Public Key Infrastructure is a structured security framework designed to establish and maintain trust across digital communication networks. It enables verification of identities, protection of data confidentiality, and assurance of data integrity through the use of cryptographic key pairs. At a conceptual level, PKI acts as the foundation for secure digital interaction, ensuring that entities communicating over untrusted networks can still validate each other’s authenticity. Instead of relying on physical verification or direct trust relationships, PKI introduces mathematical trust through encryption mechanisms. The system works by binding digital identities to cryptographic keys in a controlled manner so that systems can confidently determine whether a message, transaction, or connection originates from a legitimate source. This becomes especially important in environments where communication occurs across distributed systems, cloud-based infrastructures, and global networks, where direct trust cannot be assumed.
Asymmetric Cryptography as the Foundation of PKI Operations
Asymmetric cryptography forms the core operational principle behind Public Key Infrastructure. It is based on a pair of mathematically related keys that perform complementary functions. One key is designated as public and is meant for open distribution, while the other is designated as private and is strictly kept under secure control. The fundamental advantage of this approach is that data encrypted with the public key can only be decrypted by the corresponding private key. This eliminates the need for prior secret exchange between communicating parties, which was a limitation in traditional symmetric encryption systems. In addition to encryption, asymmetric cryptography also enables digital signing, where the private key is used to generate a signature that can be verified by anyone using the public key. This dual functionality ensures both confidentiality and authentication within digital communication systems. The mathematical complexity underlying key generation ensures that deriving a private key from its public counterpart is computationally infeasible, making the system highly secure when implemented correctly.
Self-Signed Certificates and Their Role in Initial Trust Establishment
Self-signed certificates represent a fundamental starting point in many cryptographic environments. These certificates are created and signed by the same entity that uses them, rather than being validated by an external trust authority. They are often generated automatically during system setup or application initialization to enable immediate encrypted communication. Because they do not rely on external validation, self-signed certificates are useful in controlled environments such as internal testing, development stages, and isolated systems where external trust chains are not required. However, their lack of third-party validation means that external systems cannot automatically verify their authenticity. This introduces a requirement for manual trust configuration if they are to be used in broader communication environments. Despite this limitation, self-signed certificates play an important role in enabling encryption from the earliest stages of system deployment. They provide a functional mechanism for secure communication while more formal trust relationships are established later in the system lifecycle. Over time, these certificates are often replaced with externally validated alternatives to support wider trust compatibility.
Private Keys as the Foundation of Confidential Control and Security Integrity
Private keys are the most sensitive component within the PKI ecosystem because they provide exclusive control over encrypted data and digital signatures. The confidentiality of a private key directly determines the security of the entire cryptographic system. If a private key is exposed or compromised, any data encrypted with its corresponding public key may become vulnerable to unauthorized access. Additionally, digital signatures generated by that private key could potentially be forged, undermining trust in the system. For this reason, private keys are stored in highly secure environments with strict access restrictions. These environments may include encrypted storage systems, hardware security modules, or isolated system components designed to prevent unauthorized extraction. In well-designed security architectures, private keys are never transmitted across networks and are only accessed by authorized processes when necessary. The lifecycle of a private key is carefully managed, including generation, usage, renewal, and eventual revocation if compromise is suspected. Maintaining strict control over private keys is essential for preserving the integrity of all PKI-based operations.
Public Keys as Mechanisms for Open and Secure Communication
Public keys serve as the openly distributed component of asymmetric cryptography, enabling secure communication between entities without requiring pre-shared secrets. These keys are designed to be accessible to anyone who needs to send encrypted data or verify digital signatures. When a public key is used to encrypt information, only the corresponding private key can decrypt it, ensuring confidentiality even in open communication environments. Similarly, when verifying a digital signature, the public key confirms that the signature was generated by the matching private key. This allows recipients to validate the authenticity of messages without needing direct access to sensitive credentials. Public keys are often embedded within digital certificates to simplify distribution and verification processes. Because they do not provide any ability to decrypt data or impersonate the key owner, public keys can be safely shared across systems, networks, and users. Their accessibility is a critical feature that enables scalable, secure communication across modern digital infrastructures.
Hashing as a One-Way Mechanism for Data Integrity Verification
Hashing is a cryptographic process that transforms input data into a fixed-length output known as a hash value. Unlike encryption, hashing is a one-way function, meaning it cannot be reversed to retrieve the original input. This property makes hashing particularly useful for verifying data integrity and securely storing sensitive information. When data is hashed, even a small change in the original input results in a significantly different output, allowing systems to detect any modifications or corruption. Hashing is commonly used in scenarios where data authenticity must be confirmed, such as verifying downloaded files or ensuring that transmitted data has not been altered during transit. In authentication systems, passwords are not stored in their original form but are instead converted into hash values. This ensures that even if stored data is compromised, the original passwords remain protected. The strength of a hash function lies in its ability to consistently produce unique outputs for different inputs while maintaining computational efficiency and resistance to reverse engineering.
Salting Techniques for Strengthening Hash-Based Security Models
Salting is an enhancement technique applied to hashing processes to increase resistance against predictive or precomputed attack methods. A salt is a randomly generated value that is combined with input data before hashing occurs. This ensures that identical inputs produce different hash outputs, significantly increasing security strength. Without salting, identical inputs would always produce identical hash values, making them vulnerable to lookup-based attack strategies. By introducing randomness into the hashing process, salting prevents attackers from using precomputed databases to reverse-engineer original inputs. In authentication systems, salting ensures that even if multiple users choose the same password, their stored hash values remain unique. This adds a layer of complexity that strengthens overall system security. Salting is particularly important in large-scale systems where large volumes of credential data must be protected against systematic analysis attempts. When combined with strong hashing algorithms, salting significantly enhances resilience against unauthorized data recovery techniques.
Digital Signatures as Cryptographic Proof of Identity and Integrity
Digital signatures provide a mechanism for verifying both the origin and integrity of digital data using asymmetric cryptography. When a digital signature is created, the sender uses a private key to generate a unique cryptographic representation of the data being transmitted. This signature is mathematically linked to both the data and the private key used to create it. When the recipient receives the data, they use the corresponding public key to verify the signature. If the verification process succeeds, it confirms that the data has not been altered and that it was indeed created by the holder of the private key. Digital signatures are widely used in secure communication systems, software distribution, and document validation processes where authenticity is critical. Unlike traditional handwritten signatures, digital signatures cannot be replicated without access to the private key, making them significantly more secure. They also provide non-repudiation, meaning the sender cannot deny having signed the data once it has been verified.
Message Digest Generation for Efficient Data Integrity Checking
A message digest is the output produced by applying a cryptographic hash function to a block of data. The resulting digest has a fixed length regardless of the size of the input data, which makes it efficient for comparison and verification purposes. Message digests are used to confirm whether data has remained unchanged by comparing newly generated digests with previously recorded values. If the values match, it indicates that the data is identical and has not been altered. If they differ, it signals that modifications or corruption have occurred. This mechanism is widely used in verifying software integrity, ensuring that downloaded files are authentic and unmodified. Message digests are designed to be computationally unique for different inputs, reducing the likelihood of collisions where two different inputs produce the same output. Although collision possibilities exist in theory, modern cryptographic hash functions are designed to make such occurrences extremely rare, ensuring high reliability in practical applications.
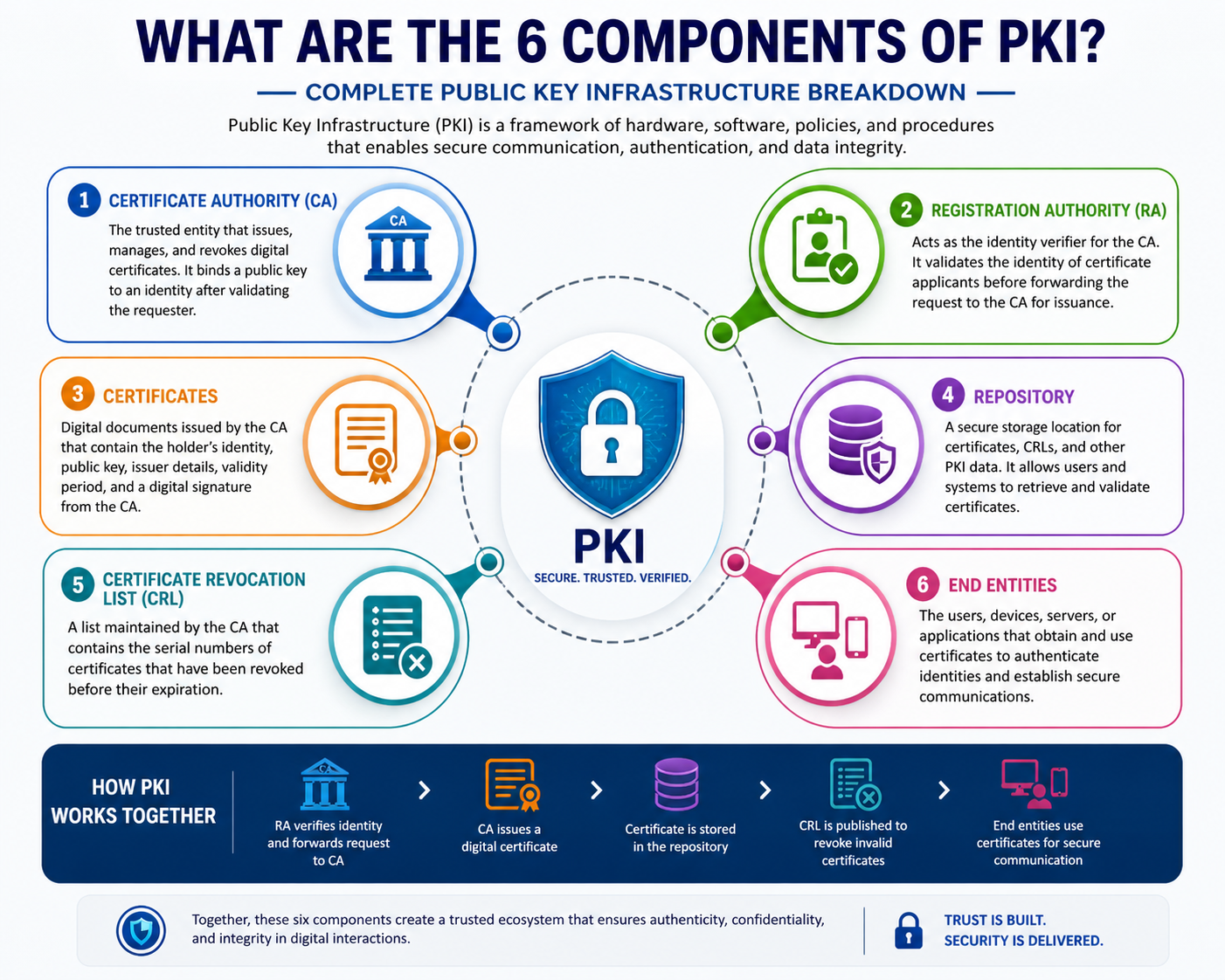
Certificate Authorities as the Trust Backbone of PKI Systems
Certificate Authorities represent one of the most critical components within Public Key Infrastructure because they are responsible for establishing trust between digital entities. A Certificate Authority is an organization or system that issues digital certificates after verifying the identity of an entity requesting them. These certificates bind a public key to an identifiable subject such as a user, device, or service. The primary function of a Certificate Authority is not encryption itself but validation and trust assurance. When a certificate is issued, it acts as a verified identity card in the digital world, confirming that the public key it contains belongs to the claimed entity. This process introduces a trusted third-party mechanism into cryptographic communication, allowing systems to rely on centralized validation rather than individual trust decisions. Certificate Authorities operate under strict security and operational policies because their trustworthiness directly affects all systems that depend on them.
Root Certificate Authorities and the Establishment of Trust Anchors
At the top of the PKI hierarchy sits the Root Certificate Authority, which serves as the ultimate trust anchor in the system. The root CA is self-signed and is considered inherently trusted within a controlled environment. This trust is not derived from external validation but from secure distribution and controlled installation within trusted systems. The root CA is responsible for issuing certificates to intermediate authorities rather than directly issuing certificates to end entities in most architectures. This separation reduces risk by limiting exposure of the root authority, which is typically kept offline or in highly secure environments. Because the root CA establishes the foundation of trust, any compromise at this level would undermine the entire PKI structure. For this reason, strict operational controls, physical security measures, and limited access policies are enforced to protect root CA assets.
Intermediate Certificate Authorities and Hierarchical Trust Distribution
Intermediate Certificate Authorities act as a bridge between the root CA and end-entity certificates. Their primary role is to distribute trust and reduce operational risk by delegating certificate issuance responsibilities. Instead of allowing the root CA to directly issue all certificates, intermediate CAs handle day-to-day certificate management tasks. This layered approach ensures that the root CA remains isolated and protected while still enabling scalable certificate issuance. Intermediate CAs are themselves signed by the root CA, creating a chain of trust that can be validated by systems receiving certificates. This hierarchical structure enhances security by limiting the exposure of the root authority and enabling segmentation of responsibilities. If an intermediate CA is compromised, its certificates can be revoked without affecting the root CA or other intermediates, preserving the integrity of the broader infrastructure.
Registration Authorities and Identity Verification Processes
A Registration Authority functions as a supporting entity within PKI that handles the verification of identities before certificates are issued. While it does not issue certificates directly, it plays a critical role in ensuring that only legitimate entities receive digital certificates. The registration authority verifies identity information provided by applicants and forwards approved requests to the certificate authority for issuance. This separation of duties strengthens security by dividing responsibilities between validation and certificate generation. Registration authorities may perform various verification checks depending on the level of assurance required, including organizational validation, domain validation, or individual identity confirmation. By ensuring that only authenticated entities proceed to certificate issuance, registration authorities help maintain the integrity and reliability of the entire PKI ecosystem.
Digital Certificate Structure and Embedded Identity Information
A digital certificate is a structured data entity that binds a public key to an identity while also containing additional metadata used for validation and trust verification. This metadata typically includes information about the issuer, validity period, subject identity, and cryptographic algorithm used. The certificate also contains a digital signature from the issuing certificate authority, which allows recipients to verify its authenticity. When a system receives a certificate, it can validate the signature using the public key of the issuing authority. If the verification succeeds, the certificate is considered trustworthy within the established chain. Digital certificates serve as the foundation for secure communication protocols by enabling identity verification without requiring direct trust relationships between communicating parties. They also ensure that public keys are associated with verified identities rather than arbitrary or malicious sources.
Certificate Lifecycle Management and Operational Continuity
The lifecycle of a digital certificate includes multiple stages such as generation, issuance, usage, renewal, and eventual expiration or revocation. Proper lifecycle management is essential for maintaining secure and reliable PKI operations. During the issuance phase, identity verification is performed before a certificate is generated and signed by a certificate authority. Once issued, the certificate is used for secure communication, authentication, or digital signing. Over time, certificates may approach expiration, requiring renewal to maintain uninterrupted functionality. Renewal involves generating a new certificate, often with updated cryptographic parameters or extended validity. Lifecycle management also includes monitoring certificate usage to ensure that only valid and trusted certificates remain active within the system. Failure to manage this lifecycle properly can lead to service disruptions, security vulnerabilities, or trust failures within communication systems.
Certificate Revocation and Trust Invalidations in Security Systems
Certificate revocation is the process of invalidating a previously issued certificate before its expiration date. This action is typically taken when a certificate is compromised, misused, or no longer required. Revocation ensures that systems no longer trust certificates that may pose security risks. Once revoked, a certificate is added to a maintained list of invalid certificates so that systems can check its status before accepting it. Revocation plays a crucial role in maintaining trust and integrity within PKI systems because it allows a rapid response to security incidents. Without revocation mechanisms, compromised certificates could continue to be used maliciously until their natural expiration, creating significant security risks. Revocation status is continuously checked during certificate validation to ensure that only valid and trusted certificates are accepted in communication processes.
Certificate Revocation Lists and Centralized Invalid Certificate Tracking
A Certificate Revocation List is a structured record maintained by certificate authorities that contains information about certificates that have been revoked before their expiration. This list is distributed to systems that rely on PKI so they can verify whether a certificate is still valid. When a certificate is presented for validation, the system checks it against the revocation list to ensure it has not been invalidated. If the certificate appears on the list, it is rejected regardless of its original validity period. Certificate revocation lists are periodically updated to reflect the most current state of revoked certificates. While effective, they require regular synchronization to ensure accuracy, which introduces operational overhead in large-scale systems. Despite this, they remain an essential mechanism for maintaining trust and integrity within distributed environments.
Online Certificate Status Protocol for Real-Time Validation
Online Certificate Status Protocol provides a real-time method for checking the validity of digital certificates. Instead of relying on periodically updated lists, systems can query a centralized responder to determine whether a certificate is still valid. This approach improves efficiency by providing immediate verification results and reducing dependency on large revocation list downloads. When a certificate is presented, the system sends a request to a validation service, which responds with the current status of the certificate. The response indicates whether the certificate is valid, revoked, or unknown. This real-time validation mechanism enhances security by ensuring that the most up-to-date status information is always used during authentication processes. It is particularly useful in environments where certificate status changes frequently and immediate verification is required.
Certificate Policies and Security Governance Frameworks
Certificate policies define the rules and guidelines that govern how certificates are issued, managed, and used within a PKI environment. These policies establish the level of trust associated with different types of certificates and outline the procedures required for identity verification. They also define security requirements for key generation, storage, and usage. By standardizing operational practices, certificate policies ensure consistency across all PKI components and reduce the risk of misconfiguration or misuse. These policies may vary depending on the intended use of certificates, with different levels of assurance applied to different types of digital identities. In enterprise environments, certificate policies play a critical role in maintaining compliance, enforcing security standards, and ensuring interoperability across systems.
Key Management Practices and Cryptographic Asset Protection
Key management involves the secure generation, storage, distribution, rotation, and destruction of cryptographic keys used within PKI systems. Effective key management is essential for maintaining the confidentiality and integrity of encrypted communications. Keys must be generated using secure algorithms and stored in protected environments to prevent unauthorized access. Rotation policies ensure that keys are periodically replaced to reduce exposure risk over time. Distribution mechanisms must ensure that public keys are shared securely without compromising associated private keys. When keys are no longer needed, they must be securely destroyed to prevent future misuse. Proper key management ensures that cryptographic systems remain resilient against compromise and maintain long-term operational security.
Certificate Enrollment and Automated Identity Provisioning
Certificate enrollment refers to the process by which entities request and obtain digital certificates within a PKI system. This process typically involves generating a key pair, submitting a certificate signing request, and undergoing identity validation. Once approved, the certificate authority issues a signed certificate that binds the public key to the verified identity. Automated enrollment systems streamline this process by reducing manual intervention and enabling scalable certificate provisioning across large infrastructures. These systems are particularly important in environments where a high volume of certificates must be issued and managed efficiently. Enrollment processes ensure that only authenticated entities receive valid certificates, maintaining the integrity of the overall PKI structure.
Digital Signatures and Their Role in End-to-End Trust Verification
Digital signatures function as one of the most powerful trust mechanisms within Public Key Infrastructure because they provide both authenticity and integrity in a single cryptographic operation. A digital signature is created when a private key is used to generate a unique cryptographic representation of a message, file, or transaction. This signature is mathematically tied to both the content and the key used to create it, meaning that even the smallest modification to the original data will invalidate the signature. When the recipient receives the signed data, they use the corresponding public key to verify the signature. If verification succeeds, it confirms two things at the same time: the data has not been altered, and the sender is the legitimate owner of the private key. This dual assurance makes digital signatures essential in environments where trust, accountability, and data integrity are critical. They are widely used in secure communications, software distribution, financial transactions, and identity verification systems where tamper detection is necessary.
Message Digest Algorithms and Data Integrity Assurance
Message digest algorithms are cryptographic functions that convert input data into a fixed-length output known as a digest. These algorithms are designed to produce unique outputs for different inputs while maintaining consistent output length regardless of input size. The fixed-length nature of message digests makes them highly efficient for comparison and verification purposes. In practical applications, message digests are used to ensure that data has not been altered during transmission or storage. When a file is created or transmitted, a digest is generated and stored separately. Later, when the file is accessed or downloaded, a new digest is computed and compared to the original. If both values match, the data is considered intact. If they differ, it indicates modification or corruption. Message digest algorithms are designed to be one-way functions, meaning it is computationally infeasible to reconstruct the original input from the output. This property ensures that digests can be safely shared without revealing sensitive information.
Cryptographic Hash Functions and Their Security Properties
Cryptographic hash functions are the mathematical foundation behind message digests and play a central role in PKI operations. These functions are designed with several key properties, including determinism, pre-image resistance, and collision resistance. Determinism ensures that the same input will always produce the same output. Pre-image resistance ensures that it is computationally infeasible to reverse-engineer the original input from the hash output. Collision resistance ensures that it is extremely unlikely for two different inputs to produce the same output. These properties make hash functions ideal for verifying data integrity, storing passwords securely, and supporting digital signature mechanisms. In security systems, hash functions are often used in combination with other cryptographic processes to enhance overall protection. Their one-way nature ensures that even if hash values are exposed, the original data remains protected.
Role of Hashing in Secure Password Storage Systems
Hashing plays a critical role in securing authentication systems by ensuring that passwords are never stored in plain text. Instead of saving the actual password, systems store a hashed version of it. When a user attempts to log in, the entered password is hashed again and compared to the stored hash. If the values match, authentication is successful. This approach ensures that even if the storage system is compromised, attackers cannot directly retrieve the original passwords. Hashing also prevents unauthorized access from being easily achieved through simple data exposure. However, because many users may choose similar or identical passwords, additional protection mechanisms are required to strengthen security. This is where salting becomes important, as it ensures that even identical passwords produce different hash outputs, making large-scale attack strategies significantly less effective.
Salting Mechanisms and Resistance to Precomputed Attacks
Salting is a cryptographic technique used to enhance the security of hashed data by introducing randomness into the hashing process. A salt is a unique random value that is combined with the input data before hashing occurs. This ensures that even if two inputs are identical, their resulting hash values will be different due to the unique salt applied to each instance. Salting is particularly effective against precomputed attack methods, where attackers attempt to use large databases of precomputed hash values to reverse-engineer original inputs. By adding a unique salt to each input, these precomputed tables become ineffective because the same input no longer produces a predictable output. In authentication systems, salting ensures that each user’s password hash is unique, even if multiple users choose the same password. This significantly improves the overall security posture of systems that rely on password-based authentication.
Collision Resistance and the Importance of Secure Hash Design
Collision resistance is a critical property of cryptographic hash functions that ensures it is extremely difficult to find two different inputs that produce the same output. While theoretically possible, well-designed hash functions make collisions computationally infeasible in practice. Collision resistance is important because if two different inputs produce the same hash, it could undermine the integrity verification process. For example, an attacker could potentially replace a legitimate file with a malicious one that shares the same hash value, bypassing integrity checks. Modern cryptographic systems rely on advanced hashing algorithms designed specifically to minimize collision risks. As computational power increases, older algorithms may become vulnerable, requiring migration to more secure alternatives. Maintaining collision resistance is essential for ensuring long-term trust in cryptographic systems.
Digital Certificate Validation and Trust Chain Verification
Digital certificate validation is the process of verifying that a certificate is legitimate and has been issued by a trusted authority. This process involves checking the certificate’s signature, validity period, and trust chain. The trust chain is a hierarchical structure that connects a certificate back to a trusted root authority through one or more intermediate authorities. When a system receives a certificate, it traces this chain to ensure that each link is valid and properly signed. If any part of the chain is invalid or untrusted, the certificate is rejected. This mechanism ensures that only certificates issued by recognized authorities are accepted within secure systems. Trust chain verification is fundamental to PKI because it prevents unauthorized or self-generated certificates from being accepted without validation.
Certificate Expiration and Lifecycle Security Enforcement
Certificate expiration is a built-in security mechanism that limits the lifespan of digital certificates. Each certificate is issued with a defined validity period after which it becomes invalid. Expiration ensures that cryptographic materials are periodically refreshed, reducing the risk of long-term compromise. Over time, cryptographic algorithms and key strengths may become outdated due to advances in computing power or the discovery of vulnerabilities. Expiration forces system administrators to replace old certificates with updated versions that meet current security standards. This lifecycle approach ensures that trust relationships remain current and secure. Systems must continuously monitor certificate expiration dates to prevent service interruptions or security failures caused by expired credentials.
Certificate Pinning for Enhanced Trust Enforcement
Certificate pinning is a security technique used to bind a specific certificate or public key to a particular service or application. This ensures that only a predefined certificate is accepted, even if other valid certificates exist within the trust chain. Certificate pinning reduces the risk of man-in-the-middle attacks by limiting the range of acceptable certificates. When a system uses certificate pinning, it ignores external trust chains and instead relies on a known certificate or key fingerprint. This approach strengthens security in high-risk environments but requires careful management because changes in certificates must be updated in all pinned systems. Improper management of certificate pinning can lead to service disruptions if certificates are updated without corresponding updates in pinned configurations.
Secure Key Storage and Hardware-Based Protection Mechanisms
Secure storage of cryptographic keys is essential for maintaining the integrity of PKI systems. Private keys must be protected from unauthorized access, extraction, or duplication. One of the most effective methods of securing private keys is through hardware-based protection systems that isolate cryptographic operations from general-purpose computing environments. These hardware systems ensure that private keys never leave the secure boundary, reducing exposure risk. Even if the host system is compromised, the private key remains protected within the secure hardware environment. Software-based protections are also used in combination with hardware solutions to enforce access controls and encryption at rest. Proper key storage practices are essential for preventing key leakage and maintaining trust in cryptographic operations.
Revocation Mechanisms and Real-Time Trust Invalidation
Revocation mechanisms allow certificate authorities to invalidate certificates that are no longer trustworthy before their natural expiration date. This is essential for responding to security incidents such as key compromise or unauthorized issuance. Once a certificate is revoked, systems must ensure that it is no longer accepted during authentication or encryption processes. Revocation information is distributed through centralized lists or real-time validation services. These mechanisms ensure that compromised certificates cannot continue to be used maliciously. Effective revocation systems are a critical part of PKI because they provide dynamic control over trust relationships, allowing rapid response to security threats.
Online Validation Systems and Dynamic Trust Verification
Online validation systems provide real-time verification of certificate status by querying centralized services. Instead of relying on periodically updated revocation lists, systems can request immediate status information to determine whether a certificate is valid. This approach ensures that trust decisions are based on the most current information available. Online validation improves security responsiveness and reduces delays associated with static verification methods. It is particularly useful in large-scale distributed systems where certificate status may change frequently. By enabling dynamic trust verification, these systems enhance the reliability and efficiency of PKI-based authentication processes.
Conclusion
Public Key Infrastructure represents one of the most fundamental security architectures in modern digital ecosystems, enabling trust, authentication, confidentiality, and integrity across virtually every form of electronic communication. Its importance is not limited to theoretical cryptography but extends deeply into real-world applications such as secure web access, encrypted communications, identity verification, software authenticity validation, and enterprise-level security management. By combining asymmetric cryptography, certificate management systems, hashing techniques, and trust validation frameworks, PKI creates a structured environment where digital identities can be reliably verified without requiring prior direct relationships between communicating parties. This ability to establish trust in untrusted environments is what makes PKI a cornerstone of cybersecurity infrastructure.
At its core, PKI is built upon the principle that trust can be mathematically enforced rather than socially assumed. The interaction between public and private keys allows secure communication channels to be established even across open and potentially hostile networks. The public key enables encryption and verification functions that are openly accessible, while the private key ensures that only authorized entities can decrypt or sign data. This separation of roles is essential for maintaining security boundaries in distributed systems. Without this mechanism, secure communication over the internet would rely heavily on pre-shared secrets, which are neither scalable nor practical in modern computing environments.
The role of certificate authorities within PKI adds another critical layer of trust by introducing a validation hierarchy. Instead of every system independently deciding whether a public key is trustworthy, certificate authorities act as centralized or semi-centralized validators that bind identities to cryptographic keys. This structured trust model ensures that digital identities are not self-declared but verified through established processes. The hierarchical structure involving root and intermediate authorities ensures scalability while preserving security isolation. Root authorities act as ultimate trust anchors, while intermediate authorities handle operational certificate issuance, reducing exposure and minimizing risk at the highest level of the trust chain.
Identity verification processes embedded within PKI are essential for ensuring that certificates are issued only to legitimate entities. Registration mechanisms ensure that, before a certificate is issued, the requesting entity undergoes verification based on predefined trust policies. This prevents unauthorized entities from obtaining valid cryptographic identities. Once issued, certificates act as verifiable digital credentials that can be validated by any system that recognizes the issuing authority. This universal validation capability is what allows PKI to function across global networks without requiring direct relationships between individual systems.
The lifecycle management of certificates further reinforces the security model by ensuring that cryptographic credentials remain valid only for a defined period. Expiration mechanisms force periodic renewal of certificates, which helps mitigate risks associated with outdated cryptographic algorithms or compromised keys. This continuous renewal cycle ensures that trust relationships remain current and aligned with evolving security standards. In addition, revocation mechanisms provide a way to immediately invalidate certificates when compromise or misuse is detected. This dynamic control over validity ensures that PKI systems can respond quickly to security incidents without waiting for natural expiration cycles.
Hashing and message digest functions contribute significantly to the integrity aspect of PKI by enabling systems to verify whether data has been altered. Since hashing is a one-way function, it ensures that original data cannot be reconstructed from its hashed output, making it ideal for integrity checks and secure storage of sensitive information such as passwords. The deterministic nature of hashing allows systems to consistently verify data consistency, while its sensitivity to input changes ensures that even minor modifications are easily detectable. When combined with salting techniques, hashing becomes even more secure by introducing randomness that prevents predictable outputs and resists precomputed attack strategies.
Digital signatures represent a critical convergence point of asymmetric cryptography and hashing, providing a mechanism for verifying both the origin and integrity of digital data. By using private keys to generate signatures and public keys to verify them, digital signatures ensure that messages cannot be forged or altered without detection. This creates a strong foundation for non-repudiation, meaning that the origin of a signed message cannot be denied once verified. In practical terms, this enables secure document exchange, authenticated software distribution, and trusted financial transactions, all of which rely on the assurance that data has not been tampered with and originates from a verified source.
Certificate validation and trust chain verification processes ensure that every certificate used within a system can be traced back to a trusted root authority. This hierarchical validation process prevents unauthorized certificates from being accepted and ensures that trust is always derived from a known and verified source. Each link in the chain must be valid for the certificate to be accepted, creating a structured and enforceable trust model. This mechanism eliminates ambiguity in identity verification and ensures consistent security enforcement across distributed systems.
Key management practices play an equally important role in maintaining the overall security of PKI systems. Cryptographic keys must be generated securely, stored safely, distributed carefully, rotated periodically, and destroyed when no longer needed. Poor key management can compromise even the strongest cryptographic algorithms, as the security of PKI ultimately depends on the secrecy and integrity of private keys. Secure storage mechanisms, including hardware-based solutions, help protect keys from unauthorized access and reduce the risk of exposure in compromised environments.
Revocation and real-time validation systems further enhance PKI by enabling immediate trust decisions based on current security conditions. Instead of relying solely on static certificate validity periods, systems can dynamically assess whether a certificate is still trustworthy. This ensures that compromised or invalid certificates are not used even if they have not yet expired. Real-time validation mechanisms improve responsiveness and strengthen overall security posture by ensuring that trust decisions are always based on the latest available information.
When all of these components operate together, PKI forms a comprehensive and layered security architecture that supports modern digital communication at scale. It enables secure interactions between unknown parties, ensures the authenticity of digital identities, protects sensitive data from unauthorized access, and maintains integrity across distributed systems. The combination of cryptographic principles, hierarchical trust models, and lifecycle-based management creates a robust framework that adapts to evolving security requirements. In an environment where digital threats continue to grow in complexity, PKI remains a foundational technology that supports secure, reliable, and trustworthy communication across global networks.