The rapid advancement of technology has significantly increased the complexity of cyber threats, making robust security measures essential for organizations. As businesses rely more heavily on digital systems, the need to protect sensitive data and maintain secure communication channels becomes increasingly critical. Firewalls serve as one of the foundational elements in cybersecurity, acting as a protective barrier that helps regulate and secure network traffic. Understanding their purpose and functionality is key to building a strong security framework that aligns with operational and regulatory requirements.
Understanding the Role of Firewalls
A firewall is a system designed to monitor and control incoming and outgoing network traffic based on predefined security rules. It acts as a gatekeeper between trusted internal networks and untrusted external environments. By analyzing traffic and applying rule-based decisions, firewalls help prevent unauthorized access, malicious attacks, and data breaches. These systems can be implemented as software, hardware, or a combination of both, depending on the scale and needs of the organization.
Firewalls are essential for maintaining the integrity, confidentiality, and availability of information systems. They ensure that only authorized communication is permitted while blocking potentially harmful traffic. This selective filtering process reduces the attack surface and helps organizations maintain control over their network interactions.
Evolution of Firewall Technology
Firewall technology has evolved significantly over time to address the growing sophistication of cyber threats. Early firewalls relied on simple packet filtering techniques, which involved inspecting individual packets based on criteria such as IP addresses and port numbers. While this approach provided basic protection, it could not understand the context of network communication.
To overcome these limitations, stateful inspection was introduced. Stateful firewalls track active connections and evaluate traffic based on the state of those connections. This allows for more intelligent decision-making, as the firewall can determine whether a packet is part of an established session or an unauthorized attempt to gain access.
Modern firewalls have advanced even further by incorporating deep packet inspection capabilities. This enables them to analyze the contents of data packets at a granular level, including application-layer information. By understanding the structure and behavior of specific protocols, these firewalls can detect and block sophisticated threats that would otherwise go unnoticed.
How Firewalls Operate in Network Environments
Firewalls function by inspecting traffic as it passes through designated points in a network. They are typically deployed in-line, ensuring that all data moving between different network segments is subject to analysis. This positioning allows firewalls to act as checkpoints, where decisions are made about whether to allow or block traffic based on predefined rules.
These rules are a critical component of firewall operation. They define the conditions under which traffic is permitted or denied, using factors such as IP addresses, ports, protocols, and sometimes user identity. Effective rule management is essential, as poorly configured rules can either expose the network to risk or disrupt legitimate operations.
Firewalls operate within the TCP/IP framework, which governs how data is transmitted across networks. Depending on their design, firewalls can function at different layers of this model, influencing the level of detail they can analyze. Lower-layer firewalls focus on network-level information, while higher-layer firewalls provide deeper insights into application behavior.
Importance of Traffic Inspection and Control
Traffic inspection is at the core of firewall functionality. By analyzing data packets, firewalls can identify patterns and behaviors associated with malicious activity. This includes detecting unauthorized access attempts, suspicious data transfers, and anomalies in communication patterns. The ability to inspect traffic at various levels allows firewalls to provide comprehensive protection against a wide range of threats.
Control mechanisms within firewalls ensure that only approved traffic is allowed to pass. This is achieved through the enforcement of security policies that reflect the organization’s requirements. These policies can be customized to address specific risks, making firewalls a flexible and adaptable security solution.
Challenges Introduced by Encryption
The widespread use of encryption has introduced new challenges for firewall systems. While encryption enhances privacy and protects data during transmission, it also limits the visibility of traditional firewalls. Encrypted traffic cannot be easily inspected without additional processing, which can create blind spots in security monitoring.
To address this issue, modern firewalls incorporate techniques that allow them to inspect encrypted traffic without compromising its integrity. This often involves decrypting the data for analysis and then re-encrypting it before forwarding it to its destination. Although effective, this process requires careful implementation to avoid introducing vulnerabilities or performance issues.
Firewall Deployment Strategies
Firewalls can be deployed in various configurations depending on the structure and needs of the network. Common deployment points include the network perimeter, where the internal network connects to external environments, and within the network itself to enforce segmentation. These strategic placements help ensure that traffic is monitored and controlled at critical points.
In smaller environments, firewalls may be managed individually, with configurations applied directly to each device. In larger organizations, centralized management systems are often used to oversee multiple firewalls from a single interface. This approach improves consistency and simplifies the process of updating and maintaining security policies.
Performance and Scalability Considerations
As firewalls inspect and process network traffic, they can impact system performance if not properly optimized. High-performance firewalls are designed to handle large volumes of data efficiently, minimizing latency while maintaining strong security controls. This is particularly important for organizations that rely on real-time applications or high-speed connectivity.
Scalability is another important factor. As organizations grow and their networks expand, firewall solutions must be able to accommodate increased traffic and additional devices. Scalable firewalls allow for the addition of resources as needed, ensuring that security measures remain effective without compromising performance.
Role of Firewalls in Network Segmentation
Network segmentation is a security strategy that involves dividing a network into smaller, isolated segments. This approach limits the spread of potential threats by containing them within specific areas. Firewalls play a crucial role in enforcing the boundaries between these segments, controlling which systems can communicate with each other.
By restricting unnecessary communication, segmentation reduces the attack surface and enhances overall security. It also helps organizations implement more granular access controls, ensuring that sensitive data is only accessible to authorized users and systems.
Integration with Broader Security Systems
Firewalls are most effective when integrated with other security technologies. They often work alongside intrusion detection systems, endpoint protection tools, and identity management solutions to provide a layered defense strategy. Each component addresses different aspects of security, creating a comprehensive approach that is more resilient to attacks.
This integration allows for better visibility and coordination across the security infrastructure. For example, information about detected threats can be shared between systems, enabling faster and more effective responses. As a result, organizations can improve their ability to detect, prevent, and respond to cyber threats.
Adapting to Modern IT Environments
The evolution of cloud computing, mobile devices, and remote work has transformed the way networks are structured. Firewalls must adapt to these changes by supporting flexible deployment models and providing protection across diverse environments. Virtual firewalls and cloud-based solutions are increasingly used to secure distributed systems and ensure consistent protection regardless of location.
These modern implementations allow organizations to extend their security measures beyond traditional network boundaries. By protecting both on-premises and cloud-based resources, firewalls continue to play a vital role in maintaining secure operations in an ever-changing technological landscape.
Introduction to Host-Based and Network-Based Firewalls
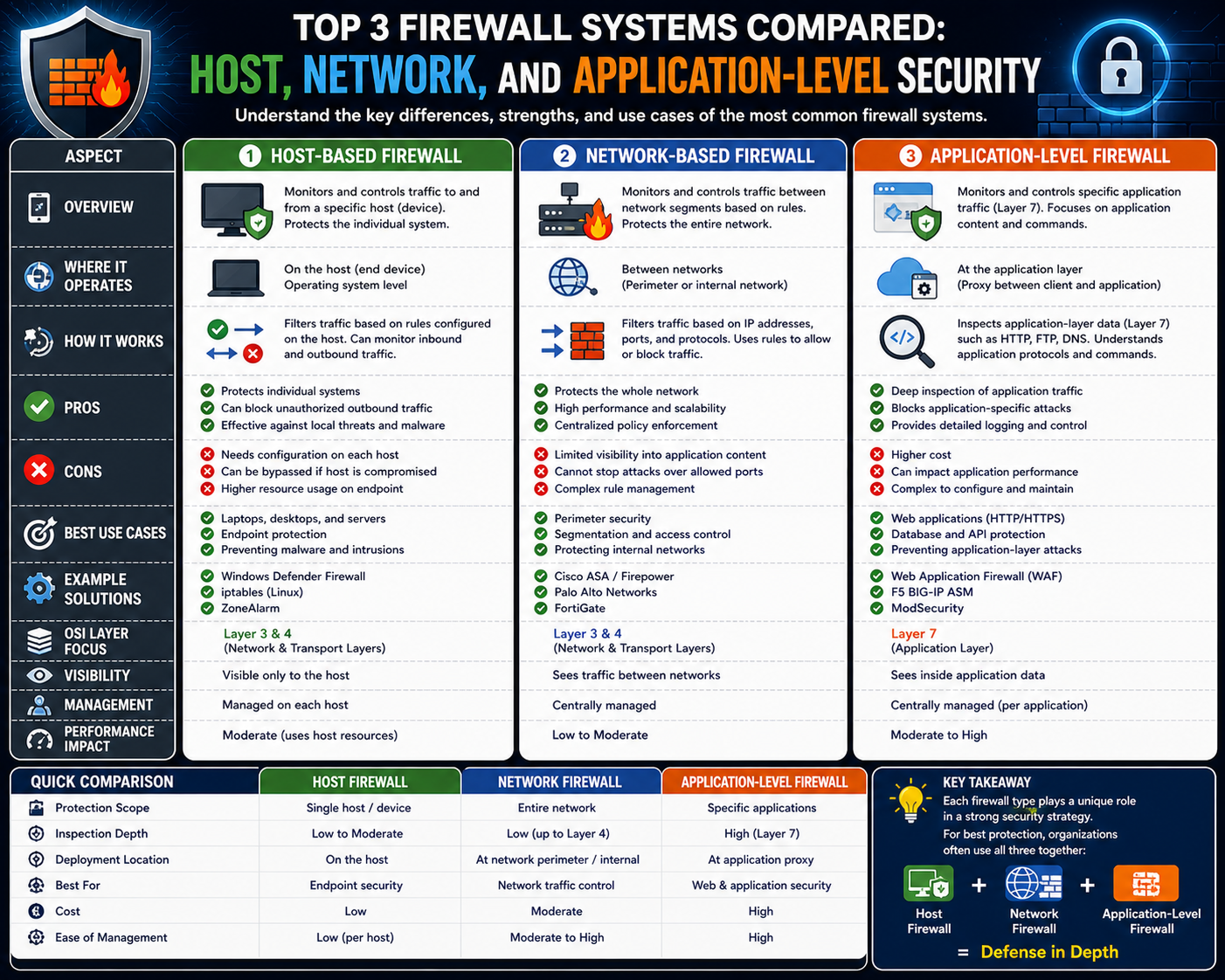
Firewalls remain a central component of cybersecurity strategies, but not all firewalls operate in the same way or serve the same purpose. Among the most widely used types are host-based firewalls and network-based firewalls. Each plays a unique role in controlling traffic and protecting systems, and understanding their differences is essential for building an effective security architecture. These two approaches complement each other by protecting different levels, ensuring that both individual devices and entire networks are safeguarded against threats.
Host-based firewalls operate directly on individual systems, while network-based firewalls are positioned within the network infrastructure. This distinction defines how they function, how they are managed, and the types of threats they are best suited to address. By exploring both types in depth, it becomes easier to understand how they contribute to a layered defense strategy.
What Are Host-Based Firewalls
Host-based firewalls are security solutions installed on individual devices such as desktops, laptops, or servers. They are typically software-based and function within the operating system of the host. Because they operate at the device level, they have direct visibility into the traffic entering and leaving that specific system.
These firewalls are designed to enforce rules that control both inbound and outbound traffic. This means they can prevent unauthorized access from external sources while also monitoring and restricting the actions of applications running on the device. This dual capability is particularly valuable for identifying compromised systems that attempt to communicate with malicious external entities.
Host-based firewalls often come pre-installed with operating systems or as part of security software packages. They can also be customized to meet specific security requirements, allowing administrators to define detailed policies tailored to individual systems or user roles.
How Host-Based Firewalls Function
Host-based firewalls monitor network traffic at the endpoint level. When data attempts to enter or leave the system, the firewall evaluates it against a set of predefined rules. These rules determine whether the traffic should be allowed, blocked, or logged for further analysis.
Because they operate within the host, these firewalls can analyze traffic with a high level of detail. They can identify which application is generating the traffic and apply rules accordingly. This level of granularity allows for more precise control compared to broader network-level filtering.
In addition to filtering traffic, host-based firewalls can also detect suspicious behavior. For example, if an application attempts to establish an unexpected connection, the firewall can block the attempt and alert the user or administrator. This proactive approach helps prevent potential security incidents before they escalate.
Advantages of Host-Based Firewalls
One of the main advantages of host-based firewalls is their ability to protect at the final stage before traffic reaches the system. Even if malicious data bypasses other security layers, the host-based firewall serves as a last line of defense. This significantly reduces the risk of successful attacks.
Another benefit is the level of control they offer. Because they operate on individual devices, they can enforce highly specific policies tailored to the needs of each system. This is particularly useful in environments where different devices have different roles and security requirements.
Host-based firewalls also enhance visibility into system activity. They can track both incoming and outgoing connections, providing valuable insights into how applications interact with the network. This information can be used to detect unusual behavior and respond to potential threats.
Limitations of Host-Based Firewalls
Despite their advantages, host-based firewalls present several challenges. Managing them across a large number of devices can be complex and time-consuming. Without centralized management tools, administrators may need to configure each system individually, increasing the risk of inconsistencies and errors.
Another limitation is their reliance on system resources. Because they run on the host, they consume CPU and memory, which can impact performance, especially on less powerful devices. This can be a concern in environments where efficiency is critical.
Additionally, host-based firewalls are limited to protecting the specific device on which they are installed. They do not provide visibility into broader network traffic, which means they cannot detect threats that occur outside the host’s immediate environment.
What Are Network-Based Firewalls
Network-based firewalls are security solutions deployed within the network infrastructure. They are typically positioned at key نقاط such as the boundary between internal networks and external connections. Their primary function is to control traffic flowing between different parts of the network.
These firewalls are often implemented as dedicated hardware devices or specialized systems designed for high-performance traffic processing. They are capable of handling large volumes of data and are optimized to minimize latency while maintaining strong security controls.
Network-based firewalls enforce policies that apply to all traffic passing through them. This centralized approach allows administrators to manage security at a broader level, ensuring consistency across the entire network.
How Network-Based Firewalls Operate
Network-based firewalls inspect traffic as it passes through designated نقاط in the network. When data arrives at the firewall, it is evaluated against a set of rules that determine whether it should be allowed or blocked. These rules are typically based on factors such as IP addresses, ports, and protocols.
Because they operate at the network level, these firewalls can monitor traffic between different segments of the network as well as between the internal network and external environments. This makes them an effective first line of defense against external threats.
Modern network-based firewalls often include advanced features such as stateful inspection and deep packet analysis. These capabilities allow them to track connections and analyze traffic in greater detail, improving their ability to detect and prevent malicious activity.
Advantages of Network-Based Firewalls
One of the primary advantages of network-based firewalls is their ability to protect entire networks from a central point. By controlling traffic at key junctions, they reduce the exposure of internal systems to external threats. This proactive approach helps prevent attacks before they reach individual devices.
Another benefit is ease of management. Because policies are applied at a central location, administrators can configure and update rules without needing to access each device individually. This simplifies maintenance and ensures consistent enforcement of security policies.
Network-based firewalls are also designed for high performance. Their specialized hardware and optimized software allow them to process large amounts of traffic, making them suitable for enterprise environments with high bandwidth requirements.
Limitations of Network-Based Firewalls
While network-based firewalls provide broad protection, they also have limitations. One of the main challenges is their inability to monitor traffic within the same network segment. This creates potential blind spots where threats can spread without detection.
Another limitation is that they may not have detailed visibility into individual applications or user behavior. This can make it difficult to detect certain types of attacks that require a deeper understanding of system activity.
Deployment location also plays a critical role in their effectiveness. If not placed correctly, network-based firewalls may fail to monitor certain types of traffic, leaving pieces of the network unprotected.
Comparing Host-Based and Network-Based Firewalls
Host-based and network-based firewalls serve different but complementary roles in cybersecurity. Host-based firewalls focus on protecting individual devices, while network-based firewalls provide broader protection across the network. Together, they create a layered defense that addresses threats at multiple levels.
Host-based firewalls offer detailed control and visibility at the endpoint level, making them effective for managing application behavior and preventing unauthorized access to specific systems. Network-based firewalls, on the other hand, provide centralized control and are better suited for managing traffic between different network segments.
The choice between these firewall types depends on the specific needs of the organization. In most cases, a combination of both is used to achieve comprehensive protection.
Layered Security Approach Using Both Firewall Types
A layered security approach involves deploying multiple types of defenses to protect against a wide range of threats. By combining host-based and network-based firewalls, organizations can address both external and internal risks.
Network-based firewalls act as the first line of defense, filtering traffic before it enters the network. Host-based firewalls then provide an additional layer of protection at the device level, ensuring that any threats that bypass the network perimeter are still detected and blocked.
This combination enhances overall security by reducing the likelihood of successful attacks. It also provides greater flexibility in managing policies and responding to threats.
Policy Management and Coordination
Effective use of multiple firewall types requires careful coordination of policies. Inconsistent rules can lead to conflicts, where traffic is allowed by one firewall but blocked by another. This can cause disruptions and make troubleshooting more difficult.
To avoid these issues, organizations should establish clear guidelines for rule creation and management. Centralized management tools can help ensure consistency and simplify the process of updating policies across different systems.
Regular reviews and audits are also important to ensure that policies remain aligned with security objectives and operational needs.
Performance Considerations in Combined Deployments
When using both host-based and network-based firewalls, performance must be carefully managed. Each layer of inspection adds processing overhead, which can impact network speed and system responsiveness.
Optimizing performance involves balancing security requirements with resource availability. This may include configuring rules to minimize unnecessary processing, using high-performance hardware, and monitoring system performance to identify bottlenecks.
Proper planning and testing are essential to ensure that security measures do not negatively impact user experience or business operations.
Adapting to Modern Infrastructure
As technology continues to evolve, firewall strategies must adapt to new environments. The rise of cloud computing, virtualization, and remote work has changed the way networks are structured and secured.
Host-based firewalls are particularly valuable in distributed environments, where devices may operate beyond traditional network boundaries. Network-based firewalls, including virtual implementations, protect cloud-based resources and hybrid infrastructures.
By adapting to these changes, organizations can maintain strong security controls while supporting modern operational requirements.
Role in Threat Detection and Response
Both host-based and network-based firewalls play a role in detecting and responding to threats. Network-based firewalls identify suspicious traffic patterns and block potential attacks at the perimeter. Host-based firewalls provide detailed insights into system behavior, helping to detect compromised devices.
Together, they contribute to a more comprehensive threat detection strategy. By combining data from both sources, organizations can gain a better understanding of their security posture and respond more effectively to incidents.
Ongoing Maintenance and Updates
Maintaining firewall systems is an ongoing process that requires regular updates and monitoring. Threat landscapes change constantly, and firewalls must be updated to recognize new attack methods.
This includes updating software, refining rules, and monitoring logs for unusual activity. Automation can assist in this process, but human oversight remains essential to ensure accuracy and effectiveness.
Consistent maintenance helps ensure that both host-based and network-based firewalls continue to provide reliable protection over time.
Introduction to Application-Based Firewalls and Advanced Protection Layers
Application-based firewalls represent a specialized category of security controls designed to protect communication at the application layer. Unlike broader firewall types that focus on network traffic or individual hosts, these firewalls analyze how specific applications behave and interact. This targeted approach allows for deeper inspection and more precise control over traffic, making it essential in environments where application security is a top priority. As cyber threats increasingly exploit application vulnerabilities, the importance of this firewall type continues to grow.
Modern digital environments rely heavily on web applications, APIs, and cloud services. These technologies introduce new attack surfaces that traditional firewalls cannot fully protect. Application-based firewalls address this gap by focusing on the structure and behavior of application-level communication. This enables them to identify threats that are embedded within legitimate traffic, which might otherwise pass through lower-level defenses unnoticed.
Core Functionality of Application-Based Firewalls
Application-based firewalls operate by analyzing traffic at the application layer, which is the highest level of communication in network models. At this level, data is interpreted in a format that aligns with specific application protocols. This allows the firewall to understand not just where the traffic is coming from, but also what the traffic is doing.
These firewalls inspect elements such as request headers, message bodies, session tokens, and command structures. By evaluating these components, they can determine whether the behavior of the traffic matches expected patterns. If anomalies are detected, the firewall can block the request, log the activity, or trigger alerts for further investigation.
This level of inspection provides a significant advantage over traditional filtering methods. Instead of relying solely on network-level indicators, application-based firewalls assess the intent and structure of communication. This enables them to detect complex threats that are designed to bypass simpler security controls.
Understanding Application Layer Threats
Application-layer attacks are among the most common and dangerous types of cyber threats. These attacks target vulnerabilities within software applications rather than the underlying network. Examples include injection attacks, cross-site scripting, session hijacking, and unauthorized data manipulation.
These threats often exploit weaknesses in how applications process input or manage sessions. Because the traffic used in these attacks can appear legitimate at the network level, traditional firewalls may not detect them. Application-based firewalls address this issue by analyzing the content and context of requests in detail.
By identifying patterns associated with known attack methods, these firewalls can block malicious requests before they reach the application. This proactive approach reduces the risk of data breaches and system compromise.
Customization and Rule Definition
One of the defining features of application-based firewalls is their ability to be highly customized. Administrators can create rules that are tailored to the specific behavior and requirements of individual applications. This allows for precise control over how traffic is handled.
Rules can be based on a wide range of criteria, including request structure, parameter values, user behavior, and session characteristics. This flexibility enables organizations to implement security policies that align closely with their operational needs.
However, this level of customization also introduces complexity. Creating effective rules requires a deep understanding of the application being protected. Without this knowledge, it can be difficult to distinguish between legitimate and malicious behavior.
Benefits of Deep Traffic Inspection
Deep inspection of application traffic provides several key benefits. It allows for the detection of subtle anomalies that may indicate an attack. It also enables the enforcement of strict validation rules, ensuring that only properly formatted and expected data is accepted.
This capability is particularly valuable in protecting sensitive applications that handle critical data. By validating inputs and monitoring behavior, application-based firewalls help prevent unauthorized access and data manipulation.
Another advantage is the ability to reduce false positives. Because the firewall understands the context of the application, it can make more accurate decisions about whether traffic is legitimate. This improves the overall efficiency of the security system.
Challenges in Managing Application-Based Firewalls
Despite their advantages, application-based firewalls can be challenging to manage. The complexity of modern applications means that rules must be continuously updated to reflect changes in functionality. This requires ongoing monitoring and adjustment.
Frequent updates to applications can lead to mismatches between expected and actual behavior. If firewall rules are not updated accordingly, legitimate traffic may be blocked, causing disruptions to users and business operations.
The need for specialized knowledge is another challenge. Administrators must understand both security principles and application behavior to configure the firewall effectively. This can create a steep learning curve and may require dedicated resources.
Performance Considerations and Optimization
Application-based firewalls perform intensive analysis of traffic, which can impact performance if not properly managed. Inspecting data at a detailed level requires processing power and can introduce latency.
To address this, modern implementations are designed to optimize performance through efficient processing techniques. These may include selective inspection, caching, and hardware acceleration. Proper configuration is essential to balance security with performance.
Organizations must carefully plan deployment to ensure that the firewall can handle expected traffic volumes. This may involve scaling resources or distributing workloads across multiple systems.
Integration with Other Firewall Types
Application-based firewalls are most effective when used in conjunction with other firewall types. Host-based and network-based firewalls provide broader protection, while application-based firewalls focus on specific vulnerabilities.
This layered approach enhances overall security by addressing threats at multiple levels. Network-based firewalls filter traffic at the perimeter, host-based firewalls protect individual devices, and application-based firewalls secure the applications themselves.
Coordination between these layers is essential. Policies should be aligned to ensure consistent enforcement and to avoid conflicts that could disrupt legitimate traffic.
Role in Modern Cloud Environments
Cloud computing has transformed how applications are deployed and accessed. Application-based firewalls have adapted to this shift by supporting cloud-native architectures. They can be deployed as virtual instances that protect applications regardless of their physical location.
In cloud environments, applications are often distributed across multiple servers and regions. Application-based firewalls provide consistent protection by monitoring traffic at the application level, regardless of where it originates.
This flexibility makes them well-suited for modern infrastructures that require scalability and dynamic resource allocation.
Supporting Zero Trust Security Models
The zero-trust model is based on the principle that no traffic should be trusted by default. Every request must be verified before access is granted. Application-based firewalls play a key role in this approach by validating interactions at a detailed level.
By analyzing user behavior, session integrity, and request structure, these firewalls help enforce strict access controls. This reduces the risk of unauthorized access and ensures that only legitimate interactions are allowed.
This approach is particularly important in environments with remote users and distributed systems, where traditional perimeter defenses are less effective.
Use of Automation and Intelligent Analysis
Automation is becoming increasingly important in managing application-based firewalls. Automated systems can analyze traffic patterns, detect anomalies, and adjust rules in real time. This improves responsiveness and reduces the burden on administrators.
Intelligent analysis techniques, including machine learning, enable firewalls to identify new and evolving threats. By learning from historical data, these systems can recognize patterns that indicate potential attacks.
While automation enhances efficiency, it must be carefully managed to ensure accuracy. Human oversight remains essential to validate decisions and refine rules.
Handling Encrypted Application Traffic
Encryption is widely used to protect data in transit, but it also presents challenges for security inspection. Application-based firewalls must be able to analyze encrypted traffic without compromising its integrity.
This is typically achieved through secure decryption and re-encryption processes. The firewall temporarily decrypts the data, inspects it for threats, and then re-encrypts it before forwarding it.
This process must be implemented with care to maintain privacy and performance. Proper configuration ensures that security is not compromised while still providing visibility into encrypted communications.
Threat Intelligence and Continuous Updates
Application-based firewalls benefit from integration with threat intelligence sources. These sources provide information about known attack patterns, vulnerabilities, and malicious actors.
By incorporating this data, firewalls can update their rules and detection capabilities to address emerging threats. Continuous updates are essential to maintain effectiveness in a rapidly changing threat landscape.
Regular monitoring and analysis of firewall logs also contribute to improved security. By reviewing activity, organizations can identify trends and adjust their defenses accordingly.
Future Trends in Application-Level Security
The role of application-based firewalls is expected to expand as applications become more complex and interconnected. Advances in technology will continue to enhance their capabilities, enabling more accurate detection and faster response times.
Integration with broader security platforms is likely to increase, creating unified systems that combine multiple mechanisms. This will simplify management and improve coordination across different layers of security.
As organizations continue to adopt new technologies, application-based firewalls will remain a critical component of comprehensive security strategies, providing the specialized protection needed to defend against advanced threats.
Conclusion
Firewalls continue to play a central role in modern cybersecurity, serving as one of the most reliable mechanisms for controlling traffic and protecting digital environments. As organizations become more dependent on interconnected systems, the need for structured and layered protection has become increasingly important. The comparison between host-based, network-based, and application-based firewalls highlights how each type contributes to a broader security strategy, rather than functioning as an isolated solution. Each firewall type operates at a different level, offering unique strengths that address specific risks, and together they form a comprehensive approach to safeguarding systems and data.
Host-based firewalls protect at the device level, ensuring that individual systems remain secure even when threats manage to bypass other defenses. Their ability to monitor both incoming and outgoing traffic gives them an important role in identifying compromised systems and preventing unauthorized communication. By focusing on the endpoint, they offer detailed control and visibility that cannot be achieved through network-level solutions alone. However, their effectiveness depends heavily on proper configuration and consistent management across all devices, which can become challenging in large environments.
Network-based firewalls, on the other hand, operate at a broader level by controlling traffic across entire networks. Positioned at strategic points such as network boundaries, they act as the first line of defense against external threats. Their centralized nature simplifies policy enforcement and ensures consistent protection across multiple systems. These firewalls are designed for performance and scalability, making them well-suited for handling large volumes of traffic in enterprise environments. Despite their strengths, they are not without limitations, particularly when it comes to monitoring internal traffic within the same network segment. This limitation reinforces the importance of combining them with other security measures.
Application-based firewalls introduce a deeper level of inspection by focusing on the behavior and structure of application-level communication. Their ability to analyze traffic in context allows them to detect sophisticated threats that would otherwise remain hidden within legitimate data flows. This makes them especially valuable for protecting modern applications, which are often targeted by attackers seeking to exploit vulnerabilities. The precision and customization they offer enable organizations to enforce highly specific security policies, although this also requires a higher level of expertise and ongoing maintenance.
The interaction between these firewall types illustrates the importance of a layered security approach. Relying on a single type of firewall is no longer sufficient in an environment where threats are diverse and constantly evolving. Instead, combining host-based, network-based, and application-based firewalls creates multiple نقاط of control, each addressing different aspects of risk. This layered model reduces the likelihood of successful attacks by ensuring that even if one layer is bypassed, others remain in place to provide protection.
Effective firewall deployment also involves careful planning and coordination. Policies must be aligned across all layers to avoid conflicts and ensure consistent enforcement. Misconfigured rules can create vulnerabilities or disrupt legitimate operations, making regular review and adjustment essential. In addition, performance considerations must be taken into account, as each layer of inspection introduces some level of processing overhead. Balancing security with efficiency is a key aspect of maintaining a functional and reliable system.
The evolving nature of technology continues to influence how firewalls are used and implemented. The rise of cloud computing, remote work, and distributed networks has expanded the نطاق of security beyond traditional boundaries. Firewalls must now operate in diverse environments, protecting resources regardless of their location. This has led to the development of virtual and cloud-based firewall solutions that offer flexibility and scalability while maintaining strong security controls.
Automation and intelligent analysis are also shaping the future of firewall management. Advanced systems can monitor traffic patterns, detect anomalies, and adapt to changing conditions with minimal human intervention. This enhances the ability to respond quickly to emerging threats and reduces the burden on administrators. However, human oversight remains essential to ensure that automated decisions align with organizational goals and do not introduce unintended risks.
Another important aspect of firewall effectiveness is the integration with other security technologies. Firewalls do not operate in isolation but are part of a larger ecosystem that includes intrusion detection systems, endpoint protection, and identity management solutions. This integration allows for better visibility and coordination, enabling organizations to detect and respond to threats more effectively. By sharing information across systems, security tools can work together to provide a more comprehensive defense.
Compliance requirements also play a significant role in shaping firewall strategies. Many industries are subject to regulations that mandate specific security measures, including the use of firewalls. Meeting these requirements involves not only implementing the appropriate technologies but also maintaining proper documentation and demonstrating adherence to established standards. This adds another layer of complexity but also reinforces the importance of maintaining strong security practices.
As cyber threats continue to evolve, the role of firewalls will remain essential. Attackers are constantly developing new methods to bypass defenses, making it necessary for security measures to adapt accordingly. Firewalls must continue to evolve in response, incorporating new technologies and techniques to stay ahead of emerging risks. This ongoing evolution ensures that they remain a relevant and effective component of cybersecurity strategies.
Ultimately, the effectiveness of any firewall solution depends on how well it is implemented and maintained. Technology alone cannot guarantee security; it must be supported by proper configuration, regular updates, and a clear understanding of the environment it is protecting. Organizations that invest in understanding the differences between firewall types and how they work together are better equipped to build resilient systems that can withstand the challenges of modern cybersecurity.
The combined use of host-based, network-based, and application-based firewalls represents a comprehensive approach to protecting digital assets. Each type addresses specific vulnerabilities and contributes to a layered defense that is greater than the sum of its parts. By leveraging the strengths of each firewall type and ensuring they work together effectively, organizations can create a security framework that is both robust and adaptable, capable of meeting current demands while preparing for future challenges.