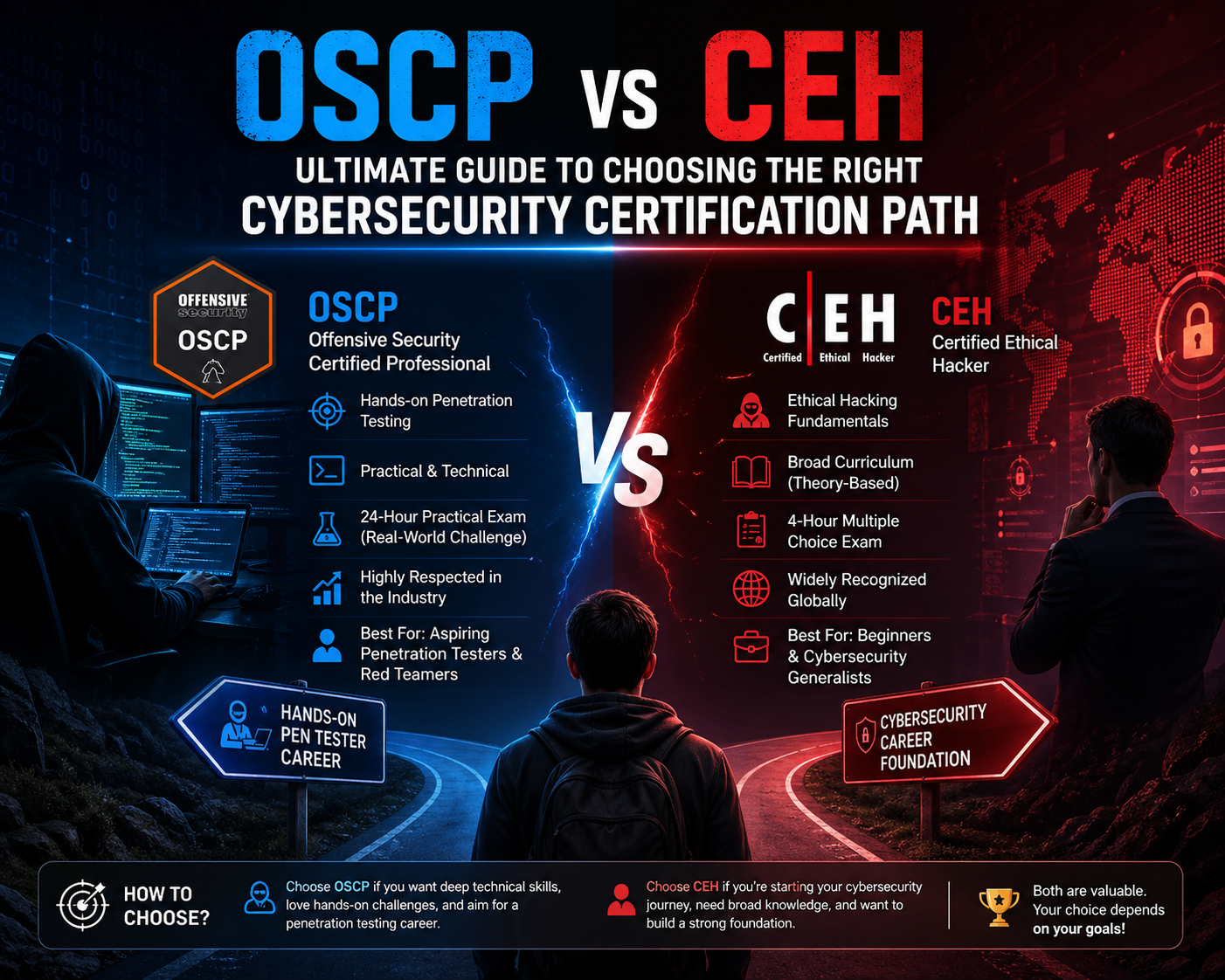
In the cybersecurity industry, professional certifications play a critical role in defining expertise, employability, and long-term career direction. Among the most widely discussed credentials are OSCP (Offensive Security Certified Professional) and CEH (Certified Ethical Hacker). Both certifications are highly recognized across global cybersecurity roles, yet they represent fundamentally different philosophies of learning, assessment, and practical application.
OSCP is designed around deep technical immersion and real-world penetration testing simulation. It requires candidates to actively engage with systems, discover vulnerabilities, and exploit them without step-by-step guidance. CEH, in contrast, emphasizes structured learning and conceptual understanding of ethical hacking methodologies, providing a broad overview of how attacks and defenses operate within modern digital infrastructures.
Although both certifications fall under ethical hacking, their purpose and execution differ significantly. OSCP focuses on proving technical ability through performance-based testing, while CEH focuses on building foundational cybersecurity awareness through structured theoretical learning.
Core Philosophy Behind OSCP and CEH Training Approaches
The OSCP certification is built on a strict hands-on methodology that prioritizes experience over memorization. Candidates are placed in controlled but realistic lab environments where they must independently analyze systems, identify weaknesses, and execute exploit strategies. There are no guided instructions during the process, meaning learners must rely on problem-solving ability, persistence, and deep technical understanding.
This approach closely mirrors real-world penetration testing scenarios. Security professionals in offensive roles rarely receive predefined instructions when assessing an organization’s infrastructure. Instead, they are expected to think like attackers, analyze systems from multiple perspectives, and adapt their approach based on live feedback from target environments.
OSCP therefore trains individuals to operate under uncertainty, requiring them to combine networking knowledge, operating system familiarity, scripting ability, and exploitation techniques into a cohesive workflow. It is less about theoretical knowledge and more about execution under pressure.
CEH takes a fundamentally different approach. It is structured around a classroom-style learning model that introduces cybersecurity concepts in a systematic way. Instead of focusing on deep exploitation mechanics, it covers a wide range of topics, including reconnaissance, scanning, system vulnerabilities, malware behavior, cryptography basics, and social engineering techniques.
The goal of CEH is to provide learners with a broad understanding of the ethical hacking lifecycle. It explains how attackers think and operate, but does not require the same depth of hands-on exploitation as OSCP. This makes it more accessible for individuals who are new to cybersecurity or transitioning from general IT roles.
Technical Depth and Skill Expectations in OSCP vs CEH
One of the most defining differences between OSCP and CEH is the level of technical depth required to succeed.
OSCP demands advanced familiarity with Linux and Windows operating systems, networking protocols, command-line operations, and scripting languages such as Python or Bash. Candidates are expected to understand how systems behave at a granular level and how vulnerabilities can be chained together to achieve unauthorized access.
In OSCP training environments, learners must independently discover entry points into systems, escalate privileges, and extract sensitive information. There is a strong emphasis on methodology, including enumeration, exploitation, post-exploitation, and reporting. Each step must be performed manually, reinforcing deep technical understanding.
CEH, in contrast, focuses on conceptual exposure rather than deep technical execution. It introduces learners to cybersecurity tools and techniques, but does not require the same level of manual exploitation. Topics are presented in a structured manner, covering a wide variety of attack types and defensive strategies.
This includes understanding how scanning tools work, how vulnerabilities are categorized, and how attackers may exploit human behavior through social engineering. While CEH includes technical elements, it does not require candidates to perform advanced system compromise activities.
The difference in technical intensity makes OSCP significantly more challenging, especially for individuals without prior hands-on experience in IT systems or networking environments.
Practical Application in Real Cybersecurity Roles
OSCP is widely regarded as one of the most practical certifications in offensive cybersecurity. Professionals who earn this certification are often involved in penetration testing roles where they simulate real-world attacks against corporate systems. Their objective is to identify security weaknesses before malicious attackers can exploit them.
These professionals operate in environments that require creativity and adaptability. They may encounter unknown systems, misconfigured services, or complex network architectures that require step-by-step investigation. OSCP-certified individuals are expected to document their findings in detailed technical reports that help organizations strengthen their security posture.
The certification is particularly valuable in roles such as penetration tester, red team operator, vulnerability researcher, and security consultant. These positions require deep technical expertise and the ability to think like an attacker.
CEH aligns more closely with defensive cybersecurity roles. Professionals with this certification often work in security operations centers, incident response teams, and compliance-driven environments. Their responsibilities focus on monitoring systems, identifying potential threats, and responding to security incidents.
Instead of actively exploiting systems, CEH-certified professionals analyze how attacks occur and implement preventive measures. They help organizations understand security risks and improve overall cyber hygiene.
This makes CEH suitable for roles such as security analyst, cybersecurity administrator, and risk management specialist.
Exam Structure and Evaluation Methodology Differences
The OSCP examination is one of the most challenging assessments in cybersecurity certification pathways. It is conducted in a practical lab environment where candidates are given a set of machines to compile. The objective is to gain access to multiple systems, escalate privileges, and document the entire attack process within a strict time limit.
This exam format tests not only technical knowledge but also endurance, patience, and problem-solving ability. Candidates must work independently without external assistance, simulating real-world penetration testing conditions.
The evaluation is based entirely on performance, meaning candidates must demonstrate actual system compromise skills rather than theoretical knowledge.
CEH uses a multiple-choice examination format that assesses knowledge across a broad range of cybersecurity topics. Candidates are tested on their understanding of ethical hacking methodologies, security tools, and attack techniques.
The exam is time-bound and structured, requiring candidates to recall information and apply conceptual understanding to answer questions correctly. While CEH does include some scenario-based questions, it does not require live system exploitation or hands-on hacking activities.
This difference in assessment style reflects the broader distinction between practical skill validation and theoretical knowledge evaluation.
Preparation Requirements and Learning Curve Differences
Preparing for OSCP requires significant hands-on practice. Candidates must spend time working in lab environments where they can safely explore vulnerabilities and practice exploitation techniques. This often involves using platforms that simulate real-world systems with intentional security flaws.
Learners are expected to develop strong familiarity with penetration testing tools, networking concepts, and system behavior. The learning curve is steep, especially for individuals without prior cybersecurity experience.
CEH preparation is more structured and study-based. Learners typically follow a syllabus that covers multiple cybersecurity domains in a sequential manner. The focus is on understanding concepts, memorizing attack techniques, and learning how security tools are used in different scenarios.
This makes CEH more approachable for beginners, as it does not require the same level of technical experimentation or system manipulation.
Professional Direction and Skill Identity in Cybersecurity
The OSCP certification tends to shape professionals into highly technical offensive security specialists. These individuals are trained to operate in environments where breaking systems is part of their job function. Their skill set is highly specialized, focusing on penetration testing, vulnerability exploitation, and adversarial simulation.
CEH, on the other hand, develops professionals with broad cybersecurity awareness. These individuals understand how cyberattacks occur and how to defend against them across multiple domains. Their role is more aligned with organizational security management rather than deep technical exploitation.
This difference influences long-term career identity. OSCP professionals often develop into advanced penetration testers or red team experts, while CEH professionals may move into security operations, governance, and compliance roles.
OSCP vs CEH: Career Pathways and Industry Positioning
In cybersecurity hiring ecosystems, OSCP and CEH certifications are often treated as entry points into two very different professional trajectories. While both credentials validate knowledge in ethical hacking, the direction they push a career is not the same. OSCP is strongly associated with offensive security specialization, whereas CEH aligns more with broad cybersecurity awareness and defensive operations.
Organizations typically interpret OSCP as proof that a candidate can perform real penetration testing tasks without supervision. It signals capability in identifying vulnerabilities, exploiting them, and producing structured technical reports that simulate real consultancy work. CEH, by contrast, signals familiarity with cybersecurity principles, attack methodologies, and defensive awareness across enterprise systems.
This difference directly influences hiring decisions. Employers seeking penetration testers, red team operators, or vulnerability analysts often prioritize OSCP because it demonstrates verified hands-on capability. Employers looking for security analysts, compliance officers, or incident response staff may prefer CEH due to its broader conceptual coverage and structured learning foundation.
The distinction is not about superiority but specialization. OSCP aligns with deep technical execution roles, while CEH aligns with analytical and governance-focused roles within cybersecurity frameworks.
Job Roles Associated with OSCP Certification
Professionals holding OSCP certification are typically placed in highly technical cybersecurity positions that require offensive security expertise. These roles involve actively identifying vulnerabilities in systems and simulating real-world attacks to test organizational defenses.
A penetration tester’s role is one of the most common career paths for OSCP-certified individuals. In this role, professionals are responsible for conducting authorized cyberattacks against networks, applications, and infrastructure to identify exploitable weaknesses. The work is highly technical and requires strong knowledge of operating systems, networking protocols, and exploit development techniques.
Another common role is red team operator. In this capacity, professionals simulate advanced persistent threats by mimicking real attacker behavior. The goal is not only to find vulnerabilities but also to evaluate how well an organization can detect and respond to sophisticated attacks.
OSCP holders may also work as vulnerability researchers. These professionals focus on discovering unknown security flaws in software, systems, or applications. Their findings are often used to improve security products or patch critical vulnerabilities before exploitation occurs in the wild.
Security consultants also represent a significant career path. In consulting roles, OSCP-certified professionals work with multiple organizations to assess security posture, conduct audits, and recommend improvements based on penetration testing results.
These roles require not just technical knowledge but also analytical thinking, documentation skills, and the ability to operate independently in complex environments.
Job Roles Associated with CEH Certification
CEH certification supports a wider range of cybersecurity roles that are more focused on defensive strategies, monitoring, and organizational security management. Unlike OSCP, which is highly specialized, CEH provides a broader entry into cybersecurity careers.
One of the most common roles is cybersecurity analyst. Professionals in this role monitor network traffic, investigate suspicious activity, and analyze potential security threats. They often work in security operations centers where they respond to alerts and ensure systems remain secure.
An information security analyst is another frequent career path. These professionals focus on maintaining security policies, evaluating risk exposure, and implementing protective measures across organizational systems. Their work often involves compliance with industry standards and regulatory frameworks.
Incident response specialists also align with CEH certification. These professionals are responsible for handling security breaches, analyzing attack patterns, and coordinating recovery efforts after cyber incidents. Their role requires quick decision-making and strong analytical skills.
In some cases, CEH-certified professionals move into governance and compliance roles. These positions involve ensuring that organizations follow cybersecurity policies, legal regulations, and industry best practices.
CEH certification also serves as a foundation for individuals transitioning into advanced cybersecurity roles later in their careers. It provides the conceptual knowledge required to understand how attacks work before moving into more technical specializations.
Salary Trends and Financial Growth in OSCP vs CEH Careers
Salary expectations in cybersecurity are influenced by multiple factors, including experience level, job role, geographic location, and certification type. However, OSCP and CEH certifications tend to show distinct patterns in earning potential due to the nature of the roles they support.
OSCP-related roles generally fall into the higher-earning category within cybersecurity. This is largely because penetration testing and offensive security roles require advanced technical expertise. Professionals in these positions are expected to perform high-risk security assessments that directly impact organizational defense strategies.
Entry-level penetration testers may start with moderate salaries, but compensation increases significantly with experience. As professionals gain deeper expertise in exploit development, red teaming, and advanced vulnerability analysis, their earning potential grows substantially.
CEH-related roles tend to have a broader salary range due to the diversity of positions available. Entry-level cybersecurity analysts may start at relatively lower salary levels compared to OSCP professionals, but experienced analysts, especially those in senior security or leadership roles, can earn competitive compensation.
Senior-level positions such as security managers, risk analysts, or compliance officers often offer higher salaries within CEH-aligned career paths. These roles require experience in managing security frameworks, policies, and organizational risk strategies.
Overall, OSCP tends to offer faster entry into high-paying technical roles, while CEH provides a more gradual salary progression across a wider range of cybersecurity positions.
Industry Demand and Market Relevance of Both Certifications
The demand for cybersecurity professionals continues to increase as organizations face growing cyber threats, regulatory requirements, and digital transformation challenges. Both OSCP and CEH certifications are recognized in the industry, but they serve different segments of this demand.
OSCP is highly valued in organizations that prioritize offensive security testing. Companies that invest in red teaming, penetration testing, and advanced security assessments actively seek professionals with OSCP certification. This demand is particularly strong in sectors such as finance, technology, government, and defense, where security testing is critical.
The certification is also respected in consulting firms that provide cybersecurity services to multiple clients. OSCP-certified professionals are often deployed to assess infrastructure security, identify vulnerabilities, and simulate real-world attack scenarios.
CEH certification has broader market applicability due to its foundational nature. Many organizations use CEH as a baseline requirement for entry-level cybersecurity positions. It is particularly common in environments where security awareness, monitoring, and compliance are key priorities.
Industries such as healthcare, education, retail, and corporate enterprises frequently hire CEH-certified professionals for roles involving security monitoring and incident response.
The widespread applicability of CEH makes it a common entry point into cybersecurity careers, while OSCP is more specialized and targeted toward advanced technical roles.
Skill Development Journey in OSCP vs CEH Paths
The skill development journey for OSCP is intensive and experience-driven. Candidates spend significant time in lab environments where they must independently discover vulnerabilities and develop exploitation strategies. This process builds strong analytical thinking and technical resilience.
OSCP learners develop deep expertise in system architecture, network protocols, and exploitation techniques. They also gain experience in documenting attack chains, which is a critical skill in professional penetration testing.
The learning process is often self-directed, requiring persistence and problem-solving ability. Candidates must continuously experiment, fail, and refine their techniques to succeed.
CEH follows a structured learning path that gradually introduces cybersecurity concepts. Learners progress through different domains, starting with basic security principles and advancing toward more complex attack methodologies.
The focus is on understanding rather than deep technical execution. Learners gain exposure to multiple areas of cybersecurity, including network security, application security, cryptography, and social engineering.
This structured approach helps build a strong conceptual foundation, making it easier for individuals to transition into cybersecurity roles or pursue advanced certifications later.
Employer Perspective on OSCP and CEH Certifications
From an employer’s perspective, OSCP and CEH certifications serve different validation purposes. OSCP is often viewed as a proof of technical capability. Employers trust OSCP-certified candidates to perform real penetration testing tasks without extensive supervision.
This makes OSCP highly valuable for roles that require immediate technical contribution. Organizations often use it as a benchmark for hiring offensive security professionals.
CEH is viewed as a foundational cybersecurity certification that demonstrates awareness of security principles and attack methodologies. Employers use it to evaluate whether candidates understand cybersecurity concepts at a baseline level.
It is particularly useful for entry-level hiring or for professionals transitioning into cybersecurity from other IT domains. CEH helps organizations identify candidates who are capable of learning and adapting to security environments.
Long-Term Career Development Potential
OSCP offers strong long-term potential for specialization in offensive security. Professionals often progress into advanced roles such as senior penetration testers, red team leaders, and security researchers. These positions require continuous skill development due to the evolving nature of cyber threats.
CEH provides long-term flexibility across multiple cybersecurity domains. Professionals can move into security management, compliance, incident response, or risk analysis depending on experience and additional training.
While OSCP leads to deep specialization, CEH supports broader career mobility across cybersecurity disciplines.
Exam Difficulty Comparison Between OSCP and CEH
The OSCP and CEH certifications differ sharply in terms of difficulty, not just in content but in cognitive demand, time pressure, and required problem-solving style. OSCP is widely regarded as one of the most challenging entry-to-intermediate cybersecurity certifications due to its fully practical nature. CEH, while still demanding, operates at a more structured and theory-driven level.
OSCP difficulty comes primarily from its absence of guidance during the examination process. Candidates are placed into a controlled but realistic environment containing multiple systems with hidden vulnerabilities. The expectation is not just to identify weaknesses but to exploit them in a logical sequence that leads to full system compromise. This requires deep familiarity with operating systems, networking behavior, privilege escalation techniques, and exploit chaining.
The challenge is amplified by time constraints and the need for precise documentation. Candidates must think like attackers while also behaving like consultants, producing structured reports that explain how each vulnerability was discovered and exploited. This dual requirement of technical execution and professional reporting increases complexity significantly.
CEH difficulty is different in nature. Instead of live exploitation, candidates face a structured examination composed of conceptual and scenario-based questions. The challenge lies in breadth rather than depth. Learners must be familiar with a wide range of cybersecurity topics, including scanning techniques, attack vectors, cryptography basics, malware behavior, and security frameworks.
While CEH requires strong memory retention and conceptual understanding, it does not demand the same level of real-time problem solving or system manipulation. The cognitive load is distributed across knowledge areas rather than concentrated in live execution.
This difference creates two distinct difficulty profiles: OSCP is execution-heavy and stress-intensive, while CEH is knowledge-heavy and structured.
Preparation Strategy Differences for OSCP and CEH
Preparation for OSCP requires an immersive and hands-on approach. Candidates must spend extensive time in practice environments where they can safely simulate attacks against vulnerable systems. This process is essential because OSCP does not test theoretical knowledge alone; it evaluates applied technical skill.
A typical OSCP preparation journey involves repeated cycles of system enumeration, vulnerability discovery, exploitation attempts, and post-exploitation analysis. Candidates must become comfortable with command-line tools, scripting automation, and manual exploitation techniques. Learning is driven by experimentation, failure, and iterative improvement.
A key aspect of OSCP preparation is developing persistence. Many vulnerabilities are not immediately obvious, and successful exploitation often requires combining multiple smaller weaknesses into a complete attack chain. This demands analytical thinking and patience.
CEH preparation follows a more structured academic approach. Candidates typically study predefined domains that cover cybersecurity fundamentals in a logical sequence. The learning process involves reading conceptual material, understanding attack methodologies, and memorizing key techniques used in ethical hacking.
Instead of building exploits, CEH candidates focus on understanding how attacks work at a high level. This includes recognizing different types of malware, understanding scanning techniques, and learning how security tools are used in defensive and offensive contexts.
The preparation journey is more linear compared to OSCP. Learners progress through topics in a guided manner, making it easier for beginners to follow without prior technical experience.
Time Commitment and Learning Curve Analysis
The time required to prepare for OSCP is typically significantly higher due to its hands-on nature. Candidates often spend months developing the required technical proficiency before attempting the exam. The learning curve is steep, especially for individuals without prior experience in penetration testing or system administration.
The difficulty lies not only in understanding concepts but in applying them under realistic conditions. OSCP requires learners to develop a hacker mindset, which involves thinking creatively about system weaknesses and attack paths.
CEH generally has a shorter learning curve. Because it is structured and concept-based, learners can progress through the material more predictably. The focus is on understanding a wide range of cybersecurity topics rather than mastering deep technical execution.
This makes CEH more accessible for individuals entering cybersecurity for the first time or transitioning from non-technical roles. However, the breadth of topics still requires consistent study and memorization.
The difference in learning curve reflects the intended purpose of each certification. OSCP is designed to build practical offensive capability, while CEH is designed to build foundational cybersecurity awareness.
Real-World Skill Application After Certification
OSCP-certified professionals are expected to immediately contribute to offensive security operations. In real-world environments, this means conducting penetration tests on corporate networks, identifying exploitable vulnerabilities, and simulating attacker behavior.
Their work often involves interacting with complex systems that may include misconfigurations, outdated software, or hidden vulnerabilities. OSCP professionals must be able to navigate these environments independently and produce actionable security reports.
The skills gained through OSCP translate directly into red team operations, vulnerability research, and advanced security assessments. These roles require continuous technical refinement as attackers constantly evolve their techniques.
CEH-certified professionals apply their skills differently. Instead of actively exploiting systems, they focus on identifying potential security risks and ensuring that organizations maintain strong defensive postures.
Their responsibilities often include monitoring security systems, analyzing logs for suspicious activity, supporting incident response teams, and ensuring compliance with cybersecurity standards. CEH professionals help organizations understand how attacks occur and how to prevent them.
The skill application is more analytical and observational compared to the execution-heavy nature of OSCP roles.
Industry Recognition and Certification Perception
Within the cybersecurity industry, OSCP holds a reputation for being highly rigorous and skill-intensive. Employers often view it as evidence that a candidate has proven hands-on penetration testing ability. It is commonly associated with advanced offensive security roles and is highly respected in technical hiring processes.
The certification is often used as a benchmark for evaluating whether candidates can perform real-world attack simulations without supervision. Because of its practical exam structure, OSCP is seen as a strong indicator of job readiness in penetration testing environments.
CEH, on the other hand, is widely recognized as a foundational cybersecurity certification. It is often used by organizations to validate that candidates understand ethical hacking principles and cybersecurity concepts at a general level.
It is especially common in job postings for entry-level cybersecurity roles or positions that require broad security awareness rather than deep technical specialization.
While CEH is respected globally, its perception is more aligned with theoretical understanding than advanced technical execution. OSCP is more associated with practical expertise and specialized offensive capability.
Career Progression Pathways After OSCP and CEH
OSCP typically leads to career paths in offensive security specialization. Professionals often move into roles such as penetration testers, red team operators, and security researchers. These positions require continuous technical development and a deep understanding of attack methodologies.
As professionals gain experience, they may advance into senior roles where they lead penetration testing teams or design advanced adversary simulations for organizations. The career path is highly technical and focused on continuous skill evolution.
CEH provides a broader career pathway across cybersecurity domains. Professionals may begin in roles such as security analysts or incident response specialists and later transition into governance, risk, and compliance positions.
The certification allows for flexibility in career direction, enabling individuals to explore different areas of cybersecurity depending on interest and opportunity. Some CEH professionals later pursue advanced certifications to specialize further in offensive or defensive security.
The progression is less linear than OSCP but offers wider optionality across cybersecurity disciplines.
Cognitive Approach Required for OSCP vs CEH
OSCP requires an attacker-oriented mindset. Candidates must think creatively about how systems can be exploited, often combining multiple vulnerabilities to achieve access. This requires logical reasoning, experimentation, and persistence under uncertainty.
The cognitive load is dynamic, as each system presents unique challenges that cannot be solved through memorization alone. Candidates must continuously adapt their approach based on system behavior and feedback.
CEH requires a structured analytical mindset. Candidates must understand how different attack techniques function and how they relate to cybersecurity frameworks. The cognitive focus is on comprehension, classification, and application of known concepts.
Rather than discovering new attack paths, CEH learners focus on understanding established methodologies and how they are used in cybersecurity operations.
This difference in cognitive style reflects the broader distinction between execution-based and knowledge-based certification models.
Industry Use Cases and Organizational Value
Organizations use OSCP-certified professionals primarily for offensive security validation. Their role is to simulate external and internal attacks to identify weaknesses before they can be exploited by malicious actors. This proactive security testing is critical for high-risk industries such as finance, healthcare, and technology.
OSCP professionals help organizations strengthen defenses by exposing vulnerabilities through controlled attacks. Their findings directly influence security architecture improvements.
CEH-certified professionals contribute to organizational security by improving awareness and monitoring capabilities. They help detect suspicious activity, analyze potential threats, and ensure compliance with security standards.
Their role is more aligned with maintaining an ongoing security posture rather than actively testing system resilience.
Both certifications provide organizational value, but in different ways. OSCP strengthens offensive security testing, while CEH strengthens defensive awareness and operational security management.
Final Technical Comparison Perspective
When comparing OSCP and CEH from a purely technical standpoint, the distinction becomes clear in terms of depth versus breadth.
OSCP prioritizes depth of technical execution. It demands mastery of penetration testing workflows, exploitation techniques, and real-world system interaction. It is highly specialized and performance-driven.
CEH prioritizes breadth of cybersecurity knowledge. It covers multiple domains of ethical hacking, providing a wide understanding of how cyber threats operate and how they are mitigated.
OSCP builds technical specialists capable of executing complex attacks in controlled environments. CEH builds cybersecurity generalists capable of understanding and responding to a wide range of security scenarios.
Both certifications serve important but different roles in the cybersecurity ecosystem, shaping professionals based on whether they pursue specialization or broad foundational expertise.
Conclusion
The comparison between OSCP and CEH ultimately reflects two fundamentally different approaches to cybersecurity education, professional development, and skill validation. Both certifications are widely recognized and respected in the information security industry, but they serve different purposes depending on where an individual wants to position themselves within the cybersecurity landscape.
OSCP is centered around practical offensive security capability. It is designed for individuals who want to work directly with systems in a hands-on manner, identifying vulnerabilities, exploiting weaknesses, and simulating real-world cyberattacks. The certification emphasizes technical depth, problem-solving ability, and persistence in complex environments. It does not rely on memorization or theoretical recall; instead, it tests how effectively a candidate can operate in realistic penetration testing scenarios under pressure.
This makes OSCP particularly valuable for roles that demand direct engagement with system security at a technical level. Professionals who pursue OSCP are typically oriented toward offensive security disciplines, where the ability to think like an attacker is essential. Their work often involves breaking into systems in a controlled and ethical manner to uncover weaknesses before malicious actors can exploit them. The certification builds resilience in analytical thinking and forces candidates to develop a structured yet flexible approach to cybersecurity challenges.
CEH, in contrast, takes a broader and more structured approach to cybersecurity education. It is designed to introduce learners to the wide landscape of ethical hacking, covering multiple domains of cybersecurity without requiring deep technical exploitation skills. Instead of focusing on how to break into systems in real-time environments, it focuses on how attacks work conceptually, how security systems are structured, and how organizations can defend against common threats.
This makes CEH particularly suitable for individuals who are either new to cybersecurity or who want to develop a broad understanding of the field before specializing. It provides exposure to many areas of cybersecurity, including network security, application security, cryptography, and social engineering. However, it does so in a controlled and structured way that emphasizes understanding over execution.
The difference in learning style between OSCP and CEH is one of the most important factors influencing career direction. OSCP demands independent thinking, experimentation, and continuous adaptation. It trains individuals to operate in uncertain environments where there are no step-by-step instructions, reflecting real-world offensive security scenarios. CEH, on the other hand, provides a guided learning path that helps learners understand cybersecurity principles in a logical and organized manner.
From a career perspective, OSCP often leads to more specialized and technically demanding roles. Professionals with OSCP certification are commonly found in penetration testing teams, red team operations, and security consulting roles where deep technical expertise is required. These roles involve actively identifying vulnerabilities in systems and simulating advanced attack scenarios to assess organizational resilience. The demand for such skills continues to grow as organizations face increasingly sophisticated cyber threats.
CEH supports a broader range of cybersecurity roles that are more aligned with monitoring, analysis, and defensive operations. Professionals with this certification often work in security operations centers, incident response teams, or compliance-focused environments. Their responsibilities include identifying potential security threats, analyzing system logs, and ensuring that organizational security policies are followed correctly.
In terms of difficulty, OSCP is widely regarded as significantly more challenging due to its practical nature. The certification requires candidates to perform live system exploitation in a timed environment without external assistance. This creates a high-pressure scenario that tests not only technical ability but also mental endurance and problem-solving efficiency. Success in OSCP requires consistent hands-on practice and a strong understanding of how systems operate at a low level.
CEH is considered less technically demanding but still requires substantial effort due to the breadth of topics covered. The challenge lies in understanding a wide range of cybersecurity concepts and being able to recall and apply them in exam scenarios. While it does not require live exploitation, it still demands structured preparation and familiarity with multiple security domains.
Industry perception of both certifications also differs based on their intended purpose. OSCP is often viewed as a strong indicator of practical offensive capability. Employers value it because it demonstrates that a candidate can perform real penetration testing tasks in realistic environments. CEH is viewed more as a foundational certification that demonstrates awareness of cybersecurity principles and methodologies. It is often used as an entry point into the field or as a stepping stone toward more advanced certifications.
Salary expectations for both certifications can overlap, but OSCP-related roles tend to offer higher compensation at the technical level due to the specialized skill set required. Penetration testers and red team professionals often command strong salaries because their expertise directly contributes to identifying and mitigating high-risk vulnerabilities. CEH-related roles vary more widely in compensation depending on job function, ranging from entry-level analyst positions to senior security management roles.
Long-term career growth also depends on how each certification is leveraged. OSCP provides a pathway into deep specialization within offensive security, where professionals continuously refine their technical expertise and advance into senior penetration testing or security research roles. CEH provides a broader foundation that allows professionals to explore multiple areas of cybersecurity before choosing a specialization path.
Ultimately, the choice between OSCP and CEH depends on an individual’s career goals, technical interests, and preferred learning style. Those who enjoy hands-on technical challenges, system exploitation, and problem-solving in complex environments are more aligned with OSCP. Those who prefer structured learning, conceptual understanding, and broader exposure to cybersecurity topics may find CEH more suitable.
Both certifications hold value in the cybersecurity industry, but they represent different philosophies of learning and professional development. OSCP builds technical specialists capable of executing advanced security operations, while CEH builds cybersecurity generalists with a broad understanding of ethical hacking principles. Each plays an important role in shaping the cybersecurity workforce, and both contribute to strengthening organizational security in different ways.