Fortinet’s certification ecosystem has evolved significantly as cybersecurity has shifted from static, perimeter-based defense into a highly distributed and cloud-driven discipline. Earlier certification models were built on a strict linear progression where professionals moved step-by-step through numbered levels. That approach worked well when enterprise networks were centralized and job roles were clearly defined.
Today’s cybersecurity environments are far more complex. Organizations operate across hybrid cloud infrastructures, remote access systems, SaaS platforms, and globally distributed networks. Security responsibilities are no longer uniform or linear. Instead, they are divided into specialized domains such as network security engineering, cloud security architecture, security operations, and identity-based access control.
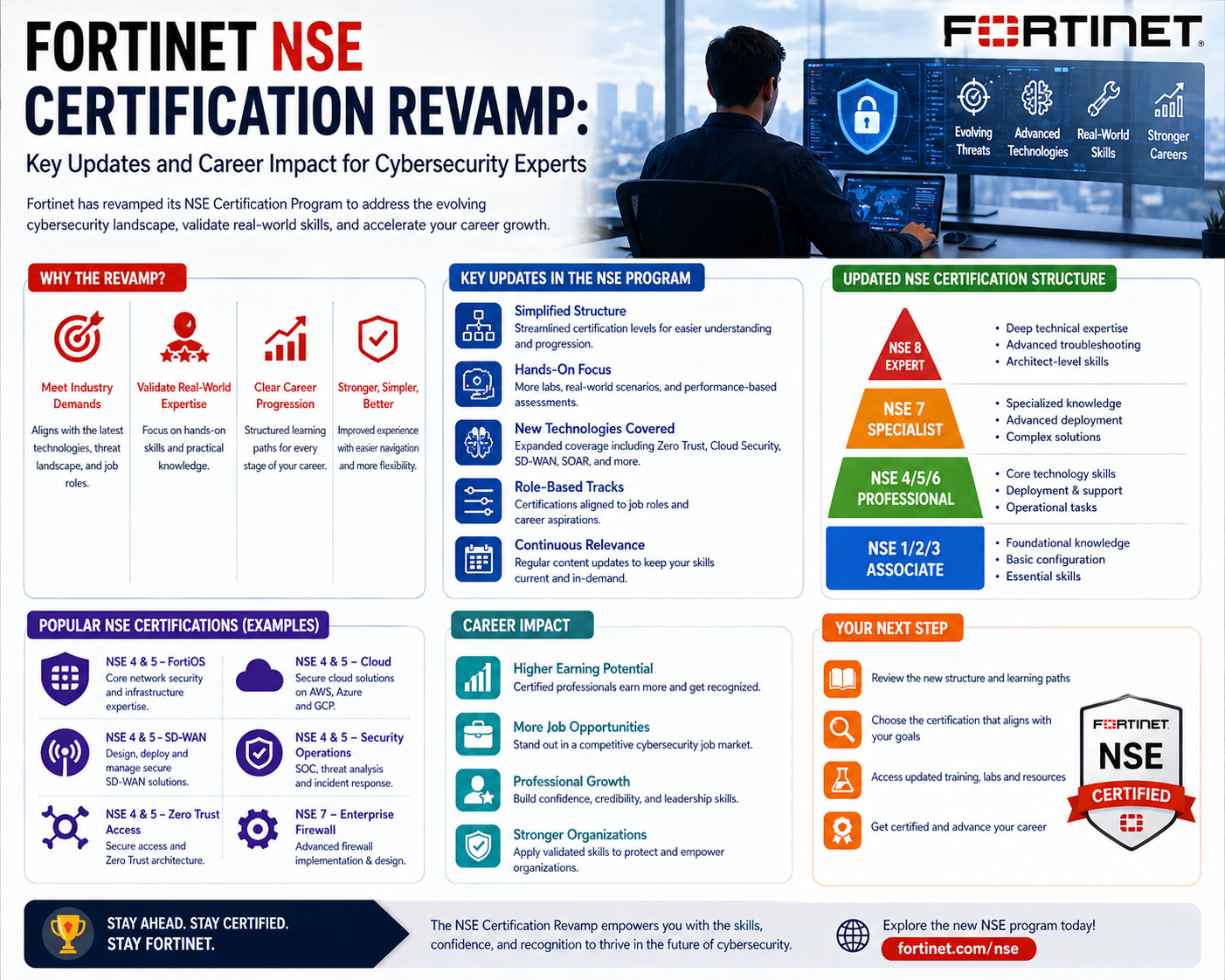
Because of this shift, Fortinet redesigned its certification philosophy to better match real-world job functions. The goal is no longer just progression through levels but alignment with actual professional roles and responsibilities. This allows individuals to focus on relevant skills instead of following a rigid sequence that may not match their career path.
Even with this transformation, the underlying technical rigor remains intact. The certification structure still ensures clear progression in complexity, but it is now embedded within a more flexible and practical framework.
Shift from Linear Certification Paths to Modular Skill Architecture
The earlier certification model followed a strict sequential ladder where each certification depended on completing the previous level. While this provided structure, it limited flexibility for professionals entering specialized cybersecurity roles.
The modern framework replaces that rigidity with a modular architecture. Instead of a single pathway, certifications are organized into multiple interconnected tracks based on cybersecurity domains. Each track represents a specific functional area rather than a generalized progression route.
This modular design reflects how cybersecurity teams operate in real environments. Organizations no longer rely on generalists to manage all aspects of security. Instead, they depend on specialists who focus on specific areas such as infrastructure security, cloud protection, or security operations.
The modular system allows professionals to enter certification paths at different points depending on their experience. This reduces redundancy for experienced individuals while still providing structured learning for beginners.
Despite the flexibility, internal structure still exists. Each certification level is mapped to a defined level of technical complexity, ensuring consistency across all specialization areas.
Role-Based Certification Structure and Functional Domains
The modern certification system is organized into role-based categories that reflect real cybersecurity job functions. Each category represents a different level of responsibility and technical depth.
The foundational level focuses on core cybersecurity concepts. It introduces basic principles such as threat awareness, risk understanding, and fundamental security operations. This stage is designed for individuals entering cybersecurity for the first time.
The associate level builds on this foundation by introducing operational skills. Professionals begin working with security tools in practical environments, learning configuration basics, system behavior, and fundamental management tasks.
The professional level represents a significant increase in responsibility. At this stage, individuals are expected to manage and secure enterprise environments using integrated security technologies. This includes firewall management, policy enforcement, secure network design, and cloud security implementation. This level is divided into multiple specialization tracks.
The solution specialist level focuses on advanced system design and implementation. Professionals at this stage are responsible for building complex security architectures that operate across hybrid environments and multiple platforms.
The expert level represents the highest tier of certification. It is intended for senior professionals who handle highly complex environments requiring deep technical expertise, architectural design, and advanced troubleshooting across multiple security domains.
Each category reflects increasing responsibility, technical complexity, and decision-making authority within cybersecurity operations.
Integration of Exam Levels with Certification Identity
Although certifications are now presented in a role-based format, the underlying exam structure still follows a defined hierarchy. This ensures that technical difficulty increases consistently across all levels.
Lower-level exams focus on foundational understanding and basic operational knowledge. These assessments evaluate whether candidates understand core cybersecurity concepts and can apply them in controlled environments.
Mid-level exams introduce more advanced scenarios involving configuration, troubleshooting, and system management in enterprise contexts.
Higher-level exams focus on architectural design and multi-system integration. Candidates must demonstrate the ability to solve complex problems across distributed environments.
At the highest level, practical exams simulate real-world enterprise conditions where candidates must configure, troubleshoot, and optimize complex security systems under constraints.
This layered structure ensures that certification holders are evaluated on both theoretical knowledge and practical ability.
Specialization Tracks and Alignment with Industry Roles
A major advancement in the modern certification model is the introduction of specialization tracks. These tracks align certifications with specific cybersecurity job functions.
Specialization allows professionals to focus on areas such as secure networking, cloud security, security operations, and secure access architecture. Each track represents a distinct operational domain within enterprise security.
Secure networking focuses on protecting infrastructure through firewalls, intrusion prevention systems, and traffic management tools. Cloud security focuses on protecting workloads and applications in cloud environments. Security operations focuses on monitoring, detection, and incident response. Secure access focuses on identity-based access control across distributed systems.
This specialization reflects how cybersecurity teams are structured in modern enterprises. Organizations rely on domain experts rather than generalists to manage specific parts of the security ecosystem.
Despite specialization, all tracks share a common foundational base, ensuring consistency and enabling professionals to transition between domains when needed.
Impact of Certification Changes on Career Development Pathways
The shift to modular certification has significantly changed how cybersecurity professionals approach career development. Instead of following a fixed sequence, individuals can now tailor their learning paths based on job roles and career goals.
This flexibility allows faster skill development in specific domains. Professionals can focus directly on relevant competencies without unnecessary training in unrelated areas.
At the same time, the structured hierarchy still supports long-term career progression. Professionals can expand into advanced certifications or additional specialization areas over time.
This creates a dual progression model that supports both depth and breadth of expertise, allowing individuals to grow within a single domain or across multiple cybersecurity disciplines.
Industry Drivers Behind Certification Modernization
The redesign of the certification system is closely tied to major industry changes. Cybersecurity has shifted from perimeter-based defense to distributed, cloud-centric security models.
Modern organizations operate without a fixed security boundary. Users connect from multiple locations, applications run across cloud platforms, and security controls are distributed across endpoints, networks, and identity systems.
This complexity requires professionals who can operate across multiple security layers. Certification systems have evolved to reflect this need by emphasizing specialization and practical application.
Automation and artificial intelligence have also transformed cybersecurity operations. Security teams now rely on automated detection, threat intelligence platforms, and real-time analytics. Professionals must understand how to work alongside these systems effectively.
The modern certification framework prepares individuals for these realities through scenario-based and role-focused training structures.
Rebuilding Certification Structure Around Real-World Cybersecurity Roles
The modern Fortinet certification framework continues its evolution by shifting even more strongly toward real-world job alignment rather than theoretical progression models. This change is driven by how cybersecurity roles have diversified across enterprise environments. Instead of a single security administrator handling all responsibilities, modern organizations divide responsibilities into highly specialized functions that require distinct technical expertise.
This restructuring is not cosmetic. It reflects a deeper change in how cybersecurity is executed operationally. Network security engineers, cloud security architects, SOC analysts, and identity access specialists all operate within different technical ecosystems. A single linear certification path cannot realistically represent this diversity, which is why the current model is built around functional domains.
Each certification tier now represents a professional role category rather than just a knowledge level. This ensures that certifications map directly to real job responsibilities, improving relevance for employers and practitioners alike. The system allows professionals to demonstrate capability in a specific domain without being forced through unrelated technical areas.
This role-based approach also improves workforce scalability. Organizations can now identify certified professionals based on specific operational needs rather than generalized certification levels. This makes hiring, team structuring, and skill validation more precise and efficient.
At the same time, the framework maintains internal consistency by ensuring that all roles are built on a shared cybersecurity foundation. This prevents fragmentation of knowledge and ensures that professionals across different domains still understand core security principles.
Deep Dive into Foundational and Associate-Level Competency Development
The foundational certification level serves as the entry point into the cybersecurity ecosystem. It is designed for individuals who are either new to IT security or transitioning from adjacent technical roles. The primary focus at this level is conceptual clarity rather than technical depth.
Candidates at this stage are introduced to fundamental cybersecurity concepts such as threat types, attack vectors, risk exposure, and security objectives. The emphasis is on understanding how cybersecurity functions within an organizational context rather than implementing technical solutions.
This foundational layer is essential because it establishes a shared vocabulary that supports all higher-level learning. Without this baseline understanding, advanced topics such as network segmentation, cloud workload protection, or incident response become significantly harder to grasp.
The associate level builds on this foundation by introducing operational familiarity with security systems. At this stage, professionals begin working with actual security platforms in controlled environments. The focus shifts from theory to practical exposure.
Individuals at this level learn how security devices function, how policies are applied, and how basic configurations are managed. This includes understanding how traffic flows through security systems and how different components interact within a network security architecture.
The associate level is particularly important because it bridges the gap between conceptual knowledge and real-world operational work. It prepares professionals for entry-level roles where they are expected to support security operations under supervision.
Professional-Level Certifications and Domain Specialization Expansion
The professional level represents a major shift in responsibility and technical depth. At this stage, certifications are no longer general in nature. Instead, they are divided into specialized tracks that align with distinct cybersecurity domains.
These tracks include areas such as secure networking, cloud security, security operations, and secure access management. Each track represents a focused discipline that corresponds to specific job roles within enterprise environments.
Secure networking focuses on protecting enterprise infrastructure. Professionals in this domain work with firewalls, intrusion prevention systems, routing policies, and network segmentation strategies. The goal is to ensure that internal and external communication remains secure, controlled, and monitored.
Cloud security focuses on protecting workloads and applications deployed in public or hybrid cloud environments. This includes securing virtual machines, containerized applications, and cloud-native services. Professionals in this domain must understand both cloud architecture and security enforcement mechanisms.
Security operations focuses on monitoring and responding to security events. This includes working with security information and event management systems, analyzing logs, detecting anomalies, and responding to incidents. Professionals in this area play a critical role in identifying and mitigating threats in real time.
Secure access focuses on identity-driven security models. This includes managing user authentication, authorization, and access control across distributed environments. The goal is to ensure that only authorized users and devices can access specific resources.
By dividing the professional level into these domains, the certification system ensures that individuals can specialize deeply in their chosen field while still maintaining alignment with broader cybersecurity principles.
Solution Specialist Level and Advanced Architecture Design
The solution specialist level represents a transition from operational execution to architectural design and system engineering. At this stage, professionals are expected to design and implement complex security infrastructures that span multiple environments and technologies.
This includes hybrid architectures that integrate on-premises systems with cloud platforms, distributed security frameworks that operate across global networks, and advanced policy enforcement systems that ensure consistent security controls.
Unlike the professional level, which focuses on execution and management, the solution specialist level emphasizes design thinking. Professionals must understand how different security components interact at a system-wide level and how to optimize them for performance, scalability, and resilience.
This level requires a deep understanding of integration challenges. Security systems rarely operate in isolation, so professionals must account for interoperability between different platforms, tools, and protocols.
In addition, solution specialists must consider organizational requirements such as compliance, regulatory constraints, and business continuity. This adds another layer of complexity to system design, requiring both technical and strategic thinking.
The solution specialist level effectively bridges the gap between hands-on engineering and enterprise-level architecture design. It prepares professionals for leadership roles in technical security planning.
Expert-Level Certification and Enterprise Security Mastery
The expert level represents the highest tier of certification within the framework. It is designed for professionals who operate in highly complex environments where multiple security domains intersect.
At this level, individuals are expected to demonstrate mastery across network security, cloud security, security operations, and identity management systems. The focus is not just on technical execution but on architectural decision-making and strategic problem solving.
Expert-level professionals are often responsible for designing large-scale security infrastructures that support entire organizations. This includes global network architectures, multi-cloud security frameworks, and advanced threat mitigation systems.
The complexity at this level lies in integration and optimization. Professionals must ensure that all components of the security ecosystem work together efficiently while maintaining strong protection against evolving threats.
Expert certification also emphasizes real-world troubleshooting under pressure. Candidates must be able to diagnose complex issues that span multiple systems and resolve them without disrupting business operations.
This level is widely regarded as one of the most challenging vendor-specific cybersecurity certifications due to its depth and practical focus.
Evolving Exam Structure and Practical Assessment Models
Although certifications are now presented in a role-based format, the underlying exam system remains structured around increasing levels of difficulty. This ensures that technical progression remains consistent even as certification naming evolves.
Lower-level exams focus on conceptual understanding and basic system interaction. These assessments evaluate whether candidates understand core cybersecurity principles and can apply them in simple environments.
Mid-level exams introduce operational complexity. Candidates must demonstrate the ability to configure systems, manage security policies, and troubleshoot common issues within enterprise environments.
Higher-level exams introduce architectural and design challenges. Candidates are evaluated on their ability to build and manage complex security systems that integrate multiple technologies.
At the expert level, exams are highly practical and scenario-based. Candidates are placed in simulated enterprise environments where they must solve real-world problems under time constraints. These scenarios often involve multiple interconnected systems and require deep technical understanding.
This progression ensures that certification holders are not only knowledgeable but also capable of applying their skills in real operational environments.
Expansion of Cloud Security and Distributed Architecture Focus
One of the most significant shifts in the certification framework is the increased emphasis on cloud security and distributed architectures. As organizations move workloads to cloud environments, traditional perimeter-based security models are no longer sufficient.
Modern cybersecurity frameworks must account for dynamic infrastructure, elastic workloads, and globally distributed systems. This requires professionals who understand both traditional networking principles and cloud-native security models.
Cloud security certifications focus on protecting workloads, applications, and data across public and hybrid cloud environments. This includes identity management, workload isolation, encryption strategies, and policy enforcement across distributed systems.
The integration of cloud security into the certification framework reflects its importance as a core cybersecurity discipline rather than an optional specialization.
Security Operations and Real-Time Threat Response Evolution
Security operations have become one of the most critical domains in modern cybersecurity environments. The ability to detect, analyze, and respond to threats in real time is essential for maintaining organizational security.
The certification framework reflects this by placing increased emphasis on operational monitoring, incident response, and threat intelligence analysis.
Professionals in this domain must understand how to interpret security logs, identify anomalies, and respond to potential threats before they escalate. This requires both technical knowledge and analytical thinking.
Automation also plays a significant role in modern security operations. Professionals must be able to work alongside automated systems that handle routine detection and response tasks while focusing on complex threat analysis.
This evolution reflects the increasing speed and sophistication of cyber threats in modern environments.
Long-Term Structural Direction of Certification Ecosystem
The current certification framework is designed for long-term adaptability. Its modular structure allows new technologies and security domains to be integrated without requiring a complete redesign of the system.
As cybersecurity continues to evolve, new specialization areas are expected to emerge. These may include advanced automation security, artificial intelligence-driven defense systems, and next-generation identity frameworks.
The role-based model ensures that these new domains can be incorporated seamlessly into the existing structure. This makes the certification ecosystem highly scalable and future-ready.
The emphasis on practical skills, specialization, and real-world application suggests that future developments will continue to move away from rigid progression models toward flexible, role-driven learning systems.
Advanced Certification Progression and Multi-Domain Skill Integration
The most advanced stage of the Fortinet certification ecosystem focuses on integrating multiple cybersecurity domains into a unified skill set. At this level, professionals are no longer operating within a single specialization. Instead, they are expected to understand how networking, cloud infrastructure, security operations, and identity management interact as part of a single security architecture.
This multi-domain integration is essential because modern enterprise environments are no longer isolated systems. A single business application may depend on cloud infrastructure, remote access systems, API gateways, identity providers, and network security layers all working together simultaneously. Any breakdown in one layer can impact the entire environment.
Advanced certification levels therefore emphasize system-wide thinking rather than isolated technical expertise. Professionals must understand how security decisions in one domain affect performance, compliance, and risk in another. For example, a change in cloud access policies may directly influence network traffic patterns or security monitoring systems.
This level of thinking requires more than technical knowledge. It demands architectural awareness, operational foresight, and the ability to evaluate trade-offs between security strength, system performance, and usability. The certification structure is designed to gradually build this capability through increasingly complex scenarios and multi-layered problem solving.
At this stage, professionals are expected to move beyond implementation and into optimization. This means improving system efficiency, reducing attack surfaces, and ensuring that security controls do not negatively impact business operations.
Expert-Level Certification Depth and Enterprise Security Mastery
The expert certification level represents the highest point in the structured cybersecurity learning path. It is designed for professionals who operate in highly complex enterprise environments where multiple technologies converge and where security failures can have significant operational impact.
At this level, the focus shifts from individual systems to entire ecosystems. Professionals must understand how distributed infrastructures behave under stress, how threats propagate across interconnected systems, and how security controls must be coordinated across different domains.
Expert-level candidates are expected to demonstrate mastery across network security, cloud environments, security operations, and identity-based access control. However, mastery here does not simply mean familiarity. It requires the ability to design, evaluate, and troubleshoot complex architectures under real-world constraints.
One of the key challenges at this level is dealing with unpredictability. Large-scale environments are rarely static. They change continuously due to scaling demands, user behavior, application updates, and evolving threat landscapes. Expert-level professionals must be able to adapt security architectures dynamically without compromising stability or performance.
Another critical aspect is incident complexity. At this level, security incidents are rarely isolated events. Instead, they often involve multiple systems interacting in unexpected ways. Professionals must be able to trace root causes across distributed environments and resolve issues without introducing additional vulnerabilities.
This level of expertise is often associated with senior security architects, principal engineers, and advanced cybersecurity consultants who operate across enterprise-scale environments.
Practical Scenario-Based Assessment and Real-World Simulation Models
A defining feature of advanced certification stages is the use of scenario-based evaluation models. Instead of relying purely on theoretical questioning, candidates are placed in simulated environments that replicate real-world enterprise conditions.
These scenarios are designed to test decision-making under pressure. Candidates may be required to configure complex systems, troubleshoot multi-layered issues, or redesign security architectures in response to evolving threats.
The goal is not just to test knowledge but to evaluate applied reasoning. In real cybersecurity environments, professionals rarely have perfect information. They must make decisions based on partial data, time constraints, and operational limitations.
Scenario-based assessments reflect this reality by introducing ambiguity and complexity. Candidates must interpret system behavior, identify root causes, and implement solutions that balance security, performance, and business continuity.
This approach ensures that certified professionals are not only technically competent but also capable of functioning effectively in dynamic enterprise environments.
Expansion of Cloud-Native Security and Hybrid Infrastructure Protection
One of the most significant developments in modern cybersecurity certification frameworks is the increasing focus on cloud-native environments. Enterprises are rapidly migrating workloads to public and hybrid cloud platforms, creating new security challenges that differ significantly from traditional on-premises systems.
Cloud-native security requires understanding dynamic infrastructure models where resources are created, modified, and destroyed continuously. Unlike traditional environments, cloud systems do not have fixed boundaries, which makes security enforcement more complex.
Professionals must understand identity-based access control, workload segmentation, encryption strategies, and automated policy enforcement mechanisms. They must also be able to secure containerized applications, microservices architectures, and serverless computing environments.
Hybrid infrastructure security adds another layer of complexity. Many organizations operate environments that span both on-premises systems and multiple cloud providers. This creates challenges related to consistency, visibility, and unified policy enforcement.
Certification frameworks now incorporate these realities by integrating cloud security deeply into advanced specialization paths. This ensures that professionals are prepared for modern infrastructure challenges rather than legacy network models.
Security Operations Evolution and Threat Intelligence Integration
Security operations have evolved into one of the most critical components of modern cybersecurity frameworks. The increasing volume and sophistication of cyber threats require continuous monitoring, rapid detection, and coordinated response strategies.
Advanced certification levels place significant emphasis on security operations capabilities. Professionals are expected to understand how to analyze security data, correlate events across systems, and identify patterns that indicate potential threats.
Modern security operations environments rely heavily on automation and artificial intelligence. These systems generate alerts, prioritize incidents, and assist in response actions. However, human expertise remains essential for interpreting complex scenarios and making final decisions.
Certified professionals must be able to work alongside these automated systems effectively. This includes tuning detection mechanisms, validating alerts, and refining response workflows to reduce false positives and improve detection accuracy.
Threat intelligence integration is also a key component. Security teams must be able to incorporate external intelligence feeds into their operational environments to enhance detection capabilities and anticipate emerging threats.
This combination of automation, intelligence, and human analysis defines the modern security operations landscape.
Identity-Centric Security and Zero Trust Implementation Models
Identity has become one of the most critical elements in modern cybersecurity architectures. Traditional perimeter-based models are no longer sufficient because users and devices operate across distributed environments.
Modern security frameworks are increasingly built around identity-centric principles. This means that access decisions are based on user identity, device posture, location, and contextual risk factors rather than simple network boundaries.
Certification systems now reflect this shift by incorporating identity-driven security models into advanced learning paths. Professionals must understand how authentication, authorization, and continuous verification mechanisms operate within distributed systems.
Zero trust architecture has become a foundational principle in this context. Instead of assuming trust based on network location, zero trust models require continuous validation of every access request.
Implementing these models requires deep understanding of identity management systems, policy enforcement mechanisms, and behavioral analysis techniques. Professionals must be able to design systems that enforce strict access controls while maintaining usability and performance.
This represents a major shift from traditional security thinking and is now a core component of advanced cybersecurity certification frameworks.
Automation, Orchestration, and Security Efficiency Optimization
Automation has become a central component of modern cybersecurity operations. As threat volumes increase and environments become more complex, manual processes are no longer sufficient to maintain effective security coverage.
Security automation involves the use of predefined workflows to handle repetitive tasks such as alert processing, incident triage, and response execution. This reduces response time and improves operational efficiency.
Orchestration takes automation further by coordinating multiple security tools and systems into unified response workflows. This allows organizations to respond to complex incidents in a structured and consistent manner.
Advanced certification frameworks now include significant focus on automation and orchestration concepts. Professionals must understand how to design and optimize automated workflows, integrate multiple security systems, and ensure that automation does not introduce unintended risks.
Efficiency optimization is another important aspect. Security systems must be designed not only for effectiveness but also for performance and scalability. This requires balancing detection sensitivity with system resource usage and operational overhead.
Long-Term Career Progression and Skill Sustainability in Cybersecurity
One of the key objectives of modern certification frameworks is to support long-term career sustainability. Cybersecurity is a rapidly evolving field, and professionals must continuously update their skills to remain relevant.
The modular structure of the certification system supports this by allowing professionals to expand into new domains without restarting their learning journey. This makes it easier to adapt to emerging technologies and evolving job roles.
Career progression is no longer strictly vertical. Instead, professionals can move laterally across domains such as cloud security, network security, and security operations. They can also specialize deeply within a single domain while maintaining awareness of broader cybersecurity principles.
This flexibility is essential in modern IT environments where job roles often evolve based on technological change rather than fixed career ladders.
The certification framework therefore functions not only as a validation system but also as a long-term skill development roadmap.
Future Direction of Cybersecurity Certification Ecosystems
The future of cybersecurity certification is expected to move even further toward specialization, modular learning, and continuous adaptation. As technologies such as artificial intelligence, machine learning, and autonomous security systems become more prevalent, certification frameworks will need to evolve accordingly.
Future certifications are likely to place greater emphasis on adaptive security models, predictive threat analysis, and automated defense systems. Professionals will need to understand not only how to configure systems but also how to interpret machine-driven security insights.
Another expected development is increased integration between certification and real-world operational environments. This may include more dynamic assessment models that reflect live system behavior rather than static scenarios.
The overall direction of cybersecurity certification is toward continuous learning ecosystems rather than fixed credentialing systems. This ensures that professionals remain aligned with rapidly changing technological and threat landscapes.
Conclusion
The evolution of Fortinet’s certification ecosystem reflects a broader transformation occurring across the entire cybersecurity industry. What was once a rigid, linear certification ladder has now been reshaped into a flexible, role-driven structure that better aligns with how real-world security operations function. This change is not simply a redesign of exam names or learning paths; it represents a fundamental shift in how technical competency is defined, validated, and applied in enterprise environments.
At the core of this transformation is the recognition that cybersecurity is no longer a single discipline with a predictable progression path. Instead, it is a multi-layered ecosystem composed of specialized domains, each requiring deep and focused expertise. Network security, cloud protection, security operations, identity management, and secure access frameworks now operate as interconnected but distinct fields. The modern certification model reflects this reality by allowing professionals to pursue targeted expertise rather than being forced through a universal progression ladder.
One of the most significant outcomes of this restructuring is improved relevance. In earlier models, professionals often had to complete broad sequences of certifications that included content unrelated to their actual job responsibilities. This created inefficiencies in both learning and career development. The updated framework removes much of this friction by enabling professionals to focus directly on domains that match their current or intended roles. This results in faster skill acquisition and more immediate applicability in real-world environments.
Despite this increased flexibility, the certification system still maintains a strong underlying structure. The presence of internal exam levels ensures that technical depth is preserved across all learning paths. Foundational knowledge still supports advanced expertise, and progression still follows a logical increase in complexity. This balance between structure and flexibility is one of the most important strengths of the modern framework, as it ensures consistency without limiting adaptability.
Another key advantage of the updated certification model is its alignment with modern enterprise architecture. Organizations today operate in highly distributed environments that span on-premises systems, multiple cloud platforms, remote work infrastructures, and globally dispersed networks. Security responsibilities are no longer centralized but distributed across specialized teams. The certification structure mirrors this operational reality by dividing knowledge into functional domains that reflect how security teams are actually organized.
This alignment improves workforce readiness. Professionals who complete certifications within this framework are better prepared to transition directly into specialized roles because the content closely matches real job responsibilities. Whether working in network defense, cloud security engineering, or security operations, certified individuals gain skills that are immediately applicable in professional environments.
The introduction of specialization tracks also supports long-term career development. Cybersecurity professionals are no longer limited to a single vertical progression path. Instead, they can move laterally across domains or deepen expertise within a specific area. This flexibility is particularly important in an industry where technologies evolve rapidly and job roles frequently shift based on emerging threats and infrastructure changes.
At the same time, the expert-level certification tier continues to serve as a benchmark for advanced technical mastery. It represents the highest level of validation for professionals who operate in complex, multi-domain environments. This tier emphasizes not only technical execution but also architectural design, system integration, and advanced troubleshooting under real-world conditions. It remains one of the most demanding assessments in vendor-specific cybersecurity training due to its depth and practical focus.
The integration of scenario-based assessments further strengthens the certification system’s relevance. By simulating real enterprise environments, these evaluations ensure that professionals are tested on applied problem-solving rather than theoretical memorization. This approach better reflects the realities of cybersecurity operations, where decisions must often be made under pressure with incomplete information.
Another important dimension of the modern framework is its emphasis on cloud-native security and hybrid infrastructure protection. As organizations increasingly migrate workloads to cloud environments, traditional perimeter-based security models have become insufficient. The certification system now incorporates these changes by embedding cloud security principles into advanced learning paths. This ensures that professionals understand how to secure dynamic, distributed systems rather than static network boundaries.
Security operations have also become a central focus area within the certification ecosystem. Modern cybersecurity environments generate vast amounts of data that must be continuously monitored, analyzed, and acted upon. The integration of automation, orchestration, and threat intelligence into certification pathways reflects the increasing importance of operational efficiency and rapid response capabilities. Professionals are expected to work alongside automated systems while maintaining the ability to interpret complex security events and make informed decisions.
Identity-centric security models further highlight the shift in cybersecurity thinking. Traditional assumptions based on network location are no longer sufficient in environments where users access systems from multiple devices and locations. The adoption of zero trust principles has reshaped how access is managed and enforced. Certification content now reflects this reality by emphasizing identity verification, contextual access control, and continuous validation mechanisms.
Automation and orchestration also play a critical role in modern cybersecurity operations. As threat volumes increase and environments become more complex, manual processes are no longer scalable. Professionals must now understand how to design and manage automated workflows that improve efficiency while maintaining security integrity. This requires a combination of technical knowledge and operational strategy, both of which are increasingly embedded into advanced certification requirements.
From a career development perspective, the modern certification framework offers significant advantages. It supports both specialization and long-term growth, allowing professionals to adapt their learning paths as technologies evolve. Instead of being locked into a fixed sequence, individuals can continuously expand their expertise across multiple domains or deepen their knowledge within a specific area of focus.
This adaptability is particularly important in cybersecurity, where technological change is constant. New threats, new platforms, and new architectural models emerge regularly, requiring professionals to remain flexible and continuously updated. The modular structure of the certification system ensures that skill development can keep pace with these changes.
Ultimately, the transformation of Fortinet’s certification ecosystem represents a broader industry shift toward practical, role-based validation of skills. It moves away from static knowledge testing and toward dynamic, applied competency assessment. This makes the certification system more relevant to both employers and professionals in modern cybersecurity environments.
The long-term direction of cybersecurity certification is clearly moving toward greater specialization, increased practical assessment, and continuous adaptation to emerging technologies. The current framework provides a scalable foundation for this evolution while ensuring that core technical standards remain consistent.
As cybersecurity continues to evolve, certification systems will likely become even more closely aligned with real-world operational environments. This will further strengthen the connection between learning, validation, and job performance, ensuring that professionals remain equipped to handle increasingly complex and dynamic security challenges.