Common Vulnerabilities and Exposures, widely known as CVE, represent a globally accepted system for identifying and cataloging cybersecurity weaknesses. These identifiers are not random strings but structured references that allow security professionals to communicate about vulnerabilities with precision and consistency. Without such a system, the cybersecurity landscape would be fragmented, with different organizations naming the same issue in different ways, leading to confusion and inefficiency. CVE provides a standardized language that enables coordination across industries, vendors, and security teams.
At its core, CVE is a publicly accessible catalog of known vulnerabilities. Each entry corresponds to a specific flaw in software, hardware, or systems that could potentially be exploited. These entries are used by security tools, analysts, and organizations to track, assess, and respond to threats in a structured manner. The system plays a foundational role in vulnerability management and threat intelligence.
The importance of CVE becomes evident when examining how modern digital environments operate. Organizations rely on interconnected systems, cloud platforms, applications, and networks. A single vulnerability, if left unidentified or unpatched, can compromise entire infrastructures. CVE ensures that such weaknesses are documented and shared globally, enabling proactive defense strategies.
The Origin and Purpose of the CVE System
The CVE program was introduced in 1999 as a response to the growing need for a unified method of identifying cybersecurity vulnerabilities. Before its introduction, different security databases and vendors used their own naming conventions, which made it difficult to correlate information across platforms. This lack of standardization created inefficiencies in vulnerability tracking and response.
The primary purpose of CVE is to provide a common reference point. By assigning a unique identifier to each vulnerability, CVE ensures that everyone—from security researchers to system administrators—is referring to the same issue. This consistency improves communication, reduces duplication of effort, and enhances collaboration across the cybersecurity ecosystem.
Another key objective of CVE is transparency. By making vulnerability information publicly available, the system empowers organizations to understand potential risks and take appropriate action. This open approach supports a more secure digital environment by encouraging shared knowledge and collective defense.
Decoding the Structure of CVE Identifiers
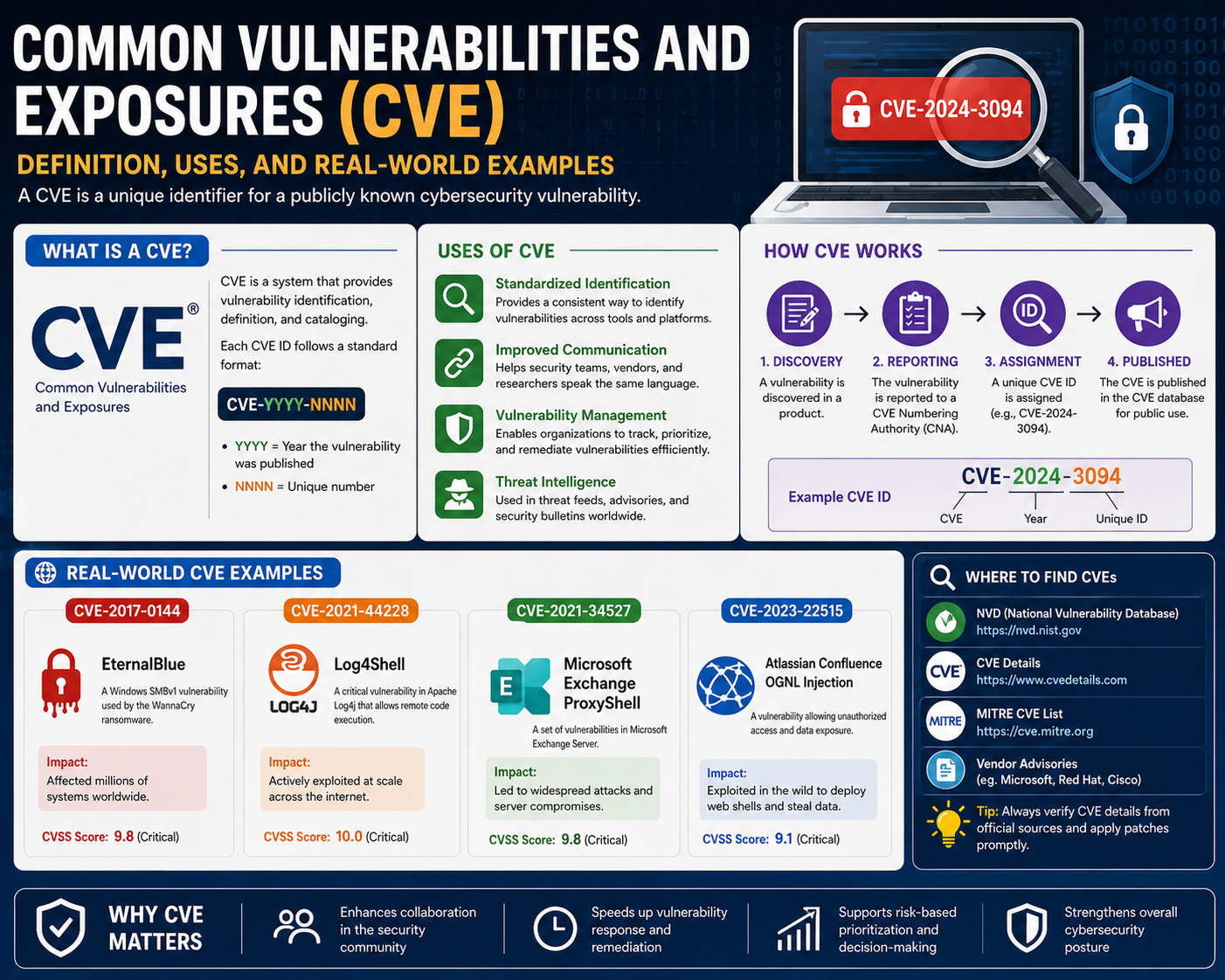
CVE identifiers follow a standardized format that conveys specific information about the vulnerability. Each ID is structured as CVE followed by a year and a unique numerical sequence. For example, CVE-2021-44228 refers to a vulnerability identified in the year 2021, with the number serving as its unique identifier.
The year component indicates when the vulnerability was first reported or assigned. It does not necessarily reflect when the vulnerability was discovered or exploited, but rather when it was officially recorded within the CVE system. The numerical portion ensures that each entry is distinct, even if multiple vulnerabilities are discovered within the same year.
This structured approach allows for easy indexing and retrieval of information. Security professionals can quickly reference a CVE ID to access detailed information about the vulnerability, including its description, impact, and related resources. The simplicity and consistency of this format make it highly effective for large-scale vulnerability management.
Key Elements Found in a CVE Entry
A CVE entry is more than just an identifier. It includes several components that provide essential context about the vulnerability. One of the most important elements is the description, which explains the nature of the flaw and how it can be exploited. This description is typically concise but informative, offering enough detail for security professionals to understand the risk.
Another critical component is the publication date. This indicates when the vulnerability was officially added to the CVE database. In addition, entries often include a last updated date, which reflects any revisions or additional information that has been incorporated over time. These timestamps help organizations track the evolution of a vulnerability and stay informed about new developments.
CVE entries also include references to external sources. These references may point to advisories, technical analyses, or vendor documentation that provide deeper insights into the vulnerability. While CVE itself does not offer remediation steps, these references often guide users toward solutions and mitigation strategies.
The Role of CVE in Modern Cybersecurity Practices
CVE plays a central role in how organizations approach cybersecurity. It serves as a foundational element in vulnerability management programs, enabling teams to identify, prioritize, and address security risks. By leveraging CVE data, organizations can maintain an up-to-date understanding of known threats and take proactive measures to protect their systems.
Security tools such as vulnerability scanners rely heavily on CVE data. These tools scan systems for known vulnerabilities and map their findings to CVE identifiers. This allows security teams to quickly assess the severity of issues and determine appropriate remediation actions. Without CVE, such tools would lack a standardized framework for reporting and analysis.
CVE also supports incident response efforts. When a security breach occurs, analysts often refer to CVE entries to understand the vulnerabilities that may have been exploited. This information helps in identifying attack vectors, assessing damage, and preventing future incidents.
Understanding CVE Numbering Authorities (CNAs)
CVE Numbering Authorities, or CNAs, are organizations responsible for assigning CVE identifiers to newly discovered vulnerabilities. These entities play a crucial role in maintaining the integrity and accuracy of the CVE system. Each CNA operates within a defined scope, which may تشمل specific products, technologies, or regions.
Vendor CNAs are typically large technology companies that manage vulnerabilities within their own products. When a flaw is discovered, these organizations evaluate the issue, assign a CVE ID, and publish relevant information. This ensures that vulnerabilities are documented quickly and accurately.
Research-focused CNAs specialize in identifying and analyzing vulnerabilities across various systems. These organizations contribute to the CVE database by uncovering new threats and ensuring they are properly classified. Their work enhances the overall quality and comprehensiveness of the CVE system.
Third-party CNAs often operate at a broader level, covering entire sectors or regions. They may coordinate vulnerability reporting across multiple organizations and ensure that issues affecting critical infrastructure are properly documented. Their role is particularly important in maintaining consistency and coverage across diverse environments.
Why CVE Standardization Matters
Standardization is one of the most significant advantages of the CVE system. In a field as complex as cybersecurity, consistency is essential for effective communication and collaboration. CVE provides a universal language that bridges gaps between different tools, organizations, and regions.
Without CVE, the same vulnerability could be described in multiple ways, leading to confusion and inefficiency. Security teams would struggle to correlate information, and important details could be overlooked. CVE eliminates this problem by assigning a single, globally recognized identifier to each vulnerability.
This standardization also enhances interoperability between security tools. Different systems can share and interpret vulnerability data بسهولة because they rely on the same set of identifiers. This integration improves efficiency and enables more comprehensive security strategies.
How CVE Supports Risk Management and Compliance
Risk management is a critical aspect of cybersecurity, and CVE plays a vital role in this process. By providing detailed information about known vulnerabilities, CVE allows organizations to assess potential risks and اتخاذ informed decisions. Security teams can prioritize vulnerabilities based on their severity and potential impact, ensuring that critical issues are addressed promptly.
CVE also supports regulatory compliance. Many security standards and frameworks require organizations to monitor and address known vulnerabilities. CVE provides a reliable source of information that helps organizations meet these requirements. Auditors often reference CVE data to verify that appropriate security measures are in place.
In addition, CVE contributes to transparency and accountability. By documenting vulnerabilities in a public database, it ensures that organizations cannot ignore known issues. This openness encourages responsible behavior and fosters a culture of continuous improvement in cybersecurity practices.
The Broader Impact of CVE on the Cybersecurity Ecosystem
The influence of CVE extends beyond individual organizations. It plays a key role in shaping the global cybersecurity landscape. By providing a centralized repository of vulnerability information, CVE enables collaboration بين researchers, vendors, and security professionals worldwide.
This collaborative approach accelerates the discovery and resolution of vulnerabilities. عندما يتم الكشف عن مشكلة جديدة، يمكن للمجتمع الأمني بأكمله العمل معًا لتحليلها ومعالجتها. This collective effort enhances the overall resilience of digital systems.
CVE also supports innovation in security technologies. Developers of security tools rely on CVE data to improve their products and provide more accurate detection capabilities. This continuous feedback loop drives advancements in cybersecurity and helps organizations stay ahead of evolving threats.
The Growing Importance of CVE in a Digital-First World
As digital transformation continues to reshape industries, the أهمية CVE becomes even more pronounced. Organizations are increasingly dependent on complex systems that span cloud environments, الإنترنت, and mobile platforms. This complexity introduces new vulnerabilities that must be identified and managed effectively.
CVE provides the foundation for addressing these challenges. By maintaining a comprehensive and standardized catalog of vulnerabilities, it enables organizations to navigate the پیچیدگی of modern cybersecurity. It ensures that even as technology evolves, there remains a consistent framework for identifying and addressing risks.
The future of cybersecurity will continue to rely on systems like CVE. As threats become more sophisticated, the need for accurate, timely, and standardized vulnerability information will only increase. CVE stands as a critical pillar in this ongoing effort to secure the digital world.
Advanced Understanding of CVE Classification and Vulnerability Taxonomy
The Common Vulnerabilities and Exposures system is not simply a list of security issues but a structured taxonomy that organizes vulnerabilities in a way that allows for systematic analysis and response. As cybersecurity ecosystems have expanded, CVE has evolved into a foundational classification framework that supports both technical and operational decision-making. Each vulnerability recorded within the system is part of a larger classification effort that enables organizations to understand not just individual flaws but patterns of weakness across technologies and environments.
CVE entries are categorized based on the nature of the vulnerability and the type of system it affects. This classification is essential for identifying trends in cyber threats. For example, recurring issues in authentication mechanisms, memory management, or input validation often indicate systemic design weaknesses rather than isolated bugs. By analyzing CVE data at scale, security researchers can identify these patterns and recommend architectural improvements.
The taxonomy also helps in prioritizing vulnerabilities. Not all CVEs carry the same level of risk. Some may allow remote code execution, while others may only expose limited information. Understanding the classification context allows security teams to allocate resources effectively. Instead of treating every vulnerability equally, organizations can focus on those that pose the highest operational risk.
The Lifecycle of a CVE Entry from Discovery to Publication
Every CVE entry follows a structured lifecycle that begins with the discovery of a vulnerability and ends with its publication in the global database. This lifecycle is critical for ensuring accuracy, validation, and consistency in how vulnerabilities are reported.
The process begins when a researcher, vendor, or security team identifies a potential flaw. This discovery stage often involves technical analysis, proof-of-concept development, and verification of exploitability. Once confirmed, the vulnerability is reported to a CVE Numbering Authority, which evaluates whether it meets the criteria for inclusion in the CVE system.
After validation, a unique CVE identifier is assigned. This step ensures that the vulnerability can be tracked consistently across systems and documentation. The assignment stage is crucial because it prevents duplication and ensures that all references point to the same issue.
Once assigned, the CVE entry is published with a basic description and relevant metadata. Over time, additional information may be appended, including severity scores, mitigation guidance, and references to external analyses. This evolving nature ensures that CVE entries remain relevant as new insights emerge.
The Role of Vulnerability Scoring and Risk Assessment Models
While CVE itself does not assign severity levels, it integrates closely with external scoring systems that evaluate the impact of vulnerabilities. These scoring systems analyze factors such as exploitability, potential damage, and attack complexity. By combining CVE identifiers with risk assessment models, organizations can better understand the urgency of addressing specific vulnerabilities.
Risk assessment models typically evaluate multiple dimensions of a vulnerability. These include the ease of exploitation, the level of access required, and the potential consequences of a successful attack. For example, a vulnerability that allows remote code execution without authentication is considered significantly more severe than one that requires physical access.
The integration of CVE with risk scoring enables automated vulnerability management. Security tools can prioritize remediation efforts based on severity scores linked to CVE entries. This automation reduces manual workload and ensures that critical issues are addressed promptly.
CVE in Threat Intelligence and Cybersecurity Operations
CVE plays a central role in modern threat intelligence operations. Security teams rely on CVE data to correlate observed activity with known vulnerabilities. When unusual behavior is detected in a network, analysts often check whether it matches exploitation patterns associated with specific CVEs.
Threat intelligence platforms aggregate CVE data from multiple sources to provide a comprehensive view of the threat landscape. These platforms help organizations identify emerging threats and understand how vulnerabilities are being exploited in the real world. By linking CVE entries with threat intelligence feeds, security teams gain actionable insights into attacker behavior.
In operational environments, CVE data is used to enhance monitoring and detection systems. Intrusion detection systems and endpoint protection tools often include signatures linked to CVE identifiers. These signatures allow systems to detect known exploit attempts and respond automatically.
CVE and the Software Development Lifecycle
The integration of CVE into the software development lifecycle has become increasingly important. Developers now consider vulnerability management as part of the design and coding process rather than a post-deployment activity. This shift reflects the growing recognition that security must be built into systems from the ground up.
During development, security testing tools scan code for potential vulnerabilities and map findings to CVE entries. This allows developers to understand whether similar issues have been identified in other systems. By referencing CVE data, developers can avoid repeating known mistakes and adopt secure coding practices.
In the testing phase, CVE-based analysis helps identify vulnerabilities before software is released. This proactive approach reduces the likelihood of security incidents in production environments. Once software is deployed, continuous monitoring ensures that newly discovered CVEs are tracked and addressed through updates and patches.
The Relationship Between CVE and Patch Management Systems
Patch management is one of the most critical processes in cybersecurity, and CVE serves as a key reference point for identifying which patches are required. When a vulnerability is assigned a CVE identifier, vendors typically release patches that address the issue. These patches are then mapped to the corresponding CVE entry.
Organizations use this mapping to prioritize updates across their systems. Instead of manually analyzing each vulnerability, IT teams can reference CVE identifiers to determine which patches are necessary. This streamlines the remediation process and reduces the risk of overlooking critical updates.
Patch management systems often integrate directly with CVE databases. This integration enables automated detection of missing patches based on known vulnerabilities. As a result, organizations can maintain a more secure environment with minimal manual intervention.
CVE in Enterprise Security Architecture
In enterprise environments, CVE serves as a foundational component of security architecture. Large organizations operate complex infrastructures that include cloud services, on-premises systems, and third-party applications. Managing vulnerabilities across these environments requires a unified approach, and CVE provides the necessary framework.
Security operations centers use CVE data to maintain visibility across all systems. By mapping vulnerabilities to CVE identifiers, organizations can create centralized dashboards that display risk exposure in real time. This visibility is essential for maintaining security at scale.
CVE also supports compliance and governance efforts within enterprises. Many regulatory frameworks require organizations to maintain accurate records of known vulnerabilities and their remediation status. CVE provides a standardized method for documenting this information.
The Evolution of Exploitation Techniques and CVE Tracking
As cyber threats evolve, so do the techniques used by attackers. CVE plays a critical role in tracking these evolving exploitation methods. When a new attack technique is discovered, it is often associated with one or more CVE entries that describe the underlying vulnerabilities being exploited.
Attackers frequently combine multiple vulnerabilities to achieve their objectives. CVE helps analysts understand these combinations by providing a structured view of each contributing flaw. This enables more effective defense strategies that address the root causes of attacks rather than just their symptoms.
The evolution of exploitation techniques has also led to the development of more sophisticated CVE entries. Modern entries often include detailed descriptions of attack vectors, prerequisites, and potential impacts. This level of detail enhances the ability of security teams to anticipate and mitigate threats.
CVE in Cloud and Distributed Systems Security
The rise of cloud computing has introduced new challenges for vulnerability management. Distributed systems operate across multiple environments, making it difficult to track and remediate vulnerabilities consistently. CVE provides a unifying framework that applies across cloud, hybrid, and on-premises infrastructures.
Cloud service providers regularly monitor CVE databases to identify vulnerabilities that may affect their platforms. When relevant CVEs are discovered, providers issue updates and advisories to protect users. This coordinated response helps maintain security across large-scale distributed systems.
In multi-cloud environments, CVE data is used to ensure consistency in security policies. Organizations can apply uniform vulnerability management practices across different platforms, reducing complexity and improving overall security posture.
The Impact of CVE on Security Automation and AI Systems
Automation has become a key component of modern cybersecurity, and CVE plays a central role in enabling automated security systems. Machine learning models and AI-driven tools use CVE data to train algorithms that detect and respond to threats.
These systems analyze patterns in CVE entries to predict potential vulnerabilities in new software. By learning from historical data, AI systems can identify weaknesses before they are exploited. This predictive capability represents a significant advancement in cybersecurity.
Automation also extends to incident response. When a CVE-linked threat is detected, automated systems can initiate predefined response actions such as isolating affected systems or applying patches. This reduces response times and minimizes damage.
Global Collaboration and the Expanding CVE Ecosystem
The CVE system is maintained through global collaboration between researchers, organizations, and governments. This collaborative model ensures that vulnerabilities are identified and addressed across diverse technological landscapes.
International cooperation is essential for maintaining the effectiveness of CVE. Cyber threats do not respect geographical boundaries, and vulnerabilities discovered in one region can have global implications. CVE provides a shared platform for addressing these challenges collectively.
As the cybersecurity ecosystem continues to expand, CVE remains a central pillar of coordination. Its role in enabling communication, standardization, and collaboration ensures that it remains relevant in an increasingly complex digital environment.
CVE Integration Across Modern Security Tooling and Infrastructure
Common Vulnerabilities and Exposures has become deeply embedded in the operational fabric of modern cybersecurity tooling. It is no longer treated as a standalone reference database but as a connective layer that enables interoperability between scanners, monitoring systems, orchestration platforms, and incident response frameworks. This integration allows security ecosystems to function cohesively rather than as isolated tools producing fragmented outputs.
In vulnerability scanners, CVE identifiers serve as the primary mapping mechanism between detected weaknesses and known security issues. When a scan is executed, the tool does not simply flag a generic “risk” but correlates findings with specific CVE entries. This mapping provides context such as exploit behavior, affected versions, and historical exploitation patterns. Without CVE integration, vulnerability data would remain abstract and significantly less actionable.
Security information and event management systems also rely heavily on CVE tagging. Logs and alerts are enriched with CVE references when known exploit signatures are detected. This enrichment allows analysts to quickly prioritize incidents based on known severity patterns. Instead of investigating every alert from scratch, teams can immediately understand the nature of the threat by referencing the associated CVE.
In orchestration and automated response systems, CVE identifiers act as triggers. When a vulnerability matching a critical CVE is detected, automated workflows can be initiated. These workflows may include patch deployment, network segmentation, or temporary service isolation. The use of CVE in automation reduces response latency and ensures consistent handling of known threats across environments.
CVE in Penetration Testing and Ethical Exploitation Analysis
Penetration testing methodologies are heavily structured around CVE data. Ethical hackers use CVE databases to identify known vulnerabilities in target systems before attempting controlled exploitation. This approach allows testers to simulate real-world attack scenarios based on documented weaknesses rather than speculative assumptions.
During reconnaissance, penetration testers map system versions and configurations against CVE listings. This mapping helps identify potential entry points that may be exploited. For example, outdated software versions often correlate with known CVEs that describe specific exploit techniques. By leveraging this information, testers can construct realistic attack paths.
Exploitation frameworks also incorporate CVE identifiers into their modules. Each exploit is often labeled with a corresponding CVE, allowing testers to select appropriate payloads based on discovered vulnerabilities. This structured approach ensures consistency in testing and aligns findings with industry-standard vulnerability references.
Post-exploitation analysis further relies on CVE data to assess impact. Testers evaluate how a vulnerability, once exploited, could lead to privilege escalation, data exfiltration, or lateral movement. CVE entries provide foundational context that supports these assessments and helps organizations understand real-world risk exposure.
The Role of CVE in Red Team and Blue Team Operations
In adversarial security simulations, CVE plays a dual role in both offensive and defensive strategies. Red teams use CVE data to emulate threat actors by exploiting known vulnerabilities in controlled environments. This allows organizations to evaluate their defensive posture under realistic attack conditions.
Red team operations often prioritize high-impact CVEs that are actively exploited in the wild. By focusing on these vulnerabilities, they simulate advanced persistent threats and test organizational resilience. CVE identifiers provide a standardized way to document and communicate these simulated attack vectors.
On the defensive side, blue teams rely on CVE intelligence to strengthen detection and response capabilities. Security controls are tuned to recognize patterns associated with specific CVEs. This includes updating intrusion detection rules, refining firewall policies, and enhancing endpoint monitoring.
The interaction between red and blue teams around CVE data creates a continuous feedback loop. Findings from simulated attacks lead to improved defenses, while evolving CVE disclosures inform new testing scenarios. This dynamic strengthens overall security maturity within organizations.
CVE and Vulnerability Prioritization in Large-Scale Environments
Large-scale enterprise environments face the challenge of managing thousands of assets and an even larger number of potential vulnerabilities. CVE provides a structured method for prioritizing remediation efforts in such complex ecosystems.
Prioritization begins with mapping all detected vulnerabilities to their corresponding CVE identifiers. Once mapped, organizations can analyze factors such as exploit availability, exposure level, and asset criticality. This analysis helps determine which vulnerabilities require immediate attention.
Not all CVEs carry equal operational risk. Some may exist in isolated systems with limited exposure, while others may affect internet-facing infrastructure. CVE-based prioritization frameworks help security teams distinguish between theoretical and actionable risks.
In mature security programs, prioritization is often automated. Systems continuously ingest CVE updates and dynamically adjust risk scores based on changing conditions. This ensures that newly discovered vulnerabilities are rapidly assessed and addressed without manual delay.
The Relationship Between CVE and Zero-Day Vulnerabilities
Zero-day vulnerabilities represent security flaws that are actively exploited before a public patch or disclosure is available. While CVE is primarily a catalog of known vulnerabilities, it also plays an important role in the lifecycle of zero-day discovery and disclosure.
Once a zero-day vulnerability is identified and confirmed, it is eventually assigned a CVE identifier. This transition marks the shift from unknown threat to documented vulnerability. The assignment process ensures that even previously undisclosed issues become part of the global security knowledge base.
The period between discovery and CVE assignment is often critical. During this time, organizations must rely on heuristic defenses, behavioral detection, and threat intelligence to mitigate risk. Once a CVE is assigned, more structured remediation strategies become possible.
CVE tracking also helps organizations understand historical zero-day trends. By analyzing past disclosures, security teams can identify patterns in exploitation techniques and target systems. This historical insight supports proactive defense strategies.
CVE in Critical Infrastructure Protection
Critical infrastructure systems such as energy grids, transportation networks, and communication systems rely heavily on stable and secure software environments. CVE plays a key role in protecting these systems by providing early warnings about vulnerabilities that could be exploited at scale.
Security teams responsible for critical infrastructure continuously monitor CVE disclosures to identify risks that could impact operational continuity. Because these systems often have long lifecycle components, legacy vulnerabilities remain a persistent concern.
CVE data is used to assess systemic risk across interconnected infrastructure components. A single vulnerability in a widely used protocol or device can have cascading effects across multiple sectors. CVE helps identify these shared dependencies and supports coordinated remediation efforts.
Governments and regulatory bodies also rely on CVE frameworks to issue security advisories for critical infrastructure. These advisories often prioritize vulnerabilities based on potential societal impact rather than just technical severity.
CVE and Software Supply Chain Security
Modern software development relies heavily on third-party libraries, frameworks, and components. This interconnected ecosystem introduces supply chain risks that CVE helps to identify and manage.
When a vulnerability is discovered in a widely used library, it is assigned a CVE identifier that immediately alerts downstream users. This visibility is essential for maintaining security across dependent applications. Without CVE, tracking vulnerabilities across supply chains would be extremely difficult.
Organizations increasingly maintain software bills of materials that map components to known CVEs. This mapping allows them to quickly assess whether their applications are affected by newly disclosed vulnerabilities. It also supports compliance and audit requirements.
Supply chain attacks often exploit vulnerabilities in less visible components. CVE helps bring these hidden risks to the surface by documenting weaknesses regardless of where they occur in the software stack.
The Evolution of CVE Data Consumption in Machine Learning Systems
Machine learning systems have introduced new methods of analyzing CVE data at scale. Instead of treating each vulnerability as an isolated entry, these systems examine relationships between CVEs to identify broader threat patterns.
By training on historical CVE data, machine learning models can predict which types of vulnerabilities are likely to emerge in specific technologies. This predictive capability supports proactive security design and risk mitigation.
Natural language processing techniques are also applied to CVE descriptions. These techniques extract meaningful features such as vulnerability type, affected components, and exploitation methods. This structured interpretation enables more advanced analytics.
In threat detection systems, machine learning models use CVE correlations to identify anomalous behavior that may indicate exploitation attempts. This enhances detection accuracy and reduces false positives.
CVE and the Future of Vulnerability Intelligence
The future of CVE is closely tied to the evolution of vulnerability intelligence systems. As cyber threats become more sophisticated, CVE is expected to integrate more deeply with real-time intelligence platforms.
Future systems are likely to provide dynamic CVE enrichment, where entries are continuously updated with live threat data. This would include active exploitation indicators, attack frequency metrics, and global impact assessments.
Automation will further expand the role of CVE in cybersecurity operations. Security systems will increasingly rely on CVE-driven decision-making without human intervention. This includes automated patching, adaptive defense mechanisms, and self-healing infrastructure.
Interoperability between CVE and other cybersecurity frameworks will also increase. Unified vulnerability models may emerge that combine CVE with broader threat intelligence standards, enabling more holistic security management.
As digital ecosystems continue to expand, CVE will remain a foundational component of vulnerability management. Its role will evolve from a static reference system into a dynamic intelligence layer that supports real-time security decision-making across global infrastructures.
Conclusion
The Common Vulnerabilities and Exposures system has become a defining structure in modern cybersecurity, primarily because it brings order to a space that would otherwise be fragmented and inconsistent. Instead of treating vulnerabilities as isolated technical issues described in different ways by different organizations, CVE assigns each one a unique identifier that can be universally recognized. This shared reference point allows security professionals across industries and regions to communicate clearly about the same issue without confusion or duplication. In an environment where thousands of vulnerabilities are discovered every year, this consistency is not just useful but essential for maintaining coordinated defense strategies.
CVE plays a critical role in turning raw vulnerability data into actionable intelligence. On its own, a software flaw or system weakness has limited meaning unless it is contextualized. Once it is assigned a CVE identifier, however, it becomes part of a global knowledge system that can be referenced in security tools, documentation, and response workflows. This transformation is what makes CVE so valuable in real-world cybersecurity operations. It bridges the gap between discovery and action, allowing teams to quickly understand what a vulnerability is, how it behaves, and why it matters.
In practical terms, CVE significantly improves how organizations handle security operations. Security teams are constantly dealing with alerts, scans, and logs that contain vast amounts of technical data. Without a standardized system, interpreting this data would require significant manual effort and lead to inconsistent responses. CVE simplifies this process by enabling tools to map detected vulnerabilities directly to known entries. This means that when a vulnerability is identified, teams can immediately access structured information about it rather than starting from scratch. The result is faster response times, more accurate assessments, and more efficient use of security resources.
Another important aspect of CVE is its role in prioritization. Not all vulnerabilities carry the same level of risk, and organizations must make decisions about which issues to address first. CVE helps support this decision-making process by serving as a foundation for risk analysis systems. When combined with additional data such as exploit availability, system exposure, and potential impact, CVE entries allow security teams to determine which vulnerabilities pose the greatest threat. This ensures that limited resources are focused on the most critical issues rather than being spread evenly across all detected flaws.
The importance of CVE extends beyond individual organizations and into the broader cybersecurity ecosystem. One of its greatest strengths is its ability to enable global collaboration. Cybersecurity threats do not respect geographical boundaries, and vulnerabilities discovered in one part of the world can quickly be exploited elsewhere. CVE provides a shared framework that allows researchers, vendors, and security teams worldwide to coordinate their understanding of these threats. When a vulnerability is assigned a CVE identifier, it becomes instantly recognizable across the global security community, enabling faster communication and more coordinated responses.
This shared understanding also improves the vulnerability disclosure process. Researchers who identify security flaws can report them in a standardized format, ensuring that their findings are properly recorded and tracked. Vendors can then respond with patches or mitigations that reference the same CVE identifier, creating a clear and traceable link between discovery and resolution. This structured workflow reduces ambiguity and ensures that critical security issues are addressed in a timely and transparent manner.
CVE also plays a significant role in supporting long-term risk management strategies. Organizations are not only concerned with immediate threats but also with understanding their overall exposure to vulnerabilities over time. By maintaining records of CVE data, security teams can analyze patterns and identify recurring weaknesses in their systems. This insight helps improve secure design practices, strengthens development processes, and reduces the likelihood of repeated mistakes. Over time, this contributes to a more resilient security posture.
As digital environments become more complex, the importance of CVE continues to grow. Modern infrastructure now includes cloud platforms, distributed systems, containerized applications, and interconnected services. Each of these introduces new layers of complexity and potential vulnerabilities. CVE provides a stable reference framework that remains consistent across all of these environments. Whether a vulnerability exists in traditional software or modern cloud architecture, it is still assigned a CVE identifier, ensuring that it can be tracked and managed in the same way.
The speed at which vulnerabilities are discovered has also increased significantly in recent years. This rapid pace makes it difficult for organizations to keep up without structured systems in place. CVE helps manage this challenge by ensuring that each new vulnerability is quickly documented and integrated into global security workflows. This reduces the time between discovery and response, which is critical in preventing exploitation.
While CVE is a technical system, its effectiveness ultimately depends on human understanding and action. Security professionals must interpret CVE data, assess its relevance to their environment, and implement appropriate responses. This requires not only technical knowledge but also judgment and experience. The system itself provides structure, but it is the people using it who determine how effectively it is applied in practice.
CVE also influences how organizations approach security culture. It reinforces the idea that vulnerabilities are not isolated incidents but part of a continuous and evolving landscape of risk. This perspective encourages ongoing monitoring, regular updates, and proactive defense strategies rather than reactive responses. Over time, this mindset becomes embedded in organizational practices, leading to stronger overall security maturity.
Another important dimension of CVE is its integration into automated systems. Modern cybersecurity increasingly relies on automation to handle large volumes of data and respond to threats in real time. CVE identifiers serve as key inputs for these automated processes. When a vulnerability is detected, systems can automatically determine its severity, check for known exploits, and trigger appropriate response actions. This reduces manual workload and ensures consistent handling of security incidents.
CVE also contributes to the advancement of predictive security models. By analyzing historical vulnerability data, machine learning systems can identify trends and patterns that help forecast future risks. This predictive capability allows organizations to prepare for potential threats before they are widely exploited. In this way, CVE is not only a record of past vulnerabilities but also a foundation for anticipating future ones.
In the broader context of cybersecurity evolution, CVE represents a stabilizing force. Despite constant changes in technology, attack methods, and infrastructure, the need for a standardized vulnerability reference system remains constant. CVE provides that stability by ensuring that every vulnerability, regardless of its origin or complexity, can be consistently identified and managed. This makes it one of the most enduring and essential components of modern digital security practice.
As cybersecurity continues to evolve, CVE will likely expand its role further, becoming even more integrated into real-time threat intelligence, automated defense systems, and global security coordination. Its value lies not only in what it currently provides but in its ability to adapt to the changing demands of the digital world while maintaining its core purpose of standardization and clarity.