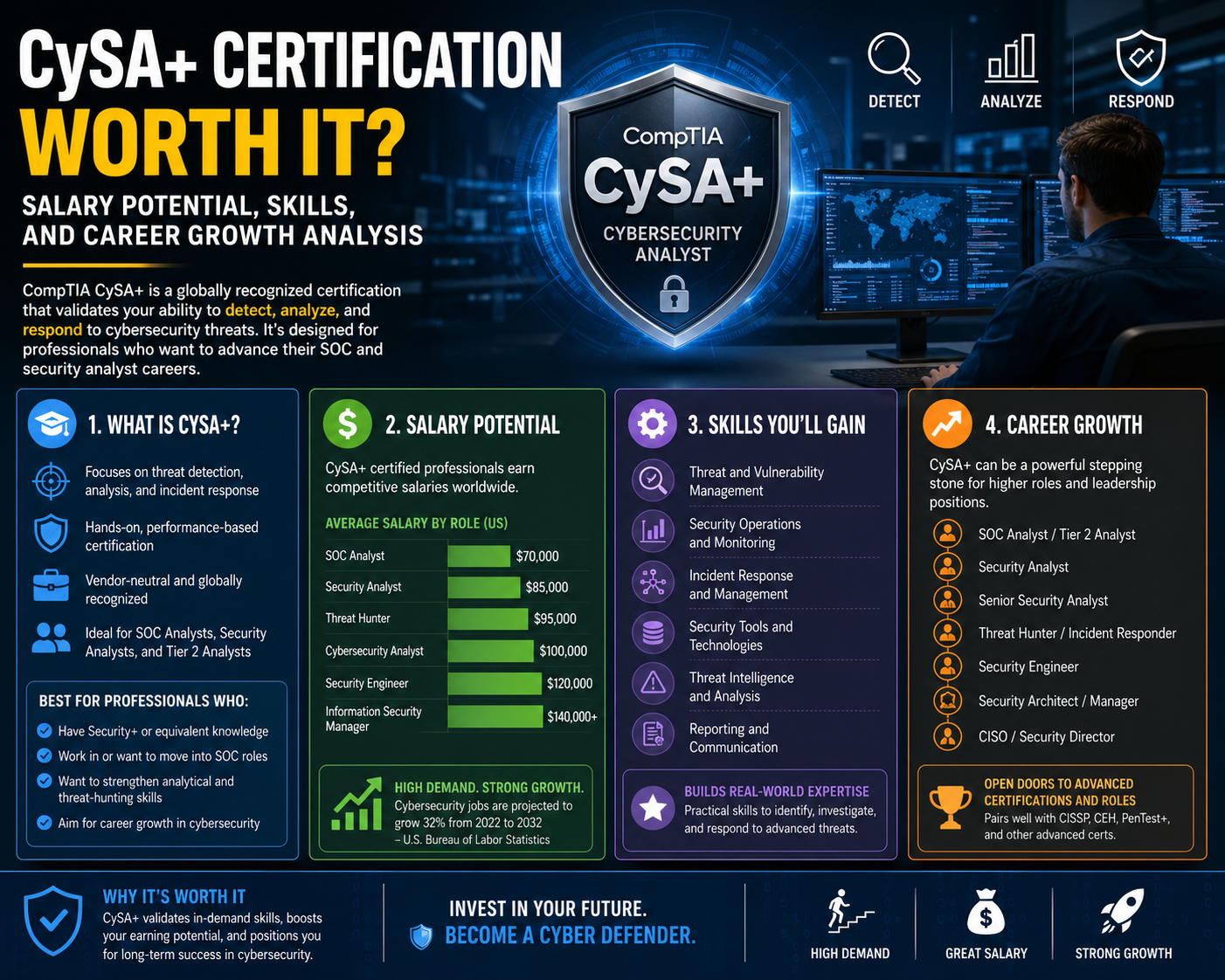
In this context, structured certification pathways have become an important mechanism for validating professional competency. Certifications that focus on intermediate-level analytical and operational security skills play a particularly important role in bridging the gap between foundational knowledge and advanced specialization. They are designed to assess an individual’s ability to work with real-world security tools, interpret complex data sets, and respond effectively to security incidents. Unlike entry-level credentials, which primarily focus on awareness and basic principles, intermediate certifications emphasize practical application and decision-making under realistic conditions. This makes them especially relevant for roles such as security analysts, threat monitors, and incident response personnel.
The value of such certifications is closely tied to their alignment with industry needs. Organizations are not simply looking for individuals who understand cybersecurity concepts in isolation; they require professionals who can operate effectively within live environments where threats are constantly evolving. This includes the ability to analyze network traffic, interpret system logs, identify anomalous behavior, and coordinate response actions across multiple teams. Professionals who can demonstrate these capabilities are better positioned to contribute meaningfully to organizational security efforts and are often considered strong candidates for advancement into more specialized or senior roles.
Another important factor contributing to the relevance of cybersecurity certifications is the increasing integration of automation and advanced analytics into security operations. While automation has improved the efficiency of threat detection and response processes, it has not eliminated the need for human expertise. On the contrary, it has shifted the focus of human analysts toward higher-level interpretation, validation, and decision-making. Automated systems can process large volumes of data and identify potential threats, but they still require skilled professionals to evaluate context, reduce false positives, and determine appropriate responses. This human-machine collaboration has become a defining feature of modern security operations, reinforcing the importance of analytical skills in cybersecurity roles.
Career progression within cybersecurity is also closely linked to the development of analytical and operational expertise. Professionals typically begin with foundational roles that provide exposure to basic security concepts and tools. Over time, they move into more specialized positions that require deeper technical knowledge and greater responsibility. This progression is not solely dependent on experience but is also influenced by the ability to demonstrate validated skills through structured assessments and practical performance. As professionals advance, they are often expected to take on broader responsibilities, including designing security strategies, leading incident response efforts, and guiding organizational risk management initiatives.
The demand for cybersecurity professionals is further amplified by the global nature of digital infrastructure. Organizations operate across multiple regions, platforms, and regulatory environments, creating complex security challenges that require coordinated responses. This global complexity increases the need for standardized skill frameworks that can be recognized across industries and geographic boundaries. Certifications that align with widely accepted security principles help establish a common baseline of competency, enabling organizations to evaluate candidates consistently and effectively regardless of their background or location.
At the same time, the cybersecurity field offers significant opportunities for long-term professional growth. As individuals gain experience and deepen their understanding of security operations, they can transition into roles that involve strategic planning, threat intelligence analysis, and security architecture design. These advanced roles require not only technical expertise but also the ability to understand organizational priorities and align security strategies accordingly. Professionals who continue to develop their skills and adapt to new technologies are well-positioned to remain relevant in a rapidly evolving industry.
Another key aspect of cybersecurity careers is the importance of continuous learning. Unlike some technical fields where foundational knowledge remains relatively stable, cybersecurity requires ongoing adaptation due to the constant emergence of new threats and technologies. Professionals must stay informed about changes in attack methodologies, updates to security tools, and evolving best practices. This continuous learning process is essential for maintaining effectiveness in operational roles and ensuring that defensive strategies remain aligned with current threat landscapes.
Ultimately, cybersecurity is not a static discipline but a dynamic and continuously evolving field that requires a balanced combination of deep technical knowledge, strong analytical thinking, and consistent hands-on practical experience across real-world environments. The increasing sophistication, automation, and coordination of modern cyber threats ensure that the global demand for skilled security professionals will not only continue to grow but will also expand into new and more specialized domains as technology advances further into cloud-native systems, distributed architectures, and AI-driven infrastructures. Organizations are no longer dealing with isolated or predictable attack patterns; instead, they face highly adaptive adversaries who continuously refine their methods to bypass traditional defenses, exploit human behavior, and target complex system interdependencies.
In this environment, individuals who actively invest in developing their analytical capabilities, strengthening their understanding of system behavior, and gaining structured, hands-on exposure to security monitoring tools and incident response processes are significantly better positioned to succeed. Practical experience remains a defining factor in professional readiness because cybersecurity is fundamentally operational in nature, requiring real-time interpretation of data, rapid decision-making under pressure, and the ability to correlate seemingly unrelated events into meaningful security insights. At the same time, formal validation of skills through recognized and structured learning pathways helps establish credibility, ensuring that professionals can demonstrate both theoretical understanding and applied competence in measurable terms.
The ability to interpret complex security data is becoming increasingly essential as modern environments generate vast volumes of logs, alerts, and behavioral signals across distributed systems. Security professionals must be capable of distinguishing between normal operational noise and genuine indicators of compromise, often within compressed timeframes where delayed responses can lead to significant organizational impact. This requires not only familiarity with security tools and technologies but also the development of intuition built through repeated exposure to varied incident scenarios. Over time, experienced professionals begin to recognize subtle deviations in system behavior that may indicate early-stage attacks or reconnaissance activity, enabling proactive rather than purely reactive defense strategies.