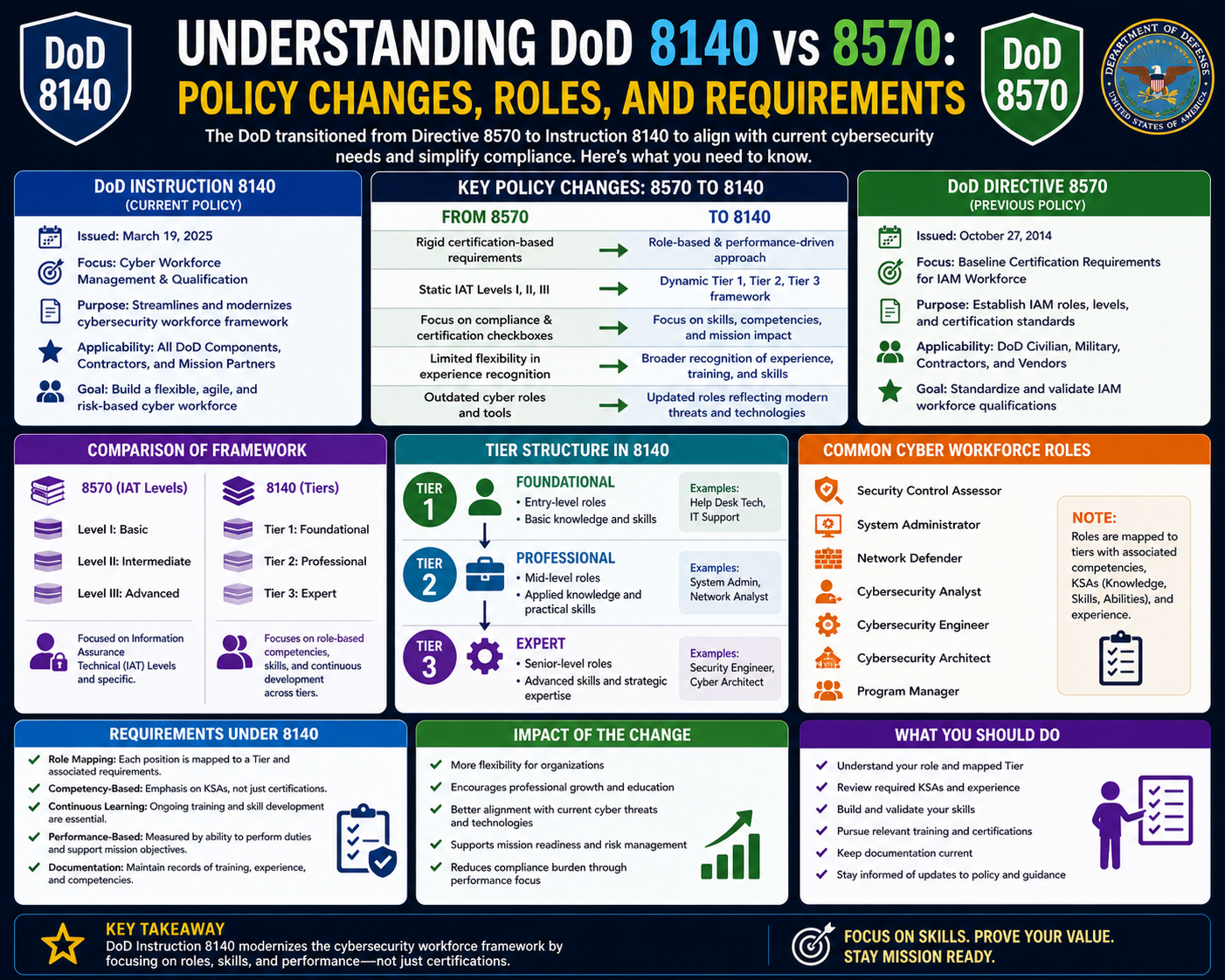
The transition from DoD Directive 8570 to DoD Directive 8140 marks a major shift in how cybersecurity workforce requirements are defined, managed, and implemented within the Department of Defense. This change reflects the growing complexity of cyber threats and the need for a more modern approach to training and certification. While DoD 8570 provided a structured foundation for information assurance roles, it was largely built around static certification requirements. Over time, this approach became less effective in addressing the fast-changing nature of cybersecurity.
DoD 8140 was introduced to modernize this system by shifting the focus from purely certification-based qualifications to a more capability-driven model. Instead of measuring professionals only by the certifications they hold, the new directive emphasizes what they can actually do in real-world situations. This represents a significant evolution in workforce planning, as it aligns more closely with operational performance and practical skills.
The impact of this change extends beyond the Department of Defense. Many public and private organizations have historically followed DoD cybersecurity standards as a benchmark. As a result, changes introduced under 8140 influence broader industry expectations and training models. The shift affects not only military and government personnel but also contractors and cybersecurity professionals across the wider IT sector.
The Purpose and Structure of DoD Directive 8570
DoD Directive 8570 was introduced in 2004 to establish a standardized framework for training and certifying information assurance professionals. At the time, cybersecurity was still developing as a formal discipline, and there was a need for consistent baseline requirements across all defense-related IT roles. The directive aimed to ensure that anyone responsible for protecting information systems had verified knowledge and skills.
The directive itself provided high-level policy guidance, while a detailed manual followed later to define implementation rules. This manual outlined certification requirements for different job roles and created a structured system for workforce classification. It became the primary reference for determining which certifications were required for specific positions within the cybersecurity workforce.
DoD 8570 organized roles into categories based on responsibility and technical complexity. These categories included technical roles, management roles, and specialized cybersecurity positions. Each category had defined certification requirements that individuals needed to meet before they could perform certain job functions. This structure created consistency across the workforce and helped organizations maintain compliance with federal cybersecurity standards.
Role Categories and Certification Pathways Under 8570
Under the DoD 8570 framework, cybersecurity roles were divided into clearly defined categories. These categories helped establish a structured career path for professionals working in information assurance. The system included technical roles responsible for hands-on security tasks, management roles focused on policy and oversight, and specialized roles involving advanced cybersecurity functions.
Technical roles included responsibilities such as system monitoring, vulnerability management, and incident response. These positions required foundational certifications that validated core cybersecurity knowledge. As individuals progressed in their careers, they were expected to obtain more advanced certifications that demonstrated deeper technical expertise.
Management roles focused on overseeing security programs, ensuring compliance, and managing teams of cybersecurity professionals. These positions required a broader understanding of organizational risk and security strategy. Certifications for management roles reflected this broader scope of responsibility.
Specialized roles included advanced areas such as system architecture, security engineering, and cybersecurity operations. These positions required high-level certifications that often involved rigorous exams and practical assessments. They were considered some of the most demanding certifications within the framework.
This structured system provided a clear pathway for career progression. However, it also created limitations by focusing heavily on certifications rather than real-world performance.
Limitations of the Certification-Based Model
While DoD 8570 provided a valuable foundation for cybersecurity workforce standardization, its reliance on certifications as the primary measure of competence eventually revealed several limitations. One of the main challenges was the gap between theoretical knowledge and practical ability. Certifications often tested understanding of concepts, but did not always measure how well individuals could apply those concepts in real operational environments.
Another limitation was the rigidity of the framework. The predefined categories and certification lists made it difficult to adapt quickly to emerging technologies and new cybersecurity roles. As the field evolved, new job functions emerged that did not fit neatly into the existing structure. This created challenges for organizations trying to keep their workforce aligned with current industry demands.
The update cycle for certification requirements also tended to lag behind technological advancements. This meant that by the time new certifications were introduced or existing ones were updated, the industry may have already moved forward. As a result, the framework sometimes struggled to stay fully relevant in a rapidly changing environment.
These limitations highlighted the need for a more flexible and adaptive approach to workforce development, leading to the creation of DoD 8140.
Transition Toward a Modern Cybersecurity Workforce Framework
The introduction of DoD 8140 represents a shift toward a more modern and flexible approach to cybersecurity workforce management. Rather than relying solely on certifications, the new framework emphasizes competencies, tasks, and real-world performance. This change reflects a deeper understanding of what cybersecurity professionals actually need to succeed in operational environments.
Under this new approach, the focus is on capability rather than just credentialing. This means evaluating whether individuals can perform specific tasks effectively, respond to incidents, and adapt to evolving threats. The goal is to ensure that cybersecurity professionals are not only knowledgeable but also capable of applying their skills in practical situations.
This shift also introduces greater flexibility into workforce planning. Instead of rigid role definitions, DoD 8140 allows for more dynamic classification of cybersecurity positions. This makes it easier to adapt to new technologies and evolving job functions without requiring constant structural overhauls.
The transition to this model represents a significant change in how cybersecurity readiness is evaluated and managed across defense-related organizations.
Emphasis on Real-World Skills and Practical Performance
One of the key principles of DoD 8140 is the emphasis on real-world skills and practical performance. This approach recognizes that cybersecurity is a hands-on discipline where theoretical knowledge alone is not sufficient. Professionals must be able to apply their skills in real-time environments where threats are constantly evolving.
To support this shift, the framework encourages the use of performance-based assessments. These assessments focus on how well individuals can complete tasks that mirror real operational scenarios. This provides a more accurate measure of readiness compared to traditional exam-based certification models.
The emphasis on practical skills also supports continuous learning. Cybersecurity professionals are expected to regularly update their knowledge and adapt to new technologies. This ongoing development ensures that the workforce remains capable of handling emerging threats and challenges.
By prioritizing performance, DoD 8140 aims to build a more effective and resilient cybersecurity workforce that can respond to real-world demands.
Expanding Cybersecurity Role Definitions
DoD 8140 introduces a broader and more detailed classification of cybersecurity roles. Instead of limiting roles to a few predefined categories, the new framework recognizes the wide range of responsibilities involved in protecting information systems. This includes areas such as threat analysis, incident response, system design, and risk management.
This expanded role structure reflects the increasing complexity of the cybersecurity landscape. As threats become more advanced, organizations require specialized skills to address different aspects of security. The new framework allows for more precise alignment between job functions and required competencies.
By providing a more flexible role structure, DoD 8140 enables organizations to better match personnel with appropriate responsibilities. This improves efficiency and ensures that individuals are placed in roles that align with their skills and experience.
It also supports career development by allowing professionals to specialize in specific areas of cybersecurity. This helps create deeper expertise within the workforce and strengthens overall security capabilities.
Foundation for a More Adaptive Cybersecurity Workforce
The transition from DoD 8570 to DoD 8140 lays the foundation for a more adaptive and capable cybersecurity workforce. By moving away from a strictly certification-based model, the new framework focuses on practical performance and real-world readiness. This ensures that cybersecurity professionals are better equipped to handle modern threats and operational challenges.
The changes introduced under DoD 8140 reflect the evolving nature of cybersecurity itself. As technology continues to advance, workforce requirements must also evolve to remain effective. This framework provides the flexibility needed to support ongoing change while maintaining a strong foundation of security standards.
Organizations adopting this model must adjust their training and evaluation approaches to align with capability-based assessments. This includes placing greater emphasis on hands-on experience and continuous skill development.
The result is a more dynamic and responsive cybersecurity workforce model that is better suited to today’s threat environment.
DoD 8140 and the Shift Toward a Capability-Based Cybersecurity Workforce
The introduction of DoD Directive 8140 represents a fundamental change in how cybersecurity professionals are evaluated and developed within defense-related environments. Unlike its predecessor, which focused heavily on certification requirements, this new framework emphasizes capabilities, tasks, and real-world performance. This shift reflects the growing understanding that cybersecurity is not just about passing exams or collecting credentials, but about demonstrating the ability to respond effectively to real operational challenges.
The capability-based model introduced under DoD 8140 is designed to ensure that individuals are assessed based on what they can actually do in practice. This includes their ability to perform specific job functions, handle security incidents, and adapt to evolving threats. The goal is to create a workforce that is not only knowledgeable but also operationally effective in dynamic environments.
This change also introduces greater flexibility into workforce development. Instead of relying on rigid certification pathways, the new framework allows for more dynamic role definitions and skill assessments. This makes it easier for organizations to adapt to technological advancements and emerging cybersecurity challenges without being constrained by outdated structures.
Integration of the NICE Framework into DoD 8140
A key component of DoD 8140 is its alignment with the National Initiative for Cybersecurity Education framework. This framework provides a structured way to define cybersecurity work roles, tasks, and competencies. By integrating this model, DoD 8140 creates a more standardized and comprehensive approach to workforce development.
The NICE framework categorizes cybersecurity work into broad functional areas, each representing different types of responsibilities. These categories include areas such as securing systems, protecting networks, analyzing threats, and managing cybersecurity operations. Each category is further divided into specific work roles, which define the skills and knowledge required to perform those tasks effectively.
This structured approach allows for a more detailed understanding of cybersecurity roles. Instead of grouping professionals into broad categories, the framework breaks down responsibilities into clearly defined functions. This makes it easier to align training programs with real-world job requirements.
The integration of this framework into DoD 8140 ensures that workforce development is based on industry-recognized standards. It also helps create consistency across different organizations and sectors that rely on similar cybersecurity principles.
Seven Functional Areas of Cybersecurity Work
Under the updated framework, cybersecurity work is organized into seven primary functional areas. These areas represent the full range of activities involved in protecting information systems and managing cyber risks. Each area focuses on a different aspect of cybersecurity operations.
The first functional area focuses on securing systems and ensuring that infrastructure is properly configured and maintained. This includes tasks such as system hardening, access control management, and vulnerability mitigation. Professionals working in this area are responsible for ensuring that systems are resistant to unauthorized access and attacks.
The second area involves operating and maintaining cybersecurity systems. This includes monitoring system performance, managing updates, and ensuring that security tools are functioning correctly. Individuals in this category play a key role in maintaining the stability and reliability of security infrastructure.
The third area is focused on protecting and defending against cyber threats. This includes activities such as threat detection, incident response, and defensive strategy implementation. Professionals in this area must be able to quickly identify and respond to security incidents.
The fourth functional area involves analyzing cybersecurity data and identifying patterns of malicious activity. This requires strong analytical skills and the ability to interpret complex data sets. Analysts in this category help organizations understand threat landscapes and potential vulnerabilities.
The fifth area focuses on collecting and operating cybersecurity intelligence. This involves gathering information about potential threats and using that intelligence to support defensive operations. It plays a critical role in proactive security measures.
The sixth area is centered on overseeing and governing cybersecurity programs. This includes policy development, compliance management, and strategic planning. Professionals in this category are responsible for ensuring that cybersecurity efforts align with organizational goals and regulatory requirements.
The seventh functional area involves investigating cybersecurity incidents. This includes forensic analysis, evidence collection, and root cause determination. Investigators play a key role in understanding how security breaches occur and preventing future incidents.
Transition from Certification-Centric to Task-Oriented Evaluation
One of the most significant changes introduced by DoD 8140 is the shift from certification-based evaluation to task-oriented assessment. In the previous framework, certifications were the primary measure of competence. While this provided a standardized method of evaluation, it did not always reflect an individual’s ability to perform real-world tasks.
The new approach focuses on evaluating professionals based on their ability to complete specific job functions. This includes assessing how well they can respond to incidents, manage systems, and apply cybersecurity principles in practical scenarios. This shift ensures that workforce readiness is measured more accurately.
Task-oriented evaluation also allows for more realistic training methods. Instead of relying solely on theoretical exams, professionals are assessed through practical exercises that simulate real-world environments. This provides a better understanding of their actual capabilities.
This approach improves the overall quality of cybersecurity personnel by ensuring that they are prepared for the challenges they will face in operational settings.
Impact on Cybersecurity Training and Development Programs
The introduction of DoD 8140 has had a significant impact on how cybersecurity training programs are designed and delivered. Training providers must now focus more on practical skills and real-world applications rather than purely theoretical knowledge.
This shift requires the development of training environments that simulate real operational scenarios. These environments allow professionals to practice responding to cyber incidents, managing systems, and analyzing threats in controlled settings. This hands-on approach improves skill retention and enhances overall readiness.
Training programs are also becoming more modular and flexible. Instead of following rigid certification pathways, learners can now focus on specific skill areas based on their job roles and career goals. This allows for more personalized and efficient learning experiences.
Continuous learning has become a central aspect of cybersecurity development under this framework. Professionals are expected to regularly update their skills to keep pace with evolving threats and technologies. This ensures that the workforce remains capable of addressing new challenges as they arise.
Role-Based Competency Mapping Under DoD 8140
A key feature of the new framework is role-based competency mapping. This approach defines the specific skills, knowledge, and abilities required for each cybersecurity role. By mapping competencies to job functions, organizations can better align training and workforce development efforts.
Each role within the cybersecurity workforce is associated with a set of core competencies. These competencies define what individuals must be able to do to perform their jobs effectively. This includes both technical skills and cognitive abilities such as problem-solving and decision-making.
Competency mapping also helps identify skill gaps within the workforce. By comparing current capabilities with required competencies, organizations can develop targeted training programs to address deficiencies. This improves overall workforce effectiveness.
This structured approach ensures that cybersecurity personnel are better prepared for their roles and that organizations can maintain a high level of security readiness.
Expansion of Cybersecurity Work Roles and Specializations
DoD 8140 introduces a more detailed classification of cybersecurity work roles. This expansion recognizes the increasing complexity and specialization within the cybersecurity field. Instead of broad categories, roles are now defined with greater precision based on specific functions and responsibilities.
This allows for more accurate alignment between job requirements and individual skills. Professionals can specialize in areas such as threat intelligence, digital forensics, security architecture, or incident response. Each specialization requires a unique set of competencies and training.
The expanded role definitions also support career development by providing clearer pathways for advancement. Individuals can progress within their chosen specialization or transition into related areas as their skills develop.
This level of granularity helps organizations build more effective cybersecurity teams by ensuring that the right skills are applied to the right tasks.
Emphasis on Continuous Skill Development
A major principle of DoD 8140 is the importance of continuous skill development. Cybersecurity is a rapidly evolving field, and professionals must constantly update their knowledge to remain effective. The framework encourages ongoing learning as a core component of workforce development.
Continuous skill development includes regular training, hands-on practice, and exposure to new technologies. This ensures that professionals remain current with emerging threats and industry best practices.
Organizations are encouraged to create environments that support lifelong learning. This includes providing access to training resources, simulation environments, and professional development opportunities. By fostering a culture of continuous improvement, organizations can maintain a more resilient cybersecurity workforce.
This approach also helps bridge the gap between academic knowledge and practical experience, ensuring that professionals are fully prepared for operational challenges.
Strengthening Operational Readiness in Cybersecurity
One of the primary goals of DoD 8140 is to improve operational readiness within cybersecurity teams. By focusing on capabilities and real-world performance, the framework ensures that personnel are better prepared to respond to incidents and manage security challenges.
Operational readiness requires a combination of technical skills, analytical thinking, and decision-making ability. The new framework emphasizes all of these areas, ensuring that professionals are well-rounded and capable of handling complex situations.
This focus on readiness improves the overall security posture of organizations. By ensuring that personnel are properly trained and evaluated, the risk of security breaches and operational failures is reduced.
The emphasis on real-world performance also helps organizations respond more effectively to emerging threats, improving overall resilience.
Preparing the Workforce for Evolving Cyber Threats
Cyber threats continue to evolve in complexity and scale, requiring constant adaptation from cybersecurity professionals. DoD 8140 is designed to support this evolution by creating a more flexible and responsive workforce model.
By focusing on capabilities rather than static certifications, the framework ensures that professionals can adapt to new threats as they emerge. This adaptability is essential in a field where attack methods and technologies change rapidly.
The framework also encourages proactive security practices. Instead of simply reacting to incidents, professionals are trained to anticipate and prevent threats. This shift toward proactive defense improves overall security effectiveness.
As cyber threats continue to grow in sophistication, the need for a capable and adaptable workforce becomes increasingly important. DoD 8140 provides the structure needed to meet this challenge.
How DoD 8140 Redefines Cybersecurity Workforce Management
The introduction of DoD Directive 8140 represents a major restructuring of how cybersecurity workforce management is handled within defense-related environments. While earlier frameworks focused heavily on certification compliance and predefined career tracks, the newer model takes a broader and more adaptive approach. It recognizes that cybersecurity is no longer a static field where fixed knowledge can guarantee long-term effectiveness. Instead, it is a constantly evolving discipline that demands flexibility, practical experience, and continuous skill refinement.
DoD 8140 shifts workforce management from a compliance-driven system to a performance-driven system. This means that rather than simply verifying whether an individual holds a specific certification, organizations are encouraged to evaluate whether that individual can perform required tasks effectively in real operational environments. This shift fundamentally changes how hiring, training, and promotion decisions are made across cybersecurity roles.
The framework also introduces a more structured alignment between job roles and required competencies. Instead of broad job categories, cybersecurity roles are now defined by specific tasks and functional responsibilities. This allows organizations to better understand exactly what skills are needed for each position and how those skills should be developed over time.
The Role of Competency-Based Workforce Planning
A major pillar of DoD 8140 is competency-based workforce planning. This approach focuses on identifying the exact skills, knowledge, and abilities required for each cybersecurity role and ensuring that personnel development aligns with those requirements. Unlike traditional models that rely on certification checklists, competency-based planning emphasizes measurable performance in real-world scenarios.
Competencies are broken down into detailed components that reflect actual job performance. These include technical abilities such as system configuration and threat detection, as well as cognitive skills like problem-solving, analysis, and decision-making. By defining roles in this way, organizations can more accurately match individuals to positions that suit their capabilities.
This approach also helps identify gaps in workforce readiness. By comparing current employee capabilities with required competencies, organizations can determine where additional training or development is needed. This ensures that cybersecurity teams remain fully prepared to handle emerging threats and operational challenges.
Competency-based planning also improves workforce flexibility. As new technologies and threats emerge, competency models can be updated without requiring a complete overhaul of the entire framework. This adaptability is one of the key advantages of DoD 8140 over earlier systems.
Standardization Through the NICE Framework Alignment
DoD 8140 is closely aligned with the National Initiative for Cybersecurity Education framework, which provides a standardized structure for defining cybersecurity roles and responsibilities. This alignment ensures consistency in how cybersecurity work is categorized and understood across different organizations.
The framework organizes cybersecurity work into functional areas and work roles, each with clearly defined tasks and required competencies. This structure allows organizations to break down complex cybersecurity operations into manageable components. Each role is associated with specific responsibilities, making it easier to design training programs and evaluate performance.
By aligning with this framework, DoD 8140 ensures that workforce development is consistent with broader industry standards. This is particularly important because cybersecurity is a global discipline that requires coordination across multiple sectors and organizations.
The alignment also helps create a common language for cybersecurity roles. This makes it easier for organizations to communicate about job requirements, training needs, and workforce capabilities. It also supports interoperability between different cybersecurity teams and agencies.
Work Role Categories and Functional Groupings
Under the DoD 8140 framework, cybersecurity work is divided into clearly defined functional categories. These categories represent the full spectrum of activities involved in protecting and managing information systems. Each category focuses on a different aspect of cybersecurity operations.
One category focuses on securing systems and ensuring that infrastructure is properly configured and protected. This includes tasks such as access control, system hardening, and vulnerability management. Professionals in this area are responsible for maintaining the foundational security of IT systems.
Another category is centered on operating and maintaining cybersecurity tools and systems. This involves monitoring security infrastructure, applying updates, and ensuring that tools function correctly. These roles are essential for maintaining operational stability.
A third category focuses on protecting and defending against cyber threats. This includes detecting malicious activity, responding to incidents, and implementing defensive strategies. Professionals in this area must be able to react quickly and effectively to security events.
Another important category involves analyzing cybersecurity data. This includes examining threat patterns, identifying vulnerabilities, and interpreting security intelligence. Analytical roles are critical for understanding the broader threat landscape.
There is also a category dedicated to collecting and operating cybersecurity intelligence. This involves gathering information about potential threats and using that intelligence to support defensive operations. This proactive approach helps organizations anticipate attacks before they occur.
Oversight and governance are another key category. This includes managing cybersecurity policies, ensuring compliance, and developing strategic security plans. These roles focus on aligning cybersecurity efforts with organizational objectives.
Finally, investigative roles focus on analyzing security incidents after they occur. This includes forensic analysis, evidence collection, and determining the root cause of breaches. These roles are essential for learning from incidents and improving future defenses.
From Certification Dependency to Skill Validation
One of the most significant changes introduced by DoD 8140 is the reduced dependency on certifications as the sole measure of competency. While certifications remain important, they are no longer the primary method for evaluating workforce readiness. Instead, the focus has shifted toward validating actual skills and performance.
This change addresses a long-standing limitation of certification-based systems, which often measure theoretical knowledge rather than practical ability. In cybersecurity, the ability to respond effectively to real-world incidents is far more important than simply passing an exam.
Skill validation under DoD 8140 involves assessing how well individuals can perform specific tasks in realistic environments. This includes simulated incident response scenarios, system management exercises, and analytical problem-solving tasks. These methods provide a more accurate representation of an individual’s capabilities.
This approach ensures that cybersecurity professionals are not only knowledgeable but also operationally effective. It also helps organizations build teams that are better prepared for real-world challenges.
Evolution of Training and Learning Models
The transition to DoD 8140 has significantly influenced how cybersecurity training programs are designed. Traditional training models that focused heavily on theoretical instruction are being replaced with more practical, hands-on approaches.
Modern training emphasizes experiential learning, where professionals engage in simulated environments that replicate real-world cyber threats. These environments allow learners to practice responding to incidents, analyzing data, and managing systems under realistic conditions.
Training programs are also becoming more modular. Instead of following a fixed curriculum, learners can focus on specific skill areas based on their job roles and career goals. This makes training more efficient and relevant to individual needs.
Continuous learning has become a core requirement under the new framework. Cybersecurity professionals are expected to regularly update their skills to keep pace with evolving threats and technologies. This ongoing development ensures that the workforce remains adaptable and capable.
Improving Real-World Cybersecurity Readiness
A central goal of DoD 8140 is to improve real-world cybersecurity readiness. This means ensuring that personnel are not only trained but also fully prepared to respond to actual security incidents. The emphasis on performance-based evaluation plays a key role in achieving this goal.
Readiness involves more than technical knowledge. It requires the ability to think critically, make decisions under pressure, and respond effectively to rapidly changing situations. The new framework emphasizes all of these skills.
By focusing on readiness, organizations can reduce response times during security incidents and improve overall resilience. This leads to stronger protection against cyber threats and more effective incident management.
The framework also encourages proactive security practices. Instead of reacting to threats after they occur, professionals are trained to identify and mitigate risks before they escalate. This proactive approach strengthens the overall security posture.
Supporting Career Growth and Specialization
DoD 8140 also enhances career development opportunities within the cybersecurity field. By providing a more detailed and flexible role structure, the framework allows professionals to specialize in specific areas of interest.
Specialization areas may include threat intelligence, incident response, digital forensics, security engineering, or risk management. Each specialization requires a unique combination of skills and competencies.
This structure allows professionals to build deep expertise in their chosen areas while still contributing to broader cybersecurity objectives. It also creates clearer career progression pathways, making it easier for individuals to understand how they can advance in their field.
Organizations benefit from this specialization by developing teams with diverse and complementary skill sets. This improves overall effectiveness and ensures that all aspects of cybersecurity are properly addressed.
Long-Term Impact on Cybersecurity Ecosystem
The long-term impact of DoD 8140 extends beyond the Department of Defense. Because DoD standards have historically influenced broader industry practices, this framework is expected to shape cybersecurity workforce development across multiple sectors.
The emphasis on capability-based evaluation is likely to become more common in both public and private organizations. This shift represents a broader movement toward performance-driven workforce management in cybersecurity.
Over time, this approach may lead to more resilient and adaptable cybersecurity teams across the industry. By focusing on real-world skills and continuous development, organizations can better prepare for evolving threats.
DoD 8140 ultimately represents a modernization of cybersecurity workforce strategy. It reflects the changing nature of cyber threats and the need for a more dynamic and practical approach to workforce development.
Conclusion
The transition from DoD Directive 8570 to DoD Directive 8140 represents one of the most important changes in cybersecurity workforce development within the defense sector. It reflects a broader transformation in how cybersecurity itself is understood, moving away from static compliance-based structures toward a more dynamic, capability-driven model. This change is not simply administrative or procedural; it fundamentally reshapes how professionals are trained, evaluated, and prepared for real-world cyber operations.
DoD 8570 played a critical role in establishing order during the early stages of cybersecurity workforce development. At a time when the field was still emerging, it provided a necessary foundation by introducing standardized certification requirements and structured role categories. This ensured that individuals working in sensitive IT and information assurance positions met a minimum level of competence. The framework helped bring consistency to a rapidly growing field and created clear career pathways that organizations could rely on for workforce planning.
However, as technology evolved and cyber threats became more sophisticated, the limitations of this certification-centric model became increasingly apparent. Cybersecurity is not a static discipline. It changes continuously, driven by new attack methods, emerging technologies, and evolving organizational needs. A framework that relies heavily on fixed certifications struggles to keep pace with such rapid transformation. Over time, gaps began to emerge between what professionals were certified to do and what they were actually required to perform in real operational environments.
DoD 8140 was introduced to address these gaps and modernize the cybersecurity workforce model. Its most significant contribution is the shift from a certification-first approach to a capability-based approach. Instead of focusing solely on whether an individual holds specific credentials, the new framework emphasizes whether they can actually perform required tasks effectively. This change aligns cybersecurity workforce development more closely with real-world operational demands.
This evolution is particularly important because cybersecurity success depends on practical performance under pressure. Threats are unpredictable, and incidents often require immediate, well-informed responses. A professional’s ability to analyze a situation, make decisions quickly, and apply technical knowledge in real time is far more important than theoretical understanding alone. DoD 8140 recognizes this reality and places greater emphasis on applied skills, hands-on experience, and task-based evaluation.
Another major contribution of DoD 8140 is its alignment with structured competency frameworks. By integrating modern cybersecurity workforce models, it provides a clearer understanding of job roles, responsibilities, and required skill sets. This structured approach allows organizations to break down cybersecurity work into specific functional areas, making it easier to define expectations and measure performance.
These functional areas cover the full spectrum of cybersecurity operations, including system protection, threat detection, incident response, intelligence analysis, governance, and investigation. Each area represents a critical component of a broader security ecosystem. By organizing work in this way, the framework ensures that no aspect of cybersecurity is overlooked and that responsibilities are clearly defined.
One of the most valuable outcomes of this structure is improved workforce alignment. Organizations can more accurately match individuals to roles based on actual skills rather than just certification titles. This leads to better job performance, more efficient team structures, and stronger overall security outcomes. It also allows professionals to develop deeper expertise in specific areas, contributing to a more specialized and capable workforce.
DoD 8140 also places a strong emphasis on continuous learning and adaptability. In the modern cybersecurity landscape, static knowledge quickly becomes outdated. Professionals must continuously update their skills to keep up with new technologies, evolving threats, and changing operational environments. The framework supports this by encouraging ongoing training, practical exercises, and real-world skill development.
This focus on continuous improvement ensures that cybersecurity teams remain resilient in the face of emerging challenges. Instead of relying on periodic certification cycles, professionals are expected to engage in lifelong learning. This shift not only improves individual performance but also strengthens organizational readiness as a whole.
Another important aspect of the transition is the move toward performance-based assessment. Traditional certification exams primarily evaluate theoretical knowledge. While this is useful, it does not fully capture a professional’s ability to operate in real-world conditions. DoD 8140 addresses this limitation by encouraging the use of practical evaluations, simulations, and scenario-based testing.
These methods provide a more accurate reflection of actual job performance. They test how individuals respond to incidents, manage systems, and solve complex problems under realistic conditions. This approach ensures that cybersecurity personnel are truly prepared for operational demands rather than just academically qualified.
The broader impact of this shift extends beyond the Department of Defense. Because DoD cybersecurity standards have historically influenced industry practices, changes introduced under 8140 are expected to shape workforce development across the entire cybersecurity ecosystem. Organizations in both public and private sectors often look to these standards as benchmarks for best practices.
As a result, the move toward capability-based workforce models is likely to influence how cybersecurity training programs are designed globally. There is an increasing emphasis on practical skills, real-world simulations, and continuous professional development. This represents a significant departure from traditional training models that focused primarily on certification preparation.
The long-term effect of this transformation is the development of a more adaptable and resilient cybersecurity workforce. As threats continue to evolve in complexity and scale, organizations require professionals who can respond effectively to unpredictable situations. DoD 8140 supports this need by ensuring that workforce development is closely aligned with operational reality.
It also encourages a more strategic approach to cybersecurity talent management. Instead of simply filling positions based on certification requirements, organizations can now focus on building teams with complementary skills and capabilities. This leads to more efficient collaboration and stronger overall defense strategies.
In addition, the framework supports clearer career progression pathways. Professionals can better understand how their skills align with different roles and what competencies are needed to advance. This improves motivation, retention, and long-term professional development within the cybersecurity field.
Ultimately, the transition from DoD 8570 to DoD 8140 represents a shift from structure to adaptability, from certification to capability, and from static compliance to dynamic performance. It acknowledges that cybersecurity is no longer just a technical discipline defined by credentials, but a complex operational field that demands real-world expertise, continuous learning, and practical decision-making ability.
This evolution ensures that cybersecurity professionals are better prepared to meet current and future challenges. It strengthens organizational resilience, improves workforce effectiveness, and aligns training with the realities of modern cyber operations. As the digital landscape continues to evolve, the principles embedded in DoD 8140 will remain central to building a capable, responsive, and forward-looking cybersecurity workforce.