Choosing a career path in cybersecurity requires a structured understanding of how modern digital systems operate and how security roles help protect them. The field is not limited to a single job function but instead includes a wide range of responsibilities that support the confidentiality, integrity, and availability of information. Individuals entering this field must evaluate their technical interests, analytical strengths, and long-term career expectations to identify the most suitable direction. Cybersecurity continues to evolve alongside emerging technologies such as cloud computing, artificial intelligence, and interconnected devices, making it a continuously expanding profession with long-term relevance.
A career in this domain is built on adaptability and continuous learning. Unlike traditional fields with static job descriptions, cybersecurity roles shift as threats evolve. This dynamic environment requires professionals who are comfortable working in fast-changing conditions while maintaining attention to detail and structured problem-solving abilities. Understanding the landscape before selecting a specialization is essential for long-term success.
The Expanding Role of Cybersecurity in the Digital Era
Modern society relies heavily on digital infrastructure for communication, business operations, financial transactions, healthcare systems, and government services. This reliance has significantly increased the importance of cybersecurity as a foundational requirement for operational stability. Every connected system introduces potential vulnerabilities that can be exploited by malicious actors seeking financial gain, data theft, or disruption.
As organizations adopt more complex technologies, their exposure to cyber risks also increases. Cloud platforms, remote access systems, and mobile integrations create new entry points that require advanced security measures. Cybersecurity professionals are responsible for identifying these risks and implementing strategies to reduce the likelihood of successful attacks. This includes monitoring systems, securing access points, and ensuring that digital environments remain resilient against potential threats.
Rising Cyber Threats and Organizational Risk Exposure
Cyber threats have become more sophisticated, frequent, and damaging over time. Attackers now use advanced techniques that combine automation, social engineering, and system exploitation to bypass traditional defenses. These threats are not limited to large organizations; small businesses and individual users are also frequently targeted due to weaker security infrastructures.
The consequences of cyber incidents can be severe, including financial loss, reputational damage, operational disruption, and compromised personal data. In critical sectors such as healthcare and finance, security breaches can also have real-world consequences beyond digital systems. This increasing level of risk has elevated cybersecurity from a technical function to a strategic organizational priority.
Organizations now invest heavily in security frameworks designed to detect, prevent, and respond to threats in real time. This growing investment directly contributes to the demand for skilled professionals who can manage and secure increasingly complex digital environments.
Global Demand and Workforce Shortage in Cybersecurity
One of the defining characteristics of the cybersecurity industry is the persistent shortage of qualified professionals. The demand for skilled workers far exceeds the available supply, creating a global skills gap that continues to widen as digital adoption accelerates. Organizations across industries struggle to fill security-related positions, resulting in increased opportunities for new entrants.
This shortage is driven by multiple factors, including the rapid pace of technological change and the complexity of modern security systems. Traditional education systems often struggle to keep up with the evolving requirements of the industry, leading to a gap between theoretical knowledge and practical skills needed in real-world environments.
For individuals entering the workforce, this gap presents a significant opportunity. Cybersecurity offers multiple entry points, allowing individuals from diverse technical backgrounds to transition into the field. The demand spans across entry-level monitoring roles to advanced architectural and strategic positions.
Career Stability and Long-Term Security Prospects
A key advantage of cybersecurity as a career path is its long-term stability. As long as digital systems exist, security professionals will be required to protect them. This creates a consistent demand for expertise regardless of economic fluctuations or industry changes. Unlike many traditional roles that may be affected by automation or outsourcing, cybersecurity remains essential due to the complexity and unpredictability of cyber threats.
Organizations cannot eliminate the need for security professionals, as threats continuously evolve and adapt. This ensures ongoing relevance for individuals working in the field. Career stability in cybersecurity is also reinforced by the increasing regulatory requirements imposed on organizations, which mandate strict security controls and compliance measures.
As a result, cybersecurity professionals often experience sustained career growth and long-term employment opportunities, particularly as they gain experience and specialize in specific domains.
Financial Growth and Professional Advancement
Cybersecurity careers are widely recognized for offering strong financial potential. Compensation levels are generally higher than those of many other IT roles due to the specialized nature of the work and the critical importance of security within organizations. Entry-level positions typically provide competitive salaries, while experienced professionals in specialized roles can achieve significantly higher earnings.
As professionals gain expertise, their value within organizations increases, leading to opportunities for advancement into senior technical, architectural, or leadership positions. Career progression is often based on skill development, practical experience, and the ability to manage increasingly complex security challenges.
Financial growth in cybersecurity is closely tied to specialization. Professionals who develop deep expertise in high-demand areas such as cloud protection, threat intelligence, or incident management often experience faster career advancement and higher compensation levels.
Core Structure of Cybersecurity Career Domains
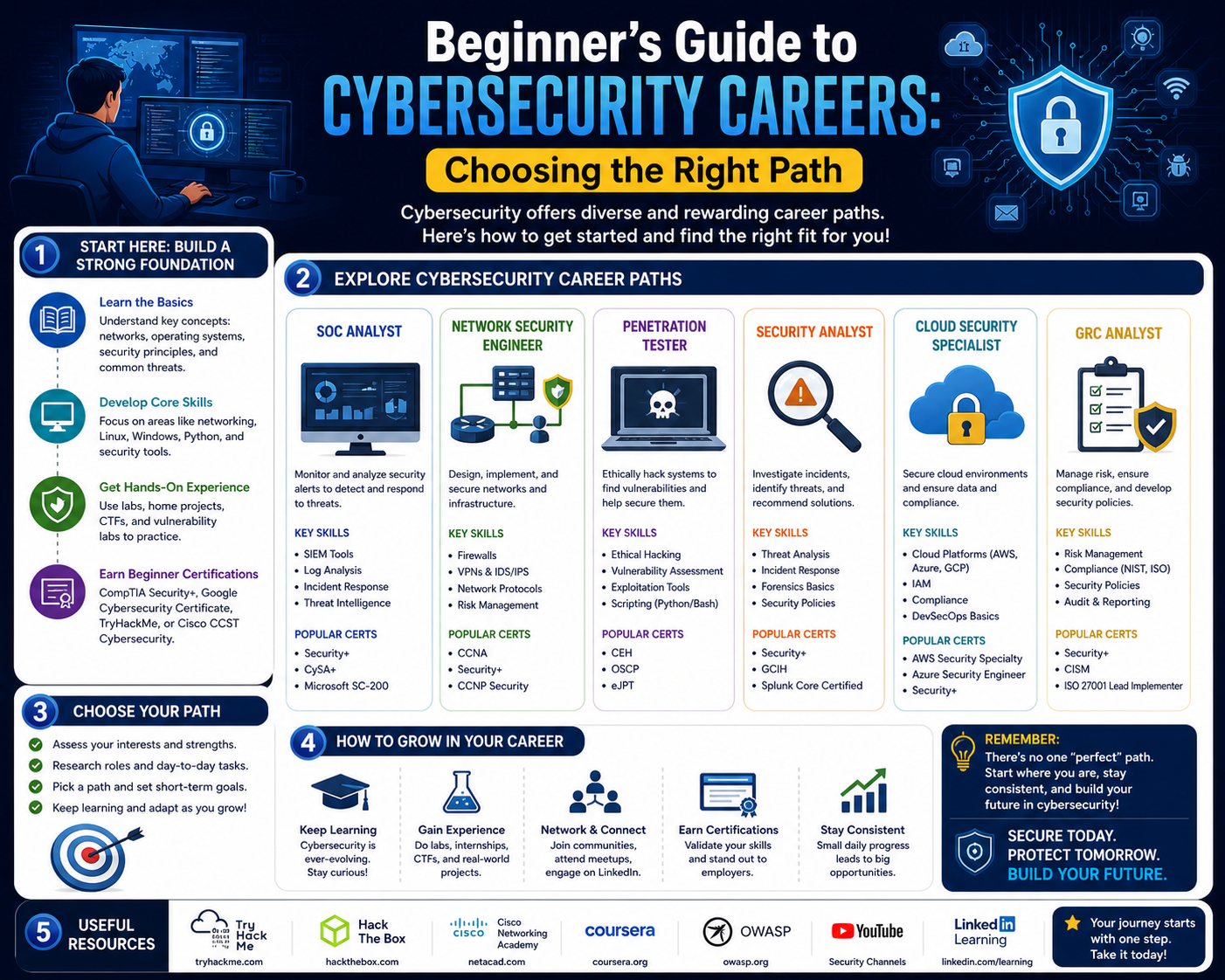
Cybersecurity is composed of multiple interconnected domains, each focusing on different aspects of security management. These domains can generally be categorized into offensive security, defensive operations, engineering and architecture, cloud security, and incident response.
Offensive security focuses on identifying vulnerabilities through controlled testing and simulation of attacks. Defensive operations involve monitoring systems and responding to threats in real time. Engineering and architecture roles focus on designing secure systems and integrating security into infrastructure. Cloud security specializes in protecting distributed cloud environments, while incident response focuses on investigating and mitigating active security breaches.
Understanding these domains helps individuals identify which area aligns most closely with their interests and strengths. Each domain requires a different mindset, skill set, and approach to problem-solving.
Offensive Security and Ethical Attack Simulation
Offensive security represents one of the most technically challenging areas in cybersecurity. Professionals in this domain simulate cyberattacks to identify weaknesses in systems before malicious actors can exploit them. This proactive approach helps organizations strengthen their defenses by uncovering vulnerabilities through controlled testing.
Individuals working in offensive security must understand how attackers operate, including their techniques, tools, and methodologies. This requires strong knowledge of networking systems, operating environments, and application structures. Creativity and analytical thinking are essential, as professionals must identify unconventional methods to bypass security controls.
The results of offensive security assessments are used to improve system defenses, patch vulnerabilities, and enhance overall security posture. This role is highly valued because it directly contributes to preventing real-world cyber incidents.
Defensive Monitoring and Security Operations
Defensive cybersecurity roles focus on monitoring systems for unusual activity and responding to potential threats. Professionals in this area analyze system logs, detect anomalies, and investigate alerts generated by security tools. Their primary objective is to identify and mitigate threats before they escalate into serious incidents.
This role requires strong analytical skills and the ability to interpret large volumes of data. Security environments often generate continuous streams of information, making it essential to distinguish between normal behavior and potential threats. Quick decision-making is also important, particularly during active security incidents.
Defensive professionals often work within structured environments where they follow established procedures for incident detection and response. Their work ensures continuous protection of organizational systems and helps maintain operational stability.
Security Engineering and Infrastructure Protection
Security engineering focuses on designing and implementing secure systems at the infrastructure level. Professionals in this domain ensure that security is integrated into networks, applications, and systems from the ground up. This includes configuring protective mechanisms, managing secure access, and maintaining system integrity.
Security engineers must understand how systems interact across different environments, including internal networks and external connections. Their work involves creating resilient architectures that can withstand attacks and minimize potential damage.
This role requires a combination of technical expertise and system design knowledge. Engineers often collaborate with other IT teams to ensure that security requirements are incorporated into all stages of system development and deployment.
Cloud Security and Distributed System Protection
As organizations increasingly adopt cloud-based systems, cloud security has become a critical specialization within cybersecurity. Cloud environments introduce unique challenges due to their distributed nature and shared infrastructure models. Security professionals in this area are responsible for ensuring that data, applications, and services hosted in the cloud remain protected.
Cloud security involves managing identity access, securing data storage, and monitoring cloud activity for suspicious behavior. Professionals must understand how cloud systems operate and how security responsibilities are shared between service providers and organizations.
The growing reliance on cloud computing has made this specialization one of the fastest-growing areas within cybersecurity, with increasing demand for professionals who understand cloud architecture and security principles.
Incident Response and Digital Forensics
Incident response focuses on managing active security breaches and minimizing their impact. When a cyber incident occurs, professionals in this field are responsible for identifying the source of the attack, containing the damage, and restoring affected systems.
Digital forensics involves analyzing compromised systems to understand how an attack occurred and what data was affected. This requires a detailed examination of system logs, files, and network activity. Findings from forensic investigations are often used to improve future security measures and support compliance requirements.
Professionals in this domain must work methodically and accurately, as their findings can have significant operational and legal implications.
Expanding the Cybersecurity Career Landscape
The cybersecurity career ecosystem extends far beyond a few well-known job titles. As organizations scale their digital infrastructure across hybrid environments, cloud platforms, and interconnected networks, the security workforce has evolved into a highly specialized structure. Each specialization serves a distinct purpose in defending systems against increasingly complex threats. Understanding these roles in depth is essential for making an informed career decision, especially for individuals transitioning into cybersecurity from other IT domains or beginning their professional journey.
Modern cybersecurity is no longer a single defensive layer but a multi-dimensional framework that integrates prevention, detection, response, and recovery. This layered approach requires professionals with different mindsets and technical capabilities working together. Some focus on proactive exploitation of vulnerabilities, while others specialize in continuous monitoring or strategic governance. This diversity creates multiple entry points and long-term growth opportunities.
Security Analysis and Threat Monitoring Roles
Security analysts play a foundational role in cybersecurity operations. Their primary responsibility is to monitor systems, detect anomalies, and respond to security alerts generated by monitoring tools and security information systems. They operate in environments where data flows continuously, requiring constant vigilance and the ability to distinguish between normal system behavior and potential threats.
A significant part of this role involves working with security monitoring platforms that aggregate logs from servers, applications, and network devices. Analysts interpret these logs to identify suspicious activity such as unauthorized login attempts, abnormal data transfers, or unexpected system behavior. The ability to recognize patterns is critical, as many attacks are subtle and designed to evade basic detection mechanisms.
Security analysts also contribute to incident response processes by escalating confirmed threats and assisting in containment procedures. Their work ensures that threats are identified early, reducing the potential impact on organizational systems. This role is often considered an entry point into cybersecurity due to its structured processes and exposure to a wide range of security scenarios.
Skill Development Path for Security Analysts
Professionals in this area require a strong understanding of network fundamentals, operating systems, and security monitoring tools. Familiarity with how data flows across networks helps analysts identify irregular patterns more effectively. Additionally, scripting knowledge can enhance their ability to automate repetitive tasks and improve response times.
Analytical thinking is one of the most important skills in this role. Security analysts must interpret large volumes of data quickly and accurately. This includes identifying false positives, correlating multiple alerts, and prioritizing incidents based on severity. Attention to detail and consistency are essential, as even small anomalies can indicate larger security issues.
Over time, security analysts often progress into more advanced roles such as threat intelligence specialists or security operations center leads. These positions involve greater responsibility and deeper involvement in strategic security planning.
Threat Intelligence and Proactive Defense Strategies
Threat intelligence is an evolving specialization focused on understanding the behavior, motives, and techniques of cyber adversaries. Instead of reacting to attacks after they occur, threat intelligence professionals aim to anticipate and prevent them. This involves analyzing global threat trends, attacker methodologies, and emerging vulnerabilities.
Professionals in this field gather information from multiple sources, including internal system logs, external threat feeds, and historical attack data. They analyze this information to identify patterns and predict potential future attacks. This proactive approach enables organizations to strengthen defenses before threats materialize.
Threat intelligence analysts often collaborate with security operations teams to provide context for ongoing incidents. By understanding the source and nature of an attack, organizations can implement more effective mitigation strategies. This role requires strong analytical capabilities and the ability to synthesize complex information into actionable insights.
Security Engineering and System Architecture Protection
Security engineers are responsible for building and maintaining secure infrastructure environments. Their focus is on integrating security controls directly into system architecture rather than applying them as afterthoughts. This includes designing secure network configurations, implementing access control systems, and ensuring secure communication channels between applications.
Unlike analysts who focus on monitoring, security engineers focus on prevention through design. They work closely with development and infrastructure teams to ensure that systems are built with security principles in mind from the beginning. This includes applying principles such as least privilege access, segmentation, and encryption.
Security engineers must have a deep understanding of networking concepts, operating systems, and system design principles. They also need to stay updated on evolving security technologies and attack techniques to ensure that defenses remain effective against modern threats.
Role of Automation in Security Engineering
Automation plays an increasingly important role in security engineering. As systems grow in complexity, manual configuration and monitoring become less efficient. Engineers use automation tools to streamline security processes such as patch management, configuration enforcement, and system monitoring.
Automated security systems can detect and respond to threats faster than manual processes. However, designing these systems requires careful planning to avoid false positives and ensure accurate detection. Security engineers must balance automation with human oversight to maintain effective control over security environments.
This combination of automation and engineering expertise is becoming increasingly important as organizations adopt large-scale cloud and hybrid infrastructures.
Cloud Security Specialization and Modern Infrastructure Protection
Cloud computing has transformed the way organizations store, process, and manage data. Instead of relying on traditional on-premises systems, many organizations now operate in distributed environments that span multiple cloud platforms. This shift has introduced new security challenges that require specialized expertise.
Cloud security professionals are responsible for protecting data, applications, and services hosted in cloud environments. This includes managing identity and access control systems, securing data storage, and monitoring cloud activity for unusual behavior. The distributed nature of cloud systems requires a different approach compared to traditional infrastructure security.
One of the key challenges in cloud security is shared responsibility. Cloud service providers manage the underlying infrastructure, while organizations are responsible for securing their data and applications. Understanding this division of responsibility is essential for maintaining effective security controls.
Identity and Access Management in Cloud Environments
Identity and access management is a critical component of cloud security. It ensures that only authorized users can access specific resources within a system. This involves managing user identities, assigning permissions, and enforcing authentication mechanisms.
Cloud environments often involve complex access structures due to the large number of users and services interacting within the system. Misconfigured access controls can lead to significant security vulnerabilities, making this area a high priority for cloud security professionals.
Effective identity management reduces the risk of unauthorized access and helps maintain compliance with regulatory standards. It also supports operational efficiency by ensuring that users have appropriate access levels based on their roles.
Incident Response and Cyber Incident Management
Incident response is a specialized cybersecurity function focused on managing active security events. When a breach or suspicious activity is detected, incident response teams are responsible for containing the threat, minimizing damage, and restoring normal operations.
This process involves several stages, including detection, analysis, containment, eradication, and recovery. Each stage requires coordination between different teams and precise execution to ensure effective resolution.
Incident responders must work quickly under pressure while maintaining accuracy in their actions. Delayed or incorrect responses can increase the impact of a security incident. Therefore, structured procedures and predefined response plans are essential in this field.
Digital Forensics and Post-Incident Investigation
Digital forensics focuses on analyzing systems after a security incident has occurred. The goal is to determine how the breach happened, what data was affected, and how attackers gained access. This requires a detailed examination of system logs, file structures, and network activity.
Forensic analysts use specialized tools to reconstruct events leading up to and during a security incident. Their findings help organizations understand vulnerabilities and prevent similar attacks in the future. In some cases, forensic evidence is also used in legal investigations or compliance reporting.
This role requires patience, precision, and strong analytical skills. Even small pieces of digital evidence can provide critical insights into an attack.
Security Governance and Risk Management Roles
Beyond technical roles, cybersecurity also includes strategic and governance-focused positions. These professionals are responsible for defining security policies, managing organizational risk, and ensuring compliance with industry standards and regulations.
Risk management involves identifying potential threats to organizational systems and evaluating their potential impact. Based on this assessment, security leaders implement controls to reduce exposure and maintain acceptable risk levels.
Governance roles require a strong understanding of both technical systems and business objectives. Professionals in this area ensure that security strategies align with organizational goals while maintaining regulatory compliance.
Strategic Decision-Making in Cybersecurity Careers
As cybersecurity becomes more integrated into business operations, strategic decision-making has become a critical component of the field. Security leaders must balance technical requirements with business priorities, ensuring that security measures do not hinder operational efficiency.
This involves evaluating security investments, defining long-term security strategies, and coordinating across multiple departments. Strong communication skills and a broad understanding of technology and business operations are essential in these roles.
Strategic cybersecurity professionals often work in leadership positions where they influence organizational security direction and policy development.
Skill Progression and Career Advancement in Cybersecurity
Career progression in cybersecurity is typically based on skill development, experience, and specialization. Professionals often begin in entry-level roles such as monitoring or support positions before advancing into more specialized or leadership roles.
Continuous learning is essential in this field due to the constant evolution of technology and threats. Professionals must stay updated on new tools, attack techniques, and security frameworks to remain effective in their roles.
Over time, individuals may choose to specialize deeply in one area or transition into broader leadership positions that oversee entire security programs.
Interconnected Nature of Cybersecurity Roles
Although cybersecurity roles are diverse, they are highly interconnected. Security analysts rely on engineers for system configurations, incident responders depend on analysts for detection, and governance professionals depend on technical teams for accurate risk assessments.
This interdependence ensures that cybersecurity functions operate as a unified system rather than isolated roles. Understanding how these roles interact is essential for choosing a career path that aligns with both individual strengths and organizational needs.
Advanced Cybersecurity Specializations and Emerging Domains
As cybersecurity continues to evolve alongside modern technology ecosystems, new specialized domains are emerging that reflect the changing nature of digital threats. These advanced areas go beyond traditional security roles and focus on protecting complex infrastructures such as cloud-native systems, artificial intelligence-driven platforms, industrial control systems, and interconnected IoT environments. Understanding these specializations is essential for individuals who want to build long-term careers that remain relevant in a rapidly shifting technological landscape.
Cybersecurity is no longer confined to static networks or on-premises systems. The modern digital environment is highly distributed, dynamic, and data-driven. As a result, security professionals must adapt to protecting environments that change in real time. This has led to the development of advanced fields such as cloud-native security engineering, AI-based threat detection, and zero-trust architecture design. Each of these domains requires a combination of technical expertise, strategic thinking, and continuous learning.
Cloud-Native Security and Distributed Systems Protection
Cloud-native security has become one of the most critical areas in modern cybersecurity due to the widespread adoption of distributed computing models. Unlike traditional infrastructure, cloud-native environments are built using microservices, containers, and orchestration platforms that dynamically scale based on demand. While this architecture improves flexibility and performance, it also introduces new security challenges.
Security professionals working in this domain are responsible for securing containerized applications, managing orchestration platforms, and enforcing security policies across distributed systems. Identity management, workload protection, and secure communication between services are key focus areas. Because cloud-native systems are constantly changing, security must be embedded into every stage of the development lifecycle.
This specialization requires a deep understanding of both development and infrastructure concepts. Professionals must be familiar with how applications are deployed, how services communicate, and how data flows across distributed environments. Security must be integrated seamlessly without affecting system performance or scalability.
Artificial Intelligence and Machine Learning in Cybersecurity
Artificial intelligence and machine learning are increasingly being used to enhance cybersecurity capabilities. These technologies help organizations analyze large volumes of data, detect anomalies, and predict potential threats with greater accuracy and speed than traditional methods.
AI-driven security systems can identify patterns in network traffic, user behavior, and system activity that may indicate malicious intent. Machine learning models are trained on historical data to recognize deviations from normal behavior, allowing for early detection of potential threats. This proactive approach significantly improves response times and reduces the likelihood of successful attacks.
Cybersecurity professionals working in this area must understand both security principles and data science concepts. This includes knowledge of algorithms, data modeling, and statistical analysis. The integration of AI into cybersecurity is still evolving, making it one of the most innovative and rapidly developing fields in the industry.
Zero Trust Architecture and Modern Security Models
Traditional security models often rely on perimeter-based defenses, assuming that internal networks are inherently safe. However, modern cyber threats have made this approach insufficient. As a result, organizations are increasingly adopting zero trust architecture, a security model based on the principle of “never trust, always verify.”
In a zero-trust environment, every user, device, and application must be continuously authenticated and authorized before accessing resources. This approach minimizes the risk of unauthorized access, even if an attacker gains entry into the network. It also reduces the impact of compromised credentials or internal threats.
Implementing zero trust requires a combination of identity management, micro-segmentation, continuous monitoring, and strict access controls. Security professionals must design systems that enforce verification at every level, ensuring that access is granted only when necessary.
Industrial Control Systems and Critical Infrastructure Security
Industrial control systems represent another highly specialized area of cybersecurity. These systems are used to manage physical processes in industries such as energy, manufacturing, transportation, and utilities. Unlike traditional IT systems, industrial environments often interact directly with physical infrastructure, making security breaches potentially dangerous in the real world.
Securing these systems requires a deep understanding of both operational technology and cybersecurity principles. Professionals must ensure that systems remain available and reliable while protecting them from cyber threats. Downtime in these environments can have serious consequences, including safety risks and economic disruption.
Security strategies in this domain focus on segmentation, monitoring, and strict access control. Because many industrial systems were not originally designed with cybersecurity in mind, professionals often face additional challenges when implementing modern security measures.
Internet of Things Security and Connected Device Protection
The expansion of Internet of Things devices has created a new category of cybersecurity challenges. These devices are embedded in everyday environments, ranging from smart homes to industrial sensors and medical equipment. While they provide convenience and efficiency, they also increase the number of potential entry points for cyber attackers.
IoT security focuses on protecting these devices from unauthorized access, data breaches, and malicious manipulation. Many IoT devices have limited processing power and security capabilities, making them vulnerable to exploitation. Security professionals must develop lightweight and efficient protection mechanisms that can operate within these constraints.
This specialization requires knowledge of embedded systems, network communication protocols, and device-level security controls. As IoT adoption continues to grow, this field is expected to become increasingly important in the cybersecurity landscape.
Building a Cybersecurity Career Through Practical Experience
While theoretical knowledge is important, practical experience is essential for developing a successful cybersecurity career. Hands-on experience allows individuals to apply concepts in real-world scenarios, develop problem-solving skills, and gain confidence in their abilities.
Practical learning can be achieved through simulated environments, virtual labs, and personal projects. These experiences help individuals understand how attacks occur, how systems respond, and how security controls function in practice. Working with real or simulated systems provides insight that cannot be gained through theory alone.
Hands-on experience also helps individuals identify which areas of cybersecurity they are most interested in. Some may discover a passion for offensive security, while others may prefer defensive monitoring or system design.
Importance of Continuous Skill Development
Cybersecurity is a field that requires continuous learning due to the constantly evolving nature of threats and technologies. New vulnerabilities, attack techniques, and defense mechanisms are introduced regularly, making it essential for professionals to stay updated.
Skill development involves both technical and conceptual learning. Technical skills include understanding tools, systems, and programming languages, while conceptual skills involve understanding security principles, risk management, and strategic thinking.
Professionals must regularly update their knowledge to remain effective. This includes learning about emerging technologies, new security frameworks, and evolving industry standards. Continuous improvement is a core requirement for long-term success in cybersecurity.
Career Transition Strategies into Cybersecurity
Many individuals enter cybersecurity from other IT or technical backgrounds. Transitioning into the field requires a structured approach that focuses on building foundational knowledge and gradually developing specialized skills.
A common starting point is gaining a strong understanding of networking, operating systems, and security fundamentals. These concepts form the basis of most cybersecurity roles. From there, individuals can explore different specializations to determine which area aligns with their interests.
Hands-on practice is particularly important during career transitions. Working with simulated environments, participating in security challenges, and building personal projects can significantly accelerate learning and skill development.
Building a Professional Cybersecurity Portfolio
A strong portfolio is an important asset in cybersecurity careers. It demonstrates practical skills and provides evidence of hands-on experience. Unlike traditional fields where resumes may be sufficient, cybersecurity employers often value demonstrated capability over theoretical knowledge alone.
A cybersecurity portfolio may include documentation of projects, security analyses, system configurations, and problem-solving exercises. It can also include case studies of simulated attacks, vulnerability assessments, or system hardening exercises.
The purpose of a portfolio is to showcase the ability to apply knowledge in practical scenarios. It reflects initiative, curiosity, and commitment to skill development.
Networking and Professional Community Engagement
Cybersecurity is a highly collaborative field where knowledge sharing plays an important role in professional growth. Engaging with the cybersecurity community allows individuals to stay informed about emerging threats, new technologies, and industry best practices.
Professional networking also provides opportunities for mentorship and career advancement. Experienced professionals can offer guidance on skill development, career planning, and industry expectations. Participation in discussions and knowledge-sharing activities helps individuals build credibility within the field.
Community engagement can take many forms, including participation in technical discussions, contribution to security projects, or involvement in professional groups. These interactions help build connections that can support long-term career growth.
Long-Term Career Growth and Specialization Strategy
Cybersecurity careers often evolve as professionals gain experience and refine their interests. Some individuals choose to specialize deeply in a single domain, while others transition into broader leadership or architectural roles.
Long-term growth depends on continuous learning, adaptability, and strategic skill development. Professionals who remain flexible and open to new technologies are better positioned to take advantage of emerging opportunities.
Specialization allows individuals to develop deep expertise in specific areas, while generalization provides broader understanding across multiple domains. Both paths offer valuable career opportunities depending on individual goals.
Final Perspective on Cybersecurity Career Decision-Making
Choosing the right cybersecurity career path is ultimately a process of alignment between personal interests, technical skills, and long-term professional goals. The field offers a wide range of opportunities, each with its own challenges and rewards. Whether focusing on offensive security, defensive operations, cloud protection, or emerging technologies, success depends on continuous learning and practical experience.
Cybersecurity remains one of the most dynamic and impactful fields in technology, offering long-term stability and meaningful work in protecting digital ecosystems.
Conclusion
Cybersecurity as a career path represents one of the most significant intersections between technology, risk management, and real-world impact in the modern digital economy. The decision to enter this field is not simply about selecting a job role; it is about committing to a continuously evolving discipline that demands adaptability, analytical thinking, and long-term professional development. As digital systems expand across every sector of society, the responsibility of protecting those systems becomes more complex and more essential. This reality positions cybersecurity professionals as critical contributors to organizational stability and global digital safety.
One of the most important aspects to understand about cybersecurity careers is that they are not linear in nature. Unlike traditional professions where roles may remain relatively stable over time, cybersecurity evolves in response to technological innovation and emerging threats. This means that professionals must constantly reassess their skills and adjust their expertise to match current industry demands. A role that is highly relevant today may transform significantly within a few years due to advancements in cloud computing, automation, artificial intelligence, and threat intelligence systems. As a result, long-term success in this field depends heavily on the willingness to learn continuously and adapt to new challenges.
Another defining characteristic of cybersecurity careers is their interdisciplinary nature. Professionals in this field often draw knowledge from networking, software development, system administration, risk analysis, and behavioral psychology. This combination of disciplines allows cybersecurity practitioners to understand both the technical and human aspects of security threats. Many cyber incidents are not purely technical failures but are influenced by human behavior, social engineering, or organizational weaknesses. Understanding these dimensions allows professionals to build more effective defense strategies and reduce vulnerabilities across multiple layers of infrastructure.
The diversity of career paths within cybersecurity also plays a major role in its appeal. Individuals are not restricted to a single type of role but can instead choose from a wide spectrum of specializations. Some may prefer offensive security roles that involve simulating attacks and identifying vulnerabilities, while others may gravitate toward defensive positions that focus on monitoring and incident response. There are also strategic roles that involve designing security policies, managing organizational risk, and ensuring regulatory compliance. This variety ensures that individuals with different skill sets and interests can find meaningful and sustainable career paths within the same field.
As organizations continue to adopt cloud-based systems and distributed architectures, the importance of specialized security knowledge becomes even more pronounced. Cloud environments introduce new challenges related to identity management, data protection, and system visibility. Similarly, the rise of connected devices and automation technologies increases the complexity of securing digital ecosystems. Cybersecurity professionals must therefore develop a deep understanding of modern infrastructure to effectively protect it. This includes not only technical expertise but also an awareness of how systems interact across different environments.
The global demand for cybersecurity professionals further reinforces the importance of this career path. Organizations across industries are actively seeking individuals who can protect sensitive data and maintain system integrity. This demand is driven by the increasing frequency and sophistication of cyber threats, as well as the growing reliance on digital infrastructure for critical operations. The resulting skills gap creates significant opportunities for individuals entering the field, particularly those who are willing to invest time in developing practical experience and specialized knowledge.
Despite the strong demand and career opportunities, cybersecurity also presents certain challenges that must be acknowledged. The fast-paced nature of the field requires professionals to stay constantly updated with new tools, techniques, and threat landscapes. This ongoing learning process can be demanding, especially for individuals transitioning from other careers or entering the field without prior technical experience. However, this challenge also contributes to the dynamic and intellectually engaging nature of the profession, making it suitable for individuals who enjoy continuous problem-solving and intellectual growth.
Another important consideration is the need for practical experience. While theoretical knowledge provides a foundation, real-world application is essential for building competence in cybersecurity roles. Hands-on experience allows professionals to understand how systems behave under real conditions, how attacks unfold, and how defenses respond under pressure. This experiential learning is often what differentiates entry-level understanding from professional-level expertise. It also helps individuals identify which areas of cybersecurity align most closely with their strengths and interests.
Career progression in cybersecurity is typically driven by specialization, experience, and demonstrated capability. As professionals gain exposure to different aspects of the field, they often develop deeper expertise in specific domains. This specialization can lead to advanced roles with greater responsibility, higher complexity, and increased strategic importance within organizations. Over time, some professionals may transition into leadership positions where they influence security strategy, manage teams, and contribute to organizational decision-making at a higher level.
Ultimately, choosing a cybersecurity career path is a process that requires careful reflection and ongoing adjustment. It involves understanding personal strengths, exploring different technical domains, and gaining practical exposure to real-world security challenges. The field rewards curiosity, persistence, and adaptability, making it suitable for individuals who are committed to long-term growth and continuous improvement. As digital transformation continues to accelerate globally, the role of cybersecurity professionals will only become more central to ensuring the safety and resilience of modern systems.