Cybersecurity has become one of the most critical priorities in modern IT environments due to the rapid growth of digital transformation across industries. Organizations of all sizes rely on interconnected systems, cloud platforms, and enterprise servers to store, process, and manage sensitive data. A large portion of this infrastructure runs on Linux-based operating systems, making Linux security knowledge an essential requirement for professionals entering the cybersecurity field. Linux systems are widely used in web hosting, cloud computing environments, enterprise servers, DevOps pipelines, and network infrastructure due to their stability, flexibility, and open-source nature. However, this widespread adoption also makes them a frequent target for attackers who exploit misconfigurations, weak authentication mechanisms, and unpatched vulnerabilities. As a result, professionals who understand how Linux systems function at a security level are increasingly valuable in protecting organizational assets and maintaining operational continuity.
Understanding the Role of Entry-Level Security Certifications in Career Development
Entry-level cybersecurity certifications play a significant role in building foundational knowledge for individuals who are new to the IT security domain. These certifications are designed to introduce core principles of system protection, access control, authentication, and threat awareness in a structured manner. Rather than focusing on advanced security architecture, they emphasize practical understanding and real-world application of basic security concepts. This approach allows learners to develop confidence in working with operating systems, particularly Linux, which is commonly used in enterprise environments. By gaining structured exposure to security fundamentals, individuals can prepare themselves for more advanced certifications and specialized roles in cybersecurity, system administration, and cloud infrastructure management.
Introduction to Linux Professional Institute Security Essentials Certification
The Linux Professional Institute Security Essentials certification is designed as an introductory credential aimed at individuals who want to develop foundational skills in Linux system security. It focuses on practical knowledge that can be applied in real IT environments rather than purely theoretical concepts. The certification is developed by a globally recognized organization that promotes vendor-neutral IT education, ensuring that the skills learned are applicable across multiple Linux distributions and enterprise systems. This makes the certification valuable for individuals seeking flexibility in their career paths, as the knowledge gained is not limited to a single technology ecosystem. The certification serves as a stepping stone for individuals aiming to build careers in cybersecurity, system administration, and infrastructure support roles.
Purpose and Learning Approach of the Certification
The primary purpose of this certification is to equip learners with essential security skills that are directly applicable in Linux environments. It introduces fundamental concepts such as system access control, authentication mechanisms, basic cryptography, and network security principles. The learning approach emphasizes practical implementation, allowing individuals to understand how security measures are configured and maintained in real systems. This hands-on focus helps bridge the gap between theoretical knowledge and operational expertise. Instead of simply learning definitions, candidates are encouraged to understand how security controls function within a live system environment, which enhances their problem-solving capabilities and technical awareness.
Importance of Linux in Enterprise and Cloud Environments
Linux has become the backbone of modern IT infrastructure due to its reliability, scalability, and open-source flexibility. It is widely used in cloud computing platforms, enterprise servers, and containerized environments. Major cloud service providers rely heavily on Linux-based systems to deliver scalable and efficient services. This widespread adoption makes Linux security knowledge essential for professionals working in cloud operations, system administration, and cybersecurity roles. Understanding how Linux systems operate allows professionals to secure critical infrastructure, manage system configurations, and respond effectively to security incidents. Since many cybersecurity tools and frameworks are also built on Linux, familiarity with the operating system provides a significant advantage in security operations and threat analysis.
Core Security Principles in Linux Environments
Linux security is built upon several foundational principles that govern how systems are protected and managed. These include authentication, authorization, access control, and encryption. Authentication ensures that users are properly identified before accessing a system. Authorization determines what actions users are permitted to perform based on their roles and privileges. Access control mechanisms enforce restrictions on system resources to prevent unauthorized usage. Encryption protects sensitive data by converting it into secure formats that cannot be easily interpreted without proper authorization. These principles work together to create a secure operating environment that minimizes the risk of unauthorized access and data breaches.
User Management and Access Control Fundamentals
User management is a critical aspect of Linux security, as it determines how individuals interact with system resources. Proper configuration of user accounts ensures that only authorized personnel have access to sensitive data and system functions. The principle of least privilege is commonly applied in Linux environments, meaning users are granted only the permissions necessary to perform their tasks. This reduces the risk of accidental or malicious system changes. Group management also plays an important role in organizing users and assigning permissions efficiently. Understanding how to create, modify, and manage user accounts is essential for maintaining system security and operational integrity.
Introduction to Network Security Concepts in Linux Systems
Network security is an essential component of Linux system protection, especially in environments where systems are connected to external networks. It involves controlling data flow, securing communication channels, and monitoring network activity for suspicious behavior. Firewalls are commonly used to regulate incoming and outgoing traffic based on predefined security rules. These rules help prevent unauthorized access and reduce exposure to potential threats. Network security also includes identifying intrusion attempts, monitoring unusual traffic patterns, and securing remote access connections. Understanding these concepts is crucial for maintaining secure communication between systems in enterprise and cloud environments.
Foundational Cryptography in System Security
Cryptography plays a vital role in protecting data within Linux systems. It ensures that sensitive information remains secure during storage and transmission by converting it into unreadable formats without proper authorization. Hashing techniques are used to securely store passwords, while encryption methods protect files and communication channels. Although the certification does not focus on advanced cryptographic engineering, it introduces essential concepts that help learners understand how data protection works at a fundamental level. This knowledge is important for ensuring confidentiality, integrity, and security in digital systems.
System Monitoring and Security Awareness Practices
Monitoring system activity is a key aspect of maintaining security in Linux environments. System logs provide detailed records of user actions, system events, and potential security incidents. By analyzing these logs, administrators can identify unusual behavior that may indicate unauthorized access or malicious activity. Security awareness involves understanding common attack methods such as brute force attacks, privilege escalation, and unauthorized access attempts. Developing the ability to interpret system behavior and respond to potential threats is an important skill for maintaining secure systems. Continuous monitoring helps organizations detect and mitigate risks before they escalate into serious security incidents.
Practical Application of Security Knowledge in Real Systems
One of the most important aspects of Linux security training is the application of knowledge in real-world environments. Practical experience allows learners to understand how security configurations are implemented and tested in actual systems. This includes setting up secure remote access, configuring user permissions, managing authentication systems, and implementing basic security policies. Hands-on practice helps reinforce theoretical concepts and improve technical proficiency. Working with real systems also enhances problem-solving skills, allowing learners to adapt to different security challenges they may encounter in professional environments.
Career Relevance of Linux Security Skills
Linux security skills are highly relevant in a wide range of IT career paths. Entry-level positions in system administration, cybersecurity analysis, and infrastructure support often require familiarity with Linux systems. Professionals who understand Linux security principles are better equipped to manage system configurations, monitor security events, and respond to incidents. As experience grows, these foundational skills can support advancement into more specialized roles such as security engineering, DevSecOps, and cloud security architecture. The demand for professionals with Linux security expertise continues to increase as organizations expand their reliance on digital infrastructure.
Value of Vendor-Neutral Knowledge in IT Security
Vendor-neutral knowledge is highly valuable in the IT industry because it focuses on universal principles rather than specific technologies. Linux security concepts remain consistent across different distributions, making the knowledge applicable in a variety of environments. This flexibility allows professionals to adapt to different systems and technologies without being restricted to a single platform. Vendor-neutral certifications also provide a broader understanding of security principles, which can be applied across multiple industries and job roles. This adaptability increases career opportunities and enhances long-term professional growth in the cybersecurity field.
Building a Foundation for Advanced Cybersecurity Learning
Entry-level Linux security knowledge serves as a foundation for more advanced cybersecurity studies and certifications. Understanding basic security principles makes it easier to transition into more complex topics such as advanced threat detection, security architecture, and incident response. As professionals gain experience, they can build upon these foundational skills to pursue higher-level certifications and specialized roles. The structured learning path provided by entry-level certifications helps individuals gradually develop expertise in cybersecurity while gaining practical experience in real-world environments.
Understanding the Structure of the Linux Security Essentials Exam
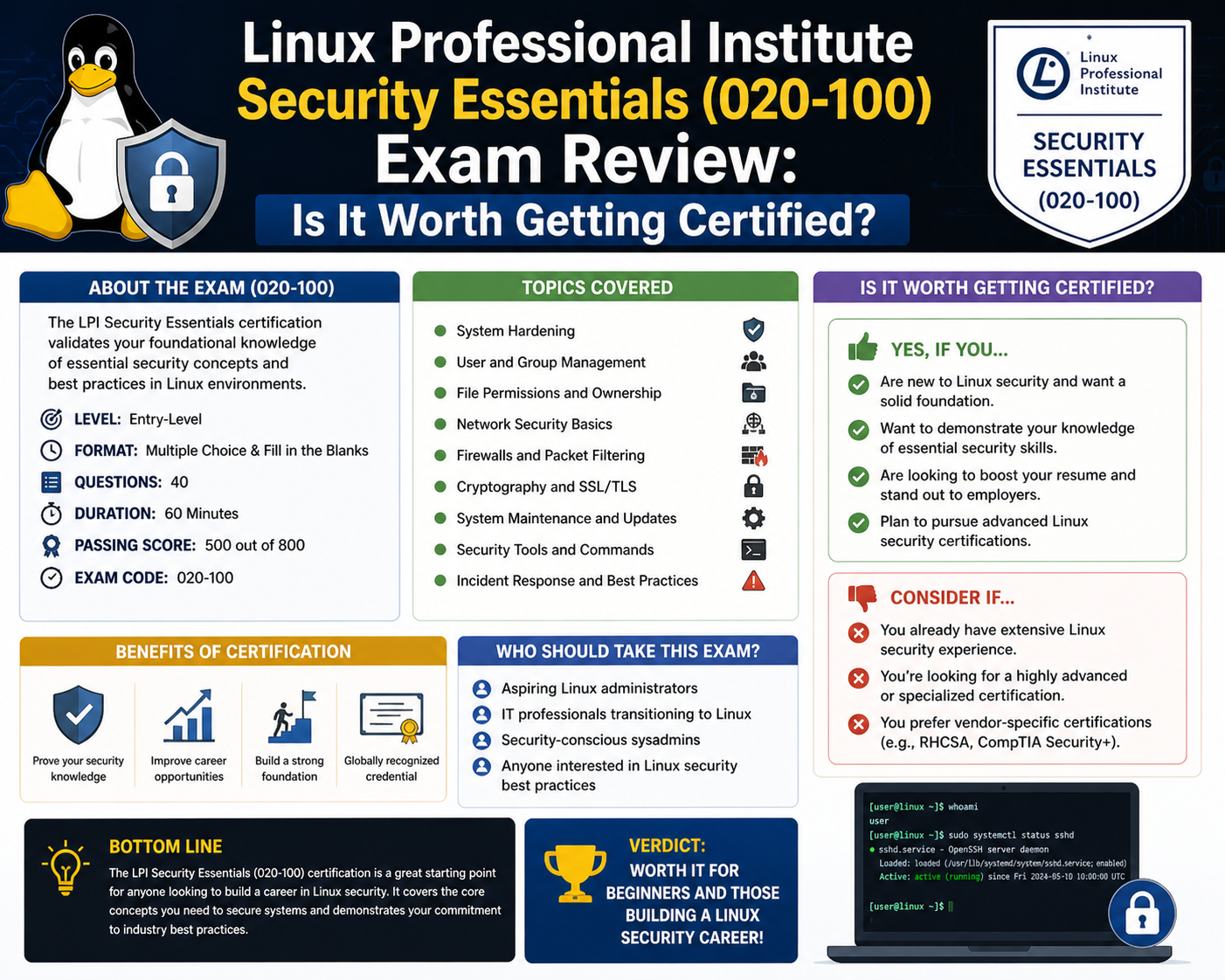
The Linux Security Essentials certification exam is designed to evaluate foundational knowledge of Linux system security through a structured assessment format. It focuses on a practical understanding of essential security concepts rather than advanced theoretical modeling. The exam typically consists of multiple-choice questions that test a candidate’s ability to recognize security principles, interpret system behavior, and apply basic security configurations in Linux environments. The time constraint requires candidates to demonstrate not only knowledge but also efficiency in analyzing and responding to security-related scenarios. The structure is intentionally designed to reflect real-world situations where security professionals must make quick and accurate decisions based on system conditions and operational requirements.
The exam format emphasizes clarity and precision in understanding Linux security fundamentals. Candidates are expected to demonstrate familiarity with system access control, authentication methods, network protection techniques, and basic cryptographic principles. Each question is designed to assess applied knowledge rather than memorization, ensuring that individuals who pass the exam have practical awareness of how Linux systems are secured in operational environments.
Key Knowledge Areas Covered in the Certification
The certification syllabus is divided into major knowledge domains that represent the core areas of Linux security. These domains are structured to ensure a balanced understanding of system administration, network protection, and security operations. Each domain contributes to building a foundational skill set that can be applied in real-world IT environments.
The first major domain focuses on system security fundamentals, which includes understanding how Linux systems manage users, permissions, and access rights. The second domain focuses on network security principles, which involve securing communication channels and managing traffic flow through system configurations. The third domain emphasizes security operations, which include monitoring systems, analyzing logs, and responding to potential security incidents. These domains collectively ensure that learners develop a comprehensive understanding of Linux security at a foundational level.
System and Network Security Fundamentals
System and network security form the backbone of Linux security operations. In this area, candidates are expected to understand how systems can be protected from unauthorized access and external threats. System security involves configuring operating system settings to ensure that only authorized users can interact with critical resources. This includes managing system updates, controlling service access, and securing administrative functions.
Network security focuses on protecting data as it moves between systems. Linux environments often rely on network communication for remote access, file sharing, and application deployment. Securing these communication channels is essential to prevent interception, tampering, or unauthorized access. Firewalls play a key role in this process by controlling incoming and outgoing traffic based on predefined rules. Understanding how these rules are configured and applied is a critical part of the certification.
Access Control and Authentication Mechanisms
Access control is one of the most important components of Linux security. It determines how users interact with system resources and what level of access they are granted. Authentication ensures that users are correctly identified before gaining access to a system, while authorization defines what actions they are permitted to perform. These two mechanisms work together to enforce system security policies.
Linux systems use a structured permission model that assigns access rights to users, groups, and system resources. Understanding how these permissions are configured is essential for maintaining secure environments. Misconfigured access controls are one of the most common causes of security breaches in enterprise systems. The certification emphasizes practical understanding of how to manage user accounts, configure permissions, and enforce security policies effectively.
Security Operations and System Monitoring
Security operations involve continuous monitoring of system activity to detect and respond to potential threats. Linux systems generate logs that record detailed information about user actions, system processes, and network activity. These logs are essential for identifying suspicious behavior and diagnosing security incidents.
Monitoring tools allow administrators to track system performance and detect anomalies that may indicate unauthorized access attempts. Security operations also include implementing backup and recovery procedures to ensure data integrity in the event of a system failure or security breach. Understanding how to interpret log data and respond to security alerts is a key skill evaluated in the certification.
Cryptography and Data Protection Concepts
Cryptography plays a fundamental role in securing Linux systems by protecting data from unauthorized access. It involves techniques such as encryption and hashing, which ensure that sensitive information remains secure even if intercepted. Encryption converts readable data into encoded formats that can only be decoded with the correct key, while hashing is used to securely store passwords and verify data integrity.
The certification introduces basic cryptographic principles to help learners understand how data protection is implemented in Linux environments. While it does not focus on advanced cryptographic algorithms, it provides sufficient knowledge to understand how encryption supports system security. This foundational understanding is important for working with secure communication protocols and data storage systems.
Practical System Hardening Techniques
System hardening refers to the process of securing a Linux system by reducing its vulnerability to attacks. This involves disabling unnecessary services, configuring secure access settings, and applying system updates regularly. Hardening also includes securing remote access mechanisms, such as SSH, to prevent unauthorized login attempts.
Proper system hardening ensures that the attack surface of a system is minimized. This reduces the number of potential entry points that attackers can exploit. The certification emphasizes practical approaches to system hardening, allowing learners to understand how security configurations are applied in real environments. This includes managing firewall settings, configuring secure user access, and applying security patches.
Network Protection and Secure Communication
Securing network communication is a critical aspect of Linux system administration. Network protection involves controlling how data is transmitted between systems and ensuring that unauthorized users cannot intercept or modify communications. Linux systems use various tools and configurations to secure network traffic, including firewalls, secure shell protocols, and virtual private networks.
Understanding how these tools function is essential for maintaining secure communication channels. Firewalls are used to define rules that control network traffic, while secure shell protocols provide encrypted remote access to systems. Virtual private networks create secure tunnels for data transmission over public networks. These tools collectively help ensure that Linux systems remain protected in connected environments.
Role of Logs and System Auditing in Security Management
System logs provide a detailed record of activities within a Linux environment. These logs are essential for auditing system behavior and identifying potential security incidents. They record information such as login attempts, system errors, and configuration changes.
System auditing involves reviewing these logs to detect unusual patterns or unauthorized activities. This process helps security professionals identify potential threats before they escalate into serious issues. The certification emphasizes the importance of understanding how logs are generated, stored, and analyzed. This knowledge is critical for maintaining system transparency and accountability in enterprise environments.
Hands-On Learning and Practical Skill Development
Practical experience plays a central role in mastering Linux security concepts. The certification encourages learners to work with real or simulated Linux environments to apply security configurations and test system behavior. Hands-on learning helps reinforce theoretical concepts and improve technical proficiency.
Setting up a practice environment allows learners to experiment with user management, network configurations, and security settings without risking production systems. This approach helps build confidence and ensures that learners are prepared to handle real-world security challenges. Practical exposure also improves problem-solving skills and enhances understanding of system interactions.
Importance of Practice Environments in Skill Building
Practice environments, such as virtual machines or isolated systems, provide a safe space for experimenting with Linux security configurations. These environments allow learners to test different scenarios, such as configuring firewalls, managing user permissions, and analyzing system logs.
Working in a controlled environment helps individuals understand how security settings impact system behavior. It also allows them to make mistakes and learn from them without affecting live systems. This experiential learning approach is essential for developing practical security skills that can be applied in professional settings.
Time Management and Study Strategy for Exam Preparation
Effective preparation for the Linux Security Essentials exam requires structured time management and consistent study practices. Candidates are encouraged to allocate dedicated study hours each week to cover different domains of the syllabus. Breaking down the content into manageable sections helps improve retention and understanding.
A balanced study strategy includes theoretical learning, hands-on practice, and review sessions. Theoretical learning helps build foundational knowledge, while practical exercises reinforce applied skills. Review sessions allow candidates to identify weak areas and strengthen their understanding. Consistent practice ensures that learners are well-prepared for the exam format and time constraints.
Understanding Question Patterns and Exam Logic
The exam questions are designed to test conceptual understanding and practical reasoning. Candidates may be presented with scenarios that require them to identify security issues or select appropriate configurations. Understanding the logic behind these questions is more important than memorizing specific answers.
Familiarity with Linux system behavior helps candidates interpret questions accurately and choose the most appropriate solutions. This includes understanding how permissions work, how network traffic is controlled, and how system logs are interpreted. Developing this analytical approach improves performance in exam conditions and enhances overall technical competence.
Building Confidence Through Continuous Practice
Confidence plays an important role in exam success. Continuous practice helps reinforce knowledge and improve familiarity with Linux systems. Regular exposure to system configurations, security settings, and troubleshooting scenarios builds confidence in handling exam questions effectively.
As learners progress through their preparation, they become more comfortable with Linux commands and system behavior. This confidence translates into better decision-making during the exam and improved ability to apply knowledge in real-world environments.
Real-World Career Applications of Linux Security Essentials Skills
Linux security skills have become deeply embedded in modern IT job roles because of the widespread use of Linux systems across enterprise infrastructure, cloud platforms, and cybersecurity operations centers. Organizations rely heavily on professionals who can manage, secure, and troubleshoot Linux environments, especially as digital transformation increases dependency on distributed systems and remote infrastructure. The knowledge gained from the Linux Security Essentials certification directly applies to entry-level and junior roles where a foundational security understanding is required to support system stability and protect organizational assets.
In system administration roles, Linux security knowledge is applied to daily operational tasks such as managing user accounts, configuring permissions, maintaining system updates, and ensuring secure access to servers. Administrators are responsible for ensuring that systems remain secure against unauthorized access and configuration errors. This includes monitoring system logs, applying security patches, and managing authentication mechanisms. These tasks require a strong understanding of how Linux systems enforce security policies at the operating system level.
In cybersecurity-focused roles, Linux security knowledge supports activities such as monitoring system behavior, analyzing security alerts, and identifying potential threats. Security analysts often work in environments where Linux servers generate large volumes of log data, which must be interpreted to detect suspicious activity. Understanding how Linux systems record events and manage access control allows analysts to identify anomalies more effectively and respond to potential security incidents promptly.
In cloud computing environments, Linux security skills are even more critical. Most cloud platforms rely on Linux-based virtual machines and containerized systems to run applications and services. Professionals working in cloud operations must understand how to secure instances, configure network access rules, and manage authentication systems. This includes controlling access to cloud resources, securing remote connections, and ensuring compliance with organizational security policies. Linux Security Essentials provides a foundational understanding that supports these responsibilities.
DevOps and DevSecOps roles also benefit significantly from Linux security knowledge. These roles involve integrating security practices into software development and deployment pipelines. Professionals must ensure that applications are securely configured before deployment and that infrastructure remains protected throughout its lifecycle. Linux systems are commonly used in automated deployment pipelines, making security awareness essential for maintaining secure continuous integration and continuous delivery environments.
Industry Relevance and Demand for Linux Security Professionals
The demand for Linux security professionals continues to grow as organizations expand their reliance on cloud computing, virtualization, and distributed systems. Nearly every major industry, including finance, healthcare, telecommunications, and e-commerce, relies on Linux-based infrastructure to support critical operations. This widespread adoption has created a strong demand for professionals who understand how to secure and maintain Linux systems.
Cybersecurity threats have also become more sophisticated, increasing the need for professionals who can identify vulnerabilities and implement effective security measures. Attackers often target misconfigured systems, weak authentication mechanisms, and unpatched vulnerabilities in Linux environments. As a result, organizations prioritize hiring individuals who understand how Linux systems operate and how to secure them effectively.
Linux Security Essentials aligns with this demand by providing foundational knowledge that supports entry into cybersecurity and IT infrastructure roles. While it is not an advanced certification, it helps individuals develop the baseline skills required to contribute to security operations teams. Employers often value candidates who demonstrate a practical understanding of Linux systems because it reduces onboarding time and improves operational efficiency.
The certification is also relevant in environments where organizations use hybrid infrastructures combining on-premises systems and cloud-based services. In such environments, Linux often serves as the underlying operating system for servers, containers, and virtual machines. Professionals who understand Linux security principles are better equipped to manage these complex environments and ensure consistent security practices across different platforms.
Comparison with Other Entry-Level Security Certifications
When evaluating the value of Linux Security Essentials, it is useful to compare it with other entry-level cybersecurity certifications that focus on general security principles. Many entry-level certifications cover broad security concepts such as risk management, network security, and compliance frameworks. These certifications provide a general overview of cybersecurity but may not focus deeply on specific operating systems.
Linux Security Essentials differs by focusing specifically on Linux environments and practical system-level security. This specialization makes it particularly valuable for individuals who plan to work in Linux-heavy environments such as cloud infrastructure, DevOps pipelines, and server administration roles. While general security certifications provide a broader overview of cybersecurity principles, Linux Security Essentials offers more targeted knowledge for system-level security tasks.
Compared to general cybersecurity certifications, Linux Security Essentials places greater emphasis on hands-on system configuration and operational security tasks. This includes managing user permissions, configuring secure services, and analyzing system logs. These practical skills are directly applicable in technical roles where Linux systems are actively managed and maintained.
Some certifications focus heavily on theoretical knowledge and security frameworks, which are important for understanding cybersecurity strategy and governance. However, Linux Security Essentials focuses more on technical implementation and system administration tasks. This makes it more suitable for individuals who prefer hands-on technical roles rather than purely analytical or managerial positions.
Positioning in the Cybersecurity Certification Pathway
Linux Security Essentials is best understood as a foundational certification within a broader cybersecurity learning pathway. It provides the initial knowledge required to progress toward more advanced certifications and specialized roles. Individuals who complete this certification often move on to intermediate and advanced certifications that cover deeper aspects of Linux administration, security engineering, and enterprise-level cybersecurity practices.
As professionals gain experience, they may pursue certifications that focus on advanced system administration, security architecture, or incident response. These advanced certifications build upon the foundational knowledge established through entry-level certifications like Linux Security Essentials. The progression typically involves moving from basic system understanding to advanced threat detection, security design, and infrastructure protection strategies.
This structured learning path allows professionals to gradually develop expertise in cybersecurity while gaining practical experience in real-world environments. Linux Security Essentials serves as the starting point for this journey by introducing essential concepts that are widely used across the industry.
Long-Term Value of Linux Security Knowledge in IT Careers
The long-term value of Linux security knowledge lies in its broad applicability across multiple IT disciplines. As organizations continue to adopt cloud-native architectures and distributed systems, Linux remains a core component of their infrastructure. This ensures that Linux security skills remain relevant over time, regardless of changes in technology trends.
Professionals with Linux security knowledge are better equipped to adapt to evolving IT environments because they understand the underlying principles of system security. This includes understanding how systems authenticate users, manage permissions, and protect data. These foundational concepts remain consistent even as technologies evolve.
In long-term career development, Linux security skills provide a strong foundation for specialization. Professionals may choose to focus on areas such as cloud security, penetration testing, incident response, or infrastructure engineering. Each of these areas requires a solid understanding of Linux systems, making foundational knowledge essential for career growth.
Salary Impact and Career Growth Potential
While entry-level certifications do not guarantee specific salary outcomes, Linux security knowledge can positively influence earning potential by improving job eligibility and career progression opportunities. Individuals with Linux security skills are often eligible for roles in system administration, security analysis, and IT support, which serve as entry points into higher-paying cybersecurity positions.
As professionals gain experience and combine Linux security knowledge with additional certifications and practical skills, they become eligible for more advanced roles such as security engineer, cloud security specialist, and DevSecOps engineer. These roles typically offer higher compensation due to their technical complexity and responsibility.
The salary impact of Linux security knowledge also depends on factors such as geographic location, industry demand, and organizational size. However, the foundational skills provided by Linux Security Essentials contribute to long-term career advancement by enabling access to technical roles that serve as stepping stones toward higher-paying positions.
Integration with Cloud and Modern Infrastructure Technologies
Modern IT environments are increasingly built around cloud computing, virtualization, and containerization technologies. Linux plays a central role in all of these areas, making Linux security knowledge highly relevant. Cloud platforms rely heavily on Linux-based virtual machines and container orchestration systems to deploy and manage applications.
Understanding how to secure Linux systems is essential for managing cloud infrastructure effectively. This includes configuring secure access controls, managing network security settings, and ensuring that cloud instances are properly hardened against potential threats. Linux Security Essentials provides a foundation for understanding these concepts in a practical context.
Containerization technologies also rely on Linux at their core. Containers are used to package and deploy applications in isolated environments, and securing these environments requires knowledge of Linux system behavior. Professionals who understand Linux security principles are better equipped to manage container security and ensure safe application deployment.
Evolving Role of Linux Security in Future IT Landscapes
As technology continues to evolve, Linux security will remain a critical component of IT infrastructure management. The increasing adoption of automation, artificial intelligence, and distributed computing systems will further increase the importance of secure Linux environments. Organizations will continue to rely on Linux systems to support scalable and efficient operations.
The role of Linux security professionals is expected to expand as systems become more complex and interconnected. Security challenges will continue to evolve, requiring professionals who understand both traditional system administration and modern cloud-based architectures. Foundational knowledge gained through certifications like Linux Security Essentials will remain relevant as a starting point for adapting to these changes.
Professional Growth Through Continuous Learning and Experience
Career development in cybersecurity requires continuous learning and practical experience. Linux Security Essentials provides the initial foundation, but long-term success depends on building additional skills and gaining hands-on experience in real environments. Professionals who actively engage with Linux systems, explore security tools, and participate in practical environments develop stronger technical capabilities over time.
As individuals progress in their careers, they often expand their knowledge into specialized areas such as threat intelligence, security architecture, and infrastructure automation. Each of these areas builds upon foundational Linux security knowledge, reinforcing the importance of starting with a strong technical base.
The ability to adapt to new technologies and security challenges is a key factor in long-term career success. Linux Security Essentials helps establish this adaptability by teaching fundamental principles that remain relevant across different technologies and industry changes.
Conclusion
The Linux Professional Institute Security Essentials certification represents more than an entry-level credential; it functions as a structured introduction to the operational side of cybersecurity within Linux-based environments. In modern IT ecosystems, where Linux underpins a large portion of cloud infrastructure, enterprise servers, and DevOps pipelines, foundational security knowledge is not optional but essential. This certification helps bridge the gap between theoretical cybersecurity awareness and practical system-level competence, enabling learners to understand how security is implemented, maintained, and enforced in real environments.
One of the most important outcomes of pursuing Linux Security Essentials is the development of a practical mindset toward system security. Many beginners in cybersecurity start with conceptual knowledge of threats, vulnerabilities, and risk management, but struggle to translate that understanding into real-world actions. This certification addresses that gap by focusing on how Linux systems actually behave under normal and adversarial conditions. It introduces learners to the mechanisms that control access, manage users, protect data, and monitor system activity. These are not abstract ideas but active components of every production environment that relies on Linux.
Another key strength of this certification lies in its emphasis on vendor-neutral Linux knowledge. In professional environments, organizations rarely rely on a single Linux distribution. Instead, they operate hybrid infrastructures that may include Ubuntu servers, Red Hat systems, Debian-based environments, and cloud-native Linux instances. A vendor-neutral foundation ensures that learners are not limited to one ecosystem and can adapt their skills across different platforms. This adaptability is especially important in cloud computing environments, where infrastructure is dynamic, distributed, and often abstracted from the underlying operating system.
The certification also plays a significant role in career entry pathways. For individuals entering IT or cybersecurity for the first time, it provides a structured starting point that helps reduce uncertainty about what to learn and how to apply knowledge. Entry-level roles in system administration, technical support, security monitoring, and infrastructure operations often require familiarity with Linux fundamentals. By completing this certification, learners demonstrate that they understand core operational security principles, which can improve employability and readiness for technical responsibilities.
Beyond entry-level roles, Linux Security Essentials serves as a stepping stone toward more advanced cybersecurity careers. The knowledge gained provides a foundation for progressing into certifications and disciplines that require deeper technical expertise. Areas such as penetration testing, incident response, cloud security, and security engineering all rely on an understanding of Linux systems at a fundamental level. Without this foundation, advanced topics become significantly harder to grasp because they build on the same principles of access control, system architecture, and network security.
The real-world relevance of Linux security skills continues to increase as organizations expand their reliance on digital infrastructure. Cloud computing platforms, which dominate modern IT operations, are heavily dependent on Linux-based systems. Virtual machines, containers, orchestration platforms, and serverless environments all rely on Linux at their core. This means that professionals who understand Linux security are better positioned to manage and protect these environments effectively. They can configure secure access policies, monitor system behavior, and respond to security incidents with greater confidence and accuracy.
Another important aspect of this certification is its focus on practical implementation rather than purely theoretical learning. Many cybersecurity learning paths emphasize frameworks, policies, and high-level concepts without providing sufficient exposure to system-level operations. Linux Security Essentials takes a different approach by encouraging learners to understand how security controls are applied in real systems. This includes managing user permissions, configuring authentication mechanisms, securing remote access, and analyzing system logs. These are hands-on skills that directly translate into workplace responsibilities.
The importance of system monitoring and log analysis cannot be overstated. In real-world cybersecurity operations, logs are one of the primary sources of truth for understanding system behavior. They provide detailed records of user activity, system processes, and potential security incidents. Learning how to interpret these logs allows professionals to detect anomalies, identify unauthorized access attempts, and investigate security events. This capability is essential in roles such as security operations center analysis and system administration.
In addition to technical skills, the certification encourages the development of analytical thinking. Security professionals must constantly evaluate system behavior, identify risks, and determine appropriate responses. This requires not only technical knowledge but also the ability to interpret patterns and make informed decisions under time constraints. By exposing learners to real-world scenarios, Linux Security Essentials helps develop this analytical mindset early in the learning process.
From a career development perspective, the certification also provides long-term flexibility. Because Linux is used across multiple industries and technologies, the skills gained are transferable across different job roles. Whether working in cloud computing, cybersecurity, DevOps, or traditional IT infrastructure, Linux security knowledge remains relevant. This flexibility allows professionals to shift between roles and industries without needing to completely retrain their foundational skills.
The certification also supports continuous learning and professional growth. It does not represent a final destination but rather an initial step in a broader learning journey. As individuals gain experience, they can build upon this foundation by exploring advanced topics such as system hardening, network defense, intrusion detection, and security architecture. Each of these areas expands upon the core principles introduced in the certification, reinforcing its long-term educational value.
Another important consideration is the increasing complexity of modern cyber threats. Attackers today use sophisticated techniques that target misconfigured systems, weak authentication methods, and unpatched vulnerabilities. Linux environments are often targeted because of their widespread use in critical infrastructure. Understanding how to secure these systems is therefore not just beneficial but necessary for maintaining operational security in real-world environments.
The certification also helps learners understand the importance of proactive security practices. Instead of reacting to security incidents after they occur, professionals are encouraged to implement preventive measures such as access control policies, system hardening, and continuous monitoring. This proactive approach is a core principle of modern cybersecurity and is essential for reducing risk exposure in enterprise environments.
In the broader context of IT careers, Linux Security Essentials contributes to building a strong technical foundation that supports long-term professional success. It equips learners with the ability to understand complex systems, apply security controls, and respond to operational challenges. These capabilities are highly valued in the job market and form the basis for more advanced technical roles.
Ultimately, the value of this certification lies in its ability to transform beginners into competent practitioners who understand how Linux systems operate in secure environments. It provides the essential building blocks required to navigate the increasingly complex world of cybersecurity and IT infrastructure. While it is not an advanced certification, its importance should not be underestimated, as it lays the groundwork for everything that follows in a cybersecurity career path.