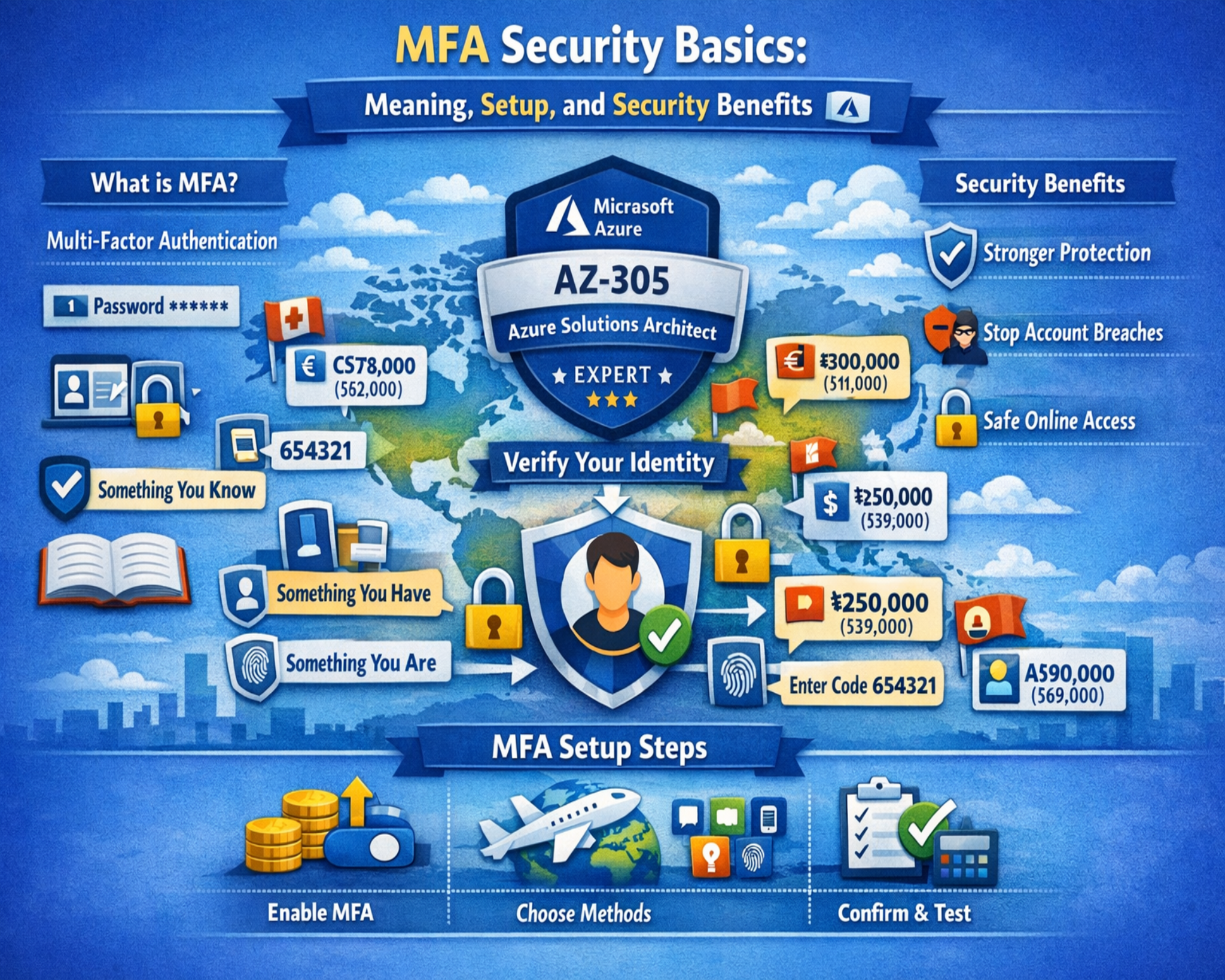
Multifactor authentication is a security framework designed to strengthen digital identity verification by requiring users to provide two or more independent credentials before access is granted to a system, application, or protected resource. In traditional authentication models, access is based solely on a username and password combination, which represents a single layer of security. While this approach was once sufficient, it has become increasingly ineffective in modern environments where cyber threats are more advanced, automated, and widespread. Multifactor authentication introduces additional layers of verification that significantly reduce the probability of unauthorized access, even if one credential is compromised. This model is now widely adopted in banking systems, enterprise networks, cloud computing platforms, and personal devices because it aligns with modern cybersecurity requirements for stronger identity assurance and risk mitigation.
The importance of multifactor authentication lies in its ability to distribute trust across multiple independent factors. Instead of relying on a single secret that can be stolen, guessed, or leaked, the system requires validation from different categories of evidence. This makes it significantly more difficult for attackers to impersonate legitimate users. As digital ecosystems expand and sensitive data becomes more distributed across platforms, multifactor authentication serves as a foundational control mechanism that supports secure access management and identity protection.
Core Concept of Identity Verification in Digital Systems
Identity verification in computing systems refers to the process of confirming whether a user or device is genuinely authorized to access a specific resource. This process is essential because digital systems cannot inherently recognize users without some form of validation mechanism. Historically, authentication relied on passwords as the primary method of verification. However, passwords alone represent a static form of security that does not adapt to evolving threat conditions. If a password is exposed through phishing, malware, or data breaches, attackers can gain unrestricted access without additional barriers.
Multifactor authentication addresses this limitation by requiring multiple forms of evidence before granting access. These verification steps are designed to operate independently, meaning that compromising one factor does not automatically compromise the entire authentication process. This separation of authentication elements creates a layered security model that significantly improves resilience against unauthorized access attempts. It also introduces a structured approach to identity validation that is more aligned with modern cybersecurity principles.
Structural Design of Multifactor Authentication Systems
Multifactor authentication systems are built on the principle of combining independent verification factors that belong to distinct categories. Each factor represents a different dimension of identity confirmation, and together they form a composite authentication process. The system evaluates each factor separately before granting access, ensuring that no single point of failure exists within the authentication chain.
In most implementations, the authentication process begins with a primary factor such as a password. Once this initial credential is validated, the system prompts the user for an additional verification step. This may involve entering a one-time code, approving a push notification, or providing biometric data. The sequential or parallel validation of these factors ensures that identity verification is both layered and context-aware. Some systems also incorporate adaptive authentication mechanisms that adjust requirements based on login behavior, device trust level, or geographic location.
The structural design of multifactor authentication is intended to balance security strength with usability. While additional verification steps increase security, they must also be implemented in a way that does not excessively disrupt user experience. This balance is critical for ensuring widespread adoption and consistent use across different environments.
Knowledge-Based Authentication and Its Role in MFA
Knowledge-based authentication is one of the foundational components of multifactor authentication systems. It involves information that the user is expected to know, such as passwords, PINs, or security responses. This factor is widely used due to its simplicity and ease of implementation. However, it is also the most vulnerable authentication category when used alone.
Passwords can be compromised through a variety of methods, including phishing attacks, brute-force attempts, credential reuse across platforms, and large-scale data breaches. Additionally, human behavior often weakens password security, as users tend to choose predictable patterns or reuse credentials for convenience. These weaknesses highlight why knowledge-based authentication cannot provide sufficient security on its own in high-risk environments.
Within a multifactor authentication framework, however, knowledge-based authentication serves as only one layer of defense. Even if an attacker obtains a password, they still must bypass additional verification factors, which significantly reduces the likelihood of successful unauthorized access. This layered dependency is what transforms weak credentials into a more secure authentication structure.
Possession-Based Authentication and Physical Security Layers
Possession-based authentication introduces a physical element into the verification process by requiring users to demonstrate ownership of a device or security token. This factor is typically implemented through mobile authentication applications, hardware security keys, or time-based one-time password generators. These tools generate dynamic codes or authentication signals that change frequently, ensuring that credentials cannot be reused or intercepted over long periods.
The strength of possession-based authentication lies in its dependency on physical access. Even if an attacker obtains a user’s password, they would still need access to the user’s registered device or token to complete the authentication process. This significantly increases the difficulty of unauthorized access attempts. In many systems, possession-based factors operate in real time, requiring immediate response during login attempts, which further reduces vulnerability windows.
Modern implementations often integrate possession-based authentication seamlessly into user workflows. Instead of requiring manual input of codes in all cases, some systems use push-based verification where users approve login attempts directly from a trusted device. This reduces friction while maintaining strong security enforcement.
Inherence-Based Authentication and Biometric Security Models
Inherence-based authentication relies on biological or behavioral characteristics that are unique to each individual. These include fingerprint patterns, facial structure, iris recognition, and voice dynamics. Biometric authentication has become increasingly common due to advancements in sensor technology and machine learning algorithms that improve recognition accuracy.
The primary advantage of biometric authentication is its uniqueness and difficulty of replication. Unlike passwords or tokens, biometric traits are inherently tied to the individual and cannot be easily transferred or shared. This makes them a strong candidate for high-security environments where identity assurance is critical.
However, biometric systems also introduce challenges related to privacy, data storage, and accuracy. If biometric data is compromised, it cannot be changed in the same way a password can be reset. Additionally, environmental factors such as lighting, angle, or physical conditions may affect recognition accuracy. Despite these limitations, biometric authentication remains a powerful component of multifactor authentication systems due to its strong security properties and user convenience.
Contextual and Location-Based Authentication Factors
In addition to the three primary authentication categories, modern multifactor authentication systems often incorporate contextual signals to enhance security decisions. These signals may include geographic location, device type, login time, IP reputation, and behavioral patterns. Contextual authentication evaluates whether a login attempt aligns with expected user behavior and flags anomalies for additional verification.
For example, if a user typically logs in from a specific region and suddenly attempts access from a distant location, the system may require additional authentication steps. Similarly, unfamiliar devices or unusual login times may trigger heightened security checks. This adaptive approach allows authentication systems to respond dynamically to potential threats without requiring constant manual intervention from the user.
Contextual authentication does not always function as a standalone factor but rather as an augmenting layer that enhances decision-making within the authentication process. It improves risk assessment and helps organizations implement more intelligent access control policies.
Security Advantages of Layered Authentication Models
The primary advantage of multifactor authentication lies in its ability to reduce reliance on a single point of failure. In traditional authentication systems, a compromised password often results in complete account takeover. In contrast, multifactor authentication requires attackers to compromise multiple independent systems or factors simultaneously, which is significantly more difficult.
This layered model also protects against automated attacks that target large numbers of accounts using stolen credentials. Even if credentials are exposed in a data breach, additional authentication layers prevent immediate exploitation. Furthermore, multifactor authentication improves organizational security posture by enforcing stronger identity verification standards across all access points.
Another important advantage is the ability to detect and respond to suspicious activity more effectively. When additional authentication factors are required, systems gain more opportunities to verify legitimacy and detect anomalies before granting access.
Evolution of Multifactor Authentication in Modern Cybersecurity Systems
Multifactor authentication has evolved as a direct response to the increasing complexity of digital threats and the limitations of traditional password-based security. Early authentication systems were built around the assumption that passwords alone could provide sufficient protection for digital accounts. However, as computing systems became more interconnected and internet usage expanded globally, attackers developed more sophisticated techniques to exploit weak or reused credentials. This shift forced security architectures to move beyond single-factor authentication and adopt more resilient identity verification models.
The evolution of multifactor authentication is closely tied to the development of enterprise IT infrastructure, cloud computing, and mobile technology. As users began accessing systems from multiple devices and locations, static authentication methods became inadequate. Organizations needed a mechanism that could validate identity across dynamic environments while maintaining usability. Multifactor authentication emerged as a structured solution that could adapt to these changing requirements by combining multiple independent verification layers.
Over time, multifactor authentication systems transitioned from basic token-based approaches to more advanced adaptive and context-aware models. Early implementations required users to manually enter codes generated by hardware tokens, while modern systems integrate seamlessly with mobile devices, biometric sensors, and behavioral analytics engines. This progression reflects a broader shift in cybersecurity strategy from reactive defense to proactive risk-based authentication.
Expansion of Authentication Factors in Enterprise Environments
Enterprise environments have significantly contributed to the expansion and sophistication of multifactor authentication systems. In large organizations, securing access to sensitive data and critical infrastructure requires more than simple credential validation. Enterprises operate complex networks with multiple access points, remote users, and cloud-based services, all of which increase the attack surface.
To address these challenges, multifactor authentication has been integrated into identity and access management frameworks. These frameworks enforce authentication policies that require users to verify their identity through multiple factors before accessing enterprise resources. This includes internal applications, administrative consoles, and remote access systems. The goal is to ensure that every access request is validated through a consistent and secure authentication process.
Enterprise adoption of multifactor authentication has also led to the development of centralized authentication systems. These systems manage identity verification across multiple platforms, allowing organizations to enforce uniform security policies. This centralization reduces complexity while improving visibility into authentication events, enabling better monitoring and threat detection capabilities.
Role of Mobile Devices in Modern Authentication Systems
Mobile devices have become a critical component in the implementation of multifactor authentication. Smartphones, in particular, serve as both possession-based and authentication delivery mechanisms. They are commonly used to receive one-time passcodes, approve login requests, or generate time-based authentication tokens.
The widespread adoption of mobile authentication is driven by convenience and accessibility. Users typically carry their mobile devices at all times, making them an ideal secondary authentication factor. Mobile authentication applications generate time-sensitive codes that refresh at regular intervals, ensuring that even if a code is intercepted, it becomes useless after a short period.
Push-based authentication has further simplified the user experience by eliminating the need to manually enter codes. Instead, users receive a notification prompting them to approve or deny a login attempt. This method reduces friction while maintaining strong security controls. However, it also requires careful implementation to prevent risks such as push fatigue attacks, where users may inadvertently approve malicious login requests.
Hardware-Based Authentication and Physical Security Keys
Hardware-based authentication represents one of the most secure forms of possession-based verification. These devices, often referred to as security keys, are physical tokens that must be connected to a system during authentication. They typically use cryptographic protocols to verify identity without transmitting reusable passwords or static codes.
The strength of hardware-based authentication lies in its resistance to phishing and remote attacks. Because authentication is tied to a physical device and cryptographic challenge-response mechanisms, attackers cannot easily replicate or intercept the authentication process. Even if a user is tricked into entering credentials on a malicious website, the absence of the physical key prevents successful authentication.
Hardware tokens are widely used in high-security environments such as financial institutions, government systems, and enterprise administrative access. They are considered one of the strongest implementations of multifactor authentication due to their reliance on secure cryptographic operations and physical possession requirements.
Biometric Authentication Advancements and Accuracy Improvements
Biometric authentication has undergone significant advancements due to improvements in sensor technology, machine learning, and pattern recognition algorithms. Early biometric systems suffered from high error rates and limited reliability, but modern implementations are far more accurate and efficient.
Fingerprint recognition remains one of the most widely used biometric methods due to its balance of accuracy and ease of implementation. Facial recognition has also become increasingly common, particularly in mobile devices and access control systems. Advanced systems now use 3D facial mapping and infrared sensing to improve accuracy under varying environmental conditions.
Behavioral biometrics is an emerging area that analyzes patterns such as typing rhythm, mouse movement, and interaction behavior. These systems provide continuous authentication by monitoring user behavior over time rather than relying on a single verification event. This approach enhances security by detecting anomalies that may indicate account compromise even after initial login.
Despite these advancements, biometric systems still face challenges related to privacy, data protection, and potential spoofing attempts. As a result, biometric authentication is typically used as part of a multifactor authentication system rather than a standalone solution.
Adaptive Authentication and Risk-Based Access Control
Adaptive authentication represents an advanced evolution of multifactor authentication that dynamically adjusts security requirements based on risk assessment. Instead of applying the same authentication steps for every login attempt, adaptive systems evaluate contextual factors to determine the level of verification required.
These systems analyze variables such as device reputation, geographic location, login history, and behavioral patterns. If a login attempt is deemed low risk, the system may allow access with minimal additional verification. However, if unusual behavior is detected, the system can trigger additional authentication steps such as biometric verification or secondary code confirmation.
Risk-based authentication improves both security and user experience by reducing unnecessary friction while maintaining strong protection against suspicious activity. It enables organizations to implement intelligent security policies that respond dynamically to changing threat conditions.
Integration of Multifactor Authentication with Cloud Systems
The rise of cloud computing has significantly increased the importance of multifactor authentication. Cloud environments host sensitive data and applications that are accessible from virtually anywhere, making them attractive targets for cyberattacks. As a result, strong identity verification is essential for securing cloud-based resources.
Multifactor authentication is integrated into cloud access management systems to ensure that only authorized users can access cloud services. These systems often combine authentication factors with identity federation, allowing users to access multiple services through a single verified identity.
Cloud-based multifactor authentication systems also support scalability, enabling organizations to enforce consistent security policies across large and distributed user bases. This ensures that security controls remain effective regardless of user location or device type.
Common Implementation Models in Digital Authentication Systems
Multifactor authentication can be implemented using different architectural models depending on system requirements and security objectives. One common model is sequential authentication, where users must complete each verification step in a specific order. Another model is parallel authentication, where multiple factors are verified simultaneously.
Some systems also use step-up authentication, where additional verification is required only when risk levels increase during a session. This model is particularly useful in environments where users perform multiple actions with varying levels of sensitivity.
Each implementation model is designed to balance security, performance, and usability. The choice of model depends on factors such as organizational risk tolerance, user behavior patterns, and regulatory requirements.
Operational Challenges in Multifactor Authentication Deployment
While multifactor authentication significantly improves security, its implementation is not without challenges. One of the primary concerns is user adoption, as additional authentication steps can sometimes be perceived as inconvenient. If systems are overly complex or intrusive, users may attempt to bypass or disable security measures, which can undermine overall protection.
Another challenge involves device dependency. If users lose access to their authentication device, they may experience difficulty accessing their accounts. This requires organizations to implement secure recovery mechanisms that do not weaken the overall security posture.
System integration is also a critical consideration, as multifactor authentication must be compatible with existing infrastructure, applications, and identity management systems. Ensuring seamless interoperability is essential for maintaining both security and usability.
Security Resilience Provided by Multi-Layer Authentication Models
Multifactor authentication significantly enhances security resilience by introducing multiple independent barriers to unauthorized access. Even if one authentication factor is compromised, additional layers continue to protect the system. This redundancy is essential in modern cybersecurity environments where attack methods are constantly evolving.
The layered structure also improves incident response capabilities by providing additional verification checkpoints that can detect suspicious activity early in the authentication process. This allows security systems to prevent unauthorized access before it occurs rather than reacting after a breach has taken place.
Advanced Multifactor Authentication Architectures in Modern Security Systems
Multifactor authentication has matured from a simple two-step verification mechanism into a complex, layered security architecture that integrates identity management, behavioral analytics, cryptographic validation, and contextual intelligence. In advanced deployments, MFA is no longer treated as a standalone feature but as a core component of a broader identity security framework. This framework is designed to continuously evaluate trust, enforce adaptive policies, and respond dynamically to evolving threat conditions.
Modern authentication architectures often integrate multifactor authentication into centralized identity providers that manage access across distributed systems. These identity systems act as authoritative sources of user verification, ensuring that authentication decisions remain consistent across applications, cloud environments, and internal networks. By centralizing authentication logic, organizations reduce fragmentation and improve visibility into access patterns, making it easier to detect anomalies and enforce security policies at scale.
In highly secure environments, MFA is often combined with zero-trust principles, where no user or device is automatically trusted regardless of network location. Instead, every access request is continuously evaluated based on identity strength, device posture, and behavioral context. This approach ensures that authentication is not a one-time event but an ongoing validation process that adapts to risk in real time.
Continuous Authentication and Behavioral Verification Systems
Continuous authentication represents an evolution of multifactor authentication that extends identity verification beyond the initial login event. Instead of verifying identity only at the point of entry, continuous authentication systems monitor user behavior throughout the entire session to ensure that the authenticated user remains legitimate.
Behavioral verification relies on analyzing patterns such as typing speed, mouse movement, touchscreen interaction, application usage habits, and navigation behavior. These patterns create a behavioral baseline unique to each user. When deviations from this baseline occur, the system can trigger additional authentication challenges or terminate the session entirely.
This approach significantly enhances security in environments where session hijacking or unauthorized access after login is a concern. Even if an attacker successfully passes initial authentication steps, abnormal behavior patterns can reveal unauthorized activity. Continuous authentication, therefore, acts as an invisible security layer that operates in the background without requiring frequent user interaction.
Cryptographic Foundations of Modern Authentication Mechanisms
At the core of advanced multifactor authentication systems lies cryptographic technology that ensures secure communication and identity verification. Cryptography is used to generate secure tokens, validate digital signatures, and protect authentication data during transmission.
Public key infrastructure plays a critical role in many modern authentication systems by enabling secure key exchange between users and servers. Instead of transmitting sensitive credentials directly, systems use cryptographic keys to verify identity through challenge-response mechanisms. This reduces the risk of credential interception and replay attacks.
Hardware security modules and secure enclaves within devices further enhance cryptographic protection by isolating sensitive operations from the main operating system. This ensures that authentication credentials and cryptographic keys are protected even if the device is compromised at the software level.
Cryptographic authentication methods are particularly important in environments where high assurance identity verification is required, such as financial systems, government infrastructure, and enterprise cloud platforms.
Multi-Channel Authentication and Cross-Device Verification
Multi-channel authentication expands the multifactor authentication model by distributing verification steps across different communication channels and devices. Instead of relying on a single device or interface, authentication factors are delivered through multiple independent pathways.
For example, a user may enter a password on a computer while receiving a verification code on a mobile device and confirming biometric identity on a secondary device. This distribution reduces the likelihood that a single compromised device can be used to bypass authentication.
Cross-device verification also improves resilience against phishing attacks, as attackers would need to compromise multiple devices and communication channels simultaneously. This significantly increases the complexity of successful attacks and strengthens overall system security.
Modern implementations of multi-channel authentication often integrate push notifications, mobile applications, hardware tokens, and biometric sensors into a unified verification workflow that operates seamlessly across devices.
Risk-Based Authentication Decision Engines
Risk-based authentication introduces intelligence into the multifactor authentication process by evaluating the likelihood that a login attempt is legitimate before determining the required authentication steps. This evaluation is performed by decision engines that analyze multiple signals in real time.
These signals may include device fingerprinting data, IP reputation, geolocation consistency, login time patterns, and historical user behavior. Based on these inputs, the system assigns a risk score to each authentication attempt. Low-risk attempts may require minimal verification, while high-risk attempts trigger additional authentication layers.
This dynamic approach improves both security and usability by reducing unnecessary friction for legitimate users while increasing scrutiny for suspicious activity. It also enables organizations to respond more effectively to emerging threats without requiring manual intervention for every authentication event.
Risk-based decision engines are increasingly used in large-scale cloud environments and enterprise identity systems where static authentication policies are insufficient to address diverse threat scenarios.
Authentication in Distributed and Cloud-Native Systems
The shift toward distributed computing and cloud-native architectures has significantly changed how multifactor authentication is implemented. In traditional on-premises systems, authentication was typically centralized within a single network boundary. However, cloud environments operate across multiple regions, services, and platforms, requiring more flexible authentication mechanisms.
Multifactor authentication in cloud-native systems is often integrated into identity federation frameworks that allow users to access multiple services using a single verified identity. This reduces credential duplication and simplifies access management while maintaining strong security controls.
In distributed systems, authentication must also account for microservices architecture, where individual services may require independent verification. Multifactor authentication can be embedded into API gateways and service meshes to ensure that only authenticated requests are processed across system components.
This distributed approach ensures that security is maintained at every layer of the architecture rather than being concentrated at a single entry point.
Human Factors and Usability in Authentication Design
While multifactor authentication significantly enhances security, its effectiveness depends heavily on user adoption and usability. Human behavior plays a critical role in determining whether authentication systems are used correctly or bypassed due to inconvenience.
One of the primary challenges in authentication design is balancing security strength with user experience. If authentication processes are too complex or time-consuming, users may attempt to find shortcuts, such as disabling security features or using weak fallback methods. This can undermine the intended security benefits.
To address this, modern authentication systems are designed with usability optimization in mind. Features such as single sign-on, trusted device recognition, and adaptive authentication reduce repetitive verification steps while maintaining strong security controls. The goal is to minimize friction without compromising identity assurance.
User education also plays an important role in successful MFA adoption. When users understand the purpose and benefits of multifactor authentication, they are more likely to engage with the system properly and follow security best practices.
Threat Landscape and Attack Mitigation Strategies
The evolving threat landscape has made multifactor authentication a critical defense mechanism against a wide range of cyberattacks. Attackers frequently target authentication systems through techniques such as phishing, credential stuffing, social engineering, and man-in-the-middle attacks.
Multifactor authentication mitigates these threats by requiring additional verification layers that cannot be easily replicated or intercepted. Even if credentials are stolen, attackers must still bypass secondary authentication factors, which significantly reduces the likelihood of successful compromise.
Advanced MFA systems also incorporate real-time threat detection capabilities that analyze login behavior for signs of malicious activity. These systems can block or challenge suspicious login attempts before access is granted, preventing unauthorized entry at the earliest stage.
Despite these protections, attackers continue to develop new techniques to bypass authentication systems, such as session hijacking and MFA fatigue attacks. As a result, authentication security must continuously evolve to address emerging threats.
Regulatory Compliance and Industry Standards for Authentication
Multifactor authentication is increasingly required by regulatory frameworks and industry standards that govern data protection and cybersecurity practices. Many compliance requirements mandate the use of strong authentication mechanisms to protect sensitive information and reduce the risk of unauthorized access.
These standards often emphasize the importance of layered authentication, secure credential storage, and continuous monitoring of access events. Organizations that fail to implement adequate authentication controls may face regulatory penalties, legal consequences, or reputational damage.
As digital ecosystems become more regulated, multifactor authentication is expected to remain a foundational requirement for compliance across industries such as finance, healthcare, government, and technology services.
Future Directions of Multifactor Authentication Technologies
The future of multifactor authentication is moving toward more seamless, invisible, and intelligent verification systems. Emerging technologies such as artificial intelligence, behavioral biometrics, and decentralized identity systems are expected to reshape how authentication is implemented.
Passwordless authentication is also gaining traction, where traditional passwords are replaced entirely by biometric or cryptographic methods. This reduces reliance on human memory and eliminates many common attack vectors associated with password-based systems.
Additionally, authentication systems are expected to become more predictive, using machine learning to anticipate threats and adjust security requirements dynamically. This will lead to more adaptive and context-aware identity verification systems that operate with minimal user disruption while maintaining high levels of security.
Multifactor authentication will continue to evolve as a core pillar of digital security infrastructure, adapting to new technologies and threat landscapes while maintaining its fundamental principle of layered identity verification.
Conclusion
Multifactor authentication has become one of the most critical components of modern digital security because it addresses a fundamental weakness in traditional password-based systems. Passwords alone are no longer sufficient to protect accounts, systems, or sensitive data, especially in environments where cyberattacks are increasingly automated, large-scale, and sophisticated. By requiring multiple independent forms of verification, multifactor authentication significantly reduces the likelihood of unauthorized access, even when one credential is compromised. This layered approach has transformed identity verification from a single checkpoint into a structured security process that strengthens trust across digital systems.
The importance of multifactor authentication lies in its ability to distribute identity verification across different categories of proof. Instead of relying on a single factor that can be stolen or guessed, MFA requires a combination of evidence, such as knowledge-based credentials, physical possession of a device, or biometric characteristics. This structure ensures that attackers cannot gain access through one weak point alone. Even if a password is exposed through phishing or data breaches, additional verification layers still block unauthorized entry. This makes MFA one of the most effective defenses against modern identity-based attacks.
Beyond its technical structure, multifactor authentication has reshaped how users interact with digital systems. It has increased awareness of security risks and encouraged more responsible digital behavior. Users are now more familiar with concepts such as one-time codes, authentication apps, and biometric verification. While this has improved overall security awareness, it has also introduced usability challenges. If authentication systems are too complex or disruptive, users may attempt to bypass them or rely on insecure workarounds. As a result, modern MFA systems are designed to balance strong security with minimal friction, ensuring that protection does not interfere with productivity.
One of the most significant advantages of multifactor authentication is its ability to reduce the attack surface of digital systems. In traditional authentication models, a single compromised password can lead to complete account takeover. With MFA, attackers must bypass multiple independent security layers, such as accessing a user’s device or replicating biometric data. This dramatically increases the difficulty and cost of successful attacks. Even when large databases of credentials are leaked, multifactor authentication prevents immediate exploitation by requiring additional verification steps.
Multifactor authentication is also deeply integrated into modern identity and access management systems. These systems control how users authenticate and what resources they can access within an organization. MFA serves as a core enforcement mechanism within these frameworks, ensuring that access decisions are based on more than just static credentials. Combined with role-based access control and conditional access policies, MFA helps organizations enforce consistent security rules across cloud platforms, enterprise applications, and remote access environments. This integration allows for centralized control while maintaining flexibility across diverse systems.
The evolution of multifactor authentication reflects a broader shift in cybersecurity strategy. Early security models focused on protecting network boundaries and trusted internal systems, but this approach is no longer effective in today’s interconnected environments. Modern security architectures assume that no user or device should be inherently trusted. Instead, every access request must be verified continuously and dynamically. MFA fits into this model by providing multiple checkpoints for identity validation, making it a key component of zero-trust security frameworks.
As authentication systems continue to evolve, they are becoming more adaptive and intelligent. Risk-based authentication is now widely used to evaluate login attempts based on contextual signals such as location, device behavior, and access patterns. This allows systems to adjust authentication requirements dynamically. Low-risk logins may require minimal verification, while high-risk attempts trigger additional security steps. This adaptive approach improves both security and user experience by applying stronger controls only when necessary.
Despite its advantages, multifactor authentication must be carefully implemented to avoid operational challenges. One of the primary concerns is user convenience. If authentication steps are too frequent or complicated, users may become frustrated and attempt to disable security features. This can undermine the effectiveness of the entire system. To address this, modern MFA implementations use techniques such as trusted devices, session persistence, and adaptive authentication to reduce unnecessary prompts while maintaining strong protection.
Another important consideration is device dependency. Since many MFA systems rely on mobile phones or hardware tokens, losing access to these devices can temporarily lock users out of their accounts. This requires organizations to implement secure recovery mechanisms that do not weaken overall security. Balancing accessibility with protection is a key challenge in MFA system design.
Looking forward, multifactor authentication is expected to continue evolving toward more seamless and invisible security models. Passwordless authentication is gaining traction, where biometric or cryptographic methods replace traditional passwords entirely. Behavioral authentication is also becoming more advanced, allowing systems to continuously verify identity based on user activity patterns rather than single login events. These developments point toward a future where authentication becomes more integrated into the background of digital interactions.
In conclusion, multifactor authentication represents a fundamental shift in how digital identity is protected. It replaces single-point verification with a layered security model that is significantly more resilient against modern threats. By combining multiple independent factors, MFA reduces the likelihood of unauthorized access and strengthens overall system security. As digital environments continue to grow in complexity, multifactor authentication will remain a central pillar of cybersecurity strategy, ensuring that identity verification evolves alongside emerging threats and technological advancements.