Web filtering in a FortiGate firewall is a core security control mechanism designed to regulate and inspect web traffic passing through a network boundary. It operates as part of a next-generation firewall framework, where traffic is analyzed not only on traditional parameters such as IP addresses and ports but also on application identity, URL categorization, and behavioral patterns. This enables a more intelligent enforcement model that adapts to modern web usage, where encrypted traffic and dynamic web applications dominate enterprise environments.
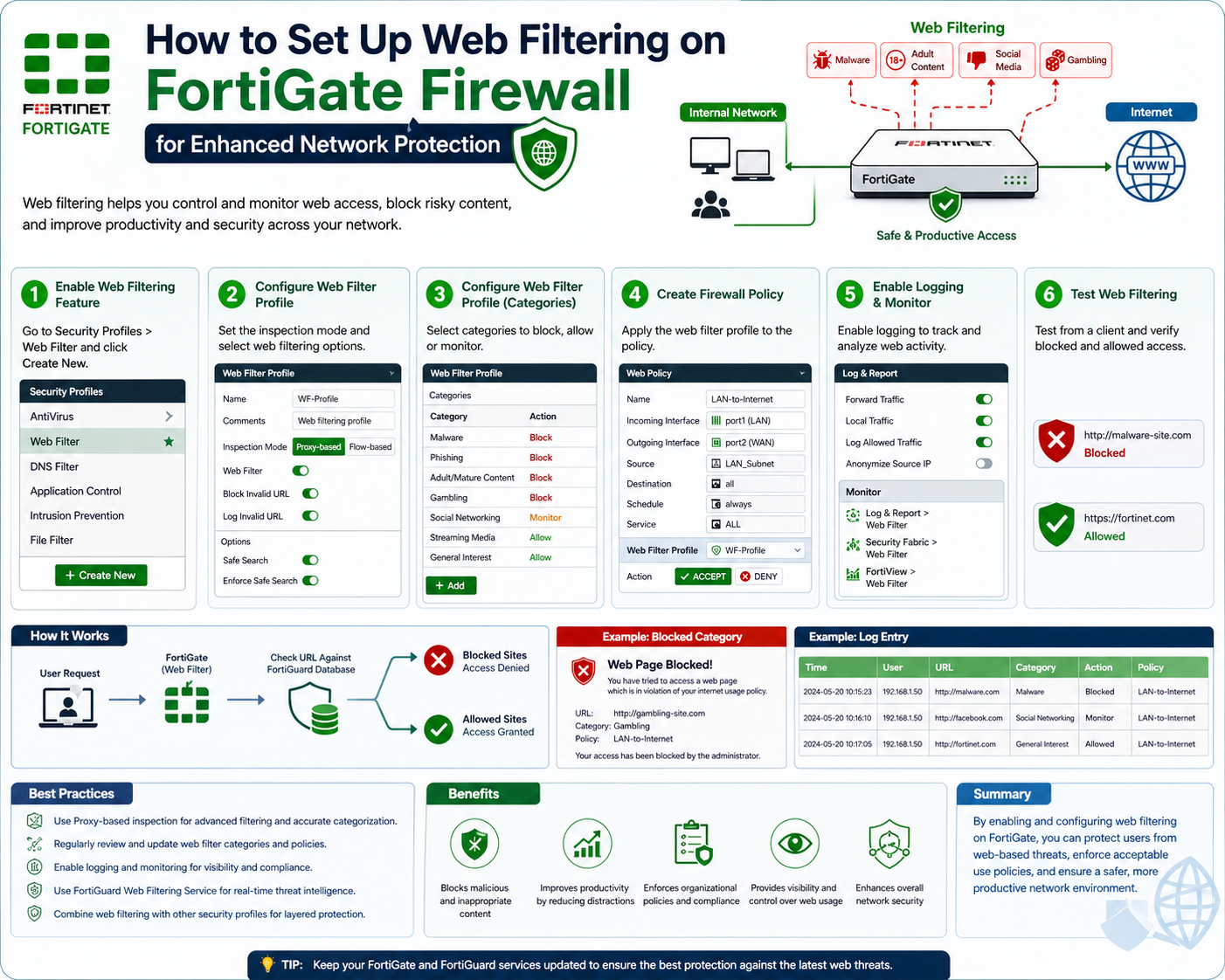
At its core, FortiGate web filtering functions by evaluating web requests against predefined security policies. These policies are constructed using web filtering profiles, which define how different categories of web content should be handled. When a user attempts to access a website, the firewall intercepts the request, analyzes it through its filtering engine, and determines whether the connection should be allowed, blocked, or monitored.
The importance of web filtering extends beyond simple access control. It plays a critical role in reducing exposure to malicious domains, preventing data exfiltration attempts, and enforcing acceptable use policies within organizations. By acting as a centralized enforcement point, FortiGate ensures consistent control over internet traffic across all users and devices connected to the network.
Role of Next-Generation Firewall Modes in Web Filtering Deployment
FortiGate devices operate using two distinct NGFW operational modes, and understanding these modes is essential before configuring web filtering.
The first mode is the profile-based mode. In this configuration model, security features such as web filtering, antivirus inspection, and application control are defined as reusable security profiles. These profiles are then attached to firewall policies. This modular design allows administrators to maintain a centralized set of security rules that can be applied consistently across multiple policies. It significantly reduces configuration redundancy and improves long-term manageability.
The second mode is the policy-based mode. In this approach, security settings are directly embedded into each firewall policy. Instead of referencing external profiles, each rule independently defines its own inspection parameters. While this can simplify small-scale deployments, it can introduce complexity in larger environments due to duplicated configurations and reduced standardization.
In most enterprise and security-focused deployments, profile-based mode is preferred. It aligns with structured security design principles, where separation of policy logic and security controls allows for better scalability, auditing, and maintenance. It also supports more efficient updates, as changes made to a single profile automatically apply across all associated policies.
System Preparation Before Enabling Web Filtering
Before implementing web filtering, the FortiGate system must be properly prepared to ensure that filtering mechanisms function as expected. One of the first steps involves confirming that the firewall is operating in the correct NGFW mode. Profile-based mode is typically required for structured web filtering configurations.
Once the operational mode is established, the system must be configured to support security profiles. This ensures that web filtering profiles can be created independently and later attached to firewall policies. Without this structure, web filtering functionality may be limited or inconsistently applied.
Another critical preparation step involves verifying firmware and security database updates. FortiGate web filtering relies heavily on cloud-based and locally cached categorization databases. These databases classify websites such as social networking, streaming media, productivity tools, malicious domains, and more. Keeping these databases updated ensures accurate classification and reduces false positives or missed detections.
Additionally, administrators must consider SSL inspection capabilities. Since a large portion of web traffic is encrypted using HTTPS, web filtering effectiveness is significantly reduced without SSL inspection. Enabling decryption allows the firewall to inspect the actual content of web sessions, enabling more accurate filtering decisions. However, this must be balanced against performance impact and privacy considerations.
Security Profiles as the Foundation of Web Filtering Control
Web filtering in FortiGate is implemented through security profiles, which act as rule-based containers defining how web traffic should be handled. A web filtering profile can include multiple layers of control, such as URL filtering, category-based filtering, reputation scoring, and content inspection.
When a user initiates a web request, the firewall evaluates the session against the active firewall policy. If the policy includes a web filtering profile, the request is passed to the filtering engine for deeper inspection. The URL is then analyzed against multiple data sources, including local allow/block lists, FortiGuard categorization services, and heuristic analysis engines.
Based on this evaluation, the firewall determines the appropriate action. If the website is categorized as safe and allowed, the connection proceeds normally. If it is classified as malicious or restricted, the session is blocked. In some configurations, traffic may be logged or monitored without being blocked, allowing administrators to observe user behavior without immediate enforcement.
This profile-based architecture allows web filtering rules to be reused across multiple policies, ensuring consistency in enforcement while reducing administrative overhead.
Traffic Inspection Flow in Web Filtering Operations
Understanding how FortiGate processes web traffic is essential for effective configuration. When a user attempts to access a website, the request first enters the firewall’s inspection pipeline. At this stage, basic policy checks are performed, including source and destination validation, service matching, and routing decisions.
If the traffic matches a policy with web filtering enabled, it is forwarded to the web filtering engine. Here, the URL is extracted and analyzed against predefined rules and external intelligence sources. The system checks whether the domain or URL path matches any block or allow rules configured in the profile.
In addition to static rule matching, FortiGate also performs dynamic classification. This involves evaluating the website’s category, reputation score, and potential threat indicators. For example, newly registered domains or sites with suspicious behavior patterns may be flagged even if they are not explicitly listed in blocklists.
After evaluation, the firewall enforces the decision in real time. If access is denied, the session is terminated immediately. If allowed, the traffic is forwarded to its destination. If logging is enabled, the event is recorded for further analysis and reporting.
This multi-layered inspection process ensures that web filtering is not limited to simple rule matching but incorporates real-time intelligence and behavioral analysis.
Importance of Category-Based Filtering in Modern Deployments
Category-based filtering is one of the most powerful features of FortiGate web filtering. Instead of managing individual URLs, administrators can control access based on predefined categories such as social media, gaming, streaming media, news, or malicious websites.
Each website is continuously classified by FortiGate’s threat intelligence system, which assigns category labels based on content type and behavior. This allows organizations to implement broad security policies without needing to manually maintain extensive blocklists.
For example, an organization may choose to block all social media platforms during working hours while allowing access to productivity-related websites. Similarly, categories associated with known malicious activity can be blocked globally to reduce security risk.
This approach simplifies policy management while maintaining strong security coverage across a wide range of web content types.
URL Filtering and Control Mechanisms
In addition to category-based filtering, FortiGate supports direct URL filtering. This allows administrators to explicitly allow or block specific domains or URLs. URL filtering can be configured using exact matches or wildcard patterns, enabling flexible control over web access.
For example, an administrator may block an entire domain or only specific subpaths within a website. Wildcard patterns allow broader control, such as blocking all subdomains under a given domain name.
URL filtering is often used in combination with category filtering to provide layered control. While categories handle broad classification, URL filtering allows fine-grained exceptions or restrictions.
Role of Reputation-Based Filtering in Threat Prevention
Modern FortiGate web filtering also incorporates reputation-based analysis. Websites are assigned reputation scores based on historical behavior, threat reports, and traffic patterns. Sites with poor reputation scores may be automatically blocked or flagged, even if they are not explicitly listed in any category or blocklist.
This mechanism is particularly effective against newly emerging threats, including phishing sites and malware distribution domains. Since these sites may not yet be categorized, reputation scoring provides an additional layer of proactive defense.
Reputation-based filtering ensures that security decisions are not solely dependent on static databases but are also informed by real-time threat intelligence.
Integration of Web Filtering into Firewall Policy Framework
Web filtering does not function independently within FortiGate; it must be integrated into firewall policies to become active. A firewall policy defines the conditions under which traffic is evaluated, including source networks, destination networks, and allowed services.
When a web filtering profile is attached to a policy, all matching traffic is subjected to filtering rules defined in that profile. This integration ensures that web filtering is consistently applied across all relevant network segments.
The policy framework also allows segmentation of web filtering rules based on user groups, departments, or network zones. This enables granular control, where different user groups may have different levels of internet access based on organizational requirements.
Foundational Importance of Web Filtering in Security Strategy
Web filtering serves as a foundational component of a comprehensive network security strategy. It reduces exposure to malicious content, enforces acceptable use policies, and helps optimize network performance by limiting non-essential traffic.
Beyond security, it also contributes to regulatory compliance by ensuring that organizations can control access to restricted or sensitive content categories. In environments where data protection and governance are critical, web filtering provides an essential enforcement layer.
The effectiveness of web filtering depends on proper configuration, correct NGFW mode selection, and consistent policy integration. These foundational elements establish the groundwork for more advanced filtering techniques and enterprise-level security enforcement.
Building the Foundation of Web Filtering Through Security Profiles
Web filtering in a FortiGate firewall becomes operational only when a properly structured web filtering profile is created and applied. These profiles function as modular security containers that define how web traffic should be inspected, categorized, and controlled. Unlike static filtering systems that rely solely on blocklists, FortiGate profiles integrate multiple inspection layers, allowing administrators to enforce granular and adaptive internet access policies.
A web filtering profile acts as the decision engine for HTTP and HTTPS traffic. When a user initiates a request, the firewall references the active profile associated with the relevant policy. The profile determines whether the request is permitted based on predefined rules, category classifications, reputation scores, and URL-specific conditions. This modular approach allows consistent enforcement across multiple firewall rules without duplicating configuration logic.
Before creating a profile, it is essential to ensure that the firewall is operating in a mode that supports security profiles. Profile-based NGFW mode is typically required, as it separates policy logic from security enforcement mechanisms, enabling reusable configuration structures.
Structuring a Web Filtering Profile in a Controlled Security Framework
A well-designed web filtering profile is structured around multiple layers of control. These layers typically include category-based filtering, URL filtering rules, reputation filtering, and content inspection parameters. Each layer contributes to the final decision-making process when evaluating web traffic.
Category-based filtering forms the first and most commonly used layer. Websites are grouped into predefined categories such as social networking, streaming media, news, business tools, and potentially malicious domains. These categories are maintained through continuously updated threat intelligence databases. Administrators can define actions for each category, such as allow, block, or monitor.
The second layer, URL filtering, allows more precise control. Instead of relying on broad categories, administrators can define specific domains or URLs that should be explicitly allowed or denied. This is useful for enforcing exceptions or blocking known unwanted sites that may not fall into broader categories.
The third layer involves reputation-based filtering. Each website is assigned a reputation score based on historical behavior, threat intelligence reports, and observed activity patterns. Sites with low reputation scores may be blocked automatically, even if they are not explicitly categorized as malicious.
The fourth layer includes advanced inspection features such as keyword filtering and content-based analysis. These mechanisms allow the firewall to identify and restrict specific patterns within web traffic, adding another dimension of control beyond domain-level filtering.
Together, these layers form a comprehensive inspection framework that ensures web filtering is both flexible and robust.
Creating a Web Filtering Profile in FortiGate Environment
When creating a web filtering profile, the first step is defining its scope and purpose. Administrators typically design profiles based on user groups, departments, or security zones. For example, a corporate environment may require different profiles for general employees, IT administrators, and guest users.
Each profile begins with a base configuration where category filtering rules are defined. Administrators assign actions to different categories based on organizational policy. For instance, social media categories may be restricted during working hours, while business-related tools remain accessible.
Once category rules are established, URL filtering rules are added. These rules allow specific control over individual domains or URL patterns. This layer is often used to override category-based decisions, either to allow access to a blocked category resource or to restrict a specific site within an allowed category.
Reputation filtering is then configured to provide an additional security layer. This ensures that even uncategorized or newly registered domains are evaluated based on their risk profile. High-risk domains are automatically blocked or flagged for monitoring.
After defining these components, logging and monitoring settings are configured. Logging ensures that all web filtering decisions are recorded for analysis, auditing, and security reporting. Monitoring mode may be used in early deployment phases to observe traffic behavior before enforcing strict blocking rules.
Understanding Category-Based Filtering Logic
Category-based filtering is one of the most powerful mechanisms within FortiGate web filtering. It eliminates the need to manually manage large lists of websites by grouping them into logical classifications. These classifications are maintained in global threat intelligence databases that are continuously updated.
Each website is assigned one or more categories based on its content, behavior, and purpose. For example, a video streaming platform may fall under both entertainment and bandwidth-intensive categories. A social networking site may be classified under communication and social interaction.
Administrators can define specific actions for each category. These actions typically include allow, block, or monitor. Allow permits unrestricted access, block prevents access entirely, and monitor allows access while logging activity for review.
This classification-based approach significantly reduces administrative overhead while maintaining strong security enforcement. It also allows organizations to implement policy-driven internet usage rules that align with business requirements.
URL Filtering Mechanisms and Rule Hierarchy
URL filtering provides a more granular level of control compared to category-based filtering. It allows administrators to define explicit rules for individual domains or URL patterns. These rules can override category-based decisions depending on the configuration hierarchy.
URL filtering supports both exact matching and wildcard-based matching. Exact matching applies rules to specific domains or URLs, while wildcard matching allows broader control over multiple subdomains or URL structures.
The rule hierarchy in FortiGate web filtering ensures that more specific rules take precedence over general ones. For example, a specific URL block rule may override an allow action defined at the category level. This hierarchical structure ensures predictable and consistent enforcement behavior.
URL filtering is often used to address exceptions, such as allowing access to a specific resource within a blocked category or blocking a known malicious site that has not yet been categorized.
Reputation-Based Filtering and Threat Intelligence Integration
Reputation-based filtering enhances web security by evaluating websites based on their historical behavior and risk indicators. Each domain is assigned a reputation score derived from global threat intelligence feeds and observed network activity.
Websites with poor reputation scores may exhibit characteristics such as hosting malware, participating in phishing campaigns, or displaying suspicious behavior patterns. These sites are automatically flagged or blocked based on configured thresholds.
This dynamic evaluation system is particularly important for detecting emerging threats. Since new malicious websites may not yet be categorized, reputation scoring provides a proactive defense mechanism that does not rely solely on static databases.
Reputation filtering works in conjunction with category and URL filtering, creating a multi-layered defense system that adapts to evolving threat landscapes.
Content Inspection and Application Awareness in Web Filtering
Modern FortiGate web filtering extends beyond simple domain-based control by incorporating content inspection and application awareness. This allows the firewall to analyze the actual content of web sessions and identify embedded threats or unauthorized applications.
Content inspection can detect specific keywords, file types, or patterns within web traffic. This is particularly useful for identifying sensitive data transfers or attempts to bypass standard filtering mechanisms.
Application awareness enables the firewall to recognize web-based applications regardless of the underlying URL structure. Many modern applications use dynamic domains or encrypted connections, making traditional URL filtering less effective. Application-level detection ensures that these services are still identified and controlled.
By combining content inspection with application awareness, FortiGate provides a deeper level of visibility into web traffic behavior.
Policy Association and Enforcement Mechanism
Once a web filtering profile is created, it must be associated with a firewall policy to become active. Firewall policies define the conditions under which traffic is processed, including source networks, destination networks, and service types.
When a policy includes a web filtering profile, all matching traffic is subjected to the rules defined within that profile. This ensures that web filtering is consistently enforced across all relevant sessions.
Policy association also allows segmentation of internet access rules based on organizational structure. Different departments or user groups can be assigned different policies, each with its own web filtering profile. This enables tailored access control based on business requirements.
Traffic Evaluation Process in Web Filtering Execution
When a user initiates a web request, the firewall processes the traffic through multiple inspection stages. First, basic policy matching is performed to determine whether the traffic is permitted to pass through the firewall.
If the traffic matches a policy with web filtering enabled, the request is forwarded to the web filtering engine. The URL is extracted and analyzed against category databases, URL rules, and reputation scores.
The firewall then applies the configured actions based on profile settings. If the request is allowed, the connection proceeds. If blocked, the session is terminated. If monitored, the event is logged without interrupting traffic flow.
This structured evaluation process ensures consistent enforcement and accurate decision-making across all web traffic.
Logging, Monitoring, and Analytical Visibility
Logging plays a crucial role in web filtering operations. Every decision made by the filtering engine can be recorded for analysis and auditing purposes. Logs typically include information such as source user, destination URL, category, action taken, and timestamp.
Monitoring capabilities allow administrators to observe web usage patterns over time. This helps identify trends such as excessive bandwidth consumption, unauthorized access attempts, or emerging security threats.
Analytical visibility provided by logging and monitoring supports long-term optimization of web filtering policies. Administrators can adjust rules based on observed behavior, ensuring that security controls remain aligned with operational needs.
Balancing Security Control and Network Performance
While web filtering enhances security, it also introduces processing overhead due to deep inspection and real-time analysis. Proper configuration is required to balance security enforcement with network performance.
Performance optimization may involve enabling hardware acceleration features, fine-tuning SSL inspection policies, and carefully selecting filtering categories. Overly aggressive filtering can impact user experience, while insufficient filtering can expose the network to risk.
A balanced approach ensures that security controls remain effective without degrading network efficiency.
Strategic Importance of Structured Web Filtering Deployment
A well-structured web filtering configuration provides more than just access control. It establishes a controlled internet usage framework that supports security, compliance, and operational efficiency.
By combining profiles, policies, categories, and reputation systems, FortiGate enables a layered defense model that adapts to evolving threats. This structured approach ensures that web filtering remains scalable, maintainable, and aligned with enterprise security objectives.
Scaling Web Filtering for Enterprise Network Environments
In large-scale network environments, web filtering is not simply a standalone configuration task but a structured security architecture that must integrate seamlessly with broader firewall policies, user identity systems, and traffic segmentation strategies. FortiGate web filtering becomes significantly more powerful when deployed as part of an enterprise-grade security framework where multiple policies, profiles, and enforcement layers interact dynamically.
At scale, web filtering must account for thousands of users, diverse departments, remote endpoints, and hybrid connectivity models. This requires a design approach where security profiles are standardized, reusable, and consistently applied across multiple policy boundaries. The goal is to ensure uniform enforcement while still allowing flexibility for departmental requirements.
Enterprise deployment also introduces the need for centralized policy governance. Rather than configuring isolated filtering rules per firewall instance, administrators typically design structured policy hierarchies where web filtering rules are inherited, reused, and modified based on organizational segmentation.
Identity-Aware Web Filtering and User-Based Enforcement
Modern FortiGate deployments extend web filtering beyond IP-based enforcement by integrating identity-aware controls. This means that filtering decisions are no longer solely dependent on network addresses but can also be based on authenticated user identities, group memberships, or directory services.
When identity-based policies are enabled, the firewall maps network sessions to specific users. This allows web filtering profiles to be applied dynamically based on who is accessing the network rather than where the traffic originates. For example, employees in an administrative group may have broader internet access compared to general users, while guest users may be restricted to limited categories.
This identity-driven model significantly enhances control granularity. It ensures that security policies align with organizational roles and access privileges. It also reduces the need for static IP-based rule assignment, which becomes difficult to maintain in dynamic environments with mobile devices and remote access.
Advanced Policy Hierarchies and Rule Precedence Logic
In complex deployments, multiple web filtering policies may exist simultaneously. FortiGate resolves conflicts using a structured rule precedence model. Policies are evaluated based on order, specificity, and matching conditions such as source interface, destination, and user identity.
More specific policies typically take precedence over general ones. For example, a policy targeting a specific department will override a broader organizational policy. This hierarchy ensures predictable enforcement behavior even in large environments with overlapping rules.
Web filtering profiles attached to these policies inherit this hierarchy. However, within a single profile, internal rule precedence also applies. Category-based rules, URL-specific rules, and reputation-based rules are evaluated in a defined order to ensure consistent decision-making.
This layered hierarchy is essential for maintaining control in environments where multiple security requirements coexist.
Deep Inspection and SSL Traffic Visibility in Web Filtering
A significant portion of modern web traffic is encrypted using HTTPS, which presents challenges for traditional filtering systems. Without visibility into encrypted sessions, malicious or restricted content may bypass filtering controls entirely.
FortiGate addresses this challenge through SSL inspection mechanisms. When enabled, the firewall decrypts HTTPS traffic, inspects its content, applies filtering rules, and then re-encrypts the session before forwarding it to the destination.
This process enables full visibility into URLs, content, and application behavior within encrypted sessions. It allows web filtering profiles to evaluate traffic with the same level of detail as unencrypted HTTP traffic.
However, SSL inspection must be carefully managed. It introduces computational overhead and may raise privacy considerations depending on organizational policies. In enterprise environments, selective inspection strategies are often used, where only high-risk categories or unknown domains are decrypted for analysis.
Advanced Category Management and Custom Classification Rules
While default web categories provide broad classification coverage, enterprise environments often require customization. FortiGate allows administrators to create custom categories or modify existing classification rules to align with organizational policies.
Custom categories can group specific domains under internal classifications such as “internal tools,” “approved cloud services,” or “restricted external platforms.” This enables more precise policy enforcement that reflects business requirements rather than generic global categorization models.
Custom classification also allows organizations to override default category assignments when necessary. For example, a website incorrectly categorized by global intelligence feeds can be reclassified locally to ensure accurate policy enforcement.
This flexibility is critical in environments where security policies must align closely with operational workflows.
Integration of Web Filtering with Application Control Systems
Web filtering does not operate in isolation within FortiGate architecture. It is often combined with application control systems that identify and regulate application-level traffic regardless of the underlying protocol or port.
Many modern applications operate over standard web ports, making them difficult to distinguish using traditional filtering methods. Application control solves this problem by analyzing traffic behavior patterns, signatures, and metadata.
When integrated with web filtering, application control provides an additional enforcement layer. For example, even if a website is allowed under web filtering rules, specific applications within that site may still be restricted based on organizational policy.
This layered approach ensures that both content access and application behavior are regulated simultaneously, improving overall security posture.
Traffic Logging, Forensic Analysis, and Security Intelligence
Logging is a critical component of web filtering in enterprise environments. Every filtering decision generates detailed log entries that include information such as user identity, source IP, destination URL, category, action taken, and timestamp.
These logs serve multiple purposes. From a security perspective, they provide forensic visibility into user activity and potential threats. From an operational perspective, they help identify bandwidth usage patterns, policy violations, and application trends.
In advanced deployments, logs are often integrated into centralized security information and event management systems. This enables correlation of web filtering data with other security events, such as intrusion detection alerts or endpoint security logs.
Over time, log analysis becomes a key input for refining web filtering policies. Administrators can identify unnecessary restrictions, emerging threats, or changes in user behavior and adjust configurations accordingly.
Bandwidth Optimization Through Web Filtering Controls
Beyond security enforcement, web filtering plays an important role in optimizing network performance. By restricting access to high-bandwidth categories such as video streaming, file sharing, or non-business-related media, organizations can ensure that critical applications receive sufficient network resources.
Bandwidth optimization is particularly important in environments with limited internet capacity or high user density. Without proper filtering, non-essential traffic can consume significant portions of available bandwidth, leading to performance degradation for business-critical applications.
Web filtering allows administrators to enforce usage policies that align network consumption with organizational priorities. This ensures that essential services remain responsive even during peak usage periods.
Managing Exceptions and Policy Flexibility in Filtering Rules
In real-world deployments, strict filtering rules often require exceptions to accommodate business needs. FortiGate supports exception handling within web filtering profiles, allowing specific domains or users to bypass general restrictions under controlled conditions.
Exception rules must be carefully structured to avoid undermining the overall security posture. They are typically limited in scope and tied to specific user groups or trusted domains.
This flexibility ensures that security controls do not interfere with legitimate business operations while still maintaining strong protective boundaries.
Cloud Integration and Threat Intelligence Synchronization
FortiGate web filtering relies heavily on continuously updated threat intelligence sources. These sources provide real-time information about malicious domains, emerging threats, and changes in website categorization.
Cloud integration ensures that filtering decisions are based on the most current data available. This dynamic update model allows the firewall to respond quickly to new threats without requiring manual intervention.
Threat intelligence synchronization also enhances reputation-based filtering systems. As new malicious domains are identified globally, they are quickly incorporated into filtering databases, reducing exposure time for potential threats.
This continuous update mechanism is essential in modern cybersecurity environments where threats evolve rapidly.
Performance Considerations in Large-Scale Filtering Deployments
As web filtering workloads increase, performance optimization becomes a critical consideration. Deep packet inspection, SSL decryption, and real-time classification all require significant processing resources.
To maintain performance, FortiGate devices may utilize hardware acceleration, optimized inspection engines, and traffic prioritization mechanisms. Administrators must also carefully design filtering policies to avoid unnecessary inspection overhead.
For example, excluding trusted internal domains from deep inspection can reduce processing load without compromising security. Similarly, limiting SSL inspection to high-risk categories can improve efficiency while maintaining visibility where it matters most.
Balancing performance and security is a key aspect of enterprise-grade web filtering design.
High Availability and Redundancy in Web Filtering Systems
In mission-critical environments, web filtering must be highly available to prevent disruptions in internet access or security enforcement. FortiGate supports high availability configurations where multiple devices operate in synchronized clusters.
In such setups, web filtering configurations are automatically replicated across devices, ensuring consistent policy enforcement even in failover scenarios. If one device fails, another immediately takes over without interrupting filtering operations.
This redundancy ensures continuous protection and minimizes downtime in enterprise networks.
Long-Term Evolution of Web Filtering in Modern Networks
Web filtering has evolved from simple URL blocking systems into sophisticated, intelligence-driven security frameworks. Modern implementations combine category classification, behavioral analysis, reputation scoring, and application awareness into a unified enforcement engine.
As networks continue to evolve toward cloud-based architectures and remote work models, web filtering will increasingly rely on identity-based controls, AI-driven threat detection, and cloud-integrated intelligence systems.
FortiGate web filtering represents this evolution by providing a flexible, scalable, and deeply integrated approach to controlling web access in complex environments.
Conclusion
Web filtering within a FortiGate firewall represents far more than a simple mechanism for blocking or allowing websites. It functions as a strategic enforcement layer that shapes how users interact with the internet, how bandwidth is consumed, and how organizational security policies are upheld across increasingly complex digital environments. When viewed holistically, it becomes clear that web filtering is not an isolated feature but an integrated component of a broader next-generation firewall architecture designed to handle modern threats, encrypted traffic, and dynamic application behavior.
At its core, FortiGate web filtering delivers structured control over internet access through layered inspection methods. These methods combine category-based filtering, URL-level rules, reputation analysis, and application-aware inspection into a unified decision-making engine. This layered approach ensures that no single point of control is responsible for enforcement, reducing blind spots and improving overall accuracy in traffic evaluation. Each layer contributes a different perspective on the same traffic flow, resulting in a more complete security posture.
One of the most significant strengths of FortiGate web filtering lies in its adaptability. Traditional filtering systems often rely on static blacklists or manually maintained rule sets, which quickly become outdated in fast-changing network environments. In contrast, FortiGate leverages continuously updated threat intelligence databases and dynamic classification systems that evolve alongside emerging web technologies and attack patterns. This ensures that newly created malicious domains, phishing sites, and suspicious platforms can be identified and controlled without requiring manual intervention from administrators.
Equally important is the role of web filtering in enforcing organizational policy. In modern enterprises, internet usage is not only a technical concern but also a governance and productivity issue. Employees require access to a wide range of online resources to perform their tasks effectively, yet unrestricted access can introduce risks related to security breaches, data leakage, and productivity loss. Web filtering bridges this gap by allowing organizations to define clear boundaries around acceptable internet usage while still preserving access to essential tools and services.
Another critical dimension of FortiGate web filtering is its contribution to bandwidth management. As digital consumption increases, especially with the rise of streaming services, cloud applications, and collaborative tools, network congestion becomes a real operational challenge. By selectively restricting high-bandwidth or non-essential categories, web filtering helps ensure that critical business applications receive the necessary network resources to function efficiently. This not only improves performance but also enhances user experience across the organization.
From a security standpoint, web filtering plays a vital role in reducing exposure to external threats. Many cyberattacks begin with simple web interactions, such as visiting a compromised website or clicking a malicious link. By proactively blocking access to known malicious domains and suspicious categories, FortiGate significantly reduces the attack surface available to threat actors. When combined with reputation-based filtering and real-time intelligence updates, this protection becomes even more effective against emerging threats that have not yet been widely documented.
The integration of identity-aware controls further enhances the precision of web filtering enforcement. Instead of relying solely on IP addresses or network segments, FortiGate can apply policies based on authenticated user identities and group memberships. This allows organizations to implement differentiated access controls, ensuring that security policies align with user roles and responsibilities. For example, administrative personnel may require broader access to web resources compared to standard users or guest accounts. This identity-driven approach brings web filtering closer to business logic, making it more aligned with real-world organizational structures.
SSL inspection also plays a transformative role in the effectiveness of modern web filtering. As encrypted traffic becomes the dominant form of internet communication, visibility into HTTPS sessions is essential for meaningful security enforcement. FortiGate’s ability to decrypt, inspect, and re-encrypt traffic allows it to apply filtering rules even within encrypted sessions. While this introduces considerations around performance and privacy, it is increasingly necessary in environments where encrypted threats are common.
Operationally, the logging and monitoring capabilities of FortiGate web filtering provide significant long-term value. Every decision made by the filtering engine generates detailed records that can be used for forensic analysis, compliance reporting, and behavioral insights. Over time, this data becomes a valuable resource for understanding how users interact with the internet, identifying potential security gaps, and refining policy configurations. In mature deployments, these insights are often integrated into centralized security monitoring systems, enabling correlation with other network and endpoint security data.
Scalability is another defining characteristic of FortiGate web filtering. In small environments, configuration may be relatively straightforward, but in enterprise-scale deployments, the system must support thousands of users, multiple network segments, and diverse access requirements. The profile-based architecture of FortiGate allows administrators to build reusable configurations that can be consistently applied across multiple policies. This ensures uniform enforcement while reducing administrative complexity and minimizing configuration errors.
Despite its technical complexity, the underlying objective of web filtering remains straightforward: to provide controlled, secure, and efficient access to web resources. However, achieving this objective in modern networks requires a sophisticated combination of technologies working in coordination. FortiGate achieves this through its integration of deep packet inspection, threat intelligence feeds, behavioral analysis, and policy-driven enforcement mechanisms.
Looking at the broader security landscape, web filtering continues to evolve in response to changing threats and usage patterns. The increasing adoption of cloud services, remote work environments, and mobile connectivity has expanded the boundaries of traditional network perimeters. In this context, web filtering is no longer limited to on-premises traffic control but is becoming part of a distributed security model that extends across hybrid infrastructures.
In summary, FortiGate web filtering serves as a critical control point in modern cybersecurity architecture. It combines visibility, intelligence, and policy enforcement into a unified system capable of addressing both security risks and operational requirements. Its layered design, identity integration, and adaptive intelligence make it a powerful tool for managing internet access in complex environments. As networks continue to evolve, web filtering will remain a foundational element in maintaining secure, efficient, and policy-compliant digital ecosystems.