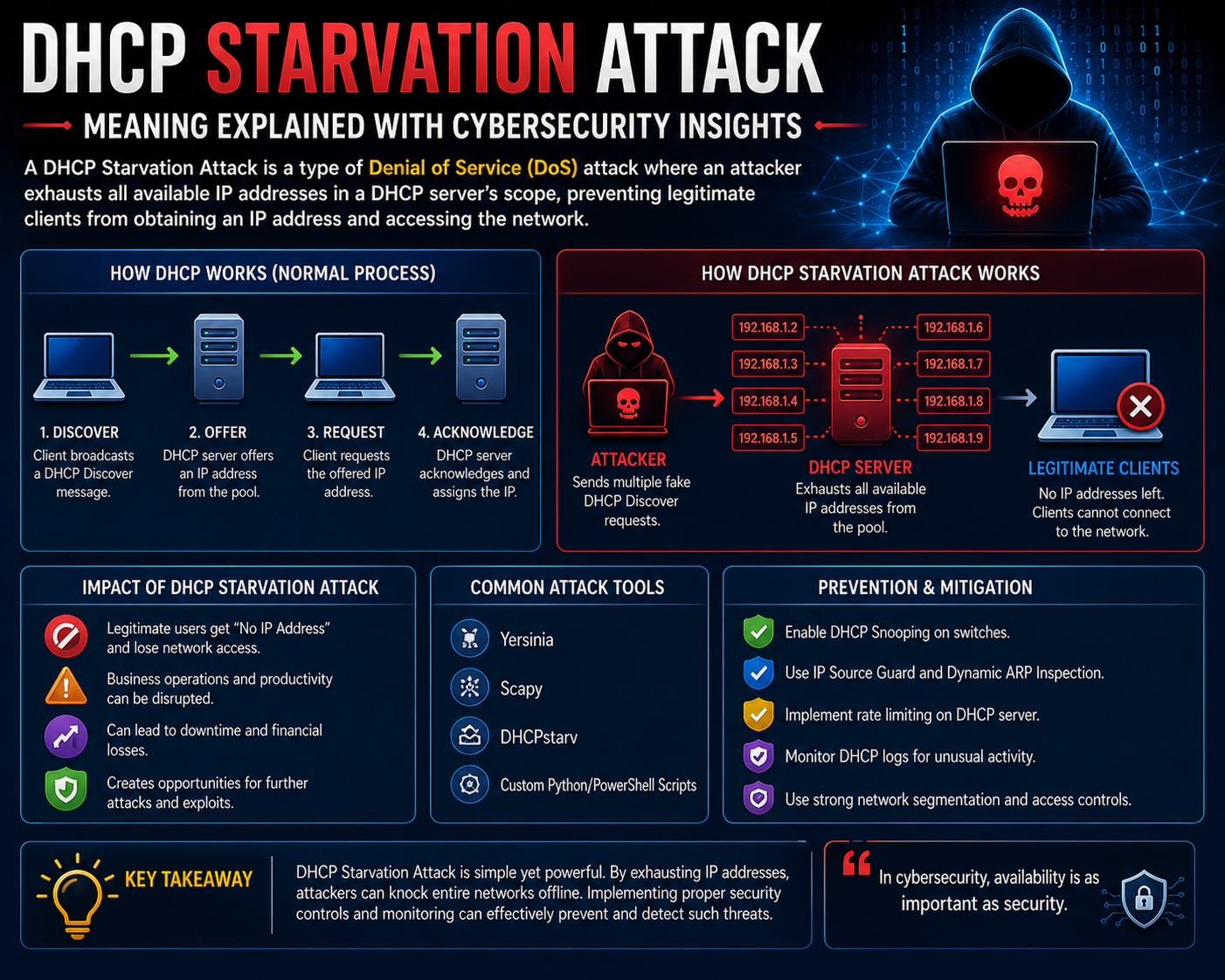
A DHCP starvation attack is a network-level disruption technique that targets the service responsible for automatically assigning IP addresses to devices. In a normal environment, every device that connects to a network must obtain an IP address before it can communicate with other systems. This assignment is handled by a centralized mechanism that manages a limited pool of addresses and distributes them dynamically. A starvation attack interferes with this process by exhausting that pool through excessive requests, preventing legitimate devices from obtaining valid network identities. Once the address pool is fully consumed, new devices are effectively locked out of the network, resulting in a denial of service condition. The impact is significant because it affects the foundational layer of connectivity, disrupting all dependent services that rely on network access.
Role of Automatic IP Assignment in Modern Digital Networks
Modern networks rely heavily on automated systems to handle IP address distribution efficiently. Instead of manually assigning addresses to every device, a centralized service dynamically allocates temporary IPs whenever a device joins the network. This system maintains a structured pool of available addresses and ensures that each device receives a unique identifier. When a device disconnects or its lease expires, the address is returned to the pool and becomes available for reuse. This continuous cycle allows large-scale networks to operate smoothly without administrative overhead. It also ensures scalability, making it possible for thousands of devices to connect and disconnect frequently without conflicts or manual intervention. However, this dependence on a finite resource pool introduces potential vulnerabilities if the allocation process is overwhelmed.
Communication Flow in the DHCP Process
The DHCP communication process follows a structured sequence designed to ensure that every device receives a valid and unique IP address. When a device connects to a network, it first sends out a broadcast request asking for configuration details. The server responds by offering an available IP address from its pool. The device then sends a confirmation request to accept that address, and finally, the server acknowledges the assignment. This four-step process ensures proper coordination between devices and the network service. It also prevents address duplication and maintains order in environments where many devices may be requesting connectivity at the same time. The efficiency of this process is essential for maintaining stable communication across modern digital infrastructures.
Structure and Limitations of IP Address Pools
Every network that uses dynamic IP assignment operates within a predefined range of available addresses known as a pool. This pool is determined by the network’s configuration and size. Smaller networks may have only a few hundred usable addresses, while larger systems can support thousands or more. Despite these differences, every pool has a strict maximum limit that cannot be exceeded. Once all available addresses are allocated, the system cannot assign new ones until existing leases expire or are released. This limitation is a natural constraint of IP-based networking and plays a critical role in how resources are managed. It also becomes a key factor in understanding how exhaustion-based disruptions can occur when demand exceeds supply.
Mechanism Behind Resource Exhaustion in Allocation Systems
Resource exhaustion occurs when the demand for IP addresses grows faster than the system can manage. Under normal conditions, devices request and release addresses in a balanced cycle. However, when a large number of requests are generated in a short period, the system begins assigning addresses rapidly without enough time for reuse. This imbalance causes the available pool to shrink quickly. In exhaustion scenarios, this process is artificially accelerated by generating excessive request traffic, forcing the system to allocate addresses at a rate far beyond normal operational expectations. Eventually, all available addresses are consumed, leaving no capacity for legitimate devices to connect. This creates a complete breakdown in network access for new users.
Impact of Address Exhaustion on Network Availability
Once the IP address pool is fully exhausted, the network enters a state of limited functionality. Existing devices that already have valid addresses may continue operating normally, but any new device attempting to connect will fail to obtain network configuration details. This results in inconsistent connectivity across the environment. Services that depend on network access, such as internal communication tools, authentication systems, and application servers, may begin to experience partial or complete disruption. The severity of the impact depends on how quickly the system can recover addresses and whether any protective mechanisms are in place. In environments with constant device activity, this disruption can quickly escalate into a widespread operational issue.
Indicators of Abnormal Allocation Behavior in Networks
Before complete exhaustion occurs, there are several warning signs that indicate abnormal network behavior. One of the most noticeable indicators is a rapid decrease in available IP addresses within a short time frame. Another sign is the presence of repeated or unusual request patterns coming from multiple sources that do not match normal user activity. Network logs may also show a sudden increase in allocation frequency, with addresses being assigned and held for unusually short durations. These patterns suggest that the system is under stress and may be experiencing excessive demand. Identifying these indicators early is essential for preventing full resource depletion and maintaining network stability.
High-Level View of Starvation-Based Disruption Behavior
In a starvation-based scenario, the system is overwhelmed by a continuous stream of connection requests that mimic legitimate device behavior. Each request triggers the allocation process, causing the system to assign an IP address from its limited pool. When this process is repeated on a large scale, the pool becomes depleted much faster than under normal conditions. The key characteristic of this behavior is that it relies on artificial demand rather than legitimate network growth. Once the pool is exhausted, new devices are unable to obtain network identities, effectively blocking access to the network. This highlights the importance of managing request volume and ensuring that allocation systems are not overwhelmed by abnormal traffic patterns.
Secondary Effects and Network Behavior After Exhaustion
After the address pool is fully consumed, the immediate effect is a loss of connectivity for new devices. However, additional consequences may also occur depending on how devices respond to the failure. Some devices may repeatedly attempt to reconnect, increasing network load even further. Others may search for alternative configuration sources, which can lead to inconsistent or unexpected network behavior. In more complex scenarios, improper configuration responses may result in traffic being redirected through unintended paths. This introduces potential risks related to data exposure and communication instability. While the primary issue remains denial of service, these secondary effects can further complicate recovery and stability.
Structural Weaknesses in Dynamic Allocation Systems
The main weakness in dynamic allocation systems lies in their reliance on a finite pool of resources combined with the need to process all incoming requests. Since every request is treated as valid unless additional validation is applied, the system can be overwhelmed by excessive demand. Without proper safeguards such as rate limiting, request filtering, or anomaly detection, the allocation system remains vulnerable to resource exhaustion. This structural limitation means that even well-designed networks can experience disruption if exposed to abnormal traffic conditions. The balance between availability, scalability, and protection is therefore critical in maintaining long-term network stability.
Network Architecture Exposure to DHCP-Based Attacks in Enterprise Environments
In modern enterprise network architectures, the dynamic allocation of IP addresses is deeply embedded within the foundational communication layer. Large-scale environments rely on centralized allocation systems to manage thousands of devices, including user endpoints, servers, IoT devices, and virtual machines. While this automation improves efficiency and reduces administrative burden, it also introduces a dependency on a single logical resource pool. When this pool is disrupted, the entire communication ecosystem can degrade rapidly. DHCP starvation attacks exploit this dependency by targeting the allocation layer rather than individual devices, making the impact systemic rather than isolated. In enterprise settings, where uptime and continuous connectivity are critical, even short periods of address exhaustion can cause cascading failures across authentication services, internal applications, and cloud-connected infrastructure.
Lifecycle of IP Address Allocation and Resource Recycling Behavior
The DHCP system operates through a structured lifecycle that governs how IP addresses are assigned, maintained, and released. When a device connects to the network, it receives an IP address for a specific lease duration. During this time, the device is considered an active participant in the network. As the lease approaches expiration, the device may request renewal to maintain continuity. If the device disconnects or fails to renew, the address is returned to the pool for reassignment. This recycling mechanism ensures efficient use of limited address space. However, this lifecycle also creates predictable allocation behavior that can be exploited under abnormal conditions. When excessive requests are introduced into the system, the natural recycling process becomes insufficient to maintain balance, leading to gradual exhaustion of available resources.
Traffic Amplification Effects in DHCP Request Flooding Scenarios
One of the critical aspects of DHCP starvation behavior is the amplification of request traffic within the network broadcast domain. Since DHCP requests are typically broadcast-based, they are processed by all listening services within the subnet. When a large number of such requests are generated simultaneously, the network experiences a significant increase in control-plane traffic. This does not necessarily affect data transfer directly but places strain on the allocation service responsible for processing these requests. As the number of requests increases, the system must allocate addresses for each perceived client, regardless of whether the request originates from a legitimate device. This amplification effect accelerates resource consumption and reduces the time available for normal recovery processes, pushing the system toward exhaustion more rapidly.
Impact on Network Services Dependent on IP Allocation Stability
Many critical network services depend on stable and continuous IP address allocation. Authentication systems, domain services, internal APIs, and cloud synchronization tools all rely on predictable connectivity. When DHCP starvation occurs, these services may experience partial or complete disruption due to the inability of new devices to obtain valid network identities. Even devices that already have active leases may be affected indirectly if they require reauthentication or reconnection. In environments such as corporate networks, educational institutions, and data centers, this instability can lead to widespread operational inefficiencies. Applications that depend on session continuity may fail, and users may experience inconsistent access to essential services.
Role of MAC Address Randomization in Allocation Pressure Increase
Modern network environments often involve devices that use MAC address randomization to enhance privacy and security. While this technique is beneficial for user anonymity, it can also increase pressure on DHCP systems when combined with abnormal request patterns. Each randomized identity may be interpreted as a new device by the allocation service, increasing the number of active lease requests. In starvation scenarios, this behavior contributes to faster consumption of available addresses because the system cannot easily correlate repeated requests from the same physical device. As a result, the allocation system treats each request independently, accelerating depletion of the address pool and intensifying the impact of the disruption.
Behavioral Patterns of DHCP Servers Under High Load Conditions
When DHCP servers are subjected to unusually high request volumes, they begin to exhibit measurable performance changes. Response times for address allocation may increase, and the system may struggle to maintain accurate tracking of active leases. In some cases, the server may temporarily delay responses or prioritize certain requests based on internal processing queues. As the load continues to increase, allocation efficiency decreases, and the risk of inconsistent or failed assignments rises. These conditions are not inherently caused by system failure but by resource saturation. Under starvation conditions, this behavior becomes more pronounced, eventually leading to complete exhaustion of the available address pool.
Effect of Subnet Size and Network Segmentation on Vulnerability Levels
The size and structure of a network subnet play a significant role in determining its susceptibility to DHCP starvation conditions. Smaller subnets with limited address pools are inherently more vulnerable because they can be exhausted with fewer requests. Larger networks may appear more resilient due to increased address capacity, but they are still vulnerable if the rate of request generation is high enough. Network segmentation can mitigate some risks by isolating traffic domains, but if multiple segments rely on centralized allocation infrastructure, the impact can still propagate across the system. Proper subnet design, including balanced address distribution and controlled segmentation, is essential for reducing exposure to resource exhaustion scenarios.
Detection Challenges in Differentiating Legitimate and Abnormal Traffic
One of the most complex aspects of managing DHCP starvation risk is the difficulty in distinguishing between legitimate and abnormal request patterns. In dynamic environments, such as public networks or large organizations, high volumes of legitimate device connections are expected. This makes it challenging to identify when request traffic exceeds normal thresholds. Attack patterns often mimic legitimate behavior, making detection reliant on statistical anomalies rather than direct identification. Without advanced monitoring systems, abnormal patterns may go unnoticed until the address pool is significantly depleted. This detection challenge highlights the importance of behavioral analysis and adaptive threshold mechanisms in network security frameworks.
Resource Contention Between Competing Network Functions
DHCP systems operate alongside other network services that compete for processing and bandwidth resources. When request volume increases significantly, the allocation system may consume a disproportionate share of available resources, leading to contention with other critical processes. This can indirectly affect routing, authentication, and DNS resolution performance. In starvation scenarios, this contention becomes more severe as the system prioritizes address allocation over other functions. The resulting imbalance can cause delays and inconsistencies across multiple layers of the network stack, amplifying the overall impact of the disruption beyond the DHCP service itself.
Temporal Dynamics of Address Pool Depletion and Recovery Cycles
The depletion of IP address pools does not occur instantaneously but follows a temporal progression based on request intensity and lease duration settings. Initially, the system may experience gradual consumption, with available addresses decreasing steadily. As demand increases, the rate of depletion accelerates until the pool reaches full exhaustion. Recovery begins only after abnormal request patterns subside and leases naturally expire or are released. However, recovery is often slower than depletion because the system must wait for expiration cycles to complete. This asymmetry between depletion and recovery makes DHCP starvation particularly disruptive, as restoration of normal operation can take significantly longer than the time required to exhaust the pool.
Interaction Between DHCP Starvation and Network Redundancy Mechanisms
Some network environments implement redundancy mechanisms to maintain availability in case of service disruption. These may include secondary allocation servers or failover configurations. While these systems improve resilience, they are not always immune to starvation-based conditions. If both primary and backup allocation systems draw from the same logical address pool or are exposed to the same request domain, they may be affected simultaneously. In such cases, redundancy does not eliminate the vulnerability but may only delay full exhaustion. Effective mitigation requires not only redundancy but also traffic control and validation at multiple layers of the network infrastructure.
Systemic Consequences of Prolonged Allocation Exhaustion States
When DHCP starvation conditions persist for extended periods, the network enters a prolonged degraded state. New devices remain unable to connect, and existing devices may experience instability due to failed renewals or service dependencies. Over time, this can lead to operational fragmentation, where parts of the network function normally while others remain isolated. This inconsistency can affect user productivity, system synchronization, and service reliability. In critical infrastructure environments, prolonged exhaustion states may require manual intervention to restore normal operation, including clearing leases, restarting services, or reconfiguring allocation parameters.
Role of Behavioral Baselines in Identifying Allocation Anomalies
Establishing a behavioral baseline for DHCP request patterns is essential for identifying deviations that may indicate abnormal activity. Under normal conditions, request frequency, lease duration, and allocation rates follow predictable patterns based on user behavior and device density. When these patterns deviate significantly, it may indicate the presence of excessive or artificial demand. Behavioral baselines allow systems to detect anomalies even when individual requests appear legitimate. This approach is particularly important in environments where static thresholds are insufficient due to dynamic usage patterns. Continuous baseline adjustment ensures that detection mechanisms remain effective in evolving network conditions.
Cumulative Impact of Small-Scale Request Increases Over Time
Even small increases in request volume can have cumulative effects on IP address availability over time. When repeated consistently, these increases reduce the effective lifespan of the allocation pool. While each individual increase may not appear significant, the aggregate impact can gradually push the system toward exhaustion. This slow accumulation effect is particularly relevant in environments with fluctuating device activity, where short bursts of high demand occur frequently. Over time, these bursts can contribute to instability if not properly managed, highlighting the importance of long-term traffic analysis rather than relying solely on short-term observations.
Long-Term Network Stability Risks from Repeated DHCP Resource Exhaustion Events
Repeated DHCP starvation conditions, even when short-lived, can create long-term instability in network environments. When address pools are repeatedly pushed close to exhaustion, the system spends more time in recovery states than in stable operation. This repeated cycling between depletion and partial recovery reduces overall efficiency and increases the likelihood of allocation delays. Over time, this can lead to inconsistent service quality, where some devices experience normal connectivity while others face intermittent failure. In enterprise and large-scale environments, this instability can accumulate into broader operational inefficiencies, affecting authentication systems, application performance, and internal communication reliability. Even if full exhaustion does not persist continuously, repeated stress events can degrade the overall responsiveness of the allocation infrastructure.
Influence of Lease Time Configuration on Exhaustion Sensitivity
The configuration of IP lease durations plays a significant role in determining how quickly a DHCP system can recover from high-demand scenarios. Short lease times increase the frequency of address recycling, allowing more dynamic reuse of limited resources. However, they also increase the frequency of renewal requests, which can add additional load to the allocation system. Longer lease times reduce renewal overhead but can slow recovery during exhaustion events because addresses remain reserved for extended periods. In starvation scenarios, systems with longer leases are typically more vulnerable because fewer addresses return to the pool within a given timeframe. The balance between lease duration and system responsiveness is therefore a critical design consideration in maintaining resilience against resource depletion conditions.
Effect of Network Density on Allocation Pressure Distribution
Network density refers to the number of devices operating within a given address space. High-density environments naturally place greater pressure on DHCP systems due to increased frequency of connection and renewal requests. In such environments, even normal traffic patterns can approach system limits, making them more sensitive to abnormal spikes. When additional artificial demand is introduced, the system has less buffer capacity to absorb the increase. This results in faster depletion of available addresses compared to low-density environments. The distribution of devices across subnets also influences how pressure is applied. Poorly balanced networks may experience localized exhaustion even if overall system capacity remains available elsewhere.
Role of Broadcast Domain Size in Amplifying DHCP Traffic Load
The size of the broadcast domain directly affects how DHCP traffic propagates within a network segment. Larger broadcast domains allow DHCP request messages to reach a wider range of systems, increasing the processing load on allocation services. In environments where multiple devices share a common broadcast domain, request traffic is amplified because every request is visible to all participating systems. This amplification effect increases the workload on the DHCP server, especially when request volume is high. In starvation scenarios, this contributes to faster resource consumption because the system must process and respond to a large number of simultaneous requests originating from the same logical segment.
Behavior of Client Devices Under IP Assignment Failure Conditions
When devices fail to obtain an IP address, they typically enter a retry loop, repeatedly attempting to request network configuration. This behavior is designed to ensure eventual connectivity in temporary failure conditions. However, in DHCP starvation scenarios, this retry mechanism can unintentionally increase network load. Each retry generates additional traffic, further contributing to system pressure. Devices may also switch between fallback states, attempting alternative configurations or self-assigned addresses that do not provide full connectivity. This creates a fragmented network experience where some devices remain partially connected while others are completely isolated, depending on how they respond to allocation failure.
Impact on Virtualized and Cloud-Based Network Environments
Virtualized and cloud-based environments rely heavily on dynamic IP allocation systems to manage large numbers of ephemeral resources. Virtual machines, containers, and microservices frequently require new IP addresses during scaling operations. In such environments, DHCP starvation conditions can have amplified effects because resource provisioning is tightly coupled with automated scaling processes. When address pools become exhausted, new instances cannot be properly initialized, leading to deployment failures or service degradation. This can interrupt automated workflows and reduce the effectiveness of elastic scaling mechanisms. The dependency on rapid provisioning makes these environments particularly sensitive to allocation instability.
Interplay Between DHCP Systems and Network Address Translation Layers
Network Address Translation systems often operate alongside DHCP services to manage external connectivity. While NAT handles external routing, DHCP manages internal address assignment. When DHCP exhaustion occurs, NAT systems may still function, but internal device connectivity becomes disrupted. This creates a situation where external communication pathways remain operational for existing devices, but new devices cannot join the internal network. The separation of these functions means that DHCP starvation primarily affects internal connectivity, but the secondary impact can extend to external communication depending on system dependencies. This layered interaction highlights how multiple network components can be indirectly affected by a single point of resource exhaustion.
Temporal Burst Patterns and Their Role in Allocation Instability
Network traffic is not always evenly distributed over time. Instead, it often occurs in bursts, where many devices attempt to connect simultaneously. These burst patterns can temporarily stress DHCP systems, even under normal conditions. When such bursts become more frequent or intense, they can reduce available buffer capacity in the allocation system. In starvation scenarios, artificially generated bursts mimic or amplify this behavior, accelerating depletion. The system’s ability to handle burst traffic depends on its queue management and processing efficiency. If burst handling capacity is exceeded, allocation delays increase, and exhaustion becomes more likely.
Effect of Overlapping Network Services on Allocation Resource Competition
DHCP services do not operate in isolation; they share infrastructure resources such as CPU, memory, and network bandwidth with other services. When multiple services compete for the same resources, allocation performance may degrade under high load conditions. This competition becomes more severe during high request volumes, where DHCP processing must handle a large number of simultaneous operations. As resource contention increases, the system may prioritize allocation tasks over other functions, further intensifying pressure on the address pool. This indirect competition contributes to system instability during starvation conditions, as multiple layers of the network stack become stressed simultaneously.
Recovery Delays Caused by Lease Persistence and System Synchronization
After an exhaustion event, recovery depends on both lease expiration and system synchronization processes. Even when request traffic returns to normal levels, allocated addresses remain reserved until their leases expire or are manually cleared. This delay slows recovery because the system cannot immediately reclaim all resources. Additionally, synchronization between distributed components may take time to update allocation states accurately. In environments with multiple DHCP servers or distributed allocation systems, synchronization delays can further extend recovery time. This creates a lag between the cessation of abnormal traffic and the restoration of full network functionality.
Influence of Device Mobility on Allocation System Stress Levels
In environments with high device mobility, such as wireless networks or large campuses, devices frequently connect and disconnect from the network. This constant movement increases the frequency of allocation and release events. While this is normal behavior, it places continuous pressure on DHCP systems. When combined with abnormal request activity, mobility amplifies the stress on the allocation pool. Devices that move between access points may generate additional requests, further accelerating resource consumption. This dynamic behavior makes it more difficult to distinguish between legitimate mobility patterns and abnormal allocation pressure.
Cascading Effects of Allocation Failure Across Dependent Services
DHCP failure does not remain isolated within the allocation system. Many dependent services rely on successful IP assignment to function correctly. When allocation fails, these services may also degrade or become unavailable. Authentication systems may fail to verify users, application servers may lose connectivity, and monitoring tools may lose visibility into network activity. These cascading effects create a chain reaction where a single point of failure impacts multiple layers of the network infrastructure. The severity of this cascade depends on how tightly integrated the services are with dynamic addressing systems.
Influence of Network Policy Enforcement on Allocation Behavior
Network policies such as access control rules, authentication requirements, and segmentation strategies influence how DHCP requests are processed. In environments with strict policy enforcement, unauthorized devices may be restricted from obtaining addresses, reducing exposure to abnormal request patterns. However, in less controlled environments, open access can allow unrestricted request generation. Policy enforcement mechanisms therefore play a critical role in shaping allocation behavior. When properly configured, they can reduce the likelihood of exhaustion by limiting unnecessary or unverified requests from entering the system.
Long-Term Architectural Considerations for Preventing Allocation Saturation
Preventing DHCP starvation conditions requires careful architectural planning that accounts for scalability, redundancy, and traffic control. Address pool sizing must be aligned with expected device density, and segmentation strategies should ensure that no single pool becomes a bottleneck. Monitoring systems should continuously track allocation trends and identify anomalies before they escalate. Additionally, rate-limiting mechanisms and validation processes can help reduce the impact of excessive request generation. Long-term resilience depends on balancing efficiency with protection, ensuring that the system can handle both normal fluctuations and abnormal spikes without reaching exhaustion states.
Conclusion
A DHCP starvation attack represents a critical disruption at the foundation of network communication because it targets the mechanism responsible for assigning IP addresses, which is the first requirement for any device to participate in a network. Without a valid IP address, a device cannot communicate, authenticate, or access any network-dependent service. This makes the attack particularly impactful because it does not need to break encryption, bypass authentication, or compromise applications directly. Instead, it disables connectivity at the most basic level, effectively removing the ability of devices to function within the network environment.
At its core, the attack exploits a structural limitation inherent in all dynamic addressing systems: the finite size of the IP address pool. Every network that relies on automatic allocation operates within a restricted range of addresses defined by its configuration. This pool, no matter how large, always has an upper limit. When that limit is reached, the system cannot assign new addresses until previously allocated ones are released. This fundamental constraint is what creates the possibility of exhaustion-based disruption. The attack does not need to alter the system’s logic; it simply forces the system to operate at its maximum allocation capacity until no resources remain available for legitimate use.
The broader significance of understanding this type of attack lies in how it reveals the dependency modern networks have on centralized allocation services. In large-scale environments, thousands or even millions of devices rely on automated IP assignment to maintain connectivity. This includes not only traditional computing systems but also mobile devices, IoT sensors, virtual machines, and cloud-based services. The moment this allocation service is disrupted, the entire ecosystem becomes unstable. Devices cannot join the network, existing sessions may become inconsistent, and dependent services begin to degrade. This demonstrates that DHCP is not just a background service but a critical infrastructure component that supports the entire communication framework.
Another important aspect of DHCP starvation behavior is how it highlights the relationship between normal network operations and abnormal traffic patterns. Under standard conditions, address allocation follows predictable cycles of request, assignment, lease, and release. The system is designed to handle continuous but balanced traffic. However, when this balance is disrupted by excessive demand, the allocation system becomes overwhelmed. The key issue is not simply the volume of requests, but the rate at which they are introduced relative to the system’s ability to process and recycle resources. When demand exceeds recovery capacity, exhaustion becomes inevitable. This imbalance is what makes the system vulnerable, even though it is functioning exactly as designed.
The impact of such an exhaustion state extends beyond simple denial of service. In many environments, DHCP failure creates cascading effects across multiple layers of infrastructure. Authentication systems may fail because new devices cannot obtain network identities. Internal applications may become unreachable because endpoints cannot establish valid connections. Even monitoring and management tools may lose visibility into network activity. This chain reaction demonstrates how deeply integrated IP allocation is within modern network architecture. A failure at this level does not remain isolated; it spreads outward and affects nearly every dependent system.
Recovery from a DHCP exhaustion condition is also not immediate. Even after abnormal traffic subsides, the system must wait for previously allocated leases to expire or be manually cleared. This introduces a delay between the end of the disruption and the restoration of normal functionality. During this period, the network remains partially degraded, with limited or inconsistent connectivity. In distributed environments, recovery may take even longer due to synchronization delays between multiple allocation systems. This asymmetry between rapid depletion and slow recovery is one of the reasons DHCP starvation can have such a strong operational impact.
From a defensive perspective, the importance of monitoring and early detection becomes clear. Networks must be able to identify abnormal allocation patterns before full exhaustion occurs. Indicators such as rapid address consumption, unusual request frequency, and inconsistent allocation logs provide early warning signs of stress on the system. However, detecting these patterns is not always straightforward because legitimate network activity can sometimes resemble abnormal behavior, especially in dynamic environments with high device turnover. This makes behavioral analysis and adaptive monitoring essential components of network security strategy.
The attack also highlights the importance of architectural design decisions in network resilience. Factors such as subnet size, lease duration, segmentation, and redundancy all influence how vulnerable a system is to exhaustion-based conditions. Poorly sized address pools or overly centralized allocation systems can increase the risk of rapid depletion. Similarly, environments without proper traffic filtering or request validation mechanisms are more exposed to abnormal demand surges. This means that prevention is not solely a matter of security controls but also of careful network design and capacity planning.
It is also important to understand that DHCP starvation is not limited to theoretical or isolated scenarios. It reflects a real-world class of resource exhaustion problems that exist across many types of distributed systems. Any system that relies on finite shared resources can potentially experience similar conditions if demand is artificially inflated or not properly controlled. This makes the concept relevant beyond networking, extending into broader areas of system design, scalability, and infrastructure engineering.
Ultimately, DHCP starvation attacks demonstrate how critical resource management is to maintaining network stability. They show that even highly automated and well-structured systems can become vulnerable when subjected to abnormal load conditions that exceed their designed operational boundaries. The key takeaway is not only the technical mechanism of the attack but the underlying principle it exposes: any finite resource system must account for imbalance, abuse, and unexpected demand patterns.
A stable network environment therefore depends on multiple layers of protection, including proper allocation design, traffic regulation, continuous monitoring, and adaptive response mechanisms. Without these safeguards, even essential services like IP address assignment can become points of failure. Understanding this dynamic is essential for building resilient, scalable, and secure network infrastructures capable of withstanding both normal operational loads and abnormal stress conditions.