Cybersecurity has evolved into one of the most critical disciplines within modern information technology environments due to the increasing dependence of organizations on digital systems, cloud computing platforms, and interconnected networks. As businesses continue to digitize operations, the number of entry points available to potential attackers expands significantly, creating a complex security landscape that demands continuous monitoring and protection. The traditional boundaries of enterprise systems have largely disappeared, replaced by hybrid infrastructures that integrate on-premises servers, cloud platforms, mobile devices, and remote access technologies. This interconnected structure increases operational efficiency but also introduces multiple layers of risk that must be carefully managed. Cyber threats are no longer isolated technical issues; they represent ongoing operational risks that can impact financial stability, customer trust, and organizational continuity. As a result, cybersecurity has become a core business requirement rather than a secondary technical function. Organizations now invest heavily in building security-aware infrastructures and ensuring that personnel at all levels possess a fundamental understanding of security principles. This shift reflects the growing recognition that human behavior, system configuration, and architectural design all contribute to the overall security posture of an organization.
Importance of Foundational Security Certification in Industry Validation
In response to the increasing complexity of cyber threats, foundational security certifications have emerged as standardized mechanisms for validating baseline knowledge and skills in cybersecurity. These certifications are widely used by organizations to assess the readiness of individuals entering security-related roles. Rather than relying solely on academic qualifications or informal experience, employers often use certification frameworks to ensure that candidates possess a verified understanding of essential security concepts. These concepts typically include threat identification, vulnerability management, risk assessment, access control, cryptographic principles, and incident response procedures. A foundational certification also demonstrates that an individual has been exposed to structured learning that aligns with industry expectations and best practices. This is particularly important in environments where security responsibilities are distributed across multiple roles, including system administrators, network engineers, and technical support staff. The certification acts as a baseline benchmark, ensuring that individuals across different technical domains share a common understanding of security principles. This shared foundation improves communication, reduces operational inconsistencies, and strengthens overall organizational defense mechanisms. It also serves as a stepping stone for advanced security roles, enabling professionals to progress toward specialized areas such as penetration testing, security architecture, and threat intelligence analysis.
Evolution of Certification Frameworks in Response to Threat Dynamics
Cybersecurity certification frameworks are periodically updated to reflect changes in technology, attack methodologies, and organizational requirements. The rapid evolution of digital systems has led to corresponding changes in how security knowledge is structured and evaluated. Earlier certification models often focused on static concepts and theoretical knowledge, but modern frameworks emphasize applied skills and scenario-based understanding. This shift is driven by the need to prepare professionals for real-world security challenges rather than purely academic assessments. As organizations adopt cloud computing, mobile integration, and distributed networks, traditional security boundaries have become less effective. Threat actors now exploit vulnerabilities across multiple layers of infrastructure, including endpoints, applications, APIs, and human interactions. Certification updates therefore aim to incorporate a more comprehensive view of cybersecurity that reflects this complexity. The updated frameworks emphasize not only technical knowledge but also analytical thinking, decision-making under pressure, and the ability to respond effectively to dynamic security incidents. This ensures that certified professionals are equipped to operate in environments where threats are constantly evolving and defensive strategies must adapt in real time. The continuous revision of certification content also highlights the importance of lifelong learning in the cybersecurity field, as static knowledge quickly becomes outdated in a rapidly changing threat landscape.
Transition Toward Structured Domain-Based Security Knowledge
Modern cybersecurity certification frameworks are organized into structured domains that reflect key areas of professional responsibility. This domain-based approach ensures that knowledge is categorized in a way that aligns with practical job functions. One of the primary domains focuses on understanding threats, attacks, and vulnerabilities. This includes the ability to identify different types of malicious activity, analyze attack vectors, and understand the techniques used by threat actors. It also involves recognizing vulnerabilities in systems, applications, and network configurations that could be exploited by attackers. Another domain focuses on system architecture and security design principles, which involves building secure infrastructures that can resist attacks and minimize risk exposure. This includes implementing segmentation strategies, secure communication protocols, and access control mechanisms. The implementation domain focuses on applying security controls in real-world environments, such as configuring firewalls, deploying encryption technologies, and managing identity systems. Operational domains emphasize continuous monitoring and incident response, ensuring that security teams can detect and respond to threats in real time. The governance domain integrates risk management, compliance requirements, and policy enforcement, ensuring that technical security measures align with organizational objectives and regulatory standards. Together, these domains create a comprehensive framework that covers both technical and strategic aspects of cybersecurity.
Modern Threat Landscape and Increasing Attack Complexity
The modern cybersecurity threat landscape is characterized by increasing complexity, diversity, and sophistication. Attackers now use a wide range of techniques to compromise systems, steal data, and disrupt operations. Social engineering remains one of the most effective attack methods, relying on psychological manipulation to trick individuals into revealing sensitive information or granting unauthorized access. These attacks often take the form of phishing emails, fraudulent messages, or impersonation attempts designed to exploit human trust. In addition to social engineering, technical attacks targeting software vulnerabilities have become more advanced. Malware has evolved from simple viruses into complex, adaptive programs capable of evading detection systems and persisting within networks for extended periods. Network-based attacks, such as distributed denial-of-service incidents, are designed to overwhelm systems by flooding them with excessive traffic, resulting in service disruptions and operational downtime. Application-level vulnerabilities, including insecure APIs and improper input validation, provide additional entry points for attackers. Cloud computing environments introduce further challenges due to shared infrastructure models and dynamic resource allocation. Misconfigurations in cloud services can lead to unintended data exposure or unauthorized access. Emerging technologies such as artificial intelligence have also contributed to the evolution of cyber threats, enabling attackers to automate reconnaissance, optimize attack strategies, and develop adaptive malware that can modify its behavior based on defensive measures. This increasing complexity requires security professionals to adopt a proactive approach that combines continuous monitoring, threat intelligence analysis, and adaptive defense strategies.
Core Security Competencies and Practical Skill Development
Modern cybersecurity frameworks emphasize the development of core competencies that combine theoretical understanding with practical application. These competencies include the ability to identify system vulnerabilities, configure and manage security controls, and respond effectively to security incidents. Professionals must understand encryption technologies and how they protect data integrity and confidentiality. Access control mechanisms are also essential, ensuring that only authorized users can access specific resources based on predefined roles and permissions. Network security principles play a critical role in protecting communication channels and preventing unauthorized interception or manipulation of data. Operational skills such as log analysis, system monitoring, and anomaly detection are increasingly important in identifying potential threats before they escalate into major incidents. Risk management is another key competency, requiring professionals to evaluate potential threats, assess their impact, and implement mitigation strategies. Governance and compliance knowledge ensures that security practices align with legal requirements and organizational policies. This combination of skills enables professionals to contribute effectively to both strategic planning and operational security management. It also ensures that security measures are not implemented in isolation but are integrated into the overall IT infrastructure of an organization.
Strategic Importance of Security Knowledge in Organizational Environments
Security knowledge has become a critical component of organizational strategy due to the increasing reliance on digital systems for business operations. Organizations must ensure that employees across different technical roles understand fundamental security principles to reduce the risk of human error and system misconfiguration. Security awareness is no longer limited to specialized teams but is distributed across all levels of IT operations. This includes system administrators responsible for maintaining server integrity, network engineers managing communication infrastructure, and developers creating secure applications. A shared understanding of security principles helps reduce inconsistencies in implementation and improves overall resilience against cyber threats. Foundational security knowledge also supports better collaboration between technical and managerial teams, enabling more effective decision-making in response to security incidents. As organizations continue to adopt new technologies and expand their digital capabilities, the importance of standardized security knowledge will continue to grow. This ensures that security remains an integral part of system design, operational management, and strategic planning across all levels of enterprise infrastructure.
Functional Breakdown of Modern Cybersecurity Domains
Modern cybersecurity knowledge frameworks are intentionally structured into functional domains that reflect how security work is performed in real enterprise environments. This domain-based structure ensures that theoretical knowledge is directly mapped to operational responsibilities, allowing professionals to transition from learning concepts to applying them in practical situations. One of the central domains focuses on threats, attacks, and vulnerabilities, which involves understanding how adversaries identify weaknesses in systems and exploit them for unauthorized access or disruption. This includes studying different categories of malware, social engineering methods, network intrusion techniques, and application-level exploits. Professionals working in this domain must develop the ability to recognize attack patterns, interpret system anomalies, and assess risk exposure in real time.
Another major domain focuses on architecture and secure system design, which emphasizes building infrastructures that are inherently resistant to compromise. This involves designing systems with layered defenses, ensuring proper segmentation of network environments, and implementing strict access control mechanisms. Secure architecture also requires understanding how different components within an IT ecosystem interact and how vulnerabilities in one area can affect the entire system. The goal is to reduce attack surfaces by ensuring that systems are designed with security principles integrated from the beginning rather than added as an afterthought.
The implementation domain focuses on applying security technologies and controls within operational environments. This includes configuring firewalls, deploying encryption systems, managing identity and authentication services, and ensuring secure communication between systems. Implementation requires not only technical knowledge but also precision and consistency, as misconfigurations can introduce significant vulnerabilities. Professionals must understand how different security tools interact and how to align configurations with organizational security policies.
Operational security forms another critical domain, centered on continuous monitoring and response activities. This involves analyzing system logs, monitoring network traffic, detecting unusual behavior, and responding to security incidents in real time. Operational security is dynamic, requiring constant vigilance and the ability to interpret complex data from multiple sources. Security teams must be able to differentiate between normal system behavior and potential indicators of compromise. This domain also includes incident response processes, which guide how organizations detect, contain, and recover from security breaches.
The final domain focuses on governance, risk, and compliance, which provides the strategic framework for all security activities. Governance defines how security policies are created and enforced, risk management evaluates potential threats and their impact, and compliance ensures adherence to regulatory requirements. Together, these domains form a complete structure that integrates technical execution with organizational strategy, ensuring that cybersecurity is both effective and aligned with broader business objectives.
Expansion of Cyber Threat Complexity and Attack Techniques
Cyber threats have evolved significantly in both complexity and scale, requiring security professionals to understand a wide variety of attack techniques. Traditional malware, once limited to simple viruses and worms, has now transformed into sophisticated, multi-stage attack tools capable of adapting to defensive mechanisms. Modern malware often operates stealthily, remaining dormant within systems while collecting data or preparing for activation at a later stage. This persistence makes detection more difficult and increases the potential impact of a successful breach.
Social engineering continues to be one of the most widely used attack methods due to its effectiveness in exploiting human behavior rather than technical vulnerabilities. Attackers often manipulate users through deception, urgency, or impersonation to gain access to sensitive information or systems. These attacks can occur through email, messaging platforms, or even voice communication, making them difficult to detect through technical controls alone. The reliance on human interaction highlights the importance of security awareness as a key defense mechanism.
Network-based attacks have also become more advanced, particularly distributed denial-of-service attacks that target system availability by overwhelming resources with excessive traffic. These attacks can disrupt services for extended periods and are often used as part of larger coordinated campaigns. Application-layer attacks exploit weaknesses in software design, such as improper input validation or insecure authentication processes. These vulnerabilities are particularly dangerous because they often exist within widely used applications that process sensitive data.
Cloud environments introduce additional security challenges due to their distributed and shared nature. Misconfigurations in cloud storage, identity management, or access controls can expose sensitive data to unauthorized users. Because cloud systems are highly dynamic, security controls must be continuously monitored and adjusted to maintain protection. Emerging technologies such as artificial intelligence have further complicated the threat landscape by enabling automated attack generation and adaptive malware that can modify behavior based on detection attempts.
Secure System Architecture and Defensive Design Principles
Secure system architecture plays a fundamental role in reducing vulnerabilities and improving resilience against cyber threats. It focuses on designing systems that minimize potential attack vectors while ensuring operational efficiency. One of the key principles in secure architecture is segmentation, which involves dividing networks into isolated zones to limit lateral movement by attackers. If one segment is compromised, proper segmentation ensures that the breach does not extend to other critical systems.
Another essential principle is least privilege access, which restricts user and system permissions to only what is necessary for their function. This minimizes the potential damage caused by compromised accounts or insider threats. Secure architecture also emphasizes redundancy and resilience, ensuring that systems remain operational even in the event of hardware failures or cyberattacks. This includes backup systems, failover mechanisms, and distributed infrastructure designs that maintain availability under adverse conditions.
Encryption is another critical component of secure system design. It ensures that data remains protected both in storage and during transmission, making it unreadable to unauthorized users. Authentication systems must also be carefully designed to prevent unauthorized access while maintaining usability for legitimate users. Multi-factor authentication has become a standard practice for strengthening identity verification by requiring multiple forms of validation.
Secure architecture is not static; it requires continuous evaluation and improvement. As new vulnerabilities are discovered and attack techniques evolve, system designs must be updated to maintain effectiveness. This ongoing process ensures that security remains aligned with technological advancements and emerging threats.
Operational Security and Continuous Monitoring Frameworks
Operational security is centered on maintaining ongoing protection of systems through continuous monitoring, analysis, and response. It involves real-time oversight of system activity to detect potential threats before they escalate into major incidents. One of the primary components of operational security is log analysis, which provides detailed records of system activity. These logs help identify unusual behavior, unauthorized access attempts, and potential security breaches.
Network monitoring is another critical function, allowing security teams to analyze traffic patterns and detect anomalies. By examining data flows, professionals can identify suspicious activity that may indicate an ongoing attack. Security information and event management systems are often used to centralize and correlate data from multiple sources, enabling faster and more accurate threat detection.
Intrusion detection systems play a key role in identifying known attack signatures and behavioral anomalies. These systems can generate alerts or automatically respond to potential threats, reducing the time between detection and response. Operational security also includes vulnerability management, which involves identifying, assessing, and addressing weaknesses in systems through patching and configuration updates.
Incident response is closely tied to operational security and involves structured procedures for handling security events. This includes detection, containment, eradication, and recovery phases. Effective incident response requires coordination between technical teams and organizational leadership to ensure a unified approach. Post-incident analysis is essential for understanding root causes and improving future defenses.
Continuous monitoring ensures that security systems remain effective over time. It enables organizations to maintain visibility across their infrastructure and respond quickly to emerging threats. This proactive approach is essential in modern environments where attacks can occur at any time and evolve rapidly.
Governance, Risk Management, and Regulatory Alignment in Security Systems
Governance, risk management, and compliance form the strategic foundation of cybersecurity operations. Governance establishes the structure and policies that guide security practices within an organization. It defines roles, responsibilities, and decision-making processes to ensure that security objectives are consistently applied across all operational areas.
Risk management focuses on identifying potential threats and evaluating their likelihood and impact. This process allows organizations to prioritize security efforts based on potential consequences. By understanding risk exposure, organizations can allocate resources more effectively and implement appropriate mitigation strategies.
Compliance ensures that organizations adhere to legal, regulatory, and industry standards. These requirements often govern how data is collected, stored, and processed. Compliance frameworks help organizations maintain trust, avoid penalties, and ensure ethical handling of information. Security professionals must understand how these regulatory requirements influence technical configurations and operational procedures.
The integration of governance, risk management, and compliance ensures that cybersecurity is not treated as an isolated technical function but as a coordinated organizational effort. This alignment strengthens overall security posture and ensures that technical controls support broader business objectives.
Integration of Cybersecurity Skills Across IT Job Roles
Modern cybersecurity responsibilities are no longer confined to dedicated security teams but are distributed across multiple IT job roles within organizations. This shift reflects the reality that security is embedded in every layer of digital infrastructure, from system configuration to application development and network management. System administrators play a critical role in maintaining secure environments by ensuring that servers, operating systems, and services are properly configured and regularly updated. They are responsible for applying patches, managing user permissions, and monitoring system health to prevent unauthorized access or exploitation. Network engineers contribute by designing and maintaining secure communication pathways, implementing firewall rules, segmenting network traffic, and ensuring that data transmission remains protected across internal and external channels.
Security analysts focus primarily on monitoring systems for suspicious activity, analyzing security logs, and investigating potential incidents. Their role requires strong analytical capabilities to distinguish between normal system behavior and potential indicators of compromise. Developers also play an increasingly important role in cybersecurity by integrating secure coding practices into software development processes. This includes validating user inputs, preventing injection attacks, and ensuring proper authentication and authorization mechanisms within applications. As organizations become more digitally dependent, the expectation that all technical personnel understand basic security principles continues to grow. This shared responsibility model ensures that security is not isolated within a single department but is embedded across all IT functions.
Hybrid Infrastructure and Multi-Environment Security Challenges
The widespread adoption of hybrid infrastructure has significantly transformed the cybersecurity landscape by combining traditional on-premises systems with cloud-based environments. This hybrid model offers flexibility, scalability, and operational efficiency, but it also introduces complex security challenges that require specialized knowledge and coordination. One of the primary challenges is maintaining consistent security policies across multiple environments. Systems that operate in different infrastructures often have varying configurations, access controls, and monitoring capabilities, which can create security gaps if not properly managed.
Identity and access management becomes particularly critical in hybrid environments, as users and systems must authenticate across multiple platforms. Ensuring that only authorized entities can access sensitive resources requires centralized identity management systems and strict authentication protocols. Cloud environments introduce additional concerns related to data storage, access visibility, and configuration management. Misconfigurations in cloud services can lead to unintended exposure of sensitive information, making continuous monitoring essential.
Another key challenge is maintaining visibility across distributed systems. Security teams must be able to monitor activity across both cloud and on-premises environments to detect anomalies and respond to threats effectively. This often requires integration of monitoring tools and centralized logging systems that provide a unified view of security events. Network complexity also increases in hybrid environments, as data flows between internal systems, external cloud platforms, and remote users. Ensuring secure communication across these channels requires encryption, segmentation, and strong access controls.
Hybrid infrastructure also introduces challenges in compliance management, as organizations must ensure that security practices meet regulatory requirements across all environments. This requires consistent policy enforcement and regular audits to verify compliance adherence. As hybrid systems continue to expand, security professionals must develop a deep understanding of how different environments interact and how security controls can be effectively applied across diverse infrastructures.
Incident Response Maturity and Organizational Preparedness
Incident response has become a central pillar of modern cybersecurity strategy, focusing on how organizations detect, manage, and recover from security events. Effective incident response requires structured processes that enable rapid identification and containment of threats. Organizations typically develop incident response frameworks that outline specific stages, including preparation, detection, analysis, containment, eradication, and recovery. Each stage plays a critical role in minimizing the impact of security incidents and restoring normal operations.
Preparation involves establishing policies, training personnel, and implementing tools that support incident detection and response. This stage ensures that teams are ready to handle security events efficiently when they occur. Detection focuses on identifying potential incidents through monitoring systems, alerts, and anomaly detection tools. Early detection is crucial in limiting the scope and severity of security breaches.
Once an incident is detected, analysis is performed to determine its nature, source, and potential impact. This step involves examining system logs, network traffic, and other data sources to understand how the incident occurred. Containment strategies are then implemented to prevent further damage, which may involve isolating affected systems or restricting access to compromised resources. Eradication focuses on removing the root cause of the incident, such as malware or unauthorized access points. Recovery involves restoring systems to normal operation and ensuring that vulnerabilities have been addressed.
Post-incident review is an essential component of maturity development, as it allows organizations to learn from past incidents and improve future response capabilities. This includes identifying weaknesses in existing processes, updating security controls, and refining detection mechanisms. Organizations with mature incident response capabilities are better equipped to handle evolving threats and minimize operational disruption.
Adaptive Defense Strategies and Continuous Security Improvement
Modern cybersecurity environments require adaptive defense strategies that evolve in response to changing threat landscapes. Static security models are no longer sufficient, as attackers continuously develop new techniques to bypass existing defenses. Adaptive security involves continuously updating controls, monitoring systems, and response mechanisms based on emerging threat intelligence and real-world incidents.
One key aspect of adaptive defense is behavioral analysis, which focuses on identifying deviations from normal system activity. Instead of relying solely on predefined attack signatures, behavioral analysis allows security systems to detect unknown or emerging threats based on unusual patterns. This approach enhances detection capabilities and reduces reliance on static rules.
Another important component is threat intelligence integration, which involves collecting and analyzing information about current and emerging threats. This intelligence is used to update security controls, improve detection accuracy, and anticipate potential attack vectors. Automation also plays a significant role in adaptive defense strategies, enabling faster response times and reducing the burden on security teams. Automated systems can respond to certain types of threats without human intervention, improving efficiency and consistency.
Continuous improvement is a core principle of adaptive security, requiring organizations to regularly evaluate and update their defenses. This includes conducting security assessments, penetration testing, and vulnerability scanning to identify weaknesses in existing systems. Feedback from incident response activities is also used to refine security strategies and improve resilience.
Long-Term Relevance of Foundational Cybersecurity Knowledge
Despite rapid technological advancements and evolving threat landscapes, foundational cybersecurity knowledge remains highly relevant across all stages of professional development. Core security principles such as confidentiality, integrity, and availability continue to form the basis of all security practices. These principles provide a consistent framework for understanding how systems should be protected, regardless of changes in technology or infrastructure.
Understanding foundational concepts enables professionals to adapt more effectively to new environments and emerging technologies. While tools, platforms, and attack techniques may change over time, the underlying logic of security remains consistent. Risk management principles, access control models, and incident response methodologies continue to serve as essential components of cybersecurity practice.
Continuous learning is essential in this field, as professionals must stay updated with evolving threats and technologies. However, foundational knowledge provides the stability needed to interpret new developments and apply them effectively. It also ensures that professionals can transition between different roles and technologies without losing their core understanding of security principles.
As organizations continue to expand their digital operations, the demand for individuals with strong foundational security knowledge will remain high. This ensures that cybersecurity remains a dynamic yet structured discipline, where long-term success depends on both adaptability and a strong understanding of core principles.
Conclusion
The evolution of cybersecurity has transformed it from a specialized technical function into a core strategic requirement for organizations operating in a digitally interconnected world. As enterprises continue to expand their reliance on cloud computing, hybrid infrastructures, mobile systems, and distributed networks, the complexity of securing digital environments has increased significantly. This growing complexity has also elevated the importance of structured cybersecurity knowledge, particularly at the foundational level where professionals begin building their expertise. Entry-level security certification frameworks serve as a critical bridge between theoretical understanding and real-world application, ensuring that individuals entering the field possess a standardized baseline of knowledge that aligns with industry expectations.
At the center of this foundational landscape is the Security+ certification, which has consistently been recognized as a globally relevant benchmark for validating essential cybersecurity competencies. Its importance does not stem solely from its status as a certification but from its alignment with real-world security demands. The structured domains covered within the certification reflect the actual responsibilities of security professionals working in modern IT environments. These responsibilities include identifying and mitigating threats, implementing secure system configurations, managing operational security tasks, and understanding governance and compliance requirements. Each of these areas contributes to building a comprehensive understanding of how cybersecurity functions within an organization.
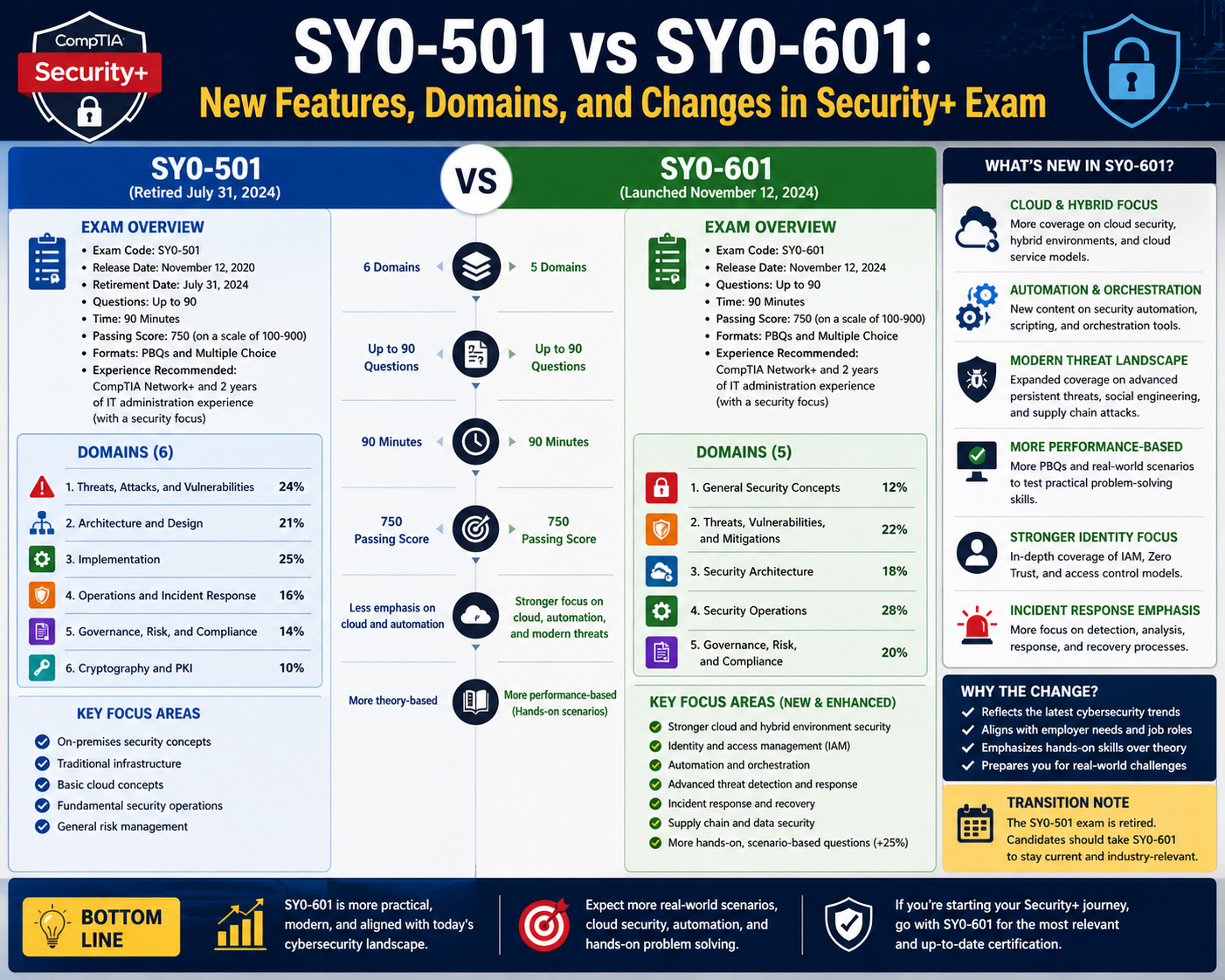
One of the most significant aspects of Security+ is its ability to adapt to evolving threat landscapes. Cybersecurity is not a static field; it changes continuously in response to new technologies, emerging vulnerabilities, and increasingly sophisticated attack methods. As a result, certification frameworks must evolve to remain relevant. The transition from earlier exam versions to updated frameworks reflects this necessity for continuous improvement. Newer versions place greater emphasis on applied knowledge, scenario-based problem-solving, and the ability to analyze complex security situations. This shift ensures that professionals are not only familiar with theoretical concepts but are also capable of applying them in dynamic and unpredictable environments.
The modern cybersecurity ecosystem is characterized by a wide range of threats that extend beyond traditional malware and network intrusions. Attackers now leverage advanced techniques such as social engineering, automated exploitation tools, artificial intelligence-driven attacks, and multi-stage intrusion campaigns. These threats target not only technical vulnerabilities but also human behavior and organizational processes. As a result, security professionals must develop a holistic understanding of cybersecurity that integrates technical, operational, and behavioral perspectives. Foundational certification frameworks play a crucial role in developing this understanding by introducing candidates to the full spectrum of threat types and defense mechanisms.
Another critical dimension of cybersecurity today is the increasing reliance on hybrid and cloud-based infrastructures. Organizations are no longer operating within isolated network boundaries; instead, they function across distributed environments that span on-premises systems, cloud platforms, and remote access networks. This shift introduces new challenges related to identity management, data protection, access control, and system visibility. Security professionals must understand how to maintain consistent security policies across these diverse environments while ensuring compliance with regulatory standards. Foundational certifications help build this understanding by introducing key concepts related to secure architecture, system integration, and risk management across multiple platforms.
Operational security has also become a central focus in modern cybersecurity practice. The ability to continuously monitor systems, detect anomalies, and respond to incidents in real time is essential for minimizing the impact of security breaches. Organizations must maintain constant vigilance over their digital environments, analyzing logs, monitoring traffic, and identifying suspicious behavior before it escalates into major incidents. Incident response frameworks provide structured approaches for handling security events, ensuring that organizations can quickly contain threats, eliminate vulnerabilities, and restore normal operations. Foundational knowledge in these areas is critical for developing effective security teams capable of responding to real-world challenges.
Governance, risk management, and compliance further strengthen the strategic importance of cybersecurity knowledge. These elements ensure that security practices are aligned with organizational goals, legal requirements, and industry standards. Governance establishes the framework for decision-making and accountability, risk management identifies and evaluates potential threats, and compliance ensures adherence to regulatory obligations. Together, these components create a structured approach to cybersecurity that extends beyond technical implementation. Professionals who understand these concepts are better equipped to contribute to organizational security strategies and support long-term risk reduction efforts.
The value of foundational cybersecurity knowledge also lies in its long-term relevance. While technologies, tools, and attack methods continue to evolve, core security principles remain constant. Concepts such as confidentiality, integrity, and availability form the foundation of all cybersecurity practices. These principles provide a stable framework for understanding how systems should be protected, regardless of changes in infrastructure or technology. Professionals who develop a strong understanding of these fundamentals are better prepared to adapt to new environments and emerging challenges throughout their careers.
In addition, foundational certification frameworks support career progression by providing a structured entry point into the cybersecurity field. Many professionals begin their journey in IT support, system administration, or networking roles before transitioning into specialized security positions. A strong foundational certification helps bridge this transition by providing essential knowledge that is applicable across multiple domains. It also enhances professional credibility, demonstrating to employers that individuals possess verified skills aligned with industry standards.
The increasing demand for cybersecurity professionals across industries further highlights the importance of foundational knowledge. As cyber threats continue to grow in frequency and sophistication, organizations require skilled personnel who can implement effective security measures, identify vulnerabilities, and respond to incidents efficiently. This demand spans across sectors including finance, healthcare, government, technology, and critical infrastructure. In each of these environments, cybersecurity is not optional but essential for operational continuity and data protection.
Ultimately, the role of foundational cybersecurity certification is not limited to passing an exam or acquiring a credential. It represents the development of a security mindset that prioritizes risk awareness, proactive defense, and continuous improvement. It encourages professionals to think critically about system design, threat detection, and incident response. This mindset is essential for navigating the complexities of modern digital environments, where security challenges are constantly evolving.
As organizations continue to adopt new technologies and expand their digital ecosystems, the importance of structured cybersecurity knowledge will only increase. Foundational certifications will remain a key component in preparing professionals to meet these challenges, ensuring that they possess the skills and understanding required to protect systems, data, and operations effectively.