Cryptographic attacks represent a critical area of concern in cybersecurity, focusing on methods used to bypass or weaken mechanisms that protect sensitive data and control access to systems. These attacks do not always rely on breaking encryption algorithms directly. Instead, they often exploit weaknesses in how cryptographic systems are implemented, especially in authentication workflows. Authentication systems are designed to verify identity, typically using credentials such as usernames and passwords. When these systems are improperly secured or rely on weak user inputs, they become prime targets for attackers. The goal of most cryptographic attacks is not necessarily to decrypt data but to gain unauthorized access by circumventing authentication controls.
Modern systems depend heavily on cryptographic primitives such as hashing algorithms, encryption standards, and secure communication protocols. These mechanisms are theoretically robust, but their real-world effectiveness depends on how they are applied. Weak password policies, predictable user behavior, and outdated hashing techniques create opportunities for attackers. Even the strongest algorithms can fail if implemented poorly. As a result, understanding the nature of cryptographic attacks requires both a conceptual understanding of cryptography and practical awareness of system vulnerabilities.
The Central Role of Authentication Systems
Authentication serves as the gateway to protected systems, making it one of the most targeted components in cybersecurity. Every time a user logs into an application, accesses a network service, or connects to a remote server, an authentication process takes place. This process typically involves verifying credentials against stored data, which is often protected using cryptographic hashing. Instead of storing plain text passwords, systems store hashed versions, which are generated using one-way algorithms. This approach ensures that even if the database is compromised, the original passwords are not immediately exposed.
However, authentication systems are only as strong as their weakest link. If users create weak passwords or reuse them across multiple platforms, attackers can exploit these habits. Additionally, if systems fail to implement protections such as rate limiting or account lockouts, attackers can repeatedly attempt to guess credentials without significant resistance. Authentication systems must also defend against both online and offline attacks. Online attacks involve interacting directly with a live system, while offline attacks occur when attackers obtain stored data and attempt to crack it without network restrictions.
The importance of authentication extends beyond individual users. In enterprise environments, compromised credentials can lead to unauthorized access to critical infrastructure, sensitive data, and administrative controls. This makes authentication a high-value target and a focal point for both attackers and defenders.
Brute Force Attacks: The Simplest Yet Effective Method
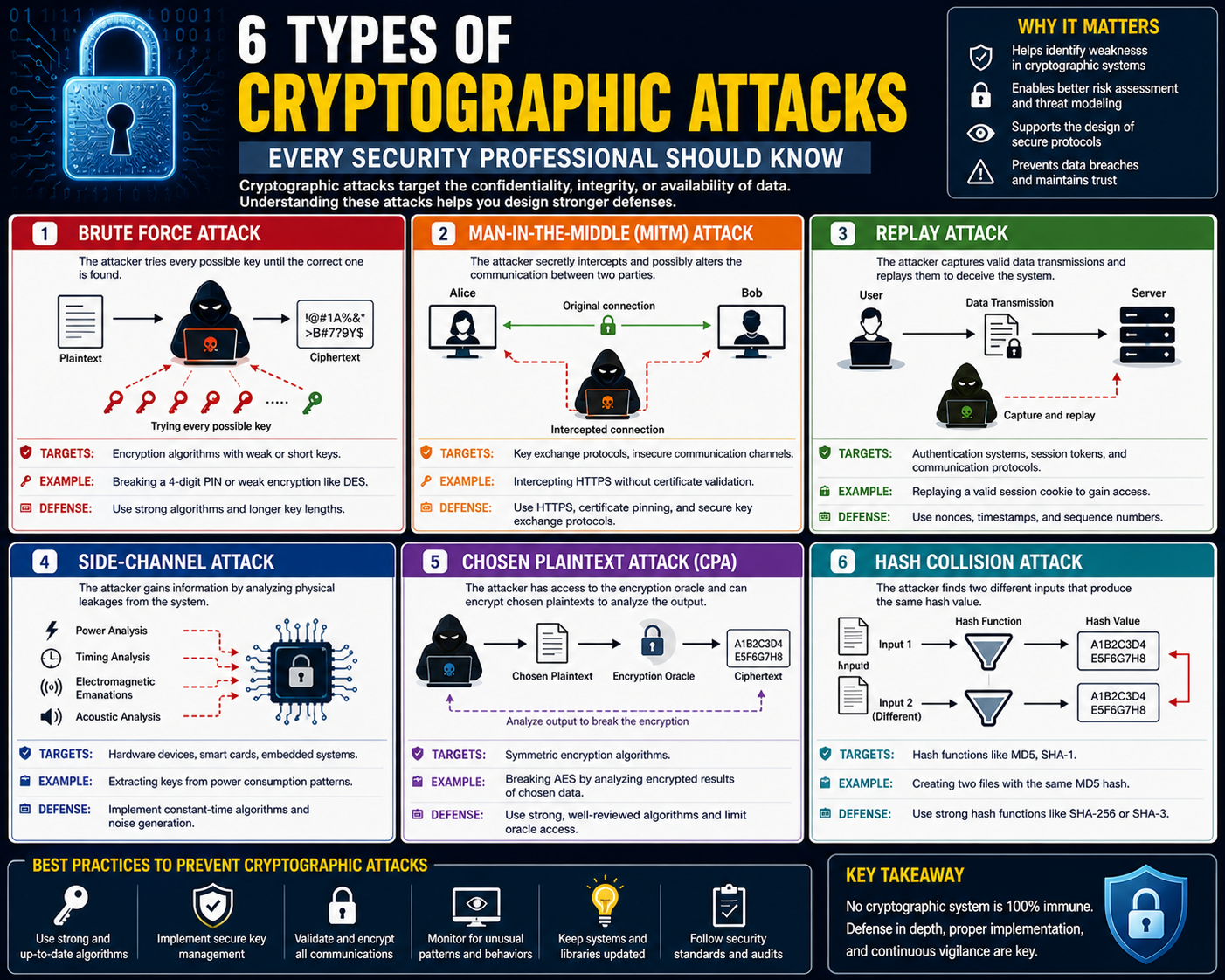
Among all cryptographic attack techniques, brute force attacks are the most straightforward. The principle behind a brute force attack is simple: try every possible password until the correct one is found. This method does not require advanced knowledge of cryptographic algorithms or system vulnerabilities. Instead, it relies on computational power and persistence. Despite its simplicity, brute force remains highly effective, particularly against weak or commonly used passwords.
Brute force attacks are often automated using specialized tools that can rapidly generate and test password combinations. These tools can target various authentication protocols, including remote access services, file sharing systems, and web-based login forms. By systematically attempting different credentials, attackers can eventually gain access if the password is not sufficiently complex. The success of a brute force attack depends on several factors, including password length, character diversity, and system defenses.
One of the key characteristics of brute force attacks is their predictability. Since they rely on exhaustive searching, they can be slow and resource-intensive. However, advancements in computing power have significantly increased the speed at which these attacks can be conducted. High-performance hardware and parallel processing allow attackers to test large numbers of combinations in a relatively short time.
Dictionary Attacks and Human Predictability
A more refined version of brute force is the dictionary attack, which leverages the predictability of human behavior. Instead of attempting every possible combination, attackers use predefined lists of commonly used passwords. These lists are compiled from leaked data, common patterns, and frequently used phrases. By focusing on likely candidates, dictionary attacks can achieve faster results compared to traditional brute force methods.
Human behavior plays a significant role in the effectiveness of dictionary attacks. Many users choose passwords that are easy to remember, such as names, dates, or simple variations of common words. Even when users attempt to create complex passwords, they often follow predictable patterns, such as replacing letters with numbers or adding symbols at the end. Attackers exploit these tendencies by including variations of common passwords in their wordlists.
Dictionary attacks are particularly effective when combined with automation. Attack tools can iterate through large wordlists, testing each entry against a target system. This approach significantly reduces the time required to find a valid password. In many cases, attackers can compromise accounts within minutes if the passwords are weak or commonly used.
Automation and Scaling of Brute Force Techniques
The true power of brute force and dictionary attacks lies in automation. Manual password guessing is impractical, but automated tools can perform thousands or millions of attempts with minimal effort. These tools are designed to handle repetitive tasks, manage network connections, and process authentication responses efficiently. Automation enables attackers to scale their operations, targeting multiple systems simultaneously.
Advanced attack tools can also incorporate features such as parallel processing, distributed attacks, and adaptive strategies. Distributed attacks involve using multiple machines or networks to perform login attempts, reducing the likelihood of detection. By spreading the attack across different sources, attackers can bypass rate limiting and IP-based restrictions. Adaptive strategies allow tools to adjust their behavior based on system responses, improving efficiency and success rates.
Automation also allows attackers to integrate additional data sources, such as leaked credential databases. By combining brute force techniques with known username and password pairs, attackers can increase their chances of success. This approach, often referred to as credential stuffing, highlights the importance of unique passwords across different platforms.
Time Complexity and Practical Constraints
While brute force attacks are conceptually simple, their practicality is limited by time and computational resources. The number of possible password combinations increases exponentially with length and complexity. For example, a short password consisting of only lowercase letters can be cracked relatively quickly, while a longer password with mixed characters requires significantly more time. This exponential growth makes exhaustive brute force attacks impractical for strong passwords.
Time complexity is a critical factor in evaluating the feasibility of an attack. Attackers must balance the effort required against the potential reward. In many cases, they prioritize targets with weaker defenses or more valuable data. Systems that implement protective measures such as rate limiting, account lockouts, and CAPTCHA challenges can significantly increase the time required for a successful attack.
Network limitations also play a role in online brute force attacks. Each login attempt requires communication between the attacker and the target system. High latency, limited bandwidth, and connection restrictions can slow down the attack process. Additionally, repeated failed attempts may trigger security alerts, leading to detection and mitigation.
System Defenses Against Brute Force Attacks
Defending against brute force attacks requires a multi-layered approach. One of the most effective measures is enforcing strong password policies. Users should be encouraged to create long, complex passwords that are difficult to guess. Password length is particularly important, as it has a significant impact on the number of possible combinations.
Rate limiting is another essential defense mechanism. By restricting the number of login attempts within a specific time frame, systems can prevent attackers from making rapid guesses. Account lockouts further enhance security by temporarily disabling accounts after a certain number of failed attempts. These measures increase the cost and complexity of conducting a brute force attack.
Multi-factor authentication provides an additional layer of protection. Even if an attacker successfully guesses a password, they must also bypass a second authentication factor, such as a one-time code or biometric verification. This significantly reduces the likelihood of unauthorized access.
Monitoring and logging are also critical components of defense. By analyzing authentication attempts, security teams can identify unusual patterns and respond to potential threats. Real-time alerts and automated responses can help mitigate attacks before they succeed.
Password Entropy and Security Strength
The concept of entropy is central to understanding password strength. Entropy measures the unpredictability of a password, reflecting the number of possible combinations an attacker must consider. Higher entropy corresponds to greater resistance against brute force attacks. Passwords with low entropy, such as simple or commonly used phrases, can be cracked quickly.
Increasing password entropy involves using longer passwords and incorporating a variety of characters. Randomly generated passwords are particularly effective, as they lack predictable patterns. However, usability must also be considered. Complex passwords can be difficult to remember, leading users to adopt insecure practices such as writing them down or reusing them across multiple accounts.
Balancing security and usability is a key challenge in password management. Techniques such as passphrases, which combine multiple random words, offer a practical solution. These passwords are easier to remember while still providing high entropy. Encouraging the use of password managers can also help users maintain strong, unique passwords without compromising convenience.
From Simple Guessing to Advanced Techniques
Brute force attacks represent the most basic form of cryptographic attack, relying on repetition and probability rather than exploiting structural weaknesses. However, they serve as a foundation for understanding more advanced techniques. As attackers seek more efficient methods, they turn to strategies that leverage mathematical properties of cryptographic systems. These methods can significantly reduce the time and effort required to compromise authentication mechanisms.
The evolution of cryptographic attacks reflects the ongoing interplay between security measures and attack strategies. As defenses improve, attackers adapt by developing new techniques or refining existing ones. This dynamic environment requires continuous learning and adaptation מצד defenders. The next stage of understanding involves exploring how attackers target hashed data directly, using methods that bypass the limitations of traditional brute force approaches.
Advanced Cryptographic Attacks Beyond Brute Force Methods
As digital systems evolved, brute force attacks alone were no longer sufficient for attackers seeking faster and more efficient ways to compromise authentication systems. This led to the development of more advanced cryptographic attack techniques that target weaknesses in how data is stored, processed, and retrieved rather than relying purely on guessing passwords. These methods exploit predictable patterns in cryptographic outputs, vulnerabilities in legacy algorithms, and weaknesses in system design. Unlike brute force attacks, which depend on exhaustive computation, advanced cryptographic attacks often reduce the search space dramatically by leveraging precomputed data or mathematical relationships.
Modern cybersecurity environments must defend not only against direct login attempts but also against offline attacks where attackers analyze stolen data without interacting with the target system. This shift has made cryptographic understanding essential for both attackers and defenders, as even small implementation mistakes can lead to large-scale compromises.
Hashing Mechanisms and Their Security Role
Hashing is a foundational concept in cryptography used to protect sensitive information such as passwords. A hash function transforms input data into a fixed-length string of characters, which appears random. This process is one-way, meaning it is computationally infeasible to reverse-engineer the original input from the hash output. Common hashing algorithms include MD5, SHA-1, and SHA-256, each with varying levels of security and resistance to attacks.
When a user creates a password, systems typically store its hashed version instead of the plaintext. During authentication, the system hashes the entered password and compares it to the stored hash. If both match, access is granted. This method ensures that even if the database is compromised, attackers do not directly obtain plaintext passwords.
However, hashing alone is not sufficient. If two users choose the same password, their hashes will also be identical unless additional security mechanisms such as salting are used. Additionally, older hashing algorithms suffer from vulnerabilities that make them easier to exploit using modern computational techniques.
Rainbow Table Attacks and Precomputed Hash Exploitation
One of the most significant advancements over brute force attacks is the use of rainbow tables. A rainbow table is a precomputed dataset that maps plaintext passwords to their corresponding hash values. Instead of calculating hashes in real time for every attempt, attackers use these precomputed mappings to quickly identify passwords from stolen hash databases.
The effectiveness of rainbow tables lies in the predictability of hash functions. Since a given input always produces the same output, attackers can generate massive databases of hashes in advance. When a breach occurs and hashed passwords are exposed, attackers simply search for matching entries in their precomputed tables.
This method dramatically reduces the time required to crack passwords compared to brute force attacks. However, rainbow tables require significant storage space and preparation time. The larger the password space covered, the larger the table becomes. Despite this limitation, they remain highly effective against systems that do not implement protective measures such as salting.
The Impact of Salting on Hash Security
Salting is a critical defense mechanism designed to counter rainbow table attacks. A salt is a random value added to a password before hashing. This ensures that even if two users have the same password, their resulting hashes will be different due to unique salt values.
The addition of a salt significantly increases the complexity of precomputed attacks. Since each password now produces a unique hash, attackers would need to generate separate rainbow tables for every possible salt combination, making the process impractical.
Salting also improves resistance against dictionary attacks. Even if attackers use common password lists, the presence of a salt forces them to recompute hashes for each attempt, increasing computational overhead. Modern systems typically combine salting with strong hashing algorithms to ensure robust password protection.
Despite its effectiveness, salting must be implemented correctly. Weak or predictable salts can still be exploited, reducing the overall security of the system. Proper implementation involves generating random, unique salts for each password and storing them securely alongside the hash.
Offline Hash Cracking and GPU Acceleration
Unlike online attacks, offline hash cracking occurs when attackers obtain hashed password databases and attempt to recover plaintext passwords without interacting with the target system. This removes network limitations such as rate limiting and account lockouts, allowing attackers to focus entirely on computational efficiency.
Offline cracking often involves tools that leverage high-performance computing resources, particularly graphics processing units. GPUs are highly efficient at performing repetitive mathematical operations, making them ideal for hashing calculations. By distributing workloads across thousands of parallel cores, attackers can test millions or even billions of password combinations per second.
This approach transforms password cracking into a computational problem rather than a network-based one. Attackers can optimize their strategies by prioritizing common passwords, patterns, and previously leaked credentials. The use of GPU acceleration has significantly reduced the time required to crack weak or moderately strong passwords.
However, modern hashing algorithms such as bcrypt, scrypt, and Argon2 are designed to resist GPU acceleration by increasing computational complexity and memory usage. These algorithms intentionally slow down hashing operations to make large-scale attacks economically unfeasible.
Collision Attacks and Hash Function Weaknesses
Collision attacks exploit a fundamental property of hash functions: different inputs can sometimes produce the same output. This occurs because hash functions generate fixed-length outputs regardless of input size. Since the number of possible inputs is virtually infinite, collisions are mathematically inevitable, although ideally extremely rare.
A collision attack occurs when an attacker finds two different inputs that produce identical hash values. In security contexts, this can have serious implications. For example, if two different passwords generate the same hash, a system may incorrectly grant access. Similarly, collisions can be used to create malicious files that appear identical to legitimate ones based on their hash values.
Older hashing algorithms such as MD5 and SHA-1 are particularly vulnerable to collision attacks. Researchers have demonstrated practical methods for generating collisions in these algorithms, making them unsuitable for modern security applications. As a result, they have been largely replaced by more secure alternatives such as SHA-2 and SHA-3.
Real-World Implications of Collision Exploitation
Collision attacks are not purely theoretical; they have real-world consequences in data integrity and security verification. Hashes are widely used to verify the authenticity of files, software updates, and digital signatures. If an attacker can generate a malicious file with the same hash as a legitimate one, they can potentially bypass integrity checks.
This becomes especially dangerous in automated systems that rely on hash verification for updates or data transfers. If a malicious payload matches a trusted hash, it may be accepted without detection, leading to widespread compromise.
While generating collisions for modern algorithms is significantly more difficult, advancements in computing power continue to push the boundaries of what is possible. Security professionals must remain aware of these risks and ensure that outdated algorithms are not in use within critical systems.
Birthday Attacks and Probability-Based Exploitation
The birthday attack is a probabilistic method that increases the likelihood of finding hash collisions. It is based on the birthday paradox, which demonstrates that in a relatively small set of randomly chosen individuals, there is a surprisingly high probability that two people share the same birthday.
Applied to cryptography, this means that instead of trying to match a specific hash, attackers look for any two inputs that produce the same hash output. This significantly reduces the number of attempts required to find a collision compared to brute force methods.
The effectiveness of birthday attacks depends on the mathematical properties of hash functions. As the number of generated hashes increases, the probability of a collision grows rapidly. This makes it an important consideration when designing cryptographic systems.
Modern hashing algorithms mitigate birthday attacks by increasing output size, making collisions statistically less likely. However, the theoretical risk remains an important factor in cryptographic design.
Replay Attacks and Credential Reuse Exploitation
Replay attacks focus on capturing and reusing valid authentication data rather than breaking cryptographic algorithms. In a replay attack, an attacker intercepts a legitimate data transmission and retransmits it to gain unauthorized access.
This type of attack is particularly effective in systems that do not implement session validation or timestamp verification. For example, if authentication tokens are not properly protected, they can be reused by attackers to impersonate legitimate users.
Replay attacks can occur in both digital and physical environments. In wireless communications, attackers may capture signals from devices such as remote key fobs and replay them to gain access. In network environments, intercepted authentication hashes can sometimes be reused to access systems without needing to decrypt them.
Pass-the-Hash and Network-Level Exploitation
A specialized form of replay attack is the pass-the-hash technique, commonly used in Windows-based environments. Instead of cracking password hashes, attackers use captured hashes directly to authenticate themselves within a network.
This technique bypasses the need for plaintext passwords entirely. Once a hash is obtained, it can be used to access other systems that rely on the same authentication mechanism. This makes lateral movement within networks significantly easier for attackers.
Pass-the-hash attacks highlight the importance of secure credential storage and transmission. If systems do not properly protect authentication data, attackers can exploit it without needing to perform complex cryptographic analysis.
Defensive Evolution Against Advanced Cryptographic Attacks
As cryptographic attacks become more sophisticated, defensive strategies must evolve accordingly. Modern systems rely on a combination of strong hashing algorithms, salting, key stretching, and multi-factor authentication to protect against both online and offline attacks.
Key stretching techniques intentionally increase the computational cost of hashing, making brute force and offline cracking significantly slower. Multi-factor authentication adds additional layers of verification beyond passwords, reducing reliance on a single point of failure.
Continuous monitoring, anomaly detection, and secure protocol design also play critical roles in defending against replay and collision-based attacks. By combining cryptographic strength with system-level protections, organizations can significantly reduce their exposure to advanced attack methods.
The progression from brute force methods to advanced cryptographic exploitation demonstrates the evolving nature of cybersecurity threats, where attackers continuously adapt to improvements in defensive technologies.
Collision Attacks and the Structural Weakness of Hash Functions
Collision attacks represent one of the most fundamental threats in cryptographic hash design. At their core, hash functions are designed to map input data of arbitrary size into a fixed-length output. This deterministic transformation ensures consistency: the same input will always produce the same hash output. However, because the output space is finite while the input space is effectively infinite, collisions are mathematically unavoidable. A collision occurs when two distinct inputs generate the same hash value.
In theory, a secure hash function should make finding collisions computationally infeasible. In practice, older algorithms such as MD5 and SHA-1 have demonstrated weaknesses that allow attackers to generate collisions using feasible computational resources. This breaks the assumption that hashes uniquely represent data integrity. When collisions can be intentionally created, the reliability of cryptographic verification systems is compromised.
Attackers exploit this weakness by crafting two different inputs: one benign and one malicious. If both produce the same hash, systems that rely solely on hash comparison may incorrectly validate the malicious input. This makes collision resistance a critical requirement in modern cryptographic design, especially in systems involving digital signatures, file verification, and authentication mechanisms.
Real-World Consequences of Hash Collisions
The practical implications of collision attacks extend far beyond theoretical cryptography. In real-world systems, hashes are widely used to verify software integrity, secure communications, and validate data authenticity. If an attacker successfully generates a collision between a legitimate file and a malicious one, they can potentially bypass security checks.
For example, software distribution systems often provide hash values for downloaded files. Users or automated systems verify downloads by comparing computed hashes against trusted values. If a malicious file shares the same hash as the legitimate version, it may be accepted as authentic without further inspection. This creates a pathway for stealthy malware injection into trusted systems.
Similarly, digital signatures rely on hash functions to verify document integrity. If collision resistance fails, attackers could substitute signed documents with malicious equivalents without invalidating the signature. This undermines trust in digital certification systems and can have serious consequences in financial, governmental, and enterprise environments.
Modern cryptographic standards mitigate these risks by adopting stronger hash functions such as SHA-256 and SHA-3, which significantly increase the computational difficulty of generating collisions. However, the continued existence of legacy systems means collision risks persist in certain environments.
Birthday Attacks and Probabilistic Collision Discovery
The birthday attack is a probabilistic method that increases the efficiency of finding collisions in hash functions. It is based on the birthday paradox, a statistical principle that demonstrates how surprisingly likely it is for two individuals in a group to share the same birthday. In cryptographic terms, this concept applies to hash outputs rather than calendar dates.
Instead of attempting to match a specific hash value, a birthday attack focuses on finding any two inputs that produce the same hash. This reduces the number of required attempts significantly compared to brute force methods. Mathematically, the probability of a collision increases exponentially as more hash outputs are generated, making this approach far more efficient than naive searching.
The effectiveness of birthday attacks depends heavily on the size of the hash output. Smaller hash sizes are more vulnerable because they have fewer possible combinations. As the hash length increases, the probability of collisions decreases, making the attack less feasible. This is one of the reasons modern cryptographic systems use larger hash outputs to maintain security.
Although birthday attacks are primarily theoretical in many modern systems, they remain an important consideration in cryptographic design and analysis. They highlight the importance of selecting appropriate hash sizes and understanding probabilistic risks in security systems.
Replay Attacks and the Reuse of Valid Authentication Data
Replay attacks shift the focus away from breaking cryptographic algorithms and instead exploit the reuse of valid authentication data. In a replay attack, an adversary intercepts a legitimate data transmission and retransmits it to gain unauthorized access. The system, failing to distinguish between original and repeated transmissions, may treat the replayed data as valid.
These attacks are particularly effective in systems that lack proper session management or temporal validation. Without mechanisms such as timestamps, nonces, or session tokens, systems cannot reliably determine whether a request is fresh or previously captured. As a result, attackers can reuse intercepted credentials to impersonate legitimate users.
Replay attacks can occur across various communication channels, including network traffic, wireless transmissions, and authentication protocols. In unsecured environments, even simple packet interception can provide attackers with sufficient data to replicate authentication attempts.
The simplicity of replay attacks makes them especially dangerous in poorly designed systems. Unlike brute force or cryptographic cracking, replay attacks do not require significant computational resources. Instead, they rely on observation and retransmission, making them difficult to detect without proper safeguards.
Pass-the-Hash Attacks in Network Environments
A more advanced variation of replay-based exploitation is the pass-the-hash technique. This method is commonly observed in Windows-based network environments, where authentication relies on hashed credentials rather than plaintext passwords during certain operations.
In a pass-the-hash attack, the attacker obtains a hashed password and uses it directly to authenticate against other systems without needing to decrypt it. Since some authentication protocols accept hashed credentials as valid proof of identity, the attacker can move laterally across a network using stolen hashes.
This technique is particularly dangerous in enterprise environments where credential reuse is common. If multiple systems trust the same authentication mechanism, a single compromised hash can grant access to multiple machines. This enables attackers to escalate privileges and access sensitive resources without ever knowing the original password.
Pass-the-hash attacks highlight a critical weakness in authentication design: the assumption that hashed credentials are safe to transmit or reuse. Modern security frameworks aim to mitigate this risk by implementing stronger authentication protocols and reducing reliance on static hashes.
Offline Attack Strategies and Computational Scaling
Offline cryptographic attacks represent a significant escalation in attack capability. Unlike online attacks, which interact with live systems and are subject to rate limits and detection, offline attacks occur entirely outside the target environment. This happens when attackers obtain hashed password databases or encrypted data and attempt to crack them independently.
The absence of network constraints allows attackers to focus entirely on computational efficiency. High-performance hardware, particularly GPUs, plays a crucial role in accelerating these attacks. GPUs are capable of performing parallel computations at extremely high speeds, making them ideal for repetitive hashing operations.
This computational advantage transforms password cracking into a resource-driven problem. Attackers can test millions or billions of password combinations per second, depending on the complexity of the hash function and the hardware used. As a result, weak or commonly used passwords can be compromised relatively quickly in offline scenarios.
To counter this, modern systems use deliberately slow hashing algorithms such as bcrypt, scrypt, and Argon2. These algorithms introduce computational and memory-intensive operations that significantly reduce the speed of brute force and offline attacks.
Key Stretching and Computational Resistance
Key stretching is a defensive technique designed to increase the computational cost of generating hash values. By repeatedly hashing a password multiple times or introducing computationally expensive operations, systems can slow down attackers attempting brute force or offline cracking.
The purpose of key stretching is not to make attacks impossible but to make them economically infeasible. If each password attempt requires significant computational resources, attackers are forced to invest more time and hardware to achieve results. This increases the cost of large-scale attacks and reduces their practicality.
Key stretching algorithms often incorporate memory-hard functions, which require substantial memory usage in addition to processing power. This further limits the effectiveness of GPU-based attacks, as memory bandwidth becomes a bottleneck.
By increasing the difficulty of each attempt, key stretching helps protect against both brute force and dictionary-based attacks, especially in offline environments where attackers have unlimited time and access to data.
Multi-Factor Authentication as a Structural Defense
While cryptographic defenses focus on strengthening password storage and hashing mechanisms, multi-factor authentication adds a layer of security beyond passwords. This approach requires users to provide multiple forms of verification before gaining access to a system.
Common authentication factors include something the user knows, such as a password; something the user has, such as a hardware token or mobile device; and something the user is, such as biometric data. By combining these factors, systems significantly reduce the risk of unauthorized access even if one factor is compromised.
Multi-factor authentication is particularly effective against password-based attacks, including brute force, dictionary, and replay attacks. Even if an attacker successfully obtains a password or hash, they still need to bypass additional authentication layers.
This layered approach aligns with the principle of defense in depth, where multiple security mechanisms work together to reduce overall system vulnerability.
Cryptographic Protocol Design and Secure Communication
Beyond authentication, cryptographic protocols play a crucial role in securing communication channels. Protocols such as TLS ensure that data transmitted over networks is encrypted and protected from interception or tampering.
Proper protocol design includes mechanisms for preventing replay attacks, ensuring data integrity, and validating authenticity. Features such as session tokens, nonces, and time-based validation help ensure that captured data cannot be reused maliciously.
Weak protocol implementation, however, can introduce vulnerabilities even when strong cryptographic algorithms are used. Misconfigured encryption, outdated protocol versions, and improper key management can all undermine system security.
Evolution of Cryptographic Attack Strategies
The evolution of cryptographic attacks reflects the ongoing balance between offensive and defensive security practices. Early attacks relied heavily on brute force methods, which were limited by computational power. As hardware capabilities improved, attackers developed more efficient techniques such as rainbow tables, offline cracking, and collision exploitation.
In response, cryptographic systems evolved to include stronger hashing algorithms, salting mechanisms, and computationally intensive processes. At the same time, attackers adapted by leveraging distributed computing, GPU acceleration, and probabilistic methods.
This continuous cycle of adaptation demonstrates that cryptographic security is not static. It requires ongoing evaluation, updates, and improvements to remain effective against emerging threats.
Integrated Defense Strategy Against Cryptographic Attacks
A comprehensive defense against cryptographic attacks requires a layered and integrated approach. No single mechanism is sufficient to protect against all attack types. Instead, systems must combine strong cryptographic algorithms, secure authentication methods, and robust operational practices.
This includes enforcing complex password policies, implementing multi-factor authentication, using modern hashing algorithms, and ensuring proper protocol design. Additionally, monitoring systems for unusual activity and maintaining up-to-date security standards are essential components of a strong defense strategy.
By combining these elements, organizations can significantly reduce their exposure to both simple and advanced cryptographic attacks, ensuring greater resilience in an evolving threat landscape.
Conclusion
Cryptographic attacks represent a constantly evolving intersection between mathematical theory, system design, and real-world exploitation. Across all the attack types discussed—from brute force methods to rainbow table exploitation, offline hash cracking, collision-based attacks, birthday paradox applications, and replay-based credential reuse—the underlying pattern is consistent: attackers are not necessarily breaking cryptography itself, but instead exploiting weaknesses in implementation, configuration, or human behavior. This distinction is critical because it shifts the focus of security from purely algorithmic strength to holistic system resilience.
At the foundation, brute force attacks demonstrate the most direct and intuitive form of password compromise. They rely on exhaustive search and computational persistence rather than intelligence or structural exploitation. While conceptually simple, their effectiveness is heavily dependent on password strength and system defenses. In modern environments, brute force attacks alone are often inefficient against well-secured systems, but they remain a baseline threat that every authentication system must account for. Their continued relevance lies not in sophistication, but in scalability and automation, which allow attackers to test large volumes of credentials rapidly when defenses are weak or absent.
Moving beyond brute force, more advanced techniques such as rainbow table attacks reveal how precomputation can dramatically reduce the effort required to reverse hashed credentials. By leveraging predictable outputs of hash functions, attackers can bypass real-time computation and instead rely on stored mappings between plaintext and hash values. However, this method also highlights an important turning point in cryptographic defense: the introduction of salting. By adding randomness to password hashes, salting fundamentally breaks the feasibility of precomputed attacks, forcing attackers to recompute hashes for each unique input. This illustrates a recurring theme in cybersecurity evolution—small architectural changes can render entire categories of attacks ineffective.
Offline hash cracking further escalates the threat landscape by removing network-based constraints entirely. Once attackers gain access to hashed databases, they can operate without rate limits, detection triggers, or connectivity restrictions. The introduction of high-performance GPU computing has transformed this space into a highly parallelized computational problem, where millions of attempts can be tested per second. However, defensive innovations such as memory-hard hashing algorithms have emerged specifically to counter this advantage. Algorithms like bcrypt and Argon2 demonstrate how increasing computational and memory cost can shift the economic balance of attacks, making large-scale cracking impractical.
Collision attacks and birthday-based probabilistic methods expose a different category of vulnerability—one rooted not in password strength but in mathematical limitations of hash functions. Since hash outputs are fixed in size, collisions are inevitable in theory. The security assumption is that they are computationally infeasible to find. However, historical weaknesses in algorithms like MD5 and SHA-1 have shown that this assumption can fail under sufficient computational effort and algorithmic breakthroughs. The implications are significant because collisions can undermine data integrity systems, digital signatures, and trust frameworks that rely on hash uniqueness. This has driven a global transition toward stronger hashing standards with larger output spaces and improved collision resistance.
Replay attacks and pass-the-hash techniques shift the focus away from cryptographic mathematics entirely and instead exploit trust in authentication data. Rather than attempting to break encryption or guess passwords, attackers reuse valid authentication tokens or intercepted credentials. This class of attacks highlights a fundamental weakness in any system that fails to distinguish between original and replayed authentication requests. Pass-the-hash attacks, in particular, demonstrate how credential reuse across networked systems can enable lateral movement without ever revealing plaintext passwords. These techniques emphasize that authentication security is not solely about protecting data at rest, but also about controlling how authentication data is used in transit and during session management.
Across all these attack types, a clear pattern emerges: cryptographic systems are rarely broken through direct mathematical defeat. Instead, failures occur due to implementation flaws, outdated algorithms, weak operational practices, or insufficient defensive layering. This reinforces the importance of defense in depth, where multiple overlapping security controls are used to mitigate risk. Strong password policies, multi-factor authentication, secure hashing algorithms, rate limiting, session validation, and continuous monitoring all contribute to reducing the effectiveness of cryptographic attacks.
Another key insight is the role of human behavior in security outcomes. Many successful attacks exploit predictable user choices such as weak passwords, reuse of credentials, and failure to adopt security best practices. Even the strongest cryptographic systems can be undermined by poor user behavior, making security awareness and policy enforcement essential components of any defensive strategy.
Ultimately, cryptographic security is not a static achievement but an ongoing process of adaptation. As computational power increases and attackers develop new techniques, defensive mechanisms must evolve accordingly. This includes adopting modern cryptographic standards, deprecating weak algorithms, and continuously reassessing system vulnerabilities. The relationship between attackers and defenders is inherently iterative, with each advancement on one side prompting innovation on the other.
The broader implication is that security cannot rely on a single layer of protection. Instead, it must be built as an interconnected framework where cryptographic strength, system design, and operational discipline work together. When these elements are aligned, the effectiveness of cryptographic attacks is significantly reduced, even as attack methods continue to evolve in complexity and scale.