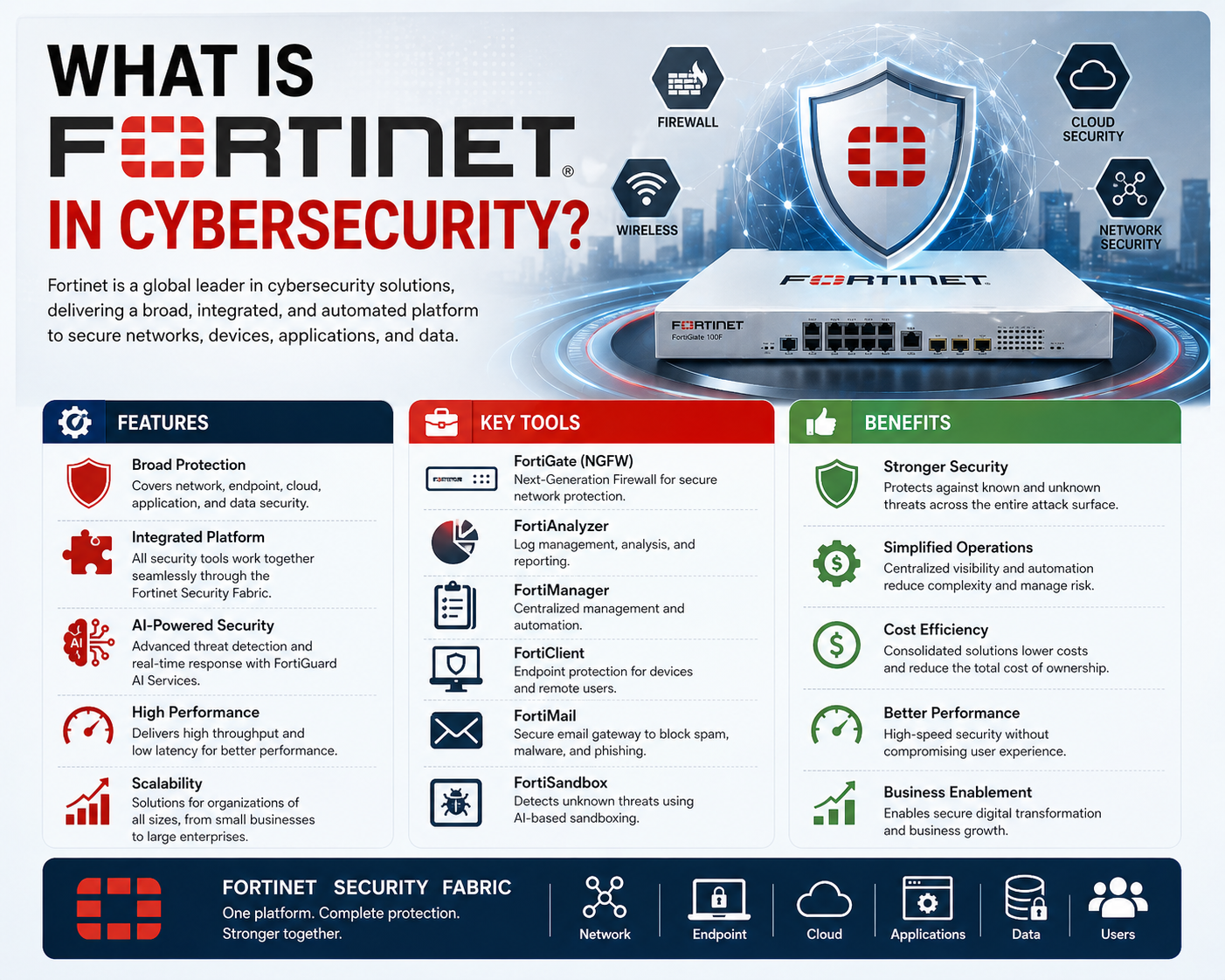
Fortinet is widely recognized in the cybersecurity industry as a major provider of network security technologies, but its role extends far beyond a single product category. It represents a comprehensive security-focused ecosystem designed to protect digital environments from evolving cyber threats. In modern enterprise infrastructure, where networks are increasingly distributed across on-premises systems, cloud platforms, and remote endpoints, Fortinet positions itself as a unified security architecture that connects and protects every layer of connectivity. The company’s reputation began with its firewall technology, but over time it expanded into a broad portfolio of integrated security solutions that address multiple aspects of enterprise risk management.
The Rise of Next-Generation Firewalls and Their Purpose
Next-generation firewalls emerged as a response to the limitations of traditional firewall systems that primarily relied on static rules and basic packet filtering. Early firewalls focused on controlling traffic based on ports, IP addresses, and predefined access rules. While effective in simple network environments, these systems struggled to handle modern threats that operate at higher layers of the network stack and often disguise themselves within legitimate traffic. Next-generation firewalls introduced deeper inspection capabilities, allowing them to analyze application-level data, detect anomalies, and identify malicious behavior patterns.
These systems are not static security devices but adaptive platforms that continuously evolve with threat intelligence. They incorporate intrusion prevention systems, application awareness, user identity tracking, and behavioral analytics. Over time, these features have become essential as cyberattacks have grown more sophisticated, often leveraging encryption, cloud services, and distributed attack infrastructures. The development of next-generation firewalls reflects a broader shift in cybersecurity from perimeter defense to intelligent, context-aware protection.
How Fortinet Established Its Position in Firewall Technology
Fortinet entered the cybersecurity market with a strong focus on high-performance firewall technology. Its early advantage came from the integration of custom hardware acceleration designed specifically for security processing. This approach enabled faster inspection of network traffic compared to software-only solutions, allowing organizations to handle large volumes of data without compromising security performance. As networks expanded and traffic demands increased, this performance-centric design became a key differentiator.
However, Fortinet’s strategy was not limited to firewall performance alone. The company adopted a broader vision that security should not exist as isolated components but as interconnected systems. This perspective led to the development of integrated solutions where firewalls, endpoint security, wireless access control, and cloud security tools could operate in coordination. The firewall became the central control point, but not the only layer of defense.
Understanding the Concept of a Security Ecosystem
A security ecosystem refers to a unified architecture in which multiple security tools work together to provide coordinated protection. Instead of managing separate systems for firewalling, intrusion detection, endpoint security, and network access control, an ecosystem-based approach connects these elements into a single management framework. Fortinet’s approach to cybersecurity is built around this principle.
Within this structure, each component contributes to a shared intelligence system. When one part of the network detects a threat, that information is shared across the entire ecosystem. This enables automated responses and faster mitigation of risks. The advantage of this design is not just efficiency but also consistency in security enforcement across different environments, including physical networks, virtualized systems, and cloud infrastructure.
Transition from Traditional Firewalls to Intelligent Security Systems
Traditional firewalls operated on predefined rules that required manual configuration. Network administrators had to specify which traffic was allowed or blocked, often leading to complex rule sets that were difficult to maintain. This approach was functional in earlier network environments but became inefficient as applications and services moved to dynamic cloud-based infrastructures.
Next-generation firewalls introduced intelligence into this process by analyzing traffic behavior instead of relying solely on static rules. This includes identifying applications regardless of port usage, inspecting encrypted traffic, and detecting anomalies in real time. Fortinet’s firewall systems incorporate these capabilities while maintaining high throughput performance, making them suitable for enterprise-scale deployments.
The evolution from rule-based filtering to intelligent inspection marks a significant shift in cybersecurity strategy. It reflects the growing need for systems that can adapt automatically to new threats without requiring constant manual updates.
Fortinet’s Role in Network Infrastructure Protection
Fortinet’s technology is designed to secure not just the perimeter of a network but the entire infrastructure. This includes internal network segments, remote access points, wireless connections, and cloud environments. The idea is that threats can originate from multiple sources, not just external attackers. Insider threats, compromised devices, and misconfigured systems can also create vulnerabilities.
To address this, Fortinet integrates multiple security layers into a single framework. Firewalls act as the primary inspection point, but additional systems monitor internal traffic, user behavior, and application activity. This layered approach ensures that threats are identified even if they bypass initial defenses.
Wireless and Network Expansion in Security Design
As organizations expanded their use of wireless technologies, new security challenges emerged. Wireless networks introduced additional entry points that could potentially be exploited by attackers. Devices connecting through Wi-Fi or cellular networks can bypass traditional wired security controls if not properly managed.
Fortinet addressed this challenge by extending its security model to include wireless access management. This allows organizations to apply consistent security policies across both wired and wireless environments. By integrating wireless control into the broader security ecosystem, Fortinet ensures that all network access points are governed under the same security framework.
Integration of Cloud Environments in Modern Security Architecture
Modern IT environments increasingly rely on cloud infrastructure for storage, processing, and application hosting. This shift has created new challenges in maintaining consistent security across hybrid environments. Fortinet integrates cloud security capabilities that allow organizations to extend their protection policies beyond physical networks.
Cloud integration enables visibility into workloads running across different cloud providers and ensures that security policies remain consistent regardless of where data is stored or processed. This unified approach helps reduce security gaps that often occur when organizations use multiple cloud platforms independently.
Importance of Centralized Security Management
Centralized management is a key concept in modern cybersecurity architecture. Instead of managing multiple security tools separately, centralized systems provide a unified dashboard for monitoring and controlling all security operations. Fortinet’s ecosystem is designed around this principle, allowing administrators to view network activity, detect threats, and enforce policies from a single control interface.
This centralization improves operational efficiency and reduces the complexity of managing large-scale networks. It also enhances response times during security incidents, as administrators can quickly identify and address issues without switching between multiple systems.
Data Flow and Security Intelligence Sharing
In modern cybersecurity systems, data flow between components is critical for effective threat detection. Security devices must be able to share information in real time to identify coordinated attacks or multi-stage intrusion attempts. Fortinet systems are designed to support bidirectional communication between different components of the security ecosystem.
This means that threat intelligence is not only collected but also distributed across the entire network infrastructure. When one device detects a suspicious activity, that information is shared with other components, enabling proactive defense mechanisms. This approach significantly improves detection accuracy and reduces response times.
Early Architectural Vision Behind Fortinet’s Design Philosophy
From the beginning, Fortinet adopted a strategic approach that emphasized control over the entire network environment rather than isolated security functions. This philosophy was based on the understanding that modern threats often exploit multiple entry points simultaneously. By designing a system where all security components are interconnected, Fortinet aimed to create a more resilient defense structure.
This architectural vision influenced the development of its entire product line, ensuring that each component contributes to a unified security strategy. The focus on integration rather than isolation remains a defining characteristic of Fortinet’s approach to cybersecurity.
The Foundation of Fortinet Security Fabric Architecture
Fortinet’s security model is built around a concept known as a unified security architecture, often referred to as a security fabric. This architecture is designed to connect multiple security functions into a coordinated system that shares intelligence and enforces policies across the entire digital environment. Instead of treating firewalls, endpoints, cloud workloads, and network devices as separate entities, the fabric approach links them into a single operational framework.
The purpose of this design is to eliminate gaps between different security layers. In traditional environments, each security tool operates independently, which can create blind spots where threats go undetected. The security fabric resolves this issue by ensuring that every component communicates with the others in real time. This creates a continuous flow of security intelligence that improves visibility and response accuracy across the entire infrastructure.
Interconnected Security Domains Across Modern Networks
Modern enterprise networks are no longer confined to a single physical location. They extend across branch offices, data centers, remote users, and cloud environments. Each of these domains introduces unique security challenges. The security fabric model addresses this complexity by extending consistent policies across all environments.
In this structure, network devices, endpoint systems, and cloud workloads are all part of a single security domain. This allows organizations to apply unified policies regardless of where the data resides or how it is accessed. The interconnected design ensures that a threat detected in one part of the network can trigger protective actions in another part without manual intervention.
Role of Centralized Intelligence in Threat Detection
Centralized intelligence plays a critical role in modern cybersecurity systems. Rather than relying on isolated detection mechanisms, Fortinet’s architecture aggregates data from multiple sources and analyzes it collectively. This includes network traffic patterns, application behavior, user activity, and endpoint telemetry.
By correlating this information, the system can identify complex attack patterns that might not be visible from a single data source. For example, a seemingly harmless login attempt combined with unusual data transfer activity can indicate a potential compromise. Centralized intelligence allows these patterns to be detected earlier in the attack lifecycle, improving the chances of preventing damage.
Deep Packet Inspection and Application Awareness
One of the core capabilities within advanced firewall systems is deep packet inspection. This process involves analyzing the contents of data packets beyond basic header information. Instead of only examining source and destination addresses, the system inspects the actual data payload to identify malicious content or unauthorized applications.
Application awareness extends this capability further by identifying applications regardless of the ports or protocols they use. This is important because modern applications often use dynamic ports or encrypted channels to bypass traditional security rules. By recognizing applications based on behavior and signatures, the system can enforce more precise security controls.
Intrusion Prevention and Behavioral Analysis
Intrusion prevention systems are integrated into modern security architectures to detect and block malicious activity in real time. These systems analyze network traffic for known attack signatures as well as abnormal behavior patterns. Unlike traditional detection methods that rely solely on known threats, behavioral analysis allows systems to identify previously unknown attacks.
This approach is particularly effective against zero-day vulnerabilities, where attackers exploit unknown weaknesses before patches are available. By monitoring deviations from normal network behavior, the system can detect suspicious activity and take immediate action to mitigate potential damage.
Identity-Based Security and Access Control Models
Modern cybersecurity frameworks increasingly rely on identity-based security rather than purely network-based controls. This means that access decisions are based on user identity, device posture, and contextual information rather than just IP addresses or network segments.
Identity-based security allows organizations to implement more granular access policies. For example, a user may be granted access to specific applications based on their role within the organization, the security status of their device, or their location. This approach aligns with zero trust principles, where no user or device is automatically trusted by default.
Zero Trust Principles in Integrated Security Systems
Zero trust architecture operates on the principle that threats can exist both inside and outside the network. As a result, every access request must be verified before permission is granted. This verification process includes authentication, authorization, and continuous monitoring.
Within an integrated security system, zero trust principles are enforced across all layers of the network. This ensures that even if an attacker gains initial access, their ability to move laterally within the network is restricted. Continuous validation of user identity and device security posture helps maintain a strong security perimeter that adapts dynamically to changing conditions.
Secure Connectivity and Encrypted Traffic Inspection
Encryption has become a standard method for protecting data in transit, but it also introduces challenges for security systems. Attackers often use encrypted channels to hide malicious activity, making it difficult for traditional security tools to detect threats.
Advanced security architectures address this challenge by implementing encrypted traffic inspection. This process involves decrypting, analyzing, and then re-encrypting data packets to ensure that threats are not hidden within secure channels. While this process requires additional processing power, it is essential for maintaining visibility in modern encrypted environments.
Hardware Acceleration and Performance Optimization
High-performance security systems rely on specialized hardware to process large volumes of network traffic efficiently. Custom processing units are designed to accelerate tasks such as packet inspection, encryption, and threat detection. This allows security systems to maintain high throughput without creating bottlenecks.
Hardware acceleration is particularly important in enterprise environments where network traffic can reach extremely high levels. Without dedicated processing capabilities, security inspection could significantly slow down network performance. By offloading critical tasks to specialized hardware, systems can maintain both security and speed.
Automation and Orchestration in Cybersecurity Operations
Automation plays a key role in modern cybersecurity strategies. As the volume of security events increases, manual response becomes inefficient and prone to delay. Automated systems can respond to threats in real time based on predefined policies and behavioral triggers.
Orchestration extends automation by coordinating multiple security tools to respond collectively to incidents. For example, when a threat is detected, the system may automatically isolate affected devices, update firewall rules, and alert administrators. This coordinated response reduces the time between detection and mitigation, limiting potential damage.
API-Driven Integration with External Systems
Modern security platforms are designed to integrate with external systems through application programming interfaces. This allows security tools to exchange data with other operational platforms, enabling a more connected IT environment. APIs enable real-time communication between security systems and infrastructure management tools.
This integration supports automated workflows, where security events can trigger actions in other systems. For example, a detected threat may automatically generate an incident record in an IT management system or trigger a response workflow in a security operations platform. This interconnected approach improves efficiency and reduces response time.
Security Information and Event Correlation
Security systems generate large volumes of data from multiple sources, including network logs, endpoint activity, and application events. Correlating this data is essential for identifying meaningful security incidents. Without correlation, individual events may appear harmless even when they are part of a larger attack pattern.
Advanced correlation engines analyze data across multiple dimensions to identify relationships between events. This helps security teams understand the full context of an attack, including its origin, progression, and impact. Correlation also reduces false positives by filtering out unrelated events.
Scalability in Distributed Enterprise Environments
As organizations grow, their network environments become more complex and distributed. Scalability is a critical requirement for security systems operating in such environments. Security architectures must be capable of handling increasing traffic volumes and expanding infrastructure without degradation in performance.
Distributed security models address this challenge by deploying security functions closer to the source of traffic. This reduces latency and improves efficiency by processing data at multiple points within the network rather than routing everything to a central location.
Multi-Layered Defense Strategy Across Infrastructure
A multi-layered defense strategy involves implementing security controls at different levels of the network stack. This includes perimeter security, internal segmentation, endpoint protection, and cloud security. Each layer provides a different type of protection, ensuring that if one layer is compromised, others remain active.
This layered approach is essential in modern cybersecurity because attackers often use multiple techniques to bypass defenses. By implementing overlapping security measures, organizations reduce the likelihood of successful intrusion and increase detection capabilities.
Telemetry and Continuous Monitoring Systems
Continuous monitoring is a critical component of modern security operations. Telemetry data provides real-time insights into network behavior, system performance, and security events. This data is continuously collected and analyzed to detect anomalies and maintain operational awareness.
Telemetry systems enable proactive security management by identifying potential issues before they escalate into full-scale incidents. This allows organizations to respond quickly and maintain system integrity under dynamic conditions.
Adaptive Security in Dynamic Network Environments
Modern networks are highly dynamic, with frequent changes in user access, application deployment, and infrastructure configuration. Adaptive security systems are designed to respond to these changes automatically. Instead of relying on static rules, they adjust security policies based on real-time conditions.
This adaptability is essential for maintaining consistent protection in environments where traditional static configurations are no longer sufficient. By continuously adjusting to network behavior, adaptive systems provide more resilient security coverage across changing environments.
Expansion of Fortinet Beyond Traditional Network Security
As enterprise environments evolved, Fortinet expanded its scope far beyond traditional perimeter firewalling. The modern digital landscape includes hybrid infrastructures, remote workforce connectivity, cloud-native applications, and distributed endpoints. In response to this complexity, Fortinet developed a broader ecosystem that integrates multiple layers of cybersecurity into a single operational framework.
This expansion reflects a shift in cybersecurity strategy from isolated defense tools to interconnected security systems. Instead of focusing solely on network borders, the architecture now addresses identity, application behavior, cloud workloads, and endpoint protection as part of a unified security model. The objective is to ensure consistent protection regardless of where data is accessed or processed.
Fortinet Security Fabric in Distributed Enterprise Environments
The security fabric concept becomes even more critical in distributed environments where infrastructure spans multiple geographical regions and cloud providers. In such setups, maintaining visibility and control is a major challenge. The security fabric addresses this by creating a synchronized environment where all security components share telemetry data and policy enforcement logic.
This structure allows organizations to maintain centralized governance while still supporting decentralized operations. Security policies can be applied globally, yet enforced locally at the network edge, in branch offices, or within cloud workloads. This reduces configuration inconsistencies and ensures that security posture remains uniform across the entire enterprise ecosystem.
Integration of Cloud-Native Security Mechanisms
Cloud adoption has fundamentally changed how security must be implemented. Traditional perimeter-based models are no longer sufficient in environments where workloads move dynamically between providers and regions. Fortinet’s architecture incorporates cloud-native security mechanisms that extend protection into virtualized environments.
These mechanisms include workload monitoring, container security, and cloud configuration analysis. Instead of treating cloud environments as separate domains, they are integrated into the broader security fabric. This enables continuous monitoring of cloud assets and ensures that misconfigurations or vulnerabilities are detected in real time.
Multi-Cloud Visibility and Unified Security Control
Organizations often operate across multiple cloud providers, creating fragmented visibility if each environment is managed separately. Unified security control addresses this issue by consolidating monitoring and policy enforcement into a single interface. This allows security teams to view all cloud assets, regardless of provider, from a centralized platform.
This unified visibility is essential for detecting cross-environment threats, such as attacks that begin in one cloud environment and move laterally into another. By correlating events across multiple cloud infrastructures, security systems can identify complex attack patterns that would otherwise remain undetected.
Secure SD-WAN and Intelligent Traffic Routing
Software-defined wide area networking introduces a more flexible approach to managing enterprise connectivity. Instead of relying on traditional static routing methods, SD-WAN dynamically selects optimal paths for network traffic based on performance, cost, and security requirements.
When integrated with security systems, SD-WAN becomes more than a connectivity solution. It becomes a security-aware routing mechanism that ensures traffic is inspected and protected as it moves across distributed networks. This integration allows organizations to enforce consistent security policies across branch offices and remote locations.
Intelligent routing also improves performance by directing traffic through the most efficient paths while maintaining security inspection at key points. This balance between speed and protection is essential for modern enterprise operations.
Endpoint Security and Device-Level Protection
Endpoints represent one of the most vulnerable components of any network. Devices such as laptops, mobile phones, and IoT systems often operate outside traditional network boundaries, making them attractive targets for attackers. Endpoint security focuses on protecting these devices from malware, unauthorized access, and data breaches.
Within an integrated security ecosystem, endpoint protection is not isolated. It communicates with network security systems to provide real-time device status information. If a device is compromised, the system can automatically restrict its access to critical resources or isolate it from the network entirely.
This integration ensures that security decisions are based on both network activity and device integrity, creating a more comprehensive defense strategy.
Threat Intelligence Sharing Across Security Layers
Threat intelligence is a critical component of modern cybersecurity operations. It involves collecting, analyzing, and distributing information about known and emerging threats. Within an integrated ecosystem, threat intelligence is shared across all security layers, including firewalls, endpoints, cloud systems, and applications.
This shared intelligence allows systems to respond more quickly to emerging threats. For example, if a malicious IP address is identified in one part of the network, that information can be immediately distributed to other security components. This prevents repeated exposure to known threats and strengthens overall defense capabilities.
Security Automation in Incident Response Workflows
Incident response has become increasingly complex due to the volume and sophistication of modern cyberattacks. Manual response processes are often too slow to effectively mitigate fast-moving threats. Automation addresses this challenge by enabling predefined response actions that are triggered automatically when specific conditions are met.
These automated workflows can include actions such as isolating affected devices, blocking malicious traffic, or initiating forensic data collection. By reducing the time between detection and response, automation minimizes the potential impact of security incidents.
In advanced environments, automated response systems are integrated with orchestration platforms that coordinate actions across multiple security tools. This ensures a synchronized response that addresses threats from multiple angles simultaneously.
Role of Artificial Intelligence in Threat Detection
Artificial intelligence has become an essential component of modern cybersecurity systems. AI-driven analysis allows security platforms to identify patterns and anomalies that would be difficult to detect using traditional rule-based methods. Machine learning algorithms continuously analyze network behavior to establish baselines and detect deviations.
This capability is particularly useful for identifying unknown or emerging threats that do not match existing signatures. AI systems can also reduce false positives by distinguishing between normal variations in behavior and actual malicious activity. Over time, these systems become more accurate as they learn from historical data.
Behavioral Analytics for Advanced Threat Identification
Behavioral analytics focuses on understanding how users, devices, and applications typically behave within a network. By establishing a baseline of normal activity, the system can detect unusual behavior that may indicate a security threat.
For example, if a user account suddenly begins accessing large volumes of sensitive data or logging in from unusual locations, the system may flag this as suspicious. Behavioral analytics is particularly effective against insider threats and compromised credentials, where attackers attempt to mimic legitimate user behavior.
Zero Trust Enforcement Across Hybrid Infrastructure
Zero trust principles are increasingly implemented across hybrid environments that include both on-premises and cloud infrastructure. In this model, every access request is treated as potentially hostile until verified. Continuous authentication and authorization checks ensure that access is granted only under appropriate conditions.
Within a hybrid infrastructure, zero trust enforcement requires consistent identity verification across all environments. This includes verifying users, devices, and applications before granting access to resources. Continuous monitoring ensures that access privileges are adjusted dynamically based on real-time risk assessments.
Role-Based Access Control and Identity Segmentation
Role-based access control is a fundamental security mechanism that restricts system access based on user roles within an organization. Instead of granting broad access rights, permissions are assigned based on job responsibilities. This minimizes the risk of unauthorized access to sensitive systems.
Identity segmentation further enhances this model by dividing users and devices into distinct security zones. Each segment has its own set of access rules and monitoring policies. This reduces the attack surface and limits lateral movement within the network.
Advanced Logging and Security Telemetry Analysis
Security telemetry involves collecting detailed logs from various components of the IT infrastructure. These logs provide insights into system behavior, network activity, and potential security incidents. Advanced analysis tools process this data to identify patterns and correlations that indicate malicious activity.
Effective telemetry systems operate in real time, allowing security teams to respond quickly to emerging threats. They also support forensic investigations by providing detailed historical records of system activity.
Micro-Segmentation in Modern Network Architecture
Micro-segmentation involves dividing a network into smaller, isolated segments to limit the spread of potential attacks. Each segment operates under its own security policies, reducing the risk of lateral movement by attackers.
In modern architectures, micro-segmentation is implemented dynamically based on workload behavior and security requirements. This ensures that even if one segment is compromised, the impact is contained within a limited area of the network.
High-Performance Security Processing at Scale
As network traffic volumes continue to increase, security systems must be capable of processing large amounts of data without introducing latency. High-performance processing architectures are designed to handle deep inspection, encryption, and analysis at scale.
This performance is achieved through a combination of hardware acceleration, distributed processing, and optimized software design. These elements work together to ensure that security enforcement does not become a bottleneck in high-speed network environments.
Continuous Evolution of Enterprise Cyber Defense Models
Cybersecurity is not a static discipline. Threat landscapes evolve continuously, requiring security architectures to adapt over time. Modern enterprise defense models are designed to be flexible, allowing new capabilities to be integrated as threats evolve.
This continuous evolution ensures that security systems remain effective against emerging attack techniques. It also enables organizations to adopt new technologies without compromising existing security controls.
Integrated Visibility Across Security Domains
Unified visibility is essential for effective cybersecurity management. Without a consolidated view of all security domains, organizations may struggle to detect complex attacks that span multiple systems. Integrated visibility provides a holistic view of network activity, enabling better decision-making and faster incident response.
This visibility extends across endpoints, cloud environments, network traffic, and application behavior, ensuring that no part of the infrastructure operates in isolation from the security framework.
Conclusion
The evolution of Fortinet as a cybersecurity ecosystem reflects a broader transformation in how modern digital infrastructure is designed, protected, and managed. What began primarily as a firewall-centric solution has expanded into a multi-layered security architecture that integrates network protection, cloud security, endpoint defense, and intelligent automation. This shift is not simply about adding more tools; it represents a fundamental change in how organizations approach cybersecurity at scale. Instead of treating security as a perimeter-bound function, it is now embedded into every layer of the digital environment, forming a continuous and interconnected defense structure.
At the core of this transformation is the idea that cybersecurity can no longer rely on isolated mechanisms. Traditional models that depended on static rules, manual configuration, and perimeter defenses are no longer sufficient in a landscape defined by cloud adoption, remote workforces, and constantly evolving attack vectors. Fortinet’s architecture addresses this challenge by creating a unified system where all components communicate and collaborate. This interconnected approach allows security intelligence to flow seamlessly across different domains, improving visibility and reducing response times during potential incidents.
One of the most significant outcomes of this model is the reduction of security blind spots. In fragmented environments, attackers often exploit gaps between disconnected systems, moving laterally without detection. By contrast, an integrated security fabric ensures that events detected in one area are immediately visible across the entire infrastructure. This interconnected awareness makes it more difficult for threats to remain hidden and increases the likelihood of early detection before damage escalates.
Another key development is the shift toward intelligence-driven security operations. Instead of relying solely on predefined rules, modern systems analyze behavior, patterns, and contextual signals to identify anomalies. This behavioral approach allows security platforms to detect unknown threats that do not match existing signatures. As cyberattacks become more sophisticated and adaptive, this ability to interpret behavior rather than just match known patterns becomes essential for maintaining effective defense.
The expansion of cybersecurity into cloud environments has also reshaped how protection strategies are implemented. Cloud infrastructure introduces dynamic workloads, distributed resources, and shared responsibility models that differ significantly from traditional on-premises systems. A unified security architecture ensures that protection mechanisms extend consistently across both cloud and physical environments. This continuity is critical for maintaining control over data, applications, and user access regardless of where resources are deployed.
In addition to cloud integration, the rise of automation has significantly changed the operational landscape of cybersecurity. Security teams now manage vast volumes of alerts, logs, and telemetry data that cannot be handled manually at scale. Automation enables systems to respond to threats in real time based on predefined policies and adaptive intelligence. This reduces response delays and minimizes the impact of security incidents by initiating containment actions immediately when suspicious activity is detected.
Closely related to automation is the increasing role of orchestration in security operations. While automation handles individual tasks, orchestration coordinates multiple actions across different systems to ensure a unified response. This coordination is essential in complex environments where a single security event may require simultaneous actions such as isolating endpoints, updating firewall rules, and triggering alerts in monitoring platforms. The ability to manage these processes cohesively strengthens overall resilience against coordinated attacks.
Identity and access management have also become central to modern cybersecurity frameworks. Instead of focusing solely on network boundaries, security decisions are now based on identity, context, and behavior. This approach ensures that access is continuously verified rather than assumed to be safe after initial authentication. By enforcing identity-based controls across all environments, organizations reduce the risk of unauthorized access and limit the potential impact of compromised credentials.
Another important aspect of modern security architecture is the use of telemetry and continuous monitoring. Security systems generate large volumes of data that provide insight into network behavior, user activity, and system performance. When analyzed effectively, this data enables organizations to detect subtle indicators of compromise that might otherwise go unnoticed. Continuous monitoring ensures that security posture is not static but constantly evaluated and adjusted based on real-time conditions.
Scalability remains a defining requirement for any enterprise security system. As organizations grow and adopt new technologies, their infrastructure becomes increasingly distributed and complex. A scalable security architecture ensures that protection mechanisms can expand alongside the organization without degradation in performance or visibility. This is achieved through distributed processing, modular design, and optimized resource utilization that allows security functions to operate efficiently at large scale.
Ultimately, the broader significance of Fortinet’s approach lies in its alignment with the realities of modern digital ecosystems. Cybersecurity is no longer a standalone function but an integrated component of every digital interaction. Networks are no longer confined to physical boundaries, and threats are no longer limited to external actors. They can emerge from within systems, across cloud platforms, or through compromised endpoints. Addressing this complexity requires a security model that is equally adaptive, interconnected, and intelligent.
The continued evolution of integrated cybersecurity systems demonstrates that protection strategies must evolve in parallel with technological advancement. As digital environments become more dynamic, security must shift from reactive defense to proactive intelligence-driven prevention. The emphasis is no longer solely on blocking attacks but on understanding behavior, predicting risks, and responding in real time across a unified ecosystem.
In this context, Fortinet represents a broader industry shift toward convergence, where networking and security are no longer separate disciplines but interconnected components of a single architecture. This convergence enables organizations to build more resilient infrastructures capable of adapting to emerging threats while maintaining operational efficiency. It also highlights the importance of continuous innovation in cybersecurity, as adversaries themselves continue to evolve their methods and techniques.
As digital transformation accelerates across industries, the demand for integrated, intelligent, and scalable security solutions will continue to grow. Systems that can unify visibility, automate response, and adapt to changing conditions will play a central role in shaping the future of enterprise cybersecurity.