In modern distributed computing environments, applications are no longer isolated systems running on a single machine. Instead, they are composed of multiple services, microservices, containers, and serverless functions that constantly interact with each other and external systems. Each of these components often requires access to sensitive information such as authentication credentials, API tokens, database passwords, encryption keys, and configuration secrets. Managing this sensitive information securely is one of the most critical challenges in cloud-native architectures.
Traditional approaches to handling secrets were built around static environments where applications were deployed on fixed infrastructure. In those environments, credentials were often stored in configuration files or embedded directly into application code. While this approach may have worked in simpler systems, it becomes highly insecure and unmanageable in modern cloud ecosystems where applications scale dynamically, and environments change rapidly.
Cloud secret management introduces a centralized, secure, and automated way to store and retrieve sensitive data. Instead of distributing credentials across multiple systems, secrets are stored in a dedicated secure repository. Applications retrieve them only when needed, using controlled and authenticated requests. This reduces exposure risk and ensures that sensitive data is not permanently stored in application code or configuration files.
A key principle in cloud secret management is the separation of concerns. Applications focus on business logic, while secret storage systems handle encryption, access control, and lifecycle management. This separation significantly improves security posture and operational efficiency.
Security Challenges in Traditional Credential Storage Methods
One of the most significant risks in legacy systems is the use of hardcoded credentials. When sensitive keys are embedded directly into application source code, they become vulnerable to accidental exposure. Code repositories, build pipelines, logs, and shared development environments can unintentionally expose these credentials to unauthorized individuals. Once exposed, these credentials can be exploited to gain access to critical systems.
Another major issue is the manual distribution of secrets across environments. In many organizations, development, testing, and production environments require different credentials. Managing these separately often leads to duplication, inconsistency, and human error. Developers may reuse the same credentials across environments for convenience, which creates unnecessary security dependencies.
Manual rotation of credentials is also a major operational challenge. Security best practices recommend frequent rotation of passwords and access keys to reduce the risk of compromise. However, in traditional systems, updating credentials across multiple services is time-consuming and error-prone. As a result, many organizations delay rotation cycles, leaving long-lived credentials active for extended periods.
Additionally, storing secrets in configuration files introduces another layer of risk. These files may be accidentally committed to version control systems or exposed through misconfigured storage permissions. Even when encrypted at rest, improper access control can still lead to unauthorized retrieval.
These challenges demonstrate the need for a more structured and automated approach to secret management that minimizes human involvement and reduces the risk of exposure.
Centralized Secret Storage and Encryption Mechanisms in Cloud Systems
A modern cloud secret management system provides centralized storage for all sensitive credentials. Instead of scattering secrets across multiple applications and environments, they are stored in a secure, encrypted repository. This centralization ensures consistency and simplifies governance.
Encryption plays a fundamental role in protecting stored secrets. Data is encrypted before being stored and decrypted only when accessed by authorized entities. This ensures that even if the underlying storage system is compromised, the data remains unreadable without proper authorization.
Encryption keys are typically managed separately from the secrets themselves. This separation adds an additional layer of protection, ensuring that access alone is not sufficient to decrypt sensitive information. The encryption process is transparent to applications, meaning developers do not need to implement encryption logic manually.
Centralized storage also eliminates duplication. Instead of maintaining multiple copies of the same credential across services, a single source of truth is maintained. This reduces inconsistencies and ensures that updates to secrets are immediately reflected across all dependent systems.
By combining encryption with centralized storage, cloud secret management systems provide a secure foundation for handling sensitive information in complex environments.
Identity-Based Access Control and Authorization Frameworks
Access control is one of the most critical components of secure secret management. Identity-based access control ensures that only authorized applications, services, or users can retrieve specific secrets. Instead of relying on static credentials for authentication, modern systems use dynamic identity verification mechanisms.
Each request for a secret is evaluated against predefined access policies. These policies define which identities are allowed to access which secrets and under what conditions. This allows organizations to enforce the principle of least privilege, ensuring that each component only has access to the minimum data required for its operation.
Fine-grained access control policies can restrict access at multiple levels. For example, a microservice responsible for processing payments may only be allowed to access payment gateway credentials, while another service handling analytics may be restricted to different data sources.
Temporary identity credentials are often used instead of long-term static keys. These temporary credentials are generated dynamically and expire after a short period. This reduces the risk of credential leakage and limits the impact of compromised credentials.
Identity-based access control also improves traceability. Every access request can be linked to a specific identity, making it easier to audit and monitor usage patterns across the system.
Encryption Integration and Secure Key Management Practices
Encryption integration is a core component of secure secret management systems. Rather than treating encryption as a separate process, it is embedded directly into the storage and retrieval lifecycle of secrets. This ensures that all sensitive data is automatically encrypted without requiring manual intervention from developers.
Encryption keys are managed through dedicated key management systems that operate independently from application logic. This separation ensures that even if application-level security is compromised, encryption keys remain protected.
Key rotation is another important aspect of encryption management. Regular rotation of encryption keys reduces the risk of long-term key compromise. Modern systems support automated key rotation, allowing new keys to be generated and applied without disrupting application functionality.
Organizations can choose between system-managed encryption keys or customer-controlled keys. System-managed keys simplify operations, while customer-controlled keys provide greater control over access policies and auditing capabilities.
Encryption integration ensures that sensitive data remains protected at all stages, including storage, transmission, and retrieval.
Lifecycle Management of Sensitive Credentials and Automation
Secret lifecycle management is essential for maintaining long-term security. Secrets are not static entities; they must be created, updated, rotated, and eventually retired. Without automation, managing this lifecycle becomes complex and prone to errors.
Automated rotation ensures that credentials are periodically updated without requiring manual intervention. When a secret is rotated, dependent applications automatically receive the updated version without downtime or service disruption.
Version control is another important feature of lifecycle management. It allows multiple versions of a secret to exist simultaneously, ensuring smooth transitions during updates. Applications can continue using older versions temporarily while migrating to new ones.
Expiration policies help enforce security by ensuring that unused or outdated secrets are automatically removed from the system. This reduces the attack surface and prevents forgotten credentials from remaining active indefinitely.
Automation plays a key role in ensuring consistency across large-scale environments where manual management would be impractical.
Integration with Cloud Identity and Temporary Credential Systems
Modern cloud environments rely heavily on identity-based access systems rather than static credentials. Applications are assigned temporary identities that define their permissions and access scope. These identities are dynamically generated and expire after a defined period.
This approach eliminates the need for long-term access keys in most scenarios. Instead, applications assume roles that grant them temporary access to required resources, including secrets.
Integration between secret management systems and identity frameworks ensures seamless authentication and authorization. When an application requests a secret, its identity is verified, and access is granted only if it matches predefined policies.
This dynamic approach significantly improves security by reducing the reliance on permanent credentials and limiting exposure windows.
Secure Retrieval and Runtime Consumption of Secrets
When an application requires a secret, it retrieves it at runtime through a secure request. The secret management system validates the request, checks permissions, decrypts the secret, and returns it securely to the application.
Many systems support in-memory caching of secrets to reduce repeated requests and improve performance. Cached secrets are stored temporarily and refreshed automatically when updated.
Secrets are never permanently stored within application code or configuration files. Instead, they are retrieved dynamically when needed and used immediately within the application lifecycle.
This runtime-based approach ensures that sensitive data is only available when required and reduces the risk of exposure during deployment or storage.
Monitoring, Logging, and Auditability in Secret Governance
Monitoring and auditability are essential for maintaining visibility into secret usage. Every access request, modification, or deletion event is recorded in detailed logs. These logs provide a complete history of secret interactions across the system.
Audit logs help security teams identify unusual behavior, such as unauthorized access attempts or abnormal usage patterns. Monitoring systems can generate alerts when suspicious activity is detected.
This level of visibility is critical for compliance requirements and internal governance. It allows organizations to demonstrate that sensitive data is being handled securely and according to defined policies.
Architectural Considerations for Secure Cloud Secret Systems
Designing secure systems around secret management requires careful architectural planning. Applications should be structured to avoid direct dependency on static credentials and instead rely on dynamic retrieval mechanisms.
Network security is also important. Communication between applications and secret management systems should be encrypted and restricted to authorized channels only.
Scalability must be considered in large distributed systems where thousands of secret requests may occur simultaneously. Efficient caching mechanisms and regional replication strategies help maintain performance while ensuring availability.
A well-designed architecture ensures that security does not become a bottleneck while maintaining strong protection for sensitive data.
Evolution of Secret Management in Modern Cloud Ecosystems
Secret management has evolved significantly from simple credential storage systems to highly automated, identity-driven platforms. Early systems relied heavily on manual processes and static configuration files, which were prone to errors and security risks.
As cloud adoption increased, the need for dynamic, scalable, and secure secret handling became more critical. Modern systems now integrate deeply with identity frameworks, encryption services, and automation tools.
The rise of microservices, container orchestration, and serverless computing has further increased the importance of centralized secret management. Applications are now ephemeral, constantly scaling, and distributed across multiple environments, making static credential storage impractical.
This evolution reflects a broader shift toward security-first design principles in cloud architecture, where secret management is treated as a foundational component rather than an afterthought.
Architectural Role of AWS Secrets Manager in Modern Cloud Ecosystems
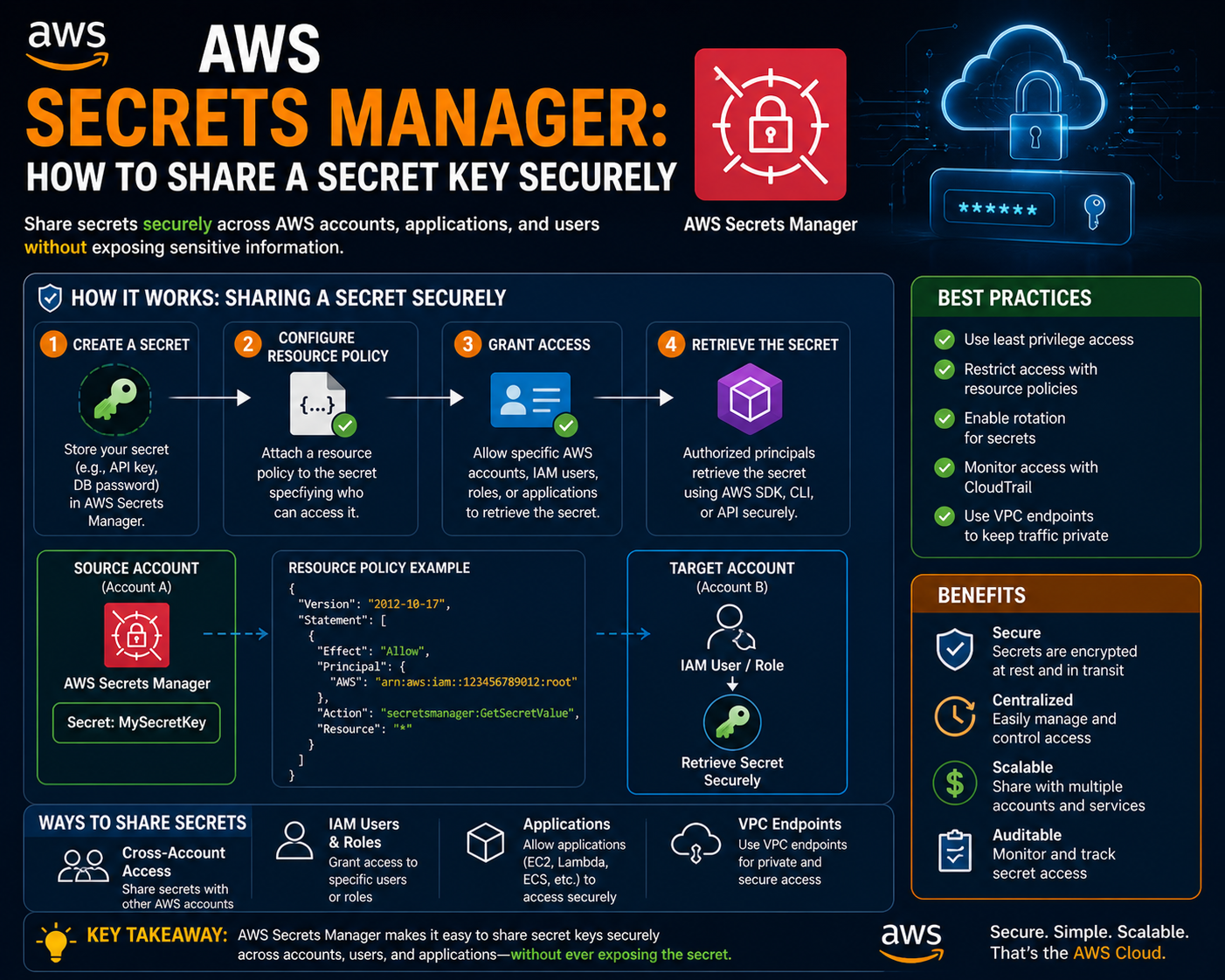
In modern cloud-native architectures, secret management is not an isolated security tool but a foundational service integrated deeply into application design, deployment pipelines, and runtime execution environments. AWS Secrets Manager operates as a centralized control plane for sensitive data, ensuring that credentials, tokens, and encryption keys are not embedded directly into applications or distributed across insecure configuration layers.
The architectural role of this service is to act as a secure intermediary between applications and sensitive resources. Instead of applications storing credentials locally, they request secrets dynamically at runtime through authenticated calls. This design introduces a clear separation between application logic and security management, reducing the risk of exposure and simplifying operational maintenance.
In distributed systems where microservices communicate across multiple accounts and regions, centralized secret management ensures consistency. Each service retrieves only the credentials it is authorized to access, and policies enforce strict boundaries between workloads. This reduces lateral movement risks in the event of a compromise and strengthens the overall security posture of the system.
Secure Storage Model and Encryption Layer Design
At the core of AWS Secrets Manager is a secure storage model where all secrets are encrypted before being persisted. The encryption process is handled using a dedicated key management layer that ensures secrets remain protected both at rest and during transit. Each secret is stored as an encrypted object, and decryption only occurs when a valid, authorized request is made.
The encryption layer is tightly integrated with AWS Key Management Service, which provides centralized control over encryption keys. These keys can either be managed by the platform or defined by the customer for additional control. This dual-model approach allows organizations to balance operational simplicity with regulatory compliance requirements.
Each secret can have multiple versions, allowing updates without disrupting running applications. When a secret is modified or rotated, the system maintains historical versions for controlled transitions. This versioning model ensures backward compatibility and reduces downtime during credential updates.
The storage architecture is designed for high availability and redundancy. Secrets are replicated across multiple availability zones within a region to ensure durability and resilience against infrastructure failures.
Integration with Identity and Access Management Systems
AWS Secrets Manager is deeply integrated with identity-based access control systems, ensuring that every request for a secret is authenticated and authorized before access is granted. Instead of relying on static credentials, applications use identity-based roles that define their permissions and scope of access.
When a service requests a secret, the system evaluates its identity against a set of predefined policies. These policies determine whether the service is allowed to access the requested secret and under what conditions. This ensures that sensitive data is only accessible to authorized workloads.
The principle of least privilege is enforced through granular policy definitions. Each application or microservice is granted access only to the specific secrets it requires for operation. This reduces the risk of unauthorized access and limits the impact of compromised components.
Temporary credentials generated through identity systems further enhance security. These credentials expire after a short duration, reducing the risk associated with long-lived authentication keys. This dynamic approach aligns with modern cloud security practices where static credentials are minimized or eliminated entirely.
Automatic Secret Rotation and Lifecycle Orchestrator
One of the most powerful features of AWS Secrets Manager is automated secret rotation. This capability ensures that credentials are regularly updated without manual intervention, reducing the risk of credential compromise over time.
Rotation workflows are typically implemented using serverless execution environments that handle the update process. When a rotation event is triggered, the system generates a new secret version, updates the target service, and validates the new credentials before finalizing the change. This ensures a seamless transition without service disruption.
For managed services such as relational databases, rotation can be fully automated with predefined templates. The system coordinates the creation of new credentials, updates the database, and synchronizes the changes with dependent applications.
Custom rotation workflows are also supported for third-party systems and non-standard applications. In these cases, serverless functions define the logic required to update external systems and propagate new credentials.
Lifecycle management extends beyond rotation to include expiration and archival policies. Secrets that are no longer in use can be automatically retired, reducing clutter and minimizing security exposure.
High-Performance Retrieval and Caching Mechanisms
In large-scale distributed systems, performance is a critical consideration for secret retrieval. Frequent API calls to retrieve secrets can introduce latency and increase operational costs. To address this, AWS Secrets Manager supports client-side caching mechanisms that temporarily store retrieved secrets in memory.
Caching reduces the number of API requests required for frequently accessed secrets, improving performance and reducing service overhead. Cached secrets are automatically refreshed based on predefined expiration policies or when updates occur.
The caching layer is typically implemented within application SDKs, allowing seamless integration without additional configuration complexity. This ensures that developers can retrieve secrets using simple API calls while benefiting from optimized performance behind the scenes.
However, caching introduces a balance between performance and freshness. Systems must ensure that cached secrets are updated promptly when changes occur to avoid inconsistencies. This is achieved through version tracking and invalidation mechanisms that synchronize cached data with the central secret store.
Multi-Account and Multi-Region Secret Replication Strategies
In enterprise environments, applications often span multiple accounts and geographic regions. AWS Secrets Manager supports cross-account and cross-region replication to ensure consistent access to secrets across distributed architectures.
Replication allows secrets to be securely copied from a primary region to secondary regions. This ensures high availability and disaster recovery capabilities in case of regional outages. Each replicated secret remains encrypted and maintains its access control policies.
Cross-account access is enabled through identity-based trust relationships. This allows services in one account to securely retrieve secrets stored in another account without exposing credentials directly.
Replication strategies must be carefully designed to balance availability, consistency, and security. Sensitive data may require stricter replication controls depending on regulatory requirements or organizational policies.
Cost Structure and Resource Optimization Considerations
AWS Secrets Manager operates on a usage-based pricing model where costs are associated with the number of stored secrets and API requests. Each stored secret incurs a monthly charge, while API calls are billed based on usage volume.
Although this model introduces operational costs, it provides significant value in terms of automation, security, and scalability. Organizations must evaluate their secret usage patterns to optimize cost efficiency.
Frequent secret retrieval can increase costs, which is why caching mechanisms are important for optimization. By reducing redundant API calls, systems can significantly lower operational expenses.
Additional costs may arise from encryption key usage and serverless rotation functions. These components are optional but often necessary for advanced security configurations.
Cost allocation tagging allows organizations to track secret usage across teams, applications, or environments. This improves financial transparency and helps identify optimization opportunities.
Error Handling, Reliability, and Fault Tolerance Mechanisms
In distributed systems, reliability is essential for secret retrieval operations. AWS Secrets Manager is designed with fault-tolerance mechanisms that ensure high availability even under adverse conditions.
If a secret retrieval request fails due to transient network issues, applications are typically designed to retry the request using exponential backoff strategies. This prevents system overload while improving success rates.
Service-level redundancy ensures that secrets remain accessible even if individual infrastructure components fail. Replication across multiple availability zones enhances durability and reduces downtime risk.
Applications must also implement fallback strategies for critical secrets. In some cases, cached secrets may be used temporarily if real-time retrieval is unavailable, although this must be handled carefully to avoid security risks.
Logging and monitoring systems capture all errors related to secret retrieval, enabling rapid diagnosis and resolution of issues.
Security Threat Models and Risk Mitigation Strategies
Secret management systems must be designed with potential threat models in mind. One of the most common risks is credential leakage through misconfigured applications or exposed logs. AWS Secrets Manager mitigates this by ensuring secrets are never exposed in plain text unless explicitly retrieved by authorized entities.
Another threat is unauthorized access through compromised identities. This is mitigated through strict identity-based access control policies and temporary credential mechanisms that limit exposure duration.
Insider threats are addressed through audit logging and access monitoring, which track all secret interactions. This ensures accountability and enables the detection of unusual behavior patterns.
Network-level threats are mitigated through encrypted communication channels and restricted access paths. Secrets are only transmitted over secure connections, reducing the risk of interception.
Integration with Serverless and Containerized Environments
Modern application architectures increasingly rely on serverless computing and container orchestration platforms. AWS Secrets Manager integrates seamlessly with these environments, allowing dynamic retrieval of secrets during runtime.
In serverless environments, functions retrieve secrets at execution time, ensuring that no credentials are stored within the function code. This aligns with ephemeral computing principles where infrastructure is stateless and short-lived.
In containerized systems, secrets can be injected at runtime or retrieved dynamically through SDK integration. This ensures that containers remain lightweight and free of embedded credentials.
This integration supports scalable architectures where applications are constantly created, destroyed, and reconfigured without manual intervention.
Comparison with Alternative Secret Storage Approaches
While AWS Secrets Manager provides advanced capabilities, alternative approaches exist for managing sensitive data. Some systems use parameter-based configuration storage for less sensitive information, while others rely on external vault solutions or custom encryption implementations.
Parameter-based systems are often suitable for static configuration values that do not require frequent rotation. However, they lack advanced features such as automated rotation and lifecycle management.
Identity-based temporary credential systems can replace some use cases for secrets, particularly for service-to-service authentication. However, they are not suitable for storing static third-party API keys or database credentials.
AWS Secrets Manager fills this gap by providing a dedicated, fully managed system for sensitive data that requires rotation, encryption, and centralized governance.
Governance, Compliance, and Organizational Security Alignment
In regulated industries, secret management plays a critical role in compliance frameworks. AWS Secrets Manager supports audit logging, access tracking, and encryption standards that align with regulatory requirements.
Governance policies can be enforced through centralized identity and access management systems, ensuring consistent security enforcement across environments.
Audit logs provide detailed visibility into secret access patterns, which is essential for compliance reporting and security reviews. These logs help organizations demonstrate adherence to security standards and internal policies.
By centralizing secret management, organizations reduce fragmentation and ensure consistent enforcement of security controls across all applications and environments.
Operational Security Models in Large-Scale Cloud Environments
In large-scale cloud environments, operational security is not limited to protecting data at rest or in transit. It extends into how systems are designed, deployed, monitored, and maintained over time. AWS Secrets Manager plays a central role in operational security by ensuring that sensitive credentials are never statically embedded into infrastructure components and are instead dynamically retrieved under strict identity control.
Operational security models in distributed systems rely heavily on automation and policy enforcement. Human interaction with secrets is minimized, reducing the risk of accidental exposure. Instead of manually handling credentials during deployment or maintenance, systems are designed to automatically retrieve and inject secrets at runtime. This reduces operational overhead while improving security consistency.
A key aspect of operational security is environmental isolation. Development, staging, and production systems must remain fully separated, with distinct secrets for each environment. AWS Secrets Manager supports this by allowing environment-specific secret configurations, ensuring that a compromise in one environment does not affect others.
Monitoring and continuous validation are also essential components of operational security. Systems must constantly verify that secrets are being accessed only by authorized services. Any deviation from expected behavior is flagged for investigation, enabling rapid response to potential threats.
Secure Deployment Pipelines and Secret Injection Strategies
Modern software delivery pipelines are highly automated and involve multiple stages, including build, test, and deployment. Managing secrets within these pipelines is critical because exposure at any stage can compromise the entire system.
AWS Secrets Manager integrates into deployment workflows by enabling secure retrieval of secrets during pipeline execution. Instead of embedding credentials in configuration files or environment variables permanently, pipelines retrieve secrets dynamically when needed.
Secret injection strategies ensure that sensitive data is only available during runtime and not stored in build artifacts. For example, applications can retrieve database credentials during deployment initialization and discard them after establishing secure connections.
This approach prevents secrets from being exposed in logs, container images, or compiled binaries. It also ensures that credentials remain up to date without requiring manual updates to deployment configurations.
Pipeline security is further enhanced by using identity-based authentication, where deployment systems assume temporary roles that allow them to access only the required secrets for a specific stage.
Multi-Layer Defense Strategy for Secret Protection
A strong secret management architecture follows a multi-layer defense strategy. This approach ensures that even if one layer is compromised, additional layers continue to protect sensitive data.
The first layer is encryption at rest, which ensures that stored secrets are unreadable without proper decryption keys. The second layer is encryption in transit, which protects secrets during retrieval from interception.
The third layer is identity-based access control, which ensures that only authorized entities can request secrets. Even if an attacker gains access to the network, they cannot retrieve secrets without valid identity credentials.
The fourth layer is audit logging and monitoring, which provides visibility into all secret-related activities. This enables the detection of abnormal behavior patterns and supports forensic investigations.
The final layer is operational isolation, where secrets are segmented across environments, accounts, and applications. This reduces the blast radius of potential security incidents.
Scaling Secret Management in High-Traffic Distributed Systems
In high-scale distributed systems, secret retrieval requests can occur at extremely high frequency. Microservices architectures, serverless functions, and containerized workloads often require rapid and repeated access to credentials.
To handle this scale, AWS Secrets Manager is designed to support high-throughput API access combined with caching mechanisms that reduce redundant requests. Cached secrets are stored temporarily within application memory, allowing repeated use without additional API calls.
Scaling also involves regional distribution. Secrets are replicated across multiple availability zones, ensuring low-latency access for geographically distributed applications. This reduces latency and improves system responsiveness.
Load distribution strategies ensure that secret retrieval does not become a bottleneck in system performance. Applications are designed to minimize unnecessary secret requests by reusing cached credentials where appropriate.
As systems scale further, architectural patterns such as sidecar containers or centralized secret agents may be used to manage secret distribution efficiently across large clusters.
Disaster Recovery and Business Continuity for Secret Storage
Disaster recovery is a critical aspect of any secure system. In the context of secret management, loss of access to credentials can result in complete system failure. AWS Secrets Manager addresses this through replication, redundancy, and backup strategies.
Secrets are stored redundantly across multiple infrastructure zones, ensuring durability even in the event of hardware or regional failure. Cross-region replication allows secrets to be available in secondary locations, supporting failover scenarios.
In disaster recovery planning, secret synchronization is essential. Applications in backup regions must have access to the same set of credentials as primary systems. Replication ensures consistency across environments.
Business continuity planning also involves secure restoration procedures. If secrets are accidentally deleted or modified, versioning mechanisms allow recovery of previous states without disrupting system operations.
These mechanisms ensure that secret management does not become a single point of failure in critical infrastructure systems.
Advanced Access Patterns and Fine-Grained Authorization Models
In complex systems, access patterns for secrets are not always simple. Different services may require conditional access based on time, environment, or operational state. AWS Secrets Manager supports fine-grained authorization models that allow highly specific access control rules.
Access policies can define constraints such as which application can access a secret, under what conditions, and from which environment. This level of control ensures that secrets are only available when necessary.
Time-based access restrictions can also be implemented, limiting secret availability to specific operational windows. This reduces exposure risk during inactive periods.
Attribute-based access control further enhances flexibility by allowing decisions based on metadata such as environment tags, service roles, or deployment stages.
These advanced access patterns enable organizations to enforce highly customized security policies that align with internal governance requirements.
Secret Management in Microservices and Service Mesh Architectures
Microservices architectures introduce unique challenges for secret management because each service operates independently and may require its own set of credentials. AWS Secrets Manager integrates well with microservices by providing centralized access while maintaining service-level isolation.
Each microservice retrieves only the secrets it requires, ensuring strict separation of responsibilities. This prevents services from accessing unnecessary credentials and reduces potential attack surfaces.
Service mesh architectures further enhance security by managing communication between services at the infrastructure layer. Secret management systems integrate with these meshes to ensure secure service-to-service authentication.
In these environments, secrets are often used for mutual TLS authentication, API access, and service identification. Centralized management ensures consistency across all services while maintaining flexibility.
Observability, Metrics, and Security Telemetry Integration
Observability is essential for maintaining secure secret management systems. AWS Secrets Manager integrates with monitoring systems that track usage patterns, access frequency, and error rates.
Security telemetry provides insights into how secrets are being used across the system. This includes tracking which services access which secrets and how frequently they are retrieved.
Anomaly detection systems can identify unusual access patterns, such as unexpected spikes in secret retrieval or access from unauthorized regions. These signals help detect potential security incidents early.
Metrics also support operational optimization by identifying frequently accessed secrets that may benefit from caching or architectural restructuring.
This visibility ensures that secret management is not a blind component of the system but a fully observable and controllable part of the architecture.
Integration with Hybrid and Multi-Cloud Architectures
Many organizations operate in hybrid or multi-cloud environments where applications span across different cloud providers and on-premises infrastructure. AWS Secrets Manager supports integration patterns that allow secure access across these environments.
In hybrid architectures, secure communication channels are established between on-premises systems and cloud-based secret stores. Identity federation ensures that external systems can authenticate securely without storing long-term credentials.
In multi-cloud environments, secret replication strategies ensure consistency across platforms. Although each cloud provider may have its own secret management system, integration layers allow centralized governance.
These architectures require careful design to ensure that secrets remain consistent, secure, and accessible across all environments.
Performance Optimization Techniques for Secret Retrieval Systems
Performance optimization is critical in systems where secret retrieval occurs frequently. One of the most effective techniques is reducing API dependency through intelligent caching strategies.
Another optimization method involves batching secret retrieval requests where possible. Instead of requesting multiple secrets individually, systems can retrieve them in grouped operations.
Connection reuse and persistent sessions also improve performance by reducing overhead associated with repeated authentication.
Lazy loading strategies ensure that secrets are only retrieved when required, preventing unnecessary API calls during application startup.
These optimizations ensure that secret management does not negatively impact application performance, even at large scale.
Security Incident Response and Secret Revocation Strategies
In the event of a security incident, rapid response is essential. AWS Secrets Manager supports immediate secret rotation and revocation mechanisms that allow compromised credentials to be replaced quickly.
When a secret is suspected of being compromised, it can be rotated immediately, invalidating previous versions. Applications are automatically updated to use new credentials, minimizing downtime.
Revocation strategies ensure that access to compromised secrets is cut off instantly. Identity-based controls prevent unauthorized retrieval even if credentials are exposed externally.
Incident response workflows often include automated detection, alerting, rotation, and validation steps to ensure rapid containment of security threats.
These mechanisms ensure that secret compromise does not lead to long-term system exposure.
Conclusion
In modern cloud computing environments, secret management has evolved from a simple operational concern into a core pillar of enterprise security architecture. The increasing complexity of distributed systems, microservices, serverless applications, and multi-account infrastructures has made traditional approaches to handling sensitive data inadequate and risky. Hardcoded credentials, manual rotation processes, and fragmented storage methods no longer meet the demands of scalable, secure, and automated cloud-native systems. Instead, centralized secret management has become essential for maintaining both security and operational efficiency.
A well-designed secret management system fundamentally changes how applications interact with sensitive data. Rather than embedding credentials directly into code or configuration files, applications retrieve them dynamically at runtime through secure, authenticated requests. This shift significantly reduces the attack surface by ensuring that sensitive information is never permanently exposed in application artifacts. It also improves maintainability, as credentials can be updated, rotated, or revoked without requiring code changes or redeployments.
One of the most important outcomes of adopting a centralized secret management approach is the reduction of human error. In traditional environments, developers and operators often had to manually distribute credentials across systems, increasing the likelihood of misconfiguration or accidental exposure. Automated systems eliminate this dependency on manual handling by enforcing consistent security policies and lifecycle management practices. This automation ensures that secrets are always stored securely, accessed appropriately, and updated regularly without relying on manual intervention.
Another key benefit lies in the integration of identity-based access control. By linking secret retrieval to authenticated identities rather than static credentials, organizations can enforce fine-grained permissions across services and users. This ensures that each component of the system only has access to the minimum required secrets necessary for its operation. The principle of least privilege becomes enforceable at scale, reducing the risk of lateral movement in the event of a compromise. Temporary credentials and role-based access further enhance this model by limiting the duration and scope of access.
Encryption also plays a central role in securing sensitive data throughout its lifecycle. Secrets are encrypted at rest, in transit, and often during processing, ensuring multiple layers of protection. Even if storage systems or communication channels are compromised, encrypted data remains unreadable without proper authorization. The separation of encryption keys from stored secrets adds another layer of defense, ensuring that access to data alone is not sufficient to expose sensitive information.
Lifecycle management capabilities, such as automated rotation and version control, ensure that secrets remain up to date and secure over time. Regular rotation of credentials reduces the risk of long-term exposure, especially in environments where credentials may otherwise remain valid indefinitely. Versioning allows smooth transitions between old and new credentials, preventing service disruption during updates. Expiration policies ensure that unused or outdated secrets are removed from the system, reducing clutter and minimizing potential attack vectors.
Scalability is another critical aspect of modern secret management systems. In large distributed architectures, thousands of services may simultaneously request credentials. Efficient caching mechanisms, regional replication, and optimized retrieval processes ensure that secret access does not become a performance bottleneck. These systems are designed to handle high throughput while maintaining strict security controls, making them suitable for enterprise-scale deployments.
Observability and auditing further strengthen the security posture by providing complete visibility into secret usage. Every access request, modification, and rotation event is logged and can be analyzed for anomalies. This level of transparency enables organizations to detect suspicious behavior, investigate incidents, and maintain compliance with regulatory requirements. Security teams can monitor patterns of access and respond quickly to any deviations from expected behavior, ensuring continuous protection of sensitive data.
In addition to security and operational benefits, centralized secret management also supports architectural consistency. In hybrid and multi-cloud environments, where systems span multiple platforms and regions, maintaining consistent secret handling practices is essential. Centralized systems ensure that secrets are managed uniformly across all environments, reducing fragmentation and simplifying governance. This consistency is especially important in large organizations where multiple teams and services interact with shared resources.
Disaster recovery and resilience are also significantly improved through replication and redundancy mechanisms. Secrets stored in centralized systems are often replicated across multiple availability zones or regions, ensuring that they remain accessible even in the event of infrastructure failures. Versioning and backup capabilities allow systems to recover quickly from accidental deletions or misconfigurations, minimizing downtime and maintaining business continuity.
From a development perspective, integrating secret management into application workflows simplifies secure coding practices. Developers no longer need to manage sensitive data directly, allowing them to focus on core application logic. Secure APIs and SDKs handle secret retrieval seamlessly, ensuring that best practices are enforced automatically. This reduces the learning curve for security implementation while improving overall code quality.
Looking at the broader evolution of cloud security, secret management represents a shift toward zero-trust architectures where no component is inherently trusted. Every access request is verified, every identity is authenticated, and every interaction is logged. This model aligns with modern security principles that assume potential compromise and focus on minimizing impact through strict access controls and continuous verification.
As cloud systems continue to evolve, secret management will likely become even more intelligent and autonomous. Future systems may incorporate predictive security models that analyze usage patterns and detect anomalies before they escalate into incidents. Integration with artificial intelligence and behavioral analytics could further enhance the ability to identify risks and automate responses.
Ultimately, centralized secret management is not just a technical feature but a foundational security discipline. It ensures that sensitive data is protected across its entire lifecycle, from creation to deletion, while enabling scalable, efficient, and resilient cloud architectures. Organizations that adopt these practices are better positioned to secure their infrastructure, reduce operational complexity, and maintain compliance in increasingly complex digital environments.