Information security managers play a central and increasingly strategic role in modern organizations where digital infrastructure forms the backbone of almost every business operation. As companies continue to expand their reliance on cloud computing, distributed systems, remote work environments, and data-driven decision-making, the responsibility of protecting sensitive information has become more complex and more critical than ever before. These professionals are no longer limited to technical oversight; they are now key decision-makers in enterprise risk management, operational resilience, and long-term cybersecurity strategy.
In today’s digital economy, information security managers act as guardians of organizational trust. Every transaction, communication, and data exchange within a company depends on secure systems functioning correctly. A single vulnerability can lead to financial loss, reputational damage, legal consequences, and operational disruption. Because of this, organizations rely heavily on security managers to design, implement, and continuously improve security frameworks that protect both internal systems and external-facing platforms.
The role requires an ability to understand both technology and business operations simultaneously. Security managers must interpret technical risks in a way that business leaders can understand, while also ensuring that business decisions do not compromise security integrity. This dual responsibility makes the position one of the most interdisciplinary roles in modern IT leadership structures.
Strategic Importance of Information Security Management in Organizations
Information security management is fundamentally about ensuring the long-term stability and trustworthiness of digital systems. The core objective is to protect three essential principles: confidentiality, integrity, and availability of information. Confidentiality ensures that sensitive data is accessible only to authorized individuals. Integrity ensures that data remains accurate and unaltered. Availability ensures that systems and data are accessible whenever needed by legitimate users.
In modern enterprises, these principles extend beyond technical systems and directly influence business performance. For example, a breach of customer data can result in financial penalties, regulatory scrutiny, and loss of customer trust. Similarly, system downtime caused by cyberattacks can halt operations and lead to significant revenue loss. Information security managers are responsible for preventing these outcomes through structured security planning and continuous monitoring.
They also play a key advisory role in executive decision-making. Senior leadership depends on their expertise to understand cyber risk exposure, evaluate security investments, and prioritize risk mitigation strategies. This makes them an essential link between technical cybersecurity teams and business leadership.
Evolution of the Information Security Manager Role
The role of information security managers has evolved dramatically over the past decade due to rapid technological advancements and the increasing sophistication of cyber threats. In earlier IT environments, cybersecurity was primarily focused on perimeter defense mechanisms such as firewalls, antivirus systems, and basic intrusion detection tools. Security was largely reactive, addressing threats after they occurred.
However, the modern digital landscape has fundamentally changed this approach. Organizations now operate in highly distributed environments that include cloud platforms, mobile devices, remote employees, third-party vendors, and interconnected applications. This complexity has made traditional security models insufficient.
As a result, information security managers now adopt proactive and predictive security strategies. Instead of simply responding to threats, they focus on identifying vulnerabilities before they are exploited. This includes implementing continuous monitoring systems, threat intelligence platforms, and advanced risk assessment frameworks.
Additionally, the rise of regulatory compliance requirements has expanded the scope of the role. Security managers must now ensure adherence to data protection laws, industry regulations, and internal governance policies. This has transformed the role into a hybrid discipline that combines technical cybersecurity expertise, legal awareness, and strategic business alignment.
Organizational Structure and Reporting Relationships
Information security managers typically operate within IT departments or dedicated cybersecurity divisions, depending on the size and maturity of the organization. In smaller companies, they may report directly to the Chief Information Officer, while in larger enterprises, they often report to a Chief Information Security Officer or equivalent executive role.
Their position within the organizational hierarchy reflects their dual responsibility. On one hand, they oversee operational cybersecurity functions such as monitoring, incident response, and vulnerability management. On the other hand, they contribute to strategic planning by advising leadership on risk exposure and security investments.
In many organizations, security managers oversee dedicated teams responsible for different aspects of cybersecurity. These teams may include incident response units, security analysts, compliance officers, and infrastructure security specialists. The manager ensures that all teams work cohesively and align with organizational objectives.
They also interact frequently with non-technical departments such as legal, finance, human resources, and executive leadership. This cross-functional communication is essential for integrating security practices into every aspect of the business.
Core Responsibilities in Security Operations Management
One of the most critical responsibilities of an information security manager is overseeing daily security operations. This includes monitoring systems for suspicious activity, managing security incidents, and ensuring that organizational policies are consistently enforced.
Security managers are responsible for developing and implementing security policies that govern how data is accessed, stored, transmitted, and protected. These policies define acceptable use standards, access control rules, encryption requirements, and authentication procedures. By establishing clear guidelines, they reduce the risk of human error and system misconfiguration.
They also oversee vulnerability management programs that continuously scan systems for weaknesses. These vulnerabilities may arise from outdated software, misconfigured systems, or unpatched security flaws. Once identified, security managers prioritize remediation efforts based on risk severity and potential business impact.
Incident response is another essential function. When a security breach occurs, managers lead coordinated response efforts to contain the threat, investigate its cause, and restore normal operations. This requires rapid decision-making, cross-team coordination, and effective communication under pressure.
Regulatory Compliance and Security Governance
Compliance management is a major component of the information security manager role, especially in industries that handle sensitive data or operate under strict regulatory frameworks. Organizations must comply with a wide range of standards that govern data protection, privacy, financial transactions, and operational security.
Security managers ensure compliance by implementing structured governance frameworks, conducting regular audits, and maintaining detailed documentation of security processes. These activities help demonstrate that the organization is meeting legal and industry requirements.
Governance also involves establishing accountability structures and decision-making processes for cybersecurity-related issues. This ensures that security decisions are consistent, transparent, and aligned with organizational objectives.
Leadership Responsibilities and Security Culture Development
Beyond technical responsibilities, information security managers play a vital role in shaping organizational culture. Cybersecurity is not solely dependent on technology; human behavior is one of the most significant factors influencing security outcomes.
Security managers are responsible for developing awareness programs that educate employees about security risks such as phishing attacks, password management, and data handling procedures. These programs help reduce the likelihood of human error and strengthen overall organizational defenses.
Leadership responsibilities also include managing security teams, developing talent, and ensuring collaboration across departments. Security managers must allocate responsibilities, monitor performance, and ensure that teams have the necessary resources to perform effectively.
Communication with executive leadership is another critical aspect of the role. Security managers must present complex technical risks in clear business terms, enabling informed decision-making at the highest levels of the organization.
Technical Expertise and Security Architecture Knowledge
Although the role is managerial in nature, strong technical expertise remains essential. Information security managers must understand network security, cloud infrastructure, identity management systems, encryption technologies, and threat detection mechanisms.
They are also responsible for evaluating and maintaining security architecture across the organization. This includes ensuring that systems are designed with multiple layers of defense and that security controls are properly integrated into infrastructure design.
As organizations increasingly adopt cloud and hybrid environments, security managers must ensure that protection extends across all platforms without gaps in visibility or control.
Integration of Security with Business Strategy
Modern information security management is deeply integrated into business strategy. Security is no longer treated as a separate technical function but as a core component of organizational planning and decision-making.
Security managers contribute to strategic discussions by identifying risks that could impact business goals and recommending solutions that balance protection with operational efficiency. This ensures that security initiatives support rather than hinder innovation and growth.
Their role continues to expand as organizations become more digitally dependent, making information security management one of the most critical leadership functions in modern enterprises.
Global Salary Landscape for Information Security Managers
Compensation for information security managers reflects the increasing global dependence on digital infrastructure, cloud computing ecosystems, and enterprise-scale data systems. As organizations expand their digital operations across multiple platforms and manage growing volumes of sensitive data, the demand for experienced cybersecurity leadership continues to rise. This growing dependence on digital systems has positioned information security managers as essential personnel within both private and public sector organizations.
Salary structures for this role vary widely across global markets, and the differences are largely influenced by economic development, cybersecurity maturity, regulatory pressure, and industry reliance on digital systems. Developed economies with advanced technological ecosystems tend to offer significantly higher salaries due to the complexity of infrastructure and the high cost of cyber risk exposure. In these regions, organizations operate large-scale digital systems that require constant monitoring, risk evaluation, and strategic security planning.
In contrast, developing economies may offer lower nominal salaries, but these are often balanced by lower living costs and rapidly growing demand for cybersecurity professionals. Many organizations in these regions are currently undergoing digital transformation, which is gradually increasing investment in cybersecurity leadership roles. As a result, salary growth in emerging markets is expected to continue rising steadily over time.
Regional Salary Differences and Economic Influences
Geographic location remains one of the most significant factors affecting compensation for information security managers. Major metropolitan areas that serve as global financial centers or technology hubs consistently offer higher salaries due to the concentration of high-value data operations and increased exposure to cyber threats.
In these regions, organizations face constant pressure to maintain strong cybersecurity frameworks due to regulatory requirements, customer expectations, and competitive market dynamics. This leads to higher investment in security leadership roles capable of managing complex infrastructures and responding to advanced threats in real time.
Mid-tier cities with growing technology ecosystems also provide competitive compensation, though typically at slightly lower levels compared to major hubs. These locations are increasingly attractive to professionals due to their balance of strong career opportunities and relatively lower living expenses. Many companies in these regions are expanding their digital operations, which is driving increased demand for experienced cybersecurity managers.
Smaller cities and rural regions tend to offer lower salary ranges overall. However, these roles often provide broader responsibility exposure, allowing professionals to manage multiple aspects of cybersecurity operations simultaneously. This can accelerate skill development and provide valuable experience that supports long-term career advancement.
Economic conditions also play a role in shaping regional salary trends. During periods of digital expansion and increased cybersecurity investment, salaries tend to rise steadily. Even during economic slowdowns, cybersecurity roles often remain stable due to their critical importance in maintaining operational continuity and protecting organizational assets.
Industry-Based Compensation Variations
Industry type has a major influence on the salary levels of information security managers. Certain industries handle highly sensitive data or operate under strict regulatory frameworks, requiring stronger cybersecurity leadership and more advanced risk management capabilities.
Financial services remain one of the highest-paying sectors for this role. Banks, insurance companies, investment firms, and fintech organizations handle massive volumes of financial transactions and personal data, making them prime targets for cyberattacks. As a result, they invest heavily in cybersecurity leadership to ensure system integrity and regulatory compliance.
Healthcare organizations also offer competitive compensation due to the sensitive nature of patient data and strict compliance requirements. Security managers in this sector are responsible for maintaining secure digital health systems, ensuring data privacy, and preventing unauthorized access to critical medical records.
Technology companies provide strong salary packages due to their reliance on cloud infrastructure, software platforms, and large-scale data processing systems. In these environments, cybersecurity is a core operational requirement rather than a supporting function, which elevates the importance of experienced security leadership.
Government and defense sectors typically offer stable compensation structures with strong job security. While base salaries may be more structured compared to private industry roles, they often include long-term benefits, pension systems, and career stability advantages.
Experience and Career Progression Impact on Salary
Experience is one of the most influential factors in determining compensation for information security managers. As professionals progress through their careers, their responsibilities expand from operational execution to strategic leadership, resulting in continuous salary growth.
At earlier stages of management, professionals typically focus on supervising security operations, monitoring systems, coordinating incident response efforts, and ensuring compliance with organizational policies. These roles involve hands-on technical oversight combined with basic team leadership responsibilities.
As professionals move into mid-level roles, their responsibilities broaden significantly. They begin managing larger teams, overseeing enterprise-level security programs, and contributing to organizational risk strategy. At this stage, professionals are expected to align security initiatives with broader business objectives and coordinate cross-functional cybersecurity efforts.
Senior-level information security managers operate at a strategic level, often overseeing entire security programs across large organizations. They are responsible for enterprise-wide risk management, long-term security planning, and direct communication with executive leadership. Their compensation reflects both leadership responsibility and deep technical expertise.
The salary difference between entry-level and senior-level positions can be substantial, reflecting the increasing complexity, accountability, and strategic influence associated with higher-level roles.
Organizational Scale and Structural Complexity
The size and complexity of an organization significantly influence compensation for information security managers. Large enterprises and multinational corporations typically offer higher salaries due to the scale of their operations and the complexity of their digital ecosystems.
These organizations manage vast networks of systems, applications, and data across multiple regions, requiring advanced cybersecurity frameworks and continuous monitoring capabilities. Security managers in such environments are responsible for coordinating global teams and ensuring compliance with multiple regulatory frameworks simultaneously.
Mid-sized organizations offer moderate compensation but often provide broader operational exposure. Professionals in these environments may be responsible for multiple aspects of cybersecurity, including risk management, incident response, and compliance oversight.
Smaller organizations generally offer lower base salaries but provide valuable opportunities for professionals to gain hands-on experience across diverse cybersecurity functions. This broad exposure can significantly enhance long-term career development.
Macroeconomic Trends and Salary Growth Dynamics
Cybersecurity compensation continues to experience steady growth driven by increasing cyber threats, digital transformation initiatives, and expanding regulatory requirements. Organizations are allocating larger portions of their IT budgets toward cybersecurity investments, which directly impacts salary levels for security leadership roles.
Inflation and rising living costs in major metropolitan areas also contribute to upward salary adjustments. Employers in these regions must remain competitive to attract and retain skilled cybersecurity professionals in high-demand markets.
Cybersecurity roles tend to demonstrate strong resilience during economic downturns compared to many other IT positions. This is due to the essential nature of security operations in protecting organizational systems and maintaining business continuity.
Remote Work and Geographic Flexibility Effects
The expansion of remote work has significantly changed salary dynamics for information security managers. Professionals are no longer limited to local job markets, allowing organizations to recruit talent from a global workforce.
Remote roles may be structured using either location-based salary adjustments or standardized compensation models based on organizational headquarters. This flexibility has enabled professionals in lower-cost regions to access higher-paying opportunities traditionally reserved for major metropolitan areas.
At the same time, relocation to high-demand regions can still result in increased compensation due to local market competition and higher operational complexity. This has created a more dynamic and flexible global salary structure within the cybersecurity field.
Tools and Technologies Used in Information Security Management
Information security managers operate within highly complex digital environments where manual monitoring is no longer sufficient to defend against modern cyber threats. Organizations today generate massive volumes of security-related data across servers, applications, endpoints, cloud platforms, and network devices. To manage this complexity, security leaders rely on integrated toolsets that provide continuous visibility, automated detection, and structured response capabilities.
Security monitoring systems form the core of this technological ecosystem. These platforms aggregate logs and events from across an organization’s entire infrastructure and analyze them in real time. By correlating seemingly unrelated events, they help identify abnormal behavior patterns that may indicate malicious activity. Information security managers use these systems to gain situational awareness of the entire security landscape, allowing them to detect threats early and respond before damage occurs.
Identity and access management systems are equally critical because they govern how users interact with organizational resources. In modern environments where employees access systems from multiple locations and devices, controlling identity has become one of the most important security priorities. These systems ensure that only authorized users can access sensitive data and that permissions are aligned with job roles and responsibilities. Security managers oversee these frameworks to reduce risks associated with unauthorized access and credential misuse.
Security Architecture and Enterprise Infrastructure Design
Security architecture represents the structural foundation of an organization’s cybersecurity strategy. It defines how systems are designed, interconnected, and protected from internal and external threats. Information security managers play a key role in evaluating, designing, and maintaining this architecture to ensure it aligns with organizational risk tolerance and operational requirements.
Modern security architecture is built on layered defense principles, where multiple protective mechanisms work together to reduce overall risk exposure. These layers may include network segmentation, encryption protocols, authentication systems, endpoint protection, and continuous monitoring mechanisms. Security managers ensure that each layer functions correctly and integrates seamlessly with the overall infrastructure.
As organizations transition toward cloud-based and hybrid environments, security architecture becomes more complex. Traditional perimeter-based models are no longer sufficient, as users and systems operate across distributed environments. Security managers must ensure that protection extends beyond traditional network boundaries and remains consistent across all platforms.
Infrastructure governance is closely tied to architecture design. It involves enforcing standardized configurations, maintaining security baselines, and ensuring that all systems adhere to organizational policies. Security managers continuously review infrastructure components to identify deviations and enforce corrective actions where necessary.
Risk Management and Threat Evaluation Processes
Risk management is one of the most fundamental responsibilities of information security managers. It involves identifying potential threats, evaluating their likelihood, and determining their potential impact on organizational operations. This structured approach allows organizations to make informed decisions about where to allocate security resources.
Security managers continuously assess both internal and external risks. Internal risks may arise from system misconfigurations, human errors, or unauthorized access attempts. External risks include cyberattacks, malware infections, phishing campaigns, ransomware incidents, and advanced persistent threats targeting organizational systems.
To manage these risks effectively, structured threat evaluation frameworks are used. These frameworks categorize risks based on severity, probability, and business impact. By assigning risk levels, security managers can prioritize mitigation efforts and focus on the most critical vulnerabilities first.
Risk mitigation strategies may include technical controls such as encryption, firewalls, and multi-factor authentication, as well as procedural controls such as employee training and access management policies. The goal is to reduce overall exposure while maintaining operational efficiency and business continuity.
Incident Response and Cyber Crisis Management
Incident response is a critical function within information security management, as it determines how quickly and effectively an organization can react to security breaches. When a cyber incident occurs, time is a crucial factor in limiting damage and preventing further compromise.
The process begins with detection, where monitoring systems identify suspicious behavior or confirmed security events. Once an incident is detected, security managers assess its severity and determine the appropriate response strategy. This may involve isolating affected systems, disabling compromised accounts, or blocking malicious network traffic.
Coordination is essential during incident response. Security managers work closely with IT teams, legal departments, compliance officers, and executive leadership to ensure a unified response. In some cases, external communication may be required if sensitive data is affected or regulatory reporting obligations are triggered.
After containment and recovery, post-incident analysis is conducted to understand the root cause of the breach. This analysis helps identify weaknesses in existing systems and leads to improvements in security controls. Lessons learned from incidents are used to strengthen future defenses and reduce the likelihood of recurrence.
Regulatory Compliance and Security Governance
Compliance management is a major responsibility for information security managers, especially in industries that handle sensitive data or operate under strict legal frameworks. Organizations must comply with a wide range of regulatory requirements that govern data protection, privacy, and cybersecurity practices.
Security managers ensure compliance by implementing structured policies, conducting regular audits, and maintaining detailed documentation of security controls. These activities help demonstrate that the organization is meeting required standards and operating within legal boundaries.
Governance frameworks define how security decisions are made and enforced across the organization. These frameworks establish accountability structures, approval processes, and policy enforcement mechanisms. Security managers play a central role in maintaining these governance systems and ensuring consistency across all departments.
Compliance is not a one-time task but an ongoing process that requires continuous monitoring and adaptation. As regulations evolve and new standards emerge, security managers must update internal policies to ensure continued alignment with external requirements.
Leadership, Communication, and Security Culture Development
Information security managers are not only responsible for technical systems but also for shaping organizational behavior and security culture. Human behavior is often one of the weakest links in cybersecurity, making awareness and training essential components of a strong security program.
Security managers develop training programs that educate employees on safe practices such as password management, phishing awareness, and data handling procedures. These initiatives help reduce human error and strengthen the overall security posture of the organization.
Leadership responsibilities also include managing security teams and ensuring effective collaboration between technical and non-technical departments. Security managers must allocate responsibilities, monitor performance, and ensure that teams are aligned with organizational security goals.
Communication with executive leadership is another critical aspect of the role. Security managers must present complex technical risks in clear business terms, enabling decision-makers to understand potential impacts and allocate resources effectively. This communication bridge is essential for integrating cybersecurity into broader business strategy.
Career Progression and Long-Term Professional Development
Career growth in information security management is closely tied to continuous learning and adaptation. As cyber threats evolve, professionals must constantly update their technical knowledge and leadership capabilities to remain effective in their roles.
Progression typically begins with operational security roles and advances toward strategic leadership positions. Early-career professionals focus on technical execution, while mid-level managers take on broader responsibilities involving team management and policy enforcement.
At senior levels, professionals transition into enterprise-wide leadership roles where they oversee entire security programs and contribute to organizational strategy. These positions require a deep understanding of both technical systems and business operations.
Specialization in areas such as cloud security, risk management, and identity governance can significantly accelerate career growth. Professionals who develop expertise in these high-demand areas are often positioned for faster advancement and increased responsibility over time.
Long-term success in this field depends on the ability to adapt to emerging technologies, regulatory changes, and evolving threat landscapes while maintaining strong leadership and strategic decision-making capabilities.
Conclusion
Information security managers have become one of the most strategically important roles in modern organizations, driven by the accelerating pace of digital transformation and the increasing sophistication of cyber threats. As businesses continue to expand their reliance on digital systems, cloud infrastructure, remote operations, and data-driven decision-making, the responsibility of safeguarding these environments has shifted from a purely technical function to a core business priority. This shift has elevated information security management into a leadership discipline that directly influences organizational stability, financial performance, and long-term sustainability.
The role now extends far beyond traditional cybersecurity oversight. Information security managers are responsible for shaping security strategy, managing enterprise-wide risk, ensuring regulatory compliance, and aligning cybersecurity initiatives with business objectives. They serve as the bridge between technical security teams and executive leadership, translating complex technical risks into actionable business insights. This ability to connect security operations with organizational goals makes them essential contributors to strategic planning and corporate governance.
One of the most defining characteristics of this role is its adaptability. Cybersecurity is not a static field, and the responsibilities of information security managers continue to evolve alongside technological advancements. The rapid adoption of cloud computing has fundamentally changed how security is implemented, requiring managers to rethink traditional perimeter-based defenses. Instead of relying on fixed network boundaries, modern security frameworks emphasize identity-based access control, continuous monitoring, and zero trust principles. Information security managers must ensure that these evolving models are properly integrated into organizational infrastructure without disrupting operational efficiency.
At the same time, the rise of remote and hybrid work environments has introduced new challenges in managing security risks. Employees now access systems from multiple devices and locations, often outside traditional corporate networks. This distributed environment increases the potential attack surface, requiring security managers to implement stronger authentication mechanisms, endpoint protection strategies, and real-time monitoring systems. Ensuring secure access in such dynamic environments has become a core responsibility of modern security leadership.
Regulatory compliance has also become significantly more complex in recent years. Organizations must navigate a growing landscape of data protection laws, industry standards, and international regulatory frameworks. Information security managers are responsible for ensuring that systems and processes remain compliant with these requirements at all times. This involves continuous auditing, documentation, policy enforcement, and coordination with legal and compliance teams. Failure to maintain compliance can result in severe financial penalties, reputational damage, and operational disruption, making this aspect of the role critically important.
Another important dimension of the role is risk management. Information security managers are not only responsible for responding to threats but also for anticipating them. This proactive approach involves identifying vulnerabilities, assessing potential impacts, and implementing mitigation strategies before incidents occur. Risk management has become increasingly data-driven, with security managers relying on advanced analytics, threat intelligence platforms, and automated monitoring tools to make informed decisions. This shift toward predictive security has transformed how organizations approach cybersecurity, moving from reactive defense to proactive resilience.
Leadership and organizational influence are also central to the effectiveness of information security managers. Beyond technical responsibilities, they play a key role in shaping security culture within organizations. Human behavior remains one of the most significant risk factors in cybersecurity, and employees at all levels must be trained to recognize and avoid potential threats. Information security managers develop awareness programs, training initiatives, and internal communication strategies to promote a culture of security consciousness. This cultural aspect of security is just as important as technical defenses, as even the most advanced systems can be compromised through human error.
The career trajectory of information security managers reflects the increasing importance of cybersecurity in modern business environments. Professionals in this field often begin their careers in technical roles such as network security, systems administration, or security analysis before transitioning into management positions. As they gain experience, their responsibilities expand from operational oversight to strategic leadership, eventually leading to enterprise-level security governance roles. This progression highlights the importance of continuous learning, adaptability, and leadership development within the field.
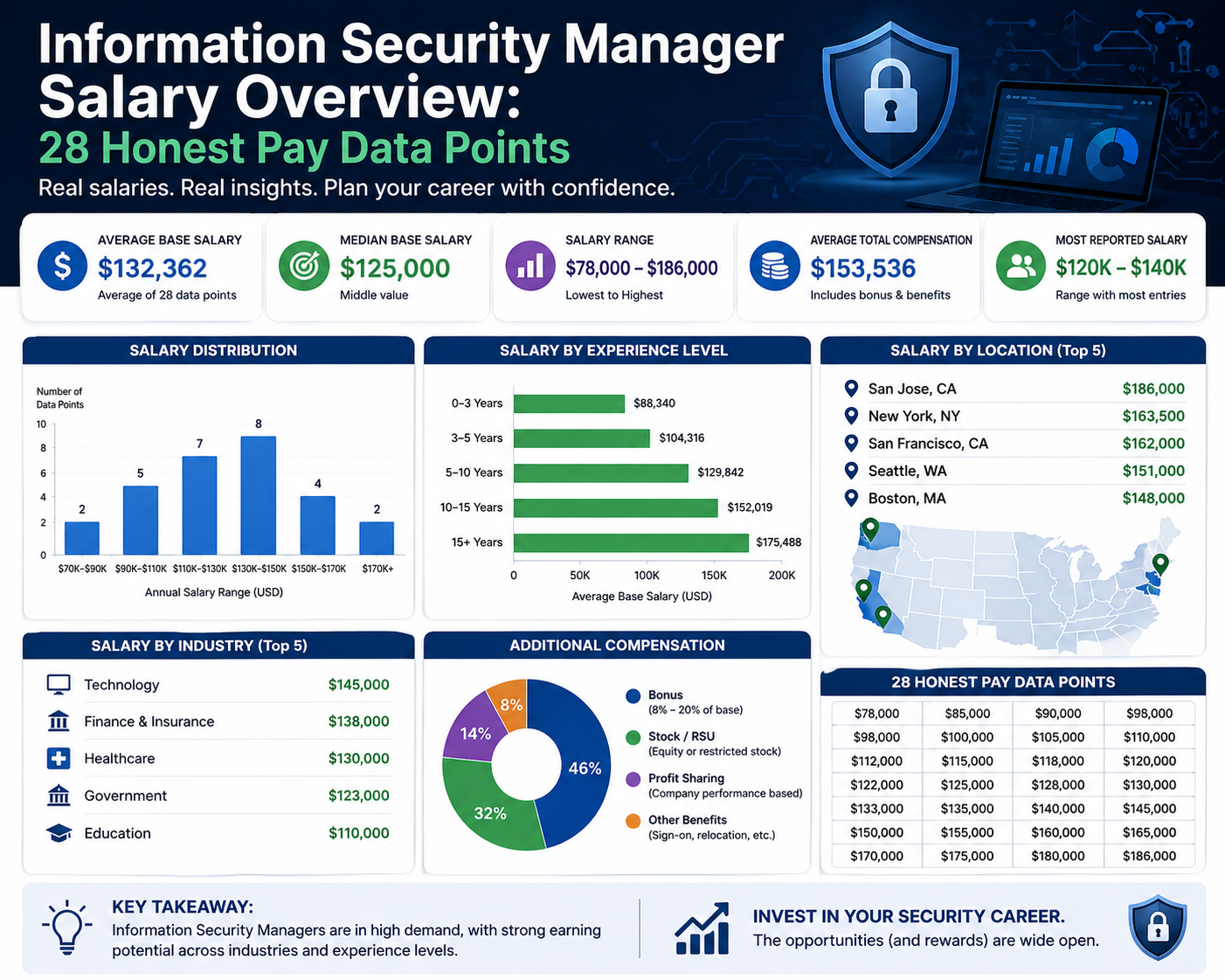
Compensation trends also reflect the growing demand for skilled cybersecurity leaders. Information security managers are among the highest-paid professionals within the IT sector, with salaries influenced by factors such as experience, industry, location, and technical specialization. Organizations operating in high-risk industries such as finance, healthcare, and technology tend to offer higher compensation due to the critical nature of their security requirements. Similarly, professionals with expertise in cloud security, identity management, and regulatory compliance often command higher salaries due to the specialized nature of their skills.
Looking ahead, the demand for information security managers is expected to continue growing at a strong pace as digital ecosystems expand further. Every organization, regardless of size or industry, is becoming increasingly dependent on secure digital infrastructure. This means cybersecurity leadership will remain a non-negotiable requirement rather than an optional investment. As attack methods become more automated and intelligent, security strategies will also need to evolve toward more predictive and adaptive models.
The integration of artificial intelligence, machine learning, and advanced automation into cybersecurity operations will further transform the role. These technologies will enhance threat detection speed, improve anomaly identification, and reduce response times. However, they will not replace the need for human leadership. Instead, they will increase the importance of decision-making roles that can interpret data, manage risk, and guide security strategy at an organizational level.
At the same time, cyber risk is becoming deeply embedded in business strategy discussions at the highest levels. Boards of directors and executive leadership teams are increasingly treating cybersecurity as a core business risk rather than a technical issue. This shift is expanding the influence of information security managers, giving them greater involvement in budgeting decisions, investment planning, and enterprise risk governance. Their input is becoming essential in shaping how organizations allocate resources and prioritize digital transformation initiatives.
Global regulatory frameworks will also continue to evolve, placing additional responsibility on security leaders. Governments and regulatory bodies are introducing stricter rules around data protection, privacy, and cybersecurity accountability. This will require information security managers to maintain a continuous understanding of legal developments and ensure that organizational practices remain aligned with global standards. The increasing complexity of compliance environments will further elevate the importance of structured governance and documentation practices.
Another long-term trend is the growing convergence between cybersecurity and overall enterprise risk management. Information security is no longer an isolated function but is becoming integrated into broader risk frameworks that include financial, operational, and reputational risks. This integration will further expand the strategic importance of security managers within organizational hierarchies.
Ultimately, information security managers represent a critical intersection of technology, leadership, and risk intelligence. Their role ensures that organizations can operate confidently in an increasingly interconnected digital world where threats are constant and evolving. As technology continues to advance, the expectations placed on these professionals will also increase, requiring stronger analytical capabilities, deeper technical understanding, and more sophisticated leadership skills.
The future of cybersecurity leadership will depend heavily on professionals who can balance technical expertise with strategic foresight, operational discipline with innovation, and risk management with business growth. Information security managers who can adapt to this evolving landscape will remain central to organizational success, ensuring resilience, trust, and stability in a digital-first global economy.