CompTIA, formally known as the Computing Technology Industry Association, is a globally recognized non-profit organization focused on developing and supporting the information technology workforce. It operates as an industry consortium made up of technology companies, service providers, training organizations, and enterprise stakeholders who collectively contribute to shaping IT skill standards. The organization’s influence extends across multiple continents, making it one of the most widely accepted certification authorities in the technology sector.
The primary mission of CompTIA is to strengthen the global IT workforce by defining standardized skill benchmarks that align with industry needs. As technology continues to evolve rapidly, organizations require professionals who can adapt to new systems, tools, and security challenges. CompTIA addresses this need by developing certification frameworks that validate practical, job-ready skills rather than purely theoretical knowledge.
Unlike vendor-specific certification bodies, CompTIA focuses on vendor-neutral certifications. This means that the skills validated by its programs are not tied to a single technology provider. Instead, they are applicable across multiple platforms, including enterprise environments that use diverse technologies. This neutrality is one of the key reasons CompTIA certifications are widely accepted by employers across different industries.
The organization plays a significant role in bridging the gap between education and employment in the IT sector. By collaborating with industry experts and employers, it ensures that certification content reflects real-world job requirements. This alignment between learning outcomes and job roles helps candidates transition more effectively into technical careers.
The Purpose and Structure of CompTIA Certification Programs
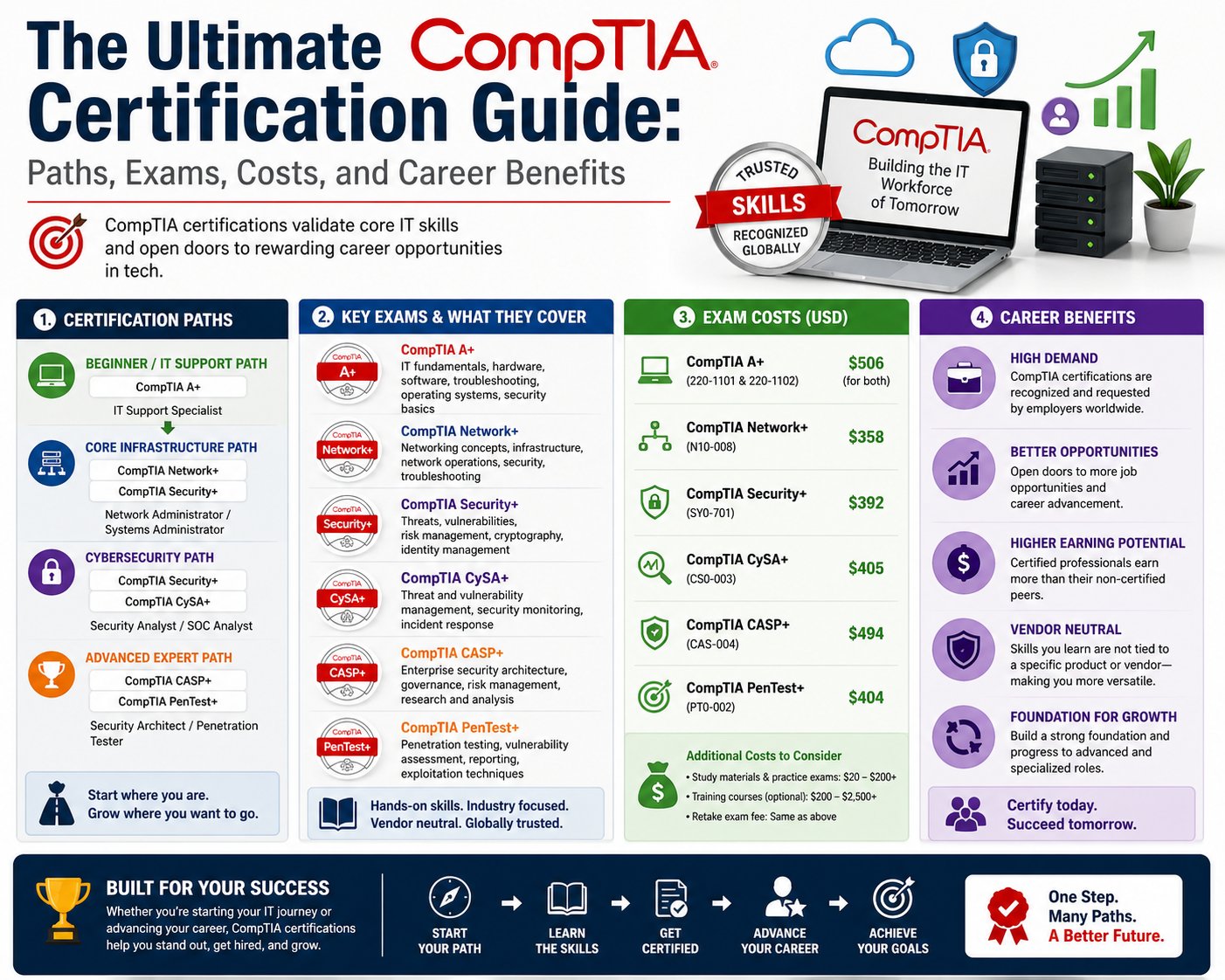
CompTIA certification programs are designed to establish a structured pathway for individuals pursuing careers in information technology. These programs are organized in a way that supports progressive skill development, starting from foundational knowledge and advancing toward specialized expertise.
Each certification is built around specific job roles and responsibilities. Rather than focusing solely on academic knowledge, the certifications emphasize practical application. Candidates are evaluated based on their ability to perform tasks that are commonly required in real IT environments. This approach ensures that certified professionals are prepared for workplace challenges.
The certification framework is divided into distinct categories that represent different areas of IT specialization. These categories include core technologies, infrastructure systems, cybersecurity, and professional skills. Each category serves a unique purpose in career development and reflects different stages of professional growth.
The structure of these programs allows individuals to begin with entry-level certifications and gradually progress toward advanced credentials. This step-by-step progression supports continuous learning and enables professionals to build expertise over time. It also allows employers to identify candidates with clearly defined skill levels.
Another important aspect of CompTIA certification programs is their global recognition. Because they are not tied to specific vendors or technologies, they are accepted by organizations worldwide. This makes them particularly valuable for professionals seeking international career opportunities.
The Role of Vendor-Neutral Certifications in IT Careers
Vendor-neutral certifications are a defining feature of CompTIA’s approach to professional development. These certifications validate skills that are applicable across multiple technology platforms, rather than focusing on a single vendor’s products or systems. This approach provides significant flexibility for IT professionals.
In real-world environments, organizations often use a combination of technologies from different vendors. For example, a company may use one vendor for networking equipment, another for cloud services, and yet another for security solutions. In such environments, professionals must be able to work across different systems without being limited to a specific technology ecosystem.
Vendor-neutral certifications address this challenge by focusing on fundamental principles and transferable skills. These include networking concepts, operating system fundamentals, security principles, and infrastructure management techniques. By mastering these foundational areas, professionals can adapt to different technologies more easily.
This flexibility is particularly important in modern IT careers, where technological change is constant. New tools, platforms, and frameworks are introduced regularly, and professionals are expected to learn and adapt quickly. Vendor-neutral certifications provide a stable foundation that supports long-term career growth.
Employers also value vendor-neutral certifications because they indicate a broader understanding of IT systems. Rather than being limited to one technology stack, certified professionals can contribute in diverse environments. This makes them more versatile and valuable to organizations.
Categories Within the Certification Framework
The CompTIA certification framework is organized into multiple categories that reflect different stages and areas of IT specialization. Each category is designed to support a specific aspect of career development.
The first category focuses on core IT knowledge. This includes fundamental concepts related to hardware, software, networking, and basic security principles. These certifications are intended for individuals who are new to the IT field or transitioning from non-technical backgrounds. They provide the foundational knowledge required for entry-level roles.
The second category focuses on infrastructure technologies. This includes systems such as servers, cloud environments, and operating systems. Certifications in this category are designed for professionals who manage and support IT infrastructure. They require a deeper understanding of technical systems and often build on core-level knowledge.
The third category focuses on cybersecurity. This area has become increasingly important due to the growing number of cyber threats facing organizations worldwide. Cybersecurity certifications cover topics such as threat detection, vulnerability management, incident response, and secure system design. These certifications are designed for professionals who specialize in protecting digital assets.
The fourth category focuses on professional skills that are not strictly technical. These include project management, training, and business-related IT functions. These certifications are intended for individuals who work in roles that support IT operations from a managerial or organizational perspective.
This structured categorization ensures that professionals can choose certification paths that align with their career goals. It also allows for clear progression from foundational knowledge to advanced specialization.
Core IT Certifications and Their Importance
Core certifications form the foundation of the CompTIA certification ecosystem. They are designed to introduce essential IT concepts and prepare individuals for entry-level roles in the technology industry.
One of the primary certifications in this category focuses on general computing knowledge. It introduces candidates to basic hardware components, software applications, and IT terminology. This certification is often used by individuals who are exploring IT as a potential career path.
Another key certification in the core category focuses on technical support skills. It covers topics such as installing and configuring operating systems, troubleshooting hardware and software issues, and supporting end users. This certification is widely recognized as a starting point for careers in IT support and help desk roles.
Networking fundamentals are also addressed within the core category. This includes understanding how devices communicate, how networks are structured, and how data is transmitted across systems. Candidates learn about basic networking protocols and troubleshooting techniques, which are essential for many IT roles.
Security fundamentals are introduced through another core certification. This certification focuses on basic cybersecurity concepts such as threat identification, risk management, and secure system practices. Given the increasing importance of cybersecurity, this foundational knowledge is valuable for all IT professionals.
Core certifications serve as the entry point into the IT industry. They provide the essential skills needed to move into more advanced technical roles and form the basis for further specialization.
Career Development Through Certification Progression
One of the key strengths of the CompTIA certification framework is its structured progression model. This model allows individuals to build their skills incrementally, moving from basic knowledge to advanced expertise over time.
The progression typically begins with core certifications, which establish foundational knowledge. From there, professionals can move into infrastructure certifications, which introduce more complex technical concepts. After gaining experience in infrastructure technologies, individuals may choose to specialize in cybersecurity or other advanced areas.
This progression reflects the natural development of IT careers. As professionals gain experience, they take on more complex responsibilities and require more advanced skills. The certification framework supports this growth by providing clearly defined milestones.
Each stage of certification builds on the previous one. This ensures that professionals develop a comprehensive understanding of IT systems rather than isolated knowledge areas. It also helps employers identify candidates with appropriate skill levels for specific roles.
The progression model also supports long-term career planning. Individuals can map out their certification journey based on their career goals, whether they are interested in technical support, network engineering, cybersecurity, or cloud computing.
Industry Relevance and Workforce Impact
CompTIA certifications are widely recognized across the global IT industry. They are used by organizations to evaluate candidates for technical roles and to ensure that employees meet established skill standards.
One of the key reasons for this recognition is the practical nature of the certifications. Rather than focusing solely on theoretical knowledge, they emphasize real-world skills that are directly applicable in workplace environments. This makes certified professionals immediately valuable to employers.
The certifications also play a role in workforce development. By establishing standardized skill benchmarks, they help ensure consistency in IT capabilities across different organizations and regions. This contributes to a more stable and reliable IT workforce.
In addition to private sector adoption, these certifications are also recognized in public sector and government environments. Many organizations use them as part of their hiring and training requirements, particularly in roles related to infrastructure and cybersecurity.
The widespread adoption of CompTIA certifications reflects their relevance in addressing current and future IT challenges. As technology continues to evolve, the demand for skilled professionals remains strong, and certification programs play a key role in meeting this demand.
Foundational Knowledge as a Career Entry Point
For individuals entering the IT industry, foundational certifications provide a structured and accessible starting point. These certifications are designed to introduce essential concepts clearly and practically.
They help candidates develop an understanding of how computer systems operate, how networks function, and how basic security measures are implemented. This knowledge is critical for entry-level roles such as technical support, help desk assistance, and junior system administration.
By starting with foundational certifications, individuals can build confidence and gain practical experience before moving on to more advanced topics. This reduces the learning curve and improves long-term career success.
Foundational certifications also serve as a gateway to further specialization. Once individuals have mastered basic concepts, they can choose to focus on areas such as networking, cloud computing, or cybersecurity, depending on their interests and career goals.
This approach ensures that professionals are not overwhelmed by complex topics at the beginning of their careers. Instead, they are able to build knowledge gradually and systematically.
Evolving Role of IT Certifications in Modern Industry
The role of IT certifications has evolved significantly over time. In earlier stages of the industry, certifications were often seen as optional credentials. However, in today’s technology-driven environment, they have become an important requirement for many roles.
This shift is driven by the increasing complexity of IT systems and the growing demand for specialized skills. Organizations now rely heavily on certified professionals to manage critical infrastructure and protect against cyber threats.
Certifications also provide a standardized way to measure skills across a global workforce. This is particularly important in multinational organizations where employees may come from different educational and professional backgrounds.
As technology continues to advance, the importance of structured certification programs is expected to grow further. They provide a reliable framework for developing and validating skills in a rapidly changing industry.
The continued evolution of IT certifications reflects the ongoing transformation of the technology landscape and the need for professionals who can adapt to new challenges.
Advancing Through CompTIA Infrastructure Certifications
Infrastructure certifications represent the intermediate stage in the CompTIA certification ecosystem, bridging foundational IT knowledge with advanced technical specialization. These certifications focus on the systems, platforms, and environments that form the backbone of modern enterprise IT operations. Unlike entry-level certifications that emphasize basic concepts, infrastructure-level credentials require a deeper understanding of how complex systems are designed, deployed, and maintained in real-world environments.
At this stage, professionals transition from learning individual components to managing interconnected systems. This includes servers, cloud platforms, operating systems, virtualization technologies, and enterprise-level storage solutions. The goal is to prepare individuals for roles that involve maintaining and optimizing IT infrastructure at scale.
Infrastructure certifications are particularly relevant in modern organizations that rely heavily on hybrid environments. These environments combine on-premises systems with cloud-based services, requiring professionals to understand both traditional and modern computing architectures. As a result, infrastructure certifications emphasize adaptability and systems-level thinking.
The importance of this certification level has grown significantly with the expansion of cloud computing and remote infrastructure management. Organizations now expect IT professionals to manage distributed systems that operate across multiple platforms and geographic locations. Infrastructure certifications address this need by providing structured training in these complex environments.
Cloud Computing as a Core Infrastructure Skill
Cloud computing has become a central component of enterprise IT strategy. Infrastructure certifications that focus on cloud technologies are designed to prepare professionals for roles involving cloud deployment, management, and optimization. These certifications cover both conceptual understanding and practical implementation of cloud-based systems.
Cloud environments can be categorized into private, public, and hybrid models. Each model has distinct characteristics and use cases. Private cloud environments are dedicated to a single organization, offering greater control and security. Public cloud environments are shared across multiple users and provide scalability and cost efficiency. Hybrid environments combine elements of both, allowing organizations to balance flexibility and control.
Professionals working with cloud infrastructure must understand how resources are allocated and managed. This includes computing power, storage capacity, and network bandwidth. Efficient resource management is critical to ensuring performance and cost-effectiveness in cloud environments.
Another key aspect of cloud infrastructure is automation. Modern cloud systems rely heavily on automated processes for deployment, scaling, and maintenance. Infrastructure professionals must be able to configure and manage these automated systems to ensure consistent performance and reliability.
Security is also a major focus in cloud infrastructure. Professionals must implement appropriate security controls to protect data and applications. This includes identity management, access control, encryption, and monitoring systems. As cloud environments are often exposed to external networks, security considerations are more complex than in traditional on-premises systems.
Operating Systems and Open-Source Infrastructure
Operating systems form the foundation of all computing environments. Infrastructure certifications place significant emphasis on open-source operating systems, particularly Linux-based systems, due to their widespread use in enterprise environments.
Linux is commonly used in servers, cloud platforms, and development environments. Its flexibility, stability, and open-source nature make it a preferred choice for many organizations. Infrastructure professionals must be able to configure, manage, and troubleshoot Linux systems effectively.
Working with Linux involves understanding system architecture, file systems, user permissions, and process management. Professionals must also be familiar with command-line tools, which are essential for managing Linux environments efficiently.
Security is a critical aspect of operating system management. Infrastructure professionals must implement proper authentication mechanisms, configure firewalls, and manage user access controls. These measures help protect systems from unauthorized access and potential security breaches.
Automation and scripting are also important skills in operating system management. Infrastructure professionals often use scripts to automate repetitive tasks, manage configurations, and streamline system operations. This improves efficiency and reduces the likelihood of human error.
Open-source operating systems also require continuous monitoring and updates. Infrastructure professionals must ensure that systems are patched and updated regularly to maintain security and performance. This includes managing software dependencies and resolving compatibility issues.
Server Management and Enterprise Infrastructure
Servers are a fundamental component of enterprise IT infrastructure. They provide the computing power and services required to support business applications, databases, and network operations. Infrastructure certifications related to server management focus on configuring, maintaining, and troubleshooting server environments.
Server environments can vary widely depending on organizational needs. Some organizations use physical servers located on-site, while others rely on virtualized or cloud-based server environments. Infrastructure professionals must be able to work across all these environments.
Server configuration involves setting up hardware components, installing operating systems, and configuring network settings. Professionals must ensure that servers are optimized for performance, reliability, and security.
Storage management is another critical aspect of server administration. This includes configuring storage devices, managing data backups, and ensuring data redundancy. Proper storage management is essential for preventing data loss and ensuring business continuity.
Virtualization technology is widely used in modern server environments. It allows multiple virtual machines to run on a single physical server, improving resource utilization and flexibility. Infrastructure professionals must understand how to deploy and manage virtualized environments effectively.
Server security is also a key responsibility. Professionals must implement access controls, monitor system activity, and protect against unauthorized access. This includes both physical security measures and digital security protocols.
Networking Infrastructure and System Connectivity
Networking is a critical component of infrastructure management. It enables communication between devices, systems, and users across local and global environments. Infrastructure certifications emphasize the importance of understanding network design, configuration, and troubleshooting.
Networks consist of multiple interconnected components, including routers, switches, cables, and wireless access points. Infrastructure professionals must understand how these components interact to ensure smooth communication.
Network configuration involves setting up IP addressing, routing protocols, and subnetting structures. Professionals must ensure that networks are designed for efficiency, scalability, and security.
Troubleshooting network issues is a key skill in infrastructure roles. This involves identifying connectivity problems, diagnosing performance issues, and resolving configuration errors. Professionals use various diagnostic tools and techniques to analyze network behavior.
Security is an integral part of the networking infrastructure. Professionals must implement measures such as firewalls, intrusion detection systems, and encryption protocols to protect network traffic. This helps prevent unauthorized access and data breaches.
Wireless networking has also become increasingly important in modern environments. Infrastructure professionals must understand how to configure and secure wireless networks, including managing access points and encryption standards.
Data Center Operations and Physical Infrastructure
Data centers are central to modern IT infrastructure. They house the servers, storage systems, and networking equipment that support enterprise operations. Infrastructure certifications provide knowledge related to data center design, management, and maintenance.
Data center environments require careful planning to ensure efficiency and reliability. This includes managing power supply, cooling systems, and physical security. Infrastructure professionals must ensure that systems operate within optimal environmental conditions.
Redundancy is a key principle in data center design. Critical systems are often duplicated to ensure continuous operation in case of failure. This includes backup power systems, redundant network connections, and replicated storage systems.
Monitoring and maintenance are essential for data center operations. Professionals must continuously monitor system performance and address issues before they impact operations. This requires the use of monitoring tools and alerting systems.
Disaster recovery planning is also a critical aspect of data center management. Infrastructure professionals must develop strategies to restore operations in the event of system failures or natural disasters. This includes data backups, failover systems, and recovery procedures.
Cloud Integration with Traditional Infrastructure
Modern IT environments often combine traditional infrastructure with cloud-based systems. This hybrid approach allows organizations to balance control, scalability, and cost efficiency. Infrastructure certifications emphasize the importance of understanding how these environments interact.
Hybrid infrastructure requires seamless integration between on-premises systems and cloud platforms. This involves configuring network connections, synchronizing data, and managing workloads across environments.
Professionals must understand how to migrate workloads between local systems and cloud environments. This includes assessing system requirements, planning migration strategies, and minimizing downtime during transitions.
Performance optimization is also important in hybrid environments. Infrastructure professionals must ensure that systems operate efficiently across both local and cloud platforms. This requires continuous monitoring and adjustment of resources.
Security considerations become more complex in hybrid environments. Professionals must ensure that data is protected during transmission and storage across different systems. This includes implementing encryption and access control policies.
Automation and Infrastructure Efficiency
Automation plays a significant role in modern infrastructure management. It allows organizations to streamline operations, reduce manual intervention, and improve consistency across systems.
Infrastructure professionals must be familiar with automation tools and techniques used to manage systems at scale. This includes automated deployment, configuration management, and system monitoring.
Automation is particularly important in cloud environments, where resources can be dynamically allocated based on demand. Professionals must configure systems that automatically scale resources to meet performance requirements.
Scripting is commonly used to implement automation tasks. Infrastructure professionals use scripting languages to create workflows that automate repetitive processes and improve operational efficiency.
The use of automation also reduces the risk of human error. By standardizing processes, organizations can ensure that systems are configured consistently and reliably.
Security Considerations in Infrastructure Management
Security is a fundamental aspect of infrastructure management. Infrastructure professionals must ensure that systems are protected from unauthorized access, data breaches, and other security threats.
This involves implementing multiple layers of security, including physical security, network security, and application security. Each layer plays a role in protecting different aspects of the infrastructure.
Access control is a key security measure. Professionals must ensure that only authorized users have access to systems and data. This includes managing user accounts, permissions, and authentication mechanisms.
Monitoring and detection are also important security functions. Infrastructure professionals must continuously monitor systems for suspicious activity and respond to potential threats.
Security updates and patch management are essential for maintaining system integrity. Professionals must ensure that systems are regularly updated to address vulnerabilities and protect against emerging threats.
Performance Optimization and System Reliability
Infrastructure professionals are responsible for ensuring that systems operate efficiently and reliably. This involves monitoring performance metrics and making adjustments to improve system behavior.
Performance optimization includes managing CPU usage, memory allocation, and network bandwidth. Professionals must ensure that resources are distributed effectively to avoid bottlenecks.
System reliability is achieved through redundancy and failover mechanisms. Infrastructure professionals must design systems that continue operating even in the event of component failures.
Load balancing is another important technique used to distribute workloads across multiple systems. This helps improve performance and prevent system overload.
Continuous monitoring is essential for maintaining system reliability. Professionals must use monitoring tools to track system health and respond to issues proactively.
Evolving Role of Infrastructure Professionals
The role of infrastructure professionals continues to evolve as technology advances. Modern IT environments require professionals who can manage both traditional systems and emerging technologies such as cloud computing and automation.
Infrastructure professionals are increasingly expected to have a broad skill set that includes networking, system administration, security, and cloud management. This reflects the interconnected nature of modern IT systems.
As organizations adopt more complex technologies, the demand for skilled infrastructure professionals continues to grow. Certifications in this area provide a structured pathway for developing the necessary skills.
The integration of new technologies such as artificial intelligence and machine learning is also influencing infrastructure management. Professionals must adapt to these changes and develop new competencies to remain effective in their roles.
Understanding CompTIA Cybersecurity Certifications in Modern IT Environments
Cybersecurity certifications represent the most advanced stage within the CompTIA certification ecosystem and are designed for professionals responsible for defending digital systems, networks, and organizational data from increasingly sophisticated threats. As modern enterprises become more dependent on interconnected systems, the attack surface expands significantly, requiring structured security expertise that goes beyond foundational IT knowledge.
These certifications focus on developing analytical thinking, threat intelligence capabilities, and practical defensive strategies. Unlike earlier certification levels that emphasize system operation and infrastructure management, cybersecurity certifications concentrate on identifying vulnerabilities, responding to incidents, and implementing long-term security controls.
The cybersecurity domain is no longer limited to specialized security teams. Today, almost every IT role involves some level of security responsibility. This shift has made cybersecurity certifications highly relevant across multiple career paths, including system administration, network engineering, cloud operations, and IT auditing.
A key aspect of cybersecurity certifications is their emphasis on real-world threat scenarios. Candidates are trained to analyze attack patterns, interpret system logs, and respond to security incidents in dynamic environments. This practical orientation ensures that certified professionals can function effectively in live operational settings.
The Shift from Reactive Security to Analytical Defense Models
Traditional security approaches relied heavily on reactive defense mechanisms, where systems responded to threats after they were detected. However, modern cybersecurity strategies focus on predictive and analytical models that aim to identify threats before they cause damage.
Cybersecurity certifications emphasize this shift by teaching professionals how to analyze large volumes of security data. This includes identifying unusual patterns in network traffic, detecting unauthorized access attempts, and evaluating system vulnerabilities before exploitation occurs.
Analytical security models rely on continuous monitoring and data correlation. Professionals must be able to interpret logs from multiple systems simultaneously and determine whether observed behavior indicates a potential threat. This requires both technical knowledge and critical thinking skills.
Threat intelligence is another core component of modern security operations. It involves gathering information about emerging threats, understanding attacker behavior, and applying this knowledge to strengthen defenses. Cybersecurity certifications train professionals to use this intelligence effectively in real-world scenarios.
The transition from reactive to proactive security has significantly increased the demand for skilled cybersecurity professionals. Organizations now prioritize early detection and prevention strategies to minimize risk exposure.
Security Analysis and Threat Detection in Enterprise Systems
Security analysis is a foundational element of advanced cybersecurity practice. It involves examining system activity, network traffic, and user behavior to identify potential security threats.
Professionals in this field must be able to distinguish between normal system behavior and suspicious activity. This requires a deep understanding of how systems operate under typical conditions, as well as knowledge of common attack techniques.
Threat detection tools play a central role in this process. These tools collect and analyze data from various sources, including firewalls, intrusion detection systems, and endpoint devices. Cybersecurity professionals must be able to configure and interpret the output of these tools effectively.
One of the key challenges in security analysis is managing large volumes of data. Modern IT environments generate continuous streams of information, making it difficult to identify meaningful signals. Professionals must develop the ability to filter relevant data and focus on high-priority threats.
Correlation techniques are used to link related events across different systems. For example, multiple failed login attempts combined with unusual network activity may indicate a coordinated attack. Cybersecurity certifications train professionals to recognize these patterns and respond appropriately.
Vulnerability Management and Risk Assessment Practices
Vulnerability management is a structured process used to identify, evaluate, and address security weaknesses in IT systems. It is a critical component of cybersecurity operations and is heavily emphasized in advanced certification training.
The process begins with vulnerability identification, where systems are scanned to detect potential security flaws. These vulnerabilities may exist in software applications, operating systems, network configurations, or hardware components.
Once vulnerabilities are identified, they must be assessed based on their severity and potential impact. Not all vulnerabilities pose the same level of risk, so professionals must prioritize remediation efforts accordingly.
Risk assessment involves evaluating the likelihood of a vulnerability being exploited and the potential consequences of such an event. This requires both technical analysis and business understanding, as security risks often have operational and financial implications.
After assessment, remediation strategies are implemented. These may include applying security patches, reconfiguring systems, or implementing additional security controls. Cybersecurity professionals must ensure that remediation efforts do not disrupt system functionality.
Continuous monitoring is essential in vulnerability management. New vulnerabilities are discovered regularly, and systems must be reassessed to ensure ongoing protection.
Security Architecture and System Protection Design
Security architecture refers to the design and structure of secure IT systems. It involves integrating security controls into the foundational design of networks, applications, and infrastructure.
A well-designed security architecture ensures that systems are protected at multiple layers. This concept is often referred to as defense in depth, where multiple security mechanisms work together to reduce risk exposure.
Network segmentation is a common architectural strategy used to isolate sensitive systems from less secure environments. This limits the spread of attacks and reduces the potential impact of security breaches.
Access control mechanisms are also integrated into the security architecture. These controls determine who can access specific systems and what actions they can perform. Proper access control is essential for preventing unauthorized activity.
Encryption is another critical component of security architecture. It ensures that data remains protected during transmission and storage. Cybersecurity professionals must understand how to implement and manage encryption technologies effectively.
Security architecture also includes monitoring and logging systems. These systems provide visibility into network activity and help detect potential threats in real time.
Incident Response and Digital Forensics Principles
Incident response is the process of identifying, managing, and mitigating security breaches or cyberattacks. It is a structured approach designed to minimize damage and restore normal operations as quickly as possible.
The incident response process typically begins with detection. Security systems identify unusual activity or confirmed breaches, triggering an investigation.
Once an incident is confirmed, containment measures are implemented to prevent further damage. This may involve isolating affected systems or blocking malicious traffic.
After containment, eradication procedures are carried out to remove malicious elements from the system. This includes deleting malware, closing vulnerabilities, and restoring affected components.
Recovery is the next stage, where systems are restored to normal operation. This may involve restoring data from backups and verifying system integrity.
Post-incident analysis is a critical step in improving future security. It involves reviewing the incident to identify root causes and implementing improvements to prevent recurrence.
Digital forensics plays a key role in incident response. It involves collecting and analyzing evidence from compromised systems to understand how an attack occurred. This requires careful handling of data to ensure its integrity and admissibility.
Ethical Hacking and Penetration Testing Methodologies
Ethical hacking, also known as penetration testing, is a controlled process used to identify security weaknesses in systems by simulating real-world attacks. This practice is essential for strengthening organizational defenses.
Penetration testing begins with planning and reconnaissance. Professionals gather information about target systems to understand potential entry points and vulnerabilities.
The next phase involves scanning and analysis. Tools are used to identify open ports, services, and potential weaknesses in the system.
Exploitation is the process of attempting to take advantage of identified vulnerabilities. This is done in a controlled environment to assess the potential impact of real attacks.
After exploitation, professionals evaluate the extent of system compromise and document findings. This information is used to develop remediation strategies.
Reporting is a critical component of penetration testing. It involves documenting vulnerabilities, explaining their impact, and recommending corrective actions.
Ethical hacking requires a strong understanding of legal and ethical boundaries. Professionals must operate within authorized limits and ensure that testing does not disrupt system operations.
Professional Growth in Cybersecurity Roles
Cybersecurity certifications provide a structured pathway for professional development in the security field. As individuals progress through certification levels, they gain access to more advanced roles and responsibilities.
Entry-level roles may involve basic security monitoring and support tasks. Mid-level roles focus on analysis, vulnerability management, and incident response. Advanced roles involve security architecture, strategy development, and leadership responsibilities.
The demand for cybersecurity professionals continues to grow as organizations face increasing digital threats. This has made cybersecurity one of the most critical areas within the IT industry.
Professionals who develop expertise in this field are well-positioned for long-term career growth. The combination of technical knowledge, analytical skills, and practical experience is highly valued across industries.
Cybersecurity remains a dynamic and evolving discipline, requiring continuous learning and adaptation to new challenges.
Conclusion
CompTIA certifications collectively form a structured framework for building and validating IT skills across multiple domains, including foundational computing, infrastructure management, networking, cloud computing, and cybersecurity. Their value lies not only in individual certifications but in the broader career pathway they create, allowing professionals to progress logically and measurably. This structured progression is especially important in an industry where technologies evolve rapidly, and job roles continuously expand in complexity.
At the foundational level, CompTIA certifications establish essential technical literacy. They ensure that individuals entering the IT field understand core computing concepts such as hardware functionality, operating systems, basic networking, and introductory security principles. This baseline knowledge is critical because nearly every advanced IT role depends on these fundamentals. Without a strong foundation, professionals often struggle to adapt to more complex systems later in their careers.
As professionals move beyond entry-level knowledge, infrastructure-focused certifications provide the technical depth required to manage real-world systems. These certifications build competence in areas such as server administration, cloud environments, virtualization, and enterprise networking. In modern IT ecosystems, infrastructure is rarely isolated; instead, it operates in hybrid environments where on-premises systems and cloud platforms work together. Infrastructure certifications prepare professionals to navigate this complexity with confidence.
Cybersecurity certifications represent the most advanced technical layer within the CompTIA ecosystem. These credentials focus on defending systems against increasingly sophisticated threats. Rather than simply reacting to incidents, cybersecurity professionals are trained to analyze, predict, and prevent security breaches. This includes vulnerability assessment, threat detection, incident response, and security architecture design. In a digital environment where cyberattacks are becoming more frequent and more complex, these skills are essential for organizational survival and resilience.
One of the most important strengths of CompTIA certifications is their vendor-neutral design. Unlike certifications tied to specific technologies or platforms, CompTIA focuses on universal principles that apply across different systems and environments. This approach provides professionals with long-term flexibility. Whether working in a Windows-based enterprise, a Linux server environment, or a multi-cloud architecture, the core skills remain applicable. This adaptability is a significant advantage in an industry where technology stacks change frequently.
Another key benefit of CompTIA certifications is their alignment with real-world job roles. Each certification is developed with input from industry professionals to ensure that it reflects current workplace demands. As a result, certified individuals are not only theoretically knowledgeable but also practically prepared to perform job functions effectively. This alignment between certification content and job requirements increases employability and reduces the gap between learning and professional application.
The stackable certification model further enhances career development by allowing professionals to combine multiple certifications into recognized skill profiles. This modular approach reflects how IT careers naturally evolve, with individuals accumulating expertise in different but related areas over time. By stacking certifications, professionals can demonstrate specialization in fields such as network infrastructure, cloud administration, or security analysis. This structured accumulation of skills provides a clearer representation of professional capability than isolated certifications alone.
From an industry perspective, CompTIA certifications contribute significantly to workforce standardization. Organizations benefit from having a consistent benchmark to evaluate technical skills across candidates and employees. This reduces uncertainty in hiring decisions and helps ensure that IT teams possess the necessary competencies to manage critical systems. In sectors where reliability and security are essential, such standardization is particularly valuable.
The certifications also support career mobility across industries and geographic regions. Because they are globally recognized, professionals can pursue opportunities in different markets without needing to revalidate their skills through vendor-specific credentials. This global recognition enhances career flexibility and opens pathways to international employment opportunities.
In terms of long-term professional development, CompTIA certifications encourage continuous learning. The requirement for renewal ensures that professionals stay updated with evolving technologies and industry practices. This is especially important in IT, where outdated knowledge can quickly become irrelevant. Continuous education helps professionals remain competitive and ensures that their skills remain aligned with current technological standards.
Salary potential and career advancement opportunities are also positively influenced by certification achievement. While compensation varies based on experience, location, and role, certified professionals generally have access to higher-level positions and more specialized job functions. Certifications often serve as a gateway to roles in cybersecurity analysis, network engineering, system administration, and cloud infrastructure management.
Ultimately, CompTIA certifications represent more than just technical credentials. They form a structured learning and career development system that supports individuals from entry-level positions through advanced technical roles. By combining foundational knowledge, specialized skills, and continuous learning, these certifications create a sustainable pathway for long-term success in the IT industry.