Cybersecurity has become a foundational requirement across nearly every industry due to the increasing sophistication of digital threats and the expansion of cloud-based infrastructure, remote work environments, and interconnected enterprise systems. Organizations now prioritize structured security frameworks and demand professionals who can not only implement technical safeguards but also design resilient security architectures aligned with business risk models. Within this landscape, professional certifications have evolved into standardized indicators of competence, helping employers evaluate expertise in a consistent and measurable way. Among these credentials, ISC2 certifications are widely recognized for their rigor, structured domain coverage, and alignment with real-world security responsibilities. The demand for validated security expertise continues to rise as organizations face regulatory pressure, data protection requirements, and evolving cyber threats that target both technical systems and human vulnerabilities.
Positioning of CISSP in the Cybersecurity Career Framework
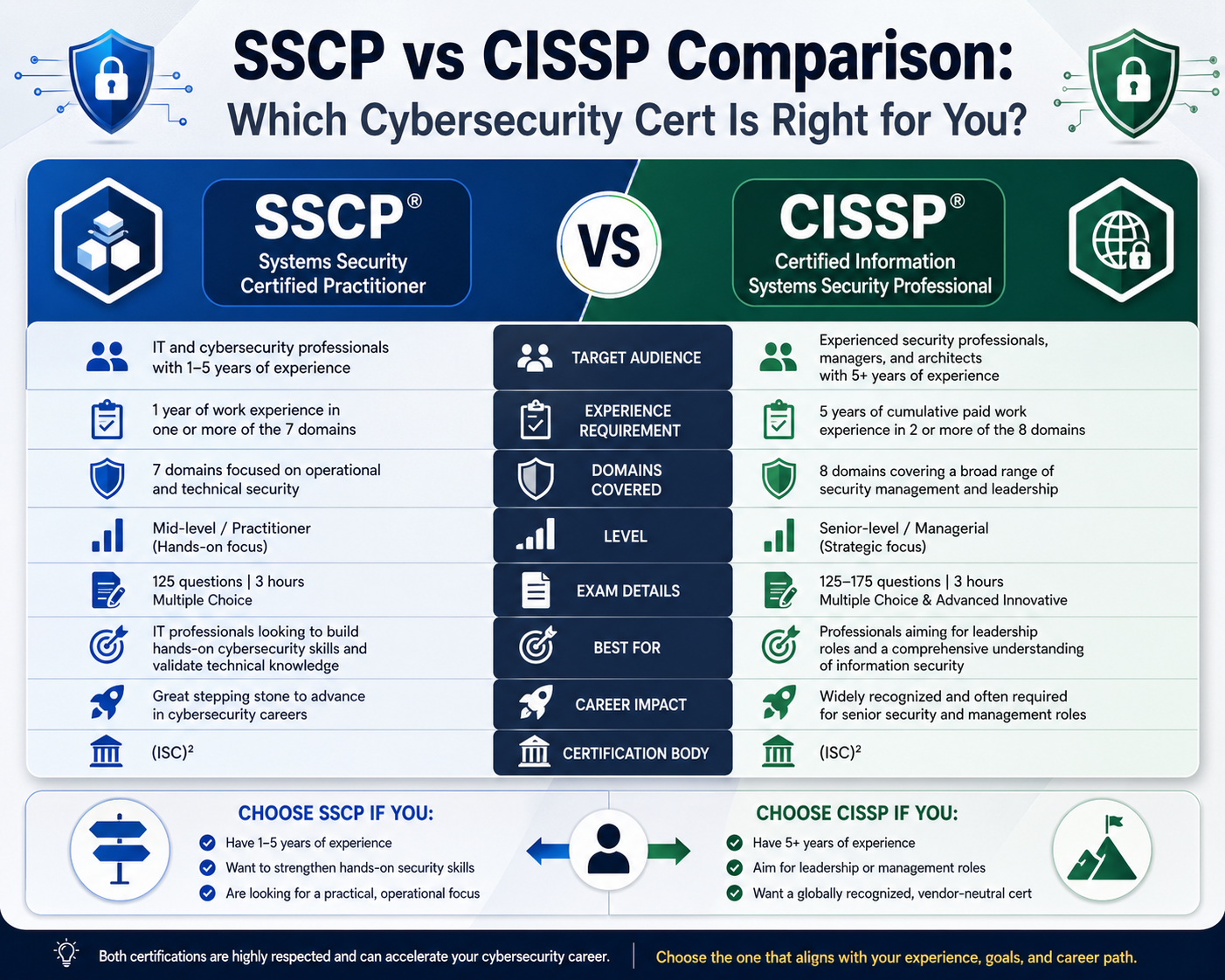
The Certified Information Systems Security Professional credential is positioned at the advanced tier of cybersecurity qualifications and is designed for individuals who operate at a strategic or architectural level within security programs. It is not intended for entry-level professionals but instead for those who have accumulated significant hands-on experience in multiple areas of security operations. The certification validates a broad understanding of security principles across organizational systems, emphasizing governance, risk management, and enterprise-level security architecture. Professionals pursuing this certification are typically expected to engage in decision-making roles that influence security policy, design secure infrastructures, and manage organizational risk exposure across diverse technology environments. Its structure reflects the expectation that candidates possess both theoretical understanding and practical application experience across complex security domains.
Core Knowledge Domains Covered Under CISSP
The CISSP framework is structured around eight primary domains that collectively represent a comprehensive security body of knowledge. These domains include security governance, asset management, security engineering, communication protection, identity and access management, security testing methodologies, operational security management, and secure software lifecycle principles. Each domain reflects a critical area of enterprise cybersecurity operations. Security governance focuses on establishing policies and compliance frameworks, while asset management addresses classification and protection of organizational data and systems. Security engineering emphasizes the design of resilient architectures capable of resisting threats. Communication security ensures secure transmission of data across networks, and identity management governs authentication and authorization mechanisms. Security testing evaluates system vulnerabilities, operational security focuses on monitoring and incident handling, and software security integrates secure coding practices into development processes. Together, these domains ensure that certified professionals possess a holistic understanding of cybersecurity at both technical and managerial levels.
Experience Requirements and Validation Process
A defining characteristic of CISSP certification is its requirement for substantial professional experience. Candidates are expected to demonstrate a minimum of five years of full-time work experience across at least two of the core security domains. This requirement ensures that individuals holding the certification have practical exposure to real-world security challenges rather than purely theoretical knowledge. In cases where candidates successfully pass the examination but do not yet meet the experience threshold, they are provisionally recognized as associate-level credential holders until they complete the necessary professional requirements. Additionally, a formal endorsement process is required, where an existing certified professional verifies the candidate’s qualifications and professional background. This validation mechanism reinforces the credibility of the certification and ensures that only qualified individuals are fully certified.
Examination Structure and Cognitive Demands
The CISSP examination is designed to assess not only factual knowledge but also analytical and decision-making abilities under complex scenarios. The exam uses a computerized adaptive testing model, where question difficulty adjusts based on candidate responses. The total number of questions varies, typically ranging between 125 and 175, and candidates are given a limited time window to complete the assessment. The exam evaluates conceptual understanding, applied reasoning, and situational judgment across all domains. Questions are often scenario-based, requiring candidates to evaluate risk, prioritize actions, and select the most appropriate security response within organizational constraints. This format is intended to reflect real-world cybersecurity decision-making environments where multiple variables must be considered simultaneously.
Professional Roles Associated with CISSP Certification
Individuals who obtain this certification are commonly found in senior-level roles that require oversight of security programs and strategic decision-making authority. These roles include security architects responsible for designing enterprise security frameworks, security consultants who advise organizations on risk mitigation strategies, and security managers overseeing operational teams. Additionally, professionals in auditing, compliance management, and executive security leadership positions often hold this credential due to its emphasis on governance and enterprise-level security planning. The certification is also relevant for individuals involved in regulatory compliance, risk assessment, and security policy development, as it provides a structured understanding of how security integrates with broader organizational objectives.
Strategic Value of CISSP in Enterprise Environments
The value of CISSP certification lies in its ability to validate a professional’s capacity to manage security at scale. Organizations operating in complex digital environments require individuals who can align security strategies with business objectives while maintaining regulatory compliance and operational efficiency. The certification emphasizes risk-based thinking, encouraging professionals to evaluate threats in terms of business impact rather than isolated technical vulnerabilities. This approach enables organizations to prioritize security investments effectively and develop resilient infrastructures capable of adapting to evolving threat landscapes. As enterprises increasingly adopt cloud computing, hybrid infrastructures, and distributed systems, the demand for professionals with advanced security planning capabilities continues to expand.
Career Progression and Industry Recognition
CISSP is widely recognized across both private and public sector organizations as a benchmark for senior cybersecurity expertise. It is often associated with leadership progression within IT and security departments, particularly for individuals transitioning from technical roles into managerial or architectural positions. The certification is frequently referenced in job requirements for advanced security roles due to its comprehensive coverage of enterprise security principles. Its recognition extends across global industries, including finance, healthcare, government, and technology sectors, where security governance and regulatory compliance are critical operational priorities. This broad acceptance reinforces its role as a standard credential for experienced security professionals.
Security Knowledge Integration Across Organizational Layers
One of the defining aspects of CISSP-level expertise is the ability to integrate security considerations across multiple layers of an organization. This includes technical infrastructure, application development environments, business processes, and regulatory frameworks. Professionals at this level are expected to bridge communication gaps between technical teams and executive leadership, ensuring that security strategies are aligned with organizational risk tolerance and operational goals. This integrative capability distinguishes CISSP-certified professionals from those focused solely on technical implementation, as it requires both strategic awareness and deep technical understanding.
Evolution of Enterprise Security Expectations
The evolution of cybersecurity threats has significantly influenced the structure and relevance of advanced certifications. Modern organizations face threats that are not only technically sophisticated but also socially engineered and economically motivated. As a result, security professionals are required to develop adaptive strategies that account for dynamic threat environments. Certifications such as CISSP reflect this evolution by emphasizing governance, risk management, and continuous security improvement rather than static technical knowledge. This shift aligns with the broader industry trend toward proactive security models that anticipate threats rather than simply responding to them.
Transition Toward Broader Security Leadership Roles
As professionals advance in their cybersecurity careers, certifications like CISSP serve as a bridge between technical expertise and leadership responsibility. The role of security professionals increasingly involves collaboration with executive stakeholders, policy development, and organizational risk assessment. This transition requires a deep understanding of both technical systems and business operations. CISSP certification supports this transition by providing a structured framework for understanding how security decisions impact organizational performance, regulatory compliance, and long-term strategic planning.
The Role of SSCP in Operational Security Environments
The Systems Security Certified Practitioner certification is designed around the operational layer of cybersecurity, where day-to-day implementation, monitoring, and enforcement of security controls take place. Unlike strategic certifications that focus on governance and enterprise architecture, SSCP emphasizes the hands-on responsibilities required to keep systems secure in active production environments. This includes maintaining access controls, responding to incidents, monitoring network activity, and ensuring that security policies are properly executed at the technical level. Professionals who pursue this certification are typically embedded within IT teams where they directly interact with infrastructure, security tools, and operational workflows. The certification reflects the reality that security is not only designed at the top but continuously enforced and adjusted at the operational level, where systems are exposed to real-time threats and vulnerabilities.
Foundational Skill Expectations and Hands-On Orientation
The SSCP framework is built on the expectation that candidates already possess foundational cybersecurity knowledge and have practical exposure to IT environments. The certification reinforces applied security skills rather than abstract theory, focusing on how systems behave in production conditions. Candidates are expected to understand how security controls function in real environments, including authentication systems, network configurations, system hardening practices, and monitoring tools. The emphasis is on execution rather than design, requiring professionals to implement security policies, troubleshoot vulnerabilities, and maintain secure configurations. This hands-on orientation makes the certification particularly relevant for individuals working in system administration, network security, or technical support roles that involve direct interaction with security infrastructure.
Access Control Mechanisms and Identity Enforcement
A core component of SSCP knowledge is access control, which governs how users and systems interact with protected resources. This includes authentication methods, authorization models, and identity lifecycle management. Professionals must understand how to enforce least privilege principles, ensuring that users only receive the minimum level of access required to perform their functions. Access control systems may involve role-based frameworks, policy-based restrictions, or attribute-driven models depending on organizational architecture. In operational environments, implementing access controls requires continuous monitoring and adjustment, particularly when users change roles or systems evolve. Identity enforcement also extends to managing credentials securely, preventing unauthorized escalation, and ensuring that authentication mechanisms remain resilient against attacks such as credential theft or session hijacking.
Security Operations and Administrative Practices
Security operations form the backbone of SSCP responsibilities, encompassing system monitoring, configuration management, and routine administrative tasks that maintain security posture. This includes overseeing logs, analyzing system behavior, and ensuring that security tools are functioning correctly. Administrative practices involve maintaining secure configurations across servers, endpoints, and network devices while ensuring compliance with established security policies. Professionals in this domain are often responsible for implementing updates, managing patches, and verifying that systems remain aligned with security baselines. Operational security also involves coordination with other IT functions, ensuring that security requirements are integrated into routine system administration tasks without disrupting business continuity.
Risk Monitoring and Analytical Security Functions
Risk monitoring within SSCP focuses on identifying, evaluating, and tracking potential security threats within operational environments. This involves continuous observation of system behavior, network traffic patterns, and user activity to detect anomalies that may indicate malicious activity. Analytical functions require professionals to interpret security data and distinguish between normal operational fluctuations and genuine security incidents. Risk monitoring is not limited to detection but extends to prioritization, where identified risks are assessed based on their potential impact on systems and business operations. This analytical approach enables security teams to allocate resources effectively and respond to the most critical threats in a timely manner.
Incident Response and Recovery Methodologies
Incident response is a critical operational function within SSCP, focusing on how organizations react to security breaches or system compromises. This includes identifying incidents, containing threats, eradicating malicious activity, and restoring affected systems to normal operation. Professionals must understand structured response procedures that minimize downtime and prevent further damage. Recovery processes involve restoring data integrity, validating system functionality, and ensuring that vulnerabilities have been addressed before systems are returned to production. Incident handling also requires documentation and analysis to understand root causes and improve future response strategies. In operational environments, speed and accuracy are essential, as delayed or improper responses can significantly increase organizational risk exposure.
Cryptographic Fundamentals in Practical Systems
Cryptography within SSCP is approached from an implementation perspective, focusing on how encryption technologies are applied in real systems rather than theoretical mathematics. This includes understanding encryption protocols, secure communication channels, and data protection mechanisms used in storage and transmission. Professionals must be familiar with how cryptographic tools protect confidentiality, integrity, and authenticity of data across networks and applications. Practical application includes configuring secure connections, managing cryptographic keys, and ensuring that encryption standards are properly enforced across systems. Operational security personnel also need to understand the limitations of cryptographic systems and how improper implementation can weaken overall security posture.
Network and Communication Security Implementation
Network security represents a significant portion of SSCP responsibilities, as networks are primary channels through which data flows and threats propagate. Professionals must understand how to secure communication pathways, segment networks, and monitor traffic for suspicious activity. This includes implementing firewalls, intrusion detection systems, and secure routing configurations. Network security also involves ensuring that remote access connections are properly authenticated and encrypted to prevent interception or unauthorized access. In operational environments, maintaining network security requires continuous observation and adjustment, as network conditions and threat landscapes evolve rapidly. Effective communication security ensures that data remains protected both within internal systems and during external transmission.
System and Application Security Hardening
System and application security focuses on reducing vulnerabilities within operating systems, software environments, and deployed applications. Hardening processes involve configuring systems to minimize attack surfaces by disabling unnecessary services, applying security patches, and enforcing strict configuration standards. Application security includes ensuring that software behaves securely under various conditions and does not expose sensitive data or system resources. Professionals must understand how to evaluate system configurations, identify weaknesses, and implement corrective measures to strengthen overall security posture. This domain emphasizes proactive protection rather than reactive response, aiming to prevent security incidents before they occur by reducing exploitable conditions.
Examination Structure and Cognitive Expectations
The SSCP examination is designed to evaluate both technical knowledge and applied understanding of security operations. It typically consists of multiple-choice questions that assess comprehension across all domains, with a focus on practical scenarios rather than abstract concepts. Candidates are expected to demonstrate the ability to interpret operational situations and select appropriate security responses based on real-world constraints. The cognitive demand of the exam lies in applying knowledge to situations involving system vulnerabilities, access control issues, and incident response scenarios. Unlike higher-level certifications that emphasize strategic decision-making, SSCP focuses on execution-level judgment within defined operational parameters.
Experience Requirements and Professional Validation
To qualify for full certification, candidates must demonstrate at least one year of relevant work experience in one or more of the SSCP domains. This requirement ensures that individuals have practical exposure to security operations before obtaining certification status. For those with academic backgrounds in cybersecurity or related disciplines, certain waivers may apply, reducing the required experience duration. Similar to other advanced certifications within this framework, SSCP also requires professional endorsement, where an existing certified individual verifies the candidate’s qualifications and professional background. This validation process ensures credibility and maintains consistency in professional standards across certified practitioners.
SSCP Career Roles in Enterprise Environments
Professionals holding SSCP certification typically occupy roles that involve direct interaction with security systems and infrastructure. These roles include security administrators responsible for maintaining system configurations, network security specialists managing communication protections, and security analysts monitoring operational environments for threats. Additional roles include system administrators with security responsibilities, incident response technicians, and IT support professionals working within security-focused environments. These positions require a strong understanding of how security controls function in practice and the ability to respond quickly to operational issues. SSCP-certified individuals often serve as the technical foundation of security teams, ensuring that security policies are effectively implemented across systems.
Comparative Positioning within Cybersecurity Skill Hierarchy
Within the broader cybersecurity skill hierarchy, SSCP occupies an intermediate position between entry-level foundational certifications and advanced strategic credentials. It builds upon basic security knowledge while focusing more deeply on implementation and operational execution. Compared to foundational certifications, SSCP requires greater technical depth and real-world experience. However, it remains distinct from advanced certifications that emphasize enterprise governance, risk strategy, and architectural design. This positioning makes SSCP particularly valuable for professionals transitioning from general IT roles into dedicated cybersecurity positions, where hands-on responsibility becomes a central requirement.
Industry Value of Operational Security Certification
The value of SSCP certification lies in its alignment with operational security needs within modern IT environments. Organizations require professionals who can manage security controls effectively at the system and network level, ensuring that protective measures are continuously enforced. As cyber threats become more sophisticated, operational security roles have gained increased importance, particularly in environments where continuous monitoring and rapid response are essential. The certification demonstrates that an individual possesses the technical capability to maintain secure systems under real-world conditions, making it relevant across industries such as finance, healthcare, government, and technology infrastructure.
Practical Security Decision-Making in Real Environments
Operational cybersecurity roles require continuous decision-making based on system behavior, threat indicators, and organizational priorities. SSCP-certified professionals are often required to make quick judgments regarding system access, incident escalation, and vulnerability mitigation. These decisions must balance security requirements with operational continuity, ensuring that protective measures do not disrupt essential business functions. Practical decision-making in this context involves evaluating multiple variables simultaneously, including system impact, threat severity, and available mitigation options. This dynamic environment requires both technical competence and situational awareness, reinforcing the importance of applied security expertise in day-to-day operations.
Strategic Comparison Between CISSP and SSCP in Modern Cybersecurity Roles
When evaluating advanced cybersecurity credentials within enterprise environments, CISSP and SSCP represent two distinct operational layers rather than competing alternatives. Their differences are best understood through the lens of organizational structure. CISSP aligns with strategic governance, risk oversight, and enterprise security architecture, while SSCP is embedded in operational execution, focusing on system-level enforcement and technical administration. In practical terms, CISSP professionals define security direction, while SSCP professionals implement and maintain that direction within live environments. This separation mirrors how modern cybersecurity programs are structured, where leadership establishes policies and technical teams ensure those policies are continuously enforced across infrastructure. The distinction is not merely academic but reflects how responsibilities are distributed across security teams in organizations of varying size and complexity.
Differences in Cognitive Focus and Professional Mindset
The cognitive orientation of each certification reflects fundamentally different professional mindsets. CISSP emphasizes analytical reasoning at the organizational level, requiring professionals to evaluate risk in terms of business impact, regulatory exposure, and long-term strategic consequences. Decision-making is abstracted, often involving trade-offs between cost, compliance, and operational resilience. SSCP, by contrast, focuses on situational execution. Professionals operating at this level make decisions based on system states, network conditions, and immediate security events. The mindset is reactive-proactive in nature, where rapid identification and mitigation of threats is essential. While CISSP requires systems thinking across entire enterprises, SSCP demands precision in technical environments where actions have immediate operational consequences.
Skill Progression Pathways Across Security Careers
Cybersecurity career development often follows a layered progression that aligns naturally with SSCP and CISSP frameworks. Early-stage professionals typically begin in operational roles involving system administration, network support, or technical monitoring. In these environments, SSCP-level competencies become relevant as individuals begin to manage access controls, analyze security logs, and respond to incidents. As experience deepens, professionals transition toward broader responsibilities involving architecture, governance, and risk analysis, which align with CISSP-level expectations. This progression reflects an expansion of scope rather than a replacement of skills. Operational expertise remains essential even at advanced levels, as strategic decisions rely on an understanding of how systems function at the technical layer.
Organizational Role Mapping and Functional Separation
Within enterprise cybersecurity teams, roles are typically divided into functional layers that correspond indirectly to SSCP and CISSP domains. Operational teams manage daily system security, including configuration enforcement, monitoring, and incident response. These responsibilities align closely with SSCP competencies. Strategic teams, on the other hand, focus on designing security frameworks, defining policies, and ensuring compliance with external regulations. These responsibilities align more closely with CISSP expertise. Between these layers exists a coordination function, where information flows from operational teams to leadership, enabling informed decision-making. This structure ensures that security programs remain both technically grounded and strategically aligned with organizational objectives.
Industry Demand Patterns and Workforce Distribution
Demand for cybersecurity professionals is influenced by a persistent global shortage of skilled practitioners. However, demand is not evenly distributed across all levels of expertise. Operational roles associated with SSCP-level skills are consistently required due to the need for continuous system monitoring, infrastructure maintenance, and incident response. These roles are often high-volume positions within organizations, forming the backbone of security operations centers and IT departments. CISSP-level roles, while fewer in number, are critical for governance and strategic oversight. These positions are typically concentrated in senior leadership, consultancy, and architectural functions. The imbalance between operational and strategic roles highlights the importance of both certifications within the broader cybersecurity ecosystem.
Salary Structure Dynamics Across Experience Levels
Compensation within cybersecurity reflects both skill level and organizational responsibility. SSCP-level professionals generally fall within mid-tier salary ranges, reflecting their technical specialization and operational responsibilities. Their compensation is influenced by factors such as system complexity, industry sector, and regional demand for technical security expertise. CISSP-level professionals command higher compensation due to their involvement in strategic decision-making, risk governance, and enterprise architecture. Their responsibilities directly influence organizational security posture and regulatory compliance, which increases their value in executive-level roles. Salary differences between the two certifications are not only a reflection of technical complexity but also of organizational impact and decision-making authority.
Governance Versus Execution in Security Architecture
A critical conceptual distinction between CISSP and SSCP lies in governance versus execution. Governance refers to the establishment of policies, standards, and frameworks that guide security behavior across an organization. This is the domain of CISSP-level expertise, where professionals design systems that define how security should function. Execution refers to the implementation of these frameworks in real environments, ensuring that systems, users, and processes comply with defined standards. This is the domain of SSCP-level expertise, where professionals translate policy into operational reality. Both functions are interdependent, as governance without execution lacks enforcement, and execution without governance lacks direction.
Incident Lifecycle Responsibilities Across Certification Levels
Incident management responsibilities differ significantly between operational and strategic roles. At the SSCP level, professionals are directly involved in identifying, containing, and mitigating security incidents. Their focus is on immediate response, system restoration, and technical remediation. They interact with logs, alerts, and system indicators to determine the scope of an incident and take corrective action. At the CISSP level, professionals are involved in overseeing incident response frameworks, analyzing incident trends, and refining organizational response strategies. They focus on post-incident evaluation, policy improvement, and risk reduction strategies. This layered approach ensures that incidents are handled both technically and strategically.
Technical Depth Versus Architectural Breadth
SSCP emphasizes technical depth within defined operational domains. Professionals are expected to understand system configurations, network behavior, cryptographic implementation, and access control mechanisms in detail. Their expertise is applied directly to systems and infrastructure. CISSP emphasizes architectural breadth, requiring professionals to understand how different security components interact across an entire enterprise ecosystem. This includes integrating security into business processes, aligning with regulatory requirements, and designing scalable security frameworks. While SSCP professionals operate within system boundaries, CISSP professionals operate across organizational boundaries.
Security Monitoring and Analytical Responsibility Split
Security monitoring functions are shared between operational and strategic roles but differ in interpretation and application. SSCP-level professionals are responsible for real-time monitoring of systems, analyzing logs, detecting anomalies, and responding to alerts. Their focus is immediate and technical. CISSP-level professionals analyze aggregated security data over time, identifying trends, systemic weaknesses, and organizational risk patterns. They use this information to adjust security policies and improve overall security posture. This dual-layer monitoring approach ensures that both immediate threats and long-term risks are addressed within security programs.
Certification Lifecycle and Professional Continuity
Both certifications operate within structured lifecycle models that require ongoing professional engagement. Certified individuals must maintain their credentials through continuing education activities and periodic renewal requirements. This ensures that professionals remain current with evolving technologies, emerging threats, and changing regulatory environments. The lifecycle approach reflects the dynamic nature of cybersecurity, where static knowledge quickly becomes outdated. Continuous learning is not optional but embedded into the certification framework, reinforcing the expectation that security professionals must evolve alongside the threat landscape.
DoD Alignment and Structured Security Frameworks
Within structured governmental security frameworks, certifications like CISSP and SSCP are aligned with defined role categories based on responsibility levels. Operational certifications correspond to technical support and system administration functions, while advanced certifications correspond to managerial, architectural, and engineering roles. This structured alignment ensures that personnel assigned to sensitive systems possess appropriate levels of verified expertise. The framework supports workforce standardization, enabling consistent security practices across different organizational units. It also ensures that individuals working in high-security environments meet baseline competency requirements appropriate to their roles.
Hybrid Roles and Overlapping Competencies
In modern cybersecurity environments, strict separation between operational and strategic roles is becoming less rigid. Many professionals operate in hybrid roles that require both SSCP-level technical expertise and CISSP-level strategic understanding. For example, security engineers may be required to implement technical controls while also participating in policy development discussions. Similarly, senior system administrators may contribute to architectural decisions while maintaining operational responsibilities. This blending of roles reflects the increasing complexity of cybersecurity environments, where technical and strategic considerations are closely intertwined.
Impact of Cloud and Distributed Systems on Certification Relevance
The rise of cloud computing and distributed architectures has significantly influenced the relevance of both certifications. SSCP-level skills remain critical for managing cloud configurations, securing virtual environments, and monitoring distributed systems. CISSP-level skills are equally important for designing cloud security architectures, managing compliance across multi-cloud environments, and ensuring governance consistency across distributed infrastructures. As organizations adopt hybrid and multi-cloud strategies, the need for professionals who understand both operational and strategic security dimensions continues to grow.
Evolving Threat Landscape and Skill Adaptation
Cyber threats have evolved from isolated attacks to highly coordinated, persistent campaigns targeting both technical systems and organizational structures. This evolution requires security professionals to adapt their skills continuously. Operational professionals must respond to increasingly sophisticated attack vectors that exploit system vulnerabilities, while strategic professionals must anticipate long-term risk trends and design adaptive security frameworks. Both SSCP and CISSP frameworks reflect this evolution by emphasizing adaptability, continuous monitoring, and integrated security approaches rather than static defensive models.
Long-Term Career Trajectories in Cybersecurity Domains
Career trajectories within cybersecurity often evolve from technical execution toward strategic leadership. Early career stages focus on developing operational expertise, where certifications like SSCP are highly relevant. As professionals gain experience, they transition into roles involving architecture, governance, and risk management, where CISSP becomes increasingly relevant. Over time, individuals may move into executive roles such as security leadership, advisory positions, or enterprise risk management. This progression reflects a natural expansion of responsibility rather than a shift away from technical expertise, as foundational knowledge remains essential throughout all stages of a cybersecurity career.
Interdependence of Operational and Strategic Security Layers
The effectiveness of any cybersecurity program depends on the seamless interaction between operational execution and strategic governance. Operational teams ensure that systems are protected, monitored, and maintained according to defined standards. Strategic teams define those standards based on organizational objectives, regulatory requirements, and risk assessments. Without operational execution, policies remain theoretical. Without strategic governance, operational efforts lack direction. The interdependence between SSCP and CISSP-level functions ensures that cybersecurity programs remain both actionable and aligned with broader organizational goals.
Ecosystem Perspective of Cybersecurity Certification Value
When viewed as part of a broader ecosystem, cybersecurity certifications represent structured pathways for developing comprehensive expertise across multiple layers of security responsibility. SSCP contributes to the technical foundation required for system protection and incident response, while CISSP provides the strategic framework necessary for enterprise security design and governance. Together, they represent complementary dimensions of cybersecurity competence, supporting both immediate operational needs and long-term organizational resilience in complex digital environments.
Conclusion
The relationship between CISSP and SSCP becomes clearer when viewed as part of a unified cybersecurity ecosystem rather than isolated credentials. Both certifications serve distinct but interconnected purposes that reflect the layered structure of modern security operations. SSCP operates at the implementation layer, where security controls are actively deployed, monitored, and maintained within technical environments. CISSP operates at the governance layer, where those controls are conceptualized, standardized, and aligned with organizational objectives. The effectiveness of any cybersecurity program depends on the interaction between these two layers, as strategic decisions must be grounded in operational reality, and operational execution must be guided by strategic intent. Without this alignment, organizations risk either designing impractical security frameworks or executing technically sound but strategically misaligned controls.
As digital environments have grown more complex, the responsibilities associated with cybersecurity roles have expanded significantly. Early IT environments were relatively centralized, with clearly defined boundaries between systems, networks, and applications. In such environments, security roles were often narrowly defined and focused on perimeter defense. However, modern architectures now include cloud infrastructures, hybrid deployments, distributed applications, and globally connected systems. This complexity has led to a natural division of security responsibilities into operational and strategic domains. SSCP reflects the operational necessity of managing real-time systems in dynamic environments, while CISSP reflects the strategic necessity of designing adaptable security frameworks capable of scaling across diverse infrastructures. This evolution demonstrates that cybersecurity is no longer a single discipline but a multi-layered field requiring specialization across different levels of abstraction.
An often overlooked dimension of cybersecurity is the human factor, which plays a critical role in both operational and strategic environments. At the SSCP level, professionals frequently interact with users, systems, and incident scenarios that require immediate judgment and technical intervention. Human error, misconfigurations, and behavioral vulnerabilities are often encountered in real time, requiring quick corrective action and procedural discipline. At the CISSP level, human factors are addressed from a systemic perspective, focusing on policy design, organizational culture, and risk awareness programs. Strategic professionals must anticipate how human behavior influences security outcomes and design frameworks that reduce dependency on perfect user compliance. This dual perspective ensures that both immediate human-driven risks and long-term behavioral trends are addressed within cybersecurity programs.
Risk is interpreted differently depending on whether it is analyzed from an operational or strategic standpoint. In operational environments associated with SSCP-level work, risk is often immediate, technical, and event-driven. It may manifest as a detected vulnerability, an active intrusion attempt, or a misconfigured system that requires immediate remediation. The focus is on containment, mitigation, and restoration of normal operations. In contrast, CISSP-level risk interpretation is broader and more analytical, focusing on patterns, probabilities, and long-term impact. Strategic professionals evaluate how individual risks aggregate across systems and how they affect organizational objectives, regulatory compliance, and business continuity. This layered interpretation of risk ensures that both immediate threats and systemic vulnerabilities are addressed in a coordinated manner.
Security controls do not exist in isolation; they are embedded throughout the lifecycle of systems, applications, and infrastructure. SSCP-level responsibilities focus on implementing and maintaining these controls during operational phases, ensuring that systems remain secure as they are deployed, updated, and used. This includes continuous monitoring, patch management, and configuration enforcement. CISSP-level responsibilities focus on designing these controls during planning and architecture phases, ensuring that security is integrated from the outset rather than added as an afterthought. This lifecycle-based integration highlights the dependency between the two certification domains, as effective security requires both proactive design and continuous enforcement across all stages of system operation.
Modern cybersecurity environments require continuous adaptation due to the evolving nature of threats and technologies. Static security models are no longer sufficient, as attackers constantly develop new techniques to exploit system vulnerabilities. SSCP-level roles contribute to this adaptive model by providing real-time feedback from operational environments, identifying emerging threats, and implementing immediate countermeasures. CISSP-level roles contribute by analyzing this operational data to refine policies, update frameworks, and improve organizational resilience. This feedback loop between operational execution and strategic refinement forms the foundation of continuous security improvement models. It ensures that organizations remain responsive to changing threat landscapes while maintaining structural stability in their security programs.
Cybersecurity today is inherently interdisciplinary, requiring knowledge that spans technical systems, organizational behavior, regulatory frameworks, and business operations. SSCP represents the technical foundation of this discipline, focusing on how systems are secured in practice through configuration, monitoring, and response. CISSP represents the integrative layer, where technical knowledge is combined with governance, risk management, and organizational strategy. Professionals operating in either domain must understand how their responsibilities intersect with broader organizational goals. This interdisciplinary nature ensures that cybersecurity is not treated as an isolated technical function but as a core component of organizational decision-making and operational resilience.
The cybersecurity workforce is structured in a stratified manner, reflecting varying levels of expertise, responsibility, and decision-making authority. Entry into the field often begins with foundational technical roles, where individuals develop operational skills that align closely with SSCP competencies. As professionals gain experience, they may transition into more advanced roles involving system design, security architecture, and risk governance, which align with CISSP competencies. This stratification is not rigid but fluid, allowing professionals to move between roles as their skills evolve. However, the distinction between operational and strategic responsibilities remains important for organizational clarity and effective security management. This structured progression ensures that cybersecurity teams are composed of individuals with complementary skill sets that collectively address both immediate and long-term security needs.
Long-term sustainability in cybersecurity careers depends on continuous learning and adaptation. Both SSCP and CISSP require professionals to remain current with evolving technologies, emerging threats, and changing regulatory environments. This requirement reflects the dynamic nature of cybersecurity, where knowledge quickly becomes outdated without ongoing professional development. Operational professionals must continuously update their technical skills to remain effective in managing modern systems, while strategic professionals must stay informed about evolving risk landscapes and governance frameworks. This continuous development ensures that cybersecurity expertise remains relevant over time and that professionals are capable of responding to new challenges as they emerge.
When viewed collectively, SSCP and CISSP contribute to a unified model of security maturity within organizations. SSCP ensures that systems are protected at the operational level through consistent implementation of security controls, while CISSP ensures that these controls are strategically aligned with organizational objectives and risk tolerance. Together, they form a comprehensive security model that supports both tactical execution and strategic planning. Organizational resilience depends on this integration, as it enables systems to withstand attacks, recover from incidents, and adapt to evolving threats. This unified perspective highlights the importance of developing expertise across both operational and strategic dimensions to achieve effective cybersecurity outcomes in complex digital environments.