Cross-site scripting is a category of security weakness found in interactive web environments where user input is displayed or processed without sufficient validation or encoding. It emerges when an application accepts external data and later presents it to other users in a way that allows unintended instructions to be executed inside a browser. Modern web platforms rely heavily on dynamic content generation, personalization, and real-time interaction, which increases the number of entry points where user-supplied information is processed. This makes the environment highly dependent on proper input handling and output rendering practices. When these safeguards are missing or incomplete, malicious input can blend into normal page content and be interpreted as part of the application logic rather than external manipulation. The core issue behind this vulnerability is not a flaw in the browser itself but a breakdown in how the application distinguishes between trusted code and untrusted data. Browsers are designed to execute instructions provided by websites under the assumption that the content originates from a reliable source. When attackers successfully insert crafted input into this flow, they are able to influence how a page behaves for every user who interacts with it. This can include modifying visible elements, altering user experience flows, or redirecting interactions in unintended directions. Because these actions occur inside the normal rendering process of a page, they are often difficult to detect without detailed inspection of underlying application behavior.
Why Cross-Site Scripting Continues to Appear in Evolving Web Applications
Despite ongoing improvements in web development practices, cross-site scripting continues to be a recurring issue across digital platforms due to the complexity of modern application design. Applications today are not static pages but highly interactive systems that depend on continuous data exchange between users and servers. This constant flow of input increases the likelihood that some portion of user-generated content may not be fully sanitized or properly encoded before being displayed. Another contributing factor is the integration of multiple technologies that handle content rendering, each with its own processing rules and interpretation methods. When these systems interact, inconsistencies in how input is treated can create gaps that attackers exploit. Additionally, development speed and feature expansion often take priority over exhaustive security validation, which can result in overlooked vulnerabilities. The widespread use of personalization features, comment sections, feedback forms, and dynamic search interfaces further expands the attack surface. Each of these components processes external data and displays it within a browser context, creating potential pathways for unwanted instructions to be executed. As applications grow more complex, ensuring consistent validation across all input points becomes more challenging, allowing vulnerabilities to persist even in otherwise well-designed systems.
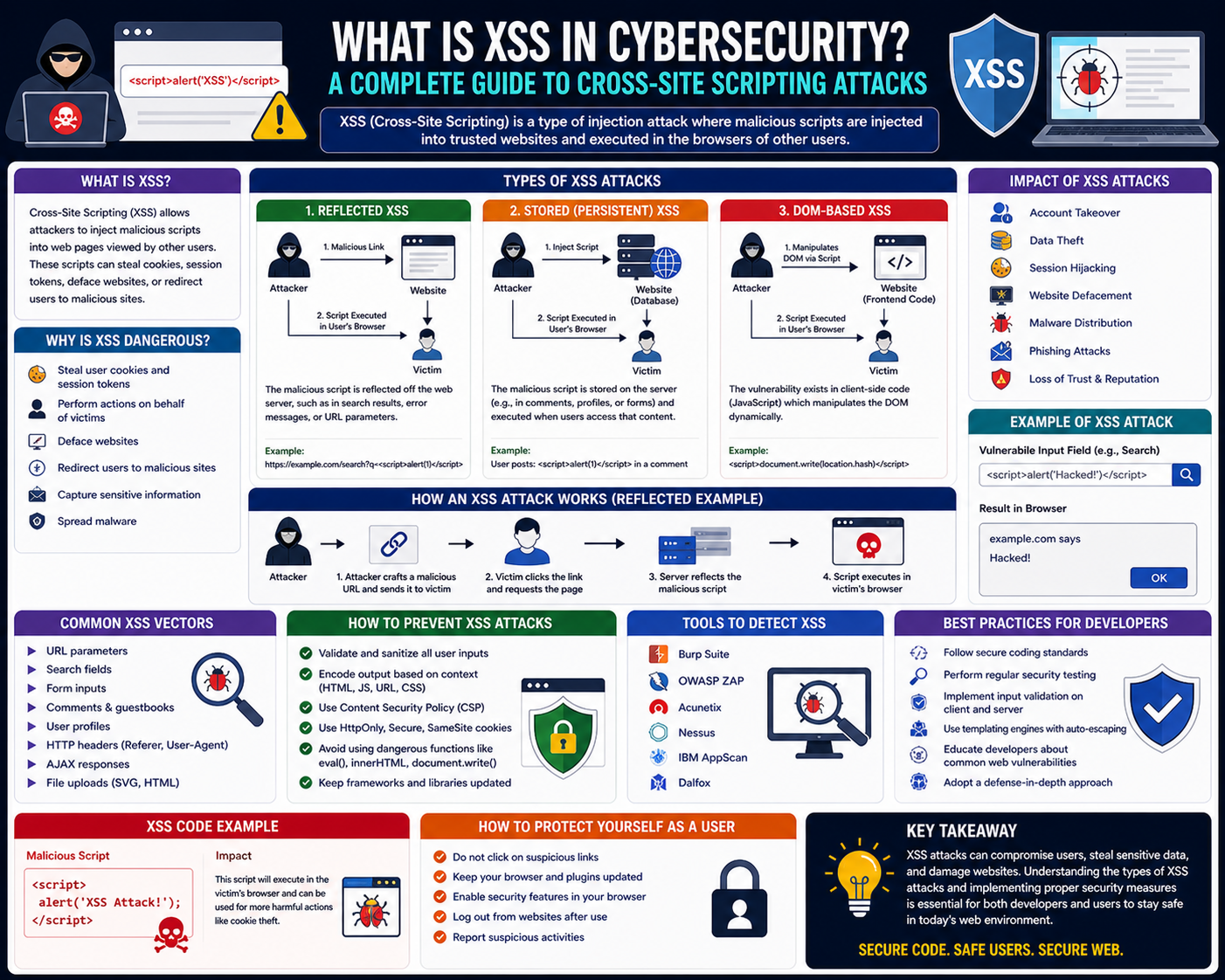
Stored Cross-Site Scripting and the Nature of Persistent Injection
Stored cross-site scripting occurs when malicious input is permanently saved within a system and later retrieved and displayed to users. This form of vulnerability is particularly impactful because it does not require repeated interaction from the attacker once the initial input has been accepted. Instead, the harmful content becomes part of the application’s stored data and is delivered automatically whenever the associated page or feature is accessed. This typically occurs in environments that allow users to contribute content such as profiles, comments, messages, or public posts. When the application fails to properly sanitize this input before storing it, the data retains its original structure, including any embedded instructions. Once stored, this content is treated as normal data by the system, which means it is retrieved and displayed alongside legitimate information. When other users access this content, their browsers interpret the injected elements as part of the page itself, allowing unintended execution to occur. The persistence of this type of injection makes it particularly dangerous because a single successful submission can affect a large number of users over an extended period. Unlike temporary manipulations, stored injection becomes embedded within the core content structure of the application until it is identified and removed.
How Persistent Injection Influences User Experience and System Behavior
When malicious input is stored within a system and later rendered in user interfaces, it can subtly alter how individuals interact with the platform. Because the injected content appears as part of the legitimate page structure, users may not immediately recognize that something is incorrect. This can lead to unintended interactions where users engage with modified interface elements or follow altered navigation paths. The presence of unexpected behavior within a trusted environment can reduce user confidence in the platform and create confusion regarding the authenticity of displayed information. In some cases, injected content may modify how page components are arranged or how data is presented, leading to misinterpretation of important details. Since the browser executes these instructions within the context of a trusted session, the effects are not limited to visual changes but can also extend to how data is processed during user interaction. Over time, repeated exposure to altered content can impact the reliability of the platform and create inconsistencies in how information is perceived. The most significant concern arises from the fact that users generally assume that visible content originates from a secure and controlled source, which makes them more likely to trust manipulated elements without questioning their legitimacy.
Transitioning from Stored Injection to Reflective Behavior in Web Requests
Reflective cross-site scripting represents a different category of vulnerability where malicious input is not stored but instead immediately returned within a server response. This type of behavior typically occurs when applications dynamically generate pages based on user input parameters without properly filtering or encoding them. The attacker crafts a specially designed request that includes malicious content embedded within input fields or query structures. When the server processes this request, it includes the input directly in the generated response, causing it to be interpreted by the browser as part of the page content. Unlike stored injection, reflective behavior is temporary and occurs only during the processing of a specific request. However, it can still be highly effective because it often relies on user trust in links or requests that appear legitimate. Users may unknowingly trigger the execution by interacting with a manipulated link or submitting crafted input through a form. The immediate reflection of input into the response creates an opportunity for unintended execution within the browser environment, allowing attackers to influence page behavior during that session.
How Reflected Injection Exploits Trust in Dynamic Page Generation
Reflective injection takes advantage of the way modern applications generate responses based on user-supplied parameters. Many systems personalize content or provide search results by incorporating user input directly into response templates. When this input is not properly sanitized, it can be returned to the browser in its original form. The browser then processes this content as part of the page structure, which can lead to unintended execution of embedded instructions. Because this process occurs within a single request-response cycle, the attack is often dependent on user interaction with a specially crafted link or submission. The effectiveness of reflective behavior lies in its ability to exploit user trust in familiar interfaces. Since the response often appears to be legitimate feedback from the system, users may not realize that the content has been manipulated. This makes reflective injection particularly effective in scenarios where users are accustomed to clicking links or entering data without closely inspecting the underlying structure of the request.
Reflective Cross-Site Scripting and Its Execution Flow in Web Applications
Reflective cross-site scripting occurs when malicious input is embedded into a request and immediately returned in the server’s response without being stored. This type of vulnerability typically appears in applications that dynamically generate web pages based on user supplied parameters such as search queries, form inputs, or URL parameters. A user-supplied issue arises when the application directly includes this input in the output page without proper validation or encoding. In such cases, the browser interprets the returned content as part of the page structure rather than raw data, which allows unintended instructions to execute within the user session. The execution flow usually begins when a user interacts with a crafted link or submits a specially designed input. The server processes the request and inserts the input into the response page, which is then rendered by the browser. Because the input is reflected immediately, the impact is temporary but still highly effective in manipulating user behavior. This form of attack relies heavily on social engineering techniques, as users are often tricked into clicking links that appear legitimate. Once the response is generated, the browser executes the injected content in the same context as trusted page elements, allowing attackers to influence page behavior or user interaction without requiring persistent storage on the server.
How Reflective Injection Exploits User Trust and Dynamic Response Systems
Modern web applications frequently generate responses dynamically based on user input to provide personalized experiences. This includes search results, error messages, and query-based responses that reflect user-provided values back to the interface. When these values are not properly sanitized, they can be directly embedded into the HTML output, creating opportunities for unintended execution. Reflective injection exploits this mechanism by inserting crafted input into fields that are later displayed in the browser. Because the response appears to come directly from the application, users often assume it is safe and legitimate. This trust becomes a critical weakness, as attackers rely on users interacting with manipulated links or submitting input that triggers the vulnerability. The browser, following its standard execution model, processes the returned content as part of the page structure, which allows injected instructions to run within the context of the session. This can lead to modifications in how the page behaves, how information is displayed, or how user actions are processed. The transient nature of reflective injection does not reduce its impact, as it can still be used to capture session information or redirect user activity during a single interaction.
DOM-Based Cross-Site Scripting and Client Side Execution Risks
DOM-based cross-site scripting is a variation of client-side scripting that occurs entirely within the client side environment without requiring server side reflection or storage. On the client-side, the issue arises when the client-server-side dynamically modifies the Document Object Model based on user input or URL parameters. The Document Object Model represents the structured representation of a web page that browsers use to render content and manage interactions. When JavaScript functions manipulate this structure using untrusted input without proper validation, attackers can influence how the page is constructed in the browser. Unlike stored or reflective injection, DOM based vulnerabilities do not depend on server responses containing malicious code. Instead, the vulnerability exists within the way client side code processes and inserts data into the page. This makes detection client-side lengthening because the malicious behavior occurs entirely within the browser after the page has already been loaded. Attackers often exploit this by modifying URL fragments or input fields that are later used by scripts to update page content. Once the browser processes this modified input, it can lead to unintended execution within the client environment, allowing manipulation of page elements or behavior.
Understanding the Role of the Document Object Model in Web Security
The Document Object Model plays a central role in how modern web applications function, as it defines the structure and behavior of interactive pages. It allows scripts to access and modify elements dynamically, enabling features such as live updates, interactive forms, and responsive interfaces. However, this flexibility also introduces security risks when untrusted input is incorporated into DOM manipulation processes. When input data is directly inserted into the DOM without proper encoding or filtering, it can alter the structure of the page in unintended ways. This becomes particularly problematic when scripts rely on URL parameters or user input fields to determine how content is displayed. If these inputs are not properly validated, attackers can inject values that modify how scripts behave during execution. Because DOM manipulation occurs within the browser, these vulnerabilities bypass traditional server side security checks. The browser executes the scripts as part of normal server-side behavior, making it difficult to distinguish between legitimate functionality and malicious modification. This internal execution environment creates a unique challenge for securing modern applications that rely heavily on client side interactivity.
Differences Between Stored, Reflected, and DOM-Based Client-Side Techniques
While all forms of cross-site scripting involve the execution of unauthorized instructions within a browser, they differ in how the malicious input is delivered and processed. Stored injection involves the persistent storage of malicious content on the server, which is later delivered to multiple users. This makes it the most impactful in terms of scale, as a single entry can affect many individuals over time. Reflective injection, on the other hand, does not involve storage but instead relies on immediate inclusion of user input in server responses. This makes it dependent on user interaction with crafted requests, often requiring social engineering techniques to be effective. DOM based injection differs from both by occurring entirely within the client DOM environment, without involving server side processing of malicious input. Instead, it relies on insecure hand server-side within JavaScript functions that manipulate page content. These distinctions are important because each type requires different defensive strategies and occurs at different points within the application lifecycle. Despite their differences, all three types share the common weakness of failing to properly handle untrusted input before it is executed or rendered within the browser environment.
Browser Execution Context and the Risk of Trusted Content Misinterpretation
Browsers operate under a security model that assumes content delivered from a website is intended to be executed as part of the page. This includes scripts, styles, and dynamic elements that define how a page behaves and appears. When malicious input is injected into this environment, the browser may interpret it as legitimate content because it originates from a trusted source within the application flow. This trust model is essential for enabling modern web functionality, but also creates opportunities for exploitation when input validation is insufficient. Once malicious instructions are executed within the browser context, they inherit the same permissions as legitimate scripts running on the page. This allows them to interact with page elements, access session data, or modify user interactions. The difficulty in detecting such behavior lies in the fact that it often blends seamlessly with normal page operations. Users typically cannot distinguish between legitimate interface elements and those introduced through unauthorized manipulation. This makes the browser execution context one of the most critical areas to secure when addressing cross-site scripting vulnerabilities.
Input Handling Weaknesses in Dynamic Web Application Design
A major factor contributing to cross-site scripting vulnerabilities is inadequate handling of user input within dynamic web applications. Modern systems rely heavily on accepting external data to generate personalized content, but this creates multiple opportunities for improper validation. When input is directly inserted into output without transformation or encoding, it retains its original structure, which may include unintended instructions. Applications that fail to distinguish between data and executable content are particularly vulnerable to manipulation. This issue is often compounded by inconsistent validation practices across different parts of an application. For example, input may be sanitized at one stage but later reintroduced into a different context without proper checks. Additionally, multiple layers of processing, such as server-side rendering and client-side scripting, can introduce gaps where validation is not consistently applied. These weaknesses allow attackers to craft input that bypasses certain filters and reaches the browser in a form that can be executed. Strengthening input handling requires a consistent approach across all stages of data processing, ensuring that untrusted content is treated as data rather than executable code.
The Expanding Attack Surface of Interactive Web Interfaces
The evolution of web applications toward highly interactive interfaces has significantly expanded the potential attack surface for cross-site scripting vulnerabilities. Features such as real-time updates, dynamic content loading, and client-side rendering introduce numerous points where user input is processed and displayed. Each of these points represents a potential entry path for malicious input if not properly secured. Applications that rely heavily on JavaScript frameworks and asynchronous data loading often process input in multiple stages, increasing the complexity of maintaining consistent security controls. The integration of third party libraries and external data sources further complicates this environment; each additional component introduces its own processing logic. As applications become more feature rich, ensuring that every input path is properly validated becomes increasingly challenging. This expanded complexity creates opportunities for subtle vulnerabilities to remain undetected within large codebases. Attackers exploit these weaknesses by identifying areas where input handling is inconsistent or incomplete, allowing them to inject instructions that execute within the browser environment.
Deep Dive into DOM-Based Cross-Site Scripting and Client Side Manipulation Risks
DOM-based cross-site scripting represents a client-side vulnerability that exists entirely within the browser’s execution environment. Unlike stored or reflected variants, it does not depend on server side processing of malicious input. Instead, it arises when client sideserver-sideke untrusted data and uses it to dynamically modify the structure or behavior of a web page. The Document Object Model acts as the bridge between web content and interactive functionality, allowing scripts to read and update page elements in real time. When this model is manipulated using unsanitized input, the browser may execute unintended instructions as part of normal page rendering. This makes the vulnerability particularly subtle because the malicious behavior is not visible in server responses and may only exist after the page has fully loaded. Attackers often exploit this by influencing input sources such as URL fragments, query parameters, or client side storage values. These inputs are then consumed by a JavaScript function client-side on the DOM without proper validation or encoding. Once processed, the browser integrates the modified structure into the active page, allowing unintended execution to occur within the same context as legitimate scripts.
How Client Side Execution Environments Enable Hidden Injection Paths
Modern web applications rely heavily on client side scripting to deliver dynamic and responsive user experiences. This client-side moved a significant portion of application logic from the server to the browser, increasing the complexity of input handling. In client side execution environments, scripts often retrieve data from multiple sources, including user input fields, URL parameters, and asynchronous responses. When these sources are not properly validated before being inserted into the DOM, they create hidden injection paths that attackers can exploit. The browser executes JavaScript within a shared context where all scripts have access to the same document structure, which means any manipulated input that becomes part of the DOM can influence page behavior. This environment makes it difficult to isolate trusted and untrusted data once both are combined during rendering. As a result, even small inconsistencies in input handling can lead to significant security risks. The challenge lies in ensuring that dynamic updates to the page do not inadvertently introduce executable content derived from external sources.
The Role of Data Encoding and Output Handling in Preventing Injection
One of the most critical defenses against cross-site scripting vulnerabilities lies in proper data encoding before output rendering. Encoding transforms user input into a format that is safe for display, ensuring that it is interpreted as plain text rather than executable instructions. Without this transformation, browsers may interpret special characters or structured input as part of the page logic. Output handling plays a similarly important role by determining how data is inserted into the DOM. When applications directly inject raw input into HTML structures, they risk allowing unintended execution within the browser. Proper handling requires distinguishing between content meant for display and content meant for execution. This separation ensures that user supplied data cannot alter the structure of the page or influence the script. User-supplied code output handling is one of the most common contributing factors to DOM based vulnerabilities, as it allows client side scripts to treat untrusted DOM-based parts of the application loServer-sideer -si, de these processes reduce the likelihood that injected content will be interpreted as executable code.
Session Based Risks and Browser Level Data Exposure Concerns
Cross-site scriptSession-Basedlities can Browser-Levelsession based risks where attackers attempt to access or manipulate information associated with a user’s active session. When malicious scripts execute within the browser context, they operate with the same level of access as legitimate scripts running on the page. This means they can interact with session related data stored in the browser environment. Although modern browsers impose session-related restrictions to limit direct access to certain types of sensitive storage, improperly secured applications may still expose data through client side logic. Attackers can exploit these weaknesses by injecting scripts client-side with page elements containing session related information. Because the execution occurs within the trusted cosession-related application, the browser does not inherently distinguish between legitimate and malicious actions. This creates a scenario where sensitive data may be exposed indirectly through manipulated page behavior. The risk is amplified in applications that rely heavily on client side rendering, where session information is frequently used to personalize client-side and manage user state.
Interaction Between User Input Channels and Dynamic Rendering Pipelines
Modern applications often rely on multiple input channels to build dynamic rendering pipelines that generate real time content. These channels include form inputs, URL parameters, API response-timed browser storage mechanisms. Each of these sources contributes data that is used to construct the final rendered page. When these inputs are combined without consistent validation, they create opportunities for injection vulnerabilities to emerge. Dynamic rendering pipelines are designed to be flexible and responsive, but this flexibility can introduce security weaknesses if input handling is not standardized. For example, data retrieved from an external source may be directly inserted into the DOM without verification, allowing malicious content to propagate through the rendering process. Once this data becomes part of the page structure, it may influence how other components behave or interact with the user. The complexity of these pipelines makes it difficult to track the flow of untrusted input, especially in large applications where multiple modules contribute to page generation. Ensuring secure rendering requires strict control over how data moves through each stage of the pipeline.
Comparative Understanding of Cross-Site Scripting Variants in Real Systems
In practical environments, stored, reflected, and DOM-based cross-site scripting often coexist within the same application due to overlapping input handling mechanisms. Stored variants typically emerge in content management systems or platforms that allow persistent user contributions. Reflective variants are more common in applications that generate responses based on user queries or dynamic input parameters. DOM based variants arise in highly interactive applications where client side sDOM-basedndle significant portions of rendering logic. Although the client-side operates differently, they share a common weakness in failing to properly separate untrusted input from executable code. In real systems, these vulnerabilities may not appear in isolation but instead interact with each other through shared data flows. For example, input stored in a database may later be processed by client side scripts, creating a hybrid scenario that combines stored and DOM baclient-sideeristics. Understanding these interactions is essential for identifying complex security weaknesses that may not be visible when examining individual components in isolation. Each variant contributes to the overall risk profile of an application and must be addressed through comprehensive input handling strategies.
Evolution of Web Application Architecture and Expanding Security Challenges
The evolution of web application architecture has significantly increased the complexity of managing security vulnerabilities such as cross-site scripting. Early web systems were primarily static, with limited user interaction and minimal client side processing. Modern applications, however, rely on continuous inter-client-side and server-side processing, with extensive use of asynchronous data loading and dynamic content rendering. This shift has introduced multiple layers of processing where user input can be modified, combined, or displayed in different contexts. Each layer introduces potential points of failure where input validation may be inconsistent or incomplete. Additionally, the widespread use of modular development frameworks and reusable components has increased code reuse across applications, which can propagate vulnerabilities if insecure patterns are reused. The integration of external services and third party scripts further expands the attack surface, as each external dependency third-parand ty script has its own execution context. These architectural changes have made it more challenging to maintain consistent security controls across entire applications, requiring more sophisticated approaches to input handling and output rendering.
Browser Security Models and Their Limitations Against Injection Attacks
Browsers implement security models designed to isolate content and restrict unauthorized access between different sources. These models include policies that define how scripts interact with content from different origins. However, cross-site scripting vulnerabilities exploit scenarios where malicious content is introduced within the same origin as legitimate application code. In such cases, the browser treats injected content as part of the trusted execution environment, allowing it to bypass many isolation mechanisms. This limitation highlights the importance of application level security rather than relying solely on browser protections. Application-level scripts execute within the same context as legitimate code; they inherit the same privileges and access rights. This allows them to interact with page elements, modify content, and influence user interactions without triggering browser level security warnings. The effectiveness of these attacks demonstrates that browser-level security models are not designed to differentiate between legitimate and malicious content within the same origin, making proper input handling at the application level essential.
Long Term Implications of Uncontrolled Script Injection in Web Ecosystems
Unconventional long-term injection can have long term consequences for web ecosystems, particularly in platforms that rely on long-term user-generated content or continuous interaction. Over time, even small vulnerabilities accumulate and create significant security risks across interconnected systems. Once malicious content becomes embedded within application workflows, it can persist across multiple user sessions and interactions. This persistence can lead to gradual degradation of trust in the platform and increased exposure of sensitive data. In environments where applications share data or integrate with external services, the impact of injection vulnerabilities can extend beyond a single system. Malicious scripts may influence data flow between connected services or alter how information is displayed across different interfaces. The long-term challenge lies in ensuring that all components of a web ecosystem maintain long-term security standards for input handling and output rendering. Without this consistency, vulnerabilities can propagate across systems and create widespread security concerns that are difficult to isolate and resolve.
Conclusion
Cross-site scripting remains one of the most persistent and impactful security vulnerabilities in modern web applications because it exploits the natural way websites are designed to function. Web systems are built to accept user input, process it dynamically, and display it back in a browser environment where users expect immediate interaction. This continuous flow of data between users and applications creates opportunities for malicious input to be interpreted as executable instructions when proper safeguards are missing. Even as development frameworks evolve and security tools improve, the core challenge stays the same: ensuring that data provided by users is never confused with executable code inside the browser. This distinction is difficult to maintain consistently across complex systems, especially when applications rely heavily on client side rendering, asynchronous updates, and dynamic content generation. As client-side cross-site scripting continues to appear in both legacy platforms and modern architectures, not because developers ignore security, but because the boundary between data and execution is inherently difficult to enforce in highly interactive environments.
A key takeaway from understanding this vulnerability is the importance of trust boundaries within application design. Every piece of data entering a system should be treated as untrusted until it has been properly validated, sanitized, and encoded. Many vulnerabilities occur when systems assume that data is safe simply because it originates from internal components or previously processed layers. In reality, data often passes through multiple stages, such as APIs, databases, client side scripts, and rendering engines, and each stage introduces the possibility of interpretation or modification. When applications fail to maintain strict separation between raw input and rendered output, malicious content can slip through unnoticed and become part of the page structure. Once this happens, the browser may execute it as part of normal page behavior, allowing attackers to influence how the application behaves for end users. Maintaining strict trust boundaries is therefore one of the most important principles in secure system design.
Another critical aspect of this issue lies in how browsers execute content. Modern browsers are highly capable environments that support scripting, dynamic rendering, and real time updates. They assume that content delivered from the same origin is real-time and safe to execute. This assumption is essential for enabling interactive web experiences, but it also creates a significant weakness when malicious content is introduced into that trusted context. Once injected input becomes part of the page, it inherits the same privileges as legitimate scripts, allowing it to manipulate page elements, modify user interactions, and influence application behavior. The browser itself does not inherently distinguish between intended and unintended instructions if both exist within the same execution context. This is why application level security controls are essential, because relying solely on application-level controls is not sufficient to prevent exploitation.
Secure development practices play a central role in reducing exposure to these vulnerabilities. Input validation ensures that only expected types of data are accepted by the system, while encoding ensures that special characters are treated as plain text rather than executable instructions. Output handling is equally important because it determines how data is rendered in the browser. If raw input is directly inserted into the page structure, it may be interpreted as part of the document rather than as harmless content. Consistency across both server side and client side processing is essential because inconsistencies can bypass server-side security controls. In many real world cases, vulnerabilities occur not because validation is absent, but because it is applied inconsistently across different parts of the system. Ensuring uniform handling of data throughout its lifecycle is therefore a fundamental requirement for secure application design.
Cross-site scripting also highlights the importance of understanding how client side execution environments operate. Modern applications increasingly rely on client-side JavaScript frameworks to manage page behavior directly within the browser. These scripts often interact with user input, URL parameters, and external data sources to update the page in real time. When these inputs are not properly validated before being used in DOM manipulation, they can alter the structure or behavior of the page in unintended ways. This type of vulnerability is particularly difficult to detect because it occurs entirely within the browser after the page has loaded, without requiring server side reflection or storage. As a result, tra aditional server focused secuserver-side may not identify the issue. The complexity of client-server-focused makes it essential to carefully control how data is introduced into the Document Object Model and to ensure that untrusted input is never directly interpreted as executable code.
The long term impact of these vulnerabilities extends beyond technical security, long-term affects user trust and system reliability. When users encounter unexpected behavior in a trusted environment, their confidence in the platform decreases. This is especially significant for applications that handle sensitive interactions or personal data. Even a single instance of manipulated content can create uncertainty about the integrity of the entire system. If vulnerabilities persist over time, they can erode user engagement and damage the reputation of the platform. In interconnected digital ecosystems, the impact may also extend beyond a single application, affecting integrated services and external systems that rely on shared data. This demonstrates that security weaknesses are not isolated technical issues but broader risks that influence user perception and system stability.
As web applications become more complex and interconnected, the attack surface for cross-site scripting continues to expand. Modern systems rely on multiple data sources, third-party integrations, and asynchronous communication channels that all contribute to dynamic page rendering. Each of these components introduces additional points where input must be carefully managed. The more layers involved in processing data, the harder it becomes to maintain consistent validation and encoding practices. External libraries and frameworks may also introduce their own processing logic, which can conflict with or bypass application-level safeguards. This growing complexity requires a more holistic approach to security, where input handling is considered at every stage of the data lifecycle rather than at a single point in the system.
Preventing these vulnerabilities ultimately requires a combination of disciplined development practices, consistent security enforcement, and careful architectural design. No single technique is sufficient on its own because vulnerabilities often arise from interactions between multiple components rather than isolated mistakes. The most effective strategy is to ensure that untrusted input is never allowed to become executable content under any circumstances. This requires continuous attention to how data flows through the system, how it is transformed, and how it is rendered. As applications continue to evolve toward more dynamic and interactive experiences, maintaining this separation between data and execution becomes increasingly important for long-term security and reliability.