Policy-based routing is a technique that allows network devices to forward traffic based on predefined policies instead of relying only on destination-based routing tables. In traditional routing systems, packets are forwarded according to the best path calculated by routing protocols such as OSPF, EIGRP, or BGP. These decisions are primarily based on metrics like hop count, bandwidth, delay, or administrative distance. While this approach works well for general connectivity, it does not consider business requirements or application-specific needs.
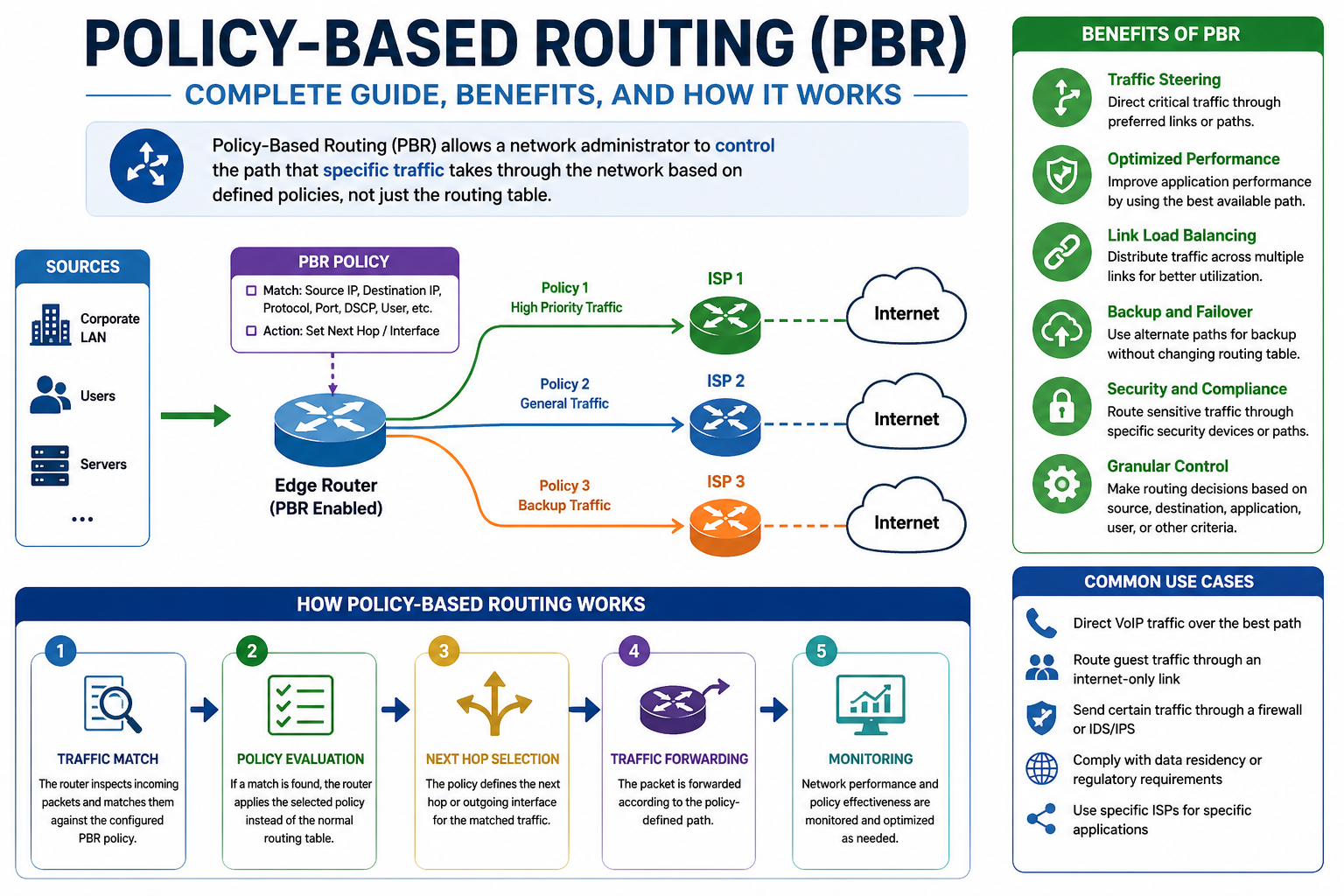
Policy-based routing changes this behavior by introducing rule-based decision-making into the forwarding process. Instead of treating all traffic equally, the router evaluates packets using defined conditions before deciding where to send them. These conditions can include source IP address, destination IP address, protocol type, port numbers, or even specific traffic flows. This allows different types of traffic to follow different paths even if they share the same destination network. The result is a more flexible and controlled routing environment where traffic behavior can be aligned with organizational priorities rather than purely technical routing metrics.
Real-World Analogy of Policy-Based Routing Behavior
Policy-based routing can be understood more clearly by comparing it to a real-world logistics and postal delivery system. When a package is sent over long distances, it typically passes through multiple processing points such as local offices, regional hubs, transportation centers, and sorting facilities. This structured path ensures efficient handling of large-scale deliveries.
However, not all deliveries require such a complex route. A letter sent within the same city does not need to travel through national hubs or distant processing centers. If it did, it would waste time and resources. Similarly, in computer networks, not all packets need to follow the same routing path. Some traffic benefits from direct or optimized routes rather than default paths chosen by routing protocols. Policy-based routing allows network administrators to define smarter paths for specific traffic types, ensuring that each packet follows the most efficient route based on its characteristics rather than a generalized routing decision.
Limitations of Traditional Routing and the Need for Policy Control
Traditional IP routing depends heavily on routing tables that are built using static routes or dynamic routing protocols. These protocols calculate the best path based on predefined metrics. While this method ensures consistency and scalability, it lacks flexibility when different types of traffic require different handling.
For example, a network may carry both critical business application traffic and general internet browsing traffic. Even if both types share the same destination, traditional routing would send them through the same path. This can lead to inefficiencies, congestion, or suboptimal performance for sensitive applications. In larger enterprise environments, this limitation becomes even more noticeable because traffic diversity increases significantly. Without policy-based routing, administrators often need to manipulate routing metrics indirectly, which can be complex and inefficient.
How Policy-Based Routing Overrides Default Routing Behavior
Policy-based routing introduces a layer of control that sits above the normal routing decision process. When a packet arrives at a router, it is first evaluated against a set of predefined policies. If the packet matches a policy condition, the router overrides the standard routing table decision and applies the specified action.
This action may include forwarding the packet to a specific next-hop address, sending it through a particular interface, or applying a custom routing path. If the packet does not match any policy, it follows the normal routing process. This dual behavior allows networks to maintain standard routing for general traffic while applying customized rules for selected traffic flows. As a result, policy-based routing acts as a selective traffic steering mechanism that enhances routing intelligence without replacing existing routing protocols.
Key Components Involved in Policy-Based Routing
Policy-based routing relies on a structured set of components that work together to define and enforce traffic behavior. The first component is traffic classification, which identifies packets that require special handling. This is typically done by examining packet headers and matching specific attributes such as IP addresses or protocols.
The second component is policy definition, where actions are assigned to the classified traffic. These actions determine how matching packets should be handled, such as selecting an alternative next-hop or redirecting traffic flow. The third component is policy enforcement, which applies these rules to a network interface so that incoming packets are evaluated in real time. Together, these components form a complete system that enables precise control over how traffic is processed and forwarded within a network environment.
Traffic Classification Using Packet Attributes
Traffic classification is the foundation of policy-based routing. It involves inspecting packet headers to identify key attributes that define the nature of the traffic. These attributes may include source IP address, destination IP address, protocol type, or transport layer ports.
By analyzing these parameters, routers can group packets into specific categories. For example, traffic originating from a particular subnet can be treated differently from general internet traffic. Similarly, voice, video, or application-specific traffic can be identified using protocol-based filtering. This classification process ensures that only relevant traffic is subjected to policy-based routing rules, allowing for precise and efficient traffic management across the network.
Role of Route Mapping in Policy-Based Decisions
Once traffic has been classified, route mapping is used to define the behavior that should be applied to matching packets. A route map functions as a conditional logic structure that evaluates traffic against defined criteria. If a packet matches the specified condition, the route map triggers an action that modifies its forwarding behavior.
This may include setting a specific next-hop address or redirecting traffic through a designated path. Route maps can also include multiple conditions and actions, allowing for complex policy structures within a single configuration framework. They serve as the decision-making engine of policy-based routing, linking traffic classification to actual forwarding behavior in a structured and flexible manner.
How Interface-Level Policy Application Works
After defining traffic classification and routing behavior, the policy must be applied to a network interface. This ensures that all incoming traffic on that interface is evaluated against the configured rules.
When a packet enters the interface, the router immediately checks whether it matches any defined policy. If a match is found, the router applies the corresponding forwarding action before sending the packet to its next destination. If no match is found, the packet follows standard routing behavior. This interface-level enforcement ensures that policy-based routing operates at the point of entry, allowing decisions to be made as early as possible in the forwarding process.
Operational Benefits of Policy-Based Routing in Networks
Policy-based routing provides several important benefits in modern network environments. One of the primary advantages is traffic optimization, where specific types of traffic can be directed through more efficient paths to reduce latency and improve performance. It also provides enhanced control over traffic flows, allowing administrators to implement business-driven routing decisions.
Another key benefit is flexibility, as policies can be adjusted without changing the underlying network topology. This makes it easier to respond to changing network demands. Additionally, policy-based routing improves resource utilization by distributing traffic more intelligently across available paths. These advantages make it a powerful tool for managing complex networks with diverse traffic requirements.
Initial Overview of Traffic Flow Adjustment Through Policy Rules
In practical use, policy-based routing modifies how traffic flows through a network based on predefined conditions. When packets enter a router, they are not immediately forwarded based solely on destination information. Instead, they are evaluated against policy rules that determine whether special routing behavior should be applied.
If a packet matches a policy, it may be redirected through a different path or forwarded to a specific next-hop device. This allows network traffic to be dynamically adjusted based on its characteristics rather than relying entirely on static routing logic. The ability to influence traffic flow in this way provides a significant level of control over network performance and efficiency.
Deeper Understanding of Policy-Based Routing Decision Process
Policy-based routing operates by inserting an additional decision layer into the standard packet forwarding process. In traditional routing, once a packet enters a router, the destination IP address is checked against the routing table, and the best path is selected. Policy-based routing modifies this sequence by introducing conditional evaluation before the routing table lookup is finalized.
When a packet arrives, it is first inspected against a configured set of policy rules. These rules define specific traffic characteristics that must be matched before any routing modification occurs. If a match is found, the router overrides the default forwarding decision and applies a predefined action. If no match is found, the packet continues through the normal routing process without alteration.
This dual-path decision model creates a structured hierarchy in packet processing. Instead of relying solely on destination-based forwarding, the router now evaluates intent, context, and traffic classification. This allows administrators to design routing behavior that aligns with application requirements, security policies, and performance optimization strategies rather than only network topology.
How Packet Matching Works in Policy-Based Routing
Packet matching is the foundational mechanism that determines whether a packet will be subject to policy-based routing rules. This process involves inspecting packet headers and comparing them against predefined conditions. These conditions are typically expressed through filtering logic that identifies specific traffic attributes.
The most commonly used attributes include source IP address, destination IP address, protocol type, and transport layer port numbers. In more advanced configurations, multiple attributes can be combined to create highly specific traffic definitions. For example, traffic originating from a particular subnet and using a specific application protocol can be isolated for special handling.
Once a packet is analyzed, it is classified into either a matching or non-matching category. Matching packets are processed according to the defined policy, while non-matching packets are routed using standard routing logic. This classification process ensures that policy-based routing only affects targeted traffic, preventing unintended disruption to general network operations.
Importance of Access Control Logic in Traffic Identification
Access control logic plays a critical role in policy-based routing because it defines how traffic is identified and grouped. This logic acts as a filtering mechanism that determines which packets qualify for special routing treatment.
The filtering process works by evaluating packet attributes against a set of conditions. If a packet satisfies these conditions, it is marked as eligible for policy-based routing. Otherwise, it is excluded from policy processing. This mechanism allows administrators to create precise traffic definitions that can be reused across different routing policies.
By leveraging access control logic, networks gain the ability to distinguish between different types of traffic at a granular level. This is especially important in environments where multiple applications share the same infrastructure but require different performance or security handling.
Role of Conditional Route Maps in Traffic Steering
Route maps serve as the decision engine within policy-based routing systems. They define the conditions under which traffic is modified and specify the actions that should be taken when those conditions are met.
A route map operates using an if-then structure. The “if” portion defines the matching criteria, while the “then” portion defines the resulting action. This structure allows for flexible and modular policy design. Multiple conditions can be defined within a single route map, enabling complex decision trees for traffic handling.
When a packet matches the conditions defined in a route map, the router applies the associated action, such as changing the next-hop address or redirecting traffic through a different interface. If the packet does not match, it is processed using standard routing behavior. This conditional logic makes route maps a powerful tool for implementing dynamic traffic control strategies.
Next-Hop Manipulation in Policy-Based Routing
One of the most important capabilities of policy-based routing is next-hop manipulation. In traditional routing, the next hop is determined by the routing table based on destination lookup. Policy-based routing allows this decision to be overridden for specific traffic flows.
When a packet matches a policy, the router can be instructed to send it to a manually defined next-hop address. This allows traffic to be redirected through alternative paths that may not be selected by standard routing protocols. The ability to control the next hop at a granular level enables more efficient use of network resources and better traffic distribution.
Next-hop manipulation is particularly useful in scenarios where multiple paths exist between two points in a network. Instead of relying on automatic path selection, administrators can define explicit routing behavior based on traffic type, source location, or application requirements.
Interface-Level Enforcement of Routing Policies
Policy-based routing is applied at the interface level, meaning that traffic is evaluated as it enters a specific router interface. This design ensures that decisions are made as early as possible in the packet forwarding process.
When a packet arrives at an interface, it is immediately checked against the configured policy. If it matches the policy criteria, the router applies the specified routing modification before forwarding the packet. If it does not match, the packet follows the standard routing process.
This interface-level enforcement is critical because it allows for localized control of traffic behavior. Different interfaces can have different policies, enabling highly customized routing decisions within the same device. This flexibility is essential in complex network environments where traffic enters from multiple sources with varying requirements.
Traffic Flow Diversion and Path Optimization
One of the primary use cases of policy-based routing is traffic flow diversion. This involves redirecting specific types of traffic away from their default path and sending them through alternative routes that are more efficient or appropriate.
Traffic diversion is often used to optimize network performance by balancing load across multiple links. It can also be used to prioritize certain types of traffic, ensuring that critical applications receive better performance. For example, business-critical traffic may be routed through high-performance links, while less important traffic is sent through standard paths.
This selective routing approach allows networks to make better use of available bandwidth and reduce congestion on primary links. It also improves overall user experience by ensuring that high-priority traffic is not delayed by lower-priority data flows.
Interaction Between Policy-Based Routing and Standard Routing Protocols
Policy-based routing does not replace traditional routing protocols; instead, it operates alongside them. Standard routing protocols continue to build and maintain the routing table, while policy-based routing selectively overrides those decisions when necessary.
This coexistence allows networks to benefit from both dynamic routing efficiency and policy-driven customization. Routing protocols handle general connectivity and path optimization, while policy-based routing handles specialized traffic requirements.
The interaction between these two systems must be carefully managed to avoid conflicts. If policies are too broad or improperly defined, they can override important routing decisions and create unintended traffic behavior. Proper design ensures that policy-based routing complements rather than disrupts normal routing operations.
Impact of Policy-Based Routing on Network Performance
Policy-based routing can significantly influence network performance when implemented correctly. By directing traffic through optimized paths, it reduces congestion and improves latency for critical applications. It also allows better utilization of available network links by distributing traffic based on defined rules rather than default routing behavior.
However, improper configuration can negatively impact performance. If policies are too complex or incorrectly applied, they may introduce inefficiencies or create routing loops. Therefore, careful planning and precise rule definition are essential for achieving optimal performance benefits.
When properly implemented, policy-based routing enhances both efficiency and predictability in network traffic behavior, making it a valuable tool for performance optimization in enterprise environments.
Scalability Considerations in Policy-Based Routing Environments
As networks grow in size and complexity, policy-based routing configurations must also scale accordingly. Large-scale environments often involve multiple routers, interfaces, and traffic types, each requiring different routing policies.
Scalability challenges arise when policies become too numerous or complex to manage efficiently. To address this, administrators often design modular policies that can be reused across multiple devices or interfaces. This reduces configuration complexity and improves consistency across the network.
Scalable policy design also involves careful planning of traffic classification rules to ensure that only necessary traffic is evaluated by policy-based routing. This helps maintain performance while still providing the required level of traffic control.
Security Implications of Policy-Based Routing
Policy-based routing can also play a role in network security by directing sensitive traffic through secure paths. For example, certain types of traffic can be routed through monitored or encrypted links, while less sensitive traffic follows standard routes.
This selective routing approach allows organizations to enforce security policies at the network layer without requiring changes to application behavior. It also enables better control over data flow, reducing the risk of exposure for sensitive information.
However, misconfiguration can introduce security risks. If policies are not properly defined, sensitive traffic may be routed through unintended paths. Therefore, careful policy design and validation are essential to maintaining network security integrity.
Advanced Traffic Engineering Using Policy-Based Routing
Policy-based routing is often used as a traffic engineering tool in advanced network environments. It allows administrators to design custom traffic flows that optimize performance, reliability, and resource utilization.
By analyzing traffic patterns and defining targeted policies, networks can be tuned to handle different workloads more effectively. This includes distributing traffic across multiple links, prioritizing specific applications, and avoiding congested paths.
Traffic engineering with policy-based routing provides a high level of control over how data moves through the network. This level of customization is not possible with traditional routing alone, making policy-based routing a key component of modern network design strategies.
Advanced Architecture of Policy-Based Routing in Large Networks
In large-scale network environments, policy-based routing becomes part of a broader traffic engineering architecture rather than a simple configuration feature on a single router. At this level, routing decisions are influenced by multiple layers of logic that work together to shape how traffic moves across distributed systems.
Instead of being used in isolation, policy-based routing is typically integrated into hierarchical network designs where edge devices, distribution routers, and core infrastructure each play different roles. Edge devices often handle traffic classification and initial policy enforcement, while upstream devices focus on high-speed forwarding. This separation of responsibilities ensures that policy-based decisions are made close to the source of traffic, reducing unnecessary processing at the core layer.
At scale, policy-based routing must also account for redundancy, failover paths, and multiple exit points. This introduces complexity because each policy must remain consistent across different devices while still adapting to local interface conditions. A well-designed architecture ensures that policies are predictable, synchronized, and aligned with overall routing strategy rather than acting as isolated configurations on individual routers.
Interaction Between Policy-Based Routing and Redundant Paths
Modern networks rarely rely on a single path between two endpoints. Instead, multiple redundant links are used to ensure availability and resilience. Policy-based routing interacts with these redundant paths by selectively choosing which path specific traffic should take.
When multiple next-hop options exist, policy-based routing can force traffic through a preferred path even if traditional routing protocols would select a different one based on metrics. This allows administrators to prioritize certain links for specific types of traffic while reserving others for backup or general use.
However, this introduces a design challenge. If policies are not carefully structured, they can unintentionally bypass redundancy mechanisms or create uneven load distribution. To avoid this, policy-based routing is often combined with path monitoring and dynamic adjustments that ensure traffic continues to flow even when preferred links become unavailable.
Policy-Based Routing in Multi-Link Load Distribution
One of the most powerful uses of policy-based routing is controlled load distribution across multiple links. Unlike equal-cost multipath routing, which distributes traffic based on hashing algorithms or equal metrics, policy-based routing allows explicit control over which traffic flows through which link.
For example, high-priority application traffic can be assigned to a high-bandwidth, low-latency link, while background data transfers can be routed through a secondary link. This separation ensures that critical services are not affected by non-critical traffic congestion.
Load distribution using policy-based routing is not random. It is based on deterministic rules that evaluate packet characteristics before making forwarding decisions. This allows network designers to create predictable traffic flows that align with business requirements rather than relying solely on automated balancing mechanisms.
Design Principles for Scalable Policy-Based Routing
As networks expand, policy-based routing must be designed with scalability in mind. Poorly structured policies can quickly become difficult to manage, especially when applied across multiple routers and interfaces.
A scalable design typically follows a modular approach. Traffic classification rules are defined once and reused across multiple policies. Route maps are structured in reusable segments, allowing consistent behavior across different network segments. Interface-level application is also standardized to reduce configuration drift.
Another key principle is minimizing overlap between policies. When multiple rules attempt to control the same traffic in different ways, conflicts can occur, leading to unpredictable routing behavior. A clean design ensures that each traffic type is governed by a single, well-defined policy path.
Scalability also depends on documentation and logical grouping of policies. Without clear structure, policy-based routing configurations can become difficult to troubleshoot and maintain as the network grows.
Common Misconfigurations in Policy-Based Routing Environments
Although policy-based routing is powerful, it is also prone to misconfiguration if not carefully implemented. One common issue is overly broad traffic matching, where policies unintentionally capture more traffic than intended. This can lead to unexpected routing behavior and degraded performance.
Another frequent issue is incorrect next-hop definition. If the specified next-hop is unreachable or incorrectly configured, traffic may be dropped or misrouted. This is especially problematic in environments with dynamic topology changes.
Interface misapplication is another common error. Applying a policy to the wrong interface can result in traffic not being evaluated as intended, leading to inconsistent routing behavior. Similarly, forgetting to apply a policy entirely results in traffic bypassing the intended routing logic.
Conflicts between multiple policies can also cause unpredictable behavior. When overlapping rules exist, packets may match unintended conditions, leading to inconsistent routing paths.
Troubleshooting Policy-Based Routing Behavior
Troubleshooting policy-based routing requires a structured approach that begins with verifying traffic classification. The first step is confirming whether packets are correctly matching the intended policy conditions. If traffic is not matching, the issue often lies in the access control definitions or classification logic.
The next step involves verifying route map configuration. This includes checking whether correct conditions are defined and whether the correct actions are assigned. Even small configuration errors in route maps can lead to major routing inconsistencies.
Interface-level verification is also critical. It is important to confirm that the policy is applied to the correct interface and direction. Policy-based routing typically operates on inbound traffic, so incorrect direction selection can result in the policy being bypassed entirely.
Finally, next-hop validation ensures that the destination defined in the policy is reachable. If the next-hop is not accessible, traffic may fail or revert to default routing behavior depending on the configuration.
Behavioral Analysis of Traffic Under Policy-Based Routing
Understanding how traffic behaves under policy-based routing requires analyzing packet flow at multiple stages. When a packet enters a router, it first undergoes policy evaluation before routing table lookup. If a match is found, the packet is assigned a new forwarding decision that overrides the default path.
This behavior changes the natural flow of traffic through the network. Instead of following shortest-path logic, packets follow policy-defined paths that may prioritize performance, security, or operational requirements.
Over time, this creates a traffic pattern that is shaped more by administrative intent than by automated routing algorithms. This shift from reactive routing to proactive traffic engineering is one of the most important characteristics of policy-based routing.
Impact of Policy-Based Routing on Network Convergence
Network convergence refers to the process by which routing tables stabilize after a change in topology. Policy-based routing does not directly participate in convergence but can influence traffic behavior during convergence events.
When a primary path becomes unavailable, routing protocols adjust the network topology and update routing tables. However, policy-based routing may still enforce specific next-hop decisions based on static rules. This can either improve or complicate convergence depending on how policies are designed.
If policies are aligned with backup paths, traffic can continue flowing smoothly during convergence. However, if policies reference unavailable paths, traffic may be disrupted until configurations are adjusted. This makes coordination between dynamic routing and policy-based routing essential in resilient network design.
Role of Policy-Based Routing in Hybrid Network Environments
Modern networks often consist of multiple technologies and transport methods, including leased lines, broadband connections, and private links. Policy-based routing plays an important role in managing traffic across these hybrid environments.
By defining rules that consider link type, cost, or performance characteristics, traffic can be directed to the most appropriate transport medium. For example, latency-sensitive applications can be routed through high-performance private links, while bulk data transfers can use lower-cost connections.
This hybrid approach allows organizations to optimize both performance and cost efficiency. Policy-based routing acts as the decision layer that determines how traffic is distributed across different network technologies.
Performance Tuning Through Policy-Based Routing Adjustments
Performance tuning using policy-based routing involves continuously refining traffic policies to match changing network conditions. As traffic patterns evolve, policies may need to be adjusted to maintain optimal performance.
This tuning process may include modifying traffic classification rules, adjusting next-hop preferences, or redistributing traffic across different interfaces. The goal is to ensure that high-priority traffic consistently receives optimal routing while avoiding congestion on critical links.
Performance tuning is not a one-time task but an ongoing process that requires monitoring and analysis of network behavior over time.
Real-World Enterprise Use Cases of Policy-Based Routing
In enterprise environments, policy-based routing is commonly used to separate different types of business traffic. For example, internal corporate applications may be routed through secure internal links, while guest or external traffic is routed through internet-facing connections.
It is also used to prioritize real-time communication traffic such as voice and video over less sensitive data transfers. This ensures consistent quality of service for time-sensitive applications.
Another common use case is multi-site connectivity optimization, where traffic between branches is routed based on bandwidth availability or latency considerations rather than fixed routing paths.
Long-Term Evolution of Policy-Based Routing in Networking
As networks continue to evolve, policy-based routing is becoming part of more intelligent and automated systems. Instead of static rule-based configurations, future implementations increasingly integrate with dynamic analytics and adaptive routing systems.
This evolution allows policy-based routing to respond to real-time network conditions rather than relying solely on predefined rules. While the core concept remains the same, its integration with intelligent systems enhances its flexibility and effectiveness in modern network architectures.
Over time, policy-based routing is expected to remain a foundational tool for traffic control while becoming more tightly integrated with automated network management systems.
Conclusion
Policy-based routing represents a fundamental shift in how modern networks handle traffic decisions. Instead of relying exclusively on destination-based routing logic, it introduces a layer of intelligent control that allows forwarding behavior to be shaped by organizational intent, application requirements, and operational priorities. This transformation is significant because it moves networking from a purely protocol-driven model to a policy-driven model where administrators can actively influence how data flows across infrastructure.
At its core, policy-based routing solves a limitation that exists in traditional routing systems: the inability to differentiate between types of traffic that share similar network characteristics. In real-world environments, not all packets are equal. Some traffic carries critical business transactions, some supports real-time communication, and others may simply represent background updates or non-urgent data transfers. Treating all of this traffic the same way can lead to inefficiencies, congestion, and inconsistent user experience. Policy-based routing addresses this by allowing traffic to be classified and directed based on meaningful attributes rather than only destination information.
One of the most important strengths of this approach is the level of control it provides. Network administrators are no longer constrained by the automatic decisions made by routing protocols alone. Instead, they can define explicit rules that align traffic flow with business logic. This means that sensitive applications can be prioritized, high-performance paths can be reserved for critical services, and less important traffic can be routed through alternative links. The result is a more predictable and optimized network environment where resources are used more effectively.
Another key advantage lies in its flexibility. Networks today are highly dynamic, with varying workloads, hybrid connectivity models, and constantly changing application demands. Policy-based routing adapts to this environment by allowing rules to be modified without redesigning the entire network topology. This makes it particularly valuable in enterprise environments where agility is essential. Changes in business requirements can be translated directly into routing policies, ensuring that the network continues to support organizational goals without requiring extensive structural modifications.
In addition to performance optimization, policy-based routing also contributes to improved resource utilization. Many networks have multiple available paths between endpoints, but traditional routing protocols often select a single best path based on metrics. This can result in underutilization of alternative links. By contrast, policy-based routing allows traffic to be distributed more intelligently across multiple paths based on predefined conditions. This leads to better bandwidth usage, reduced congestion on primary links, and improved overall network efficiency.
Security considerations also play an important role in the value of policy-based routing. By controlling the path that specific types of traffic take, organizations can enforce security boundaries more effectively. Sensitive data can be directed through monitored or secured segments of the network, while less critical traffic can be routed through standard paths. This helps reduce exposure risks and supports compliance requirements without requiring major architectural changes.
Despite its advantages, policy-based routing must be implemented with careful planning. Because it overrides default routing behavior, improper configuration can lead to unintended consequences such as traffic misdirection, asymmetric routing, or performance degradation. This makes design discipline essential. Policies must be clearly defined, logically structured, and consistently applied across the network. Without this discipline, complexity can increase quickly, making troubleshooting more difficult and reducing the overall effectiveness of the system.
Another important consideration is the relationship between policy-based routing and dynamic routing protocols. Both systems must coexist in a balanced way. Routing protocols are responsible for maintaining connectivity and calculating optimal paths based on network conditions, while policy-based routing introduces intentional overrides based on specific requirements. When properly aligned, these two mechanisms complement each other. However, when they are not coordinated, conflicts can arise that disrupt traffic flow or create unexpected routing behavior.
From an operational perspective, monitoring and visibility are critical to maintaining a stable policy-based routing environment. Because traffic is being directed based on rules rather than purely dynamic decisions, administrators must be able to verify that policies are functioning as intended. This includes understanding how traffic is being classified, which rules are being triggered, and how packets are being forwarded. Without proper visibility, it becomes difficult to ensure that the network is behaving according to design expectations.
Scalability is another important aspect of long-term policy-based routing design. As networks grow, the number of policies and traffic patterns can increase significantly. To manage this complexity, policies must be designed in a modular and reusable manner. This helps prevent configuration sprawl and ensures that changes can be applied consistently across multiple devices. Scalable design practices also reduce the risk of conflicts between policies and improve maintainability over time.
In modern network environments, policy-based routing is often part of a broader traffic engineering strategy. It is not used in isolation but integrated with other mechanisms that manage quality of service, load balancing, and redundancy. This integration allows for more sophisticated control over how traffic behaves under different conditions. Instead of relying on a single mechanism, networks use a combination of tools to achieve optimal performance and reliability.
As networking continues to evolve, the role of policy-based routing is also expanding. It is increasingly being combined with automation, analytics, and adaptive systems that can respond to real-time network conditions. This evolution is gradually shifting policy-based routing from a static configuration tool to a more dynamic and intelligent traffic control mechanism. While the core concept remains the same, its application is becoming more advanced and responsive to changing environments.
Ultimately, policy-based routing is best understood as a mechanism for aligning network behavior with real-world requirements. It provides the ability to move beyond generic routing logic and implement decisions that reflect actual operational priorities. Whether the goal is performance optimization, security enforcement, or traffic distribution, it offers a structured and powerful way to influence how data moves through a network.
Its long-term value lies in its ability to bridge the gap between technical routing decisions and business-driven outcomes. By giving administrators precise control over traffic flow, it ensures that networks are not just functional but strategically aligned with organizational needs.