The modern digital environment is defined by constant connectivity, where information flows continuously between devices, systems, and users across the world. This level of interconnection is not accidental; it is the result of decades of development in computer networking. Every digital interaction, whether it involves sending a message, watching a video, or accessing a remote application, depends on structured communication systems that operate silently in the background.
Networking forms the operational foundation of nearly all modern technologies. It enables communication between systems that may differ in design, location, or purpose. Without networking, digital tools would function only as isolated units, severely limiting their usefulness. The ability to share data efficiently has transformed industries such as finance, healthcare, education, entertainment, and manufacturing, creating new possibilities for innovation and global collaboration.
One of the defining characteristics of networking is its scalability. It supports small environments such as home networks as well as massive infrastructures that span continents. This adaptability makes networking a core element of technological ecosystems, allowing systems to grow and evolve without losing functionality. As digital demands increase, networking continues to expand in complexity, incorporating new technologies and methods to handle growing volumes of data.
The significance of networking is also evident in how deeply it is integrated into everyday life. Activities that appear simple on the surface often involve multiple layers of communication between servers, databases, and end-user devices. This hidden complexity ensures that digital services remain fast, reliable, and accessible.
Foundations of Computer Networking
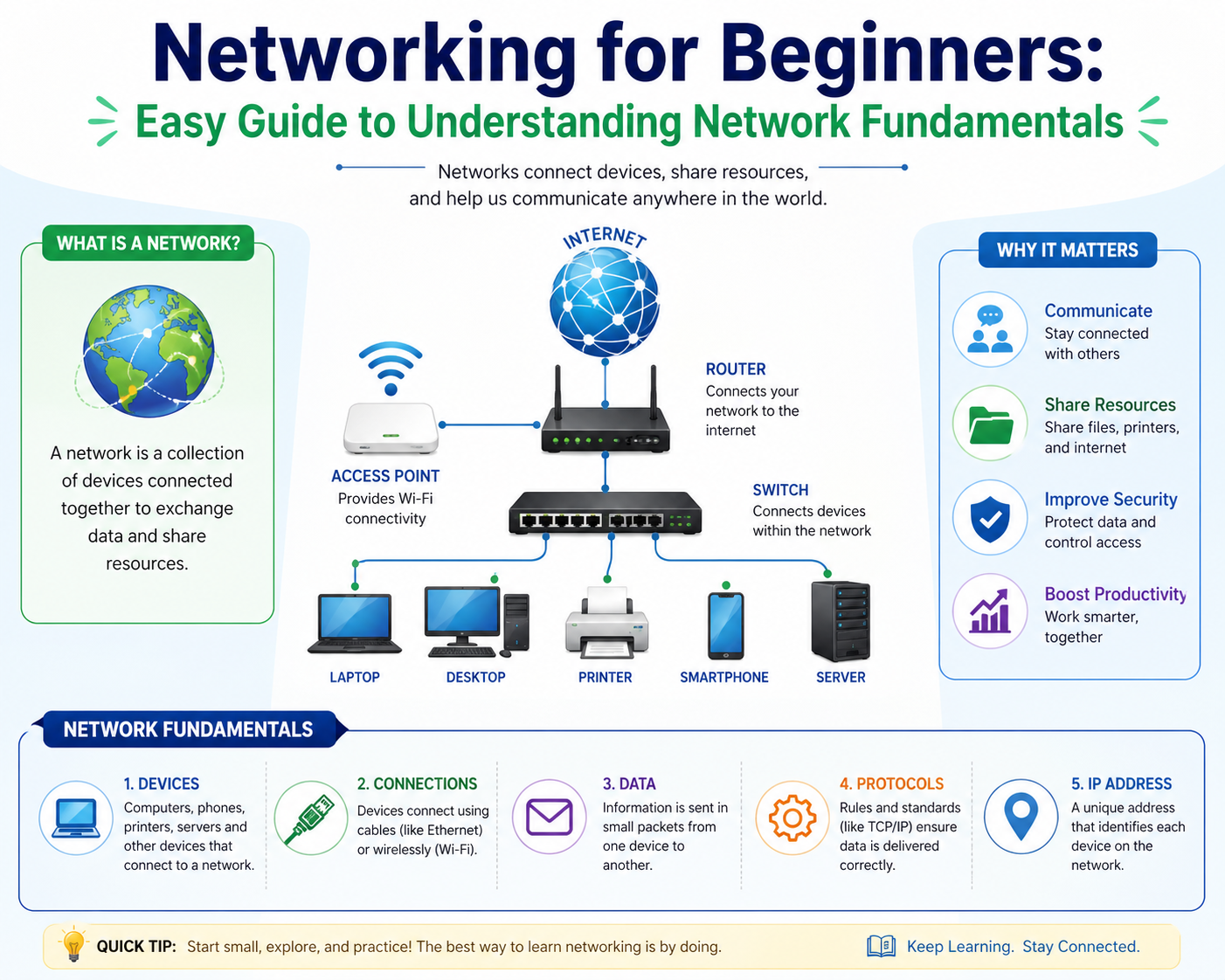
At its core, computer networking is the practice of connecting multiple computing devices so they can exchange information. These devices can include computers, servers, smartphones, sensors, and specialized hardware systems. The primary goal is to enable communication and resource sharing in a structured and efficient manner.
Networking is built upon a set of fundamental principles that ensure consistency and reliability. One of these principles is standardization, which allows different systems to communicate regardless of manufacturer or design. Standardization ensures that devices interpret data in the same way, preventing miscommunication and errors during transmission.
Another foundational principle is modular design. Networks are structured in layers, with each layer responsible for specific tasks. This separation simplifies complex processes by dividing them into manageable components. For example, one layer may handle physical transmission of data, while another manages logical addressing or application-level communication.
Reliability is also a key foundation. Networks are designed to ensure that data reaches its destination accurately, even in the presence of interruptions or failures. Mechanisms such as error detection, retransmission, and redundancy contribute to maintaining consistent communication.
Networking also relies heavily on efficiency. As data volumes increase, systems must be capable of handling large-scale communication without delays or congestion. This requires careful planning of infrastructure, optimization of routing paths, and intelligent distribution of network resources.
How Data Communication Actually Works
Data communication within a network follows a structured process that ensures information is transmitted accurately from one device to another. When a user initiates an action, such as sending a file or loading a webpage, the data generated by that action is broken down into smaller units known as packets. These packets are easier to manage and transmit across complex networks.
Each packet contains two main components: the payload and the header. The payload carries the actual data, while the header includes essential routing information such as source address, destination address, and sequencing details. This structure allows packets to travel independently across the network and still be reassembled correctly at the destination.
Once packets are created, they begin their journey through the network. They pass through various intermediary devices that help guide them toward their destination. These devices analyze the information contained in the packet headers and determine the most efficient path for forwarding them.
The path that packets take is not always fixed. Networks are dynamic environments where conditions can change rapidly due to traffic congestion, hardware failures, or other disruptions. As a result, packets may take different routes to reach the same destination. This flexibility ensures that communication remains uninterrupted even under varying conditions.
After reaching the destination device, packets are reassembled in the correct order to reconstruct the original data. This process is coordinated by protocols that ensure accuracy and completeness. If any packets are missing or corrupted during transmission, they are requested again to maintain data integrity.
Key Network Architecture Models
Network architecture refers to the structured design of how devices, systems, and services are organized and interact within a network. Several architectural models exist to help standardize communication and improve understanding of complex network behavior.
One widely recognized model divides networking functions into conceptual layers. Each layer serves a specific purpose and interacts with adjacent layers to facilitate communication. This layered approach simplifies troubleshooting and development by isolating different aspects of network functionality.
The lower layers are typically responsible for the physical transmission of data, including electrical signals, cables, and wireless communication methods. These layers ensure that raw data can move between devices. Higher layers focus on logical processes such as addressing, routing, and application-level communication.
Another important aspect of network architecture is the separation between client and server roles. In many networks, certain devices provide services or resources, while others request and consume those services. This structure allows for efficient resource management and centralized control of data and applications.
Modern network architectures also incorporate distributed systems, where processing and storage are spread across multiple devices rather than centralized in one location. This approach improves performance, scalability, and reliability by reducing dependency on a single system.
In addition, hybrid architectures combine different models to meet specific organizational needs. These systems integrate local infrastructure with remote services, allowing for flexible deployment of resources across different environments.
Essential Networking Devices and Their Roles
Networking relies on a variety of physical and logical components that work together to enable communication. Each device plays a specific role within the network infrastructure, contributing to overall performance and functionality.
Switching devices are responsible for connecting multiple devices within a local environment. They manage internal traffic by directing data to the appropriate destination based on hardware addresses. This ensures that information is delivered efficiently without unnecessary congestion.
Routing devices operate at a broader level, connecting multiple networks. They analyze destination information and determine optimal paths for data to travel between different network segments. These devices are essential for enabling communication across large-scale systems such as the internet.
Wireless access devices provide connectivity without the need for physical cables. They allow devices to connect to networks using radio signals, offering flexibility and mobility. This has become increasingly important as mobile computing continues to grow.
Network interface components enable devices to connect physically or wirelessly to a network. These interfaces convert data into signals that can be transmitted across communication channels and then convert received signals back into usable data.
Supporting devices such as firewalls and load balancers enhance network performance and security. Firewalls monitor and control incoming and outgoing traffic based on predefined rules, while load balancers distribute traffic across multiple systems to prevent overload and maintain efficiency.
Together, these components form the physical and logical infrastructure that supports all network communication. Their coordination ensures that data flows smoothly and securely across interconnected systems.
Addressing and Data Identification Systems
For communication to function effectively in a network, each device must have a unique identifier. Addressing systems provide this identification, allowing data to be delivered to the correct destination without confusion.
The most widely used addressing system assigns numerical identifiers to devices within a network. These identifiers are structured in a way that reflects both the device and its location within the network hierarchy. This structure enables efficient routing of data across complex systems.
Addressing also plays a critical role in ensuring scalability. As networks grow, new devices can be added without disrupting existing communication. The addressing system automatically integrates new nodes into the existing structure, maintaining order and organization.
In addition to device addressing, networks also use logical identifiers for services and applications. These identifiers allow users to access resources without needing to know the exact physical location of the system providing them. This abstraction simplifies user interaction and improves flexibility.
Routing systems rely heavily on addressing information to determine how data should travel through a network. Each intermediary device uses this information to make decisions about forwarding packets toward their destination. This process is repeated across multiple stages until the data reaches its final endpoint.
Addressing systems are also essential for security and access control. By identifying devices and users, networks can enforce policies that regulate who can access specific resources. This helps maintain the integrity and confidentiality of data within the system.
Evolution of Network Technologies
Network technology has undergone continuous transformation since its early development. Initial systems were limited in scale and capability, often restricted to small environments with minimal connectivity. Over time, advancements in hardware, software, and communication methods have significantly expanded networking capabilities.
Early networks were primarily focused on basic data sharing between a small number of computers. As demand for connectivity increased, more sophisticated systems were developed to support larger and more complex environments. These developments introduced standardized protocols, improved routing mechanisms, and more efficient data transmission methods.
The introduction of global connectivity marked a major turning point in networking evolution. Systems were no longer isolated but became part of a vast interconnected structure that spans the entire world. This shift enabled real-time communication on a global scale and paved the way for modern digital ecosystems.
Recent advancements have focused on increasing speed, scalability, and automation. Networks are now capable of self-adjusting based on traffic conditions, optimizing performance without manual intervention. Virtualization has also played a significant role, allowing network resources to be managed dynamically rather than through fixed physical configurations.
As technology continues to evolve, networking systems are becoming more intelligent and adaptive. Emerging innovations are focused on improving efficiency, reducing latency, and enhancing security. These developments ensure that networking remains a central component of technological progress in the digital age.
Expanding Network Infrastructure in the Digital World
Modern networking has evolved far beyond simple device-to-device communication. It now represents a global infrastructure that supports critical systems, large-scale digital platforms, and continuously growing data exchange requirements. As digital transformation accelerates, networks must handle increasing complexity while maintaining stability, speed, and security. This expansion is not only technical but also structural, requiring new methods of design, management, and optimization.
Network infrastructure today is built to support vast ecosystems of connected devices. These include personal computers, mobile devices, cloud servers, industrial sensors, and embedded systems. Each device contributes to a constantly changing flow of data that must be efficiently routed and processed. The challenge is not only to connect these devices but also to ensure that communication remains reliable under heavy demand.
One of the key drivers of modern network expansion is the rise of distributed computing. Instead of relying on a single centralized system, computing tasks are spread across multiple interconnected nodes. This reduces bottlenecks, improves fault tolerance, and increases scalability. As a result, networks are no longer static structures but dynamic systems capable of adapting to changing workloads.
The increasing reliance on digital services has also pushed organizations to redesign their infrastructure strategies. Traditional network designs that once focused on local environments are now being replaced by hybrid and global architectures. These architectures integrate on-premises systems with remote resources, creating flexible environments that can scale based on demand.
Advanced Data Transmission and Flow Management
Data transmission in modern networks involves more than simply sending information from one point to another. It requires sophisticated mechanisms that manage traffic flow, prioritize important data, and ensure efficient utilization of resources. As network traffic grows in volume and complexity, these mechanisms become essential for maintaining performance.
At the core of data transmission is the concept of packet-based communication. Information is divided into smaller units that can travel independently across the network. These packets may take different paths depending on network conditions, congestion levels, and routing decisions. Once they reach their destination, they are reassembled into their original form.
Flow control mechanisms regulate the rate at which data is transmitted between devices. This ensures that sending devices do not overwhelm receiving devices with excessive data. Without flow control, networks would experience congestion, leading to delays and potential data loss.
Congestion management is another critical aspect of data flow. When too many packets attempt to traverse the same network path, performance can degrade significantly. To address this, networks implement strategies that distribute traffic more evenly across available routes. These strategies help maintain stability even during periods of high demand.
Error handling is also integrated into data transmission systems. Networks continuously monitor for corrupted or lost packets and initiate retransmission processes when necessary. This ensures that data integrity is preserved throughout the communication process.
Routing Mechanisms and Path Optimization
Routing is one of the most important functions in networking. It determines how data moves from its source to its destination across interconnected systems. Routing decisions are made based on a variety of factors, including network topology, traffic conditions, and predefined rules.
Each router in a network maintains a set of instructions that guide its decision-making process. These instructions help determine the most efficient path for forwarding data packets. In complex networks, multiple routing paths may exist between two points, allowing systems to choose alternative routes when necessary.
Dynamic routing is widely used in modern networks to adapt to changing conditions. Unlike static routing, which relies on fixed paths, dynamic routing allows systems to adjust routes automatically based on real-time information. This improves resilience and ensures continuous communication even when parts of the network experience failures or congestion.
Path optimization is another key aspect of routing. Networks aim to minimize delays, reduce bandwidth usage, and improve overall efficiency. Advanced algorithms analyze network conditions and calculate the most efficient routes for data transmission. These optimizations are essential for supporting high-performance applications such as video streaming, online gaming, and real-time communication.
Routing also plays a significant role in scalability. As networks grow, routing systems must be able to handle increasing numbers of devices and connections. Scalable routing architectures ensure that performance remains consistent even as complexity increases.
Network Security and Protective Mechanisms
As networks become more interconnected, security has become a fundamental concern. The increasing volume of sensitive data being transmitted across networks makes them attractive targets for unauthorized access and malicious activity. To address these challenges, networks implement multiple layers of security mechanisms.
One of the primary security components is access control. This system ensures that only authorized users and devices can access specific resources within a network. Access control mechanisms rely on authentication processes that verify the identity of users before granting permissions.
Encryption is another essential security technique. It converts data into a coded format that can only be decoded by authorized parties. This ensures that even if data is intercepted during transmission, it cannot be understood without the proper decryption key. Encryption is widely used in secure communication protocols to protect sensitive information.
Firewalls act as protective barriers between trusted internal networks and external systems. They monitor incoming and outgoing traffic and apply predefined rules to determine whether data should be allowed or blocked. Firewalls help prevent unauthorized access and reduce the risk of cyber threats.
Intrusion detection systems monitor network activity for suspicious behavior. These systems analyze traffic patterns and identify potential security breaches. When unusual activity is detected, alerts are generated so that appropriate action can be taken.
Network segmentation is another important security strategy. By dividing a network into smaller segments, organizations can limit the spread of potential threats. This approach also improves performance by reducing unnecessary traffic within each segment.
Wireless Networking and Mobility Expansion
Wireless networking has significantly transformed how devices connect and communicate. Unlike traditional wired networks, wireless systems use radio signals to transmit data between devices. This provides greater flexibility and mobility, allowing users to connect from virtually any location within range.
Wireless access points serve as the primary connection points for devices in a wireless network. They manage communication between wireless devices and the broader network infrastructure. These access points are strategically placed to ensure coverage and minimize signal interference.
One of the major advantages of wireless networking is mobility. Users can move freely without losing connectivity, making wireless systems ideal for mobile computing environments. This has contributed to the widespread adoption of laptops, smartphones, and tablets.
However, wireless networking also introduces challenges such as signal interference, limited range, and security vulnerabilities. To address these issues, advanced technologies such as signal encryption, frequency management, and mesh networking are used.
Mesh networks are particularly important in large environments. In a mesh network, multiple access points work together to provide seamless coverage. If one access point fails, others can continue to maintain connectivity, ensuring reliability and redundancy.
Wireless technology continues to evolve, with improvements in speed, range, and efficiency. These advancements are enabling new applications such as smart cities, autonomous systems, and Internet of Things ecosystems.
Cloud Integration and Distributed Networking Systems
Cloud-based networking has become a central component of modern digital infrastructure. Instead of relying solely on local hardware, organizations now use remote servers to store data, run applications, and manage services. This approach provides scalability, flexibility, and cost efficiency.
In cloud environments, resources are distributed across multiple data centers. These data centers are interconnected through high-speed networks that enable seamless access to applications and data. Users can connect to cloud services from anywhere, provided they have an internet connection.
One of the key benefits of cloud integration is scalability. Resources can be increased or decreased based on demand without requiring physical infrastructure changes. This allows organizations to respond quickly to changing workloads.
Cloud networks also support redundancy and fault tolerance. Data is often replicated across multiple locations, ensuring that it remains available even if one system fails. This improves reliability and reduces the risk of data loss.
Virtualization plays a major role in cloud networking. It allows multiple virtual systems to operate on a single physical machine. These virtual systems function independently, providing efficient resource utilization and flexibility.
Network Performance Optimization Techniques
Maintaining optimal network performance requires continuous monitoring and adjustment. As traffic patterns change, networks must adapt to ensure consistent speed and reliability. Several techniques are used to achieve this optimization.
Traffic prioritization ensures that critical data is transmitted before less important information. This is particularly important for applications such as video conferencing and financial transactions, where delays can have significant consequences.
Bandwidth management controls the amount of data that can be transmitted across a network at any given time. By allocating bandwidth efficiently, networks can prevent congestion and maintain stable performance.
Caching is another technique used to improve performance. Frequently accessed data is stored closer to users, reducing the need for repeated requests to central servers. This reduces latency and improves response times.
Load balancing distributes network traffic across multiple servers or paths. This prevents any single system from becoming overwhelmed and ensures that resources are used efficiently. Load balancing is essential for maintaining performance in high-traffic environments.
Latency reduction techniques focus on minimizing delays in data transmission. This involves optimizing routing paths, improving infrastructure, and reducing unnecessary processing steps.
Emerging Trends in Network Development
Networking continues to evolve with the introduction of new technologies and methodologies. One of the most significant trends is the move toward automation. Automated networks can configure, monitor, and optimize themselves without manual intervention, reducing complexity and improving efficiency.
Another emerging trend is the use of artificial intelligence in network management. Intelligent systems can analyze traffic patterns, predict potential issues, and make real-time adjustments to improve performance.
Software-defined networking is also transforming how networks are designed and managed. By separating control functions from physical hardware, networks become more flexible and easier to manage. This allows for centralized control and dynamic configuration.
Edge computing is another important development. Instead of sending all data to centralized locations, processing is performed closer to the source of data generation. This reduces latency and improves efficiency for time-sensitive applications.
As these trends continue to develop, networking systems will become more adaptive, intelligent, and efficient. The evolution of networking reflects the growing demand for faster, more reliable, and more secure communication systems in an increasingly digital world.
Network Protocols and Communication Standards
Modern networking depends heavily on structured communication rules known as protocols. These protocols define how data is formatted, transmitted, received, and interpreted across different devices and systems. Without them, interoperability between diverse technologies would not be possible, and global communication systems would fail to function consistently.
Protocols operate at multiple levels within a network. Some govern how data is physically transmitted, while others manage how applications communicate or how security is enforced. This layered structure ensures that each aspect of communication is handled efficiently without overwhelming any single component of the system.
At a foundational level, communication protocols establish consistency in how devices interpret data. For example, when one system sends information to another, both must agree on how that information is structured. This includes how data is broken into packets, how errors are detected, and how lost information is recovered.
Transport protocols are responsible for ensuring the reliable delivery of data. They manage sequencing, flow control, and retransmission when necessary. These mechanisms help ensure that even if packets arrive out of order or are delayed, they can still be reconstructed accurately at the destination.
Application-level protocols define how specific services communicate over a network. These include systems for transferring files, sending messages, or accessing web resources. Each protocol is designed for a specific purpose, ensuring efficient and standardized communication across platforms.
Security protocols add another layer of protection by encrypting data during transmission. This ensures that sensitive information remains confidential and protected from unauthorized access. Encryption standards are continuously updated to counter evolving security threats.
Network Models and Layered Architecture Understanding
Networking systems are often described using layered models that simplify how communication processes are organized. These models divide complex networking functions into structured layers, each responsible for a specific set of tasks. This approach makes it easier to design, manage, and troubleshoot networks.
At the lowest level of these models, physical transmission occurs. This includes electrical signals, optical fiber communication, and wireless transmission. The primary focus at this level is moving raw data between devices without considering its meaning or structure.
Above the physical layer are data handling layers that manage framing, error detection, and addressing. These layers ensure that data is properly packaged and delivered across network links. They also handle retransmission when errors occur during communication.
Higher layers focus on routing and logical addressing. These layers determine how data moves across multiple networks and reaches its intended destination. They are responsible for ensuring that data travels through the most efficient available paths.
At the top layers, application communication takes place. These layers interact directly with software applications, enabling services such as file transfer, email communication, and web browsing. They translate network data into formats that users and applications can understand.
This layered structure allows for modular development and easier troubleshooting. If an issue occurs, engineers can isolate the problem within a specific layer rather than analyzing the entire system. It also enables interoperability between different technologies and vendors.
Network Scalability and Growth Management
As digital environments expand, networks must be able to scale efficiently to accommodate increasing demand. Scalability refers to a network’s ability to grow in size, capacity, and complexity without losing performance or stability. This is a critical requirement in modern systems where data traffic continues to increase rapidly.
One method of achieving scalability is through modular infrastructure design. Instead of building a single large system, networks are constructed using smaller components that can be expanded or modified independently. This allows organizations to add new devices, services, or users without disrupting existing operations.
Hierarchical network design also supports scalability by organizing systems into structured layers. This reduces complexity and ensures that changes in one part of the network do not negatively impact the entire system. It also improves efficiency by limiting unnecessary data traffic between unrelated segments.
Load distribution plays a major role in scalability. As network demand increases, traffic must be distributed evenly across available resources. This prevents bottlenecks and ensures that no single component becomes overwhelmed. Load distribution systems continuously monitor traffic patterns and adjust routing decisions accordingly.
Virtualization technologies further enhance scalability by allowing multiple virtual systems to operate on shared physical infrastructure. This reduces hardware dependency and enables rapid deployment of new services. Virtual environments can be adjusted dynamically based on workload requirements.
Cloud-based architectures also contribute significantly to scalability. They provide on-demand access to computing resources, allowing organizations to increase or decrease capacity as needed. This eliminates the need for large upfront infrastructure investments and supports flexible growth.
Performance Optimization in Complex Networks
Network performance is a critical factor in ensuring smooth communication and efficient data transfer. As networks become more complex, maintaining optimal performance requires continuous monitoring and adjustment of various system components.
One of the key aspects of performance optimization is latency reduction. Latency refers to the delay between sending and receiving data. High latency can negatively impact applications that require real-time communication. To reduce latency, networks optimize routing paths and minimize unnecessary processing steps.
Bandwidth management is another important optimization technique. Bandwidth represents the amount of data that can be transmitted within a given time period. Efficient bandwidth allocation ensures that critical applications receive the necessary resources without being affected by less important traffic.
Traffic shaping techniques are used to control data flow within a network. These techniques regulate the rate at which data is transmitted, preventing congestion and maintaining stability. By prioritizing certain types of traffic, networks can ensure that important services remain responsive even during peak usage periods.
Caching mechanisms improve performance by storing frequently accessed data closer to users. This reduces the need for repeated data retrieval from distant servers, resulting in faster response times and reduced network load.
Network monitoring tools continuously analyze system performance and detect potential issues. These tools collect data on traffic patterns, resource usage, and error rates. By analyzing this information, administrators can identify bottlenecks and implement corrective actions.
Wireless Systems and Expanding Connectivity
Wireless networking has revolutionized the way devices connect and communicate. By eliminating the need for physical cables, wireless systems provide greater flexibility and mobility for users. This has led to widespread adoption across homes, businesses, and public environments.
Wireless communication relies on electromagnetic signals to transmit data between devices. These signals are transmitted through access points that act as intermediaries between wireless devices and the broader network infrastructure. Access points manage connections and ensure that data is transmitted efficiently.
One of the primary advantages of wireless systems is mobility. Users can move freely within a network’s coverage area without losing connectivity. This has enabled the growth of mobile computing and the widespread use of portable devices.
However, wireless systems also face challenges such as signal interference, limited range, and security risks. Environmental factors and physical obstacles can affect signal quality, leading to reduced performance. To address these issues, advanced technologies such as signal optimization and channel management are used.
Security is particularly important in wireless environments. Since wireless signals are transmitted through open space, they are more susceptible to interception. Encryption and authentication mechanisms are used to protect data and ensure that only authorized users can access the network.
Mesh networking is an advanced wireless architecture that improves coverage and reliability. In a mesh system, multiple devices work together to relay data across the network. If one node fails, others automatically compensate, ensuring continuous connectivity.
Network Security Principles and Defense Strategies
Security is one of the most critical aspects of modern networking. As networks become more interconnected, they also become more vulnerable to unauthorized access, data breaches, and malicious attacks. To protect against these threats, multiple layers of security mechanisms are implemented.
Access control systems regulate who can enter and use network resources. These systems rely on authentication methods such as passwords, digital certificates, or biometric verification. Once authenticated, users are granted permissions based on predefined roles.
Encryption plays a central role in protecting data during transmission. It converts readable information into an encoded format that can only be deciphered by authorized parties. This ensures confidentiality even if data is intercepted during transfer.
Firewalls act as protective barriers that filter incoming and outgoing network traffic. They enforce security policies by allowing or blocking data based on predefined rules. Firewalls are essential for preventing unauthorized access and reducing exposure to external threats.
Intrusion detection and prevention systems monitor network activity for suspicious behavior. These systems analyze traffic patterns and identify anomalies that may indicate security breaches. When threats are detected, alerts are generated, or automatic countermeasures are activated.
Network segmentation divides large networks into smaller, isolated sections. This limits the spread of potential security breaches and improves overall control. If one segment is compromised, others remain protected.
Cloud-Based Networking and Virtual Infrastructure
Cloud networking has transformed how computing resources are accessed and managed. Instead of relying on local infrastructure, organizations now use remote systems to store data, run applications, and deliver services. This shift has introduced new levels of flexibility and scalability.
Cloud environments are built on a distributed infrastructure consisting of multiple data centers. These centers are interconnected through high-speed networks that ensure seamless communication. Users can access cloud services from virtually any location, making it highly versatile.
Virtualization is a core component of cloud networking. It allows multiple virtual systems to run on a single physical machine, maximizing resource utilization. These virtual systems operate independently and can be configured dynamically based on demand.
One of the key advantages of cloud networking is elasticity. Resources can be scaled up or down based on usage requirements. This ensures that systems remain efficient without over-provisioning hardware.
Redundancy is also built into cloud systems. Data is often replicated across multiple locations to ensure availability in case of failure. This enhances reliability and minimizes downtime.
Cloud networking also supports automated management. Systems can self-adjust based on performance metrics, reducing the need for manual intervention. This improves efficiency and allows for faster response to changing conditions.
Emerging Technologies and Future Network Directions
Networking continues to evolve rapidly as new technologies reshape how systems communicate and operate. Automation is becoming increasingly important, allowing networks to configure and manage themselves with minimal human input. This reduces operational complexity and improves efficiency.
Artificial intelligence is being integrated into network management systems. AI-driven tools can analyze large volumes of data, predict potential issues, and optimize performance in real time. This leads to more intelligent and adaptive networks.
Software-defined networking is another major advancement. It separates control functions from physical hardware, allowing networks to be managed through centralized software systems. This increases flexibility and simplifies configuration.
Edge computing is also gaining importance. Instead of processing all data in centralized locations, computation is performed closer to the source of data generation. This reduces latency and improves responsiveness for time-sensitive applications.
As networks continue to evolve, they are becoming more autonomous, efficient, and intelligent. These advancements are shaping the future of digital communication and ensuring that networking remains a fundamental pillar of technological progress.
Conclusion
Computer networking has become one of the most essential pillars of the modern digital world, shaping how individuals, organizations, and entire industries communicate, operate, and evolve. What began as a relatively simple method of connecting a small number of computers has now transformed into a vast, global infrastructure that supports billions of devices and an almost continuous exchange of data. Every digital interaction, from sending a message to running complex cloud-based applications, relies on the invisible but highly structured systems that networking provides.
One of the most important takeaways from understanding networking is recognizing that it is not a single technology but a combination of many interconnected systems working together. Hardware devices such as routers, switches, and access points form the physical backbone of communication. Protocols define the rules that ensure data is transmitted and interpreted correctly. Addressing systems ensure that every piece of information reaches the correct destination without confusion. When combined, these components create a highly coordinated environment where data can flow efficiently and reliably across vast distances.
The evolution of networking has also been driven by the increasing demand for speed, reliability, and scalability. In earlier stages of technological development, networks were limited in size and capability, often serving small groups of users within confined environments. Today, networks must support global connectivity, real-time communication, and massive data processing requirements. This shift has led to the development of advanced routing mechanisms, optimized traffic management systems, and intelligent infrastructure capable of adapting to changing conditions.
Security has become another defining aspect of modern networking. As the amount of sensitive information transmitted across networks has increased, so too have the risks associated with unauthorized access and cyber threats. This has led to the implementation of layered security systems that include encryption, authentication, firewalls, and intrusion detection mechanisms. These protective measures ensure that data remains confidential, accurate, and accessible only to authorized users. In this way, networking is not only about connectivity but also about trust and protection in a digital environment.
Wireless technologies have further expanded the reach and flexibility of networking. By removing the dependency on physical connections, wireless systems have enabled mobility and accessibility on an unprecedented scale. Devices can now connect from virtually anywhere, supporting the rise of mobile computing, smart environments, and interconnected ecosystems. This has fundamentally changed how people interact with technology, making connectivity a constant presence rather than a fixed location-based service.
Cloud computing has also reshaped the networking landscape by decentralizing resources and making them accessible on demand. Instead of relying solely on local infrastructure, organizations now leverage remote systems that offer scalability, redundancy, and efficiency. This shift has allowed businesses to adapt more quickly to changing demands while reducing infrastructure limitations. It has also contributed to the development of more flexible and resilient network architectures that can support global operations.
Another key aspect of networking is its role in enabling innovation across multiple fields. Technologies such as artificial intelligence, automation, and edge computing rely heavily on robust network infrastructures to function effectively. These advancements are not isolated developments but are deeply interconnected with networking systems that provide the necessary communication pathways and data exchange capabilities. As a result, networking continues to serve as a foundation for technological progress across industries.
Looking forward, the future of networking is expected to become even more dynamic and intelligent. Automation will reduce the need for manual configuration and management, allowing networks to self-adjust based on real-time conditions. Artificial intelligence will enhance decision-making processes by analyzing data patterns and optimizing performance automatically. Edge computing will further reduce latency by processing data closer to its source, improving responsiveness for time-sensitive applications.
Despite these advancements, the core principles of networking will remain consistent. The need to connect devices, transmit data efficiently, ensure security, and maintain reliability will continue to define the field. What will change is the scale, speed, and intelligence with which these goals are achieved.
In essence, networking is no longer just a technical discipline but a foundational element of modern society. It influences how people communicate, how businesses operate, and how technology evolves. As digital transformation continues to accelerate, networking will remain at the center of innovation, enabling new possibilities and shaping the future of global connectivity in ways that are still unfolding.