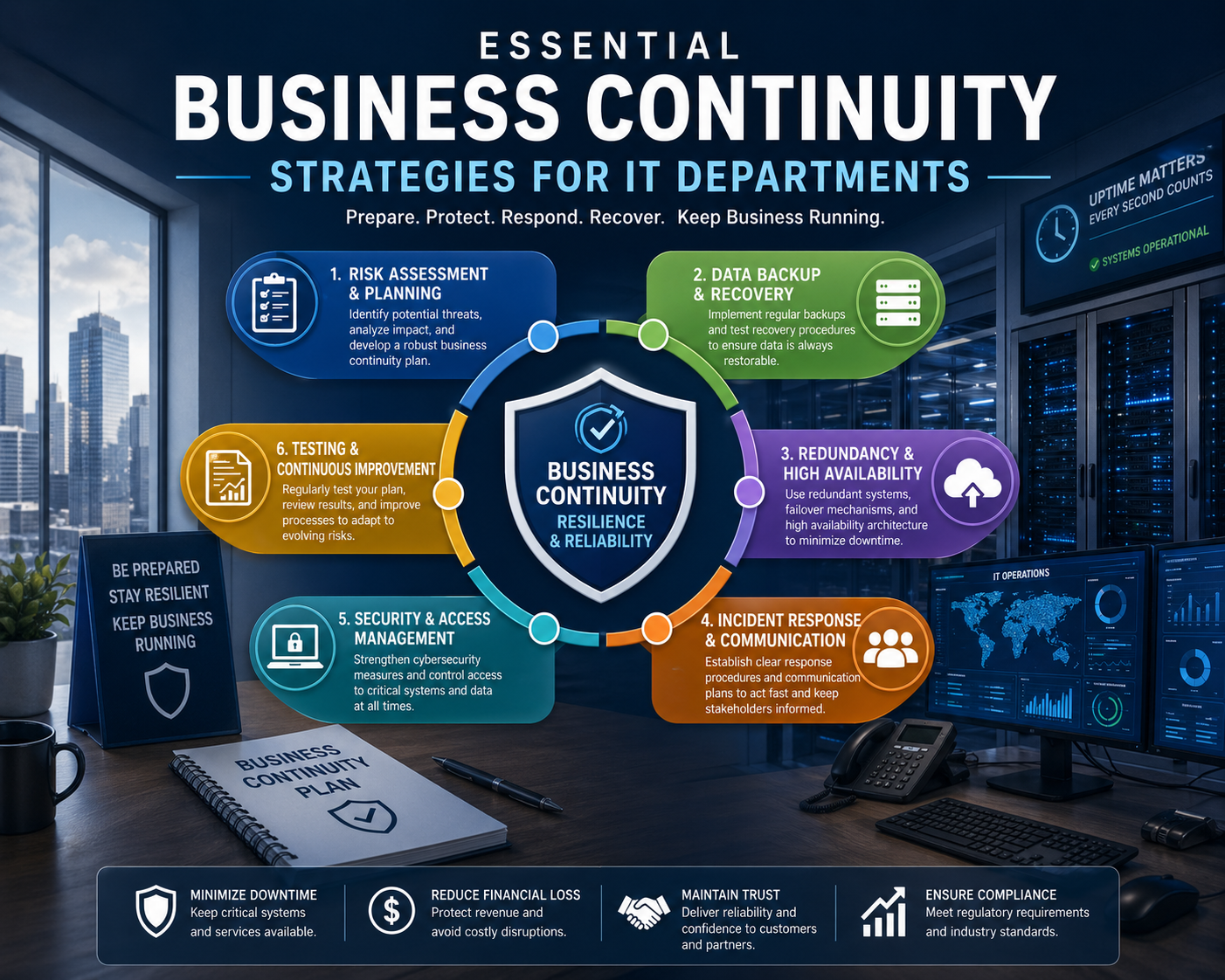
Business continuity planning in IT environments refers to the structured approach used to ensure that digital systems, applications, and infrastructure continue operating or can be restored quickly when unexpected disruptions occur. These disruptions may include cyber incidents, system failures, infrastructure outages, or environmental events that impact the availability of critical services. The primary objective is to reduce operational downtime, protect information integrity, and maintain essential business functions under adverse conditions. In modern organizations, where digital dependency is deeply integrated into every workflow, continuity planning is no longer optional but a core requirement of operational stability. IT departments play a central role in designing and maintaining these continuity frameworks because they are responsible for the systems that support communication, data processing, customer interactions, and internal workflows. Without a structured continuity approach, even minor technical failures can escalate into significant operational interruptions affecting productivity, revenue flow, and service delivery. Business continuity planning in IT environments focuses not only on recovery after an incident but also on minimizing the probability and impact of disruptions before they occur. This proactive stance involves identifying vulnerabilities within systems, understanding interdependencies across infrastructure layers, and implementing safeguards that ensure resilience under stress conditions.
Importance of Continuity Planning in Modern IT Operations
Modern IT operations are built on interconnected systems that span cloud platforms, on-premise infrastructure, virtual environments, and distributed applications. This complexity increases efficiency but also introduces multiple potential points of failure. A disruption in one component can cascade across dependent systems, resulting in widespread service degradation. Business continuity planning addresses this risk by establishing structured safeguards that ensure operational stability even when certain components fail. Organizations rely heavily on uninterrupted access to data, applications, and network services to maintain business functions. When these systems become unavailable, employees lose access to critical tools, customers experience service interruptions, and business processes slow down significantly. Continuity planning helps reduce these risks by ensuring that alternative mechanisms are available to maintain functionality during disruptions. This includes redundancy in infrastructure, backup systems, and predefined recovery procedures. In addition to technical stability, continuity planning also contributes to organizational trust and reliability. Consistent service availability strengthens stakeholder confidence and supports long-term business continuity in competitive environments.
Core Objectives of IT Continuity Frameworks
The primary objective of IT continuity frameworks is to ensure that essential services remain operational or can be restored within acceptable time limits after an incident. This involves identifying critical systems, prioritizing recovery efforts, and defining acceptable levels of disruption. One key objective is minimizing downtime across mission-critical applications such as databases, authentication systems, and transaction processing platforms. Another objective is protecting data integrity so that information remains consistent and recoverable even after unexpected failures. Continuity frameworks also aim to reduce financial and operational impact by ensuring the rapid restoration of services. This requires careful planning of recovery processes, resource allocation, and system dependencies. Additionally, these frameworks support compliance requirements in regulated industries where system availability and data protection are essential. By aligning technical recovery strategies with business priorities, IT continuity planning ensures that recovery efforts support overall organizational goals rather than focusing solely on infrastructure restoration.
Business Impact Analysis in IT Continuity Design
A foundational step in continuity planning is understanding the operational importance of different IT systems through structured analysis. This process evaluates how system disruptions affect business functions and identifies which services require immediate restoration. Not all systems carry the same level of importance, and prioritization is essential for efficient recovery planning. Core systems that support revenue generation, customer interactions, and essential internal operations are typically assigned higher priority levels. Less critical systems may tolerate longer downtime without significant business impact. This classification allows IT teams to allocate resources effectively during recovery scenarios. Business impact analysis also examines the financial consequences of system outages, including revenue loss, productivity decline, and reputational effects. It further evaluates operational dependencies to understand how failures in one system may influence others. By mapping these relationships, IT teams gain a clearer understanding of system criticality and recovery sequencing. This structured approach ensures that continuity planning is aligned with real-world business needs rather than technical assumptions alone.
Risk Identification and Threat Evaluation in IT Systems
Risk identification plays a central role in building effective continuity strategies. IT environments face a wide range of potential threats, including cyberattacks, hardware malfunctions, software errors, network failures, and environmental disruptions. Each of these risks can affect system availability in different ways, making a comprehensive evaluation essential. Cybersecurity incidents may lead to data breaches or system unavailability, while hardware failures can cause unexpected downtime in physical infrastructure. Software issues may introduce instability or application crashes, and environmental factors such as power outages or natural events can impact entire data centers. Human error also remains a significant risk factor, particularly in complex IT environments where manual configurations and operational changes are frequent. Risk evaluation involves identifying these threats and assessing their likelihood and potential impact. This enables IT teams to design protective measures that address the most significant vulnerabilities. The goal is not to eliminate all risks but to reduce their impact and ensure rapid recovery when incidents occur.
System Dependencies and Infrastructure Complexity
Modern IT environments are highly interconnected, meaning that systems rarely operate in isolation. Applications depend on databases, authentication services, network infrastructure, and external integrations. This interdependence increases efficiency but also introduces complexity in continuity planning. A failure in one component can trigger cascading effects across multiple systems, making recovery more challenging. Understanding these dependencies is essential for designing effective continuity strategies. IT teams must map how systems interact and identify critical pathways that support essential business functions. This includes analyzing data flows, service relationships, and infrastructure layers. Without this understanding, recovery efforts may overlook hidden dependencies, leading to incomplete restoration and prolonged downtime. Infrastructure complexity also requires careful consideration of virtualization environments, cloud services, and hybrid deployments. Each layer introduces unique recovery requirements and potential failure points. Continuity planning must account for these complexities to ensure coordinated recovery across all system components.
Establishing Recovery Objectives for IT Systems
Recovery objectives define the acceptable limits of disruption and data loss within IT systems. These objectives guide the design of recovery strategies and determine how quickly systems must be restored after an incident. Two key metrics are commonly used in this process. The first defines the maximum acceptable downtime for a system, which determines how quickly recovery must occur to avoid significant business impact. The second defines the acceptable amount of data loss measured over time, which influences backup frequency and data replication strategies. Together, these objectives help IT teams prioritize systems based on business criticality and operational impact. Systems with strict recovery requirements require more robust redundancy and faster restoration mechanisms, while less critical systems may have more flexible recovery thresholds. Establishing these objectives ensures that technical recovery efforts align with business expectations and operational needs. It also provides measurable targets for evaluating continuity performance during testing and real-world incidents.
Communication Structures During Operational Disruptions
Effective communication is a critical component of continuity planning, especially during system disruptions. When incidents occur, timely and accurate information must be shared with relevant stakeholders to ensure coordinated response efforts. Communication structures define how information flows within the organization during such events. This includes identifying responsible individuals, communication channels, and escalation procedures. IT teams must ensure that technical updates are communicated clearly to decision-makers, support teams, and operational staff. Miscommunication or delays in information sharing can significantly hinder recovery efforts and increase downtime. Communication planning also includes predefined notification processes for internal teams and external stakeholders when necessary. This ensures transparency and helps maintain trust during disruptive events. Structured communication frameworks reduce confusion, improve coordination, and support faster decision-making during recovery operations.
Foundational Strategies for Maintaining System Resilience
System resilience in IT environments is achieved through a combination of architectural design, redundancy, and proactive monitoring. One key strategy involves implementing duplicate system components that can take over operations when primary systems fail. This ensures continuous availability even during hardware or software disruptions. Another important strategy is maintaining synchronized data copies across multiple environments to prevent data loss during failures. Load distribution mechanisms also contribute to resilience by balancing system traffic and reducing pressure on individual components. Additionally, automated switching mechanisms allow systems to transition seamlessly to backup environments when disruptions occur. These strategies work together to ensure that IT services remain available under varying conditions. Resilience is not achieved through a single solution but through layered protection mechanisms that address different types of failure scenarios.
Designing Scalable Continuity Architectures in Complex IT Environments
Modern IT continuity architecture is built around scalability, redundancy, and modular recovery design. As organizations expand their digital ecosystems, continuity planning must evolve from isolated backup strategies into fully integrated resilience architectures that span multiple environments. These architectures typically combine on-premise infrastructure, cloud-based resources, virtualized systems, and distributed applications into a unified recovery ecosystem. The primary goal is to ensure that no single point of failure can disrupt critical business functions. In practice, this requires designing systems that can dynamically reroute workloads, replicate data across environments, and automatically restore services without manual intervention. Scalability becomes essential because IT systems are no longer static; workloads fluctuate, user demand changes, and applications continuously evolve. Continuity architectures must therefore accommodate growth without requiring a complete redesign. This is achieved through modular infrastructure components that can be expanded independently while maintaining consistency in recovery capabilities. A scalable continuity architecture ensures that as new systems are introduced, they inherit the same resilience principles as existing infrastructure. This alignment prevents fragmentation in recovery planning and maintains operational consistency across the entire IT ecosystem.
Role of Infrastructure Redundancy in Preventing Service Disruption
Redundancy is one of the most critical pillars of IT continuity engineering. It involves creating duplicate system components that can take over operations when primary systems fail. These components may include servers, storage systems, network paths, and application instances. The purpose of redundancy is to eliminate single points of failure that could disrupt business operations. In highly available environments, redundancy is implemented at multiple layers of the infrastructure stack. At the hardware level, duplicate servers and storage arrays ensure that physical failures do not impact service availability. At the network level, multiple routing paths and switching mechanisms ensure continuous connectivity even if one pathway becomes unavailable. At the application level, load-balanced clusters distribute traffic across multiple instances to prevent overload and maintain performance stability. Redundancy is not simply about duplication but about intelligent coordination between primary and backup components. Systems must be able to detect failures automatically and shift operations without manual intervention. This process ensures continuity without noticeable interruption to end users. Properly implemented redundancy significantly reduces downtime risk and strengthens overall system resilience under unpredictable conditions.
Failover Mechanisms and Automated Recovery Switching Systems
Failover mechanisms are designed to ensure seamless transition from a failed system to a backup environment. These mechanisms operate automatically, detecting failures and redirecting operations without requiring human intervention. In high-availability environments, failover systems are essential for maintaining uninterrupted service delivery. They rely on continuous monitoring of system health indicators such as response time, resource availability, and connectivity status. When predefined thresholds are exceeded or system failures are detected, failover processes initiate immediately. These processes may involve switching to backup servers, activating secondary data centers, or redirecting traffic to cloud-based environments. The effectiveness of failover systems depends on synchronization between primary and backup environments. Data replication must occur in near real time to prevent inconsistencies during transitions. Additionally, application configurations must remain consistent across environments to ensure seamless continuity. Well-designed failover systems reduce downtime to seconds or milliseconds, depending on infrastructure maturity. This level of automation is essential for mission-critical systems where even brief interruptions can have significant operational or financial consequences.
Data Protection Strategies and Multi-Layer Backup Systems
Data protection is a foundational element of continuity planning because data loss can have irreversible consequences for business operations. Multi-layer backup systems are designed to ensure that data remains recoverable under various failure scenarios. These systems typically include multiple backup tiers, each serving a different recovery purpose. Local backups provide fast recovery for minor incidents such as accidental deletion or system corruption. Off-site backups protect against localized failures such as hardware damage or environmental disruptions. Cloud-based backups add a layer of resilience by distributing data across geographically separated environments. This multi-layered approach ensures that data remains accessible even when multiple failure conditions occur simultaneously. Backup frequency is also a critical factor in a data protection strategy. High-frequency backups reduce potential data loss but require more storage and processing resources. Lower-frequency backups reduce resource consumption but increase recovery gaps. Balancing these factors requires careful analysis of business requirements and recovery objectives. Data protection strategies also include encryption, version control, and integrity verification to ensure that backups remain reliable and secure over time.
Cloud-Based Continuity Models and Distributed Recovery Systems
Cloud-based infrastructure has transformed continuity planning by introducing flexible, scalable, and geographically distributed recovery options. In traditional environments, continuity depended heavily on physical infrastructure duplication, which was expensive and complex to maintain. Cloud environments eliminate many of these constraints by offering on-demand resources that can be activated during disruptions. Distributed recovery systems leverage multiple cloud regions to ensure that services remain available even if one region experiences failure. This geographic distribution reduces the risk of localized disruptions affecting overall system availability. Cloud-based continuity models also support rapid provisioning of virtual resources, allowing organizations to restore systems quickly without waiting for physical infrastructure recovery. Another advantage of cloud-based systems is elasticity, which enables resources to scale dynamically based on demand during recovery operations. This ensures that performance remains stable even under increased load conditions following an outage. Integration between on-premise systems and cloud environments creates hybrid continuity models that combine the strengths of both infrastructures. These models provide flexibility, cost efficiency, and enhanced resilience across diverse operational environments.
Dependency Mapping and System Interconnection Analysis
Effective continuity planning requires a deep understanding of how systems interact within the IT ecosystem. Dependency mapping involves identifying relationships between applications, databases, network services, and infrastructure components. These relationships determine how failures propagate across systems and influence recovery prioritization. In complex environments, a single application may depend on multiple backend systems, authentication services, and external integrations. Without proper mapping, these dependencies may remain hidden, leading to incomplete recovery strategies. System interconnection analysis helps IT teams visualize how data flows between components and identify critical pathways that must be restored first during disruptions. This analysis also highlights potential bottlenecks and single points of failure that could impact multiple systems simultaneously. By understanding these relationships, organizations can design more effective recovery sequences that prioritize essential services and minimize cascading failures. Dependency mapping is an ongoing process because IT environments continuously evolve. New applications, integrations, and infrastructure changes can introduce new dependencies that must be incorporated into continuity planning frameworks.
Recovery Sequencing and Prioritization Frameworks in IT Systems
Recovery sequencing refers to the structured order in which systems are restored after a disruption. This sequence is determined based on system criticality, dependencies, and business impact. Not all systems can be recovered simultaneously, so prioritization is essential for efficient restoration. Core infrastructure services such as authentication systems, network services, and database platforms are typically restored first because they support other dependent systems. Once foundational services are operational, secondary applications and user-facing systems can be brought online. Recovery sequencing must also consider interdependencies between systems to avoid partial restoration scenarios where applications are operational but cannot function fully due to missing backend services. Prioritization frameworks ensure that recovery efforts align with business needs rather than technical convenience. This structured approach reduces downtime, improves coordination, and ensures that essential operations resume as quickly as possible. Effective sequencing also minimizes system instability during recovery by preventing overload on partially restored infrastructure components.
Operational Resilience Through Continuous Monitoring Systems
Continuous monitoring systems play a vital role in maintaining operational resilience in IT environments. These systems track performance metrics, detect anomalies, and provide real-time visibility into infrastructure health. Monitoring tools analyze system behavior across multiple layers, including network performance, server utilization, application response times, and security events. Early detection of potential issues allows IT teams to address problems before they escalate into full-scale disruptions. Monitoring systems also support automated alerting mechanisms that notify administrators when predefined thresholds are exceeded. This proactive approach reduces response times and improves system stability. In advanced environments, monitoring systems incorporate predictive analytics that identify patterns indicating potential failures. This allows organizations to take preventive action before disruptions occur. Continuous monitoring is not limited to internal systems; it also extends to external dependencies such as cloud services and third-party integrations. This comprehensive visibility ensures that IT teams maintain awareness of all components that influence system availability.
Automation in Continuity Planning and Recovery Execution
Automation has become a fundamental component of modern continuity planning. It reduces reliance on manual intervention, accelerates recovery processes, and improves consistency in execution. Automated systems can perform tasks such as system health checks, failover activation, data synchronization, and resource provisioning without human input. This is particularly important in large-scale environments where manual recovery processes would be too slow or error-prone. Automation also ensures that recovery procedures are executed consistently every time, reducing variability and improving reliability. Infrastructure as code practices enable IT teams to define system configurations programmatically, making it easier to replicate environments during recovery scenarios. Automated workflows can coordinate complex recovery sequences across multiple systems, ensuring that dependencies are respected and services are restored in the correct order. By integrating automation into continuity planning, organizations can significantly reduce recovery time and improve overall system resilience.
Governance Structures in IT Business Continuity Management
Effective IT business continuity is not only a technical discipline but also a governance-driven framework that ensures accountability, consistency, and strategic alignment across the organization. Governance structures define how continuity policies are created, approved, implemented, and maintained over time. They establish clear ownership of responsibilities across IT leadership, infrastructure teams, security units, and operational stakeholders. Without structured governance, continuity planning becomes fragmented, inconsistent, and difficult to enforce across large-scale environments. Governance frameworks typically define roles for decision-making authority, escalation pathways during incidents, and compliance alignment with internal and external operational standards. These structures ensure that continuity planning is not treated as a one-time technical project but as an ongoing organizational capability. IT governance also ensures that continuity objectives are aligned with business priorities rather than purely technical considerations. This alignment is essential because recovery decisions must reflect operational impact, financial implications, and service criticality. Governance frameworks also enforce regular review cycles to ensure continuity strategies remain relevant as infrastructure evolves. As systems expand and new technologies are introduced, governance ensures that continuity controls adapt accordingly rather than becoming outdated or ineffective.
Crisis Management Frameworks During IT Disruptions
Crisis management in IT environments refers to the structured approach used to coordinate response efforts during significant operational disruptions. Unlike routine incident handling, crisis management addresses large-scale failures that impact multiple systems, users, or business functions simultaneously. The primary objective is to stabilize the environment, restore critical services, and minimize organizational impact under high-pressure conditions. Crisis management frameworks define command structures that determine who leads response efforts, how decisions are escalated, and how communication flows across teams. During major disruptions, rapid decision-making becomes essential, and predefined structures help avoid confusion or delays. These frameworks also ensure coordination between technical teams, business units, and external stakeholders. A well-designed crisis management structure includes clear roles for incident commanders, technical responders, communication coordinators, and executive decision-makers. Each role has defined responsibilities to ensure that recovery efforts remain organized and efficient. Crisis management also emphasizes situational awareness, where teams continuously assess system status, identify root causes, and prioritize restoration efforts. The ability to maintain structured coordination under pressure is a key factor in reducing downtime and operational impact during major IT disruptions.
Incident Escalation Pathways and Decision Hierarchies
Escalation pathways define how incidents move through different levels of authority based on severity and impact. In IT continuity environments, not all incidents require the same level of response. Minor disruptions may be handled at the operational level, while major outages require escalation to senior technical leadership or executive teams. Structured escalation ensures that critical issues receive appropriate attention without overwhelming higher-level decision-makers with low-impact events. Escalation hierarchies are designed to balance speed and control, ensuring that response actions are both rapid and well-coordinated. As incidents escalate, additional resources are allocated, and decision authority shifts to individuals with broader oversight. This ensures that recovery strategies align with overall business priorities rather than isolated technical perspectives. Escalation pathways also define communication timing, ensuring that stakeholders are informed at appropriate intervals without unnecessary delays or information overload. Clear escalation frameworks reduce confusion during crises and ensure that recovery efforts progress in a controlled and structured manner.
Continuous Testing and Validation of Continuity Systems
Testing is a critical component of IT continuity planning because it validates whether recovery mechanisms function as intended under real-world conditions. Without regular testing, continuity plans remain theoretical and may fail during actual disruptions. Testing frameworks include a variety of approaches such as simulation exercises, system failover drills, partial recovery tests, and full-scale disaster simulations. Each testing method serves a different purpose in evaluating system readiness. Simulation exercises allow teams to evaluate response coordination without impacting live systems. Failover drills test the ability of systems to switch between primary and backup environments. Full-scale tests evaluate the entire recovery ecosystem under controlled conditions. Continuous testing ensures that backup systems remain functional, dependencies are properly configured, and recovery procedures are up to date. It also helps identify weaknesses in infrastructure design, communication gaps, and procedural inefficiencies. Over time, testing improves organizational preparedness and strengthens overall system resilience. Regular validation ensures that continuity strategies evolve alongside changing infrastructure and business requirements.
Change Management and Its Impact on Continuity and Stability
Change management plays a crucial role in maintaining continuity and stability because IT environments are constantly evolving. System updates, configuration changes, infrastructure upgrades, and application deployments can all introduce new risks if not properly controlled. Change management frameworks ensure that modifications are reviewed, tested, and approved before being implemented in production environments. This reduces the likelihood of unintended disruptions that could compromise system availability. In continuity planning, change management is closely linked to risk assessment because every change has the potential to affect system dependencies and recovery processes. Proper documentation of changes ensures that continuity plans remain accurate and reflective of current system configurations. Without effective change management, continuity plans can quickly become outdated, leading to gaps in recovery strategies. Structured change control processes ensure that continuity considerations are integrated into every modification cycle, preserving system stability and resilience over time.
Operational Readiness and Workforce Preparedness in IT Continuity
Operational readiness refers to the ability of IT teams to respond effectively during disruptions. This includes technical skills, procedural knowledge, and familiarity with continuity systems. Workforce preparedness is essential because even the most advanced recovery systems depend on human coordination and execution. Training programs ensure that IT personnel understand recovery procedures, escalation protocols, and system dependencies. Regular drills and simulations help reinforce this knowledge and improve response efficiency. Prepared teams are better equipped to handle high-pressure situations, make informed decisions, and coordinate recovery efforts effectively. Operational readiness also includes documentation accessibility, ensuring that recovery procedures are clearly defined and available during incidents. Cross-training within teams ensures that multiple individuals can perform critical functions if primary personnel are unavailable. This reduces dependency on specific individuals and strengthens overall resilience. Workforce preparedness transforms continuity planning from a technical framework into an operational capability that can be executed reliably during real-world disruptions.
Third-Party Dependencies and External Risk Management
Modern IT ecosystems often rely on third-party services such as cloud providers, software vendors, and external APIs. These dependencies introduce additional risks into continuity planning because disruptions in external systems can directly impact internal operations. Managing third-party risk involves evaluating service reliability, understanding contractual obligations, and ensuring that alternative solutions are available when external systems fail. Continuity frameworks must account for these dependencies by incorporating fallback mechanisms and redundancy strategies where possible. This may include multi-vendor architectures, alternative service integrations, or cached operational modes that allow systems to function temporarily without external connectivity. Risk assessment must extend beyond internal infrastructure to include all external components that influence system availability. Without proper third-party risk management, organizations may experience unexpected disruptions that are outside their direct control. Structured evaluation of external dependencies ensures that continuity planning remains comprehensive and resilient across the entire operational ecosystem.
Security Integration Within Continuity Planning Frameworks
Security and continuity planning are closely interconnected because many disruptions originate from security-related incidents. Cyberattacks, malware infections, ransomware events, and unauthorized access attempts can all lead to system downtime or data loss. Integrating security into continuity planning ensures that recovery strategies address both operational restoration and threat containment. Security controls such as access management, encryption, intrusion detection, and network segmentation play a critical role in preventing disruptions from escalating. During recovery scenarios, security validation ensures that restored systems are not compromised or re-infected. This dual focus on recovery and protection ensures that continuity efforts do not inadvertently reintroduce vulnerabilities into the environment. Security integration also includes monitoring for abnormal activity during recovery phases, ensuring that systems remain stable and secure throughout the restoration process. By combining security and continuity planning, organizations create a unified resilience strategy that addresses both operational availability and threat mitigation.
Performance Optimization During Recovery Operations
Recovery operations often place significant strain on IT systems because multiple services are restored simultaneously, sometimes under increased demand conditions. Performance optimization ensures that systems remain stable and responsive during this phase. This involves balancing resource allocation, prioritizing critical workloads, and preventing system overload. Load management strategies distribute traffic evenly across available resources to maintain performance stability. Resource scaling allows systems to dynamically adjust capacity based on recovery demands. Performance monitoring ensures that bottlenecks are identified and addressed quickly. Optimization during recovery is essential because poorly managed restoration processes can lead to secondary failures or degraded service performance. By maintaining performance stability during recovery, IT teams ensure that restored systems operate reliably and meet business expectations immediately after restoration.
Enterprise-Level Resilience Execution and Continuous Improvement Cycles
Enterprise resilience is achieved through continuous improvement cycles that refine continuity strategies over time. This involves analyzing past incidents, evaluating recovery performance, and identifying areas for enhancement. Continuous improvement ensures that continuity planning evolves alongside technological advancements and organizational growth. Lessons learned from real incidents and testing exercises are integrated into updated recovery procedures and system designs. This iterative process strengthens resilience by addressing weaknesses and reinforcing successful strategies. Enterprise resilience is not a static achievement but an ongoing capability that must adapt to changing environments, emerging threats, and evolving business requirements. Organizations that implement continuous improvement cycles develop stronger recovery capabilities, reduced downtime, and improved operational stability across all IT systems.
Conclusion
Business continuity planning in IT environments represents a structured discipline that ensures organizations can sustain or rapidly restore critical operations when disruptions occur. Across modern digital infrastructures, where applications, data systems, and network services are deeply interconnected, even short periods of downtime can lead to significant operational, financial, and reputational impact. The purpose of continuity planning is not only to respond to incidents after they happen but to design systems and processes that reduce the likelihood and severity of disruption in the first place. When implemented effectively, it transforms IT operations from reactive problem-solving into a proactive, resilience-driven model.
A central theme across continuity planning is the alignment between technical systems and business priorities. IT environments are not uniform in importance; some systems directly support revenue generation, customer engagement, or core operational workflows, while others provide auxiliary support. Understanding this hierarchy is essential for designing recovery strategies that reflect real business needs. Without this alignment, technical recovery may occur in an order that does not support operational recovery, leading to inefficiencies and extended downtime. Business impact analysis plays a key role in identifying these priorities, allowing organizations to categorize systems based on criticality and dependency relationships.
Another fundamental aspect of continuity planning is the management of risk across diverse failure scenarios. IT systems are exposed to multiple categories of threats, including hardware failures, software defects, cyberattacks, network outages, and environmental disruptions. In addition, human error and third-party service failures introduce additional uncertainty. Because these risks vary in likelihood and severity, continuity planning must adopt a layered approach rather than relying on a single protective measure. This is where redundancy, failover systems, backup strategies, and distributed architectures become essential. Each layer of protection addresses a different category of failure, ensuring that no single vulnerability can completely disrupt operations.
The increasing complexity of modern IT environments has made dependency mapping and system interconnection analysis critical components of continuity design. Applications rarely function independently; instead, they rely on multiple underlying services such as authentication systems, databases, APIs, and network infrastructures. A failure in one component can cascade across the entire system if dependencies are not properly understood. Mapping these relationships allows IT teams to design recovery sequences that prioritize foundational systems first, ensuring that dependent applications can be restored effectively. This structured approach prevents partial recovery scenarios where systems appear operational but cannot function fully due to missing dependencies.
Recovery objective,s such as recovery time targets and data loss threshol,ds provide measurable benchmarks for continuity performance. These objectives define how quickly systems must be restored and how much data loss is acceptable under different conditions. By establishing these parameters, organizations can design recovery strategies that balance cost, complexity, and business impact. Systems with strict recovery requirements often require more advanced redundancy and real-time replication, while less critical systems can tolerate longer recovery windows. These objectives also serve as evaluation metrics during testing exercises, helping organizations assess whether continuity strategies meet defined expectations.
Communication is another essential pillar of continuity planning. During disruptions, technical recovery alone is not sufficient; coordinated communication ensures that stakeholders remain informed and aligned. Clear communication structures define how information flows between IT teams, business units, leadership, and external parties. Without structured communication, confusion can escalate during incidents, slowing down recovery efforts and increasing operational impact. Effective communication frameworks establish roles, responsibilities, and escalation pathways so that information is delivered accurately and consistently throughout the lifecycle of an incident.
Resilience engineering further strengthens continuity planning by introducing redundancy, automation, and distributed system design. Redundant infrastructure ensures that backup components are available when primary systems fail, while failover mechanisms enable seamless transitions without manual intervention. Automation plays a critical role in reducing recovery time by executing predefined processes consistently and accurately. Distributed architectures, particularly those leveraging cloud environments, enhance resilience by spreading workloads across multiple geographic locations. This reduces the impact of localized failures and ensures higher availability under diverse conditions.
Testing and validation are essential for ensuring that continuity plans function effectively under real-world conditions. Without regular testing, even well-designed plans may fail due to outdated configurations, overlooked dependencies, or procedural gaps. Testing frameworks evaluate system readiness through simulations, failover drills, and full-scale recovery exercises. These exercises help identify weaknesses in infrastructure design, communication processes, and operational coordination. Over time, continuous testing strengthens organizational preparedness and ensures that recovery procedures remain aligned with evolving system architectures.
Governance structures provide the organizational foundation for continuity planning. They define how decisions are made, how responsibilities are assigned, and how compliance is maintained across IT environments. Governance ensures that continuity planning is not fragmented across teams but instead operates as a unified organizational capability. It also ensures alignment between technical strategies and business objectives, preventing misalignment between recovery actions and operational priorities. Regular governance reviews help maintain relevance as systems evolve and new technologies are introduced.
Crisis management frameworks support continuity planning during large-scale disruptions that affect multiple systems simultaneously. These frameworks establish command structures, escalation processes, and coordination mechanisms that enable efficient response under pressure. During major incidents, structured crisis management ensures that decisions are made quickly, resources are allocated effectively, and recovery efforts remain organized. This reduces confusion and improves the speed of restoration across critical systems.
Change management further supports continuiand ty stability by ensuring that system modifications are controlled and evaluated before implementation. Since IT environments are constantly evolving, uncontrolled changes can introduce unexpected vulnerabilities or disrupt recovery configurations. Structured change management processes ensure that continuity considerations are included in every system update, reducing the risk of misalignment between operational systems and recovery strategies.
Workforce preparedness remains a critical factor in continuity success. Even the most advanced technical systems require skilled personnel to execute recovery processes effectively. Training, simulation exercises, and cross-functional knowledge sharing ensure that IT teams are capable of responding to disruptions with confidence and accuracy. Prepared teams reduce recovery time, improve coordination, and minimize operational errors during high-pressure situations.
Third-party dependencies introduce additional complexity into continuity planning because external systems can impact internal operations without direct control. Managing these dependencies requires careful evaluation of vendor reliability, integration points, and fallback mechanisms. Organizations must account for these external risks within their continuity frameworks to ensure that disruptions outside their infrastructure do not compromise overall resilience.
Security integration ensures that continuity planning also addresses threats originating from malicious activity. Cyber incidents can disrupt availability just as significantly as technical failures, making security and continuity interdependent disciplines. Integrating these functions ensures that recovery efforts also consider threat containment, system validation, and vulnerability mitigation during restoration processes.
Performance management during recovery operations ensures that systems remain stable even under increased load conditions. Recovery phases often introduce simultaneous demand on infrastructure, making performance optimization essential for maintaining service quality. Proper resource allocation, load balancing, and monitoring ensure that restored systems operate efficiently and reliably.
Ultimately, enterprise resilience is achieved through continuous improvement cycles that refine continuity strategies over time. By analyzing incidents, evaluating recovery performance, and updating procedures, organizations strengthen their ability to respond to future disruptions. Continuity planning is not a static framework but a continuously evolving capability that adapts to technological, operational, and environmental changes. Through this ongoing refinement, IT environments become more stable, resilient, and capable of sustaining operations under increasingly complex conditions.