The PenTest+ certification has evolved as a response to the rapid transformation of cybersecurity environments, where traditional perimeter-based defenses have largely been replaced by distributed, cloud-integrated, and identity-driven infrastructures. The move from PT0-002 to PT0-003 is not simply a revision of exam content but a structural adjustment that reflects how penetration testing is performed in real operational environments today. Security teams no longer operate within isolated networks; instead, they assess systems that span cloud platforms, remote endpoints, containerized applications, and continuously deployed services.
Earlier versions of the certification focused primarily on conventional network penetration testing methodologies, including scanning internal networks, identifying vulnerabilities in operating systems, and exploiting known weaknesses in applications. While these foundational skills remain relevant, they are no longer sufficient on their own. Modern security assessments require a broader understanding of distributed architectures and how attackers move across interconnected systems.
The updated version integrates a more dynamic perspective on offensive security, emphasizing adaptability and contextual awareness. Candidates are expected to understand not only how vulnerabilities exist but also how they are exploited in multi-layered environments. This includes recognizing dependencies between systems, understanding authentication flows, and evaluating how different components interact under real-world conditions.
Structural Shift from PT0-002 to PT0-003 Examination Focus
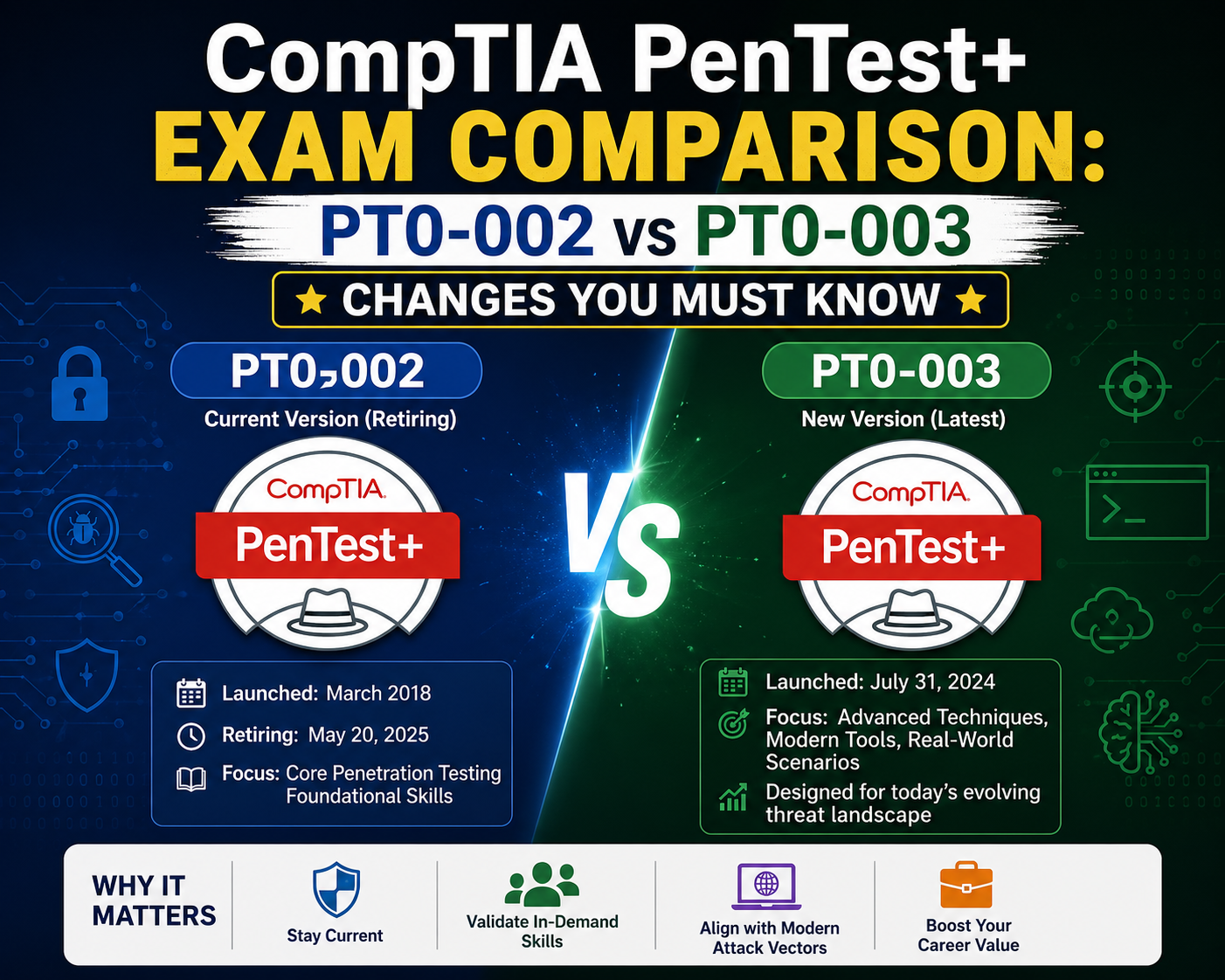
The transition from PT0-002 to PT0-003 reflects a deliberate restructuring of examination priorities. PT0-002 was designed around a more traditional cybersecurity model, where systems were often assumed to be on-premises and relatively static. PT0-003 shifts the focus toward hybrid infrastructures that combine cloud services, remote access technologies, and automated deployment pipelines.
This shift introduces a more realistic testing environment that mirrors current enterprise architectures. Instead of focusing heavily on isolated vulnerabilities, the updated approach emphasizes attack chains and how multiple weaknesses can be combined to achieve system compromise. Candidates are expected to understand the full lifecycle of an attack, from initial reconnaissance to post-exploitation activities and persistence techniques.
Another significant change is the increased emphasis on scenario-based thinking. Rather than relying on isolated technical knowledge, candidates must analyze complex environments and determine the most effective approach to penetration testing. This includes evaluating risk exposure, prioritizing targets, and adapting methodologies based on system responses.
The structural changes also reflect a broader industry trend toward continuous security validation. Organizations increasingly require ongoing testing rather than periodic assessments, which means penetration testers must be familiar with evolving systems rather than static snapshots.
Modern Threat Landscape Driving Certification Evolution
The evolution of the PenTest+ certification is closely tied to changes in the global threat landscape. Cyberattacks have become more sophisticated, automated, and targeted. Attackers now leverage advanced techniques that combine social engineering, credential abuse, and infrastructure exploitation to bypass traditional defenses.
One of the most significant changes in the threat environment is the rise of cloud-native attacks. As organizations migrate critical workloads to cloud platforms, attackers have shifted their focus accordingly. Misconfigured storage systems, overly permissive identity roles, and insecure APIs have become primary targets. These attack vectors require penetration testers to understand cloud architecture principles and how security misconfigurations can be exploited.
In addition, the proliferation of remote work has expanded the attack surface significantly. Endpoints are no longer confined to corporate networks, making identity verification and access control more critical than ever. Attackers frequently exploit weak authentication mechanisms or stolen credentials to gain initial access to systems.
Automation has also changed the speed and scale of attacks. Modern adversaries use automated tools to scan large ranges of IP addresses, identify vulnerabilities, and exploit them within minutes. This requires penetration testers to adopt similarly efficient methodologies to keep pace with evolving threats.
Expansion of Cloud Security Testing in PT0-003
Cloud security has become a central component of modern penetration testing practices, and this is reflected strongly in PT0-003. Unlike traditional environments where infrastructure was centrally managed, cloud systems operate under shared responsibility models where both providers and users play roles in securing resources.
Penetration testers must now understand how misconfigurations in cloud environments can lead to significant security breaches. These include improperly configured identity and access management policies, unsecured storage services, and excessive permissions granted to applications or users. Such weaknesses are often exploited without the need for complex exploitation techniques, making configuration analysis a critical skill.
Another important aspect of cloud security testing is the ability to assess multi-tenant environments. In such systems, resources are shared across multiple users or organizations, increasing the risk of cross-tenant data exposure if isolation controls are weak or improperly configured.
Additionally, cloud environments introduce new logging and monitoring challenges. Attackers often attempt to blend into legitimate traffic patterns, making detection more difficult. Penetration testers must therefore understand how cloud-native logging systems operate and how security events are recorded and analyzed.
The inclusion of cloud-focused content ensures that candidates are prepared to assess modern infrastructure realistically rather than relying solely on traditional network-based assumptions.
Identity-Centric Attacks and Zero Trust Integration
Modern cybersecurity frameworks increasingly rely on identity as the primary security boundary, replacing traditional perimeter-based models. The PT0-003 update reflects this shift by placing greater emphasis on identity-centric attacks and Zero Trust principles.
In identity-driven environments, attackers focus on compromising credentials rather than directly exploiting systems. This includes techniques such as credential theft, session hijacking, and privilege escalation through misconfigured roles. Once access is obtained, attackers can move laterally within systems while appearing as legitimate users.
Zero Trust architecture fundamentally changes how access is granted and verified. Instead of assuming trust based on network location, every request is evaluated based on identity, device posture, and contextual factors. From a penetration testing perspective, this introduces new challenges in identifying weaknesses in authentication workflows and authorization logic.
Penetration testers must also evaluate how effectively organizations implement least privilege principles. Excessive permissions remain one of the most common security weaknesses in modern environments. Misconfigured roles can allow attackers to escalate privileges or access sensitive resources without detection.
The integration of these concepts into the certification reflects their importance in contemporary security strategies and highlights the need for testers to think beyond traditional network boundaries.
Evolution of Attack Techniques and MITRE Alignment
Attack methodologies have evolved significantly, and PT0-003 reflects this by aligning more closely with modern frameworks that categorize adversarial behavior. Instead of focusing solely on isolated exploits, the updated approach emphasizes understanding attack patterns and techniques used across different stages of an intrusion.
One key development is the increased focus on living-off-the-land techniques. These involve using legitimate system tools to perform malicious activities, reducing the likelihood of detection. Attackers frequently leverage built-in operating system utilities to execute commands, move laterally, and maintain persistence.
Another important area is defense evasion. Modern security systems rely heavily on detection mechanisms, including endpoint monitoring and behavioral analysis. Attackers respond by developing methods that minimize their visibility within monitored environments.
Credential-based attacks also play a central role in modern penetration testing scenarios. Instead of exploiting software vulnerabilities, attackers often rely on stolen credentials to gain access to systems. Understanding how these credentials are obtained, reused, or escalated is critical for effective testing.
The updated certification encourages a broader understanding of these techniques, emphasizing how they fit into complete attack chains rather than isolated events.
Increased Role of Scripting and Security Automation
Automation has become an essential component of modern penetration testing workflows. The complexity and scale of current environments make manual testing inefficient in many cases. As a result, scripting and automation skills are increasingly important for security professionals.
PT0-003 reflects this shift by emphasizing practical understanding of scripting languages commonly used in security operations. These include tools for automating reconnaissance, vulnerability scanning, and data analysis. The focus is not on advanced software development but on the ability to modify and apply scripts effectively in real scenarios.
Automation also plays a critical role in improving efficiency during testing engagements. Large-scale environments often contain thousands of assets, making manual analysis impractical. Automated scripts allow testers to identify patterns, prioritize targets, and streamline repetitive tasks.
Additionally, scripting is often used in post-exploitation phases to maintain access, extract data, or pivot between systems. Understanding how these scripts function and how they can be adapted is essential for realistic penetration testing scenarios.
The integration of automation concepts ensures that candidates are prepared for modern workflows where efficiency and scalability are key factors.
Transformation of Web Application and API Security Testing
Web applications and APIs have become central components of modern digital infrastructure, and their complexity has increased significantly. PT0-003 reflects this evolution by expanding the scope of web application security testing.
Modern applications rely heavily on APIs for communication between services. These APIs often expose sensitive functionality and data, making them attractive targets for attackers. Penetration testers must understand how to analyze API endpoints, identify authentication weaknesses, and evaluate data validation mechanisms.
Web applications themselves have also evolved beyond traditional architectures. Dynamic content, client-side rendering, and microservices introduce new challenges in identifying vulnerabilities. Attackers often exploit logic flaws rather than simple injection vulnerabilities, requiring deeper analysis of application behavior.
Authentication and session management remain critical areas of focus. Weaknesses in these mechanisms can allow attackers to bypass security controls or impersonate legitimate users. Understanding how these systems function is essential for effective testing.
The expanded coverage of web and API security ensures that candidates are prepared to assess modern application ecosystems accurately and comprehensively.
Cloud-Native Architecture and Its Impact on Penetration Testing
The expansion of cloud-native architectures has fundamentally changed how penetration testing is conducted. Traditional models assumed relatively stable infrastructure where systems were deployed on fixed servers with predictable network boundaries. In contrast, cloud-native environments are highly dynamic, often composed of microservices, ephemeral containers, serverless functions, and distributed storage systems. This creates a constantly shifting attack surface that requires a different mindset from penetration testers.
In PT0-003, this shift is reflected through a deeper expectation that candidates understand how cloud-native systems behave under real operational conditions. Instead of treating cloud platforms as simple infrastructure providers, penetration testers are now expected to evaluate how applications are designed, deployed, and secured within them. This includes understanding orchestration systems, automated deployment pipelines, and infrastructure-as-code practices that define modern environments.
One of the most critical aspects of cloud-native penetration testing is identifying misconfigurations that arise from automation. Since cloud resources are often deployed through templates and scripts, a single configuration error can propagate across multiple environments. These misconfigurations may include overly permissive roles, exposed storage endpoints, or insecure default settings that are unintentionally left active during deployment.
Another important factor is the transient nature of cloud workloads. Unlike traditional servers that remain static, cloud instances may be created and destroyed within minutes. This requires penetration testers to adapt their methodology to account for short-lived assets that may only exist temporarily during testing windows. As a result, reconnaissance and enumeration must be faster and more automated than in traditional environments.
The certification update emphasizes that understanding cloud-native architecture is no longer optional. It is a foundational requirement for modern penetration testing, as most enterprise environments now rely heavily on these technologies.
Identity and Access Management as a Primary Attack Surface
In modern cybersecurity environments, identity has become the new perimeter. PT0-003 reflects this transformation by placing increased emphasis on identity and access management systems as primary targets for penetration testing. Instead of focusing solely on network-based vulnerabilities, testers are now expected to analyze how authentication and authorization systems can be exploited.
Identity-based attacks are particularly effective because they bypass traditional perimeter defenses. Once an attacker obtains valid credentials, they can often operate within systems without triggering alerts. This makes credential security one of the most critical areas of focus in modern penetration testing.
Misconfigurations in identity systems are common and often severe in impact. These may include excessive permissions assigned to user roles, weak password policies, or improper implementation of multi-factor authentication. Attackers frequently exploit these weaknesses to escalate privileges or gain unauthorized access to sensitive resources.
Another important aspect of identity-focused testing is session management. Poorly managed sessions can allow attackers to hijack authenticated users or reuse tokens to maintain persistent access. Understanding how session tokens are generated, validated, and invalidated is essential for identifying these weaknesses.
PT0-003 also reflects the growing importance of federated identity systems. Many organizations now rely on external identity providers for authentication, which introduces additional complexity and potential points of failure. Penetration testers must understand how trust relationships are established and how they can be abused if improperly configured.
Advanced Exploitation Techniques in Modern Environments
The evolution of penetration testing has led to a greater emphasis on advanced exploitation techniques that reflect real-world attacker behavior. PT0-003 incorporates these developments by focusing on more sophisticated methods of gaining and maintaining access within target environments.
One key area is the use of chained vulnerabilities. Instead of relying on a single exploit, modern attackers often combine multiple low-impact vulnerabilities to achieve significant compromise. For example, a minor information disclosure vulnerability may be used to identify credentials, which are then leveraged to escalate privileges within a system.
Another important concept is post-exploitation activity. Once initial access is gained, attackers typically focus on expanding their control over the environment. This may include lateral movement across systems, privilege escalation, and data extraction. Penetration testers must understand how these activities are performed and how they can be detected or prevented.
Defense evasion techniques are also increasingly relevant. Modern security systems use endpoint detection, behavioral analytics, and network monitoring to identify malicious activity. Attackers respond by using techniques that blend into normal system behavior. This includes using legitimate administrative tools, encrypting traffic, or timing actions to avoid detection.
Persistence mechanisms are another critical area of focus. Attackers often attempt to maintain access to compromised systems even after initial vulnerabilities are patched. This may involve creating hidden accounts, modifying startup processes, or leveraging scheduled tasks. Understanding these techniques helps penetration testers evaluate the long-term impact of a compromise.
Modern Web Application Security Challenges
Web applications have evolved significantly over the past decade, and PT0-003 reflects this evolution through expanded coverage of modern application security challenges. Traditional vulnerabilities such as injection flaws remain relevant, but they are now part of a much broader threat landscape.
Modern applications often rely heavily on client-side logic, which introduces new attack vectors. Attackers may manipulate client-side code or intercept communications between the browser and server to exploit weaknesses in application logic. Understanding how these interactions work is essential for effective testing.
Another major shift is the widespread use of APIs in application architecture. APIs serve as the backbone of modern applications, enabling communication between services, mobile apps, and external systems. However, they also introduce new risks, particularly when authentication and authorization mechanisms are weak or improperly implemented.
Common API vulnerabilities include broken object-level authorization, excessive data exposure, and insecure endpoint configurations. These issues often arise from assumptions made during development that are not properly validated during deployment. Penetration testers must be able to identify these weaknesses and understand their potential impact.
In addition, modern web applications frequently use complex authentication flows, including single sign-on and token-based systems. Misconfigurations in these systems can lead to unauthorized access or privilege escalation. Understanding how these mechanisms function is essential for identifying security gaps.
Role of Automation in Large-Scale Security Assessments
As environments become more complex, manual penetration testing alone is no longer sufficient. PT0-003 reflects this reality by emphasizing the importance of automation in security assessments. Automation allows testers to efficiently analyze large environments and identify vulnerabilities at scale.
One of the primary uses of automation is in reconnaissance. Automated tools can quickly gather information about networks, systems, and applications, reducing the time required for initial assessment. This allows testers to focus on deeper analysis and exploitation rather than manual data collection.
Automation is also critical during vulnerability scanning. Large enterprise environments may contain thousands of assets, making manual scanning impractical. Automated tools can identify potential weaknesses and prioritize them based on severity and exploitability.
Another important application of automation is in exploitation workflows. Scripts can be used to standardize attack procedures, ensuring consistency across testing environments. This is particularly useful in repeated assessments where similar vulnerabilities may exist across multiple systems.
Post-exploitation activities also benefit from automation. Tasks such as credential harvesting, privilege escalation, and data extraction can be streamlined using scripts, allowing testers to focus on strategic decision-making rather than repetitive tasks.
The emphasis on automation in PT0-003 reflects its importance in modern cybersecurity operations, where speed and efficiency are critical factors in both attack and defense scenarios.
Understanding Modern Network Security Boundaries
Traditional network security relied heavily on perimeter-based defenses, where firewalls and intrusion detection systems defined the boundary between trusted and untrusted environments. However, PT0-003 reflects the reality that these boundaries are increasingly obsolete in modern infrastructures.
Modern networks are highly distributed, with users accessing systems from multiple locations and devices. This has led to a shift toward identity-based security models rather than location-based trust assumptions. As a result, penetration testers must adapt their methodologies to account for these changes.
Network segmentation remains an important security control, but it is often imperfectly implemented. Misconfigurations can allow attackers to move laterally between network segments without detection. Understanding how segmentation is enforced and where it may fail is a key aspect of modern penetration testing.
Another important consideration is encrypted traffic. Increasingly, network communications are encrypted by default, making traditional inspection methods less effective. Penetration testers must understand how encrypted traffic impacts visibility and how attackers may exploit blind spots in monitoring systems.
Wireless networks also remain a relevant attack surface. Weak encryption, misconfigured access points, and rogue devices can all be used to gain unauthorized access to internal networks. Despite advances in security technology, these weaknesses continue to be exploited in real-world attacks.
Social Engineering and Human-Centric Security Risks
Human factors continue to play a critical role in cybersecurity, and PT0-003 reflects this by including a stronger focus on social engineering techniques. Attackers often target individuals rather than systems because humans are frequently the weakest link in security defenses.
Social engineering attacks can take many forms, including phishing, pretexting, and impersonation. These techniques rely on manipulating trust rather than exploiting technical vulnerabilities. Understanding how these attacks are constructed and executed is essential for effective penetration testing.
Phishing remains one of the most common attack vectors. Attackers craft messages designed to trick users into revealing credentials or executing malicious actions. Penetration testers must understand how to simulate these attacks safely and evaluate organizational resilience.
Pretexting involves creating a fabricated scenario to obtain sensitive information. This may include impersonating IT staff, vendors, or internal employees. The effectiveness of these attacks often depends on the quality of the pretext and the level of organizational awareness.
Physical social engineering is also relevant in some environments. This includes attempts to gain physical access to facilities or systems by exploiting human trust. While not always applicable, it remains an important consideration in comprehensive security assessments.
Integration of Modern Security Frameworks and Methodologies
PT0-003 aligns closely with modern security frameworks that categorize and structure attacker behavior. These frameworks provide a standardized way to understand how attacks progress through different stages, from initial access to data exfiltration.
One of the key benefits of this alignment is improved consistency in penetration testing methodologies. By following structured frameworks, testers can ensure that their assessments cover all relevant stages of an attack lifecycle.
These frameworks also help organizations better understand risk exposure. Instead of focusing on individual vulnerabilities, they provide a broader view of how different weaknesses can be combined to achieve system compromise.
In addition, the use of standardized terminology improves communication between technical and non-technical stakeholders. This is particularly important when presenting findings and recommending remediation strategies.
The integration of these methodologies into PT0-003 ensures that candidates are prepared to operate in professional environments where structured approaches to security testing are expected.
Modern Penetration Testing Workflow in PT0-003 Context
The workflow of penetration testing has evolved significantly, and PT0-003 reflects this shift by emphasizing a structured, iterative, and highly adaptive approach to security assessments. Traditional penetration testing models often followed a linear path: reconnaissance, scanning, exploitation, and reporting. While these stages still exist, modern environments require a more fluid interpretation of the workflow where stages overlap and feedback loops are continuous.
In PT0-003-aligned scenarios, reconnaissance is no longer a one-time activity performed at the beginning of an engagement. Instead, it becomes an ongoing process that continues throughout the testing lifecycle. As new systems, services, or misconfigurations are discovered, testers must continuously update their understanding of the target environment. This dynamic approach is essential in cloud-native infrastructures where assets can appear and disappear rapidly.
Scanning and enumeration have also become more adaptive. Instead of relying solely on broad automated scans, testers are expected to combine targeted scanning with contextual analysis. This means interpreting results in real time and adjusting strategies based on discovered vulnerabilities or defensive mechanisms.
Exploitation is now more closely tied to chaining vulnerabilities rather than isolated attacks. A single weakness may not be sufficient to gain meaningful access, so testers must think in terms of attack paths. This requires a deeper understanding of how systems interact and how different misconfigurations can be combined to escalate privileges or move laterally.
Reporting has also evolved beyond static documentation. PT0-003 emphasizes clear communication of technical findings in a way that aligns with business risk. This includes prioritizing vulnerabilities based on impact and likelihood, rather than simply listing them in order of discovery.
Advanced Reconnaissance Techniques in Modern Environments
Reconnaissance remains the foundation of penetration testing, but its scope has expanded significantly in PT0-003-aligned methodologies. Modern reconnaissance is no longer limited to passive information gathering or basic network scanning. Instead, it incorporates a combination of automated tools, manual investigation, and contextual analysis.
One of the most important shifts is the increased focus on external attack surface mapping. Organizations now have a much larger digital footprint due to cloud services, APIs, third-party integrations, and remote access systems. Identifying all exposed assets requires a combination of automated discovery tools and manual validation techniques.
Another key aspect of modern reconnaissance is metadata analysis. Attackers and testers alike often extract valuable information from publicly available sources such as domain records, certificate transparency logs, and exposed configuration files. These data points can reveal hidden infrastructure components or misconfigured services.
Social reconnaissance also plays an important role. This involves gathering information about organizational structure, employee roles, and technology stacks through publicly available information. While often overlooked, this data can be critical in planning realistic attack scenarios.
Active reconnaissance techniques have also become more refined. Instead of broad scanning that may trigger detection systems, testers often use targeted probes designed to minimize noise while maximizing information gain. This approach reflects the need to operate in environments with advanced monitoring and detection capabilities.
Exploitation Strategies in Complex Network Architectures
Exploitation in modern penetration testing is no longer a simple process of identifying a vulnerability and executing a payload. PT0-003 reflects the reality that modern systems are interconnected, layered, and protected by multiple defensive mechanisms. As a result, exploitation strategies must be carefully planned and executed.
One of the key concepts in modern exploitation is attack path analysis. Instead of focusing on individual vulnerabilities, testers analyze how multiple weaknesses can be combined to achieve a specific objective. This may involve moving from a low-privilege account to administrative access through a series of intermediate steps.
Privilege escalation remains a critical component of exploitation. However, modern systems often include additional safeguards that make escalation more challenging. This requires testers to identify subtle misconfigurations, such as insecure file permissions, weak service configurations, or improperly restricted system capabilities.
Lateral movement is another essential aspect of exploitation. Once access is gained to a single system, attackers often attempt to expand their control across the network. This requires an understanding of internal trust relationships, authentication mechanisms, and network segmentation weaknesses.
Modern exploitation also increasingly involves bypassing detection mechanisms. Security tools such as endpoint detection systems and behavioral analytics are designed to identify malicious activity. Testers must understand how these systems work in order to simulate realistic attack scenarios without being immediately blocked.
Post-Exploitation Activities and Persistence Mechanisms
Post-exploitation represents one of the most critical phases of penetration testing in PT0-003-aligned environments. Once initial access is achieved, the focus shifts toward understanding the extent of compromise and maintaining access for further analysis.
One of the primary objectives during post-exploitation is privilege escalation. This involves identifying ways to gain higher levels of access within a system or network. Common methods include exploiting misconfigured services, leveraging weak credentials, or abusing system utilities.
Another key aspect is data discovery and extraction. Testers must identify sensitive information within compromised systems, including configuration files, user data, and system credentials. This process helps organizations understand the potential impact of a real-world breach.
Persistence mechanisms are also a major focus. Attackers often attempt to maintain access even after initial vulnerabilities are patched. This may involve creating hidden user accounts, modifying startup processes, or leveraging scheduled tasks. Understanding these techniques helps testers evaluate long-term security resilience.
Credential harvesting is another important activity. Compromised systems often contain stored credentials that can be reused across other systems. Identifying and analyzing these credentials is critical for understanding the broader impact of a compromise.
Post-exploitation activities also include network mapping from the inside. Once inside a system, testers can gain a more accurate understanding of internal network structures, trust relationships, and security boundaries.
Modern Defense Evasion Techniques
As defensive technologies have become more sophisticated, attackers have developed increasingly advanced methods to avoid detection. PT0-003 reflects this evolution by emphasizing defense evasion techniques as part of penetration testing knowledge.
One common approach is the use of legitimate system tools for malicious purposes. Instead of introducing external malware, attackers leverage built-in utilities to perform actions such as file transfer, command execution, and network communication. This makes detection more difficult because activity appears legitimate.
Another important technique is traffic obfuscation. Attackers may encrypt or encode communications to avoid detection by network monitoring systems. This is particularly relevant in environments where deep packet inspection is used.
Timing-based evasion is also frequently used. Attackers may delay actions or execute them at irregular intervals to avoid triggering behavioral detection systems. This requires penetration testers to understand how timing affects detection thresholds.
Memory-based execution techniques are another advanced method used to avoid detection. Instead of writing malicious files to disk, attackers may execute code directly in memory. This reduces the likelihood of detection by traditional antivirus systems.
Understanding these techniques is essential for realistic penetration testing, as it allows testers to simulate advanced adversaries more accurately.
Risk Analysis and Security Prioritization
Penetration testing is not only about identifying vulnerabilities but also about understanding their impact. PT0-003 emphasizes the importance of risk analysis and prioritization in security assessments.
Not all vulnerabilities carry the same level of risk. Some may be easy to exploit but have limited impact, while others may be harder to exploit but result in significant compromise. Understanding this distinction is critical for effective reporting.
Risk analysis involves evaluating both the likelihood and impact of a vulnerability. Likelihood refers to how easily an attacker can exploit a weakness, while impact refers to the potential damage caused by successful exploitation.
Prioritization is especially important in large environments where hundreds or thousands of vulnerabilities may be identified. Security teams must focus on issues that pose the greatest risk to the organization.
Context also plays an important role in risk assessment. A vulnerability in a critical system may be more important than a similar issue in a non-essential system. Understanding business context is therefore essential for accurate prioritization.
PT0-003 reflects this by encouraging a more analytical approach to vulnerability assessment rather than purely technical evaluation.
Reporting and Communication in Professional Penetration Testing
Effective communication is a key component of penetration testing. PT0-003 emphasizes the importance of translating technical findings into clear, actionable insights for different audiences.
Technical reports must accurately describe vulnerabilities, exploitation methods, and potential impacts. However, they must also be structured in a way that is understandable to non-technical stakeholders. This often involves simplifying complex concepts without losing accuracy.
Executive summaries play a critical role in communication. These summaries provide high-level overviews of findings, focusing on business risk rather than technical detail. This allows decision-makers to understand the significance of vulnerabilities without needing deep technical knowledge.
Remediation guidance is another important aspect of reporting. Penetration testers are expected to provide recommendations for addressing identified issues. These recommendations must be practical, specific, and aligned with organizational capabilities.
Clear communication also involves prioritization of findings. Reports should highlight the most critical issues first, ensuring that attention is directed toward the most significant risks.
Continuous Learning and Adaptation in Penetration Testing Careers
The field of penetration testing is constantly evolving, and PT0-003 reflects the need for continuous learning. New technologies, attack methods, and defensive strategies emerge regularly, requiring professionals to stay up to date.
One of the most important aspects of career development in this field is adaptability. Penetration testers must be able to adjust their methodologies based on the environment they are assessing. This includes learning new tools, understanding emerging technologies, and staying informed about current threat trends.
Hands-on experience is also critical. Practical exposure to real or simulated environments helps develop the problem-solving skills required for effective penetration testing. This includes working with cloud platforms, scripting environments, and complex network architectures.
Collaboration is another important factor. Penetration testers often work alongside security analysts, developers, and system administrators. Understanding how to communicate effectively across teams is essential for successful outcomes.
The evolving nature of PT0-003 highlights that penetration testing is not a static discipline. It is a dynamic field that requires continuous growth, experimentation, and refinement of skills.
Conclusion
The transition from PT0-002 to PT0-003 represents far more than a routine certification update. It reflects a structural transformation in how penetration testing is defined, executed, and evaluated in modern cybersecurity ecosystems. Where earlier approaches focused heavily on traditional network boundaries and relatively static infrastructures, the updated framework aligns with today’s distributed, cloud-driven, and identity-centric environments. This shift is not cosmetic; it is a direct response to how real-world attacks are conducted and how organizations now operate digitally.
At its core, PT0-003 acknowledges that the attack surface has expanded dramatically. Modern enterprises no longer operate within isolated data centers. Instead, they rely on hybrid infrastructures that combine cloud platforms, SaaS applications, remote endpoints, APIs, and automation pipelines. Each of these components introduces unique vulnerabilities, and more importantly, new ways for attackers to chain weaknesses together. Penetration testers are therefore expected to think in terms of interconnected systems rather than isolated assets.
One of the most important outcomes of this evolution is the increased emphasis on cloud security. Cloud environments have become the backbone of digital transformation, but they also introduce complexity in configuration, identity management, and access control. PT0-003 places significant weight on understanding how misconfigurations in cloud platforms can lead to large-scale compromise. This includes issues such as excessive permissions, insecure storage configurations, and weak identity governance. The certification now expects candidates to understand not only how these flaws exist but also how they are exploited in real attack scenarios.
Another defining change is the shift toward identity as the primary security boundary. Traditional perimeter-based security models are no longer sufficient in environments where users access systems from multiple locations and devices. Identity and access management systems have become central to security enforcement, making them a primary target for attackers. PT0-003 reflects this reality by emphasizing credential-based attacks, privilege escalation, and session manipulation as core areas of study. Understanding how identity systems function, and how they fail, is now essential for any penetration tester.
The updated certification also highlights the growing importance of automation and scripting in modern security workflows. In large-scale environments, manual testing alone is no longer practical. Penetration testers must be able to leverage automation to perform reconnaissance, analyze vulnerabilities, and streamline exploitation processes. However, the focus is not on advanced software engineering. Instead, it is on practical application—understanding how scripts work, how they can be modified, and how they integrate into broader testing methodologies. This reflects real-world expectations where efficiency and scalability are critical.
Modern attack techniques also play a central role in the updated framework. PT0-003 emphasizes how attackers operate in today’s environments, including the use of living-off-the-land techniques, credential reuse, lateral movement, and defense evasion strategies. These methods are particularly relevant because they allow attackers to blend into normal system activity, making detection significantly more difficult. Penetration testers must therefore develop a deeper understanding of how legitimate tools and processes can be abused in sophisticated attack scenarios.
Web application and API security have also undergone a major expansion in scope. Modern applications are no longer monolithic systems; they are distributed across multiple services and heavily dependent on APIs for communication. This introduces a wide range of potential vulnerabilities, particularly in authentication, authorization, and data exposure. PT0-003 reflects this by requiring a more detailed understanding of API structures, request flows, and logic-based vulnerabilities. The ability to analyze how different components interact is now a fundamental skill rather than an advanced specialization.
Another significant aspect of the updated certification is its focus on Zero Trust principles. Security models are shifting toward continuous verification rather than implicit trust. This means every access request is evaluated based on identity, device posture, and contextual factors. From a penetration testing perspective, this introduces new challenges in identifying weak points within authentication flows and policy enforcement mechanisms. It also requires testers to think beyond traditional network boundaries and focus on identity-driven attack paths.
Physical security and social engineering considerations have also been expanded. While cybersecurity is often viewed as a purely technical discipline, real-world attacks frequently exploit human behavior and physical access points. PT0-003 acknowledges this by incorporating scenarios where attackers manipulate individuals or gain unauthorized physical access to systems. This reinforces the idea that effective security testing must consider both technical and human factors.
Perhaps one of the most important overarching themes in PT0-003 is realism. The certification is designed to reflect actual penetration testing environments rather than theoretical constructs. This means candidates are expected to understand how systems behave under real attack conditions, including detection mechanisms, defensive countermeasures, and operational constraints. The focus is on practical thinking, adaptability, and problem-solving rather than memorization of isolated concepts.
Risk analysis and communication also play a central role in the updated framework. Identifying vulnerabilities is only one part of the process; understanding their impact and communicating them effectively is equally important. Penetration testers must be able to translate technical findings into business-relevant insights. This includes prioritizing risks based on impact, explaining exploitation paths clearly, and providing actionable remediation guidance. In modern organizations, this communication layer is often what determines the value of a security assessment.
From a career perspective, PT0-003 aligns more closely with current industry expectations. Employers are increasingly looking for professionals who can operate in complex, cloud-based environments and understand modern attack methodologies. The updated certification reflects these expectations by emphasizing practical skills that are directly applicable to real-world roles. This includes not only technical expertise but also analytical thinking, adaptability, and communication ability.
Ultimately, the shift from PT0-002 to PT0-003 represents a broader evolution in cybersecurity itself. The field has moved away from static, perimeter-based models toward dynamic, identity-driven, and cloud-integrated systems. Attackers have adapted quickly to these changes, and defensive strategies must evolve at the same pace. Penetration testing sits at the center of this evolution, serving as a critical function for identifying weaknesses before they can be exploited in real environments.
PT0-003 captures this reality by redefining what it means to be a penetration tester in today’s world. It emphasizes not just technical knowledge, but also strategic thinking, adaptability, and real-world application. For professionals entering or advancing in the field, it represents a more accurate reflection of the skills required to succeed in modern cybersecurity roles.