Secure communication has become a fundamental requirement in today’s internet-driven environment where data is constantly exchanged between users, applications, and servers. Every login attempt, online transaction, or data submission involves sensitive information that must be protected from interception or unauthorized access. To achieve this level of protection, encryption protocols were developed to secure communication channels. Among these, SSL and TLS are the most widely recognized technologies responsible for enabling encrypted data transfer across networks.
These protocols operate behind the scenes whenever a user accesses a secure website or interacts with a protected service. Their primary role is to ensure that the information transmitted between a client and a server remains confidential and unaltered. While users often recognize the presence of security through visual indicators such as secure connection messages or HTTPS usage, the underlying mechanism relies on complex cryptographic processes governed by these protocols. The evolution of SSL into TLS represents a major advancement in how internet security is implemented and maintained across modern systems.
Early Development of Secure Internet Communication Protocols
The early internet was designed primarily for open communication, with little emphasis on security or data protection. As a result, information transmitted across networks was vulnerable to interception, modification, and unauthorized monitoring. With the rapid growth of online services and digital communication, the need for secure transmission has become increasingly important. This led to the development of structured encryption systems designed to protect data in transit.
Secure Sockets Layer was introduced as one of the first widely adopted solutions to address these concerns. It provided a framework for encrypting communication between web browsers and servers, ensuring that sensitive information could not be easily accessed by third parties. The protocol introduced a systematic approach to authentication and encryption, allowing users to verify the identity of a website before sharing data.
As internet usage expanded globally, the limitations of early security mechanisms became more apparent. Cyber threats evolved, computational power increased, and weaknesses in initial encryption methods were identified. These challenges led to continuous improvements and eventually the development of a more advanced protocol designed to replace SSL and strengthen internet security standards.
Structural Functioning of Secure Sockets Layer
Secure Sockets Layer operates as a cryptographic protocol that establishes a secure channel between two communicating systems. Its main function is to encrypt data during transmission so that it remains unreadable to unauthorized entities. This encryption process ensures that even if data is intercepted, it cannot be interpreted without the appropriate decryption key.
The protocol relies on a combination of authentication and encryption mechanisms. Authentication verifies the identity of the server, ensuring that users are connecting to a legitimate source rather than a fraudulent one. Encryption then protects the data being transmitted, converting it into a coded format that can only be deciphered by the intended recipient.
SSL uses digital certificates to establish trust between the client and server. These certificates contain information about the identity of the server and are validated through a structured trust system. Once the certificate is verified, a secure session is created, allowing encrypted communication to begin. This process ensures that data integrity and confidentiality are maintained throughout the session.
Despite its effectiveness at the time of introduction, SSL underwent multiple revisions due to emerging vulnerabilities. Each version attempted to address weaknesses identified in previous iterations, but over time, it became clear that a more advanced system was required to meet modern security demands.
Limitations and Security Challenges in SSL Protocols
Although SSL played a critical role in establishing secure internet communication, it was not without flaws. One of the primary concerns was its reliance on outdated encryption algorithms that eventually became vulnerable to modern computational attacks. As processing power increased, attackers were able to exploit weaknesses in encryption strength, making certain versions of SSL less secure.
Another significant limitation was related to the handshake process used to establish secure connections. Early implementations lacked robust protection mechanisms, making them susceptible to interception and manipulation. This created potential risks during the initial stages of communication setup, where encryption keys were exchanged.
Over time, additional vulnerabilities were discovered in SSL implementations, including weaknesses in cipher selection and authentication validation. These issues highlighted the need for a more flexible and secure protocol capable of adapting to evolving cybersecurity threats. As a result, SSL was gradually phased out in favor of a more advanced and secure alternative.
Transition Toward Transport Layer Security Development
The development of Transport Layer Security marked a significant advancement in the field of internet security. Designed as an improvement over SSL, TLS introduced stronger encryption methods, enhanced authentication processes, and more secure handshake mechanisms. The goal was to address the limitations of SSL while maintaining compatibility with existing systems.
TLS operates in a similar manner to SSL but incorporates modern cryptographic standards that provide greater protection against attacks. It supports a wider range of encryption algorithms, allowing systems to negotiate the most secure option during communication setup. This flexibility ensures that TLS can adapt to different security requirements and remain effective in diverse environments.
One of the key improvements introduced in TLS is the strengthening of the handshake process. This process ensures that both parties involved in communication are properly authenticated before data exchange begins. Enhanced validation techniques reduce the risk of impersonation and unauthorized access, making TLS significantly more secure than its predecessor.
TLS has undergone several iterations, each improving upon the previous version. These updates address newly discovered vulnerabilities and incorporate advancements in cryptographic research. As a result, TLS has become the standard protocol for securing internet communication across modern platforms.
Role of Cryptography in Secure Data Transmission
At the core of both SSL and TLS lies cryptography, which is the science of securing information through mathematical algorithms. Cryptography ensures that data transmitted over networks remains confidential and protected from unauthorized access. It achieves this by converting readable information into encrypted formats that can only be decoded using specific keys.
Public key cryptography plays a central role in secure communication systems. It involves the use of two related keys: a public key and a private key. The public key is used to encrypt data, while the private key is used to decrypt it. This structure allows secure communication between parties without requiring them to share sensitive decryption information directly.
Digital certificates are used to validate the identity of servers within this system. These certificates are issued through trusted validation processes and serve as proof of authenticity. When a client connects to a server, it verifies the certificate before establishing a secure connection. This ensures that communication is taking place with a legitimate source.
The integration of cryptographic principles within SSL and TLS ensures that data confidentiality, integrity, and authentication are maintained throughout the communication process.
Establishing Secure Connections Through Handshake Processes
The handshake process is a critical component of secure communication protocols. It is responsible for establishing a secure connection between a client and a server before data transmission begins. During this process, both parties agree on encryption methods and exchange cryptographic keys required for secure communication.
The handshake begins with a series of negotiation steps where encryption parameters are selected. This includes determining the encryption algorithm, authentication method, and key exchange process. Once both parties agree on these parameters, a secure session is established.
This process ensures that both the client and server are authenticated and that communication remains protected from interception. Improvements in handshake design have played a significant role in strengthening modern security protocols, reducing vulnerabilities, and enhancing overall system reliability.
Evolution of Encryption Standards in Internet Communication
Encryption standards have evolved significantly over time, driven by advancements in technology and increasing cybersecurity threats. Early encryption methods used in SSL were effective for their time, but eventually became outdated as computational capabilities improved.
TLS introduced more advanced encryption standards that provide stronger protection against attacks. These include modern cipher suites and improved key exchange mechanisms that enhance overall security. The continuous evolution of encryption standards ensures that secure communication protocols remain effective against emerging threats.
This ongoing development reflects the dynamic nature of cybersecurity, where protocols must constantly adapt to new challenges. The transition from SSL to TLS represents a major milestone in this evolution, establishing a foundation for modern secure communication systems.
TLS Version Progression and Modern Security Standards
Transport Layer Security has undergone continuous development since its introduction, evolving through multiple versions designed to address emerging security challenges and cryptographic advancements. Each iteration of TLS introduced improvements in encryption strength, handshake efficiency, and resistance to known vulnerabilities. The progression from early TLS versions to modern implementations reflects the increasing complexity of securing digital communication in an environment where cyber threats are constantly evolving.
Early versions of TLS were built as direct improvements over SSL, inheriting its structural concepts while replacing weaker cryptographic components. TLS 1.0 marked the beginning of this transition, introducing enhanced security mechanisms but still retaining some legacy dependencies that later became problematic. TLS 1.1 introduced refinements to initialization vectors and improved resistance to certain types of cryptographic attacks. However, both versions eventually became insufficient due to advancements in attack techniques and computational capabilities.
TLS 1.2 represented a significant milestone by introducing stronger cryptographic algorithms and improved flexibility in cipher suite selection. It allowed systems to use advanced encryption methods such as stronger hashing functions and more secure key exchange protocols. This version became widely adopted due to its balance between security and compatibility. TLS 1.3 further refined the protocol by simplifying the handshake process, removing outdated cryptographic primitives, and reducing the number of round-trips required for secure connection establishment. These improvements not only increased security but also enhanced performance by reducing latency during connection setup.
Deep Structure of the TLS Handshake Process
The TLS handshake is a foundational process that establishes a secure communication channel between a client and a server before any data is transmitted. It is responsible for negotiating encryption parameters, authenticating identities, and generating session keys used for secure communication. This process ensures that both parties agree on how data will be protected throughout the session.
The handshake begins when a client initiates a connection request to a server. The server responds by presenting its digital certificate and supported cryptographic options. The client then verifies the authenticity of the certificate and selects an appropriate encryption method from the available options. This negotiation ensures that both parties use compatible and secure cryptographic settings.
Once encryption parameters are agreed upon, key exchange mechanisms are used to generate shared secret keys. These keys are essential for encrypting and decrypting data during the session. Modern TLS versions optimize this process by reducing the number of steps required, making the handshake more efficient while maintaining strong security guarantees.
The handshake also includes mechanisms for verifying message integrity. This ensures that no data exchanged during the setup process has been altered or tampered with. Once the handshake is complete, a secure session is established, and encrypted communication can begin. This entire process happens within milliseconds in modern systems, making it seamless to end users while providing strong protection against interception.
Cipher Suites and Encryption Negotiation Mechanisms
Cipher suites are a critical component of TLS, defining the combination of cryptographic algorithms used during secure communication. They specify how encryption, authentication, and key exchange are handled within a session. The selection of a cipher suite determines the overall security strength of the connection.
A typical cipher suite includes algorithms for key exchange, bulk encryption, and message authentication. Key exchange algorithms are responsible for securely sharing cryptographic keys between client and server. Bulk encryption algorithms handle the actual encryption of transmitted data, ensuring confidentiality. Message authentication algorithms verify that data has not been altered during transmission.
TLS supports multiple cipher suites to accommodate different security requirements and system capabilities. During the handshake process, the client and server negotiate which cipher suite to use based on mutual support and security preferences. Modern implementations prioritize strong encryption methods and eliminate support for outdated or vulnerable algorithms.
The evolution of cipher suites reflects the broader advancement of cryptographic research. Older suites relied on weaker algorithms that eventually became susceptible to attacks. Modern suites incorporate advanced encryption standards that provide significantly stronger protection against brute force and cryptographic analysis attacks. This flexibility allows TLS to adapt to changing security landscapes while maintaining backward compatibility where necessary.
Public Key Infrastructure and Trust Architecture
Public Key Infrastructure forms the backbone of secure communication systems by enabling identity verification and secure key exchange. It is a structured framework that manages digital certificates, encryption keys, and trust relationships between entities on a network. PKI ensures that communication occurs only between verified parties, reducing the risk of impersonation and unauthorized access.
At the core of PKI is the concept of asymmetric cryptography, where two mathematically related keys are used. The public key is shared openly, while the private key is kept secure by the server. This system allows encrypted data to be transmitted securely without requiring prior exchange of secret keys.
PKI also introduces a hierarchical trust model that establishes relationships between different entities. This hierarchy ensures that trust can be extended from a central authority to multiple users and systems. It creates a scalable framework that supports secure communication across large networks, including global internet infrastructure.
The integration of PKI with TLS ensures that encrypted connections are not only secure but also authenticated. This prevents malicious entities from impersonating legitimate servers and intercepting sensitive data.
Role and Function of Certificate Authorities in Trust Verification
Certificate Authorities play a crucial role in establishing trust within public key infrastructure systems. They are responsible for issuing digital certificates that validate the identity of websites and servers. These certificates confirm that a public key belongs to a legitimate entity, allowing users to trust the authenticity of a connection.
When a certificate is issued, it undergoes a verification process that confirms the identity of the requesting entity. Once validated, the certificate is digitally signed by the authority, making it recognizable by browsers and operating systems. This signature acts as proof that the certificate has not been tampered with and is issued by a trusted source.
During a secure connection, the client verifies the certificate presented by the server. If the certificate is valid and issued by a trusted authority, the connection proceeds securely. If not, the system may display warnings or block access to prevent potential security risks.
Certificate Authorities are essential in maintaining the integrity of secure communication systems. Without them, there would be no reliable way to verify the authenticity of digital identities, increasing the risk of fraudulent activity and data interception.
Digital Certificate Lifecycle and Validation Process
Digital certificates follow a structured lifecycle that includes issuance, validation, renewal, and revocation. This lifecycle ensures that certificates remain valid and trustworthy throughout their usage period. When a certificate is issued, it includes information about the entity it represents, the public key, and the expiration date.
Validation occurs whenever a secure connection is established. The client checks whether the certificate is still valid, has not expired, and has not been revoked. This process ensures that only active and trustworthy certificates are used for secure communication.
Renewal is required when a certificate approaches its expiration date. This process involves revalidation of identity and issuance of a new certificate. Revocation occurs when a certificate is compromised or no longer valid, ensuring that it cannot be used maliciously.
This lifecycle management is essential for maintaining trust in secure communication systems and preventing unauthorized access through outdated or compromised certificates.
HTTPS Integration and Secure Web Communication Framework
Secure communication over the web is commonly implemented through the HTTPS protocol, which combines HTTP with TLS encryption. This integration ensures that all data transmitted between a browser and a web server is encrypted and protected from interception.
When a user accesses a secure website, the browser initiates a TLS handshake to establish an encrypted connection. Once the handshake is complete, all data exchanged is encrypted using session keys. This prevents attackers from reading or modifying transmitted information.
HTTPS also provides authentication benefits by verifying the identity of the website through digital certificates. This ensures that users are connected to legitimate servers rather than fraudulent ones. The presence of HTTPS has become a standard indicator of secure communication in modern web environments.
Security Threats and Protocol Exploitation Techniques
Despite strong security mechanisms, SSL and TLS have historically been targeted by various attacks that exploit vulnerabilities in protocol design or implementation. One such attack involves protocol downgrade techniques, where attackers force a connection to use an older, less secure version of a protocol. This can expose communication to known vulnerabilities present in outdated systems.
Another notable vulnerability involves padding-based attacks that target weaknesses in encryption implementation. These attacks exploit predictable patterns in encrypted data to extract sensitive information. Over time, such vulnerabilities have been addressed through protocol updates and stronger encryption standards.
Man-in-the-middle attacks represent another category of threat where attackers intercept communication between two parties. By impersonating one side of the connection, they can potentially access or modify transmitted data. TLS mitigates this risk through authentication mechanisms and certificate validation processes.
The continuous evolution of TLS is driven by the need to counter these emerging threats and strengthen overall system resilience.
Browser Security Indicators and Trust Mechanisms
Modern web browsers provide visual indicators to inform users about the security status of a connection. These indicators are based on the presence and validity of TLS encryption. When a secure connection is established, browsers typically display visual cues that indicate encrypted communication.
If a certificate is invalid or a connection is insecure, browsers may display warning messages to alert users about potential risks. These indicators help users make informed decisions about the websites they interact with and reduce the likelihood of engaging with malicious sources.
Browser security systems rely heavily on TLS validation processes to determine the trustworthiness of a connection. This integration ensures that users benefit from automated security checks without needing to understand the underlying cryptographic mechanisms.
Modern TLS Security Hardening and Cryptographic Strength Improvements
Modern Transport Layer Security has evolved into a highly optimized cryptographic framework designed to withstand contemporary cyber threats while maintaining performance efficiency across global networks. Unlike earlier SSL implementations that relied on relatively static encryption structures, TLS introduces adaptive cryptographic negotiation that allows systems to dynamically select stronger algorithms based on security requirements and system capability.
One of the most important improvements in modern TLS is the removal of outdated cryptographic primitives. Weak hashing functions and legacy encryption methods have been eliminated in newer versions, reducing exposure to brute-force attacks and cryptographic collisions. This shift ensures that encrypted communication is no longer dependent on vulnerable legacy algorithms that could be exploited through increasing computational power.
TLS also strengthens forward secrecy, a mechanism that ensures session keys are not reused across multiple communication sessions. Even if a long-term private key is compromised, past communication sessions remain protected because each session uses independently generated keys. This significantly reduces the long-term risk associated with key exposure.
The protocol also enforces stricter validation of certificate chains, ensuring that each certificate in the trust hierarchy is properly verified. This reduces the risk of fraudulent certificates being accepted by browsers or applications. These improvements collectively create a more resilient encryption environment that aligns with modern cybersecurity expectations.
SSL Vulnerabilities and Legacy Security Failures in Real Systems
Secure Sockets Layer, while foundational in the development of encrypted communication, contains structural weaknesses that make it unsuitable for modern security requirements. Many of these vulnerabilities stem from outdated cryptographic design choices and insufficient protection against evolving attack methods.
One of the most significant weaknesses in SSL is its susceptibility to protocol downgrade attacks. In such scenarios, attackers force a connection to fall back to an older version of SSL that contains known vulnerabilities. Once the downgrade occurs, encrypted communication can be intercepted or decrypted using established attack techniques.
Another critical issue lies in SSL’s weak handshake protection in early versions. The handshake process, which is responsible for establishing secure communication parameters, lacked sufficient safeguards against tampering. This allowed attackers to manipulate negotiation steps or exploit weak encryption selections.
SSL also suffered from limited cipher flexibility. Many early implementations supported outdated or weak encryption algorithms that could be broken using modern computational techniques. Over time, these weaknesses accumulated, making SSL increasingly unreliable for securing sensitive data transmission.
Due to these issues, SSL was formally deprecated and replaced by TLS, which introduced stronger cryptographic foundations and more secure design principles.
TLS Protection Against Modern Cyber Attacks
TLS is designed to resist a wide range of cyber threats that target encrypted communication systems. One of its primary defenses is against interception-based attacks, where attackers attempt to capture and decode transmitted data. TLS prevents this through strong encryption and secure key exchange mechanisms that ensure intercepted data remains unreadable.
Another major threat addressed by TLS is impersonation attacks. These occur when a malicious entity attempts to mimic a legitimate server in order to deceive users. TLS counters this by requiring validated digital certificates issued through trusted verification systems. Without a valid certificate, the connection is flagged as untrusted.
TLS also mitigates replay attacks, where previously captured data is retransmitted to gain unauthorized access. By incorporating unique session identifiers and time-sensitive encryption parameters, TLS ensures that captured data cannot be reused effectively.
Additionally, TLS defends against cryptographic downgrade attempts by enforcing strict version negotiation rules in modern implementations. This prevents attackers from forcing weaker protocol versions during handshake initialization.
These protective mechanisms make TLS significantly more robust compared to its predecessor, especially in environments where security threats are constantly evolving.
Role of Session Keys in Secure Communication Lifecycle
Session keys play a central role in TLS by enabling secure and efficient encryption during active communication sessions. These keys are generated dynamically during the handshake process and are used to encrypt all data transmitted between a client and server.
Unlike long-term cryptographic keys, session keys are temporary and are discarded once the communication session ends. This reduces the risk of key exposure and limits the potential impact of security breaches.
Session keys are derived using secure key exchange algorithms that ensure both parties independently compute identical encryption keys without directly transmitting them over the network. This approach prevents attackers from intercepting or reconstructing the keys during transmission.
Modern TLS implementations further enhance session key security by incorporating forward secrecy mechanisms. This ensures that even if long-term keys are compromised, past session keys remain secure and cannot be retroactively decrypted.
The use of session keys is essential for maintaining both performance and security, allowing encrypted communication to occur efficiently without compromising protection.
Performance Optimization in TLS Communication Systems
While security is the primary function of TLS, performance optimization is also a critical consideration in modern implementations. Secure communication introduces computational overhead due to encryption and decryption processes, which can impact system efficiency if not properly optimized.
TLS addresses performance challenges through streamlined handshake procedures that reduce the number of communication exchanges required to establish a secure connection. Modern versions minimize latency by combining multiple handshake steps into fewer interactions.
Session resumption mechanisms also improve performance by allowing previously established secure sessions to be reused without repeating the full handshake process. This reduces computational load and improves response times for frequently accessed services.
Hardware acceleration is another factor that enhances TLS performance. Many modern systems integrate cryptographic processing capabilities directly into hardware components, allowing encryption tasks to be executed more efficiently than software-based implementations alone.
These optimizations ensure that strong encryption does not come at the cost of usability or system responsiveness.
Real-World Implementation of TLS in Digital Infrastructure
TLS is widely implemented across digital infrastructure to secure communication between applications, services, and users. It is used in web browsing, email transmission, messaging systems, cloud platforms, and enterprise networks.
In web communication, TLS ensures that data exchanged between browsers and servers remains encrypted and authenticated. This protects sensitive user information such as login credentials, payment details, and personal data.
In email systems, TLS secures message transmission between mail servers, preventing interception during delivery. Messaging applications also rely on TLS to protect real-time communication between users.
Cloud-based systems use TLS to secure data transfer between distributed services and storage systems. This ensures that internal communication within cloud environments remains protected from unauthorized access.
Enterprise networks also rely heavily on TLS to secure internal communication channels, particularly in environments where sensitive corporate data is exchanged between multiple systems.
Evolutionary Direction of Internet Encryption Standards
The future of internet encryption continues to evolve as cyber threats become more sophisticated. TLS serves as the foundation for ongoing advancements in secure communication protocols, with continuous updates aimed at improving resilience, efficiency, and cryptographic strength.
Future developments focus on reducing handshake complexity, improving resistance to quantum-based attacks, and enhancing automated certificate management systems. These improvements aim to ensure that secure communication remains effective even as computational capabilities and attack methods evolve.
The progression from SSL to modern TLS demonstrates a clear trajectory toward stronger, more adaptive security systems. Each stage of development reflects lessons learned from previous vulnerabilities and introduces improvements designed to strengthen overall digital trust infrastructure.
TLS continues to serve as the core framework for secure communication across the internet, ensuring that data protection remains a fundamental component of modern digital interaction.
Conclusion
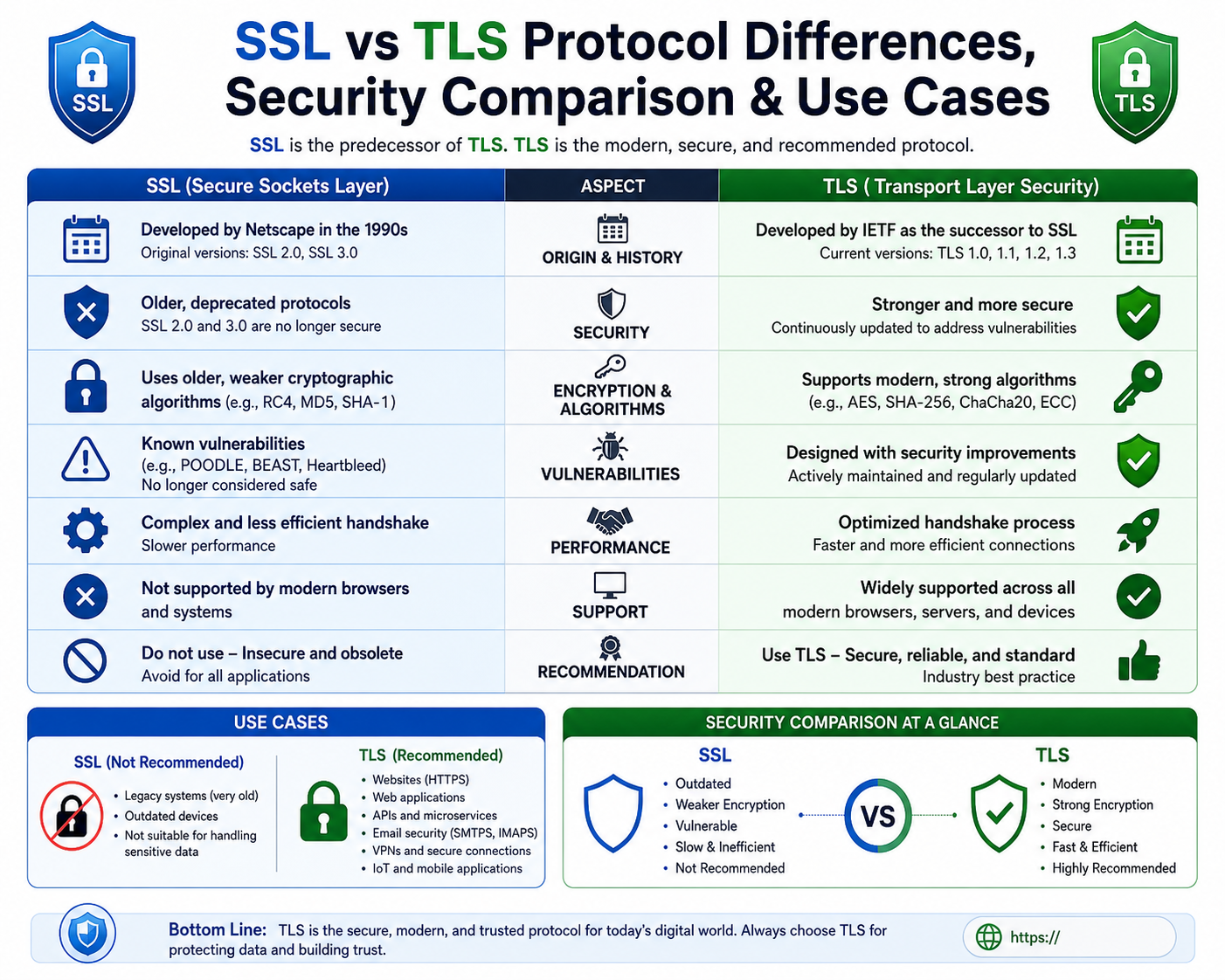
The evolution of SSL and TLS represents one of the most important developments in the history of internet security. These protocols were created to solve a critical problem that emerged as digital communication expanded: ensuring that data transmitted over open networks remains private, authentic, and unchanged. SSL introduced the first widely adopted framework for encrypted communication, while TLS refined and strengthened that foundation into a modern security standard capable of supporting today’s complex internet ecosystem.
SSL emerged during the early development of the Internet when security requirements were still relatively simple. At that time, most data was transmitted without encryption, making it vulnerable to interception and misuse. SSL introduced the concept of securing communication between a browser and a server through encryption, allowing sensitive information such as passwords and financial details to be transmitted more safely. This was a breakthrough because it addressed the absence of built-in security in early web systems. However, as technology advanced, the weaknesses of SSL became increasingly clear. Older versions lacked the resilience needed to withstand modern cyberattacks, and their cryptographic methods were eventually considered outdated.
TLS was developed as a successor to SSL with the goal of addressing these weaknesses while improving performance and security. It introduced stronger encryption algorithms, more secure handshake procedures, and improved authentication mechanisms. Over time, TLS evolved through multiple versions, each designed to enhance security and remove outdated cryptographic practices. TLS 1.0 and 1.1 represented early improvements, but they still retained some legacy weaknesses. TLS 1.2 brought significant advancements, including stronger encryption options and more flexible cipher negotiation. TLS 1.3 further improved the protocol by simplifying the handshake process, reducing latency, and eliminating insecure cryptographic methods.
One of the most important differences between SSL and TLS lies in their cryptographic strength and flexibility. SSL relied on older encryption techniques that eventually became vulnerable as computing power increased. TLS was designed to be adaptable, allowing it to support stronger encryption standards and more secure key exchange methods. This adaptability ensures that TLS can evolve alongside advancements in cybersecurity and remain effective against emerging threats.
Another key improvement introduced by TLS is the enhancement of the handshake process. The handshake is responsible for establishing a secure connection between a client and a server before any data is transmitted. In SSL, this process was more complex and less secure, leaving potential gaps for exploitation. TLS streamlined the handshake while strengthening its security, ensuring that both parties are properly authenticated before communication begins. This reduces the risk of interception or impersonation during connection setup.
Forward secrecy is another major advancement associated with TLS. This feature ensures that session keys are unique for each communication session and are not reused. As a result, even if a long-term encryption key is compromised, past communication remains protected. This significantly improves long-term data security and reduces the impact of potential breaches.
TLS also enhances certificate validation processes, ensuring that digital certificates used for authentication are more reliably verified. Certificates play a crucial role in confirming the identity of servers, and stronger validation reduces the risk of fraudulent or malicious certificates being accepted. This strengthens trust across digital communication systems and helps prevent impersonation attacks.
In real-world applications, TLS is essential for securing nearly all forms of online communication. Web browsing is one of the most visible examples, where TLS ensures that data exchanged between browsers and websites remains encrypted. This protects sensitive information such as login credentials, personal details, and payment data. Without TLS, this information would be exposed to potential interception.
TLS is also widely used in email systems, messaging applications, and cloud computing environments. In these systems, data is constantly transmitted between servers and users, often across public networks. TLS ensures that this communication remains secure regardless of where it is transmitted. In cloud environments, it plays a particularly important role in securing communication between distributed services, helping maintain data integrity and confidentiality across complex infrastructures.
Despite its strength, TLS is not without challenges. Cybersecurity threats continue to evolve, and attackers constantly develop new methods to exploit weaknesses in systems. One ongoing concern is protocol downgrade attacks, where attackers attempt to force a connection to use an older, less secure version of a protocol. Modern TLS implementations address this by restricting support for outdated versions and enforcing stricter negotiation rules.
Misconfiguration also remains a significant risk. Even strong encryption systems can be weakened if improperly configured. Weak cipher selection or incorrect certificate handling can introduce vulnerabilities that compromise security. This highlights the importance of proper implementation and maintenance in ensuring secure communication.
Man-in-the-middle attacks are another persistent threat, where attackers intercept communication between two parties. TLS mitigates this risk through authentication mechanisms and certificate validation, but its effectiveness depends on correct deployment and system integrity.
TLS continues to play a central role in modern internet infrastructure. It has become the standard protocol for securing data in transit across virtually all digital systems. Its ability to adapt to new threats and incorporate stronger cryptographic standards ensures its continued relevance in an evolving cybersecurity landscape. As technology advances, TLS will likely continue to evolve, incorporating even stronger encryption methods and improved performance optimizations.
The broader impact of SSL and TLS extends beyond technical implementation. These protocols have fundamentally shaped how secure communication is approached in the digital world. They have established expectations for privacy and security across online services, influencing both system design and user behavior. Today, encrypted communication is not just a feature but a standard requirement for trust in digital systems.
As cybersecurity continues to evolve, TLS remains at the core of secure communication frameworks. Its ongoing development reflects the constant need to balance security, performance, and usability in an increasingly connected world.