Microsoft 365 has become one of the most widely adopted enterprise productivity ecosystems in the world, forming the backbone of communication, collaboration, and document management for organizations of all sizes. From email and file sharing to real-time collaboration and cloud storage, it integrates multiple services into a single environment that supports modern digital workplaces. As adoption grows, so does the complexity of securing the vast amount of data generated daily within this ecosystem.
This increasing reliance on cloud-based productivity platforms has created a shift in how organizations approach security. Traditional perimeter-based models, which focused on securing the network boundary, are no longer sufficient. Data now moves fluidly between devices, locations, and users, making it necessary to focus on securing the data itself rather than just the infrastructure it resides on. This shift has given rise to specialized roles centered on data governance, compliance, and information protection.
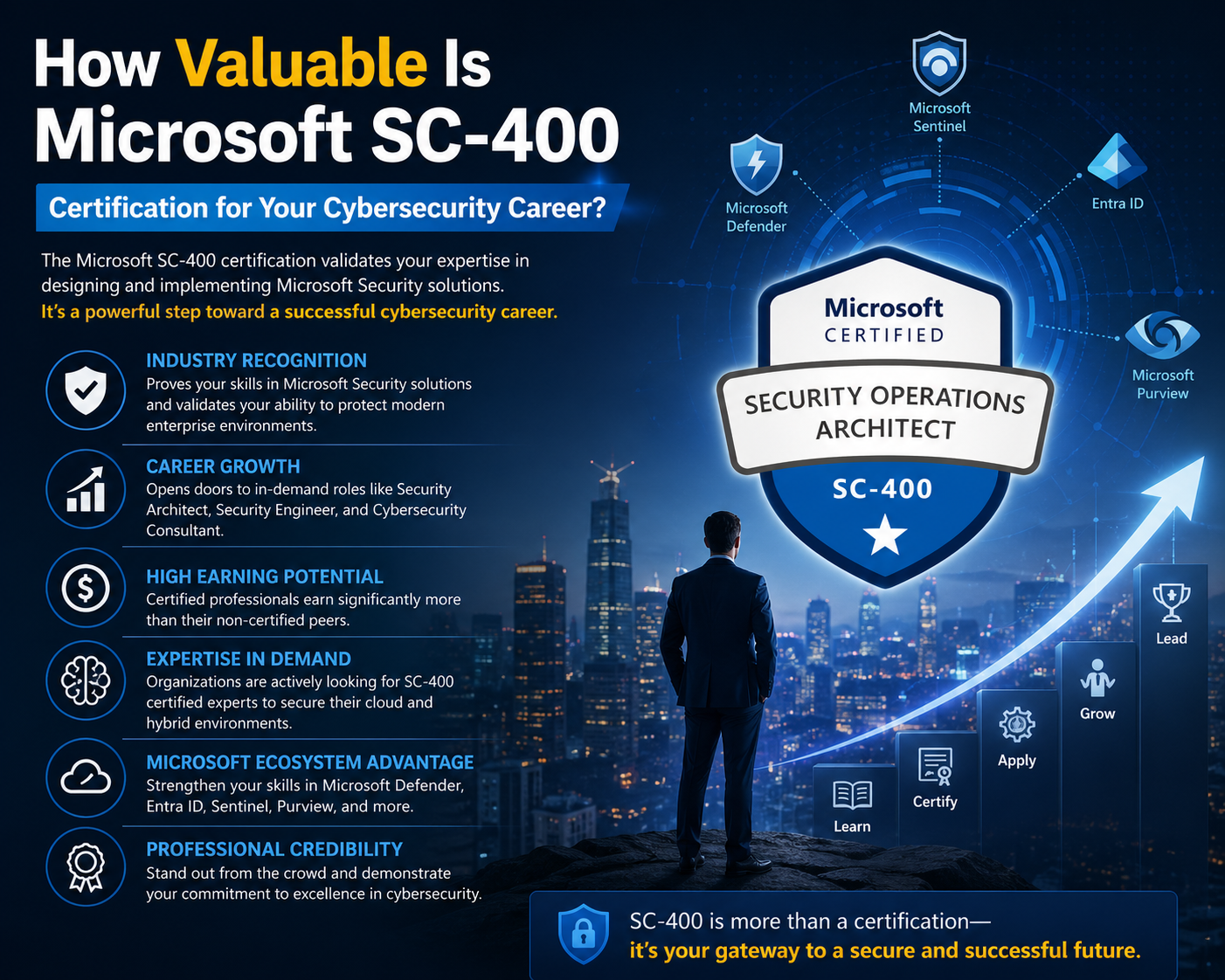
The SC-400 certification is positioned directly within this evolving landscape. It focuses on developing professionals who can manage information protection and compliance within Microsoft 365 environments. Rather than concentrating on general cybersecurity principles, it specifically targets the governance and protection of organizational data. This makes it highly relevant in environments where regulatory compliance, data privacy, and internal governance policies are critical business requirements.
Role of Information Protection in Modern Enterprises
In modern enterprises, data is not only an operational asset but also a regulatory responsibility. Organizations must ensure that sensitive information is properly classified, protected, and retained according to legal and internal requirements. Failure to manage this properly can lead to data breaches, compliance violations, and financial penalties.
Information protection involves identifying sensitive data and applying appropriate controls to prevent unauthorized access or misuse. This includes protecting personal data, financial records, intellectual property, and confidential business information. Within Microsoft 365 environments, this responsibility becomes even more significant due to the scale and diversity of data being processed across multiple applications.
The SC-400 certification prepares professionals to handle these responsibilities by teaching them how to implement structured data protection strategies. This includes classifying data based on sensitivity, applying labels that define handling requirements, and enforcing policies that control how data is accessed and shared. These capabilities ensure that organizations maintain control over their information regardless of where it is stored or how it is accessed.
Core Responsibilities of an Information Protection Administrator
An Information Protection Administrator operates at the intersection of technology, policy, and compliance. This role requires a deep understanding of how data flows through an organization and how it can be protected at each stage of its lifecycle. Rather than focusing on infrastructure maintenance or application development, the role centers on ensuring that data is governed and secured according to organizational and regulatory standards.
One of the primary responsibilities is implementing data classification frameworks. This involves defining categories for data based on its sensitivity and importance. For example, data may be classified as public, internal, confidential, or highly sensitive. Each classification level determines how the data should be handled and what restrictions should be applied.
Another key responsibility is managing sensitivity labels. Sensitivity labels are metadata tags applied to data that dictate how it should be protected. These labels can enforce encryption, restrict access, and control sharing permissions. By applying these labels consistently across an organization, administrators ensure that data protection policies are automatically enforced without relying on manual intervention.
In addition to classification and labeling, Information Protection Administrators are responsible for configuring data loss prevention policies. These policies help prevent sensitive information from being shared outside the organization or accessed by unauthorized users. They can detect patterns such as credit card numbers, personal identification data, or confidential business information and take automated actions when violations occur.
Understanding Data Classification and Sensitivity Labels
Data classification is a foundational concept in information protection. It involves categorizing data based on its level of sensitivity and the potential impact of unauthorized disclosure. Without proper classification, organizations cannot effectively apply security controls or compliance measures.
Within Microsoft 365 environments, classification can be both manual and automated. Manual classification relies on users or administrators assigning labels based on their understanding of the data. Automated classification uses predefined rules and patterns to identify sensitive information and apply labels accordingly. This dual approach ensures both flexibility and scalability in large enterprise environments.
Sensitivity labels extend the concept of classification by enforcing protection policies based on the assigned category. For instance, a document labeled as highly confidential may automatically be encrypted and restricted to specific users or groups. These labels travel with the data, ensuring that protection remains intact even when the data is shared externally.
The SC-400 certification emphasizes the practical implementation of these concepts. Professionals are trained to design classification schemes that align with organizational needs and regulatory requirements. They also learn how to configure labeling policies that ensure consistent application across all Microsoft 365 services.
Data Loss Prevention and Risk Mitigation Strategies
Data loss prevention is a critical component of modern information security strategies. It focuses on identifying and preventing the unauthorized transmission or exposure of sensitive data. This includes both intentional and accidental data leaks.
In enterprise environments, data loss can occur in many ways. Employees may accidentally send confidential information to external recipients, upload sensitive files to unsecured platforms, or share data through unauthorized channels. Without proper controls in place, these actions can result in significant security incidents.
Data loss prevention policies help mitigate these risks by monitoring data activity and enforcing predefined rules. These policies can detect sensitive information based on content patterns, keywords, or classifications. When a potential violation is detected, the system can take actions such as blocking the transmission, alerting administrators, or notifying the user.
The SC-400 certification provides in-depth coverage of how to design and implement these policies within Microsoft 365. It emphasizes the importance of balancing security with usability, ensuring that protective measures do not disrupt legitimate business activities.
Information Governance and Lifecycle Management
Information governance is another critical area covered in the SC-400 certification. It focuses on managing the entire lifecycle of data, from creation to deletion. This includes defining how long data should be retained, when it should be archived, and when it should be permanently removed.
Effective governance ensures that organizations comply with legal and regulatory requirements while also maintaining operational efficiency. Retaining unnecessary data can increase storage costs and create security risks, while deleting data too early can lead to compliance violations.
Retention policies are a key component of information governance. These policies define how long specific types of data should be preserved and what actions should be taken after the retention period expires. For example, certain financial records may need to be retained for several years, while temporary communication data may only need to be kept for a short period.
The SC-400 certification teaches professionals how to design and implement these policies effectively. It also covers how to apply retention labels that automate the governance process across different types of content.
Legal Compliance and Data Preservation Requirements
Organizations operating in regulated industries must adhere to strict legal and compliance requirements regarding data handling and preservation. These requirements often vary depending on industry standards, geographic location, and organizational policies.
One important aspect of compliance is the ability to preserve data during legal proceedings. This is where concepts such as litigation holds become important. A litigation hold ensures that relevant data is preserved and cannot be altered or deleted while legal investigations are ongoing.
Another important concept is electronic discovery, which involves identifying and retrieving data that may be relevant to legal cases or regulatory audits. This process must be efficient, accurate, and secure to ensure compliance with legal obligations.
The SC-400 certification guides how to implement these mechanisms within Microsoft 365. It emphasizes the importance of maintaining data integrity while ensuring that organizations can respond effectively to legal and regulatory requests.
Integration of Microsoft 365 Security and Compliance Tools
Microsoft 365 provides a wide range of integrated tools designed to support information protection and compliance. These tools work together to create a unified security framework that spans multiple applications and services.
The SC-400 certification focuses on how to configure and manage these tools effectively. This includes understanding how different services interact and how policies can be applied consistently across the environment. By leveraging these integrated capabilities, organizations can create a cohesive security strategy that reduces complexity and improves efficiency.
Automation plays a significant role in this integration. Automated policies ensure that security and compliance measures are consistently enforced without requiring manual intervention. This reduces the risk of human error and ensures that policies remain effective at scale.
Importance of SC-400 in Today’s Cybersecurity Environment
The relevance of the SC-400 certification is closely tied to the increasing importance of data protection in modern cybersecurity strategies. As organizations continue to adopt cloud-based services and remote work models, the volume and complexity of data continue to grow.
This growth has made data protection a critical priority for organizations across industries. Regulatory frameworks are becoming more stringent, and the consequences of data breaches are becoming more severe. As a result, there is a growing demand for professionals who can manage data governance and compliance effectively.
The SC-400 certification addresses this demand by providing specialized knowledge in information protection. It equips professionals with the skills needed to design, implement, and manage data protection strategies in complex enterprise environments.
Skill Development and Professional Relevance
From a career perspective, the SC-400 certification contributes to both technical skill development and professional credibility. It demonstrates an ability to handle complex data protection challenges and implement effective governance strategies.
Professionals who pursue this certification often work in roles that require collaboration across multiple departments. This includes working with IT teams, compliance officers, legal departments, and business stakeholders. The ability to translate technical requirements into practical solutions is a key skill developed through this certification.
The certification also encourages a strategic approach to security. Rather than focusing solely on technical configurations, it emphasizes the importance of aligning security measures with business objectives and regulatory requirements.
Cost Structure and Exam Framework of SC-400 Certification
The SC-400 certification exam is designed with a structure that evaluates both theoretical understanding and applied technical capability within Microsoft 365 security and compliance environments. Unlike entry-level certifications that focus heavily on memorization, this exam emphasizes real-world scenarios where candidates must interpret requirements and implement appropriate information protection solutions.
The cost of the exam is generally fixed across most regions, although minor variations may occur depending on local taxation or testing provider policies. The financial investment is positioned at a mid-range level compared to other cybersecurity certifications, making it accessible to professionals who are already working in IT or security-related roles. However, the value of the certification is not measured solely by its cost, but by the depth of knowledge it validates.
The exam duration typically spans around two hours, during which candidates are required to answer a mix of question formats. These formats include scenario-based questions, multiple-choice questions, case studies, and configuration-based problem-solving tasks. This variety ensures that candidates are tested on both conceptual understanding and practical application.
A significant aspect of the exam is its focus on Microsoft 365 compliance tools and security frameworks. Candidates are expected to understand how to configure policies, manage data protection settings, and interpret organizational requirements. The questions are often structured in a way that simulates real enterprise environments, requiring careful analysis before selecting an answer.
The passing score is determined through a scaled scoring system rather than a simple percentage. This means that performance is evaluated based on weighted question difficulty. Candidates must demonstrate competence across all major domains rather than excelling in only one area.
Detailed Breakdown of Exam Domains and Knowledge Areas
The SC-400 exam is divided into multiple domains, each representing a core aspect of information protection and compliance within Microsoft 365. These domains collectively cover the full lifecycle of data governance, from classification to enforcement and monitoring.
One of the primary domains focuses on implementing information protection. This area emphasizes the identification and classification of sensitive data. Candidates are expected to understand how to create classification policies that automatically detect sensitive content. This includes recognizing patterns such as financial data, personal identifiers, and confidential business information.
Within this domain, sensitivity labeling plays a central role. Candidates must understand how labels are created, configured, and applied across different types of content. These labels determine how data is handled, including whether it is encrypted, restricted, or shared externally. The ability to design effective labeling strategies is essential for maintaining consistent data protection across an organization.
Another important component is the use of keyword dictionaries and custom classifiers. These tools allow organizations to identify specific types of sensitive information based on defined criteria. For example, a company may create a dictionary of internal project names or proprietary terms that should not be shared outside the organization. The certification tests the ability to configure and manage these classification tools effectively.
Document fingerprinting is also included within this domain. This technique allows organizations to identify sensitive documents based on their structure and content rather than just keywords. It is particularly useful for detecting variations of confidential files that may have been modified or partially copied.
Data Loss Prevention Architecture and Enforcement Mechanisms
The second major domain of the SC-400 certification focuses on data loss prevention strategies. This area is critical in modern cybersecurity environments where data movement is constant and often difficult to control.
Data loss prevention policies are designed to detect and prevent the unauthorized sharing of sensitive information. These policies operate across multiple Microsoft 365 services, including email, cloud storage, and collaboration platforms. The goal is to ensure that sensitive data does not leave the organization without proper authorization.
Candidates are expected to understand how to configure DLP policies that align with organizational requirements. This includes defining conditions under which data should be restricted, monitored, or blocked. Policies can be based on content types, user roles, or specific activities.
Endpoint monitoring is another key aspect of this domain. It involves tracking user activities on devices to detect potential data leakage risks. For example, copying sensitive files to external storage devices or uploading them to unauthorized cloud services can trigger alerts or enforcement actions.
Microsoft Cloud App Security, often integrated into DLP strategies, provides additional visibility into cloud application usage. It allows administrators to monitor how data is accessed and shared across different applications. This helps identify risky behavior and enforce compliance policies more effectively.
The certification also covers the implementation of policy tips and user notifications. These mechanisms inform users when they are about to perform actions that may violate organizational policies. By providing real-time feedback, organizations can reduce accidental data loss and improve overall compliance awareness.
Information Governance and Regulatory Alignment
Information governance represents a structured approach to managing data throughout its lifecycle. This includes defining how data is created, stored, accessed, archived, and deleted. Effective governance ensures that data is managed consistently and in accordance with legal and organizational requirements.
The SC-400 certification places strong emphasis on retention policies and retention labels. These tools allow organizations to define how long specific types of data should be preserved. Retention policies can be applied broadly across entire systems, while retention labels provide more granular control at the document or item level.
Retention strategies are often driven by regulatory requirements. Different industries have varying obligations regarding data retention. For example, financial institutions may be required to retain transaction records for extended periods, while healthcare organizations must comply with strict patient data preservation rules.
The certification also covers the concept of record management. Once data is classified as a record, it becomes immutable, meaning it cannot be modified or deleted until the retention period expires. This ensures data integrity and supports compliance with legal standards.
Archiving strategies are another important aspect of governance. Archiving involves moving infrequently accessed data to long-term storage while maintaining accessibility when needed. This helps optimize storage resources and improve system performance.
Legal Hold and eDiscovery Implementation
Legal compliance is a critical responsibility for organizations operating in regulated environments. The SC-400 certification addresses this by covering legal hold and electronic discovery processes.
A legal hold ensures that relevant data is preserved during legal proceedings or investigations. When a legal hold is applied, data cannot be deleted or modified, even if retention policies would normally allow it. This ensures that evidence remains intact and available for review.
Electronic discovery, often referred to as eDiscovery, involves identifying, collecting, and analyzing data for legal purposes. This process is essential in legal cases where organizations are required to produce specific information. Efficient eDiscovery processes reduce the time and effort required to respond to legal requests.
The certification teaches how to configure eDiscovery cases, define search parameters, and export relevant data. It also emphasizes the importance of maintaining data integrity throughout the process.
Microsoft 365 Security Architecture and Compliance Integration
Microsoft 365 provides a comprehensive security and compliance framework that integrates multiple tools and services. These tools work together to provide a unified approach to data protection.
The SC-400 certification focuses on understanding how these components interact. This includes services related to information protection, compliance management, identity security, and threat detection.
One of the key advantages of this integrated approach is centralized policy management. Administrators can define policies in one location and apply them across multiple services. This reduces complexity and ensures consistency in security enforcement.
Automation plays a significant role in this architecture. Automated workflows allow organizations to enforce policies without manual intervention. This improves efficiency and reduces the risk of configuration errors.
Practical Application of SC-400 Skills in Enterprise Environments
The skills developed through SC-400 certification are highly applicable in real-world enterprise environments. Information Protection Administrators are often responsible for designing and implementing data security strategies that align with organizational goals.
In practice, this involves working closely with IT teams, compliance officers, and business stakeholders. Administrators must understand business requirements and translate them into technical configurations. This requires both technical expertise and strong communication skills.
For example, a business may require that customer data be protected with strict access controls. The Information Protection Administrator would design sensitivity labels, configure access policies, and implement monitoring systems to ensure compliance.
Another practical application involves incident response. When a data breach or policy violation occurs, administrators must quickly identify the source, assess the impact, and implement corrective actions. This requires familiarity with monitoring tools and investigative processes.
Enterprise Demand and Industry Adoption Trends
The demand for professionals with expertise in information protection continues to grow across industries. As organizations increasingly adopt cloud-based solutions, the need for structured data governance becomes more critical.
Industries such as finance, healthcare, government, and legal services place a particularly strong emphasis on data protection and compliance. These sectors handle highly sensitive information and are subject to strict regulatory requirements.
The SC-400 certification aligns with these industry needs by providing a standardized framework for managing data protection in Microsoft 365 environments. This makes certified professionals valuable assets in organizations that prioritize compliance and security.
Another trend influencing demand is the rise of hybrid work environments. With employees accessing corporate data from multiple locations and devices, traditional security models are no longer sufficient. Information protection strategies must adapt to this new reality by focusing on data-centric security.
Strategic Importance of Data Protection Roles
Data protection roles are becoming increasingly strategic within organizations. Rather than being purely technical positions, they now involve significant input into business decisions and risk management strategies.
Information Protection Administrators contribute to defining how data is used, shared, and secured across the organization. Their decisions directly impact operational efficiency, regulatory compliance, and risk exposure.
This strategic importance elevates the value of certifications like SC-400. They not only validate technical skills but also demonstrate an understanding of how data protection aligns with broader organizational objectives.
Skill Progression and Career Development Pathways
The SC-400 certification often serves as a stepping stone for more advanced roles in cybersecurity and compliance. It provides foundational knowledge that can be expanded into specialized areas such as cloud security architecture, identity management, or advanced threat protection.
Professionals who obtain this certification often continue to build expertise in related domains. This progression allows them to take on more complex responsibilities and transition into senior-level positions.
The certification also supports cross-functional career development. Individuals with SC-400 knowledge can work in roles that intersect with legal, compliance, and business strategy functions.
Real-World Value of SC-400 in Modern Cybersecurity Ecosystems
The SC-400 certification has practical relevance that extends far beyond theoretical knowledge. In modern cybersecurity ecosystems, organizations are dealing with increasingly complex data environments where information flows across cloud services, endpoints, and third-party applications. This creates a constant need for structured governance and protection mechanisms that can adapt to dynamic usage patterns.
In real-world enterprise settings, data is no longer confined to a single system or department. Employees collaborate across regions, share documents externally, and access corporate resources from multiple devices. This distributed environment introduces significant risks, particularly around unauthorized access, accidental data leaks, and regulatory non-compliance. The SC-400 certification prepares professionals to address these challenges by equipping them with the ability to implement centralized information protection strategies.
One of the key real-world applications of SC-400 skills is the enforcement of consistent data classification across an organization. Without standardized classification, different departments may handle similar data in inconsistent ways, leading to security gaps. By implementing unified classification policies, organizations can ensure that sensitive data is identified and protected regardless of where it is created or stored.
Another important application is in securing collaboration platforms. Modern workplaces rely heavily on tools that allow real-time communication and document sharing. While these tools improve productivity, they also increase the risk of sensitive information being shared with unintended recipients. Information Protection Administrators use SC-400 skills to configure restrictions, apply sensitivity labels, and monitor data flows within these collaboration environments.
Data Protection Strategy Design in Enterprise Environments
Designing a data protection strategy is one of the most critical responsibilities associated with SC-400 expertise. This process involves analyzing organizational requirements, identifying data risks, and implementing appropriate technical controls.
A well-designed data protection strategy begins with understanding data classification needs. Not all data within an organization carries the same level of sensitivity. Some information is intended for public use, while other data may contain confidential or regulated content. Identifying these categories is the first step in building an effective protection framework.
Once classification requirements are defined, the next step involves mapping these classifications to sensitivity labels and protection policies. These labels determine how data behaves across the Microsoft 365 environment. For example, highly sensitive data may require encryption, restricted sharing, and watermarking, while less sensitive data may have fewer restrictions.
Another important aspect of strategy design is scalability. As organizations grow, the volume of data increases significantly. A manual approach to data protection becomes unsustainable at scale. SC-400 principles emphasize automation to ensure that classification and protection policies are applied consistently across large datasets without requiring constant human intervention.
Risk assessment is also a fundamental component of strategy design. Organizations must evaluate potential threats to their data, including both internal and external risks. Internal risks may include accidental data sharing or misuse of access privileges, while external risks often involve cyberattacks or unauthorized access attempts. Understanding these risks allows administrators to design targeted protection measures.
Advanced Sensitivity Labeling Implementation Techniques
Sensitivity labeling is one of the most powerful mechanisms within Microsoft 365 for enforcing data protection policies. It allows organizations to classify and control data based on its level of sensitivity, ensuring that appropriate safeguards are automatically applied.
In advanced implementations, sensitivity labels are not limited to simple classification. They can trigger a wide range of protective actions, including encryption, access restrictions, content marking, and external sharing limitations. These actions are dynamically applied based on the label assigned to the data.
One advanced technique involves hierarchical labeling structures. In this approach, labels are organized in tiers that reflect increasing levels of sensitivity. For example, a basic label may apply minimal restrictions, while higher-level labels enforce stricter controls. This hierarchical structure simplifies policy management and ensures consistency across the organization.
Another advanced concept is automatic labeling based on content analysis. Instead of relying solely on user input, systems can analyze document content and automatically assign appropriate labels. This reduces the risk of human error and ensures that sensitive data is consistently identified and protected.
Integration with other Microsoft 365 services enhances the effectiveness of sensitivity labeling. For example, labels can be enforced across email, document storage, and collaboration tools, ensuring that protection remains consistent regardless of where the data is accessed.
Enterprise Data Loss Prevention Optimization Strategies
Data loss prevention strategies in large organizations require careful optimization to balance security and usability. Overly restrictive policies can disrupt business operations, while weak policies may leave sensitive data exposed.
One optimization strategy involves defining granular policy conditions. Instead of applying broad restrictions, organizations can tailor policies based on specific data types, user roles, or business contexts. This ensures that protection measures are relevant and minimally intrusive.
Another important optimization approach is policy tuning. Data loss prevention systems often generate alerts or block actions based on predefined rules. However, these rules may need adjustment over time to reduce false positives and improve accuracy. Continuous monitoring and refinement of policies help achieve this balance.
User education also plays a significant role in optimizing data loss prevention. When users understand why certain restrictions are in place, they are more likely to comply with policies and avoid risky behavior. SC-400 knowledge emphasizes the importance of combining technical controls with awareness strategies.
Endpoint integration is another optimization area. By extending data loss prevention controls to user devices, organizations gain visibility into local activities that may not be captured by cloud-based monitoring alone. This creates a more comprehensive security posture.
Regulatory Compliance Framework Alignment
Organizations operating in regulated industries must align their data protection strategies with specific legal and regulatory frameworks. These frameworks define how data must be handled, stored, and protected.
The SC-400 certification provides knowledge that supports this alignment by teaching how to implement compliance controls within Microsoft 365 environments. These controls help organizations meet requirements related to data privacy, retention, and access management.
Regulatory compliance often involves multiple overlapping requirements. For example, an organization may need to comply with data protection laws, industry-specific regulations, and internal governance policies simultaneously. Managing these requirements manually can be complex, which is why automated compliance tools are essential.
Retention management plays a key role in regulatory alignment. Different regulations may require data to be retained for specific periods. SC-400 skills enable professionals to configure retention policies that automatically enforce these requirements across different types of data.
Audit readiness is another critical aspect of compliance. Organizations must be able to demonstrate that they are properly managing and protecting data. This requires detailed logging, reporting, and monitoring capabilities. SC-400 concepts include configuring systems that provide visibility into data activities and policy enforcement actions.
Cloud Security Integration and Shared Responsibility Model
Cloud environments operate under a shared responsibility model, where security responsibilities are divided between the service provider and the organization using the service. Understanding this model is essential for effective data protection.
In Microsoft 365 environments, the provider is responsible for securing the underlying infrastructure, while organizations are responsible for managing their data, identities, and access policies. The SC-400 certification focuses on this organizational responsibility layer.
Data protection within this model requires careful configuration of security policies. Organizations must ensure that their data is properly classified, access is controlled, and usage is monitored. Failure to manage these responsibilities can lead to security gaps.
Cloud integration also introduces additional complexity due to the use of third-party applications and services. Data may flow between multiple systems, each with its own security requirements. SC-400 principles help professionals maintain consistent protection across these environments.
Automation and Policy-Driven Security Enforcement
Automation is a key theme in modern information protection strategies. Manual enforcement of security policies is not scalable in large enterprise environments, especially when dealing with high volumes of data.
Policy-driven security enforcement allows organizations to define rules that are automatically applied across systems. These rules can govern how data is classified, labeled, shared, and retained. Once configured, they operate continuously without requiring manual intervention.
Automation reduces the risk of human error, which is one of the leading causes of data breaches. It also improves efficiency by eliminating the need for repetitive administrative tasks.
Advanced automation scenarios include dynamic policy adjustment based on user behavior or risk levels. For example, if unusual activity is detected, additional restrictions can be automatically applied to protect sensitive data.
Incident Response and Data Breach Mitigation
Despite strong preventive measures, security incidents can still occur. The SC-400 certification includes knowledge related to incident response and data breach mitigation.
Incident response involves identifying, analyzing, and containing security incidents. In the context of data protection, this may include investigating unauthorized data access or identifying sources of data leakage.
Effective incident response requires detailed monitoring and logging capabilities. Administrators must be able to trace data activity across systems to understand how an incident occurred.
Mitigation strategies focus on minimizing the impact of security incidents. This may involve revoking access, applying additional restrictions, or restoring data integrity.
Organizational Impact of Information Protection Roles
Information protection roles have a significant impact on organizational structure and decision-making processes. These roles are not limited to technical execution but also contribute to strategic planning.
Professionals in these roles often collaborate with leadership teams to define data governance policies. Their input helps shape how data is managed across the organization and ensures that security considerations are integrated into business decisions.
This organizational influence highlights the importance of certifications like SC-400. They provide not only technical knowledge but also a framework for understanding how data protection aligns with business objectives.
Long-Term Evolution of Data Protection Practices
Data protection practices continue to evolve as technology advances and threats become more sophisticated. The SC-400 certification reflects current industry standards but also prepares professionals for ongoing changes in the cybersecurity landscape.
Future trends include increased automation, greater reliance on artificial intelligence for threat detection, and more granular control over data access. Organizations will continue to move toward data-centric security models that prioritize protection at the information level rather than the infrastructure level.
As these trends develop, the skills associated with SC-400 will remain highly relevant. Professionals who understand information protection principles will be well-positioned to adapt to new technologies and security challenges.
Final Perspective on SC-400 Knowledge Application
The knowledge gained through SC-400 certification is applicable across a wide range of real-world scenarios. From configuring data protection policies to managing compliance frameworks, the skills developed are directly aligned with modern enterprise needs.
Organizations continue to prioritize data security as a core business function rather than a secondary technical concern. This shift has elevated the importance of roles focused on information protection and governance.
SC-400 expertise enables professionals to contribute meaningfully to this evolving landscape by ensuring that data is protected, compliant, and properly managed throughout its lifecycle.
Conclusion
The SC-400 certification sits within a highly specialized segment of cybersecurity that focuses on information protection, data governance, and compliance enforcement within Microsoft 365 environments. Its value is best understood not in isolation but within the broader context of how modern organizations operate, store, and secure data. As enterprises continue to expand their reliance on cloud-based collaboration platforms, the importance of structured data governance frameworks becomes increasingly critical. SC-400 addresses this need by equipping professionals with the ability to manage sensitive information throughout its entire lifecycle, from creation and classification to retention and controlled deletion.
In practical enterprise environments, data is one of the most valuable and vulnerable assets. It is constantly being generated, modified, and shared across multiple platforms and devices. Without structured governance, this fluid movement of data introduces significant risks, including unauthorized disclosure, accidental leakage, and regulatory non-compliance. The SC-400 certification provides a framework for mitigating these risks through standardized classification systems, sensitivity labeling mechanisms, and policy-driven enforcement models. These components collectively ensure that data remains protected regardless of where it resides or how it is accessed.
The relevance of SC-400 becomes even more apparent when examining the increasing complexity of regulatory requirements. Organizations are subject to a growing number of data protection laws and compliance standards that vary across industries and geographic regions. These regulations often require strict control over how data is stored, accessed, and retained. SC-400 knowledge enables professionals to translate these regulatory obligations into actionable technical configurations within Microsoft 365. This includes implementing retention policies, managing legal holds, and ensuring that audit requirements can be met efficiently. In this sense, the certification acts as a bridge between legal compliance and technical execution.
Another significant dimension of SC-400 value lies in its alignment with modern security architecture principles. Traditional security models focused heavily on perimeter defense, where the primary goal was to secure the network boundary. However, this approach has become less effective in environments where cloud computing, remote work, and mobile access are standard. Modern security strategies emphasize data-centric protection, where security controls are applied directly to the information itself rather than the infrastructure surrounding it. SC-400 aligns closely with this model by focusing on classification, labeling, and policy enforcement at the data level. This ensures that protection remains consistent even when data moves outside traditional organizational boundaries.
The certification also plays a critical role in supporting automation-driven security operations. In large-scale enterprise environments, manual enforcement of data protection policies is neither efficient nor reliable. The volume of data and the speed at which it moves across systems make automation essential. SC-400 concepts emphasize the use of automated classification, labeling, and policy enforcement to ensure consistent protection without requiring constant administrative intervention. This reduces operational overhead while improving accuracy and reducing the likelihood of human error, which is often a contributing factor in data security incidents.
From an operational perspective, the skills associated with SC-400 contribute directly to improved organizational resilience. Data breaches and compliance violations can have significant financial, legal, and reputational consequences. By implementing structured information protection strategies, organizations can reduce their exposure to these risks. SC-400-trained professionals are able to design systems that detect sensitive data, prevent unauthorized sharing, and monitor user activity for potential policy violations. These capabilities contribute to a proactive security posture, where risks are addressed before they escalate into incidents.
The certification also supports cross-functional collaboration within organizations. Information protection is not solely an IT responsibility; it involves coordination between legal teams, compliance officers, business stakeholders, and technical administrators. SC-400 professionals often act as intermediaries who translate business requirements into technical policies. This requires not only technical proficiency but also an understanding of organizational objectives and regulatory constraints. As a result, individuals with SC-400 expertise are often involved in strategic decision-making processes related to data governance and risk management.
In terms of long-term professional relevance, SC-400 provides a foundation for career development in specialized areas of cybersecurity and compliance. The knowledge gained through this certification can be extended into broader domains such as cloud security architecture, identity governance, and advanced threat management. It also supports progression into roles that require a deeper understanding of enterprise risk frameworks and regulatory compliance strategies. As organizations continue to prioritize data protection, professionals with expertise in this area are likely to remain in high demand.
The evolving nature of cybersecurity threats further reinforces the importance of SC-400-related skills. Attackers are increasingly targeting data rather than just systems or networks. This includes attempts to exfiltrate sensitive information, exploit misconfigured access controls, and leverage human error to gain unauthorized access. SC-400 principles directly address these threats by focusing on controlling how data is classified, accessed, and shared. This data-centric approach provides a more resilient defense model that adapts to modern threat landscapes.
Another important aspect of SC-400 value is its contribution to organizational efficiency. While security and compliance are often viewed as constraints, effective implementation can actually improve operational workflows. For example, automated labeling and retention policies reduce the need for manual data management tasks. This allows employees to focus on core business activities rather than administrative compliance requirements. Additionally, consistent data governance reduces confusion around data handling practices, leading to more streamlined collaboration across departments.
The certification also supports scalability in growing organizations. As businesses expand, their data environments become more complex and distributed. Without standardized governance frameworks, managing this complexity becomes increasingly difficult. SC-400 provides structured methodologies for maintaining control over data at scale. This includes centralized policy management, automated enforcement mechanisms, and consistent classification systems that apply across all organizational units.
In a broader strategic context, SC-400 contributes to building a culture of accountability around data usage. When employees understand how data should be classified and protected, they are more likely to follow secure practices. This cultural shift is an important component of long-term security success. Technical controls alone are not sufficient; organizational awareness and behavioral alignment are equally important. SC-400 frameworks support this by embedding security principles directly into everyday workflows.
Ultimately, the value of SC-400 lies in its ability to unify technical implementation, regulatory compliance, and organizational strategy into a cohesive data protection approach. It provides professionals with the tools and knowledge required to manage sensitive information effectively in complex, cloud-driven environments. As data continues to grow in volume, velocity, and importance, the need for structured information protection will only increase. SC-400 remains a relevant and practical framework for addressing these evolving challenges in a systematic and scalable way.