Modern digital communication depends on secure systems that protect sensitive information as it travels across networks. Every time data is transmitted between a user and a server—such as logging in, making payments, or sharing personal details—it moves through multiple network layers before reaching its destination. Without proper protection, this information can be intercepted, modified, or stolen by unauthorized entities. Because of these risks, secure communication has become a core requirement in all internet-based systems.
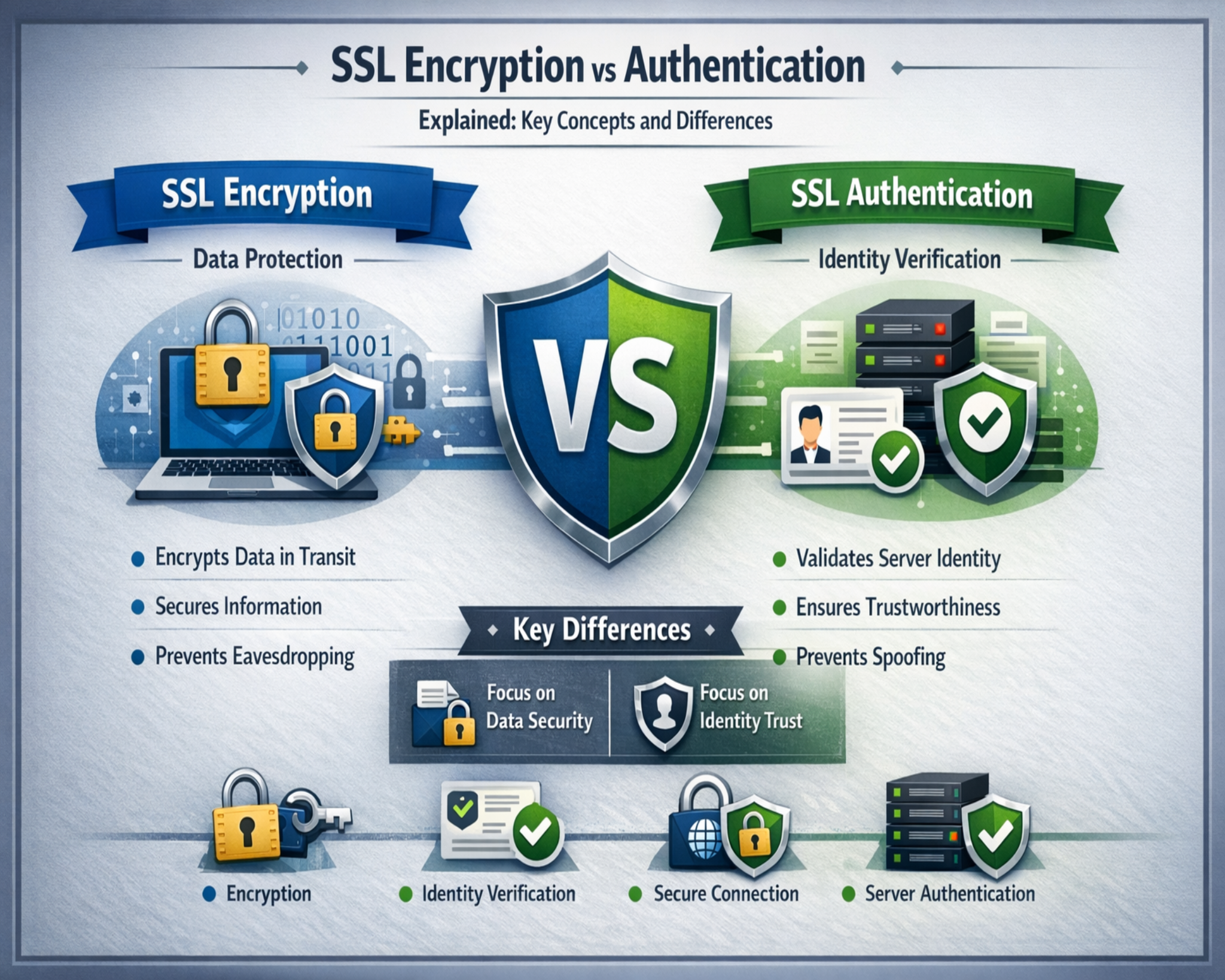
The purpose of secure communication is to ensure three main principles: confidentiality, integrity, and authentication. Confidentiality ensures that only authorized users can access the data being transmitted. Integrity ensures that the data remains unchanged during transmission. Authentication ensures that both the sender and receiver can verify each other’s identity before exchanging information. These principles work together to establish trust in digital systems and protect users from cyber threats.
As online services continue to expand, the volume of sensitive data being transmitted has increased significantly. This includes financial transactions, healthcare records, business communications, and personal information. Without strong security mechanisms, such data would be highly vulnerable to interception and misuse. Secure communication protocols ensure that this information remains protected throughout its journey.
Evolution of secure socket layer and modern encryption protocols
Secure Socket Layer was originally developed to create encrypted communication channels between web browsers and servers. Its primary purpose was to ensure that data transmitted over the internet could not be read or modified by unauthorized parties. Over time, advancements in cryptography led to the development of more secure protocols known as Transport Layer Security, which improved upon the limitations of early SSL versions.
The evolution from SSL to modern secure protocols was driven by increasing cybersecurity threats and the need for stronger protection. Early versions of SSL had vulnerabilities that could be exploited by attackers to intercept or manipulate data. Newer protocols introduced stronger encryption algorithms, improved key exchange mechanisms, and better authentication processes. These improvements significantly enhanced the security and reliability of online communication.
Even though SSL has been replaced technically, the term is still commonly used to refer to secure communication protocols in general. These protocols form the foundation of encrypted internet traffic and ensure that data exchanges remain secure across modern digital systems.
Importance of encryption in protecting data
Encryption is one of the most critical technologies used in securing digital communication. It works by converting readable data into an encoded format that cannot be understood without the correct decryption key. This ensures that even if data is intercepted during transmission, it remains unreadable and unusable to unauthorized individuals.
Encryption is widely used to protect sensitive information such as passwords, financial details, personal messages, and corporate data. Its main purpose is to maintain confidentiality by ensuring that only authorized parties can access the original information. In addition to confidentiality, encryption also helps maintain data integrity by making it possible to detect unauthorized modifications.
The effectiveness of encryption depends on the strength of the algorithms used and the security of the cryptographic keys. Strong encryption methods make it extremely difficult for attackers to decode information, even with advanced computational resources. This makes encryption a fundamental part of modern cybersecurity systems.
How encryption works during secure communication
Encryption operates through a structured process that begins before any data is transmitted. When a user connects to a secure server, both systems initiate a negotiation process to establish encryption parameters. During this process, cryptographic keys are generated and securely exchanged between the client and server.
Once the secure connection is established, data is encrypted before transmission. This means the information is converted into a coded format that cannot be interpreted without the correct key. When the data reaches its destination, it is decrypted back into readable form using the corresponding decryption key.
This process continues throughout the entire communication session. Each piece of data is individually encrypted and decrypted, ensuring continuous protection. Even if attackers intercept the data during transmission, it remains unreadable without the required cryptographic keys.
Encryption also provides a way to detect tampering. If encrypted data is altered during transmission, it will fail to decrypt correctly at the receiving end. This helps identify potential security breaches and ensures data integrity.
Asymmetric and symmetric encryption in secure systems
Secure communication relies on two primary types of encryption: asymmetric encryption and symmetric encryption. Each plays a distinct role in protecting data.
Asymmetric encryption uses a pair of keys: a public key and a private key. The public key is shared openly and is used to encrypt data, while the private key is kept secret and used for decryption. This method is mainly used during the initial connection phase to securely exchange information between systems that do not share prior trust.
Although asymmetric encryption is highly secure, it requires significant computational resources, making it slower for large-scale data transmission. To address this limitation, symmetric encryption is used after the secure connection is established.
Symmetric encryption uses a single shared key for both encryption and decryption. This method is faster and more efficient, making it ideal for continuous data exchange during an active session. Both the client and server use the same key to secure communication throughout the session.
The combination of both encryption methods allows secure systems to achieve both security and performance. Asymmetric encryption ensures safe key exchange, while symmetric encryption ensures fast and efficient communication.
Key exchange and secure session creation
The establishment of a secure connection begins with a key exchange process. During this process, the client and server agree on encryption methods and generate cryptographic keys that will be used for securing the session. These keys are exchanged securely to prevent interception by unauthorized parties.
Once the key exchange is complete, a secure session is created. This session allows encrypted communication between both parties. All data transmitted during this session is protected using the agreed encryption method.
Session keys are temporary and are discarded once the communication ends. This ensures that each new session requires fresh key generation, reducing the risk of long-term vulnerabilities. Even if one session is compromised, future sessions remain secure due to independent key creation.
This dynamic approach enhances overall security by ensuring that encryption keys are not reused across multiple sessions.
Role of encryption in maintaining digital trust
Encryption plays a critical role in maintaining trust in digital communication systems. Without encryption, sensitive data would be exposed to interception and misuse, making online interactions unsafe. Secure communication ensures that users can confidently exchange information without fear of exposure.
Encryption not only protects confidentiality but also ensures that data integrity is maintained throughout transmission. Any unauthorized changes to encrypted data can be detected during decryption, allowing systems to identify potential security issues.
As digital ecosystems continue to expand, encryption remains a foundational technology that supports secure communication across all platforms. It ensures that data remains private, reliable, and protected from unauthorized access throughout its entire journey.
Understanding authentication in secure communication
Authentication is a core security mechanism used in secure digital communication systems to verify the identity of the parties involved before any sensitive data is exchanged. While encryption protects the content of data, authentication ensures that the data is being shared with the correct and legitimate entities. Without authentication, encrypted communication could still be vulnerable to impersonation attacks, where an attacker pretends to be a trusted server or client.
In secure communication systems, authentication typically occurs at the beginning of a connection. Before any meaningful data transfer begins, both the client and server must establish trust. This process ensures that neither side is communicating with a malicious or unauthorized entity. Authentication is especially important in environments where sensitive data such as login credentials, financial information, or personal records are exchanged.
Authentication also strengthens overall system security by reducing the risk of man-in-the-middle attacks. In such attacks, a malicious actor secretly intercepts and possibly alters communication between two parties who believe they are directly communicating with each other. Proper authentication prevents this by ensuring that both ends of the communication are verified before data exchange begins.
Role of identity verification in secure sessions
Identity verification is a fundamental component of authentication in secure communication systems. It ensures that each party involved in the communication is who they claim to be. This verification process relies on digital credentials that are issued and validated by trusted systems.
When a client connects to a secure server, it requests proof of identity from the server. The server responds by presenting a digital certificate that contains verified identity information. The client then checks this certificate against trusted validation sources to confirm its legitimacy. If the certificate is valid, the connection proceeds; if not, the connection is rejected or flagged as unsafe.
In some cases, identity verification is mutual. Both client and server verify each other’s identity before establishing a secure session. This dual verification process is commonly used in high-security environments where both parties must be fully authenticated before communication can begin.
Identity verification ensures that communication does not occur blindly. Instead, it introduces a structured trust model where each party must prove legitimacy before participating in data exchange.
Understanding SSL certificates in authentication
SSL certificates play a crucial role in the authentication process. They act as digital identity documents that verify the legitimacy of a website or server. These certificates contain important information such as the domain name, organization details, cryptographic keys, and the issuing authority.
When a secure connection is initiated, the server presents its SSL certificate to the client. The client then evaluates the certificate to determine whether it is valid and trustworthy. This evaluation includes checking whether the certificate is issued by a trusted authority, whether it has expired, and whether it matches the intended domain.
If the certificate passes all validation checks, the client accepts it and continues with the secure connection. If the certificate fails validation, the connection may be blocked or marked as unsafe. This process ensures that users are not unknowingly connected to fraudulent or malicious servers.
SSL certificates also enable encrypted communication by providing the necessary public key required for secure data exchange. This makes them an essential component of both authentication and encryption processes in secure communication systems.
Structure and components of SSL certificates
An SSL certificate contains several key components that work together to establish identity and enable secure communication. One of the most important elements is the public key, which is used to encrypt data before transmission. The corresponding private key is kept securely by the server and is used to decrypt the data.
The certificate also includes information about the entity that owns the certificate. This typically includes the domain name, organization name, and sometimes geographic information. This identity data helps clients verify that they are communicating with the correct server.
Another important component is the digital signature provided by a trusted issuing authority. This signature confirms that the certificate has been validated and has not been tampered with. The presence of this signature adds a layer of trust to the authentication process.
SSL certificates also include validity periods, which define how long the certificate remains valid. Once the certificate expires, it must be renewed to maintain secure communication. This ensures that outdated or compromised certificates cannot be used indefinitely.
One-way authentication in secure systems
One-way authentication is a process in which only one party, typically the server, is verified by the client. In this model, the server presents its SSL certificate, and the client validates it before proceeding with communication. The server does not verify the identity of the client during this process.
This type of authentication is commonly used in public-facing systems where users need to access services without requiring identity verification from the server side. It is widely used in websites and online applications where secure data transmission is required, but full mutual verification is not necessary.
One-way authentication ensures that users are connected to legitimate servers and not malicious impostors. However, it does not provide verification of the client, which means the server must rely on additional security measures to manage client interactions.
Despite this limitation, one-way authentication remains highly effective for most standard internet communication scenarios where server identity verification is the primary requirement.
Two-way authentication and mutual verification
Two-way authentication, also known as mutual authentication, involves both the client and server verifying each other’s identity before establishing a secure connection. In this model, both parties present digital certificates that are validated by the opposite side.
This process ensures a higher level of trust because both ends of the communication are authenticated. The client verifies the server’s certificate, while the server verifies the client’s certificate. Only when both validations are successful is a secure connection established.
Two-way authentication is commonly used in high-security environments such as financial systems, enterprise networks, and secure data exchange platforms. It provides an additional layer of protection by ensuring that unauthorized clients cannot access sensitive services.
This method significantly reduces the risk of impersonation and unauthorized access, making it suitable for systems that require strict identity control.
The role of certificate authorities in trust validation
Certificate authorities play a central role in establishing trust within secure communication systems. They are trusted organizations responsible for issuing and validating digital certificates. When a certificate is issued by a recognized authority, it is considered trustworthy by default in most systems.
The certificate authority verifies the identity of the entity requesting the certificate before issuing it. This ensures that only legitimate organizations receive valid certificates. Once issued, the certificate is digitally signed by the authority, allowing clients to verify its authenticity during communication.
When a client receives a certificate, it checks the signature against a list of trusted authorities. If the certificate is signed by a recognized authority, it is accepted. If not, the connection may be flagged as untrusted.
This trust model allows secure communication systems to scale globally while maintaining consistent verification standards.
The SSL handshake process in authentication
The SSL handshake is a critical process that establishes a secure connection between a client and a server. It begins when the client initiates a request to connect to a secure server. The server responds by sending its SSL certificate, which includes its public key and identity information.
The client then verifies the certificate to ensure it is valid and trustworthy. If the certificate passes validation, the client generates a session key and encrypts it using the server’s public key. This encrypted key is then sent back to the server.
The server decrypts the session key using its private key and uses it to establish a secure communication channel. From this point onward, both parties use symmetric encryption for data exchange.
The handshake process ensures that both encryption and authentication are established before any sensitive data is transmitted. It forms the foundation of secure communication sessions and prevents unauthorized access.
Importance of authentication in preventing cyber threats
Authentication plays a critical role in preventing a wide range of cyber threats. Without proper authentication, attackers could impersonate legitimate servers or clients and gain access to sensitive data. This could lead to data theft, identity fraud, and unauthorized system access.
By verifying identities before communication begins, authentication ensures that only trusted entities can participate in secure sessions. This significantly reduces the attack surface and prevents unauthorized access attempts.
Authentication also helps detect fraudulent certificates and suspicious connections. If a certificate does not match expected validation criteria, the connection can be immediately blocked or flagged for further inspection.
This proactive approach strengthens overall system security and ensures that communication remains trustworthy and protected.
Integration of authentication with encryption systems
Authentication and encryption work together to create a completely secure communication system. Authentication ensures that the correct parties are communicating, while encryption ensures that the data being exchanged remains confidential.
Without authentication, encryption alone would not be sufficient to prevent impersonation attacks. Without encryption, authentication alone would not protect sensitive data from interception. Together, they form a unified security framework that protects both identity and information.
This integration ensures that secure communication systems maintain both trust and confidentiality throughout the entire data exchange process.
Continuous validation in secure communication environments
In advanced secure systems, authentication is not limited to the initial connection. Continuous validation mechanisms ensure that the integrity of the session is maintained throughout communication. This includes monitoring session behavior, validating encryption consistency, and ensuring that no unauthorized changes occur during transmission.
Continuous validation strengthens long-term security by ensuring that even established sessions remain protected. It adds a layer of defense that complements initial authentication and encryption processes.
This ongoing verification approach is especially important in systems that handle sensitive or high-value data, where continuous trust validation is required to maintain system integrity.
Understanding ssl certificates in secure communication systems
SSL certificates are digital identity files that play a central role in establishing trust between a client and a server in secure communication environments. They act as verifiable proof that a server is legitimate and that it is authorized to operate under a specific domain or organizational identity. These certificates are essential because they bridge the gap between encryption and authentication, allowing systems to not only secure data but also confirm the identity of the party receiving or sending it.
When a secure connection is initiated, the server presents its SSL certificate to the client. This certificate contains structured identity information, including the domain name, organization details, public key, and digital signature issued by a trusted authority. The client evaluates this information before deciding whether to trust the connection. If the certificate is valid and verified, secure communication proceeds. If not, the connection is blocked or flagged as unsafe.
SSL certificates are not static documents. They have defined validity periods and must be renewed regularly. This ensures that outdated or potentially compromised certificates are not used indefinitely. The presence of a valid certificate ensures that communication is taking place with a verified and trusted source, which is essential for preventing impersonation and fraud.
Structure and key components of SSL certificates
An SSL certificate is composed of several important elements that work together to establish identity and security. One of the most critical components is the public key, which is used during encryption processes. This key allows clients to securely send encrypted data to the server without exposing sensitive information.
Another important element is the identity information, which includes details such as the domain name and organizational identity. This information ensures that the certificate is tied to a specific and verified entity rather than an anonymous source. It allows clients to confirm that they are communicating with the intended server.
The certificate also contains a digital signature issued by a trusted certificate authority. This signature acts as proof that the certificate has been validated and issued by a recognized entity. It ensures that the certificate has not been altered or forged during transmission.
In addition, SSL certificates include validity timestamps that define the active period of the certificate. Once this period expires, the certificate must be renewed to maintain secure communication. These components together ensure that SSL certificates provide both identity verification and cryptographic support for secure communication.
Role of public and private keys in secure systems
Public and private keys form the backbone of modern encryption systems used in secure communication. These keys work together as a pair to enable secure data exchange between systems that may not have prior trust relationships.
The public key is openly shared and is used to encrypt data before it is transmitted. Anyone can access this key, but it can only be used for encryption purposes. The private key, on the other hand, is kept strictly confidential by the server and is used to decrypt incoming data that was encrypted using the public key.
This asymmetric relationship ensures that data encrypted with the public key can only be decrypted by the corresponding private key. This mechanism provides a secure way to exchange information without exposing sensitive decryption keys to external systems.
Public and private key systems are especially important during the initial stages of secure communication. They allow two parties to establish a secure channel without needing to share secret information beforehand. Once the secure channel is established, faster encryption methods are used for ongoing communication.
How cryptographic key pairs enable secure communication
Cryptographic key pairs enable secure communication by ensuring that only intended recipients can access encrypted data. When a client connects to a secure server, it uses the server’s public key to encrypt a session key or sensitive information. This encrypted data can only be decrypted using the server’s private key.
This process ensures that even if encrypted data is intercepted, it cannot be decoded without the private key. This makes interception attacks ineffective because attackers cannot access the original information without the correct decryption mechanism.
Key pairs also support authentication processes. By verifying that a private key matches a known public key, systems can confirm the identity of the server. This ensures that communication is not only encrypted but also authenticated.
The use of cryptographic key pairs creates a secure foundation for all modern encryption systems. They enable both confidentiality and trust, which are essential for secure digital communication.
Certificate authority and trust hierarchy systems
Certificate authorities play a critical role in establishing trust in secure communication systems. They are trusted organizations responsible for issuing digital certificates and verifying the identity of entities requesting them. Without certificate authorities, there would be no standardized way to confirm whether a certificate is legitimate.
When a certificate is issued, the authority performs identity verification checks to ensure that the requesting entity is valid. Once verified, the certificate is digitally signed by the authority, making it recognizable by systems that trust that authority.
Clients maintain a built-in list of trusted certificate authorities. When a certificate is presented, the client checks whether it was issued by a trusted authority. If it is, the certificate is accepted as valid. If not, the connection may be rejected or marked as insecure.
This creates a hierarchical trust system where trusted authorities act as intermediaries between clients and servers. This structure allows secure communication to scale across the internet while maintaining consistent trust validation.
Certificate validation and trust verification process
Certificate validation is the process of verifying whether an SSL certificate is legitimate and trustworthy. When a client receives a certificate from a server, it performs several checks before establishing a secure connection.
The first check involves verifying the digital signature of the certificate. This ensures that the certificate was issued by a trusted authority and has not been altered. The second check involves confirming that the certificate is still within its valid date range. Expired certificates are automatically rejected.
The third check involves verifying that the certificate matches the domain or entity it claims to represent. This prevents attackers from using valid certificates for fraudulent purposes. If all checks pass, the certificate is considered valid, and the secure connection proceeds.
This validation process is essential for preventing unauthorized access and ensuring that users are communicating with legitimate servers.
SSL handshake process in secure communication
The SSL handshake is the initial negotiation process that establishes a secure connection between a client and a server. It begins when the client sends a request to connect to a secure server. The server responds by sending its SSL certificate, which includes its public key and identity information.
The client then validates the certificate using trust verification methods. If the certificate is valid, the client generates a session key and encrypts it using the server’s public key. This encrypted key is then sent back to the server.
The server decrypts the session key using its private key and uses it to establish a secure communication channel. From this point onward, both parties use symmetric encryption for efficient data exchange.
The handshake process ensures that both authentication and encryption are established before any sensitive data is transmitted. It forms the foundation of secure communication sessions and ensures that both parties are verified and trusted.
Security risks addressed by SSL authentication systems.
SSL authentication systems are designed to protect against a wide range of security threats. One of the most common threats is impersonation, where attackers attempt to pose as legitimate servers. SSL certificates prevent this by requiring verified identity proof before establishing connections.
Another major threat is data interception. Without encryption, attackers could capture sensitive data during transmission. SSL systems prevent this by encrypting all data before it is transmitted across networks.
Man-in-the-middle attacks are also a significant risk in unsecured communication. In such attacks, an attacker secretly intercepts and possibly alters communication between two parties. SSL authentication prevents this by verifying both server identity and encryption integrity before communication begins.
These security mechanisms ensure that communication remains private, authenticated, and tamper-resistant throughout the entire session.
Integration of authentication and encryption systems
Authentication and encryption are tightly integrated in secure communication systems. Authentication ensures that both parties are verified before communication begins, while encryption ensures that the data exchanged remains confidential during transmission.
Without authentication, encryption alone would not prevent attackers from impersonating legitimate servers. Without encryption, authentication alone would not protect sensitive data from interception. Together, they form a complete security framework.
This integration ensures that communication is both secure and trustworthy. It allows users to confidently exchange information without fear of exposure or manipulation.
Continuous trust and session protection mechanisms
Modern secure communication systems often include continuous protection mechanisms that monitor active sessions for potential threats. These mechanisms ensure that encryption remains intact throughout the communication process and that no unauthorized changes occur during transmission.
Session keys are also designed to be temporary. Once a communication session ends, the keys are discarded. This reduces the risk of long-term exposure and ensures that each session is independently secured.
This continuous protection approach strengthens overall system security by ensuring that trust is maintained not only at the beginning of communication but throughout the entire session lifecycle.
Final integration of secure communication principles
Secure communication systems are built on the combined principles of encryption, authentication, and trust verification. Encryption ensures data confidentiality, authentication ensures identity verification, and certificate systems ensure trust between unknown parties.
Together, these components create a secure environment where digital communication can take place safely across untrusted networks. Every stage of the communication process is protected through layered security mechanisms that prevent unauthorized access and ensure data integrity.
This integrated system forms the foundation of modern internet security and enables safe digital interactions across global networks.
Conclusion
Secure digital communication has become one of the most essential foundations of modern internet infrastructure, supporting everything from simple website browsing to highly sensitive financial and enterprise-level data exchanges. As digital ecosystems continue to expand, the importance of protecting data in transit has grown significantly. The combination of encryption, authentication, and certificate-based trust systems ensures that communication between clients and servers remains safe, reliable, and resistant to unauthorized interference. Without these mechanisms, the internet as it functions today would not be able to maintain user trust or operational stability.
At the core of secure communication is encryption, which transforms readable information into an unreadable format during transmission. This ensures that even if data is intercepted by malicious actors, it cannot be understood or misused. Encryption provides confidentiality, which is a fundamental requirement in any system handling sensitive data. However, encryption alone is not sufficient to guarantee complete security. It must work alongside authentication systems that verify the identity of communicating parties before any meaningful data exchange occurs. This combination ensures that data is not only protected but also transmitted between trusted entities.
Authentication plays an equally important role by ensuring that both clients and servers can verify each other’s identity before establishing a connection. This prevents impersonation attacks where malicious systems attempt to disguise themselves as legitimate services. Through mechanisms such as SSL certificates and cryptographic validation, authentication introduces a structured trust model that allows systems to distinguish between legitimate and fraudulent entities. This verification process is critical in maintaining secure digital interactions, especially in environments where sensitive data is exchanged frequently.
SSL certificates act as the backbone of this trust system. They provide verifiable identity information about servers and organizations, allowing clients to determine whether a connection is legitimate. These certificates are issued by trusted authorities that validate the identity of the requesting entity before approving. This hierarchical trust structure ensures that only verified participants are allowed to engage in secure communication. The presence of a valid certificate signals that a server has undergone proper verification and is authorized to handle secure data exchanges.
Another essential component of secure communication is the use of public and private key cryptography. These cryptographic key pairs enable secure data exchange without requiring prior shared secrets between communicating parties. The public key is used to encrypt data, while the private key is used to decrypt it. This ensures that even if encrypted data is intercepted, it cannot be decoded without access to the private key. This mechanism is particularly important during the initial stages of communication, where secure key exchange must occur before symmetric encryption can be used.
The handshake process further strengthens secure communication by combining authentication and encryption setup into a single structured sequence. During this process, both the client and server exchange necessary information to establish a secure session. This includes certificate validation, key exchange, and agreement on encryption methods. Once the handshake is complete, a secure session is created where all subsequent data is transmitted using encrypted channels. This ensures that communication is protected from the very beginning of the session lifecycle.
Symmetric encryption then takes over for the duration of the session, providing a faster and more efficient method for continuous data exchange. Since both parties share a single session key, data can be quickly encrypted and decrypted without the computational overhead of asymmetric encryption. This balance between security and performance is what makes modern secure communication systems both effective and scalable.
Security systems also incorporate mechanisms to prevent a wide range of cyber threats. These include protection against data interception, impersonation, and man-in-the-middle attacks. By ensuring that both identity verification and encryption are enforced before communication begins, these systems significantly reduce the risk of unauthorized access. Continuous validation techniques further enhance security by monitoring active sessions and ensuring that no unauthorized changes occur during transmission.
Trust remains a central concept throughout all aspects of secure communication. Every layer of the system, from certificate authorities to encryption algorithms, contributes to building and maintaining this trust. Without trust, users would have no reliable way to determine whether their data is being handled safely. Secure communication protocols ensure that trust is not assumed but verified through structured cryptographic processes.
As digital systems continue to evolve, the demand for stronger and more efficient security mechanisms will continue to grow. Emerging technologies, increased data volumes, and more sophisticated cyber threats require continuous improvements in encryption standards, authentication methods, and trust frameworks. The principles underlying secure communication, however, remain consistent. Protecting data confidentiality, ensuring identity verification, and maintaining system integrity will always be the core objectives.
Ultimately, secure communication is not just a technical requirement but a fundamental necessity for maintaining the stability of the digital world. It enables safe interactions across global networks, supports critical infrastructure, and protects users from evolving cyber threats. By combining encryption, authentication, and trusted verification systems, modern communication frameworks create a secure environment where data can move freely without compromising privacy or integrity.