The CCENT certification represents an entry point into structured networking knowledge that focuses on essential concepts required to understand, build, and troubleshoot small to medium-sized network environments. Even though certification structures may evolve over time, the foundational skills associated with ICND1-level content remain highly relevant in practical networking roles. These skills form the base for more advanced topics in routing, switching, and infrastructure services. Preparation for this level requires more than memorization of commands or definitions. It demands conceptual clarity, hands-on understanding, and the ability to interpret how network components interact in real-time communication scenarios. A strong preparation strategy begins with understanding the full scope of exam objectives and breaking them into manageable learning domains. These domains typically include network fundamentals, LAN switching, routing basics, infrastructure services, and operational procedures. Each of these areas builds on the others, creating a layered understanding of how modern networks function. The most effective learners focus on mastering each layer step by step rather than attempting to cover all topics at once.
Building a Strong Foundation in Network Fundamentals
Network fundamentals form the core of CCENT-level understanding and define how data moves across interconnected systems. At the most basic level, networking involves devices communicating through structured addressing and standardized protocols. One of the first concepts to understand is the difference between data communication types. In a network environment, communication can occur in three primary forms: unicast, multicast, and broadcast. Unicast communication refers to a one-to-one transmission where data is sent from a single sender to a specific receiver. This is the most common form of network communication and is used in everyday activities such as browsing websites or accessing remote servers. Broadcast communication, on the other hand, involves sending data to all devices within a local network segment. This method is useful for discovery processes, but can create unnecessary network load if used excessively. Multicast communication introduces a more efficient model where data is sent to a selected group of devices that have expressed interest in receiving it. This approach is particularly useful in streaming and real-time data distribution environments because it reduces unnecessary duplication of traffic and improves bandwidth efficiency. Understanding these communication types is essential for analyzing network behavior and optimizing performance in different scenarios.
Understanding IPv4 Addressing and Network Segmentation Concepts
IPv4 addressing remains a fundamental component of networking knowledge and plays a critical role in identifying devices within a network. Each IPv4 address serves as a unique identifier that allows devices to send and receive data accurately. IPv4 addresses are divided into logical sections that define both the network portion and the host portion. Subnetting is used to divide larger networks into smaller, more manageable segments, improving both performance and security. A proper understanding of subnet masks is essential for determining which devices belong to the same network and which require routing to communicate. Network segmentation using IPv4 also supports efficient traffic management by reducing unnecessary broadcast traffic within large environments. As networks grow, subnetting becomes increasingly important for maintaining scalability and organization. Learners must also understand private versus public addressing, where private IP ranges are used within internal networks and require translation when communicating externally. This introduces the concept of address translation, which plays a key role in modern network design.
Exploring IPv6 Addressing and Modern Network Transition Principles
IPv6 was developed to address limitations in IPv4, particularly the exhaustion of available address space. It introduces a significantly larger address structure, allowing for virtually unlimited device connectivity in modern networks. One of the key features of IPv6 is its hierarchical addressing model, which simplifies routing and improves efficiency across large-scale environments. A critical component of IPv6 is the link-local address, which is automatically assigned to every interface and is used for communication within the same network segment. These addresses are essential for local operations and are commonly used by routing protocols to establish neighbor relationships. Unlike IPv4, IPv6 does not rely on traditional broadcast communication. Instead, it uses multicast groups to handle similar functions more efficiently. This shift improves overall network performance and reduces unnecessary traffic overhead. Understanding how IPv6 integrates with modern routing systems is essential for ensuring compatibility in evolving network infrastructures. Transition mechanisms between IPv4 and IPv6 also play an important role in real-world deployments, allowing both protocols to coexist during migration periods.
LAN Switching Fundamentals and Data Link Layer Behavior
Local area network switching forms the foundation of internal network communication and operates at the data link layer. Switches are responsible for forwarding frames based on MAC addresses, ensuring that data reaches the correct destination within a network segment. Each device connected to a network interface has a unique MAC address that identifies it at Layer 2. These addresses are used by switches to build forwarding tables that map devices to specific ports. Understanding how switches learn and store MAC address information is essential for diagnosing connectivity issues and optimizing network performance. VLANs, or virtual local area networks, introduce logical segmentation within a physical switching environment. By dividing a network into multiple VLANs, administrators can isolate traffic, improve security, and reduce broadcast domains. A key concept within VLAN configuration is the native VLAN, which handles untagged traffic on trunk links. Proper VLAN configuration ensures that data flows correctly between network segments without unintended interference or leakage. Switching fundamentals also include understanding trunking protocols and how multiple VLANs can traverse a single physical link while maintaining logical separation.
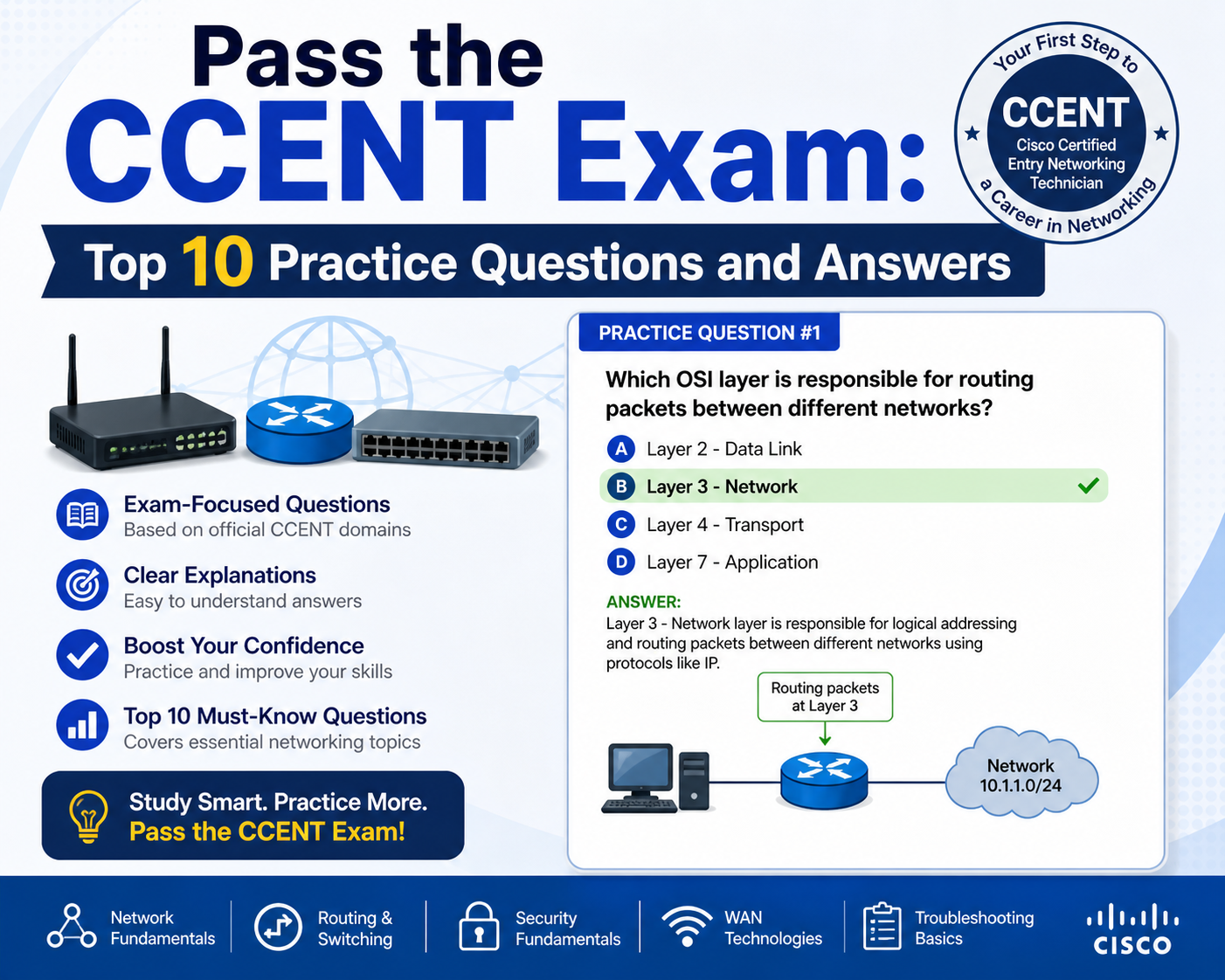
Routing Fundamentals and Inter-Network Communication Principles
Routing is the process of directing data between different networks and is a core component of CCENT-level knowledge. Routers analyze destination IP addresses and determine the most efficient path for data delivery. Routing tables are used to store network paths, including directly connected networks, static routes, and dynamically learned routes. Each routing protocol contributes entries to the routing table using specific identifiers that help distinguish between different sources. Understanding how routing decisions are made is essential for troubleshooting connectivity issues and optimizing network performance. Routing protocols also use metrics to determine the best path, considering factors such as distance, cost, and reliability. In addition to protocol behavior, learners must understand how routers handle packet forwarding at a technical level, including how headers are modified and how time-to-live values prevent routing loops. These mechanisms ensure that data is delivered efficiently across complex network topologies.
Introduction to Network Services and Infrastructure Operations
Network services play a critical role in maintaining operational efficiency and consistency across devices. One important service is network time synchronization, which ensures that all devices within a network share a consistent time reference. This is essential for logging, security authentication, and system coordination. Time synchronization relies on hierarchical structures where devices are assigned different levels based on their distance from a primary time source. Another important infrastructure service is address translation, which allows private networks to communicate with external systems using a shared public address. This process conserves IP resources and enhances security by masking internal network structures. Dynamic translation combined with port-level differentiation enables multiple devices to access external networks simultaneously. These services are essential components of modern networking environments and require a clear understanding of configuration principles and operational behavior.
Developing Analytical Skills for Network Troubleshooting and Exam Readiness
Successful preparation for CCENT-level certification requires the ability to analyze network behavior and troubleshoot issues effectively. This involves understanding how different network layers interact and how problems in one layer can affect overall communication. Practical troubleshooting often begins with verifying physical connectivity, followed by examining addressing configurations, routing tables, and service availability. Tools used for network analysis provide insights into packet flow and help identify where communication breakdowns occur. Developing these analytical skills requires consistent practice and exposure to different network scenarios. Over time, learners become more proficient at identifying patterns, predicting outcomes, and resolving issues efficiently. This level of understanding is essential not only for certification success but also for real-world network administration tasks where quick and accurate decision-making is required.
Advanced LAN Switching Concepts and VLAN Architecture in Modern Networks
As networking environments scale beyond simple device connectivity, LAN switching evolves into a structured system designed to control traffic flow, improve security, and optimize bandwidth usage. At this stage of CCENT-level understanding, switching is no longer just about forwarding frames but about intelligently segmenting networks and managing traffic behavior across multiple logical domains. Virtual LANs, commonly known as VLANs, are central to this design. VLANs allow a single physical switch infrastructure to be divided into multiple logical networks, each operating independently. This segmentation reduces broadcast traffic and improves overall network efficiency by limiting unnecessary data propagation. Each VLAN functions as a separate broadcast domain, meaning devices within one VLAN do not directly communicate with devices in another VLAN without routing intervention. Switches maintain MAC address tables that map device addresses to specific ports and VLAN identifiers. When a frame arrives, the switch examines the destination MAC address and VLAN association before making a forwarding decision. This process ensures that traffic remains within its intended logical boundary unless explicitly routed. Trunk links extend VLAN functionality across multiple switches by carrying traffic from several VLANs over a single physical connection. These trunk links rely on tagging mechanisms that identify which VLAN each frame belongs to, ensuring proper segregation across the network infrastructure. The concept of a native VLAN is also important in trunking environments, as it handles untagged traffic and ensures backward compatibility between devices. Misalignment in native VLAN configurations can lead to traffic leakage or unintended communication paths, making consistency critical in switched network design.
Inter-VLAN Routing and Segmented Network Communication Flow
While VLANs effectively isolate traffic at Layer 2, communication between different VLANs requires routing capabilities at Layer 3. This process is known as inter-VLAN routing and is essential for enabling controlled communication between segmented networks. A router or Layer 3 switching device examines incoming traffic, identifies the destination network, and forwards packets accordingly. Each VLAN is typically associated with a unique IP subnet, allowing routing decisions to be made based on IP addressing information. The routing device maintains knowledge of these subnets and determines the optimal path for data transfer between them. This structure allows organizations to maintain logical separation while still enabling controlled interconnectivity between departments, services, or user groups. Proper configuration of inter-VLAN routing ensures that traffic flows efficiently without bypassing security policies or segmentation rules. Understanding this process is essential for diagnosing connectivity issues in multi-VLAN environments and ensuring consistent communication across network boundaries.
Routing Protocol Behavior and Routing Table Interpretation Techniques
Routing forms the backbone of inter-network communication, enabling data to travel between different network segments through defined paths. Routing protocols are responsible for dynamically sharing network information between routers, allowing them to build and maintain accurate routing tables. These tables contain entries that describe destination networks, next-hop addresses, and associated metrics. Different routing protocols use unique identifiers within routing tables to distinguish their source. These identifiers help network professionals quickly determine how a route was learned and how it should be prioritized. For example, some protocols emphasize speed of convergence, while others prioritize path reliability or simplicity. Understanding how to interpret routing tables is a critical skill for identifying connectivity issues and verifying network design accuracy. Routing behavior is also influenced by administrative distance and metric values, which determine the preference of one route over another when multiple paths exist. Routers continuously evaluate these values to ensure optimal path selection. This dynamic decision-making process allows networks to adapt to changes such as link failures or topology modifications without manual intervention.
Static Versus Dynamic Routing Decision Logic and Network Design Implications
Routing decisions in network environments can be categorized into static and dynamic approaches. Static routing involves manually defining network paths, where administrators specify exact routes that data must follow. This method provides precise control and is often used in smaller or more predictable environments. However, it lacks flexibility when network conditions change. Dynamic routing, on the other hand, relies on routing protocols that automatically discover and update network paths based on real-time conditions. This approach is more scalable and adaptable, making it suitable for larger and more complex networks. Dynamic routing protocols exchange information between routers, allowing them to maintain updated views of network topology. When changes occur, such as a link failure, routers recalibrate their routing tables to reflect new optimal paths. This ability to adapt without manual intervention is one of the key advantages of dynamic routing systems. Understanding the trade-offs between static and dynamic routing is essential for designing efficient and resilient network architectures.
Network Address Translation and Port-Based Traffic Management Systems
Network Address Translation plays a critical role in modern networking by enabling multiple devices within a private network to share a single public address when communicating externally. This process modifies packet header information as traffic moves between internal and external networks. One widely used form of this technology involves combining address translation with port-level differentiation, allowing multiple sessions to be distinguished even when originating from the same external IP address. This mechanism conserves public address space and enhances network security by masking internal network structures from external observers. Translation entries are maintained dynamically, allowing sessions to be tracked and managed efficiently. When internal devices initiate communication with external systems, translation rules map private addresses to public interfaces while maintaining session consistency. This process is essential in environments where large numbers of devices require simultaneous internet access without consuming excessive public IP resources.
Access Control Mechanisms and Traffic Filtering Logic in Network Security
Access control mechanisms provide a structured way to regulate traffic flow within a network by defining rules that permit or deny specific types of communication. These rules operate based on criteria such as source address, destination address, protocol type, and port numbers. By applying filtering logic at strategic points in the network, administrators can enforce security policies and control access to sensitive resources. Access control rules are typically evaluated in a sequential manner, where traffic is compared against each rule until a match is found. Once a match occurs, the corresponding action is applied, either allowing or blocking the traffic. Proper configuration of these rules is essential for maintaining network security while ensuring legitimate communication is not disrupted. Misconfigured access controls can lead to unintended connectivity issues or security vulnerabilities, making careful planning and testing critical.
Infrastructure Services and Time Synchronization in Distributed Networks
Time synchronization is a vital infrastructure service that ensures all devices within a network maintain consistent and accurate system time. This consistency is important for logging events, coordinating authentication processes, and maintaining synchronized operations across distributed systems. Time synchronization systems operate in hierarchical structures where devices are assigned levels based on their proximity to a primary reference source. Devices closer to the source provide more accurate time information, while those further away rely on intermediate synchronization points. This hierarchical approach prevents timing conflicts and ensures stability across large-scale environments. Consistent timekeeping is essential for troubleshooting and auditing network activity, as it allows administrators to correlate events accurately across multiple devices.
Network Troubleshooting Techniques Using Command-Line Verification Tool
Effective network troubleshooting relies heavily on command-line tools that provide real-time visibility into device configurations and network behavior. These tools allow administrators to verify interface status, check IP configurations, and inspect routing tables. One of the most commonly used verification methods involves displaying interface summaries to confirm correct addressing and operational status. Additional tools allow for detailed inspection of routing paths and connectivity tests between devices. These diagnostic techniques are essential for identifying misconfigurations, connectivity failures, and performance issues. By systematically analyzing network components, administrators can isolate problems and implement corrective actions efficiently. The ability to interpret command output accurately is a critical skill for both certification success and real-world network management.
Packet Flow Analysis and Time-to-Live Mechanisms in Network Communication
Understanding how packets move through a network is essential for diagnosing routing behavior and identifying communication issues. Each packet contains a time-to-live value that determines how many hops it can traverse before being discarded. This mechanism prevents packets from circulating indefinitely in the event of routing loops. As packets pass through each router, the time-to-live value is reduced until it reaches zero, at which point the packet is dropped. Network diagnostic tools use this behavior to map routing paths by intentionally manipulating time-to-live values and observing responses from intermediate devices. These responses reveal the path that data takes through the network, providing valuable insight into topology structure and potential bottlenecks. Packet analysis also involves understanding how different protocols respond to expired packets and how error messages are generated to inform the source device of delivery issues. This level of analysis is crucial for diagnosing complex network behavior and ensuring efficient data transmission across interconnected systems.
Understanding Infrastructure Services in Scalable Network Environments
Infrastructure services form the operational backbone of modern networks, enabling communication, coordination, and resource sharing across distributed systems. At the CCENT level, these services are essential for maintaining stability and ensuring that network operations function consistently under varying loads. One of the most important infrastructure services is name resolution, which allows devices to communicate using readable identifiers instead of numeric addresses. Although this concept extends beyond basic CCENT objectives, its influence on network behavior is significant because it affects how users and systems interact with network resources. Another critical service is dynamic configuration management, which ensures that devices can automatically receive network settings such as IP addresses, subnet masks, and gateway information. This automation reduces configuration errors and simplifies network administration, particularly in large-scale environments. Infrastructure services also include monitoring and synchronization mechanisms that help maintain operational consistency across all network devices. These services work together to ensure that data flows smoothly, systems remain synchronized, and network resources are efficiently utilized.
Network Time Synchronization and Hierarchical Clock Distribution Systems
Accurate time synchronization is essential in network environments where coordinated operations and precise logging are required. Network Time Protocol systems operate using a hierarchical structure that defines different levels of time accuracy. Devices at the highest level are directly connected to authoritative time sources, while lower-level devices synchronize through intermediate systems. This hierarchy ensures that time information remains consistent across all devices while preventing synchronization loops. Each device evaluates available time sources and selects the most reliable reference based on its position in the hierarchy. This structured approach is particularly important in environments where security auditing, transaction logging, and system monitoring are required. Without consistent time synchronization, it becomes difficult to correlate events across multiple devices, leading to potential diagnostic challenges. Proper configuration of time synchronization systems ensures that all network components operate with a unified sense of time, which is critical for maintaining operational integrity.
Address Translation Mechanisms and Network Efficiency Optimization
Address translation plays a significant role in enabling communication between private internal networks and external systems. In modern network environments, large numbers of devices often share a limited pool of public addresses. Address translation mechanisms dynamically map internal private addresses to external public interfaces, allowing multiple devices to access external networks simultaneously. This process involves modifying packet headers as traffic passes through network boundaries. One of the most efficient implementations of this concept involves combining address translation with port-level differentiation. This allows multiple internal sessions to be uniquely identified even when they share a single external address. As a result, network resources are conserved while maintaining full connectivity for internal devices. Translation entries are dynamically created and removed based on active sessions, ensuring efficient memory and resource usage. This system is essential for modern network scalability, especially in environments with high device density and frequent external communication requirements.
Routing Table Interpretation and Path Selection Behavior in Network Systems
Routing tables serve as the decision-making framework for network devices when determining how to forward data. Each entry in a routing table contains information about destination networks, next-hop addresses, and associated metrics. These metrics are used to evaluate the most efficient path for data transmission. Routing protocols continuously update these tables based on changes in network topology, ensuring that devices maintain accurate information about available routes. When multiple routes exist to the same destination, the routing system evaluates each based on predefined preferences and performance metrics. This process ensures that data is always forwarded along the most efficient available path. Understanding routing table structure is essential for diagnosing connectivity issues and verifying network design accuracy. Each entry provides insight into how routes were learned and how they are prioritized within the network. This level of understanding is critical for maintaining stable and efficient communication across interconnected systems.
Dynamic Routing Adaptation and Network Convergence Processes
Dynamic routing systems are designed to adapt to changes in network topology without requiring manual intervention. When a change occurs, such as a link failure or new route availability, routing protocols exchange updated information between devices. This process allows the network to converge on a new stable state where all devices have consistent routing information. Convergence speed is an important factor in network performance, as faster convergence reduces downtime and improves reliability. Different routing protocols use various mechanisms to achieve convergence, balancing speed, accuracy, and resource usage. During convergence, routers may temporarily experience inconsistent routing information, but the system stabilizes once all updates are propagated. Understanding convergence behavior is important for diagnosing routing instability and optimizing network performance. It also provides insight into how resilient a network is under changing conditions.
LAN Switching Optimization and Traffic Flow Efficiency Techniques
LAN switching plays a critical role in optimizing internal network communication by ensuring that data is forwarded efficiently between devices. Switches use MAC address tables to determine where to send incoming frames, reducing unnecessary traffic and improving overall performance. These tables are dynamically built as devices communicate across the network. When a switch receives a frame, it records the source MAC address and associates it with the incoming port. This allows future frames destined for that address to be forwarded directly without flooding the network. Efficient switching behavior reduces congestion and improves response times across the network. VLAN segmentation further enhances this efficiency by limiting broadcast domains and isolating traffic between different groups of devices. Proper VLAN design ensures that network traffic is logically organized and that communication paths are optimized for performance and security.
Inter-VLAN Communication and Layer 3 Routing Integration
While VLANs provide effective segmentation at Layer 2, communication between VLANs requires routing at Layer 3. This integration is achieved through routing devices that connect multiple VLANs and enable controlled communication between them. Each VLAN is assigned a unique subnet, and routing decisions are made based on destination IP addresses. This structure allows networks to maintain logical separation while still enabling necessary communication between different segments. Inter-VLAN routing is essential for environments where departments or services need to interact while remaining isolated from unnecessary traffic. Proper configuration ensures that data flows only through approved paths, maintaining both efficiency and security. Understanding how Layer 2 and Layer 3 technologies interact is critical for designing scalable and manageable network architectures.
Packet Forwarding Logic and Time-to-Live Mechanisms in Network Analysis
Packet forwarding is governed by a structured set of rules that determine how data moves across a network. Each packet contains a time-to-live value that prevents it from circulating indefinitely. As packets pass through routers, this value is decreased until it reaches zero, at which point the packet is discarded. This mechanism prevents routing loops and ensures network stability. Diagnostic tools use this behavior to map network paths by gradually increasing time-to-live values and observing responses from intermediate devices. These responses reveal the structure of the network and help identify potential issues such as bottlenecks or misconfigurations. Understanding packet forwarding behavior is essential for troubleshooting connectivity problems and optimizing network performance.
Command-Line Diagnostics and Network Verification Techniques
Network administrators rely on command-line tools to verify configurations and diagnose issues. These tools provide detailed information about interface status, IP configuration, and routing behavior. One of the most important verification steps involves confirming that interfaces are correctly configured and operational. Additional tools allow administrators to inspect routing tables, test connectivity, and analyze packet flow. These diagnostic techniques are essential for identifying configuration errors and resolving connectivity issues efficiently. Accurate interpretation of command output is a critical skill that directly impacts troubleshooting effectiveness and network reliability.
Exam Strategy Development and Structured Learning Approach for Certification Success
Effective preparation for CCENT-level certification requires a structured approach that combines theoretical understanding with practical application. The learning process typically begins with an initial assessment to identify knowledge gaps, followed by targeted study sessions focused on weak areas. As understanding improves, learners shift toward reinforcement and repeated practice through simulated exam scenarios. This iterative process helps build confidence and improve problem-solving speed. Time management is also an important factor during preparation, as exam scenarios require quick and accurate decision-making. Consistent review of core concepts ensures long-term retention and reduces the likelihood of errors during testing. Developing a strong mental model of how networks operate is more valuable than memorizing isolated facts, as it enables learners to apply knowledge flexibly across different scenarios. This approach ensures readiness not only for certification exams but also for real-world networking challenges where adaptability and analytical thinking are essential.
Conclusion
CCENT-level networking knowledge is most valuable when it is understood as an integrated system rather than a collection of isolated topics. Concepts such as IP addressing, subnetting, VLANs, routing behavior, and infrastructure services all work together to form the foundation of modern network communication. The ability to see how these elements interact is what separates theoretical learners from practical network professionals. For example, understanding how VLAN segmentation influences routing decisions or how address translation affects external connectivity provides deeper insight into real-world network behavior. Similarly, recognizing how routing protocols dynamically adapt to changes in network topology helps build an intuitive understanding of how data flows across complex environments. This level of integration is essential not only for exam success but also for long-term effectiveness in networking roles where systems are constantly evolving and expanding.
One of the most important outcomes of the CENT-level study is the development of analytical thinking skills. Networking is not simply about configuring devices but about understanding how and why systems behave in certain ways. When connectivity issues occur, a structured troubleshooting approach is required to isolate the root cause. This involves analyzing each layer of the network, starting from physical connectivity and moving upward through data link, network, and transport layers. Each layer provides specific clues that help narrow down the source of a problem. For instance, a failure at the MAC address level may indicate switching issues, while incorrect IP configuration may point to routing or addressing errors. Developing this layered thinking approach allows network professionals to diagnose issues more efficiently and accurately. Over time, this analytical mindset becomes second nature, enabling faster decision-making and more effective problem resolution in real-world environments.
Consistent practice is a critical factor in mastering CCENT-level concepts. Theoretical knowledge alone is not sufficient for success; it must be reinforced through repeated application in practical scenarios. Working through simulated network environments helps reinforce understanding of how different protocols and configurations behave under various conditions. Practice also improves familiarity with command-line tools, which are essential for verifying configurations and diagnosing issues. Exposure to realistic scenarios builds confidence and prepares learners for the unpredictability of actual network environments. It also helps develop time management skills, which are important during certification exams where complex questions must be answered within limited timeframes. Regular practice ensures that knowledge remains fresh and readily accessible when needed.
A structured learning progression is essential for building confidence in networking skills. Starting with foundational concepts and gradually advancing to more complex topics allows learners to build a strong knowledge base without becoming overwhelmed. Each stage of learning reinforces the previous one, creating a layered understanding of networking principles. This progression typically begins with basic concepts such as IP addressing and device communication, followed by switching and VLANs, then routing and infrastructure services, and finally troubleshooting and optimization techniques. As learners move through these stages, they develop a clearer understanding of how networks operate as complete systems. Confidence grows naturally as knowledge becomes more structured and interconnected. This confidence is crucial not only for passing certification exams but also for performing effectively in professional network environments.
Troubleshooting is one of the most valuable skills developed during CCENT-level study. Networks are dynamic systems where issues can arise unexpectedly due to configuration errors, hardware failures, or changes in topology. Effective troubleshooting requires a logical and systematic approach. This involves gathering information, isolating the problem, testing hypotheses, and applying corrective actions. Command-line tools play a central role in this process by providing visibility into device status, routing information, and connectivity paths. Understanding how to interpret this information accurately is essential for identifying the root cause of issues. Over time, troubleshooting becomes more intuitive as learners develop experience and pattern recognition skills. This ability to quickly diagnose and resolve issues is highly valued in professional networking roles.
While CCENT-level certification serves as an important milestone, the knowledge gained during preparation extends far beyond the exam itself. The concepts learned form the foundation for advanced networking certifications and professional roles in network administration, engineering, and security. Skills such as routing analysis, switching configuration, infrastructure management, and troubleshooting are directly applicable to real-world environments. As networks become more complex, the ability to understand underlying principles becomes increasingly important. Professionals who master these foundational skills are better equipped to adapt to new technologies and evolving network architectures. This adaptability is a key factor in long-term career growth within the networking field.
Networking is a continuously evolving field where technologies, protocols, and best practices are constantly changing. As a result, successful professionals adopt a long-term learning mindset that emphasizes continuous improvement and skill development. CCENT-level knowledge serves as the starting point for this journey, providing the essential building blocks needed for advanced learning. Maintaining curiosity and staying engaged with new developments in networking helps ensure that skills remain relevant and up to date. This mindset also encourages exploration of advanced topics such as network automation, security integration, and cloud networking, which are becoming increasingly important in modern IT environments.
Mastering CCENT-level concepts provides a strong foundation for anyone pursuing a career in networking. The combination of theoretical understanding and practical application builds a comprehensive skill set that is applicable in a wide range of professional environments. From basic connectivity to advanced routing and infrastructure services, each concept contributes to a deeper understanding of how networks function as interconnected systems. The ability to analyze, configure, and troubleshoot these systems is what defines a competent network professional. As learners progress beyond this level, they carry forward not just technical knowledge but also critical thinking skills, problem-solving abilities, and a structured approach to learning that will support continued success in the field of networking.