Modern digital infrastructure depends heavily on the ability of routers to communicate and exchange information about reachable destinations. Without routing protocols, every route between devices would need to be manually configured, which would be impossible to manage at scale. Dynamic routing protocols solve this problem by allowing routers to automatically learn, update, and maintain path information. This automation ensures that networks remain functional even when links fail, new devices are added, or traffic patterns change.
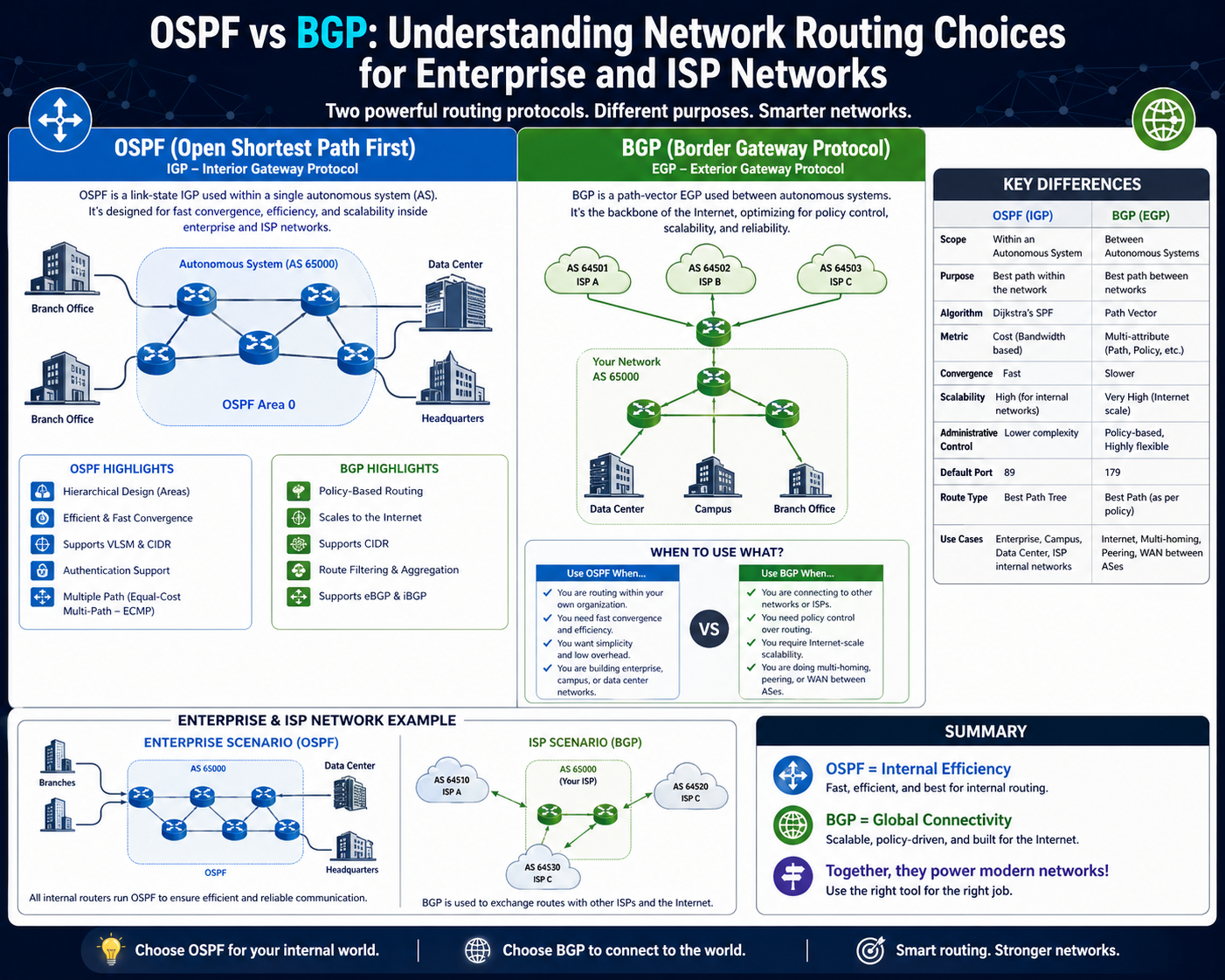
Within this ecosystem, routing protocols are generally divided into two major categories: interior routing protocols and exterior routing protocols. Interior protocols operate within a single organization or administrative boundary, while exterior protocols operate between different organizations or autonomous systems. OSPF belongs to the first category, whereas BGP belongs to the second. Although they are often compared, they are not direct competitors. Instead, they solve different problems in different layers of network design.
Understanding when and why each protocol is used requires a clear view of how routing decisions are made, how topology information is shared, and how scalability is achieved in complex environments.
Interior Gateway Protocols and the Position of OSPF
OSPF, which stands for Open Shortest Path First, is a widely deployed Interior Gateway Protocol designed for internal routing within an autonomous system. An autonomous system refers to a network or collection of networks under a single administrative control. This could be an enterprise organization, a university network, or a large data center infrastructure.
The primary objective of OSPF is to ensure that all routers within the same domain have a synchronized view of the network topology. This shared understanding allows consistent and efficient routing decisions. Unlike simpler routing methods, OSPF does not rely on exchanging full routing tables. Instead, it distributes information about network links, enabling each router to construct a complete map of the network.
This design makes OSPF highly suitable for environments where reliability and fast adaptation to changes are important. Internal networks often experience frequent topology adjustments due to hardware upgrades, link failures, or configuration changes, and OSPF is designed to respond quickly to such events.
Link-State Routing Fundamentals in OSPF
The foundation of OSPF lies in its link-state routing mechanism. Each router participating in OSPF collects information about its directly connected interfaces, including link status, cost, and neighbor relationships. This information is packaged into link-state advertisements and shared with all other routers in the same OSPF domain.
Once this information is distributed, every router builds a complete link-state database that represents the entire network topology. This database is identical across all routers in the same area, ensuring consistency in routing decisions.
After building the topology database, each router independently runs a shortest path computation using a graph-based algorithm. The algorithm evaluates all possible paths to a destination and selects the one with the lowest cumulative cost. Cost is typically based on link bandwidth, with higher bandwidth links assigned lower cost values.
This approach ensures that routing decisions are optimal based on the current network state. However, it also means that any change in the network triggers recalculations of routing paths, which can temporarily increase processing load.
OSPF Area Structure and Hierarchical Design
To manage scalability, OSPF introduces the concept of areas. Instead of treating the entire network as a single large topology, OSPF divides it into smaller logical segments. Each area maintains its own link-state database, reducing the amount of routing information that needs to be processed.
The backbone area serves as the central point of connection between all other areas. Routers that connect different areas are responsible for summarizing and distributing routing information between them. This hierarchical design significantly reduces overhead in large networks.
By limiting the scope of link-state updates, OSPF reduces CPU usage and improves efficiency. Without areas, every router would need to process every topology change in the entire network, which would not scale effectively.
In smaller networks, a single-area design is often sufficient. However, in large enterprise environments, multi-area OSPF is essential for maintaining performance and stability.
Shortest Path First Calculation and Routing Decisions
The shortest path first algorithm is the core computation engine of OSPF. It takes the link-state database as input and constructs a shortest path tree rooted at the local router. This tree represents the most efficient routes to all known destinations.
Each router independently performs this calculation, but because all routers share the same topology database, they arrive at consistent results. This eliminates routing conflicts and ensures predictable packet forwarding behavior.
The algorithm assigns cumulative cost values to each path and selects the route with the lowest total cost. If multiple paths have equal cost, OSPF supports load balancing across those paths. This capability improves bandwidth utilization and provides redundancy.
Although efficient, SPF recalculations can become resource-intensive in large networks, especially when frequent topology changes occur. Modern hardware mitigates this issue, but it remains an important design consideration.
Convergence Behavior and Network Stability
Convergence refers to the time it takes for all routers in a network to reach a consistent routing state after a change occurs. OSPF is known for relatively fast convergence compared to older distance-vector protocols.
When a link fails, the affected router immediately generates an updated link-state advertisement. This update is quickly propagated throughout the network, allowing all routers to adjust their topology databases. Each router then recalculates its shortest path tree to reflect the new state.
This rapid reaction ensures that traffic is quickly rerouted around failures, minimizing downtime. However, convergence speed depends on network size, design complexity, and timer configurations.
In well-designed OSPF networks, convergence is typically fast enough to support enterprise-grade applications that require high availability.
Resource Consumption and Scalability Considerations
Although OSPF is efficient in many respects, it does require significant processing and memory resources compared to simpler routing protocols. Each router must maintain a full or partial copy of the network topology, depending on its role within the OSPF hierarchy.
As the network grows, the size of the link-state database increases, which in turn increases memory usage. Additionally, frequent topology changes can trigger repeated SPF recalculations, increasing CPU load.
To address these challenges, network engineers rely on careful design principles such as area segmentation, route summarization, and controlled adjacency formation. These techniques help limit the scope of routing updates and improve scalability.
Despite these requirements, OSPF remains widely used due to its balance of efficiency, reliability, and vendor interoperability.
OSPF in Internal Network Environments
OSPF is primarily deployed in internal environments where full control over network infrastructure exists. These include enterprise campuses, data centers, and private organizational networks.
In such environments, administrators benefit from OSPF’s predictable behavior and ability to quickly adapt to changes. Because all routers belong to the same administrative domain, trust relationships are simplified, and routing policies are easier to manage.
OSPF also supports hierarchical design, allowing complex networks to be broken into manageable segments. This makes it suitable for both small and large-scale internal deployments.
However, OSPF is not intended for use between independent organizations or across the internet. Its design assumptions do not align with the requirements of global-scale routing.
Limitations of OSPF in External Routing Scenarios
While OSPF performs well internally, it has clear limitations when applied to external routing. One of the primary constraints is its requirement for full topology visibility. In a global environment such as the internet, maintaining complete knowledge of all network paths would be impractical.
Additionally, OSPF focuses on shortest-path optimization rather than policy-based routing decisions. External routing often requires complex policies related to traffic engineering, business agreements, and administrative control, which OSPF is not designed to handle.
Another limitation is scalability. The number of routers and links on the internet is far too large for OSPF’s link-state database model to manage efficiently. Frequent changes at this scale would result in excessive recalculation overhead and instability.
Because of these limitations, a different routing approach is required for inter-domain communication, which leads to the use of BGP.
Transition Toward External Gateway Routing Concepts
As networks grow beyond a single organization, the need arises to connect independent systems together. These systems are known as autonomous systems, each operating under its own routing policies and administrative control.
Communication between these systems requires a routing protocol that does not depend on full topology visibility. Instead, it must rely on path information and policy-based decisions. This requirement led to the development of BGP, which operates fundamentally differently from OSPF.
The Role of Exterior Gateway Protocols in Global Connectivity
As networks expand beyond a single organization, internal routing protocols are no longer sufficient to handle communication between independent administrative domains. These domains, known as autonomous systems, operate with their own routing policies, infrastructure designs, and operational objectives. The internet itself is a collection of thousands of these autonomous systems interconnected through agreed routing relationships.
Exterior gateway protocols exist specifically to manage routing between these separate systems. Unlike interior protocols that focus on optimal internal path selection, exterior protocols focus on scalability, policy enforcement, and stability across administrative boundaries. BGP is the dominant protocol in this category and serves as the foundation for global internet routing.
The key challenge in inter-domain routing is not simply finding the shortest path, but ensuring that routing decisions respect organizational policies, commercial agreements, and traffic engineering constraints. This makes BGP fundamentally different in design philosophy compared to OSPF.
BGP as a Path Vector Routing Protocol
BGP, or Border Gateway Protocol, operates as a path vector routing protocol. This means that instead of calculating the shortest path based on internal topology knowledge, it relies on a recorded sequence of autonomous systems that a route has traversed.
Each route advertisement in BGP carries a list of autonomous system identifiers. These identifiers represent the sequence of networks that the route has passed through from its origin to the current point. This sequence is known as the AS path. Routers use this information to make routing decisions by evaluating path attributes rather than complete network topology.
This approach allows BGP to scale across the entire internet without requiring every router to maintain a full map of global connectivity. Instead, routers only store information about reachable prefixes and the paths used to reach them.
Because of this design, BGP does not attempt to compute the shortest physical or logical path. Instead, it focuses on selecting the most appropriate path based on policy, path length, and other attributes.
Autonomous Systems and Their Role in BGP
An autonomous system represents a collection of IP networks and routers under a single administrative control that presents a unified routing policy to external networks. Each autonomous system is assigned a unique identifier used in BGP operations.
These systems exchange routing information with other autonomous systems using BGP sessions. When a route is advertised from one system to another, the originating system’s identifier is appended to the AS path. As the route propagates through multiple systems, the AS path grows, creating a traceable record of the route’s journey.
This mechanism allows BGP to prevent routing loops at a global scale. If a router detects its own autonomous system identifier in the AS path, it will reject the route to avoid circular routing.
Autonomous systems form the structural backbone of internet routing, and BGP is the protocol that binds them together into a coherent global routing system.
Internal BGP and External BGP Relationships
BGP operates in two primary modes: internal and external. External BGP is used when routers in different autonomous systems exchange routing information. Internal BGP is used within a single autonomous system to ensure consistent routing information across multiple border routers.
External BGP sessions typically form between routers belonging to different organizations or service providers. These sessions are responsible for exchanging routes between independent networks. Internal BGP sessions, on the other hand, are used to distribute externally learned routes within the same autonomous system.
One important distinction is that internal BGP does not modify the AS path in the same way external sessions do. This ensures that internal routing remains consistent while preserving external path information for decision-making at the network edge.
Both forms of BGP are essential for maintaining routing consistency across large and complex network environments.
BGP Decision Process and Route Selection Logic
Unlike OSPF, which uses a single metric based on link cost, BGP uses a multi-attribute decision process to select the best route. This decision process evaluates multiple factors in a hierarchical order.
The most important attribute is typically the AS path length. Routes that traverse fewer autonomous systems are often preferred because they are considered more efficient or reliable. However, this is not the only factor influencing decisions.
Other attributes include route origin type, local preference values, and policy-based configurations defined by network administrators. These attributes allow organizations to control how traffic enters and exits their networks.
The decision process is sequential, meaning that if one attribute cannot determine a clear best path, the next attribute is evaluated. This layered approach ensures that routing decisions can incorporate both technical and policy-based considerations.
Because of this flexibility, BGP is widely used in environments where traffic engineering and business relationships influence routing behavior.
Scalability Advantages of BGP in Global Networks
One of the most significant advantages of BGP is its ability to scale across extremely large networks. Unlike OSPF, which requires each router to maintain a complete view of the network topology within its domain, BGP routers only store information about reachable prefixes and associated paths.
This significantly reduces memory and CPU requirements, especially in environments where the number of routes is extremely large. Internet backbone routers, for example, may handle hundreds of thousands of route entries without needing full topology awareness.
BGP achieves this scalability by avoiding frequent global recalculations. Instead of recomputing entire network paths when changes occur, BGP incrementally updates routing tables based on received advertisements.
This design makes it suitable for environments where stability and scalability are more important than rapid convergence.
Stability and Convergence Characteristics of BGP
BGP prioritizes stability over speed. Unlike OSPF, which rapidly reacts to topology changes, BGP deliberately introduces delays and damping mechanisms to prevent excessive route fluctuations.
When a route changes frequently, BGP may suppress updates temporarily to prevent instability. This behavior helps maintain overall network stability, especially in large-scale environments where rapid changes could lead to routing oscillations.
As a result, BGP convergence is generally slower than OSPF convergence. However, this trade-off is necessary for maintaining global routing stability.
In practice, BGP is designed to handle long-lived routing decisions rather than rapid internal network changes. This makes it ideal for internet routing but less suitable for internal environments where fast failover is critical.
Policy-Based Routing Control in BGP
One of the most powerful features of BGP is its support for policy-based routing. Network administrators can define rules that influence how routes are selected, advertised, or suppressed.
These policies can be based on business relationships, traffic engineering goals, or security considerations. For example, an organization may prefer to route traffic through a specific provider even if an alternative path is shorter.
This level of control is not available in OSPF, which primarily focuses on shortest path calculation. BGP allows organizations to shape traffic flow in alignment with operational objectives rather than purely technical metrics.
Policy control is one of the main reasons BGP is used at the internet edge, where multiple connectivity options exist.
Route Propagation and Advertisement Mechanisms
BGP relies on route advertisement between peers to distribute routing information. When a router learns about a new network prefix, it decides whether to advertise that prefix to its neighbors based on configured policies.
This selective propagation allows networks to control which routes are visible to external systems. It also prevents unnecessary routing information from flooding the entire network.
Unlike OSPF, where link-state information is broadly distributed within an area, BGP follows a controlled propagation model. Only relevant and policy-approved routes are shared between autonomous systems.
This makes BGP highly efficient for large-scale inter-domain routing.
Traffic Engineering and Path Optimization in BGP
BGP provides mechanisms for traffic engineering that allow administrators to influence the flow of traffic entering and leaving a network. This is achieved by manipulating route attributes such as local preference, AS path length, and route weighting.
By adjusting these attributes, network operators can prioritize certain paths over others, balance traffic loads, or avoid congested links.
This capability is essential in multi-homed environments where multiple external connections exist. Without BGP, controlling traffic flow between different providers would be extremely limited.
Traffic engineering in BGP is both an art and a science, requiring careful planning to ensure optimal performance and resilience.
BGP in Internet Backbone and Service Provider Networks
BGP is the foundational protocol used across internet service provider networks and backbone infrastructure. It enables interconnection between large-scale networks operated by different organizations.
In these environments, routing decisions are influenced not only by technical metrics but also by contractual agreements and routing policies. BGP provides the flexibility needed to implement these complex relationships.
Service providers rely on BGP to manage peering relationships, transit agreements, and global routing visibility. Without BGP, the internet would not be able to function as a decentralized and scalable system.
Limitations and Operational Complexity of BGP
Despite its scalability and flexibility, BGP is not without challenges. One of the primary limitations is its operational complexity. Configuring and managing BGP requires careful planning, especially in large networks with multiple peers and policies.
Incorrect configuration can lead to routing instability, suboptimal paths, or even network outages. Additionally, BGP does not inherently provide fast convergence, which can be problematic in environments requiring rapid failover.
Another challenge is the lack of automatic topology awareness. Unlike OSPF, BGP does not build a complete network map, which means administrators must rely on configuration and monitoring tools to understand routing behavior.
Complementary Nature of OSPF and BGP in Network Design
In modern network architectures, OSPF and BGP are often used together rather than in competition. OSPF is typically deployed within an organization to manage internal routing, while BGP is used at the network edge to handle external connectivity.
This combination allows organizations to benefit from both fast internal convergence and scalable external routing. Internal traffic is efficiently managed by OSPF, while external traffic is controlled and optimized using BGP.
The separation of roles ensures that each protocol operates within its strengths, creating a balanced and resilient network design.
Integration Between Internal and External Routing Domains
When OSPF and BGP are used together, routing information must often be exchanged between them. This process involves controlled redistribution of routes from one protocol to another.
Internal routes learned through OSPF may need to be advertised externally through BGP, while external routes learned through BGP may need to be injected into the internal OSPF domain.
This integration must be carefully managed to prevent routing loops and ensure consistency. Proper route filtering and policy controls are essential in such configurations.
The interaction between OSPF and BGP represents a critical aspect of large-scale network engineering, bridging internal efficiency with global connectivity.
Integrating OSPF and BGP in Real-World Network Architectures
Modern enterprise and service provider networks rarely rely on a single routing protocol in isolation. Instead, they combine multiple protocols to address different layers of the network. OSPF is typically used for internal routing within an organization, while BGP is used at the edge to communicate with external networks. This separation of responsibilities creates a layered routing architecture that balances performance, scalability, and policy control.
In practical deployments, OSPF handles the internal distribution of routes between routers and switches inside a controlled domain. These devices share a consistent view of internal topology and can quickly adapt to changes. At the same time, border routers use BGP to exchange routing information with external autonomous systems such as internet service providers, cloud platforms, or partner organizations.
The integration between these two protocols is not automatic. It requires deliberate configuration and careful planning to ensure that routing information flows correctly between internal and external domains. This is typically achieved through controlled route redistribution, filtering mechanisms, and policy-based controls that govern which routes are shared and how they are modified during propagation.
Route Redistribution Between OSPF and BGP
Route redistribution is the process of transferring routing information from one protocol into another. In networks that use both OSPF and BGP, redistribution is essential for ensuring connectivity between internal systems and external networks.
When an internal network uses OSPF and connects to external systems via BGP, routes learned in OSPF must often be advertised into BGP so that external networks can reach internal resources. Similarly, external routes learned via BGP may need to be injected into the OSPF domain so that internal devices can reach destinations outside the organization.
However, redistribution is not a simple or automatic process. It introduces complexity because each protocol uses different metrics, structures, and decision-making logic. OSPF relies on cost-based shortest path calculations, while BGP relies on path attributes and policy-based decisions. When routes move between these systems, their attributes must be translated or adjusted to fit the receiving protocol.
Without proper control, redistribution can lead to routing loops, suboptimal paths, or excessive route propagation. For this reason, network engineers use filtering rules and route maps to control exactly which prefixes are shared between protocols.
Challenges of Mixing Link-State and Path Vector Systems
OSPF and BGP are fundamentally different in design, which creates challenges when they are used together. OSPF is a link-state protocol that builds a complete map of the internal network and calculates optimal paths based on that map. BGP, on the other hand, is a path vector protocol that makes decisions based on advertised AS paths and routing policies.
When these two systems interact, differences in their operational logic must be carefully managed. For example, OSPF may prefer a path based on lowest cost, while BGP may prefer a path based on policy or AS path length. These conflicting decision mechanisms can lead to unexpected routing behavior if not properly aligned.
Another challenge is metric translation. OSPF uses a cost metric that is typically based on bandwidth, while BGP does not use a comparable metric in the same way. When redistributing routes, administrators often assign default metrics or manually adjust values to ensure consistency.
These differences highlight why OSPF and BGP are not interchangeable but complementary.
Design Principles for Dual-Protocol Networks
Networks that use both OSPF and BGP must follow structured design principles to ensure stability and predictability. One of the most important principles is clear separation of roles. OSPF should remain responsible for internal routing, while BGP should remain responsible for external routing.
Another key principle is controlled redistribution. Routes should not be freely exchanged between protocols without filtering. Instead, only necessary prefixes should be shared, and unnecessary routes should be excluded to reduce complexity.
Hierarchical design is also important. Internal networks should be divided into logical segments where OSPF can efficiently manage routing within defined boundaries. At the edge of the network, BGP should handle all external communication, ensuring that internal topology details are not exposed externally.
These design principles help maintain clarity in routing behavior and reduce the risk of configuration errors.
Scalability Differences Between Internal and External Routing
Scalability is one of the main reasons OSPF and BGP exist as separate protocols. OSPF scales well within a single administrative domain but becomes inefficient when extended beyond it. BGP, on the other hand, is designed to scale across the entire internet.
OSPF achieves scalability through hierarchical area design, which limits the scope of routing updates and reduces the size of topology databases. However, it still requires each router to maintain a relatively detailed view of internal network structure.
BGP achieves scalability by avoiding full topology awareness. Instead of maintaining a complete map of the network, it only stores route information and associated attributes. This makes it capable of handling extremely large routing tables, such as those found in global internet backbones.
The difference in scalability models reflects the different roles each protocol plays in network architecture.
Convergence Behavior in Combined Environments
When OSPF and BGP are used together, convergence behavior becomes more complex. OSPF typically converges quickly because it reacts immediately to topology changes and recalculates shortest paths within the internal network. BGP converges more slowly because it prioritizes stability over speed.
In a dual-protocol environment, internal traffic may reroute quickly due to OSPF convergence, while external traffic may take longer to adjust due to BGP’s slower update propagation. This mismatch can create temporary inconsistencies during network events such as link failures or re-routing scenarios.
To manage this, network engineers often design redundancy and failover strategies that account for differences in convergence timing. Internal and external routing domains are optimized separately to ensure that overall network performance remains stable even during transitions.
Policy Control and Traffic Engineering Across Protocol Boundaries
One of the most important aspects of modern network design is traffic engineering, which involves controlling how data flows through the network. BGP provides extensive support for policy-based routing, allowing administrators to influence path selection based on business or operational requirements.
OSPF, by contrast, primarily focuses on shortest path selection within the internal network. While it does allow some degree of cost manipulation, it is not designed for complex policy enforcement.
When both protocols are used together, policy control is typically implemented at the BGP layer. This allows organizations to determine how external traffic enters and exits the network, while OSPF ensures efficient internal delivery.
Traffic engineering often involves adjusting route attributes, controlling route advertisement, and applying filtering rules. These mechanisms allow network operators to optimize performance, balance load, and ensure redundancy.
Failure Scenarios and Network Resilience
Network resilience refers to the ability of a system to continue functioning despite failures. OSPF and BGP contribute to resilience in different ways.
OSPF provides fast recovery within internal networks. When a link or router fails, OSPF quickly recalculates paths and reroutes traffic using alternative links. This minimizes downtime and ensures that internal communication remains stable.
BGP contributes to resilience at the external boundary of the network. If one external connection fails, BGP can switch to an alternative path through a different autonomous system. However, this process is typically slower than OSPF convergence due to BGP’s stability-focused design.
Together, these protocols create a multi-layered resilience model where internal and external failures are handled independently but cohesively.
Operational Complexity in Dual-Protocol Environments
Running both OSPF and BGP in the same network increases operational complexity. Administrators must manage two different routing systems, each with its own configuration rules, metrics, and behavior.
This complexity requires careful monitoring and troubleshooting practices. Misconfigurations in one protocol can affect the other, especially when route redistribution is involved. For example, incorrect redistribution settings can lead to routing loops or unintended route propagation.
To manage this complexity, networks are often designed with clear boundaries and strict policy enforcement. Each protocol is assigned a specific role, and interaction between them is tightly controlled.
Despite the complexity, this dual-protocol approach remains standard in large-scale networks due to its flexibility and performance advantages.
Evolution of Routing Protocol Usage in Modern Infrastructure
Over time, network design practices have evolved to accommodate increasing traffic demands and distributed architectures. OSPF and BGP have both remained central to this evolution, but their roles have become more specialized.
OSPF continues to dominate internal routing environments due to its efficiency and fast convergence. It is particularly well-suited for modern data centers and enterprise backbones where internal traffic patterns are dense and dynamic.
BGP continues to dominate external routing due to its scalability and policy control capabilities. It is essential for connecting large-scale networks and managing global internet routing.
Together, they form a foundational routing model that supports both local efficiency and global connectivity.
Strategic Considerations in Routing Protocol Selection
Choosing between OSPF and BGP is not a matter of preference but of architectural requirement. OSPF is selected when the goal is fast internal routing with full topology awareness. BGP is selected when the goal is scalable external routing with policy control.
In most real-world scenarios, both protocols are used together rather than individually. Their combined use reflects the layered structure of modern networks, where internal and external routing requirements differ significantly.
Understanding how these protocols interact, complement each other, and differ in operational behavior is essential for designing stable and scalable network infrastructures.
Conclusion
In modern network design, OSPF and BGP are best understood not as competing technologies but as complementary routing mechanisms that operate at different layers of the networking stack. Their coexistence reflects a fundamental principle of large-scale infrastructure design: internal efficiency and external scalability require different operational models. OSPF is optimized for controlled environments where rapid convergence, deterministic path selection, and full topology awareness are essential. BGP, on the other hand, is engineered for environments where control, policy enforcement, and global scalability matter more than speed of convergence or complete visibility.
Within internal networks, OSPF provides a structured and highly responsive routing system. It ensures that all routers within an organization maintain a consistent view of the network topology. This consistency is achieved through link-state propagation and synchronized database construction, allowing each router to independently compute optimal paths using identical information. The result is a highly stable and predictable internal routing environment. When changes occur, OSPF reacts quickly, recalculating only the affected portions of the topology and restoring optimal routing paths with minimal disruption. This makes it particularly suitable for enterprise LANs, campus networks, and data center environments where internal traffic must be delivered with low latency and high reliability.
However, OSPF’s strength in maintaining a full internal map of the network becomes a limitation when considering large-scale or inter-organizational routing. As networks grow, maintaining full topology awareness becomes resource-intensive. More importantly, OSPF is not designed to understand or enforce complex routing policies between independent administrative domains. It is built on the assumption that all participating devices belong to a single trust boundary, which does not reflect the reality of internet-scale networking.
This is where BGP becomes essential. BGP operates without requiring full topology knowledge. Instead, it relies on path information and policy-based decision-making. Each routing decision is influenced not only by reachability but also by attributes such as AS path length, local preference, and administrative policies. This allows organizations to influence how traffic enters and exits their networks, enabling traffic engineering strategies that align with business requirements, contractual obligations, and performance goals.
The AS path mechanism is one of the most important structural components of BGP. By recording the sequence of autonomous systems that a route traverses, BGP not only prevents routing loops but also provides a scalable way to evaluate routing paths across the global internet. Unlike OSPF, which calculates shortest paths based on internal metrics, BGP evaluates routes based on policy and path attributes. This difference is critical because global routing is not purely a technical optimization problem; it is also a matter of governance, economics, and inter-network agreements.
Another important distinction lies in convergence philosophy. OSPF is designed for rapid convergence, making it highly responsive to network changes. This responsiveness is critical in environments where internal links may fail or recover frequently. BGP, however, prioritizes stability over speed. It intentionally slows down propagation of routing changes to avoid instability across large-scale networks. While this results in slower convergence, it prevents widespread routing oscillations that could disrupt global connectivity.
When both protocols are deployed together, their interaction creates a layered routing architecture. OSPF manages internal reachability, ensuring that all internal nodes can communicate efficiently. BGP manages external reachability, ensuring that the organization can connect to external networks and control how that connectivity is presented to the outside world. This separation of concerns is essential for maintaining both performance and control.
One of the most sensitive aspects of combining OSPF and BGP is route redistribution. This process acts as a bridge between internal and external routing domains. However, it must be handled with precision. Improper redistribution can lead to routing loops, inconsistent route preferences, or unintended exposure of internal network structure to external systems. Because OSPF and BGP use different metrics and decision-making logic, route translation requires careful mapping of attributes and strict filtering rules. In well-designed networks, redistribution is minimized and tightly controlled, ensuring that each protocol remains within its intended scope.
From an architectural perspective, the combination of OSPF and BGP reflects a layered approach to network engineering. Internal layers prioritize speed, consistency, and automated path calculation. External layers prioritize scalability, policy enforcement, and controlled information exchange. This separation allows networks to scale from small enterprise environments to global infrastructures without losing operational stability.
Another key consideration is operational complexity. Running both protocols requires advanced understanding of routing behavior, as well as careful monitoring of how routes propagate between domains. Misconfigurations can have far-reaching consequences, particularly in environments where multiple external connections exist. Despite this complexity, the dual-protocol approach remains the industry standard because it provides unmatched flexibility and resilience.
In terms of performance trade-offs, OSPF delivers superior internal efficiency, while BGP delivers unmatched external scalability. OSPF minimizes path calculation delays within a controlled environment, whereas BGP minimizes memory and topology overhead across vast, decentralized systems. Each protocol is optimized for a different scale of operation, and their combined use ensures that neither internal nor external routing requirements are compromised.
The evolution of modern networks has only reinforced the importance of this dual approach. As organizations adopt hybrid infrastructures spanning on-premises systems, cloud environments, and distributed edge locations, routing complexity increases significantly. OSPF continues to serve as the backbone of internal communication, while BGP provides the flexibility needed to interconnect diverse and geographically distributed systems.
Ultimately, the decision is not about choosing OSPF versus BGP in isolation, but about understanding where each fits within the broader network architecture. OSPF excels in environments where control, speed, and internal optimization are critical. BGP excels in environments where scale, policy control, and interconnectivity define operational requirements. When used together, they form a cohesive routing strategy that supports both organizational efficiency and global reachability.