Virtual Local Area Network, commonly referred to as VLAN, represents one of the foundational technologies in modern networking. It was introduced to solve a fundamental inefficiency in early local area networks where all devices shared the same broadcast domain. In such environments, network traffic was distributed to every connected device regardless of relevance, leading to congestion, inefficiency, and potential security concerns. VLAN technology addressed this issue by logically segmenting a physical network into multiple isolated broadcast domains.
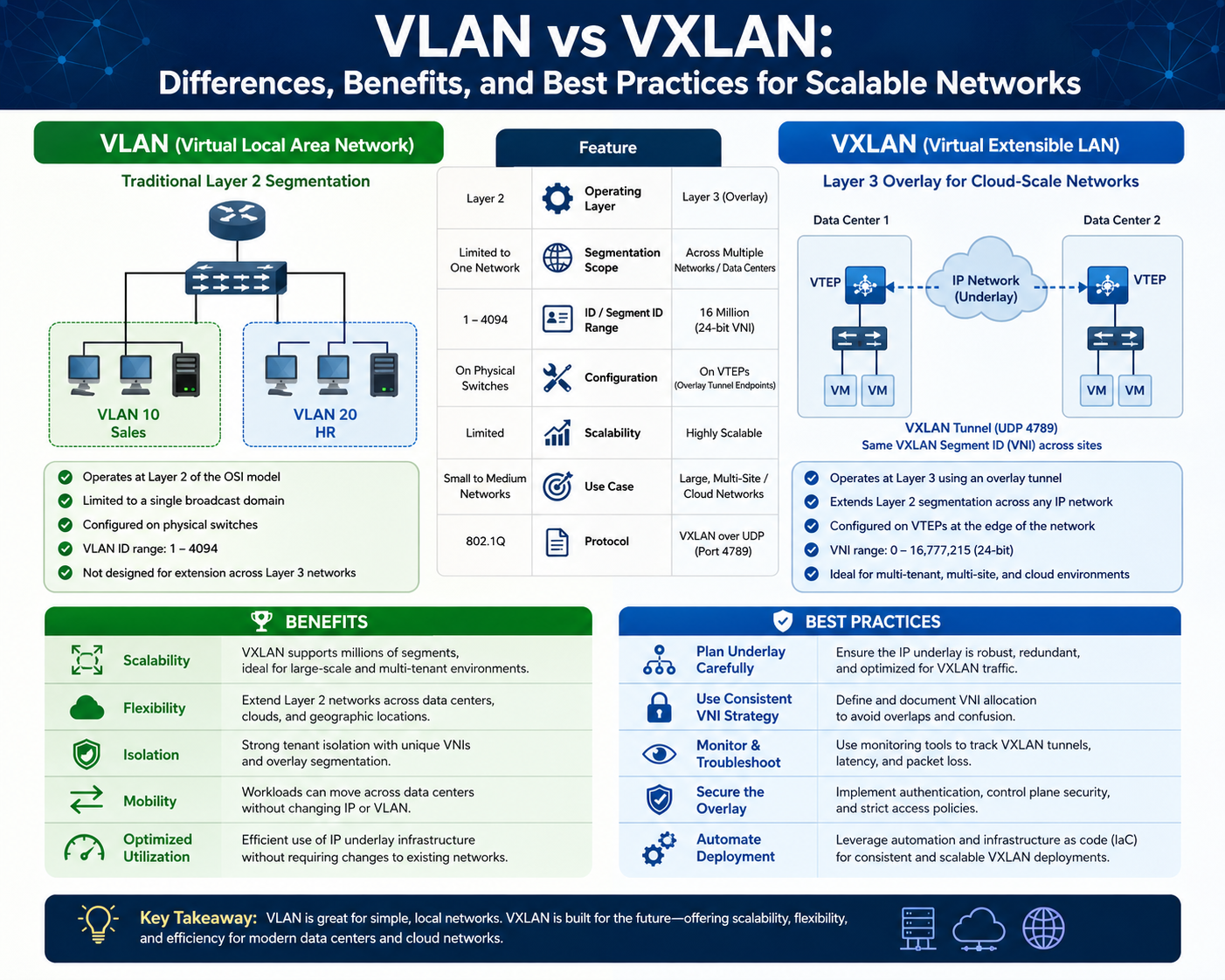
At its core, VLAN operates at Layer 2 of the OSI model and uses tagging mechanisms to differentiate traffic between segments. Each VLAN is assigned a unique identifier, allowing switches to forward frames only to the intended group of devices. This logical segmentation provides a level of isolation without requiring additional physical infrastructure, making VLANs both cost-effective and practical for a wide range of deployments.
In practical implementations, VLANs are configured on network switches, where ports are assigned to specific VLAN IDs. Devices connected to these ports become part of the corresponding VLAN, regardless of their physical location within the network. This abstraction allows administrators to group users based on function, department, or security requirements rather than physical proximity. For example, employees from finance and human resources can be placed in separate VLANs even if they sit next to each other in the same office space.
One of the most significant advantages of VLANs is improved network performance. By reducing broadcast domains, VLANs minimize unnecessary traffic, ensuring that devices only receive relevant data. This leads to better bandwidth utilization and overall network efficiency. Additionally, VLANs enhance security by isolating sensitive traffic. Devices in one VLAN cannot directly communicate with devices in another VLAN without routing through a Layer 3 device, such as a router or a multilayer switch.
However, VLANs are not without limitations. The VLAN identifier is a 12-bit field, which restricts the total number of VLANs to 4096. While this may seem sufficient for small to medium-sized networks, it becomes a constraint in large-scale environments such as data centers or cloud infrastructures. As organizations grow and require more granular segmentation, managing VLAN configurations can become increasingly complex.
Another limitation lies in VLAN mobility. Since VLANs are tied to the physical network infrastructure, extending them across multiple locations or data centers can be challenging. This often requires complex configurations involving trunk links, spanning tree protocols, and careful planning to avoid loops and inefficiencies. As a result, VLANs are best suited for relatively static environments where network topology does not change frequently.
Despite these challenges, VLANs remain widely used due to their simplicity and effectiveness. They are particularly valuable in enterprise networks, campus environments, and small to medium-sized businesses where segmentation needs are moderate, and infrastructure remains relatively stable. VLANs provide a reliable way to organize network resources, enforce policies, and maintain control over traffic flow.
Understanding VLANs also involves familiarity with tagging protocols, most notably IEEE 802.1Q. This standard defines how VLAN information is embedded into Ethernet frames, allowing switches to identify and handle traffic appropriately. Tagged frames carry VLAN identifiers, enabling them to traverse trunk links between switches while preserving segmentation. Untagged frames, on the other hand, are associated with a default VLAN, often referred to as the native VLAN.
Trunking plays a crucial role in VLAN deployment. Trunk ports allow multiple VLANs to pass through a single physical link between switches, reducing the need for multiple cables and simplifying network design. This capability is essential for scaling VLAN-based networks, as it enables efficient communication across different segments while maintaining isolation.
Inter-VLAN communication is another important aspect. Since VLANs are isolated at Layer 2, communication between them requires routing at Layer 3. This is typically achieved באמצעות routers or multilayer switches that can perform routing functions. Inter-VLAN routing introduces additional considerations, such as access control and traffic filtering, which can be used to enforce security policies and regulate data flow between segments.
As networks evolve, the role of VLANs continues to be relevant, but their limitations become more apparent in dynamic and large-scale environments. The need for greater scalability, flexibility, and mobility has led to the development of more advanced technologies that build upon the principles of VLANs while addressing their shortcomings. This transition marks the beginning of a shift toward network virtualization, where logical networks are decoupled from physical infrastructure.
Limitations of VLAN in Modern Network Architectures
While VLAN technology has served as a cornerstone of network segmentation for decades, its design inherently reflects the needs of earlier network environments. As modern infrastructures demand higher scalability, automation, and flexibility, VLANs begin to show constraints that can hinder performance and growth.
One of the primary challenges associated with VLANs is scalability. The 4096 VLAN limit, derived from the 12-bit VLAN ID field, becomes restrictive in large environments. In data centers that host thousands of tenants or applications, this limitation can quickly be reached. Organizations requiring extensive segmentation for security or operational purposes may find themselves constrained by this ceiling, forcing them to adopt workarounds that add complexity.
Another significant issue is the dependency on physical topology. VLAN configurations are closely tied to the underlying network infrastructure, which means that any changes in topology require manual reconfiguration. This lack of abstraction makes VLANs less suitable for environments where workloads are dynamic and frequently move across different locations. For example, virtual machine migration across data centers becomes complicated when VLAN boundaries must be maintained.
The management overhead associated with VLANs also increases as networks grow. Administrators must configure VLAN IDs, assign ports, manage trunk links, and ensure consistency across multiple switches. In large deployments, this can become time-consuming and prone to errors. Misconfigurations can lead to connectivity issues, security vulnerabilities, or inefficient traffic routing.
Broadcast traffic, although reduced compared to flat networks, still exists within each VLAN. As the number of devices in a VLAN increases, broadcast traffic can accumulate, impacting performance. This is particularly problematic in environments where large numbers of devices are grouped into the same VLAN for operational reasons.
VLANs also face challenges in multi-tenant environments. Isolation between tenants is limited, and ensuring strict separation requires careful configuration and monitoring. In scenarios where security is critical, such as cloud services, VLANs alone may not provide the level of isolation required.
Another limitation is the complexity of extending VLANs across geographically dispersed locations. Technologies such as VLAN trunking and tunneling can be used to stretch VLANs, but these approaches often introduce additional latency, complexity, and potential points of failure. Maintaining consistent configurations across multiple sites becomes increasingly difficult as the network expands.
The reliance on spanning tree protocols to prevent loops in VLAN-based networks introduces additional inefficiencies. Spanning tree can block redundant paths to avoid loops, which means that available bandwidth is not fully utilized. This can lead to suboptimal performance, especially in environments that require high availability and redundancy.
Security within VLANs is also not absolute. While VLANs provide logical separation, they are not inherently secure against certain types of attacks, such as VLAN hopping. Additional security measures, such as access control lists and proper configuration practices, are necessary to mitigate these risks.
As organizations adopt virtualization and cloud computing, the limitations of VLANs become more pronounced. Modern applications require networks that can scale rapidly, adapt to changing workloads, and provide consistent connectivity across diverse environments. VLANs, with their static and infrastructure-dependent nature, struggle to meet these demands.
These challenges have driven the development of more advanced network virtualization technologies that address the shortcomings of VLANs while preserving their core benefits. The need for greater scalability, flexibility, and abstraction has led to innovations that redefine how networks are designed and managed.
Introduction to VXLAN and Overlay Networking Concepts
Virtual Extensible LAN (VXLAN) emerges as a response to the limitations of traditional VLANs. It represents a shift from physical network segmentation to virtualized overlay networks that operate independently of the underlying infrastructure. VXLAN is designed to provide scalable and flexible network virtualization, making it well-suited for modern data centers and cloud environments.
VXLAN operates by encapsulating Layer 2 frames into Layer 3 packets using User Datagram Protocol (UDP). This encapsulation allows Layer 2 networks to be extended across Layer 3 boundaries, enabling seamless communication between devices regardless of their physical location. The concept of overlay networking is central to VXLAN, where logical networks are built on top of existing physical networks without requiring changes to the underlying infrastructure.
One of the defining features of VXLAN is its use of a 24-bit segment identifier, known as the VXLAN Network Identifier (VNI). This significantly expands the number of available segments to approximately 16 million, compared to the limited scale of VLANs. This scalability makes VXLAN ideal for large-scale environments where thousands of isolated networks may be required.
The encapsulation process in VXLAN involves wrapping an original Ethernet frame inside a UDP packet, which is then transmitted across the IP network. At the receiving end, the packet is decapsulated, and the original frame is delivered to the destination device. This process enables seamless Layer 2 connectivity across Layer 3 networks, effectively bridging the gap between traditional networking and modern virtualization requirements.
VXLAN introduces the concept of Virtual Tunnel Endpoints (VTEPs), which are responsible for encapsulating and decapsulating traffic. These endpoints can be implemented in network devices such as switches or in software within hypervisors. This flexibility allows VXLAN to integrate seamlessly with virtualized environments, where virtual machines can communicate as if they were on the same local network.
Another key advantage of VXLAN is its ability to support multi-tenant architectures. Each tenant can be assigned a unique VXLAN segment, ensuring complete isolation between different environments. This is particularly important in cloud computing, where multiple customers share the same physical infrastructure while maintaining strict separation of their data and applications.
VXLAN also enhances network mobility. Since overlay networks are decoupled from the physical infrastructure, workloads can move freely across different locations without requiring changes to network configurations. This capability is essential for modern applications that rely on dynamic scaling and high availability.
The use of IP-based transport in VXLAN enables better utilization of network resources. Unlike traditional VLANs that rely on spanning tree protocols, VXLAN can leverage advanced routing techniques to optimize traffic flow and utilize all available paths. This results in improved performance and reduced latency.
Despite its advantages, VXLAN introduces additional complexity compared to VLANs. The encapsulation process adds overhead, and proper configuration of tunnel endpoints and control planes is required. However, these challenges are often outweighed by the benefits of scalability and flexibility, especially in large-scale deployments.
VXLAN is often used in conjunction with control plane technologies that simplify management and improve efficiency. These mechanisms help automate the creation and maintenance of overlay networks, reducing the operational burden on administrators.
As networking continues to evolve, VXLAN represents a significant step forward in addressing the limitations of traditional segmentation methods. It provides a foundation for building modern, scalable, and flexible networks that can support the demands of contemporary applications and services.
VXLAN Architecture and How Overlay Networking Works in Practice
VXLAN represents a shift from physical-centric networking to a model where logical networks are built independently of underlying hardware. This architectural change is primarily achieved through overlay networking, where virtual networks are created on top of an existing IP-based infrastructure. Instead of relying on traditional Layer 2 adjacency, VXLAN extends Layer 2 communication across Layer 3 boundaries, enabling large-scale, distributed network designs.
At the center of VXLAN architecture is the concept of encapsulation and decapsulation. When a device inside a VXLAN segment sends traffic, the original Ethernet frame is encapsulated inside a UDP packet. This encapsulated packet is then transmitted across an IP network to a remote endpoint. Once it reaches its destination, the packet is decapsulated, and the original Ethernet frame is delivered to the target device. This process effectively creates a virtual tunnel between endpoints, allowing Layer 2 connectivity over Layer 3 infrastructure.
The devices responsible for handling this encapsulation process are known as VXLAN Tunnel Endpoints. These endpoints can exist in hardware switches, software-based hypervisors, or virtual networking appliances. Their role is to maintain VXLAN segment integrity by ensuring that traffic is properly encapsulated before leaving the source network and correctly restored at the destination.
Each VXLAN segment is identified by a VXLAN Network Identifier, which is a 24-bit value. This identifier allows for a significantly larger number of isolated networks compared to traditional VLANs. While VLANs are restricted to a few thousand segments, VXLAN expands this space into millions, making it suitable for large-scale cloud infrastructures and multi-tenant environments.
The use of an IP underlay network is a critical component of VXLAN design. Unlike traditional Layer 2 networks that rely heavily on switching domains, VXLAN uses standard IP routing to transport encapsulated traffic. This allows network designers to take advantage of existing routing protocols, load balancing techniques, and redundancy mechanisms already established in Layer 3 networks.
In practical implementations, VXLAN architectures are often built using a leaf-spine topology. In this design, leaf switches connect directly to endpoints, while spine switches provide high-speed interconnection between leaf nodes. VXLAN traffic flows through this fabric using IP routing, ensuring predictable latency and high bandwidth utilization. This structure eliminates the need for spanning tree protocols, which are commonly used in traditional Layer 2 networks to prevent loops.
Another important aspect of VXLAN architecture is the separation of data plane and control plane functions. The data plane handles the actual forwarding of encapsulated packets, while the control plane is responsible for distributing network information such as endpoint location and segment membership. This separation allows for more scalable and efficient network management.
In environments without a dedicated control plane, VXLAN can rely on multicast flooding for traffic discovery. However, modern deployments often use more advanced control mechanisms to reduce overhead and improve efficiency. These mechanisms allow endpoints to dynamically learn the location of other devices within the same VXLAN segment without relying on broadcast traffic.
VXLAN also introduces the concept of distributed routing, where routing decisions are made closer to the source of traffic. This reduces latency and improves overall network performance by avoiding unnecessary traffic traversal through centralized routing points. It also enhances scalability by distributing workload across multiple devices.
From an operational perspective, VXLAN simplifies network design in large environments by abstracting physical topology. Network administrators can define logical segments without worrying about the underlying physical layout. This abstraction enables greater flexibility in workload placement and movement, which is particularly important in cloud and virtualization environments.
Despite its advantages, VXLAN architecture introduces additional complexity in terms of configuration and troubleshooting. Engineers must understand encapsulation behavior, tunnel endpoint configuration, and overlay-underlay interaction. However, this complexity is often offset by the scalability and flexibility benefits it provides.
Scalability Differences Between VLAN and VXLAN in Large Networks
Scalability is one of the most significant differences between VLAN and VXLAN, and it is often the primary reason organizations transition from traditional segmentation models to overlay-based architectures. VLAN technology, while effective in smaller environments, is fundamentally constrained by its design limitations.
The VLAN identifier space is limited to 12 bits, which allows for a maximum of 4096 unique VLANs. In real-world deployments, this number is often even lower due to reserved VLAN IDs and operational best practices. As organizations grow and require more granular segmentation for applications, departments, and security zones, this limitation becomes increasingly restrictive.
In contrast, VXLAN uses a 24-bit identifier space, enabling approximately 16 million unique segments. This dramatic increase in scale allows network architects to design highly segmented environments without worrying about exhausting available identifiers. In large data centers, this capability is essential for supporting multi-tenant architectures, where each tenant may require multiple isolated networks.
Scalability in VLAN-based networks is also limited by the reliance on spanning tree protocols. As the number of switches and links increases, spanning tree complexity grows, and convergence times can become slower. Additionally, spanning tree often blocks redundant paths to prevent loops, which reduces overall network efficiency and limits scalability in high-density environments.
VXLAN eliminates the dependency on the spanning tree by operating over Layer 3 networks. Since routing protocols inherently support loop-free topologies, VXLAN can utilize all available paths in the network simultaneously. This enables better bandwidth utilization and more predictable performance as the network scales.
Another scalability challenge in VLAN environments is broadcast traffic. VLANs rely on broadcast domains, and as the number of devices within a VLAN increases, broadcast traffic can consume significant network resources. This becomes particularly problematic in large deployments where broadcast storms or excessive ARP traffic can degrade performance.
VXLAN addresses this issue by reducing reliance on broadcast traffic through more efficient control mechanisms. Instead of flooding the network with broadcast frames, VXLAN can use centralized or distributed control systems to map endpoints and distribute reachability information. This reduces unnecessary traffic and improves scalability in large environments.
Operational scalability is also an important consideration. Managing VLANs across multiple switches requires consistent configuration of VLAN IDs, trunk ports, and access policies. As the network grows, maintaining this consistency becomes increasingly difficult and error-prone.
VXLAN abstracts much of this complexity by decoupling logical networks from physical infrastructure. Network administrators can define virtual segments independently of the underlying hardware, reducing the operational burden associated with large-scale network management. This abstraction enables faster provisioning and more efficient network automation.
In cloud environments, scalability requirements extend beyond simple segmentation. Workloads must be able to move dynamically across physical hosts and even across data centers. VLANs struggle in this area due to their dependence on physical Layer 2 adjacency. VXLAN, on the other hand, supports workload mobility by maintaining a consistent logical network identity regardless of physical location.
This capability is particularly important in environments that use virtualization technologies, where virtual machines or containers may be frequently migrated for load balancing, maintenance, or disaster recovery. VXLAN ensures that network connectivity remains intact during these transitions without requiring manual reconfiguration.
Scalability also extends to geographic distribution. VLANs are typically confined to a single data center or campus environment due to their reliance on Layer 2 connectivity. Extending VLANs across wide area networks introduces complexity and performance challenges.
VXLAN, being IP-based, naturally supports geographically distributed architectures. Encapsulated traffic can traverse wide area networks without requiring direct Layer 2 connectivity between sites. This makes VXLAN well-suited for global cloud infrastructures and multi-site deployments.
Encapsulation Mechanisms and Traffic Flow Behavior in VXLAN Networks
Encapsulation is the defining technical mechanism that distinguishes VXLAN from traditional VLAN-based networking. It is the process that enables Layer 2 communication to occur across Layer 3 networks, fundamentally changing how traffic is transported and managed.
In a VXLAN environment, when a device sends a data frame, the frame is first received by a VXLAN Tunnel Endpoint. This endpoint encapsulates the original Ethernet frame inside a UDP packet. The UDP header includes information such as source and destination ports, while the VXLAN header contains the VXLAN Network Identifier, which identifies the virtual segment.
Once encapsulated, the packet is forwarded through the IP underlay network using standard routing protocols. Intermediate routers and switches treat the packet as regular IP traffic, unaware of the underlying VXLAN structure. This transparency is what allows VXLAN to extend Layer 2 networks across Layer 3 boundaries.
When the encapsulated packet reaches the destination VXLAN Tunnel Endpoint, the process is reversed. The outer UDP and IP headers are removed, revealing the original Ethernet frame. This frame is then forwarded to the appropriate destination device within the virtual network segment.
This encapsulation and decapsulation process introduces additional overhead compared to traditional VLAN tagging. However, it provides significant advantages in terms of scalability, flexibility, and network design simplicity.
Traffic flow in VXLAN networks is highly dependent on the underlying IP routing infrastructure. Unlike VLANs, where traffic is confined to a single broadcast domain, VXLAN traffic can take multiple paths through the network. This allows for load balancing and redundancy at the IP layer.
VXLAN also supports equal-cost multipath routing, which enables traffic to be distributed across multiple available paths. This improves bandwidth utilization and reduces congestion in large-scale networks.
Another important aspect of VXLAN traffic behavior is its ability to support distributed endpoints. Virtual machines or containers located on different physical hosts can communicate as if they were on the same local network, even if they are separated by multiple network hops.
The decoupling of logical and physical networks also simplifies traffic engineering. Network administrators can optimize routing paths independently of VLAN constraints, allowing for more efficient use of infrastructure resources.
Encapsulation does introduce some challenges, particularly in terms of maximum transmission unit size. Since VXLAN adds additional headers to each packet, the effective payload size is reduced unless the network is configured to support larger frame sizes. Proper configuration is necessary to avoid fragmentation and performance degradation.
Despite these considerations, encapsulation remains the key enabler of VXLAN’s scalability and flexibility advantages. It transforms traditional networking by allowing logical networks to exist independently of physical constraints, enabling modern cloud and data center architectures.
VXLAN Control Plane Models and Network Discovery Mechanisms
VXLAN is not only defined by its encapsulation method but also by how it handles control plane operations. The control plane determines how network endpoints are discovered, how reachability information is exchanged, and how VXLAN Tunnel Endpoints learn about each other within the overlay network. Unlike traditional VLAN environments, where flooding and learning are dominant mechanisms, VXLAN introduces more scalable approaches to managing network state.
In early VXLAN implementations, a flood-and-learn mechanism was commonly used. When a VXLAN Tunnel Endpoint did not know the location of a destination MAC address, it would flood the encapsulated frame across the VXLAN segment using multicast in the underlay network. Remote endpoints would then learn the source MAC addresses dynamically as traffic was received. While this approach is functional, it does not scale efficiently in large environments due to unnecessary replication of broadcast, unknown unicast, and multicast traffic.
As network environments grew in complexity, more advanced control plane solutions were introduced. One of the most widely adopted models integrates VXLAN with a centralized or distributed control system that advertises endpoint reachability information. In this model, instead of relying on flooding, VXLAN Tunnel Endpoints exchange information about MAC and IP address mappings through a structured control protocol. This significantly reduces unnecessary traffic and improves scalability.
A more modern approach combines VXLAN with Ethernet Virtual Private Network technology, which introduces a control plane that distributes endpoint information using a routing-like mechanism. In this model, endpoints advertise their presence and reachability through control messages, allowing other devices in the network to build a complete mapping table without relying on broadcast-based discovery. This method greatly improves efficiency in large-scale deployments and multi-tenant environments.
The separation of control plane and data plane in VXLAN architecture is a critical design improvement over traditional VLAN networks. In VLAN-based systems, learning and forwarding are tightly coupled with data traffic. In VXLAN, however, control information can be distributed independently, allowing for more intelligent and scalable network behavior.
Another important aspect of VXLAN control plane design is endpoint mobility. In dynamic environments such as virtualized data centers, workloads frequently move between physical hosts. The control plane ensures that when a workload migrates, its new location is immediately updated across the network. This prevents traffic blackholing and ensures continuous connectivity without manual intervention.
The efficiency of the VXLAN control plane directly impacts overall network performance. In poorly designed systems that rely heavily on flooding, network congestion can occur due to excessive control traffic. In contrast, optimized control plane implementations reduce overhead by ensuring that only necessary updates are propagated across the network.
Control plane scalability is particularly important in multi-tenant environments. Each tenant may have its own isolated VXLAN segments, and the control plane must manage endpoint information for potentially thousands of tenants simultaneously. Efficient data structures and hierarchical distribution models are often used to handle this complexity.
In modern architectures, the control plane also plays a role in policy enforcement. Network policies such as segmentation rules, security groups, and traffic filtering can be distributed alongside endpoint information. This allows for consistent policy enforcement across the entire overlay network, regardless of physical location.
VXLAN control plane design also supports automation and orchestration systems. In software-defined networking environments, network state is often managed programmatically. The control plane provides the necessary interfaces for these systems to dynamically create, modify, and remove network segments as needed.
Overall, the VXLAN control plane represents a shift from static, hardware-centric networking to dynamic, software-driven networking. This transition enables greater flexibility, scalability, and operational efficiency in modern infrastructures.
VXLAN vs VLAN in Security, Isolation, and Multi-Tenant Environments
Security and isolation are critical considerations in any network design, especially in environments that support multiple tenants or sensitive workloads. VLANs and VXLANs both provide segmentation capabilities, but they differ significantly in how isolation is achieved and maintained.
In VLAN-based networks, isolation is achieved by separating traffic into distinct broadcast domains. Devices within one VLAN cannot directly communicate with devices in another VLAN without routing through a Layer 3 device. This provides a basic level of security by limiting direct Layer 2 communication between segments.
However, VLAN isolation has inherent limitations. Since VLANs rely on shared physical infrastructure, misconfigurations or security vulnerabilities can potentially expose traffic between segments. Attacks such as VLAN hopping can exploit weaknesses in trunk configuration or tagging mechanisms to gain unauthorized access to other VLANs.
VXLAN improves isolation by introducing encapsulation and overlay networking. Each VXLAN segment is logically separated using a unique network identifier, and traffic is encapsulated before being transmitted across the physical network. This encapsulation ensures that even if multiple tenants share the same underlying infrastructure, their traffic remains logically isolated.
In multi-tenant environments, VXLAN provides stronger separation between tenants by assigning each tenant its own virtual network segment. This allows multiple organizations or applications to coexist on the same physical infrastructure without interfering with each other. The overlay model ensures that tenant boundaries are enforced at the logical level rather than relying solely on physical separation.
Security policies in VXLAN environments can be applied at the virtual network level. This allows administrators to define rules that control communication between different segments, enforce access restrictions, and monitor traffic flows. These policies can be consistently applied across distributed environments, ensuring uniform security enforcement.
Another advantage of VXLAN in terms of security is its ability to hide internal network topology. Since traffic is encapsulated, intermediate devices in the underlay network are unaware of the actual communication patterns within the overlay. This reduces exposure of the internal network structure and limits the attack surface.
VXLAN also supports integration with advanced security mechanisms such as micro-segmentation. In this approach, individual workloads can be isolated at a very granular level, allowing for strict control over communication between applications. This level of isolation is difficult to achieve with traditional VLAN-based designs due to scalability constraints.
In contrast, VLAN-based security models often rely on manual configuration and physical segmentation. As networks grow, maintaining consistent security policies across VLANs becomes increasingly complex. VXLAN simplifies this process by centralizing policy management within the overlay architecture.
Multi-tenant isolation is one of the strongest use cases for VXLAN. In cloud environments, where multiple customers share the same physical infrastructure, VXLAN ensures that each tenant’s traffic remains completely isolated. This is achieved through logical segmentation, encapsulation, and control plane separation.
From a compliance perspective, VXLAN also provides advantages by enabling consistent policy enforcement across distributed environments. Organizations can define security rules at the overlay level and ensure they are applied uniformly regardless of physical location.
While VLANs remain effective for basic segmentation and smaller environments, they lack the advanced isolation capabilities required for modern cloud-scale infrastructures. VXLAN addresses these gaps by providing a more robust and flexible security model.
Design Considerations and Real-World Deployment Strategies for VLAN and VXLAN
Choosing between VLAN and VXLAN is not simply a matter of technology preference but a design decision based on scale, architecture, and operational requirements. Each technology serves a different role in network design, and understanding how they fit into real-world deployments is essential for effective implementation.
In traditional enterprise environments, VLANs are often used to segment departments, user groups, or service types. Their simplicity makes them ideal for environments where network topology is relatively stable and does not require frequent changes. VLANs are easy to implement, require minimal overhead, and integrate well with existing switching infrastructure.
However, as organizations transition toward virtualization and cloud-based architectures, VLAN limitations become more apparent. Dynamic workloads, distributed applications, and multi-site deployments require a more flexible approach to segmentation. This is where VXLAN becomes a more suitable choice.
In data center environments, VXLAN is commonly used to build large-scale overlay networks that span multiple racks, clusters, or even geographic locations. The leaf-spine architecture is often used in conjunction with VXLAN to ensure high performance and predictable latency. In this model, leaf switches connect directly to endpoints, while spine switches provide high-speed interconnectivity between leaf nodes.
VXLAN enables seamless workload mobility within these environments. Virtual machines or containers can be moved between physical hosts without changing their network identity. This is particularly useful for load balancing, maintenance operations, and disaster recovery scenarios.
Another important design consideration is network convergence. VLAN-based networks often rely on spanning tree protocols, which can introduce delays during topology changes. VXLAN, operating over Layer 3 networks, benefits from faster convergence times provided by routing protocols. This improves overall network resilience and reduces downtime during failures or reconfigurations.
From an operational perspective, VXLAN introduces a higher level of abstraction compared to VLANs. While this improves scalability and flexibility, it also requires more advanced network management practices. Engineers must understand both the overlay and underlay networks to effectively troubleshoot issues.
In hybrid environments, VLAN and VXLAN often coexist. VLANs may be used within smaller segments or legacy systems, while VXLAN is used for large-scale virtualization and data center connectivity. In such designs, interoperability between VLAN and VXLAN domains is achieved through gateway devices that translate between the two technologies.
Performance optimization is another key consideration. VXLAN encapsulation introduces additional overhead, which can impact throughput if not properly managed. Network designers must ensure that the underlying infrastructure supports appropriate frame sizes and that routing paths are optimized for encapsulated traffic.
Automation plays an increasingly important role in VXLAN deployments. Modern networks often rely on software-defined networking principles to dynamically configure VXLAN segments, distribute control plane information, and enforce policies. This reduces manual configuration and improves consistency across large environments.
In contrast, VLAN environments typically rely more heavily on manual configuration and static network design. While this simplicity can be advantageous in smaller networks, it becomes a limitation at scale.
Ultimately, the choice between VLAN and VXLAN depends on the specific requirements of the environment. VLANs remain effective for simple segmentation and small-scale deployments, while VXLAN provides the scalability, flexibility, and abstraction required for modern distributed infrastructures.
Final Comparison and Strategic Perspective on VLAN vs VXLAN in Modern Networks
VLAN and VXLAN represent two distinct stages in the evolution of network segmentation and virtualization. VLAN is rooted in traditional Ethernet switching principles, designed for environments where physical topology is relatively static, and network scale is moderate. VXLAN, in contrast, is designed for modern distributed infrastructures where scalability, mobility, and multi-tenancy are primary requirements. Understanding their differences is not just a technical comparison but a reflection of how networking has shifted from hardware-centric design to software-defined architecture.
VLAN remains one of the most widely deployed technologies in enterprise networking due to its simplicity and reliability. Its ability to logically segment a physical network into isolated broadcast domains provides an effective mechanism for improving performance and security in controlled environments. For organizations with limited scale or stable infrastructure, VLAN continues to deliver sufficient functionality without introducing unnecessary complexity.
However, VLAN’s structural limitations become increasingly evident as network demands grow. The restriction of 4096 VLAN IDs places a hard ceiling on segmentation capacity. In environments where thousands of applications, tenants, or services must be isolated, this limitation becomes a bottleneck. Additionally, VLANs depend heavily on physical topology and Layer 2 adjacency, which restricts flexibility in dynamic environments where workloads frequently move across systems or data centers.
VXLAN addresses these constraints by introducing an overlay architecture that decouples logical networks from physical infrastructure. Through encapsulation, VXLAN allows Layer 2 communication to extend across Layer 3 networks, enabling seamless connectivity regardless of physical location. This abstraction fundamentally changes how networks are designed, shifting the focus from hardware configuration to logical network definition.
One of the most significant advantages of VXLAN is its scalability. With support for approximately 16 million unique segments, VXLAN eliminates the segmentation limitations inherent in VLAN-based designs. This expanded address space makes it suitable for large-scale cloud environments, multi-tenant infrastructures, and distributed data centers. It enables organizations to design highly granular network segmentation models without worrying about exhausting available identifiers.
Another critical advantage of VXLAN is its support for workload mobility. In modern virtualized environments, applications are no longer tied to specific physical machines or locations. Virtual machines and containers can be migrated across hosts or even across data centers. VXLAN preserves network identity during these migrations, ensuring that connectivity remains consistent without requiring manual reconfiguration. This capability is essential for achieving high availability, load balancing, and disaster recovery objectives.
From an architectural perspective, VXLAN also introduces a more efficient use of network resources. By leveraging IP-based routing in the underlay network, VXLAN eliminates the need for spanning tree protocols, which are commonly used in VLAN environments to prevent loops. This allows all available network paths to be utilized simultaneously, improving bandwidth utilization and reducing latency. The result is a more resilient and efficient network fabric.
Security and isolation are also significantly enhanced in VXLAN environments. While VLANs provide basic segmentation, they are still tied to shared physical infrastructure, which can introduce risks if misconfigurations occur. VXLAN improves isolation by encapsulating traffic within distinct virtual segments, ensuring that tenant or application boundaries are enforced at the overlay level. This makes it particularly well-suited for multi-tenant cloud environments where strict separation between workloads is required.
VXLAN also supports more advanced security models such as micro-segmentation. This allows network policies to be applied at a very granular level, controlling communication between individual workloads rather than just broad network segments. This level of control is difficult to achieve with VLANs due to their scalability and management limitations.
Despite its advantages, VXLAN is not without complexity. It introduces additional overhead due to encapsulation and requires a more sophisticated understanding of both overlay and underlay networks. Proper design and configuration are essential to avoid issues such as inefficient routing or packet fragmentation. VXLAN also relies on control plane mechanisms to distribute endpoint information, which adds another layer of architectural complexity compared to traditional VLAN learning processes.
VLAN, on the other hand, remains highly effective in environments where simplicity is a priority. It is easy to configure, widely supported, and well understood by network engineers. For small to medium-sized networks, VLAN provides a cost-effective solution for segmentation without requiring advanced infrastructure or complex control systems. Its predictability and stability make it a reliable choice for traditional enterprise networks.
In real-world deployments, VLAN and VXLAN are often used together rather than as mutually exclusive technologies. VLANs may exist at the edge of the network or within smaller segments, while VXLAN forms the backbone of large-scale data center and cloud environments. This hybrid approach allows organizations to leverage the strengths of both technologies while mitigating their respective limitations.
The transition from VLAN to VXLAN also reflects a broader shift in networking philosophy. Traditional networking models were designed around static infrastructure, where devices and services were tied to fixed physical locations. Modern networking, however, is defined by abstraction, automation, and elasticity. VXLAN aligns with this paradigm by enabling networks to be defined in software, independent of physical constraints.
As organizations continue to adopt cloud computing, virtualization, and distributed application architectures, the importance of scalable overlay networking will continue to grow. VXLAN provides the foundation for these environments by enabling flexible, high-performance, and highly segmented network designs. VLAN, while still relevant, is increasingly limited to smaller-scale or legacy environments where its simplicity remains an advantage.
Ultimately, the choice between VLAN and VXLAN is not a matter of superiority but of suitability. VLAN is optimal for simplicity and stability in smaller networks, while VXLAN is designed for scale, flexibility, and modern cloud-native infrastructures. Understanding both technologies allows network engineers to design architectures that are not only functional but also future-ready, capable of supporting evolving demands in enterprise and cloud networking environments.