Cryptography has existed for thousands of years, long before the invention of computers and digital networks. Early forms of encryption were used by ancient civilizations to protect military strategies, diplomatic messages, and sensitive administrative records. These early methods were often simple substitutions or transpositions of characters, but they served an important purpose: keeping information hidden from unintended recipients. As societies became more complex, so did their communication systems, leading to more advanced techniques for encoding messages.
Over time, cryptography evolved from manual techniques into mathematically driven systems. The rise of computing introduced a major transformation in how encryption was designed and applied. Instead of relying on manual encoding, machines began using algorithms to perform complex transformations on data. This shift allowed encryption to become faster, more reliable, and far more secure than earlier methods.
In modern digital environments, cryptography is a foundational element of security. Every time data is transmitted across a network, it faces potential exposure to unauthorized access. Encryption ensures that even if data is intercepted, it remains unreadable without the proper decryption method. This principle protects everything from personal communications to financial transactions and enterprise systems.
The need for strong encryption has grown alongside the expansion of digital infrastructure. Cloud computing, mobile devices, and global communication networks all rely on cryptographic systems to maintain confidentiality and integrity. Without encryption, sensitive information would be vulnerable to interception and misuse, making secure communication nearly impossible in modern environments.
Core principles behind encryption and secure communication
Encryption is built on the transformation of readable information into an unreadable format. The original data, known as plaintext, is converted into ciphertext through a mathematical process. This transformation is controlled by an encryption algorithm and a key, which together determine how the data is processed.
The algorithm defines the set of rules used to perform encryption and decryption. It is designed to be complex enough to resist unauthorized decoding attempts. The key acts as a variable input that influences the output of the algorithm. Even if the same algorithm is used, different keys will produce completely different ciphertext results.
Decryption is the reverse process, where the ciphertext is converted back into plaintext using the appropriate key. This ensures that only authorized users who possess the correct key can access the original information. The security of the entire system depends on both the strength of the algorithm and the secrecy of the key.
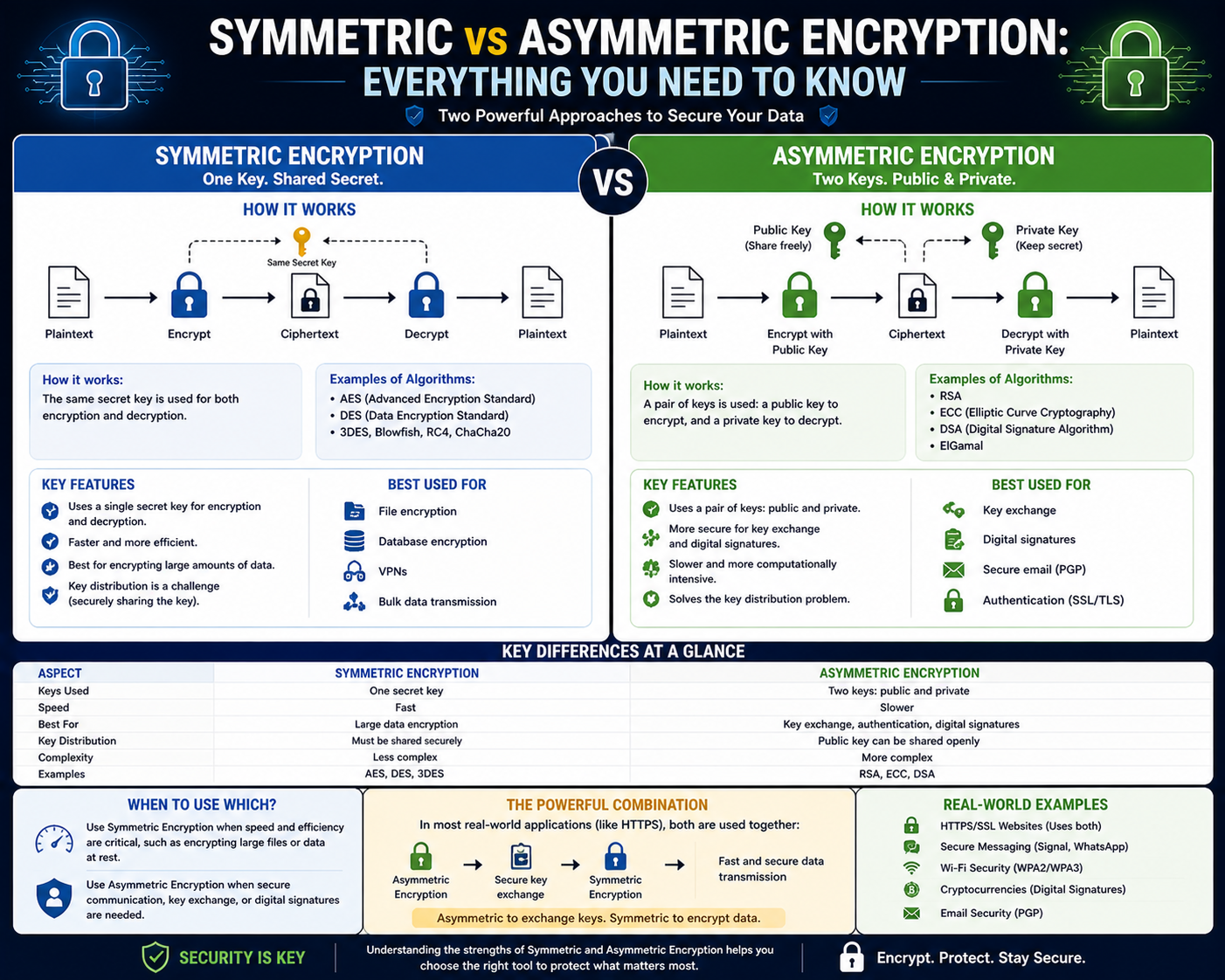
Encryption systems are generally classified based on how keys are used. In some systems, a single key is shared between parties. In others, a pair of keys is used, with each key serving a different role. These two approaches form the basis of symmetric and asymmetric encryption, which are the primary methods used in modern cryptography.
Fundamentals of symmetric encryption systems
Symmetric encryption is one of the most widely used methods for securing data due to its simplicity and efficiency. In this approach, the same key is used for both encryption and decryption. This means that both the sender and the receiver must have access to the same secret key before communication can take place.
When data is encrypted using symmetric encryption, the sender applies the shared key to transform plaintext into ciphertext. The encrypted data is then transmitted across the network. Upon receiving the data, the recipient uses the same key to reverse the process and recover the original message.
The primary advantage of symmetric encryption lies in its speed. Because only one key is used, the computational requirements are relatively low. This allows large volumes of data to be encrypted and decrypted quickly, making it suitable for high-performance environments.
Symmetric encryption is commonly used in scenarios where efficiency is critical. It is often applied in data storage systems, secure file transfers, and internal network communications. Its ability to handle large datasets efficiently makes it a preferred choice for bulk encryption tasks.
Despite its advantages, symmetric encryption introduces a major challenge related to key management. Since both parties must share the same key, there must be a secure method for distributing it. If the key is intercepted during transmission, the security of the entire system is compromised.
Key distribution challenges and secure exchange mechanisms
One of the most significant challenges in symmetric encryption is the secure exchange of the shared key. Before any encrypted communication can occur, both parties must possess the same secret key. However, transmitting this key over an insecure network introduces risk, as it may be intercepted by unauthorized entities.
To address this problem, various key exchange techniques have been developed. These methods allow two parties to establish a shared secret without directly transmitting the key itself in its final form. Instead, they exchange mathematical values that can be used to independently derive the same secret key.
One widely known method involves the use of mathematical principles that allow two parties to compute a shared value based on private inputs and exchanged information. This approach ensures that even if the exchange is observed, the final key remains secure because it cannot be easily derived without the private inputs.
Modern systems also use automated key management processes to handle the generation, distribution, and rotation of encryption keys. These systems help reduce the risk of human error and improve overall security by ensuring that keys are updated regularly and stored securely.
Stream ciphers in symmetric encryption systems
Symmetric encryption can be implemented using different approaches, one of which is the stream cipher. A stream cipher encrypts data one bit or one byte at a time, creating a continuous flow of encrypted output. This method is particularly useful when data is transmitted in real time or when the length of the data is not known in advance.
Stream ciphers generate a pseudo-random sequence of bits, which is combined with the plaintext to produce the ciphertext. This process ensures that each bit of data is individually encrypted, allowing for efficient and flexible encryption of continuous data streams.
One advantage of stream ciphers is their speed. They require relatively low computational resources, making them suitable for environments where performance is important. They are often used in real-time communication systems where delays must be minimized.
However, stream ciphers must be implemented carefully to avoid security weaknesses. If the same key stream is reused for multiple messages, it can create vulnerabilities that allow attackers to analyze patterns and potentially recover the original data. Proper key management is essential to maintaining their security.
Block ciphers and structured encryption methods
Block ciphers represent another major approach to symmetric encryption. Unlike stream ciphers, block ciphers process data in fixed-size chunks known as blocks. Each block is encrypted independently using the same key, resulting in a structured encryption process.
Block ciphers are widely used because they provide strong security and flexibility. They can operate in different modes that enhance their effectiveness, such as linking blocks together to prevent patterns from appearing in the encrypted output.
Common block sizes vary depending on the encryption method, with typical sizes including 64-bit and 128-bit blocks. Larger block sizes help reduce the risk of pattern recognition in ciphertext, increasing overall security.
Block ciphers are used in a wide range of applications, including secure data storage, encrypted communication channels, and system-level security functions. Their structured approach makes them suitable for environments where data integrity and confidentiality are critical.
Common symmetric encryption algorithms and their applications
Several symmetric encryption algorithms are widely used in modern systems. These algorithms differ in design, performance, and security strength, but all rely on the same principle of using a shared secret key.
Some earlier algorithms were widely adopted in the past but have since become less secure due to advances in computational power. Newer algorithms have been developed to address these weaknesses by increasing key length and improving mathematical complexity.
Modern symmetric encryption systems often rely on advanced algorithms designed to resist brute-force attacks and cryptographic analysis. These algorithms are used in various applications, including secure communications, encrypted storage systems, and network security protocols.
The choice of algorithm depends on factors such as performance requirements, security needs, and system constraints. In many cases, organizations select algorithms that provide a balance between speed and strong protection.
Practical use cases of symmetric encryption in digital systems
Symmetric encryption is widely used in real-world applications due to its efficiency and speed. One of its primary uses is in securing large volumes of data, such as database records or file systems. Since it can process data quickly, it is well-suited for environments where performance is critical.
It is also commonly used in network communication systems where data must be encrypted and decrypted rapidly. This includes internal enterprise communication systems, virtual private networks, and secure messaging platforms.
Another important application is in data storage encryption. Sensitive information stored on devices or servers is often protected using symmetric encryption to prevent unauthorized access in case of data breaches.
In many systems, symmetric encryption is also used alongside other cryptographic methods to enhance overall security. This combined approach allows systems to take advantage of the speed of symmetric encryption while addressing its limitations in key distribution.
Operational limitations and security considerations
While symmetric encryption offers strong performance advantages, it also presents certain operational challenges. The most significant issue is secure key management. Since the same key is used for both encryption and decryption, protecting that key becomes critical to maintaining system security.
If a key is exposed, all data encrypted with that key becomes vulnerable. This creates a dependency on secure storage, transmission, and rotation of keys. Organizations must implement strict policies to ensure that keys are not mishandled or reused improperly.
Another limitation is scalability in large networks. As the number of participants increases, the number of keys required for secure communication can grow significantly. This makes key management more complex in large distributed systems.
Despite these challenges, symmetric encryption remains a core component of modern security systems due to its efficiency and reliability when properly managed.
The emergence of asymmetric encryption in modern cryptography
As digital communication expanded across global networks, the limitations of symmetric encryption became more visible, especially around secure key exchange. This challenge led to the development of asymmetric encryption, a breakthrough in cryptographic design. Unlike symmetric systems, asymmetric encryption does not rely on a single shared secret key. Instead, it uses a pair of mathematically related keys, fundamentally changing how secure communication is established.
Asymmetric encryption was designed to solve the long-standing problem of securely sharing encryption keys over untrusted networks. In traditional systems, both parties needed access to the same secret key, which created a risk during transmission. Asymmetric encryption eliminates this issue by allowing one key to be shared publicly while keeping the other private.
This innovation made it possible to communicate securely without requiring prior secret exchange. It also laid the foundation for many modern security systems used in internet communication, digital identity verification, and secure online transactions.
The introduction of asymmetric encryption marked a turning point in cryptography. It enabled secure communication between parties who had never met or exchanged credentials before. This capability is essential in today’s interconnected digital environment, where users constantly interact across public networks.
How asymmetric encryption key pairs function
Asymmetric encryption is built around the concept of a key pair consisting of a public key and a private key. These two keys are mathematically related, but they serve different purposes and are not interchangeable.
The public key is designed to be shared openly. It can be distributed widely without compromising security. Anyone can use the public key to encrypt a message intended for the key owner. However, once data is encrypted using the public key, it can only be decrypted using the corresponding private key.
The private key is kept secret and is never shared with others. It is used to decrypt messages that were encrypted with the public key. This separation of roles ensures that even if the public key is widely available, the security of the system remains intact as long as the private key is protected.
When a sender wants to communicate securely, they use the recipient’s public key to encrypt the message. The encrypted data is then transmitted across the network. Only the recipient, who holds the private key, can decrypt and read the original message.
This structure removes the need for a shared secret key, significantly reducing the risks associated with key distribution. It also allows secure communication to be established dynamically without prior coordination.
The mathematical foundation behind asymmetric encryption systems
Asymmetric encryption relies on complex mathematical principles to ensure security. These systems are designed so that deriving the private key from the public key is computationally infeasible within a reasonable timeframe.
The strength of asymmetric encryption comes from problems that are easy to compute in one direction but extremely difficult to reverse. This one-way nature is what makes the system secure. Even if an attacker knows the public key, they cannot realistically determine the private key.
These mathematical relationships are based on number theory and algebraic structures. The computations involved require significant processing power, which is why asymmetric encryption is generally slower than symmetric encryption.
Despite its slower performance, the mathematical strength of asymmetric encryption makes it highly secure for key exchange, identity verification, and digital authentication. It is especially useful in environments where secure communication must be established between unknown parties.
The design of these systems ensures that security does not depend on the secrecy of the algorithm itself, but rather on the difficulty of solving the underlying mathematical problem.
Public key infrastructure and trust management systems
Asymmetric encryption alone is not enough to guarantee trust between communicating parties. In real-world systems, there must be a way to verify that a public key actually belongs to the claimed owner. This is where structured trust systems come into play.
Public key infrastructure is a framework designed to manage digital keys and certificates. It provides a trusted environment where public keys can be verified and associated with specific identities. This helps prevent impersonation and ensures that encrypted communication is sent to the correct recipient.
Within this system, digital certificates are issued to bind a public key to an entity. These certificates are validated by trusted authorities, creating a chain of trust that allows users to verify authenticity.
When a system receives a public key, it can check its validity through this infrastructure before using it for encryption. This reduces the risk of man-in-the-middle attacks, where an attacker could try to intercept or replace keys during communication.
Public key infrastructure plays a critical role in securing internet communication, enterprise systems, and identity verification processes. It ensures that asymmetric encryption is not only secure in theory but also reliable in practical applications.
Digital signatures and message authentication
Beyond encryption, asymmetric systems also enable digital signatures, which provide a way to verify the authenticity and integrity of a message. A digital signature is created using a private key and can be verified using the corresponding public key.
When a sender creates a digital signature, they apply their private key to a message or its hash value. This produces a unique signature that is attached to the message. The recipient can then use the sender’s public key to verify that the signature is valid.
If the signature is valid, it confirms two important things: the message was created by the owner of the private key, and the message has not been altered during transmission. This ensures both authenticity and integrity.
Digital signatures are widely used in secure communications, software distribution, and legal digital documents. They provide a reliable method for verifying identity without requiring direct interaction between parties.
This capability is especially important in environments where trust must be established across open networks. It ensures that messages cannot be forged or altered without detection.
Encryption and decryption process in asymmetric systems
The process of asymmetric encryption begins when the sender obtains the recipient’s public key. This key is used to encrypt the plaintext message into ciphertext. Once encrypted, the message becomes unreadable without the corresponding private key.
The encrypted message is then transmitted over a network. Even if it is intercepted, it remains secure because it cannot be decrypted without the private key.
When the recipient receives the message, they use their private key to decrypt the ciphertext. This process restores the original plaintext message, allowing the recipient to read the content securely.
This workflow ensures that only the intended recipient can access the message, even if the communication channel itself is insecure. It also eliminates the need for pre-shared secret keys, making it easier to establish secure communication between unknown parties.
The separation of encryption and decryption keys is what makes this system fundamentally different from symmetric encryption. It introduces a new level of flexibility in how secure communication is established.
Role of asymmetric encryption in secure internet communication
Asymmetric encryption is a critical component of secure internet communication. It is widely used in protocols that protect data transmitted between browsers and servers. These systems rely on encryption to ensure that sensitive information remains private during transmission.
When a user connects to a secure website, asymmetric encryption is used to establish a secure connection. The website provides its public key, which the user’s system uses to initiate encrypted communication. This process helps establish trust and secure data exchange before switching to faster encryption methods for ongoing communication.
This approach ensures that initial communication is protected even over untrusted networks. It also helps verify the identity of the server, reducing the risk of connecting to fraudulent or malicious websites.
Asymmetric encryption also supports secure authentication processes, allowing systems to verify user identities without exposing sensitive credentials.
Performance characteristics and computational complexity
One of the key differences between symmetric and asymmetric encryption lies in performance. Asymmetric encryption is computationally more intensive due to the complexity of its mathematical operations. This makes it slower compared to symmetric encryption when processing large amounts of data.
The additional processing requirements are a trade-off for increased security and flexibility. Because of this, asymmetric encryption is typically used for smaller tasks such as key exchange, authentication, and digital signatures rather than bulk data encryption.
In practice, systems often combine both symmetric and asymmetric methods to balance performance and security. Asymmetric encryption is used to securely exchange a symmetric key, which is then used for faster data encryption.
This hybrid approach allows systems to benefit from the strengths of both methods while minimizing their weaknesses.
Security advantages and inherent risks of asymmetric systems
Asymmetric encryption offers significant security advantages due to its separation of public and private keys. Since the private key is never shared, the risk of key exposure during transmission is greatly reduced.
However, the system is not without risks. If the private key is compromised, the security of all communications associated with that key is also compromised. This makes secure storage of private keys extremely important.
Another risk involves trust in public keys. If an attacker can impersonate a legitimate public key, they may intercept or alter communications. This is why verification systems are essential in maintaining trust within asymmetric encryption frameworks.
Despite these challenges, asymmetric encryption remains one of the most secure methods available for establishing secure communication channels over untrusted networks.
Integration of asymmetric encryption in modern security systems
Asymmetric encryption is widely integrated into modern digital security systems. It is used in secure communications, identity verification, software authentication, and encrypted data exchange.
Many systems rely on asymmetric encryption to establish trust before switching to more efficient symmetric encryption for ongoing communication. This combination ensures both security and performance.
It is also used in digital identity systems where verifying the authenticity of users and devices is critical. This helps prevent unauthorized access and ensures that only trusted entities can participate in secure communication.
The versatility of asymmetric encryption makes it a foundational component of modern cybersecurity architecture, supporting a wide range of applications across different industries.
The evolution of hybrid encryption in modern security systems
As digital communication networks expanded and security requirements became more complex, neither symmetric nor asymmetric encryption alone was sufficient to meet all demands efficiently. Symmetric encryption offered speed and performance, but struggled with secure key distribution. Asymmetric encryption solved key exchange and trust issues, but was computationally slower. This imbalance led to the development of hybrid encryption systems, which combine the strengths of both methods.
Hybrid encryption is widely used in modern secure communication frameworks because it provides a practical balance between performance and security. Instead of relying solely on one encryption method, systems use asymmetric encryption to securely exchange a symmetric key. Once the symmetric key is shared securely, it is then used to encrypt and decrypt the bulk of the data.
This approach allows systems to benefit from the fast processing speed of symmetric encryption while maintaining the secure key exchange capabilities of asymmetric encryption. It has become a standard design pattern in many secure communication protocols used across digital networks today.
The hybrid model represents a major advancement in cryptographic engineering, as it addresses the core limitations of both encryption types without compromising usability or performance.
How hybrid encryption systems operate in practice
Hybrid encryption begins with the establishment of a secure channel using asymmetric encryption. The sender obtains the recipient’s public key and uses it to encrypt a randomly generated symmetric key. This encrypted symmetric key is then transmitted to the recipient.
Once the recipient receives the encrypted symmetric key, they use their private key to decrypt it. This process ensures that only the intended recipient can access the symmetric key. After this step, both parties now share the same symmetric key securely.
From this point onward, symmetric encryption is used for all further communication. The reason for this transition is efficiency, as symmetric encryption is significantly faster and more suitable for handling large volumes of data.
This two-phase process ensures both security and performance. The initial asymmetric encryption protects the key exchange process, while symmetric encryption handles ongoing data transmission efficiently.
Hybrid systems are particularly effective in environments where large amounts of data must be transmitted securely over untrusted networks.
Role of hybrid encryption in secure internet communication
Modern internet communication relies heavily on hybrid encryption systems to ensure secure data exchange between clients and servers. When a user connects to a secure service, the system first uses asymmetric encryption to establish trust and exchange cryptographic keys.
After the secure handshake is completed, symmetric encryption takes over to handle the actual data transfer. This ensures that web pages, login credentials, financial information, and other sensitive data are transmitted securely and efficiently.
This layered approach is essential because internet traffic involves both high security requirements and high performance demands. Asymmetric encryption alone would be too slow for continuous data exchange, while symmetric encryption alone would be too risky for initial key exchange.
Hybrid encryption ensures that both requirements are met without compromising user experience or security.
Performance optimization in hybrid cryptographic systems
One of the primary reasons hybrid encryption is widely adopted is its ability to optimize performance. Asymmetric encryption requires complex mathematical computations that can slow down processing, especially when handling large datasets.
By limiting asymmetric encryption to key exchange operations, systems reduce computational overhead significantly. Once the symmetric key is established, faster encryption methods take over, allowing high-speed data processing.
This division of labor between encryption methods ensures that systems remain scalable even under heavy network traffic. It also improves response times in applications where real-time communication is critical.
In large-scale systems such as cloud infrastructure and enterprise networks, performance optimization is essential. Hybrid encryption allows these systems to maintain strong security without sacrificing efficiency.
Security architecture in hybrid encryption models
Hybrid encryption systems are designed with layered security in mind. Each layer of encryption serves a specific purpose in protecting data throughout its lifecycle.
The asymmetric layer ensures secure key exchange and identity verification. This prevents unauthorized entities from intercepting or manipulating encryption keys during transmission.
The symmetric layer provides fast and efficient data encryption for ongoing communication. This ensures that large volumes of data remain protected while being transmitted or stored.
Together, these layers create a robust security architecture that reduces the risk of compromise at multiple stages. Even if one layer is targeted, the other provides additional protection.
This multi-layered approach is a key reason why hybrid encryption is widely trusted in critical systems such as financial networks, healthcare systems, and secure communications infrastructure.
Use of encryption in secure session establishment
Secure sessions are temporary communication channels established between two systems. These sessions rely heavily on hybrid encryption to ensure both security and efficiency.
When a session begins, asymmetric encryption is used to authenticate the parties involved and securely exchange a symmetric session key. This ensures that both ends of the communication trust each other before any data is exchanged.
Once the session key is established, symmetric encryption is used for the remainder of the session. This allows data to flow quickly while remaining encrypted.
At the end of the session, the key is discarded, ensuring that even if future sessions are compromised, past communication remains secure. This concept is known as forward secrecy and is an important feature in modern encryption systems.
Secure session establishment is a fundamental part of secure communication protocols used across the internet and enterprise systems.
Key management strategies in modern encryption systems
Key management is one of the most critical aspects of any encryption system. It involves generating, distributing, storing, rotating, and revoking cryptographic keys in a secure manner.
In hybrid encryption systems, key management becomes even more important because both symmetric and asymmetric keys are involved. Each type of key has different security requirements and lifecycle management rules.
Symmetric keys must be securely exchanged and frequently rotated to minimize risk exposure. Asymmetric keys require secure storage of private keys, as their compromise can lead to complete system breaches.
Automated key management systems are often used to reduce human error and ensure consistent security practices. These systems handle key generation and lifecycle operations in a controlled and auditable manner.
Proper key management ensures that encryption systems remain secure even as they scale and evolve.
Digital certificates and identity verification systems
In hybrid encryption environments, trust is a critical factor. Systems must ensure that public keys actually belong to legitimate entities. This is achieved through digital certificates, which bind public keys to verified identities.
A digital certificate contains information about the key owner and is issued by a trusted authority. This certificate can be used to verify that a public key is authentic and has not been tampered with.
When a system receives a public key, it checks the associated certificate before using it for encryption. This ensures that communication is established with the correct entity and not an impersonator.
Identity verification systems built on digital certificates are essential for preventing man-in-the-middle attacks and ensuring secure communication across open networks.
These mechanisms form the trust foundation of many modern encryption-based systems.
Real-world applications of hybrid encryption systems
Hybrid encryption is widely used across many industries and technologies. One of its most common applications is in secure web communication, where it protects data exchanged between browsers and servers.
It is also used in secure messaging systems, where it ensures that messages remain private and are delivered only to intended recipients. In enterprise environments, hybrid encryption protects internal communications and sensitive data transfers.
Cloud computing platforms rely heavily on hybrid encryption to secure data stored and transmitted across distributed systems. This ensures that data remains protected even when it moves between multiple physical locations.
Financial systems also use hybrid encryption to secure transactions, authenticate users, and protect sensitive financial data from unauthorized access.
The versatility of hybrid encryption makes it suitable for virtually any system that requires secure and efficient data transmission.
Comparative behavior of encryption methods in operational environments
In practical environments, symmetric, asymmetric, and hybrid encryption each play distinct roles. Symmetric encryption is favored for speed and efficiency, especially when handling large datasets or continuous data streams.
Asymmetric encryption is preferred for secure key exchange, authentication, and digital signature verification. Its strength lies in its ability to establish trust without requiring prior shared secrets.
Hybrid encryption combines both approaches, allowing systems to leverage the strengths of each method. This makes it the most widely adopted model in modern secure communication systems.
The choice between these methods depends on system requirements such as performance needs, security levels, and scalability considerations.
Scalability and efficiency in modern cryptographic infrastructures
Scalability is a key requirement in modern digital systems. As the number of users and devices increases, encryption systems must be able to handle growing workloads without performance degradation.
Symmetric encryption scales efficiently in terms of processing speed but faces challenges in key distribution. Asymmetric encryption scales well in terms of trust establishment but is computationally heavier.
Hybrid encryption provides a scalable solution by separating responsibilities between the two methods. This allows systems to manage large-scale communication networks without sacrificing security or performance.
In enterprise environments, scalability is essential for supporting global operations, cloud services, and distributed applications.
Security resilience and attack resistance mechanisms
Modern encryption systems are designed to resist a wide range of attacks, including interception, impersonation, and data manipulation. Hybrid encryption strengthens resilience by combining multiple protective layers.
Even if an attacker gains access to encrypted data, they must overcome both symmetric and asymmetric protections to compromise the system. This significantly increases the difficulty of successful attacks.
Security resilience also depends on proper implementation, including secure key storage, certificate validation, and algorithm selection. Weakness in any of these areas can undermine the entire system.
Continuous updates and improvements in cryptographic standards help maintain resistance against evolving threats.
Conclusion
Cryptography has become one of the most essential pillars of modern digital security, shaping how information is protected, transmitted, and verified across virtually every connected system. From its early origins in ancient civilizations to its advanced implementation in today’s computing environments, encryption has continuously evolved to meet the growing demands of privacy, integrity, and trust in communication. The two foundational approaches, symmetric encryption and asymmetric encryption, represent distinct yet complementary methods that together form the backbone of secure digital interaction.
Symmetric encryption remains highly valued for its simplicity and efficiency. Using a single shared key for both encryption and decryption, it enables fast processing and low computational overhead, making it ideal for handling large volumes of data. This speed advantage is particularly important in environments where performance is critical, such as database encryption, file storage systems, and real-time communication channels. However, its reliance on a shared secret introduces one of its most significant challenges: secure key distribution. If the key is exposed during transmission or improperly stored, the entire system’s security can be compromised. This limitation has driven the development of more advanced key exchange mechanisms and management strategies.
Asymmetric encryption, on the other hand, addresses the key distribution problem by introducing a pair of mathematically linked keys: a public key and a private key. The public key can be openly shared, allowing anyone to encrypt messages intended for the key owner, while the private key remains confidential and is used for decryption. This structure eliminates the need for pre-shared secrets and enables secure communication between parties who have no prior relationship. Although asymmetric encryption is computationally more intensive and slower than symmetric methods, its ability to establish trust over insecure networks makes it indispensable in modern cryptographic systems.
The development of asymmetric encryption also introduced critical advancements in digital trust and identity verification. Through mechanisms such as digital signatures, it became possible to verify both the authenticity and integrity of messages. A digital signature ensures that a message originates from a verified sender and has not been altered during transmission. This capability is essential in environments where data integrity is just as important as confidentiality, such as financial transactions, software distribution, and secure communications between organizations. It allows systems to operate with a high level of assurance even when interacting over open and untrusted networks.
Despite the strengths of both symmetric and asymmetric encryption, neither method alone is sufficient for all modern security requirements. This limitation led to the widespread adoption of hybrid encryption systems, which combine the advantages of both approaches. In a hybrid model, asymmetric encryption is used to securely exchange a symmetric key, and symmetric encryption is then used for the actual data transmission. This design effectively balances security and performance, ensuring that systems remain both fast and secure.
Hybrid encryption has become a standard approach in many real-world applications, particularly in internet-based communication systems. When a secure connection is established between a client and a server, asymmetric encryption is used first to authenticate the parties and exchange a session key. Once this secure foundation is established, symmetric encryption takes over to handle ongoing communication efficiently. This process ensures that sensitive data such as login credentials, financial information, and personal communications remain protected throughout transmission without introducing unnecessary performance delays.
One of the key strengths of hybrid encryption is its scalability. Modern digital environments involve millions of users, devices, and systems interacting simultaneously across global networks. Managing secure communication at this scale requires encryption methods that are both efficient and reliable. Symmetric encryption provides the speed needed for large-scale data processing, while asymmetric encryption provides the trust framework necessary for secure initialization. Together, they enable secure systems to function effectively even under heavy load and complex network conditions.
Another important aspect of modern cryptographic systems is key management. The security of any encryption method ultimately depends on how well cryptographic keys are generated, stored, distributed, and retired. Weak key management practices can undermine even the strongest encryption algorithms. In symmetric systems, secure key exchange and rotation are essential to prevent unauthorized access. In asymmetric systems, protecting the private key is critical, as its compromise would allow attackers to decrypt sensitive communications or impersonate legitimate users. As systems grow more complex, automated key management solutions have become increasingly important in maintaining consistent security standards.
Digital certificates also play a vital role in strengthening trust within asymmetric and hybrid encryption systems. These certificates bind public keys to verified identities, allowing systems to confirm that they are communicating with legitimate entities. This verification process helps prevent impersonation attacks and ensures that encrypted communication is established with the correct recipient. Certificate-based trust models form the foundation of secure web browsing, enterprise authentication systems, and many other digital security frameworks.
From a performance perspective, encryption systems must constantly balance security requirements with computational efficiency. Symmetric encryption is highly efficient but requires secure key exchange mechanisms. Asymmetric encryption provides strong security for key exchange but is resource-intensive. Hybrid encryption resolves this trade-off by using each method where it performs best. This layered approach ensures that systems remain both secure and responsive, even in demanding operational environments.
Security resilience is another critical outcome of modern encryption design. By combining multiple cryptographic layers, systems become more resistant to a wide range of attacks, including interception, impersonation, and data tampering. Even if one layer is compromised, additional protections help maintain overall system integrity. This multi-layered defense strategy is essential in today’s threat landscape, where cyberattacks are increasingly sophisticated and persistent.
As digital transformation continues across industries, encryption technologies will remain central to securing data and communication. Emerging technologies, expanding cloud infrastructures, and increasing global connectivity all contribute to a growing need for stronger and more efficient cryptographic systems. While current methods such as symmetric, asymmetric, and hybrid encryption provide a robust foundation, ongoing research and development continue to refine and enhance these systems to address future challenges.
Ultimately, the relationship between symmetric and asymmetric encryption is not one of competition but of collaboration. Each serves a distinct purpose within the broader security ecosystem, and together they enable the secure functioning of modern digital communication. Symmetric encryption delivers speed and efficiency, asymmetric encryption provides trust and secure key exchange, and hybrid systems combine both to create scalable and resilient security architectures.