A network stack in modern enterprise environments refers to the complete layered structure of interconnected technologies responsible for enabling communication, data flow, security enforcement, and centralized control across an organization’s IT infrastructure. It is not a single product or isolated system but a coordinated ecosystem that includes multiple functional domains working together. These domains typically span connectivity, routing intelligence, security enforcement, wireless access, traffic monitoring, and operational management. The effectiveness of a network stack is determined not only by the strength of individual components but by how well those components integrate and operate as a unified system under real-world conditions.
In contemporary enterprise architecture, the network stack plays a foundational role in determining business continuity, application performance, and security resilience. Every digital interaction within an organization, whether internal communication, cloud access, or external service delivery, passes through multiple layers of this stack. As a result, design decisions made at the network stack level have direct implications on latency, reliability, scalability, and operational efficiency. Organizations increasingly treat network architecture as a strategic asset rather than a purely technical deployment.
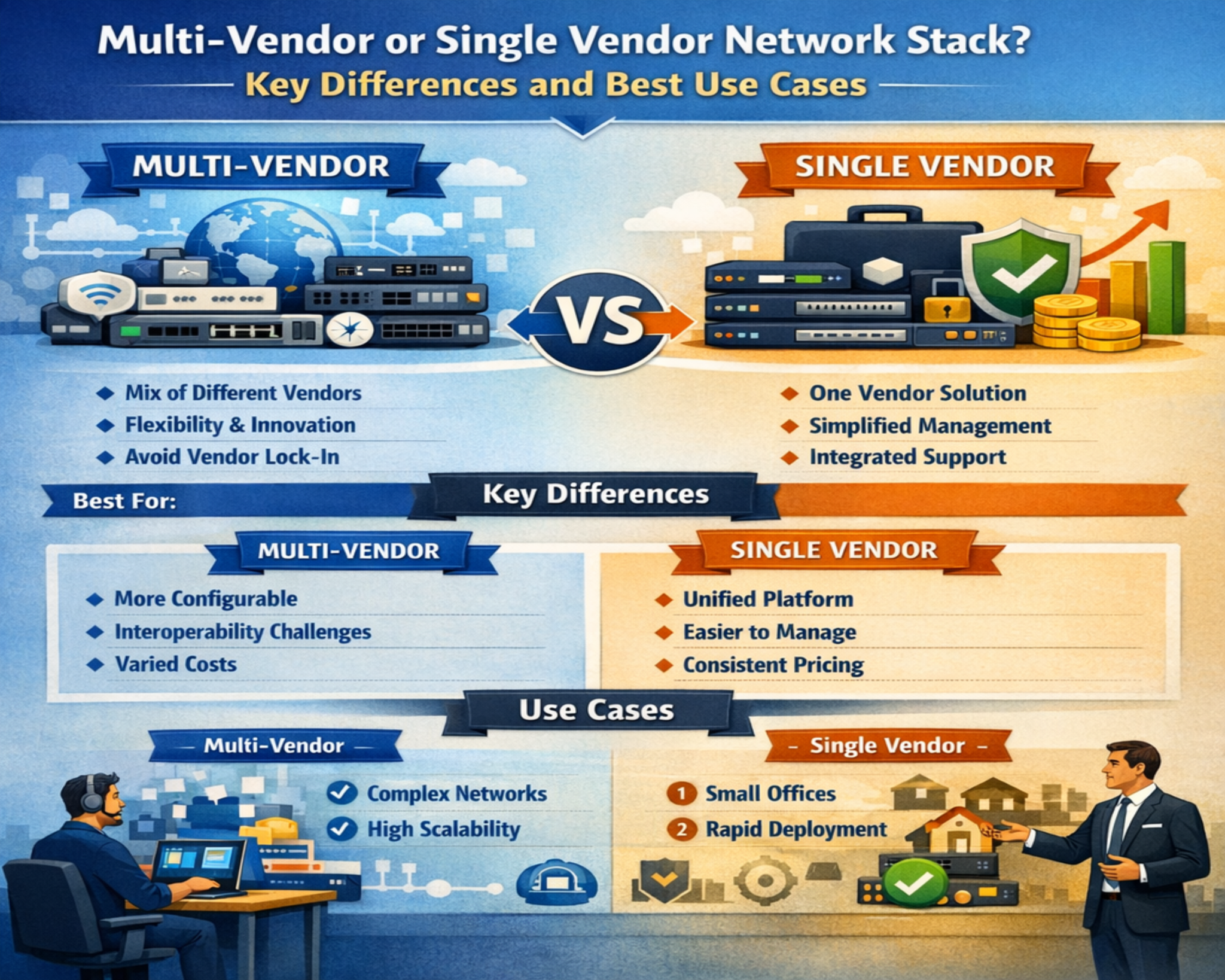
The complexity of modern environments has grown significantly due to hybrid infrastructures, distributed workforces, cloud adoption, and increasing cybersecurity threats. These factors have transformed the network stack from a static infrastructure model into a dynamic, adaptive system. As complexity increases, so does the importance of making deliberate architectural choices, particularly when deciding how network components should be sourced and integrated.
Core Components of a Network Stack
The structure of a network stack is typically composed of several core layers that collectively enable end-to-end communication. At the foundational level, switching infrastructure handles local data forwarding within and between network segments. Routing systems manage traffic between different networks, ensuring that data reaches its intended destination efficiently. Wireless systems provide mobility and flexible access for users and devices, particularly in environments with high endpoint diversity.
Security components form another critical layer of the stack. These include systems responsible for traffic inspection, access control, threat prevention, and segmentation enforcement. In modern architectures, security is no longer treated as an isolated perimeter function but as an integrated, distributed capability embedded throughout the network.
Management and orchestration tools represent the operational layer of the stack. These systems provide visibility into network behavior, enable configuration management, and support automation of repetitive tasks. Without this layer, administrators would lack the ability to maintain control over increasingly complex environments.
Each component of the stack interacts with the others through standardized protocols and configuration models. However, the degree of integration varies significantly depending on whether the environment is built using a unified vendor approach or a combination of multiple specialized systems.
Single-Vendor Network Stack Architecture Explained
A single-vendor network stack is characterized by the use of a unified ecosystem where most or all infrastructure components are sourced from a single provider. In this model, switching, routing, wireless access, security enforcement, and management tools are designed to operate within a consistent framework. The primary advantage of this approach lies in its operational simplicity and tight integration between components.
In a unified environment, configuration models are typically standardized across the entire stack. This reduces the learning curve for engineers and allows for more predictable behavior during deployment and maintenance. Network policies can often be applied consistently across multiple layers without requiring translation between different system architectures.
Another defining feature of a single-vendor model is centralized visibility. Since all components communicate within the same ecosystem, telemetry data is often aggregated into a unified dashboard. This allows for streamlined monitoring and faster identification of performance or security issues. Incident response processes are also simplified, as troubleshooting can be conducted within a single operational framework.
Lifecycle management is generally more predictable in this model. Hardware refresh cycles, firmware updates, and feature enhancements tend to follow a coordinated schedule. This reduces the likelihood of compatibility issues arising from asynchronous updates across different components.
However, this level of integration also introduces a higher degree of dependency on a single technology ecosystem. While this can simplify operations, it may also limit flexibility in adopting alternative technologies or adapting to changing requirements in specific areas of the network stack.
Multi-Vendor Network Stack Architecture Explained
A multi-vendor network stack is built by combining technologies from different providers, each selected based on specialization, performance characteristics, or cost considerations. Instead of relying on a single ecosystem, organizations deliberately choose best-fit solutions for each layer of the network architecture.
In this model, switching infrastructure may come from one provider, wireless systems from another, and security enforcement tools from yet another. The primary objective is to optimize each layer independently rather than conforming to a unified ecosystem. This allows organizations to leverage specialized strengths in different domains of the network stack.
One of the key advantages of this approach is flexibility. Organizations are not constrained by the limitations of a single vendor’s product roadmap. Instead, they can adopt new technologies or replace individual components without redesigning the entire network architecture. This adaptability is particularly valuable in rapidly evolving technological environments.
Another important benefit is performance optimization. Different vendors often excel in specific areas of networking technology. By combining these strengths, organizations can build highly optimized architectures tailored to their operational requirements. For example, one system may be selected for its advanced security capabilities, while another is chosen for its high-performance wireless connectivity.
However, this flexibility comes with increased complexity. Integration between different systems requires careful planning, especially when ensuring compatibility across protocols, configuration models, and telemetry systems. Without proper design, inconsistencies can emerge that affect performance or operational stability.
Operational Impact on IT Workflows
The structure of a network stack has a direct impact on how IT teams perform daily operational tasks. In a unified environment, workflows tend to be more streamlined because tools, interfaces, and configuration models follow a consistent design philosophy. This reduces cognitive load on engineers and simplifies routine operations such as provisioning, monitoring, and troubleshooting.
In contrast, a multi-vendor environment introduces variability in operational workflows. Engineers may need to switch between different management interfaces, interpret multiple logging formats, and apply vendor-specific troubleshooting methodologies. While this increases operational complexity, it can also provide deeper visibility into specialized system behavior when properly managed.
Incident response is another area where architectural differences become apparent. In a unified stack, root cause analysis can often be performed within a single system, reducing the time required to isolate issues. In a multi-vendor environment, troubleshooting may involve correlating data across multiple platforms, which requires more advanced analytical skills and coordination.
Lifecycle Management and Upgrade Considerations
Network infrastructure is continuously evolving through hardware upgrades, firmware updates, and feature enhancements. In a single-vendor architecture, these lifecycle events are typically coordinated across the entire stack. This ensures compatibility and reduces the risk of inconsistencies between different layers of the network.
In a multi-vendor environment, lifecycle management becomes more complex. Each component follows its own update cycle, which may not align with others in the ecosystem. This requires careful planning to avoid introducing compatibility issues during upgrades. Testing and validation become critical steps in ensuring that changes in one part of the stack do not negatively impact others.
The long-term sustainability of a network architecture is heavily influenced by how well lifecycle management is handled. Poor coordination can lead to fragmentation over time, while well-structured planning can maintain stability even in highly diverse environments.
Security Architecture and Policy Enforcement
Security is deeply embedded within the structure of a network stack. In unified environments, security policies are often integrated directly into the core infrastructure, allowing for consistent enforcement across all layers. This can simplify policy management and improve visibility into network behavior.
In multi-vendor environments, security enforcement may be distributed across different systems, each with its own configuration and monitoring model. While this can provide specialized security capabilities, it also requires careful alignment to ensure consistent policy enforcement across the entire network.
Network segmentation, access control, and threat detection mechanisms must be coordinated effectively to avoid gaps in security coverage. The complexity of managing these integrations increases with the number of vendors involved, making architectural design and documentation critical.
Performance and Scalability Considerations
Performance optimization in a network stack depends on both individual component capabilities and system-wide integration efficiency. Unified architectures often benefit from optimized communication between components, reducing latency and improving overall responsiveness.
Multi-vendor architectures, on the other hand, allow for targeted performance optimization at specific layers. This can result in superior performance in certain domains, but may introduce variability in end-to-end system behavior. Ensuring consistent performance across the entire stack requires careful tuning and continuous monitoring.
Scalability is another key consideration. Unified systems often scale more predictably due to standardized architecture models. Multi-vendor systems may offer more flexible scaling options, particularly in environments with diverse operational requirements across different locations or use cases.
Automation, Visibility, and Network Telemetry
Automation has become a central component of modern network operations. In unified environments, automation frameworks are typically integrated across all layers of the stack, enabling seamless orchestration of configuration and monitoring tasks.
In multi-vendor environments, automation often relies on external orchestration tools or custom integration layers. While this increases flexibility, it also introduces additional complexity in maintaining compatibility between systems.
Visibility into network behavior is closely tied to telemetry collection and analysis. Unified systems generally provide consolidated telemetry streams, while multi-vendor systems require aggregation from multiple sources. The ability to correlate this data effectively is critical for maintaining operational awareness and diagnosing issues.
Financial and Operational Cost Structures
Cost considerations in network stack design extend beyond initial procurement. They include licensing models, support agreements, operational overhead, and long-term maintenance requirements.
Unified architectures often benefit from simplified procurement and bundled pricing structures. This can reduce administrative overhead and provide more predictable cost planning. Multi-vendor architectures may offer cost optimization opportunities by allowing selective investment in high-priority areas while using more cost-effective solutions elsewhere.
However, operational complexity in multi-vendor environments can increase indirect costs related to training, troubleshooting, and integration management. These factors must be considered when evaluating the overall financial impact of architectural decisions.
Organizational Skills and Team Readiness
The effectiveness of any network architecture is ultimately determined by the skill level of the teams managing it. Unified environments allow teams to specialize deeply within a single ecosystem, reducing the breadth of knowledge required.
Multi-vendor environments require broader expertise across multiple platforms, increasing the importance of cross-training and documentation. Organizations must ensure that their teams are capable of managing diverse systems effectively to avoid operational inefficiencies.
The alignment between architecture and team capability is a critical factor in long-term success. Even the most advanced network design can fail if the supporting team lacks the necessary expertise to operate it effectively.
Single-Vendor Network Stack Strategy and Enterprise Operational Efficiency
A single-vendor network stack strategy is built around the principle of architectural consolidation. Instead of sourcing networking components from multiple providers, organizations standardize their entire infrastructure on one ecosystem. This typically includes switching, routing, wireless access, firewalls, identity management integration, and centralized monitoring tools all operating under a unified design philosophy. The objective is not just simplification, but operational coherence across every layer of the network.
In enterprise environments, this model is often chosen when predictability, stability, and streamlined operations are prioritized over component-level customization. The structure of a single-vendor stack allows for consistent behavior across devices, which reduces the variability that IT teams must manage during day-to-day operations. This consistency becomes especially valuable in large-scale deployments where even minor configuration differences can create significant operational friction.
The architecture of a unified stack is designed to minimize translation layers between systems. In other words, components are built to “understand” each other natively. This reduces the need for custom integrations, middleware, or external orchestration tools. As a result, organizations often experience smoother deployment cycles and more predictable network behavior under load.
Operational Simplicity in Unified Network Environments
One of the most significant advantages of a single-vendor approach is operational simplicity. In a complex IT environment, administrators must constantly interact with network devices to configure policies, monitor performance, and resolve issues. When all components are part of the same ecosystem, these tasks become significantly more streamlined.
Management interfaces are typically standardized, meaning engineers do not need to learn multiple configuration paradigms. Whether adjusting firewall rules, updating switch configurations, or managing wireless policies, the operational logic remains consistent. This reduces cognitive overhead and minimizes the likelihood of configuration errors.
Troubleshooting also becomes more efficient in a unified environment. Since logs, alerts, and telemetry data are collected within a single framework, engineers can correlate events without switching between disparate systems. This centralized visibility is particularly valuable during incident response scenarios where time is critical.
In addition, standardized automation capabilities allow organizations to automate repetitive tasks more effectively. Provisioning new devices, applying configuration templates, and enforcing security policies can all be managed through a unified automation engine. This reduces manual intervention and improves operational consistency across the network.
Integration Depth and Native Ecosystem Advantages
A defining characteristic of single-vendor environments is deep integration between components. Unlike multi-vendor architectures where interoperability must be engineered, unified ecosystems are designed from the ground up to function as a cohesive system.
This native integration enables features that are difficult to replicate in mixed environments. For example, security policies can be dynamically enforced across switching, routing, and wireless layers without requiring external coordination. Similarly, device discovery, network segmentation, and policy propagation can occur automatically across the entire infrastructure.
Another important benefit is synchronized feature development. When a vendor controls the entire stack, new capabilities can be rolled out across multiple layers simultaneously. This ensures that all components remain aligned in terms of functionality and performance expectations.
Unified ecosystems also tend to offer more mature lifecycle integration. Firmware updates, patch management, and hardware upgrades are coordinated across the stack, reducing the risk of compatibility issues. This predictability is especially important in environments with strict uptime requirements.
Security Alignment in Single-Vendor Architectures
Security architecture in a single-vendor network stack is typically more tightly integrated than in multi-vendor environments. Because all components operate within the same ecosystem, security policies can be enforced consistently across the entire infrastructure.
This consistency reduces the likelihood of policy gaps or misconfigurations between systems. For example, access control rules defined at the wireless layer can be seamlessly enforced at the switching and routing layers without requiring manual translation.
Unified security models also improve visibility. Since all telemetry data flows into a centralized platform, security teams can analyze network behavior holistically. This makes it easier to detect anomalies, correlate events, and respond to threats in real time.
In addition, integrated threat intelligence systems can operate across multiple layers simultaneously. This allows for coordinated responses to security incidents, such as automatically isolating compromised devices or dynamically adjusting firewall rules based on detected threats.
However, this level of integration also creates dependency on the vendor’s security framework. While it simplifies operations, it also means that organizations are reliant on the vendor’s approach to threat detection, policy design, and response mechanisms.
Cost Structure and Financial Predictability
From a financial perspective, single-vendor network stacks often provide predictable cost structures. Vendors typically offer bundled pricing models that include hardware, software licensing, and support agreements. This simplifies budgeting and reduces the complexity of procurement processes.
Large-scale deployments may also benefit from volume-based discounts and enterprise licensing agreements. These arrangements can significantly reduce per-unit costs and provide long-term financial stability.
Another advantage is reduced operational overhead. Since all components are managed within a single ecosystem, organizations spend less time coordinating between vendors, managing multiple support contracts, or resolving cross-platform compatibility issues. This reduction in operational complexity translates into indirect cost savings.
However, financial predictability must be balanced against potential limitations in pricing flexibility. Organizations may find themselves constrained by the vendor’s pricing model, particularly when scaling or introducing new capabilities.
Vendor Roadmap Alignment and Strategic Dependency
A critical but often overlooked aspect of single-vendor strategies is alignment with the vendor’s product roadmap. When an organization adopts a unified ecosystem, it inherently aligns its future infrastructure evolution with the vendor’s strategic direction.
This can be beneficial when the vendor’s roadmap aligns closely with the organization’s needs. New features, security enhancements, and performance improvements are typically delivered in a coordinated manner across the stack.
However, this dependency also introduces strategic risk. If the vendor shifts focus, changes licensing models, or discontinues certain product lines, the organization may be forced to adapt accordingly. This level of dependency requires careful consideration during long-term architectural planning.
Scalability in Unified Network Environments
Scalability in a single-vendor architecture is generally more predictable due to standardized design principles. As organizations expand their network footprint, additional components can be integrated using consistent configuration models.
This uniformity simplifies the process of adding new sites, expanding data centers, or integrating cloud environments. Since all components adhere to the same operational logic, scaling does not typically require significant redesign of existing infrastructure.
Centralized management systems also support large-scale visibility, allowing administrators to monitor distributed environments from a single control plane. This becomes increasingly important as networks grow in size and complexity.
However, scalability may be limited by the vendor’s product capabilities. If certain advanced features are not available within the ecosystem, organizations may need to wait for roadmap updates or consider architectural adjustments.
Multi-Vendor Network Stack Strategy and Architectural Flexibility
In contrast to unified environments, multi-vendor network stack strategies prioritize flexibility and specialization. Instead of relying on a single ecosystem, organizations select different vendors for different layers of the network based on performance, cost, and feature requirements.
This approach allows IT teams to build highly customized infrastructures tailored to specific operational needs. For example, one vendor may be chosen for its advanced firewall capabilities, while another is selected for high-performance switching or wireless optimization.
The primary advantage of this model is freedom of choice. Organizations are not restricted to a single vendor’s product capabilities and can adapt their architecture based on evolving requirements. This flexibility is particularly valuable in environments where technology requirements change rapidly.
Best-of-Breed Component Selection
A key principle of multi-vendor strategies is the concept of best-of-breed selection. This involves choosing the strongest available product for each layer of the network stack rather than relying on a single vendor’s entire portfolio.
This approach enables performance optimization at a granular level. For example, organizations may deploy advanced security appliances from one vendor while using another vendor’s wireless infrastructure for superior coverage and performance.
Best-of-breed strategies are particularly common in environments with specialized requirements. High-security environments, large-scale enterprise deployments, and cloud-integrated infrastructures often benefit from this level of customization.
However, achieving optimal results requires careful evaluation of compatibility between components. Not all systems are designed to integrate seamlessly, and differences in protocol implementation or configuration models can introduce complexity.
Operational Complexity in Multi-Vendor Environments
While multi-vendor architectures offer flexibility, they also introduce operational complexity. IT teams must manage multiple management interfaces, configuration models, and logging systems.
This increases the cognitive load on engineers and requires broader technical expertise. Troubleshooting issues often involves correlating data across multiple platforms, which can extend incident resolution times.
In addition, automation becomes more complex in multi-vendor environments. Integration between systems may require custom scripting, API development, or third-party orchestration tools.
Despite these challenges, many organizations accept the additional complexity in exchange for improved performance, flexibility, and reduced dependency on a single vendor.
Interoperability Challenges and Technical Coordination
Interoperability is one of the most critical challenges in multi-vendor environments. Even when industry standards exist, implementations can vary between vendors, leading to subtle inconsistencies.
These inconsistencies may affect VLAN behavior, routing protocols, authentication mechanisms, or power delivery standards. While these issues are often manageable, they require careful testing and validation during deployment.
Documentation and network design discipline become essential in mitigating interoperability risks. Without proper coordination, small configuration differences can escalate into larger operational issues.
Lifecycle Independence and Upgrade Flexibility
One of the key advantages of multi-vendor environments is lifecycle independence. Each component operates on its own upgrade cycle, allowing organizations to update specific parts of the network without impacting the entire system.
This enables more granular control over infrastructure evolution. Organizations can adopt new technologies incrementally, replacing or upgrading individual components as needed.
However, this independence also requires careful coordination. Misaligned upgrade cycles can introduce compatibility issues if not managed properly.
Strategic Balance Between Control and Complexity
Ultimately, the decision between single-vendor and multi-vendor strategies is not purely technical. It reflects a broader organizational philosophy regarding control, flexibility, and operational risk.
Unified environments prioritize control and simplicity, while multi-vendor environments prioritize flexibility and specialization. Both approaches are valid, but each requires different levels of expertise, governance, and operational maturity.
Organizations that succeed in either model tend to have strong architectural planning, disciplined operational processes, and well-trained engineering teams capable of managing the inherent trade-offs.
Hybrid Network Stack Design and Real-World Enterprise Architectures
Modern enterprise networks rarely fit neatly into the “single-vendor” or “multi-vendor” label in a pure form. In practice, most production environments evolve into hybrid architectures where standardization exists in certain layers while specialization is applied in others. This hybrid model emerges not as a theoretical preference but as a response to operational realities, procurement constraints, legacy infrastructure, and evolving cybersecurity demands.
A hybrid network stack combines elements of both architectural philosophies. Organizations may standardize switching and wireless infrastructure under one vendor while introducing specialized security platforms or SD-WAN solutions from another. Over time, this creates an ecosystem that balances operational consistency with technological flexibility.
This blended approach is especially common in enterprises that have grown through mergers, multi-phase modernization programs, or gradual cloud adoption. Rather than rebuilding everything from scratch, they integrate new technologies into existing environments, resulting in layered architectures that must function cohesively despite differences in design philosophy.
The hybrid model is not inherently complex or simple. Its effectiveness depends entirely on governance, engineering discipline, and architectural clarity. Without strong design principles, hybrid environments can become fragmented. With proper structure, they can outperform both pure single-vendor and fully mixed ecosystems.
Evolution of Network Stacks in Modern IT Environments
Network stacks are no longer static infrastructure deployments. They evolve continuously in response to business expansion, cloud migration, cybersecurity threats, and application modernization. This evolution typically occurs in phases rather than as a single transformation event.
In early-stage environments, organizations often begin with a single-vendor approach due to simplicity and ease of deployment. As requirements grow, additional tools are introduced to address gaps in performance, security, or scalability. Over time, this leads to partial diversification of the stack.
In mature enterprises, the network stack becomes a layered construct where different technologies coexist. Core infrastructure may remain standardized, while edge services, security layers, or cloud connectivity are handled by specialized systems. This evolutionary pattern explains why hybrid architectures dominate real-world deployments.
The transition from simple to complex architectures is rarely intentional in a rigid sense. Instead, it reflects incremental decision-making driven by operational needs. Each addition to the stack is justified by immediate requirements, but collectively these decisions shape long-term architectural behavior.
Architectural Governance in Hybrid Network Environments
Governance becomes a critical factor in hybrid network stacks. Unlike unified environments where consistency is enforced by design, hybrid architectures require explicit rules to maintain coherence across diverse systems.
Architectural governance defines how components are selected, integrated, and maintained. It establishes standards for interoperability, configuration consistency, security enforcement, and lifecycle management. Without governance, hybrid environments tend to drift into fragmentation over time.
A well-governed hybrid stack typically defines clear boundaries between layers. For example, one vendor may be designated for access-layer infrastructure, while another is responsible for perimeter security. These boundaries prevent overlap and reduce ambiguity in operational responsibilities.
Governance also plays a role in change management. Every modification in a hybrid environment has the potential to impact multiple systems. Structured approval processes, testing environments, and validation workflows are essential to prevent unintended disruptions.
In addition, governance ensures that technical decisions align with business objectives. Network architecture is not only a technical concern but also a strategic enabler for digital transformation, cloud adoption, and operational resilience.
Integration Complexity Across Multi-Vendor Systems
Integration is one of the most challenging aspects of hybrid network stacks. Even when vendors support standard protocols, real-world implementations often differ in subtle ways that affect interoperability.
Protocols such as routing exchange mechanisms, VLAN tagging, authentication frameworks, and telemetry reporting may behave differently depending on vendor implementation. These differences require careful configuration alignment to ensure consistent behavior across the network.
In hybrid environments, integration is not a one-time task. It is an ongoing process that evolves as systems are upgraded or replaced. Each change introduces the potential for compatibility issues that must be validated through testing.
API-based integration has become increasingly important in addressing these challenges. Modern networking platforms expose programmable interfaces that allow systems to exchange data and configuration information. However, API consistency varies across vendors, which means integration logic often requires customization.
Orchestration platforms are frequently used to bridge these gaps. These systems act as intermediaries, translating commands and aggregating telemetry across multiple vendors. While effective, they introduce additional architectural layers that must be maintained and secured.
Operational Visibility in Distributed Network Architectures
Visibility is a critical requirement in any network stack, but it becomes significantly more complex in hybrid environments. When multiple vendors are involved, telemetry data is often distributed across different management systems, each with its own format, granularity, and reporting structure.
Achieving unified visibility requires aggregation and normalization of data. This process involves collecting logs, performance metrics, and security events from multiple sources and consolidating them into a single operational view.
Without proper visibility, diagnosing issues becomes significantly more difficult. Engineers must correlate events manually across different systems, which increases resolution time and operational overhead.
Advanced monitoring platforms attempt to solve this problem by providing vendor-agnostic dashboards. These tools ingest data from multiple systems and present it in a unified format. However, the accuracy and depth of visibility depend heavily on integration quality.
Visibility is not only important for troubleshooting but also for capacity planning, security monitoring, and performance optimization. In hybrid environments, maintaining consistent visibility requires ongoing investment in monitoring infrastructure and data integration pipelines.
Security Posture in Hybrid Network Stacks
Security in hybrid network architectures is inherently more complex due to the distribution of enforcement points across multiple systems. Unlike unified environments where security policies are centrally defined and consistently applied, hybrid environments often rely on multiple security layers operating independently.
This distributed model can provide stronger defense-in-depth when properly implemented. Specialized security tools can be deployed at different layers of the network to address specific threat vectors. However, this approach also increases the risk of policy inconsistency.
Ensuring consistent security posture requires alignment between systems. Access control policies, segmentation rules, and threat detection mechanisms must be coordinated across all components of the stack.
Identity-based security models have become increasingly important in this context. By decoupling security policies from physical infrastructure, organizations can enforce consistent access controls regardless of underlying vendor differences.
Security telemetry integration is another critical requirement. Threat detection systems must be able to correlate events across multiple platforms to identify complex attack patterns. Without this capability, security visibility becomes fragmented.
Performance Engineering in Heterogeneous Network Environments
Performance optimization in hybrid network stacks requires a layered approach. Each component must be tuned individually, but overall system performance depends on how well these components interact.
Latency, throughput, and packet loss are influenced not only by hardware capabilities but also by integration efficiency. Mismatched configurations between vendors can introduce bottlenecks that are difficult to diagnose.
Quality of service policies must be carefully aligned across the entire stack. If one system prioritizes traffic differently than another, end-to-end performance can become inconsistent.
Load balancing and traffic engineering also become more complex in multi-vendor environments. Different systems may use different algorithms or thresholds, which can affect traffic distribution patterns.
Performance testing in hybrid environments must simulate real-world conditions across all integrated components. Isolated testing is insufficient because it does not capture cross-vendor interactions.
Lifecycle Management Across Diverse Infrastructure Components
Lifecycle management in hybrid environments involves coordinating updates, upgrades, and replacements across multiple vendor ecosystems. Each system follows its own release cycle, which introduces challenges in maintaining compatibility.
Firmware updates in one component may require validation against dependent systems to ensure continued interoperability. This requires structured testing environments that replicate production conditions.
Hardware refresh cycles also vary between vendors. Some systems may have longer support lifecycles than others, which can create imbalance in infrastructure aging.
Patch management becomes more complex as the number of vendors increases. Security updates must be applied consistently while ensuring that changes do not disrupt system integration.
Lifecycle planning in hybrid environments requires long-term visibility into vendor roadmaps and product evolution. Without this foresight, organizations risk introducing instability during upgrade cycles.
Automation and Orchestration in Multi-Vendor Networks
Automation is a critical capability in modern network operations, particularly in hybrid environments where manual management becomes impractical at scale. However, automation in multi-vendor ecosystems is inherently more complex than in unified environments.
Each vendor typically provides its own automation framework, API structure, and configuration model. Integrating these systems requires abstraction layers that can translate commands and unify operational logic.
Orchestration platforms are commonly used to manage this complexity. These systems provide centralized control over multiple infrastructure components, enabling automated provisioning, configuration management, and monitoring.
However, orchestration introduces additional dependencies. The reliability of automation workflows depends on the stability of integration layers between systems. Failures in one component can cascade across automated processes.
Despite these challenges, automation is essential for scalability. Without it, operational overhead increases linearly with infrastructure size, making large-scale hybrid environments difficult to manage.
Decision-Making Framework for Network Stack Design
Selecting an appropriate network stack architecture requires a structured decision-making process. This process must consider technical requirements, operational capabilities, financial constraints, and long-term strategic goals.
Organizations must evaluate how much complexity their teams can realistically manage. A highly specialized hybrid environment may offer technical advantages but require advanced engineering expertise.
Conversely, a unified environment may simplify operations but limit flexibility in addressing specialized requirements. The decision is not purely technical but organizational in nature.
Risk tolerance also plays a role. Some organizations prioritize stability and predictability, while others prioritize innovation and performance optimization. These preferences directly influence architectural choices.
Scalability requirements must also be considered. Networks that are expected to grow rapidly or span multiple geographies may benefit from different architectural strategies than static environments.
Strategic Balance in Modern Network Infrastructure
Modern network architecture is fundamentally about balance. No single approach provides universal superiority across all dimensions. Unified stacks offer operational simplicity and predictable behavior. Multi-vendor stacks provide flexibility and optimization potential. Hybrid architectures attempt to combine both approaches in a structured way.
The most successful environments are those that align architectural decisions with operational reality. This means understanding not only technical capabilities but also organizational maturity, skill availability, and long-term business direction.
Network stacks are no longer isolated technical constructs. They are strategic platforms that support digital transformation, security resilience, and business scalability. Their design directly influences how effectively an organization can adapt to technological change and operational demands.
Conclusion
The design of a network stack is ultimately a strategic decision that extends far beyond hardware selection or vendor preference. It represents a long-term architectural commitment that influences how an organization operates, scales, and responds to both technical and business challenges. Whether an enterprise adopts a single-vendor model, a multi-vendor approach, or a hybrid combination, the underlying objective remains the same: to create a stable, secure, and adaptable foundation for digital operations.
At its core, the network stack functions as the connective tissue of modern IT environments. Every application request, authentication event, data transfer, and security control depends on its structure. Because of this, even small architectural decisions can have wide-reaching consequences. A well-designed stack enhances visibility, reduces operational friction, and improves resilience. A poorly designed one introduces inefficiencies that compound over time and become increasingly difficult to correct.
One of the most important takeaways in evaluating network stack strategies is that there is no universally optimal model. The effectiveness of any approach depends heavily on organizational context. Factors such as internal skill sets, regulatory requirements, operational maturity, and infrastructure scale all influence what constitutes a suitable architecture. A design that works well for a centralized enterprise may not be appropriate for a distributed organization with global branch operations.
Single-vendor environments often excel in situations where operational simplicity and predictability are top priorities. By consolidating infrastructure into a unified ecosystem, organizations reduce integration overhead and simplify lifecycle management. This allows IT teams to focus more on operational execution rather than cross-platform troubleshooting. However, this convenience comes with a degree of dependency on a single technology provider, which can limit flexibility over time.
Multi-vendor environments, on the other hand, prioritize specialization and flexibility. By selecting best-in-class components for different layers of the stack, organizations can optimize performance and tailor their infrastructure to specific requirements. This approach is particularly valuable in environments where workloads are diverse or where certain functions require advanced capabilities not available within a single ecosystem. The trade-off is increased complexity, both in integration and ongoing operations.
Hybrid architectures have emerged as the most common real-world implementation because they reflect the practical realities of enterprise growth. Very few organizations build their entire infrastructure from scratch with a single design philosophy and maintain it unchanged over time. Instead, they evolve gradually, incorporating new technologies while retaining existing systems. This leads to layered environments where consistency and specialization must coexist.
In hybrid models, governance becomes the defining success factor. Without clear architectural standards and operational discipline, complexity can quickly spiral out of control. However, when properly managed, hybrid stacks can deliver a balanced combination of stability and flexibility. They allow organizations to preserve core infrastructure investments while still adopting new technologies where they provide measurable value.
Another critical aspect of network stack strategy is operational visibility. As environments become more distributed and multi-layered, the ability to understand system behavior in real time becomes increasingly important. Visibility is not just about monitoring performance metrics; it is about correlating events across systems to understand cause and effect. Architectures that support unified visibility reduce mean time to resolution and improve overall operational efficiency.
Security considerations are equally central to network stack design. Modern threats are no longer confined to external perimeters, and security must be embedded across all layers of the infrastructure. Whether in unified or hybrid environments, consistency in policy enforcement is essential. The more fragmented the stack becomes, the greater the need for coordination between security systems to ensure that no gaps are introduced.
Performance and scalability also play a significant role in architectural decision-making. A network must not only meet current demands but also accommodate future growth. This requires careful planning around throughput capacity, latency sensitivity, and workload distribution. While unified environments often provide predictable scaling patterns, multi-vendor environments may offer more granular performance optimization opportunities when properly engineered.
Operational maturity is another determining factor in choosing the right network strategy. Highly skilled engineering teams may be better equipped to manage the complexity of multi-vendor environments, while smaller or less specialized teams may benefit from the streamlined operations of a unified stack. In either case, alignment between architecture and team capability is essential for long-term success.
Lifecycle management remains an often underestimated aspect of network design. Infrastructure is not static; it evolves continuously through updates, patches, and hardware refresh cycles. Coordinating these changes across a diverse environment requires careful planning. Misalignment between components can introduce instability, while well-orchestrated lifecycle management enhances reliability and reduces risk.
Ultimately, the decision between single-vendor, multi-vendor, or hybrid network stacks should not be viewed as a one-time choice but as an ongoing architectural strategy. As business needs evolve, so too must the supporting infrastructure. Flexibility, governance, and adaptability are more important than rigid adherence to any single model.
A well-designed network stack is one that reflects the operational reality of the organization it supports. It should reduce friction rather than create it, enhance visibility rather than obscure it, and enable growth rather than constrain it. The most successful architectures are those that strike a deliberate balance between simplicity and flexibility, ensuring that the network remains both manageable and capable of evolving with future demands.