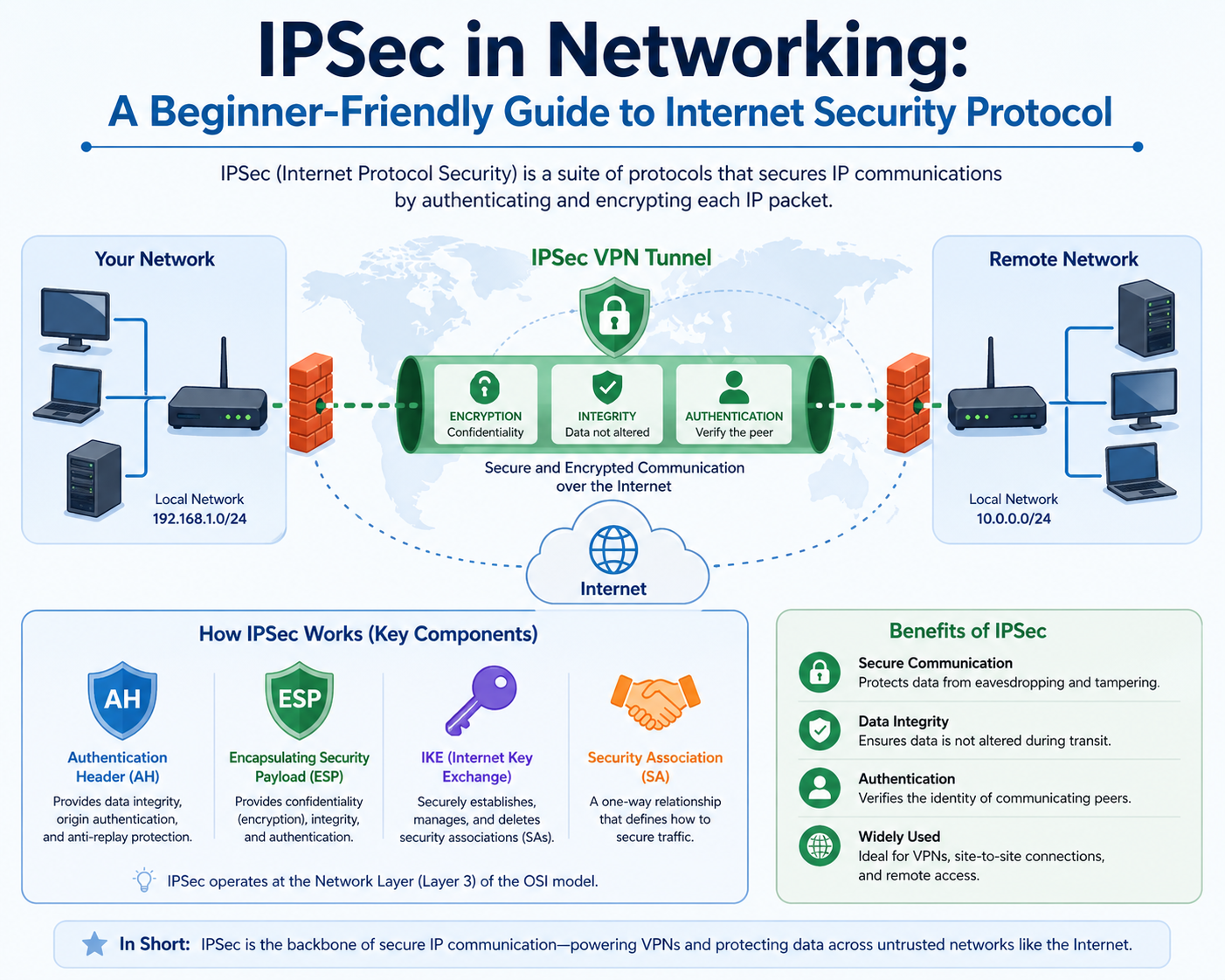
Internet Protocol Security, commonly referred to as IPsec, is a standardized framework designed to secure communications at the network layer. Unlike application-specific security mechanisms, IPsec does not depend on the type of application generating traffic. Instead, it operates directly on IP packets, which allows it to secure all types of network communication uniformly. This makes it particularly important in environments where diverse systems need to exchange sensitive information over untrusted infrastructure, such as the public internet.
IPsec is widely used in enterprise-grade network security architectures because it provides confidentiality, integrity, and authentication at the packet level. It is not limited to a single protocol but instead functions as a collection of coordinated protocols that work together to establish secure communication channels. These components ensure that data remains protected while in transit, even when passing through multiple intermediate networks.
One of the key strengths of IPsec is its transparency to applications. Since it operates below the transport layer, applications do not need to be modified or configured to support encryption. This allows organizations to implement secure communication without redesigning existing systems or software stacks.
Network Layer Positioning and Protocol Independence
IPsec operates at the network layer of the OSI model, which is responsible for routing packets between devices across different networks. This positioning gives IPsec a fundamental advantage in terms of scope and flexibility. Because it works at Layer 3, it can secure any IP-based communication regardless of the application or transport protocol involved.
This layer-based operation means that IPsec is independent of higher-level protocols such as HTTP, FTP, or SMTP. Whether data is being transmitted for web browsing, file transfer, or remote system administration, IPsec applies the same security rules consistently. This uniformity reduces complexity in security management and ensures that all IP traffic is treated equally from a protection standpoint.
Operating at the network layer also allows IPsec to integrate deeply into routing mechanisms. It modifies how packets are encapsulated and transmitted across networks, ensuring that security is maintained even as data traverses multiple routing devices and network segments.
Core Components That Form the IPsec Framework
IPsec is built from several interdependent components that collectively provide a complete security solution. These components include Authentication Header, Encapsulating Security Payload, Internet Key Exchange, and Security Associations. Each plays a specific role in ensuring secure communication.
Authentication Header is responsible for verifying that the data has not been altered during transmission and confirming the identity of the sender. It achieves this by generating cryptographic hashes that accompany each packet. When the packet reaches its destination, the receiving system recalculates the hash to verify integrity. If any modification is detected, the packet is discarded.
Encapsulating Security Payload is the most widely used component of IPsec because it provides both encryption and optional authentication. It ensures that the payload of the packet is encrypted, making it unreadable to unauthorized parties. At the same time, it can verify integrity and authenticity, making it a comprehensive security mechanism.
Internet Key Exchange is responsible for establishing secure communication parameters between two endpoints. It automates the process of negotiating encryption algorithms, authentication methods, and cryptographic keys. Without this mechanism, administrators would need to manually configure security settings, which would be inefficient and error-prone.
Security Associations define the specific parameters used to secure communication between two entities. Each association includes details such as encryption type, hashing algorithm, key lifetime, and authentication method. These associations ensure that both endpoints operate under the same security expectations.
Security Associations and Communication State Management
A Security Association represents a one-way logical connection between two endpoints that defines how traffic will be secured. Since it is unidirectional, separate associations are required for sending and receiving data. This structure allows fine-grained control over security policies in both directions of communication.
Each Security Association maintains state information that governs how packets are processed. This includes cryptographic keys, sequence numbers, and algorithm specifications. By maintaining this state, IPsec ensures consistency and prevents replay attacks, where an attacker attempts to resend previously captured packets.
Before any secure communication begins, both endpoints must agree on a Security Association. This negotiation process is handled through key exchange protocols that establish shared security parameters. Once agreed upon, the association governs all subsequent communication until it expires or is renegotiated.
Internet Key Exchange and Secure Session Establishment
Internet Key Exchange plays a central role in automating secure communication setup within IPsec. It eliminates the need for manual key distribution by dynamically negotiating cryptographic parameters between endpoints.
The negotiation process occurs in two stages. In the first stage, a secure channel is established between the two parties. This channel protects further negotiation messages from interception or modification. In the second stage, actual IPsec parameters such as encryption algorithms and session keys are agreed upon.
Modern implementations of this protocol prioritize efficiency and security improvements over earlier versions. It supports automatic key renewal, which ensures that long-lived connections remain secure by periodically refreshing encryption keys. This reduces the risk of key compromise over time and strengthens overall communication security.
Encapsulating Security Payload and Data Protection Mechanism
Encapsulating Security Payload is responsible for securing the actual content of IP packets. It encrypts the payload, ensuring that sensitive data cannot be read if intercepted during transmission. This encryption applies not only to user data but also to certain header components depending on configuration.
When ESP is applied, the original packet is encapsulated within a new structure. The payload is encrypted, and additional headers are added to ensure that the packet can still be routed through intermediate networks. This encapsulation process allows security to coexist with network functionality.
ESP also provides optional authentication, which ensures that the packet has not been modified in transit. This dual capability of encryption and integrity verification makes it one of the most important components in modern secure network communication systems.
Authentication Header and Data Integrity Verification
Authentication Header focuses exclusively on verifying the integrity and authenticity of packets. It does not encrypt data but instead ensures that packets remain unaltered during transmission. This is achieved through cryptographic hashing mechanisms that generate unique signatures for each packet.
When a packet is received, the destination system recalculates the hash and compares it with the original value. If any discrepancy is found, the packet is considered compromised and is discarded. This mechanism protects against tampering, spoofing, and replay attacks.
Although AH provides strong integrity protection, it is less commonly used in modern deployments because it does not offer confidentiality. In most environments, Encapsulating Security Payload is preferred due to its ability to encrypt data as well as verify integrity.
Transport Mode and Tunnel Mode Operation Structures
IPsec can function in two operational modes, each designed for specific communication scenarios. Transport mode is used for end-to-end communication between individual hosts. In this mode, only the payload of the packet is encrypted, while the original IP header remains intact. This allows efficient communication with minimal overhead.
Tunnel mode, on the other hand, encapsulates the entire original IP packet within a new packet structure. Both the payload and original header are protected, making this mode ideal for secure communication between networks. It is commonly used in virtual private network deployments where entire networks need to communicate securely over public infrastructure.
Tunnel mode ensures that internal network structures remain hidden from external observers. It also allows organizations to connect remote offices securely, enabling seamless communication across geographically distributed environments.
Packet Encapsulation and Routing Considerations
The encapsulation process in IPsec modifies standard IP packet structures to incorporate security features. Depending on the mode used, additional headers and trailers are added to support encryption, authentication, and routing requirements.
Since encryption alters packet size, it can impact maximum transmission unit values and introduce fragmentation challenges. Network systems must account for these changes to ensure that packets are transmitted efficiently without loss or degradation.
Despite these modifications, IPsec is designed to maintain compatibility with existing network infrastructure. Routers and intermediate devices can still forward packets based on outer IP headers, while internal data remains protected from inspection.
Encryption Behavior and Immediate Data Protection Model
One of the defining characteristics of IPsec is its immediate encryption behavior. Once a secure association is established, data is encrypted before transmission begins. This differs from application-layer security models, where encryption is applied after session establishment.
Because encryption occurs at the network layer, even packet headers can be partially protected depending on the configuration. This provides a deeper level of security compared to higher-layer protocols, which often leave routing information exposed.
However, certain routing information must remain visible to ensure proper packet delivery. IPsec balances this requirement by adding new outer headers while encrypting sensitive internal data structures.
Enterprise Deployment of IPsec in Modern Network Infrastructures
In practical network environments, IPsec is most commonly deployed as a foundational security technology for protecting data in transit across untrusted networks. Enterprises rely on it to secure communication between remote users, branch offices, data centers, and cloud environments. Unlike application-level encryption methods that protect only specific services, IPsec provides a system-wide security layer that operates transparently beneath applications and services.
In corporate architectures, IPsec is often embedded into routers, firewalls, and dedicated VPN gateways. These devices handle encryption and decryption of traffic without requiring end-user intervention. This centralized approach simplifies management and ensures consistent enforcement of security policies across the entire organization. As a result, IPsec becomes an invisible but critical part of network communication, protecting sensitive information such as financial data, internal communications, and authentication credentials.
The scalability of IPsec is one of its most important advantages in enterprise environments. Whether securing communication for a small office or a multinational organization with thousands of endpoints, IPsec can be adapted to different network topologies without requiring changes to application design or user behavior.
Virtual Private Network Architecture and IPsec Integration
One of the most widely used applications of IPsec is in virtual private network systems. A VPN built on IPsec allows secure communication over public networks by creating encrypted tunnels between endpoints. These tunnels simulate private network connectivity even though the underlying transport infrastructure is shared and untrusted.
In remote access VPN scenarios, individual devices such as laptops or mobile systems connect securely to a central corporate network. Once the IPsec tunnel is established, the remote device behaves as if it is physically connected to the internal network. This allows access to internal applications, file systems, and services without exposing them directly to the internet.
In site-to-site VPN configurations, entire networks are connected using IPsec tunnels. This is commonly used to link branch offices with headquarters or connect multiple data centers. Unlike remote access VPNs, site-to-site connections are typically persistent and operate continuously in the background, ensuring uninterrupted communication between locations.
The strength of IPsec-based VPNs lies in their ability to secure all network traffic between endpoints. This includes not only application data but also system-level communication, making it a comprehensive security solution for distributed environments.
Tunnel Mode Operation in Secure Network Bridging
Tunnel mode is the primary operational mode used in VPN architectures. In this mode, the entire original IP packet is encapsulated within a new IP packet before being transmitted across the network. This ensures that both the payload and original routing information are protected from external observation.
When a packet enters a tunnel, it is encrypted and wrapped with a new IP header. This outer header is used for routing the packet across intermediate networks, while the inner packet remains fully protected. At the destination, the outer layer is removed, and the original packet is decrypted and processed.
This mechanism allows secure communication between networks that may have no direct physical connection. It effectively creates a virtual private link over public infrastructure, ensuring that sensitive data cannot be intercepted or modified during transit.
Tunnel mode is especially important in multi-site enterprise environments where centralized resources must be accessed securely from multiple locations. It also plays a key role in cloud networking, where hybrid infrastructure models require secure communication between on-premises systems and cloud-based services.
Remote Access IPsec VPN Design and Authentication Flow
Remote access VPNs using IPsec follow a structured authentication and negotiation process before establishing secure communication. When a user initiates a connection, the client first communicates with a VPN gateway to begin the key exchange process.
The gateway authenticates the user using credentials, certificates, or multi-factor authentication mechanisms. Once authentication is successful, a secure tunnel is established using negotiated encryption parameters. This tunnel protects all subsequent traffic between the client and the corporate network.
After the tunnel is active, the client receives virtual network configuration parameters such as IP address assignment and routing information. This allows the device to integrate seamlessly into the internal network environment while maintaining secure communication over the public internet.
Remote access IPsec VPNs are widely used in modern hybrid work environments where employees require secure access to corporate systems from various locations. The ability to enforce consistent security policies across remote endpoints makes IPsec an essential technology for distributed workforces.
Site-to-Site IPsec VPN and Network Interconnection Strategy
Site-to-site VPNs extend secure communication between entire networks rather than individual devices. These connections are typically established between routers or dedicated security appliances at each location.
Once configured, the IPsec tunnel remains active continuously, allowing seamless communication between branch offices, data centers, or partner organizations. Traffic between these networks is automatically encrypted and decrypted by the gateway devices, ensuring that internal systems communicate securely without requiring endpoint configuration.
This model eliminates the need for expensive dedicated leased lines, replacing them with secure tunnels over existing internet infrastructure. Despite using public networks, site-to-site IPsec VPNs maintain high levels of confidentiality and integrity through strong encryption and authentication mechanisms.
In large-scale enterprise environments, multiple site-to-site tunnels may be interconnected to create complex network topologies. Routing protocols can be integrated with IPsec tunnels to dynamically manage traffic flow across distributed systems.
Internet Key Exchange Phase One and Secure Channel Establishment
Internet Key Exchange plays a critical role in setting up IPsec connections. The first phase of this process focuses on establishing a secure communication channel between endpoints before any sensitive information is exchanged.
During this phase, both parties negotiate authentication methods and agree on a shared secret. This initial exchange is protected using cryptographic techniques that prevent interception or modification by external attackers.
Once the secure channel is established, it is used to protect further negotiation messages. This ensures that all subsequent configuration data, including encryption algorithms and session parameters, is transmitted securely.
Phase one of key exchange is essential because it forms the foundation of trust between communicating systems. Without this secure channel, IPsec would be vulnerable to interception during setup, undermining the entire security model.
Internet Key Exchange Phase Two and Security Parameter Negotiation
The second phase of Internet Key Exchange focuses on establishing the actual IPsec Security Associations that will govern data transmission. During this phase, encryption algorithms, authentication methods, and key lifetimes are negotiated.
This phase is responsible for defining how data will be protected once communication begins. It ensures that both endpoints use compatible security settings, preventing mismatches that could disrupt communication.
Once the negotiation is complete, the resulting Security Associations are installed on both endpoints. These associations remain active for the duration of the session or until they are refreshed through rekeying mechanisms.
Phase two is typically more lightweight than phase one because it operates within the already secure channel established earlier. However, it is equally important because it determines the actual encryption and authentication parameters used in data transmission.
Encryption Algorithms and Cryptographic Strength in IPsec Systems
IPsec supports a variety of encryption algorithms, allowing organizations to choose security levels based on performance and protection requirements. Common encryption methods include symmetric algorithms that provide fast and efficient data protection.
The choice of encryption algorithm directly impacts both security strength and system performance. Stronger encryption provides better protection but may require more processing power, especially in high-traffic environments.
In addition to encryption, IPsec uses hashing algorithms to ensure data integrity. These cryptographic functions generate unique identifiers for each packet, allowing detection of any unauthorized modification during transit.
Modern implementations prioritize algorithm agility, allowing systems to adapt to evolving cryptographic standards without requiring complete redesigns of existing infrastructure.
Performance Considerations and Network Overhead Challenges
While IPsec provides strong security, it introduces additional processing overhead due to encryption, encapsulation, and key management operations. This can impact network performance, especially in high-throughput environments.
Encapsulation increases packet size, which can affect transmission efficiency and lead to fragmentation if not properly managed. Network administrators must account for these changes when designing infrastructure to avoid performance degradation.
Hardware acceleration is often used to mitigate performance impacts. Many modern network devices include dedicated cryptographic processors that handle encryption and decryption tasks more efficiently than general-purpose CPUs.
Proper configuration and optimization are essential to ensure that IPsec deployments maintain both security and performance at scale.
Routing Behavior and Packet Flow in IPsec Networks
IPsec modifies traditional packet flow by introducing encapsulation and encryption at the network layer. Despite these changes, routing infrastructure continues to operate using standard IP routing mechanisms.
Outer IP headers are used for routing packets across intermediate networks, while inner packets remain encrypted. This allows IPsec traffic to traverse complex network topologies without requiring changes to routing protocols.
At the destination, packets are decrypted and restored to their original form before being passed to higher-layer protocols. This process is transparent to applications, which continue to operate without awareness of underlying security mechanisms.
This design ensures compatibility with existing network infrastructure while providing strong security guarantees at the packet level.
Scalability and Operational Management in Large Networks
Managing IPsec in large-scale environments requires careful planning of key distribution, policy management, and tunnel configuration. As the number of endpoints increases, maintaining consistent security policies becomes more complex.
Automated key management and centralized configuration systems are often used to simplify administration. These tools help ensure that security parameters remain consistent across all devices and reduce the risk of misconfiguration.
Monitoring and logging are also critical in large deployments. Network administrators must track tunnel status, authentication events, and encryption performance to maintain visibility into secure communication channels.
Proper scalability planning ensures that IPsec can support growing network demands without compromising security or performance.
Advanced Behavior of IPsec in Complex Network Environments
In mature network infrastructures, IPsec operates far beyond basic point-to-point encryption. It becomes part of a broader security architecture that integrates routing, firewall policies, identity management, and threat mitigation systems. At this level, IPsec is not simply a tunnel mechanism but a dynamic security enforcement layer that adapts to changing network conditions and organizational requirements.
In large-scale deployments, IPsec must handle multiple concurrent tunnels, each with distinct security policies, cryptographic parameters, and routing rules. These environments often include hybrid infrastructures where on-premises systems interact with cloud services, remote users, and third-party networks. IPsec must therefore maintain consistent encryption standards while supporting diverse connectivity models.
One of the key operational challenges in such environments is maintaining synchronization between Security Associations and routing tables. As tunnels scale, ensuring correct packet forwarding without conflict becomes increasingly complex. Misalignment between encryption policies and routing behavior can lead to packet loss, latency, or security gaps.
Deep Dive into IPsec Security Architecture and Trust Boundaries
IPsec establishes a trust boundary at the network layer, where all traffic entering or leaving a protected domain is subject to encryption and authentication rules. This boundary is critical because it defines where trust begins and ends in a communication path.
Inside the trust boundary, data is considered secure and can move freely between internal systems. Outside the boundary, all communication is treated as untrusted and must be validated through IPsec mechanisms. This separation is fundamental to zero-trust network design principles, where no traffic is inherently trusted based on location alone.
The strength of this model lies in its ability to enforce security consistently regardless of application behavior. Even if an application is vulnerable or misconfigured, IPsec ensures that data is still protected at the packet level before leaving the host or network.
However, defining trust boundaries incorrectly can introduce security risks. If certain traffic bypasses IPsec enforcement due to misconfiguration, it may expose sensitive data to interception or manipulation. Therefore, strict policy enforcement and continuous validation are essential.
Cryptographic Lifecycle Management in IPsec Systems
One of the most critical aspects of IPsec operation is the lifecycle of cryptographic keys and Security Associations. These elements are not static; they must be continuously managed to maintain security integrity over time.
Each Security Association has a defined lifetime, after which it must be renegotiated or replaced. This process, known as rekeying, ensures that even if a key is compromised, its usefulness is limited by time. Shorter lifetimes improve security but increase computational overhead due to more frequent renegotiations.
Key lifecycle management also includes generation, distribution, rotation, and destruction of cryptographic material. Proper handling of these stages is essential to prevent unauthorized access. Weak key management practices can undermine even the strongest encryption algorithms.
Modern implementations automate much of this lifecycle using secure key exchange protocols. This reduces human error and ensures consistent application of cryptographic policies across distributed systems.
Threat Models and Attack Surfaces in IPsec Deployments
Although IPsec is designed to provide strong security, it is not immune to threats. Understanding its attack surface is essential for designing resilient systems.
One potential attack vector involves misconfiguration of Security Associations. If encryption parameters are weak or improperly aligned between endpoints, attackers may exploit inconsistencies to disrupt communication or intercept traffic.
Another concern is key compromise. If an attacker gains access to cryptographic keys, they may be able to decrypt traffic or impersonate legitimate endpoints. This highlights the importance of secure key storage and strict access controls.
Replay attacks are another threat, where previously captured packets are retransmitted to disrupt communication or gain unauthorized access. IPsec counters this through sequence numbers and anti-replay mechanisms, but improper configuration can weaken these protections.
Denial-of-service attacks can also target IPsec systems by overwhelming encryption processing capabilities or exhausting key negotiation resources. This can lead to degraded performance or tunnel failure.
Encapsulation Overhead and Its Impact on Network Efficiency
IPsec introduces additional data overhead due to encapsulation, encryption, and authentication processes. This overhead affects packet size and can influence overall network performance.
When packets are encapsulated, additional headers are added to support routing and security functions. This increases the total size of each packet, which can lead to fragmentation if it exceeds the maximum transmission unit supported by intermediate networks.
Fragmentation can degrade performance by increasing processing requirements and reducing throughput efficiency. In high-performance environments, this must be carefully managed through proper MTU configuration and path optimization.
Despite these challenges, the trade-off between security and performance is generally considered acceptable in enterprise environments where data protection is a priority.
Optimization Strategies for High-Performance IPsec Networks
To maintain performance while using IPsec, several optimization strategies are commonly implemented. One of the most important is hardware acceleration, where dedicated cryptographic processors handle encryption and decryption tasks.
This offloads computational burden from general-purpose CPUs, allowing systems to maintain high throughput even under heavy traffic loads. Hardware acceleration is particularly important in large-scale VPN gateways and data center environments.
Another optimization technique involves efficient key management. Reducing unnecessary rekeying operations can help minimize overhead while maintaining acceptable security levels. This requires careful balancing of key lifetimes and security requirements.
Traffic engineering is also used to optimize IPsec performance. By controlling routing paths and distributing load across multiple tunnels, network administrators can prevent congestion and improve reliability.
IPsec in Cloud and Hybrid Infrastructure Models
Modern IT environments increasingly rely on hybrid and cloud-based architectures. In these scenarios, IPsec plays a critical role in securing communication between on-premises systems and cloud services.
Cloud providers often integrate IPsec into their virtual networking infrastructure, allowing secure tunnels to be established between enterprise networks and cloud environments. This enables seamless data exchange while maintaining strong security controls.
In hybrid models, IPsec ensures consistent protection across both physical and virtual environments. It allows organizations to extend their internal security policies into cloud platforms without modifying application behavior.
However, cloud-based deployments introduce additional complexity due to dynamic scaling, distributed architecture, and multi-tenant environments. IPsec must be carefully configured to ensure isolation between different network segments.
Routing Protocol Interaction and Dynamic Network Adaptation
IPsec does not operate in isolation; it often interacts with routing protocols such as OSPF, BGP, and static routing configurations. These interactions determine how traffic flows through secure tunnels.
In dynamic environments, routing changes must be reflected in IPsec policies to ensure continuity of secure communication. If routing updates are not properly synchronized with security policies, traffic may be dropped or incorrectly routed outside secure tunnels.
Advanced deployments use policy-based routing to direct specific traffic through IPsec tunnels based on predefined rules. This allows fine-grained control over which data is encrypted and which paths it follows.
Maintaining consistency between routing and security layers is essential for preventing traffic leaks and ensuring predictable network behavior.
Latency, Throughput, and Real-Time Communication Constraints
IPsec introduces additional processing steps that can affect latency and throughput. Encryption and decryption require computational resources, which can introduce delays in packet processing.
In real-time communication systems, such as voice or video applications, even small increases in latency can impact quality. Therefore, IPsec configurations must be optimized to minimize delay while maintaining security.
Techniques such as traffic prioritization and Quality of Service policies are often used to ensure that critical traffic is processed efficiently. By prioritizing latency-sensitive data, networks can maintain acceptable performance levels even under encryption overhead.
Despite these challenges, modern hardware and optimized implementations have significantly reduced the performance impact of IPsec in most environments.
Scalability Challenges in Large Distributed Networks
As networks grow in size and complexity, managing IPsec configurations becomes increasingly difficult. Each additional tunnel introduces new security associations, routing dependencies, and key management requirements.
Without centralized management, this complexity can lead to configuration drift, where different parts of the network operate under inconsistent security policies. This can create vulnerabilities and operational inefficiencies.
Scalability solutions often involve automation tools that manage IPsec configurations across multiple devices. These systems ensure consistency and reduce the administrative burden associated with large-scale deployments.
Proper scalability planning is essential for maintaining both security and operational stability in enterprise environments.
Future Evolution of IPsec in Modern Networking Ecosystems
As network architectures continue to evolve, IPsec remains a foundational security technology. However, its role is expanding to integrate with emerging technologies such as software-defined networking and zero-trust architectures.
In these environments, IPsec is no longer just a tunneling mechanism but part of a broader policy-driven security framework. It works alongside identity-based access controls and micro-segmentation strategies to enforce granular security policies.
Future developments are likely to focus on greater automation, improved performance efficiency, and tighter integration with cloud-native networking systems. Despite the emergence of alternative encryption models, IPsec continues to remain relevant due to its maturity, reliability, and deep integration into existing network infrastructure.
Conclusion
IPsec remains one of the most foundational technologies in modern network security because it addresses a problem that exists at the very core of digital communication: how to safely transmit data across networks that cannot be trusted. While higher-layer security mechanisms such as TLS protect individual applications, IPsec secures communication at the network layer itself, which gives it a broader and more structural role in enterprise security architecture.
The primary strength of IPsec lies in its ability to operate independently of applications and user behavior. Because it functions at the IP layer, it secures all traffic passing through a network interface without requiring modifications to software or protocols running above it. This design makes it highly scalable and suitable for environments where multiple services, systems, and platforms must communicate securely in a unified manner. Whether the traffic involves databases, file systems, remote access sessions, or cloud-based services, IPsec applies consistent encryption and authentication policies across all packets.
Another key advantage of IPsec is its versatility in deployment models. It supports both remote access and site-to-site connectivity, enabling organizations to secure communication between individual users and centralized networks as well as between entire network infrastructures. This flexibility is especially important in modern enterprise environments where hybrid workforces and distributed systems are standard. Remote employees can securely access internal resources, while branch offices and data centers can exchange information as if they were part of a single unified network.
The operational design of IPsec also reflects a strong emphasis on layered security principles. Through components such as Encapsulating Security Payload and Authentication Header, IPsec ensures that data confidentiality, integrity, and authenticity are all maintained during transmission. Encryption prevents unauthorized access to sensitive information, integrity checks ensure that data is not altered in transit, and authentication mechanisms verify the identity of communicating parties. Together, these protections create a robust defense against interception, tampering, and impersonation.
The role of Internet Key Exchange is particularly important in maintaining secure operations. Automating the negotiation of cryptographic parameters, it eliminates the need for manual key management and reduces the risk of configuration errors. It also supports dynamic key rotation, which ensures that encryption remains strong over time even in long-lived connections. This automated lifecycle management is essential in large-scale environments where manual administration would be impractical.
Despite its strengths, IPsec introduces certain operational challenges that must be carefully managed. One of the most significant is performance overhead. Because IPsec encrypts and encapsulates data at the network layer, it adds additional processing requirements and increases packet size. This can affect throughput and latency, especially in high-traffic networks. However, modern hardware acceleration techniques and optimized configurations have significantly reduced these performance impacts, making IPsec viable even in demanding enterprise environments.
Another important consideration is complexity. IPsec deployments require careful planning of Security Associations, routing policies, encryption algorithms, and tunnel configurations. Misconfigurations can lead to connectivity issues or security vulnerabilities. As networks scale, managing these configurations becomes increasingly challenging, particularly in environments with multiple tunnels and dynamic routing changes. For this reason, centralized management and automation have become essential components of modern IPsec implementations.
From a security perspective, IPsec provides strong protection but is not immune to risks. The effectiveness of its security model depends heavily on proper configuration, secure key management, and adherence to cryptographic best practices. Weak encryption algorithms, poor key storage practices, or incorrect tunnel configurations can reduce its effectiveness. Additionally, like all network security systems, IPsec must defend against denial-of-service attacks and potential attempts to exploit misconfigured endpoints.
In cloud and hybrid infrastructures, IPsec plays a critical enabling role. It allows organizations to extend secure communication channels across physical and virtual environments without redesigning application logic. This capability is essential for integrating on-premises systems with cloud platforms, supporting scalable architectures while maintaining consistent security standards. As organizations continue migrating workloads to distributed environments, IPsec remains a key enabler of secure connectivity.
Another important aspect of IPsec is its alignment with modern security principles such as zero trust. By enforcing encryption and authentication at the network layer, IPsec supports the idea that no traffic should be inherently trusted, regardless of its origin. Every packet must be verified and secured before being transmitted or accepted. This approach strengthens overall security posture and reduces reliance on perimeter-based defense models.
Looking at its broader role in networking, IPsec serves as both a foundational technology and a long-term security standard. It has been widely adopted across industries due to its protocol independence, strong cryptographic design, and ability to integrate with existing infrastructure. While newer security models and transport encryption technologies continue to evolve, IPsec remains deeply embedded in enterprise networking due to its reliability and flexibility.
Ultimately, IPsec represents a critical layer of defense in modern digital communication. It ensures that data moving across untrusted networks remains protected from interception and manipulation, regardless of the underlying infrastructure. Its ability to secure entire network flows, rather than individual applications, makes it uniquely valuable in large-scale and complex environments. As networks continue to expand and evolve, IPsec will remain a central component in maintaining secure, resilient, and trustworthy communication systems across global digital ecosystems.