Virtual Desktop Infrastructure (VDI) is a centralized computing model where desktop operating systems, applications, and user sessions are hosted on server-side infrastructure and delivered remotely to end-user devices over a network. Instead of relying on local computing power, endpoints function primarily as access devices that render user sessions while all processing occurs centrally. This design shifts control away from distributed endpoints and consolidates it within managed data center or cloud environments, allowing organizations to enforce uniform configurations, tighter security controls, and centralized policy enforcement.
From an enterprise standpoint, VDI is not just a remote desktop solution but a full desktop delivery architecture. It supports use cases such as remote workforce enablement, contractor access isolation, secure application publishing, and regulated industry compliance where data residency and control are critical. By decoupling user environments from physical devices, VDI ensures that data does not persist on endpoints, reducing the risk of data leakage or device-based compromise. It also improves operational consistency because every user session is generated from a standardized image or template, eliminating configuration drift across machines.
Scalability is one of the defining advantages of this architecture. Organizations can dynamically allocate resources based on demand without physically modifying endpoint hardware. This makes VDI suitable for environments with fluctuating workloads, seasonal peaks, or global user distribution. At the same time, it introduces architectural complexity, requiring careful coordination between virtualization, brokering, provisioning, and access layers.
Core Architectural Layers That Define VDI Platforms
A VDI ecosystem is structured around multiple interdependent layers, each responsible for a specific operational function. The foundational layer is the virtualization layer, which abstracts physical compute resources into virtual machines using a hypervisor. Above this sits the provisioning layer, which defines how virtual desktops are created, updated, and managed over time. The brokering layer handles session assignment, ensuring users are connected to appropriate resources based on identity, policy, and system availability.
The access layer provides user entry points into the environment through authentication portals or client applications. It ensures that only validated users can initiate sessions. Supporting this is the external access layer, which secures remote connectivity from untrusted networks through encrypted channels and authentication enforcement. Administrative and monitoring layers sit alongside these components, providing visibility into performance metrics, session health, and infrastructure utilization.
Each layer operates independently but is tightly integrated with others. This interdependence means that performance or configuration issues in one layer can propagate across the entire system. As a result, VDI design requires careful architectural planning to maintain stability, scalability, and performance consistency.
Role of Hypervisors in Virtual Desktop Infrastructure
The hypervisor is the foundational component of any VDI environment, responsible for enabling multiple virtual machines to operate on a single physical host. It abstracts hardware resources such as CPU, memory, storage, and network interfaces, distributing them across virtual desktops based on demand and allocation policies. In VDI deployments, hypervisors must support high-density workloads since a single server may host dozens or hundreds of concurrent desktop sessions.
Resource scheduling is a critical function at this layer. The hypervisor ensures that workloads are balanced across physical hosts to prevent resource contention and performance degradation. It also enforces isolation between virtual machines, ensuring that each desktop operates independently and securely from others on the same host. This isolation is essential for both stability and security, particularly in multi-tenant or regulated environments.
Modern hypervisors provide advanced capabilities such as memory optimization, snapshot creation, live migration, and distributed resource management. These features enable administrators to perform maintenance, scale workloads, and recover from failures without disrupting active user sessions. The reliability and efficiency of the hypervisor layer directly impact the overall performance of the VDI environment.
Citrix Virtual Apps and Desktops Architectural Overview
Citrix Virtual Apps and Desktops is built on a modular architecture designed to separate control functions, delivery logic, and user access into distinct components. This separation allows each layer to scale independently while maintaining centralized control over session management and policy enforcement. At the center of this architecture is the delivery control layer, which orchestrates user connections and resource allocation.
The system is designed for flexibility across hybrid environments, supporting on-premises infrastructure as well as cloud-integrated deployments. This allows organizations to distribute workloads across multiple environments while maintaining a unified management model. Policy-driven control is a key characteristic of the architecture, enabling administrators to define rules for access, performance, and security that are consistently applied across all sessions.
Another important aspect of this model is its focus on centralized intelligence. Rather than relying on individual virtual machines for decision-making, Citrix consolidates logic within control components that manage session routing, resource allocation, and user experience optimization. This improves scalability and simplifies operational management in large environments.
Citrix Delivery Controller and Session Brokering Mechanism
The delivery controller is the central orchestration engine in Citrix environments. It is responsible for managing the full lifecycle of user sessions, from authentication through session termination. When a user initiates a connection, the controller evaluates entitlement data, checks resource availability, and determines the most appropriate virtual machine or application host for session assignment.
This process involves continuous communication with hypervisors to monitor virtual machine states, performance metrics, and availability. The controller also interacts with a centralized database that stores configuration metadata, user entitlements, and session information. This ensures that decisions are based on real-time system conditions and predefined policies.
Load balancing is an integral part of this mechanism. The controller distributes sessions across available resources to prevent overload and maintain consistent performance. It also ensures high availability by rerouting sessions in case of machine or host failures. This makes the brokering layer one of the most critical components in maintaining stability and user experience quality in large-scale deployments.
Citrix Provisioning Strategies and Image-Based Deployment Models
Citrix environments support multiple provisioning strategies designed to optimize scalability, storage efficiency, and operational flexibility. One approach is image-based provisioning, where a standardized master image is used as the foundation for creating multiple virtual machines. These machines inherit the same configuration but maintain independent identity and user data through differencing mechanisms.
Another approach is streaming-based provisioning, where operating system images are delivered over the network at runtime. In this model, machines may operate without traditional local storage, relying instead on centralized image streaming. This reduces storage overhead and allows rapid system resets or reinitialization, making it suitable for highly controlled environments.
Both models serve different operational requirements. Image-based provisioning is commonly used for general enterprise workloads due to its balance of performance and manageability. Streaming-based provisioning is used in environments where rapid recovery, strict standardization, or diskless operations are required. Each approach contributes to lifecycle management by enabling centralized updates, patching, and system consistency enforcement.
Machine Creation Services and Provisioning Services Architecture
Machine Creation Services is a provisioning method that uses hypervisor snapshots and base images to generate virtual desktops. Each new machine is created as a linked instance of a master image, allowing efficient storage utilization and simplified management. Changes to the master image can be propagated across all dependent machines, ensuring consistency in system configuration and application deployment.
Provisioning Services operates differently by streaming operating system data directly to target machines over the network. Instead of relying on local storage, machines boot from a centralized image server and load system components dynamically. This allows for diskless or semi-diskless deployments and provides strong control over system states.
Both technologies are used in enterprise environments depending on workload requirements. Machine Creation Services is generally preferred for simplicity and integration, while Provisioning Services is favored in environments requiring strict standardization or rapid system resets. The choice between them depends on infrastructure design, network reliability, and operational goals.
Citrix StoreFront and User Access Experience Layer
StoreFront functions as the primary user interface layer in Citrix environments. It handles authentication, resource enumeration, and session initiation. When a user logs in, StoreFront communicates with backend controllers to retrieve a list of authorized applications and desktops based on identity and assigned policies.
The system presents these resources through a unified interface, allowing users to launch sessions with minimal interaction. It also tracks user preferences, frequently accessed resources, and session history to improve usability over time. Authentication methods supported at this layer include directory-based login, multi-factor authentication, token-based validation, and smart card integration.
StoreFront abstracts infrastructure complexity from the end user, ensuring that users interact only with their assigned resources rather than underlying system architecture. This separation improves usability while maintaining strict backend security controls.
Citrix Secure External Access and Gateway Architecture
External access in Citrix environments is managed through a secure gateway layer that acts as a controlled entry point for remote users. This component performs authentication, encryption, and traffic inspection before allowing access to internal resources. It ensures that no direct connection is established between external devices and internal virtual machines.
The gateway operates as a proxy, relaying session traffic through secure channels while enforcing access policies. It supports advanced networking functions such as traffic filtering, session control, and load balancing. This ensures that external connections are both secure and optimized for performance.
By isolating internal infrastructure from direct exposure, the gateway significantly reduces attack surface and enhances security posture. It is a critical component in environments where remote access is a primary requirement but must remain tightly controlled under enterprise security policies.
Core Design Philosophy of VMware Horizon in Virtual Desktop Infrastructure
VMware Horizon is built around the principle of tight integration between virtualization, session brokering, and desktop delivery. Unlike more modular VDI ecosystems, Horizon is designed to operate within a closely unified infrastructure model where compute, storage, and networking layers are deeply integrated with the virtualization stack. This design reduces operational fragmentation and allows administrators to manage virtual desktops through a centralized control plane that aligns closely with the underlying hypervisor environment.
The architecture emphasizes consistency, performance predictability, and simplified lifecycle management. Instead of distributing control across multiple loosely coupled systems, Horizon centralizes orchestration through connection management services that coordinate user authentication, session assignment, and resource allocation. This approach allows VMware environments to achieve high efficiency in environments where infrastructure standardization is already in place, particularly those built on virtualized data center foundations.
Connection Management Layer and Session Orchestration in VMware Horizon
At the core of VMware Horizon lies the connection management layer, responsible for handling user authentication, session brokering, and desktop assignment. This layer evaluates user identity, entitlement policies, and system availability before directing a session to an appropriate virtual desktop or application host. The connection server acts as the primary decision-making component, ensuring that user sessions are distributed efficiently across available resources.
Unlike more distributed brokering systems, Horizon’s connection management relies heavily on centralized logic. This reduces variability in session assignment behavior and allows administrators to maintain predictable control over user environments. The system continuously communicates with virtualization hosts to monitor resource availability and ensure that session routing decisions reflect real-time infrastructure conditions. This tight integration contributes to reduced latency in session initiation and improved consistency in large-scale deployments.
Instant Clone Technology and Rapid Desktop Provisioning Model
One of the defining features of VMware Horizon is its Instant Clone technology, which enables near-instant creation of virtual desktops from a running parent image. This provisioning model is designed to eliminate traditional delays associated with full virtual machine boot cycles by leveraging in-memory cloning techniques. When a new desktop is required, it is generated almost immediately from a parent VM, inheriting its configuration, memory state, and base system attributes.
Instant Clones operate by creating lightweight, ephemeral virtual machines that share core system components with the parent image while maintaining isolated identity and user state. Any changes made during a session are stored in temporary differencing structures, allowing the desktop to be reset or refreshed rapidly. This design significantly improves operational efficiency in environments with high user turnover or non-persistent desktop requirements.
Compared to traditional cloning methods, Instant Clones reduce storage overhead, accelerate provisioning cycles, and simplify lifecycle management. They also eliminate the need for separate provisioning components, streamlining overall infrastructure complexity while maintaining scalability.
Legacy Provisioning Evolution and Desktop Lifecycle Optimization
Before Instant Clones became the standard, VMware relied on linked clone technology, which required additional management components and introduced dependencies on separate provisioning services. While functional, this approach created operational overhead due to dependency chains between parent images and cloned desktops. Instant Clones replaced this model with a more streamlined architecture that eliminates external dependencies and integrates provisioning directly into the hypervisor workflow.
This evolution reflects a broader shift toward simplifying desktop lifecycle management. Instead of maintaining complex provisioning chains, administrators now manage a single golden image that serves as the source for all desktop instances. Updates to this image can be propagated rapidly across the environment, ensuring consistency without requiring full rebuilds of virtual machines.
VMware Horizon Unified Access Gateway and External Connectivity Model
External access in VMware Horizon environments is handled through a Unified Access Gateway component, which provides secure entry points for remote users without exposing internal infrastructure directly. This gateway operates as a hardened virtual appliance designed to manage authentication, encryption, and session routing for external connections.
The gateway ensures that all incoming traffic is validated before reaching internal systems. It acts as a secure proxy, relaying session traffic between external endpoints and internal connection servers. This design eliminates the need for direct external access to core infrastructure components, significantly reducing exposure to potential security risks.
The Unified Access Gateway also supports load balancing and multi-node configurations, enabling high availability in distributed environments. It is designed to integrate seamlessly with existing network topologies, allowing organizations to deploy secure remote access without major architectural changes.
Display Protocols and User Experience Optimization in VMware Horizon
VMware Horizon uses optimized display protocols to deliver virtual desktop sessions to end-user devices. The primary protocol, Blast Extreme, is designed to adapt dynamically to network conditions, adjusting compression, encoding, and bandwidth usage in real time. This ensures consistent user experience even in environments with variable network performance.
Blast Extreme is optimized for modern workloads, including graphics-intensive applications, multimedia streaming, and multi-monitor configurations. It uses hardware acceleration where available to offload encoding tasks to GPUs, improving performance and reducing server-side CPU usage. In addition, it supports both TCP and UDP transport mechanisms, allowing flexible adaptation based on network stability.
Older protocols such as PCoIP are still supported in certain configurations but have largely been superseded by Blast Extreme due to its efficiency and broader optimization capabilities. The protocol layer plays a critical role in user experience, as it directly affects responsiveness, image quality, and session stability.
VMware Horizon Integration with Virtualization and Storage Layers
A key strength of VMware Horizon is its deep integration with virtualization infrastructure. Virtual desktops are tightly bound to the underlying hypervisor environment, allowing efficient resource scheduling and workload distribution. This integration extends to storage systems as well, where technologies such as shared datastores and distributed storage clusters optimize performance and redundancy.
Storage plays a significant role in VDI performance, particularly in environments with high concurrency. VMware leverages techniques such as caching, deduplication, and storage tiering to optimize I/O operations. In advanced deployments, hyper-converged infrastructure may be used to unify compute and storage resources, reducing latency and improving scalability.
This integration allows Horizon environments to achieve predictable performance characteristics even under heavy load, provided that underlying infrastructure is properly designed and sized.
Management and Administrative Control in VMware Horizon Environments
Administrative control in VMware Horizon is centralized through a unified management console that provides visibility into session activity, resource allocation, and system health. This interface allows administrators to manage desktop pools, configure policies, and monitor infrastructure performance from a single control plane.
The management layer is designed to reduce operational complexity by consolidating configuration and monitoring functions. Administrators can define desktop pools based on usage patterns, assign entitlements to user groups, and enforce policies related to session behavior and resource consumption. This centralized approach simplifies large-scale environment management and reduces the need for distributed configuration changes.
Automation also plays a significant role in administration. Policy-based management allows environments to adjust dynamically to user demand without requiring manual intervention. This improves operational efficiency and reduces the likelihood of configuration drift across virtual desktop pools.
VMware Horizon Cloud and Hybrid Deployment Architecture
VMware Horizon supports hybrid deployment models that extend virtual desktop infrastructure beyond traditional on-premises environments. In these configurations, workloads can be distributed across private data centers and cloud environments, allowing organizations to optimize resource utilization and geographic accessibility.
Hybrid architectures enable flexible scaling strategies where desktops can be provisioned closer to end users to reduce latency or shifted between environments based on demand. This flexibility is particularly useful in global organizations where user distribution spans multiple regions.
The cloud-integrated model also supports disaster recovery scenarios, where virtual desktop environments can be replicated or reconstituted in alternate infrastructure locations. This enhances resilience and ensures business continuity in the event of infrastructure failure.
Performance Engineering Considerations in VMware Horizon Deployments
Performance optimization in Horizon environments is closely tied to infrastructure design, including compute density, storage performance, and network configuration. Because virtual desktops are sensitive to latency and resource contention, careful capacity planning is required to ensure consistent user experience.
CPU allocation, memory overcommitment, and storage I/O performance all play critical roles in determining system responsiveness. VMware environments often rely on resource scheduling mechanisms to balance workloads across hosts and prevent performance degradation. In addition, display protocol optimization ensures that network conditions do not significantly impact user experience.
Performance engineering also involves monitoring system health and identifying bottlenecks at the hypervisor, storage, or network layers. This holistic approach ensures that VDI environments maintain consistent performance even under variable load conditions.
Security Architecture and Access Control in VMware Horizon
Security in VMware Horizon is enforced through layered access control mechanisms that regulate authentication, session initiation, and data transmission. User authentication is handled through centralized identity services, ensuring that only authorized users can access virtual desktops.
Session traffic is encrypted end-to-end, preventing interception or unauthorized access during transmission. The Unified Access Gateway further strengthens security by isolating external traffic from internal infrastructure. This layered approach reduces attack surface and ensures that sensitive data remains protected throughout the session lifecycle.
Policy enforcement mechanisms allow administrators to define access rules based on user identity, device type, or network location. This ensures that security policies are consistently applied across all sessions, regardless of access method.
Comparative Architectural Dynamics Between Citrix and VMware VDI Models
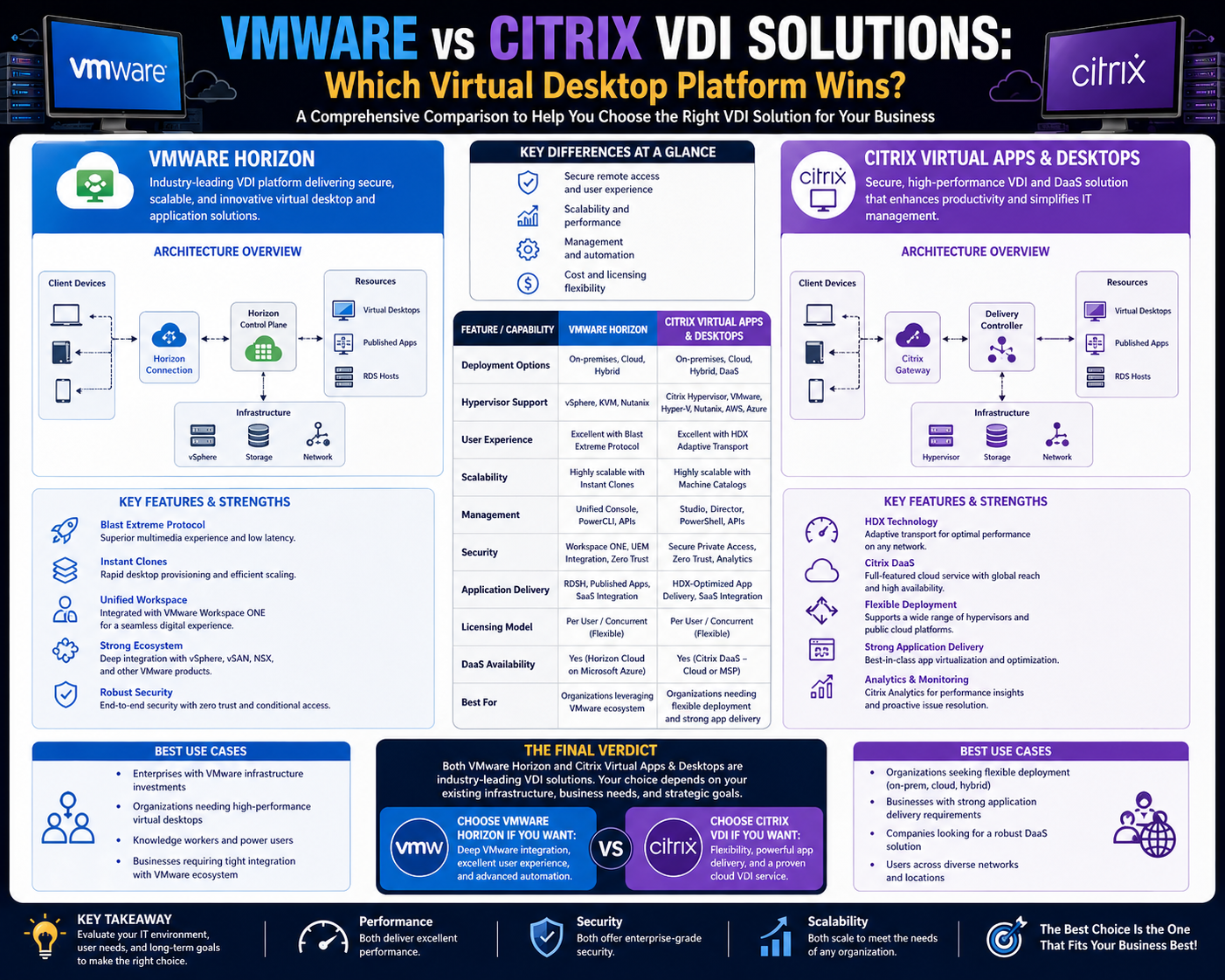
While both Citrix and VMware achieve the same fundamental goal of delivering virtual desktops, their architectural philosophies differ significantly. Citrix emphasizes modularity and flexibility, with distinct components handling provisioning, brokering, and access independently. VMware, on the other hand, focuses on tight integration between virtualization and desktop delivery layers, resulting in a more unified but less modular structure.
Citrix environments often provide greater flexibility in heterogeneous infrastructure environments, while VMware environments excel in tightly controlled, standardized virtualization ecosystems. These differences influence decisions around scalability, operational complexity, and infrastructure design preferences.
In performance terms, both platforms are capable of supporting large-scale deployments, but their optimization strategies differ. Citrix relies heavily on adaptive policy-driven control, while VMware focuses on infrastructure-level integration and resource optimization. These distinctions shape how each platform behaves under load and how administrators manage long-term scalability and maintenance strategies.
Citrix and VMware VDI Scalability Architecture in Enterprise Environments
Scalability is one of the most critical design considerations in virtual desktop infrastructure, and both Citrix and VMware approach it through fundamentally different architectural philosophies. Citrix environments are built around distributed modular components, allowing each layer—brokering, provisioning, access, and management—to scale independently. This separation enables fine-grained expansion where specific components can be scaled based on demand without necessarily expanding the entire infrastructure stack. For example, additional delivery controllers can be introduced to handle increased session brokering load, while additional StoreFront nodes can be deployed to handle authentication traffic.
VMware Horizon, in contrast, relies on a more tightly integrated scaling model where connection servers, hypervisor clusters, and provisioning mechanisms are closely aligned. Scaling typically occurs by expanding underlying virtualization clusters, which in turn increases capacity for virtual desktops and sessions. This approach simplifies architectural consistency but can reduce flexibility in heterogeneous environments. In large deployments, scalability is achieved by expanding compute clusters and ensuring that storage and networking layers scale proportionally to maintain performance balance.
Both models are capable of supporting enterprise-scale deployments, but the operational implications differ significantly. Citrix allows more granular scaling of individual services, while VMware emphasizes predictable scaling through infrastructure expansion. The choice between these models often depends on whether the organization prioritizes modular flexibility or infrastructure uniformity.
Session Performance Optimization and User Experience Delivery Models
User experience in VDI environments is heavily influenced by how efficiently session data is transmitted between servers and endpoints. Citrix and VMware both employ advanced display protocol technologies, but their optimization strategies differ in execution. Citrix relies on adaptive display technologies that dynamically adjust compression, latency handling, and bandwidth consumption based on real-time network conditions. This allows sessions to remain responsive even in unstable or low-bandwidth environments.
VMware uses a similarly adaptive protocol approach but integrates deeper optimization at the hypervisor and hardware acceleration level. By leveraging GPU acceleration and intelligent encoding mechanisms, VMware ensures that graphical workloads, multimedia applications, and multi-monitor setups maintain consistent performance. Both platforms aim to reduce perceived latency and optimize rendering efficiency, but VMware tends to emphasize hardware-level integration while Citrix focuses on network-level adaptability.
In enterprise environments, user experience consistency is a critical metric. Factors such as input latency, frame rendering speed, and session stability all contribute to perceived performance. Optimization strategies must therefore consider not only raw throughput but also variability in network conditions and endpoint capabilities. This makes protocol tuning and infrastructure alignment essential for maintaining consistent user satisfaction.
Storage Architecture and Data Efficiency Strategies in VDI Environments
Storage is one of the most resource-intensive components in any VDI deployment, and both Citrix and VMware implement strategies to reduce storage overhead while maintaining performance. Citrix environments often rely on shared image provisioning models where multiple virtual machines reference a single master image. This reduces redundant storage consumption and ensures consistency across desktop instances. Differencing disks and caching mechanisms are used to separate system-level data from user-specific changes.
VMware adopts a similar strategy through Instant Clone architecture, which minimizes storage duplication by sharing base image components across multiple virtual machines. In addition, VMware environments often integrate with high-performance storage systems that support caching, deduplication, and tiered storage allocation. This ensures that frequently accessed data is stored in high-speed tiers while less critical data is moved to lower-cost storage layers.
Both platforms benefit significantly from storage optimization techniques such as block-level deduplication and memory caching. However, VMware’s tighter integration with virtualization infrastructure often results in more predictable storage performance, while Citrix environments may require more external tuning depending on provisioning model selection.
Network Dependency and Traffic Engineering in Virtual Desktop Infrastructure
Network performance plays a decisive role in VDI usability, as all user interactions are transmitted over network channels. Citrix and VMware address this dependency through different traffic engineering strategies. Citrix environments are designed to operate efficiently even over constrained networks by compressing session data and prioritizing user input responsiveness. Adaptive network optimization techniques adjust transmission rates dynamically based on latency and packet loss conditions.
VMware, on the other hand, emphasizes protocol efficiency combined with infrastructure-level optimization. By leveraging intelligent encoding and hardware acceleration, VMware reduces the amount of data transmitted over the network while maintaining high-quality session rendering. This reduces bandwidth consumption in high-density environments while preserving graphical fidelity.
Network segmentation and routing design also play a key role in VDI performance. Proper separation of management traffic, storage traffic, and user session traffic ensures that network congestion does not degrade user experience. Both Citrix and VMware recommend dedicated network paths for different traffic types to maintain predictable performance under load.
Security Architecture and Zero Trust Alignment in VDI Platforms
Security is a foundational requirement in virtual desktop environments, particularly as organizations transition toward remote and hybrid workforce models. Citrix and VMware both implement layered security architectures designed to enforce authentication, authorization, and data protection at multiple levels.
Citrix environments rely heavily on centralized access control combined with secure gateway enforcement. All external connections are routed through controlled access points that validate user identity before granting session access. Multi-factor authentication, identity federation, and policy-based access controls are commonly integrated into the authentication layer. This ensures that only verified users can access virtual resources.
VMware employs a similar layered approach but integrates security more deeply into the virtualization stack. Access control is enforced at the connection server level, while external access gateways ensure that no direct exposure to internal systems occurs. Encryption is applied to all session traffic, and policy-based controls determine session behavior based on user identity, device posture, and network location.
Both platforms align well with zero trust security principles, where no user or device is inherently trusted. Continuous validation and contextual access enforcement ensure that security is maintained throughout the session lifecycle rather than only at login.
Administrative Operations and Lifecycle Management in VDI Environments
Operational management in VDI environments involves continuous monitoring, maintenance, and optimization of virtual desktops and supporting infrastructure. Citrix provides a modular administrative model where different components are managed through specialized interfaces. This allows administrators to independently manage brokering, provisioning, and access layers, but it also introduces operational complexity due to distributed control points.
VMware adopts a more centralized administrative approach, where most operational tasks are managed through a unified interface. This includes desktop pool configuration, resource allocation, and session monitoring. The centralized model simplifies administration but requires careful coordination with underlying infrastructure components to maintain consistency.
Lifecycle management is a critical operational function in both environments. It includes image updates, patch deployment, session monitoring, and resource optimization. Automated processes are often used to refresh virtual desktops, ensuring that systems remain compliant with security and performance standards. This reduces manual intervention and ensures consistency across large-scale deployments.
Hybrid and Multi-Cloud Integration Strategies in Modern VDI Deployments
Modern VDI architectures increasingly rely on hybrid and multi-cloud strategies to improve scalability, resilience, and geographic distribution. Citrix environments are particularly well-suited to multi-cloud deployments due to their modular architecture, which allows components to be distributed across different infrastructure providers. This enables organizations to place workloads closer to end users while maintaining centralized control.
VMware Horizon also supports hybrid deployments through integration with cloud-based virtualization environments. This allows virtual desktops to be deployed across private data centers and cloud platforms, providing flexibility in workload distribution. Hybrid models are often used for disaster recovery, workload bursting, and regional optimization.
In both cases, hybrid deployment introduces additional complexity in networking, identity management, and policy enforcement. However, it also provides significant advantages in scalability and resilience, allowing organizations to dynamically adjust infrastructure based on demand and availability.
Performance Monitoring and Infrastructure Analytics in VDI Systems
Monitoring and analytics play a crucial role in maintaining VDI performance and stability. Both Citrix and VMware provide extensive monitoring capabilities that track session performance, resource utilization, and infrastructure health. These metrics are used to identify bottlenecks, optimize resource allocation, and predict capacity requirements.
Citrix environments typically emphasize session-level analytics, providing detailed insights into user experience, application responsiveness, and resource consumption. VMware environments focus more on infrastructure-level metrics, including hypervisor performance, storage latency, and network throughput. Together, these metrics provide a comprehensive view of system health.
Predictive analytics is increasingly being used to forecast demand and optimize resource allocation proactively. By analyzing historical usage patterns, administrators can anticipate peak usage periods and adjust resource allocation accordingly. This improves efficiency and reduces the likelihood of performance degradation during high-demand periods.
Enterprise Deployment Decision Factors Between Citrix and VMware VDI
Choosing between Citrix and VMware for virtual desktop infrastructure depends on multiple architectural, operational, and organizational factors. Citrix is often favored in environments requiring high flexibility, multi-platform support, and granular control over session behavior. Its modular architecture allows organizations to customize individual components based on specific requirements.
VMware is typically preferred in environments where infrastructure standardization, simplicity, and tight integration with virtualization platforms are prioritized. Its unified architecture reduces operational complexity and provides consistent performance across standardized environments.
Both platforms are capable of supporting large-scale enterprise deployments, but their suitability depends on existing infrastructure investments, operational expertise, and long-term scalability goals. Organizations with highly heterogeneous environments may benefit from Citrix’s flexibility, while those with standardized virtualization ecosystems may find VMware more efficient operationally.
Evolution of Virtual Desktop Infrastructure in Modern IT Ecosystems
Virtual desktop infrastructure continues to evolve as organizations adapt to changing workforce models, security requirements, and cloud adoption strategies. The shift toward hybrid work environments has accelerated the demand for scalable, secure, and flexible desktop delivery systems. Both Citrix and VMware have adapted their platforms to support these changes by integrating cloud capabilities, improving provisioning efficiency, and enhancing user experience optimization.
Future VDI architectures are expected to further integrate with artificial intelligence-driven resource management, predictive scaling, and automated security enforcement. These advancements will reduce administrative overhead while improving performance consistency and security posture. As enterprise computing continues to shift toward centralized and cloud-based models, VDI will remain a critical component of digital workspace strategies.
Conclusion
Virtual Desktop Infrastructure represents a major shift in how enterprise computing environments are designed, delivered, and managed. Instead of relying on decentralized endpoints with locally installed operating systems and applications, VDI consolidates desktop workloads into centralized infrastructure. This architectural shift changes not only technical operations but also organizational strategy, security posture, and end-user computing experiences. Both Citrix Virtual Apps and Desktops and VMware Horizon address this requirement, but they approach the solution with different engineering philosophies that influence how each platform behaves in real-world deployments.
Citrix is fundamentally built around modularity and flexibility. Its architecture separates key functions such as brokering, provisioning, and access into distinct components that can be scaled or modified independently. This design makes Citrix particularly well-suited for complex environments where infrastructure is heterogeneous or distributed across multiple platforms. Organizations that operate across different hypervisors, cloud providers, or legacy systems often benefit from this adaptability. Citrix also provides deep control over session behavior, user experience tuning, and application delivery logic, which makes it attractive for environments requiring fine-grained customization.
However, this flexibility comes with operational complexity. Because Citrix environments consist of multiple interconnected components, administrators must manage and maintain several layers of infrastructure logic. Each layer must be properly configured and continuously monitored to ensure system stability. While this allows for powerful customization, it also increases the skill requirement for operational teams and introduces more potential points of failure if not properly designed.
VMware Horizon, on the other hand, is built around integration and standardization. Its architecture tightly couples virtualization infrastructure with desktop delivery mechanisms, reducing the number of independent components that must be managed separately. This results in a more streamlined operational model where virtual desktops, connection servers, and provisioning systems work within a unified ecosystem. For organizations already standardized on VMware virtualization technologies, this integration provides a natural extension into VDI without requiring significant architectural divergence.
Horizon’s Instant Clone technology is a key differentiator in this space, enabling extremely fast provisioning of virtual desktops with minimal storage overhead. This allows organizations to rapidly scale environments in response to demand while maintaining consistent performance. The simplified provisioning model also reduces operational complexity, making it easier for IT teams to manage large-scale deployments without extensive manual intervention. However, this streamlined approach can be less flexible in highly heterogeneous environments where multiple infrastructure platforms must coexist.
From a performance perspective, both platforms are capable of delivering high-quality virtual desktop experiences, but their optimization strategies differ. Citrix focuses heavily on adaptive network and session optimization, ensuring usability even in constrained or unstable network conditions. This makes it particularly effective for geographically distributed users or environments with variable connectivity. VMware, in contrast, emphasizes deep integration with hardware acceleration and virtualization infrastructure, optimizing performance at the compute and graphics rendering level. This results in highly consistent performance in environments with strong underlying infrastructure.
Security is another area where both platforms converge in principle but differ in implementation. Citrix relies on a layered security model where external access is strictly controlled through gateway components and policy-based enforcement. It places strong emphasis on secure session delivery and centralized authentication. VMware also implements a layered security model but integrates access control more closely with its connection and virtualization layers, reducing external exposure points. Both platforms align well with modern zero trust security principles, ensuring that authentication, authorization, and encryption are enforced consistently across all sessions.
Storage and resource efficiency are also key considerations in VDI design. Citrix employs image streaming and provisioning strategies that minimize storage duplication while maintaining flexibility in desktop lifecycle management. VMware achieves similar efficiency through Instant Clones and shared image architectures, which reduce storage consumption and accelerate provisioning. In both cases, the goal is to minimize redundancy while ensuring rapid scalability and consistent system states across virtual machines.
Network dependency remains one of the most critical factors influencing VDI performance. Since all user interactions must traverse network channels, latency and bandwidth conditions directly impact user experience. Citrix is often considered more resilient in low-bandwidth or high-latency environments due to its adaptive display protocols and compression techniques. VMware compensates through protocol efficiency and hardware-accelerated encoding, which reduces bandwidth consumption while maintaining high fidelity. Both approaches are effective, but their suitability depends on the network conditions and use case requirements of the organization.
Operational management differs significantly between the two platforms. Citrix provides a more distributed administrative model, offering granular control over individual components and policies. This enables highly customized environments but requires greater operational discipline. VMware provides a more centralized management experience, simplifying administration through unified interfaces and standardized workflows. This reduces operational overhead but may limit customization in highly specialized environments.
When evaluating long-term strategy, organizations must consider not only technical capabilities but also operational maturity, skill availability, and infrastructure alignment. Citrix is often chosen by enterprises that require maximum flexibility and multi-environment compatibility. VMware is often selected by organizations that prioritize simplicity, integration, and alignment with existing virtualization investments. Both approaches are valid, but they reflect different priorities in infrastructure design philosophy.
As enterprise IT continues to evolve, VDI platforms are increasingly influenced by cloud adoption, hybrid workforce models, and automation-driven operations. Both Citrix and VMware have adapted to these trends by integrating cloud capabilities, improving automation frameworks, and enhancing scalability. The direction of the industry suggests a continued convergence toward hybrid architectures where workloads can dynamically move between on-premises and cloud environments based on demand, performance, and cost considerations.
Ultimately, virtual desktop infrastructure is no longer just a remote access solution. It has become a strategic platform for delivering secure, scalable, and consistent digital workspaces. The differences between Citrix and VMware reflect broader architectural trade-offs between flexibility and integration, complexity and simplicity, and customization and standardization. Understanding these trade-offs is essential for designing environments that align with both technical requirements and long-term organizational goals.